| File name: | 十一月份公司值班人员调班通知.cmd |
| Full analysis: | https://app.any.run/tasks/c8f37966-5c6c-486c-a937-55f0b9a4e3ef |
| Verdict: | Suspicious activity |
| Analysis date: | November 12, 2020, 19:06:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 6B2532726499D8AC2FFD7B73C91D9139 |
| SHA1: | F60C2BF8B00EFAF508BC3F27A30D416389B3C9EA |
| SHA256: | 2C9E0F6E90B663293874332ACD2CAB44B8A28011337C99E828E86E3B9D1585C2 |
| SSDEEP: | 6144:Ko5Pghw3miIHzAzMNsdYOrRrRZJ/jr5MR6p:Kor3miIHoMOdYOrR9DCAp |
MALICIOUS
Application was dropped or rewritten from another process
- VGAuthService.exe (PID: 1484)
Loads dropped or rewritten executable
- VGAuthService.exe (PID: 1484)
Loads the Task Scheduler COM API
- VGAuthService.exe (PID: 1484)
SUSPICIOUS
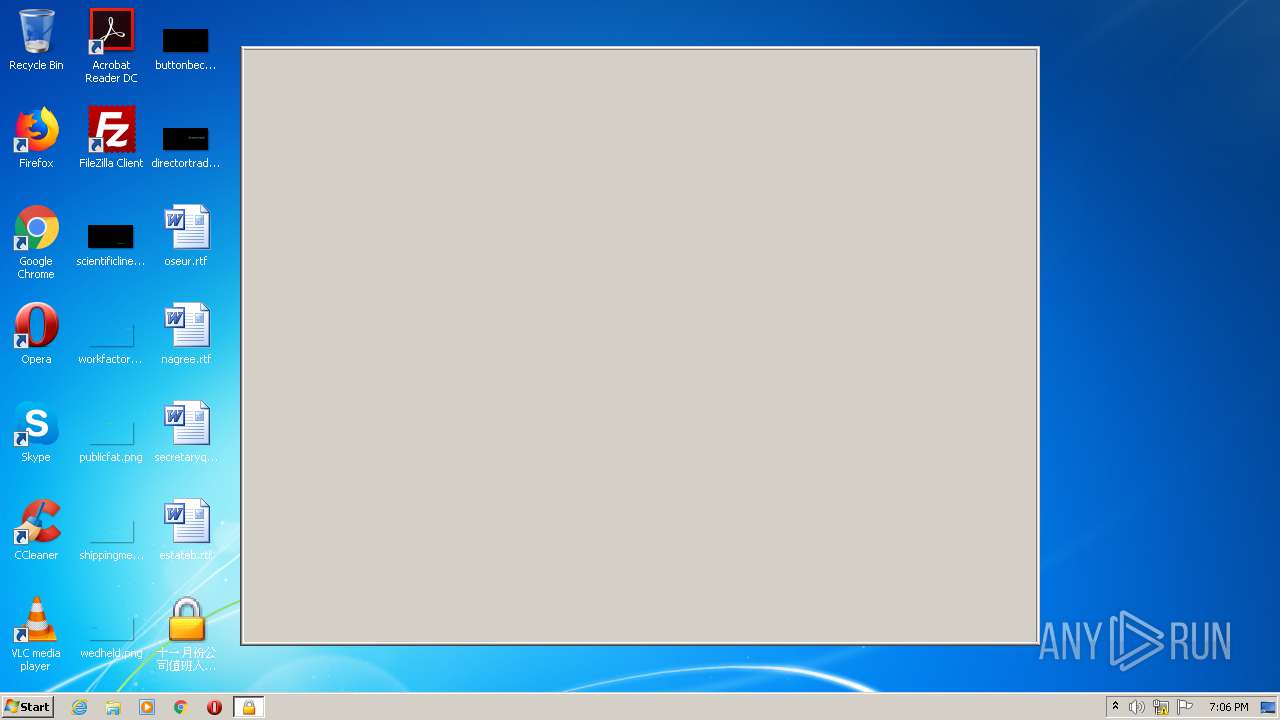
Executable content was dropped or overwritten
- 十一月份公司值班人员调班通知.cmd.exe (PID: 2588)
Creates files in the user directory
- 十一月份公司值班人员调班通知.cmd.exe (PID: 2588)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:06 09:10:07+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 151552 |
| InitializedDataSize: | 401408 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x21d0a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.1 |
| ProductVersionNumber: | 1.0.0.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| Comments: | 挂机锁屏系统 V1.0 |
| CompanyName: | 小蔡软件 |
| FileDescription: | 挂机锁屏系统 V1.0 |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | 挂机锁屏系统 |
| LegalCopyright: | 版权所有 (C) 2007-2008 |
| LegalTrademarks: | - |
| OriginalFileName: | LOCK.EXE |
| PrivateBuild: | - |
| ProductName: | 小蔡软件 |
| ProductVersion: | 1, 0, 0, 1 |
| SpecialBuild: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Nov-2020 08:10:07 |
| Detected languages: |
|
| Comments: | 挂机锁屏系统 V1.0 |
| CompanyName: | 小蔡软件 |
| FileDescription: | 挂机锁屏系统 V1.0 |
| FileVersion: | 1, 0, 0, 1 |
| InternalName: | 挂机锁屏系统 |
| LegalCopyright: | 版权所有 (C) 2007-2008 |
| LegalTrademarks: | - |
| OriginalFilename: | LOCK.EXE |
| PrivateBuild: | - |
| ProductName: | 小蔡软件 |
