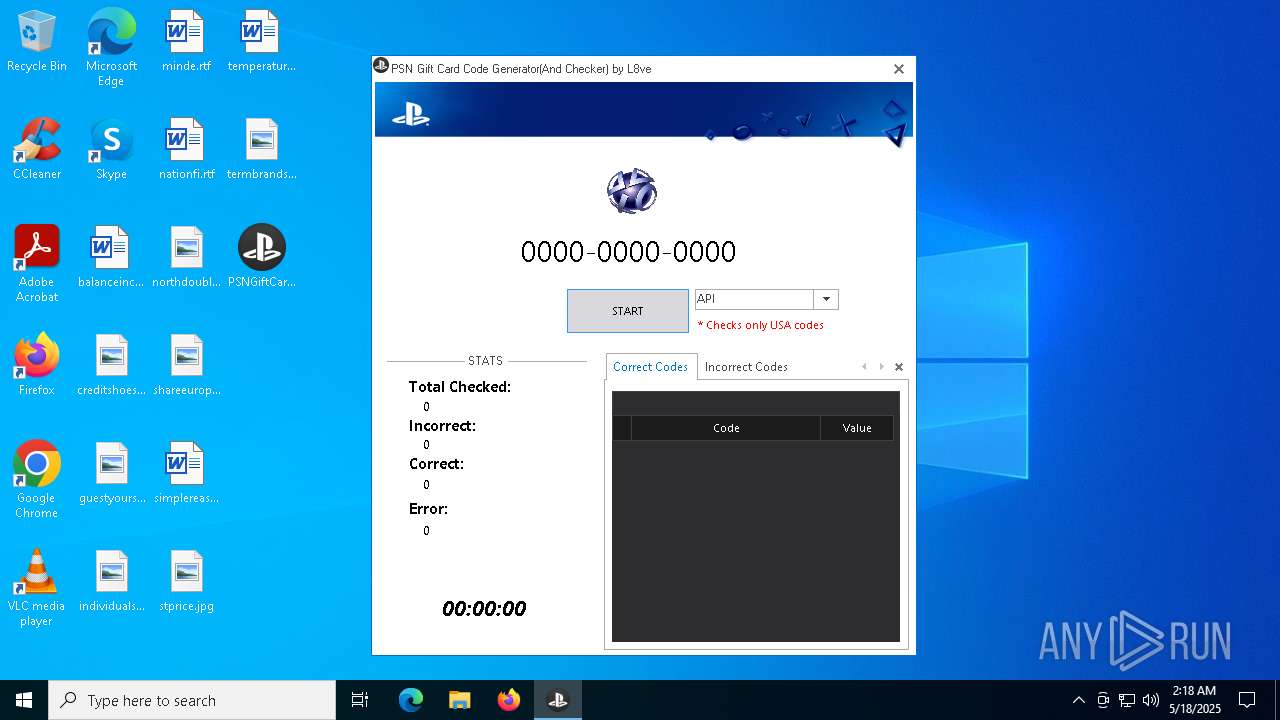
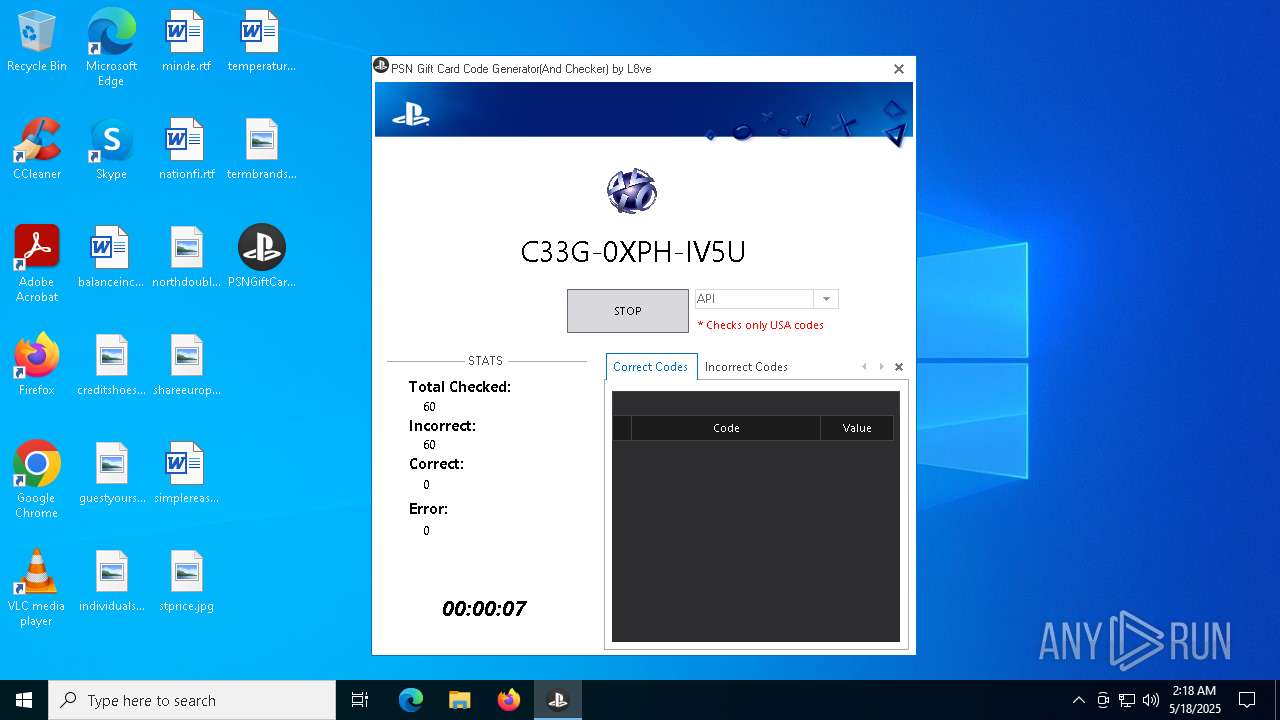