| ProductVersion: | 1, 0, 0, 1 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 06-Nov-2020 08:10:07 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00024EE6 | 0x00025000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.47567 |
.rdata | 0x00026000 | 0x00005DFA | 0x00006000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.26498 |
.data | 0x0002C000 | 0x0000169C | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.49349 |
.idata | 0x0002E000 | 0x000026C1 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.18782 |
.rsrc | 0x00031000 | 0x00053B93 | 0x00054000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.03756 |
.reloc | 0x00085000 | 0x00002968 | 0x00003000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.04634 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.69239 | 824 | UNKNOWN | Chinese - PRC | RT_VERSION |
2 | 5.9896 | 2444 | UNKNOWN | Chinese - PRC | RT_ICON |
3 | 4.42488 | 4268 | UNKNOWN | Chinese - PRC | RT_ICON |
4 | 3.35437 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
5 | 3.34394 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
6 | 2.67733 | 744 | UNKNOWN | Chinese - PRC | RT_ICON |
7 | 3.82255 | 110 | UNKNOWN | Chinese - PRC | RT_STRING |
8 | 2.40481 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
9 | 2.61916 | 296 | UNKNOWN | Chinese - PRC | RT_ICON |
10 | 3.34394 | 2216 | UNKNOWN | Chinese - PRC | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MFC42.DLL |
MSVCRT.dll |
SHELL32.dll |
USER32.dll |
WINHTTP.dll |
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
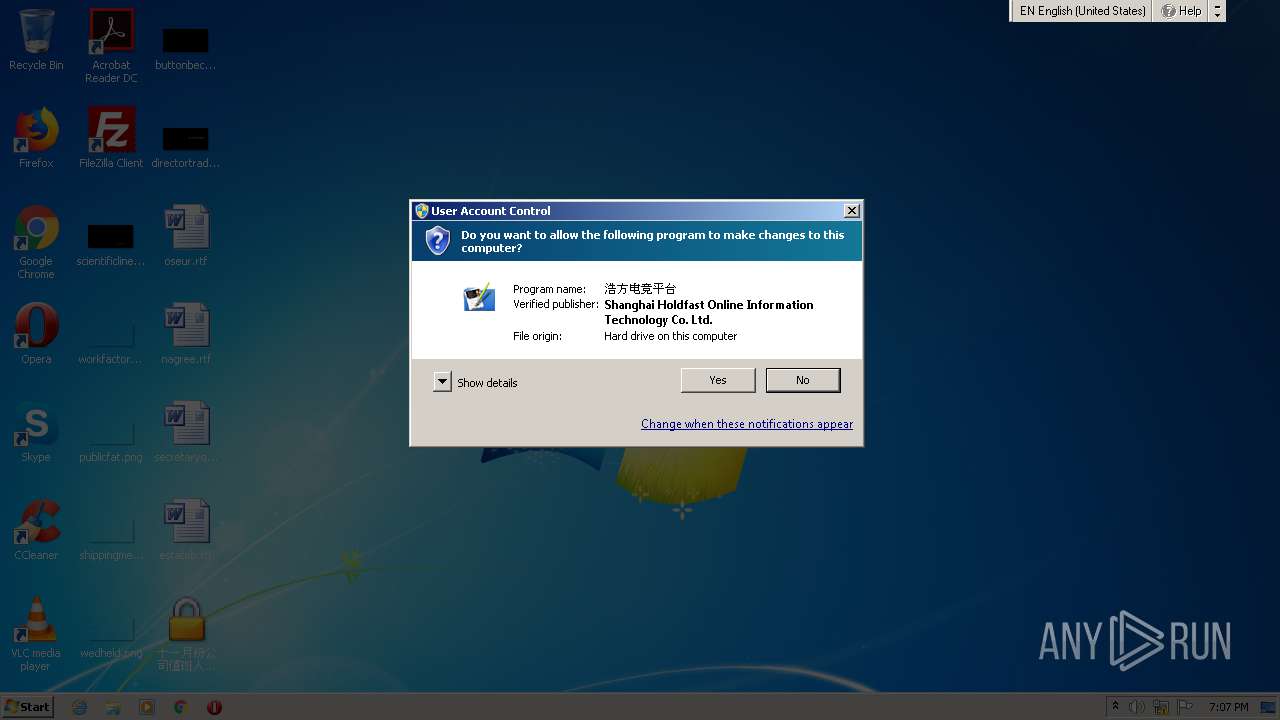
| 1484 | "C:\Users\admin\AppData\Roaming\VGAuthServices\VGAuthService.exe" -GetHFCWSPObj | C:\Users\admin\AppData\Roaming\VGAuthServices\VGAuthService.exe | — | 十一月份公司值班人员调班通知.cmd.exe | |||||||||||
User: admin Company: 上海浩方在线信息技术有限公司 Integrity Level: MEDIUM Description: 浩方电竞平台网页组件 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\Desktop\十一月份公司值班人员调班通知.cmd.exe" | C:\Users\admin\Desktop\十一月份公司值班人员调班通知.cmd.exe | explorer.exe | ||||||||||||
User: admin Company: 小蔡软件 Integrity Level: MEDIUM Description: 挂机锁屏系统 V1.0 Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
711
Read events
703
Write events
8
Delete events
0
Modification events
| (PID) Process: | (2588) 十一月份公司值班人员调班通知.cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2588) 十一月份公司值班人员调班通知.cmd.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1484) VGAuthService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1484) VGAuthService.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
4
Suspicious files
1
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\Public\Downloads\d6ytgg.zip | — | |
MD5:— | SHA256:— | |||
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\admin\AppData\Roaming\VGAuthServices\VMProtectSDK32.dll | executable | |
MD5:— | SHA256:— | |||
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\admin\AppData\Roaming\VGAuthServices\ErrHandle.dll | executable | |
MD5:— | SHA256:— | |||
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\admin\AppData\Roaming\VGAuthServices\temp.log | binary | |
MD5:— | SHA256:— | |||
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\admin\AppData\Roaming\VGAuthServices\task.dat | text | |
MD5:— | SHA256:— | |||
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\admin\AppData\Roaming\VGAuthServices\SvcProxy.dll | executable | |
MD5:— | SHA256:— | |||
| 2588 | 十一月份公司值班人员调班通知.cmd.exe | C:\Users\admin\AppData\Roaming\VGAuthServices\VGAuthService.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
0
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2588 | 十一月份公司值班人员调班通知.cmd.exe | HEAD | 200 | 43.249.24.202:80 | http://43.249.24.202/41100.zip | CN | — | — | suspicious |
2588 | 十一月份公司值班人员调班通知.cmd.exe | GET | 200 | 43.249.24.202:80 | http://43.249.24.202/41100.zip | CN | compressed | 5.87 Mb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2588 | 十一月份公司值班人员调班通知.cmd.exe | 43.249.24.202:80 | — | Sun Network (Hong Kong) Limited - HongKong Backbone | CN | suspicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
2588 | 十一月份公司值班人员调班通知.cmd.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |
2588 | 十一月份公司值班人员调班通知.cmd.exe | Potentially Bad Traffic | ET INFO Dotted Quad Host ZIP Request |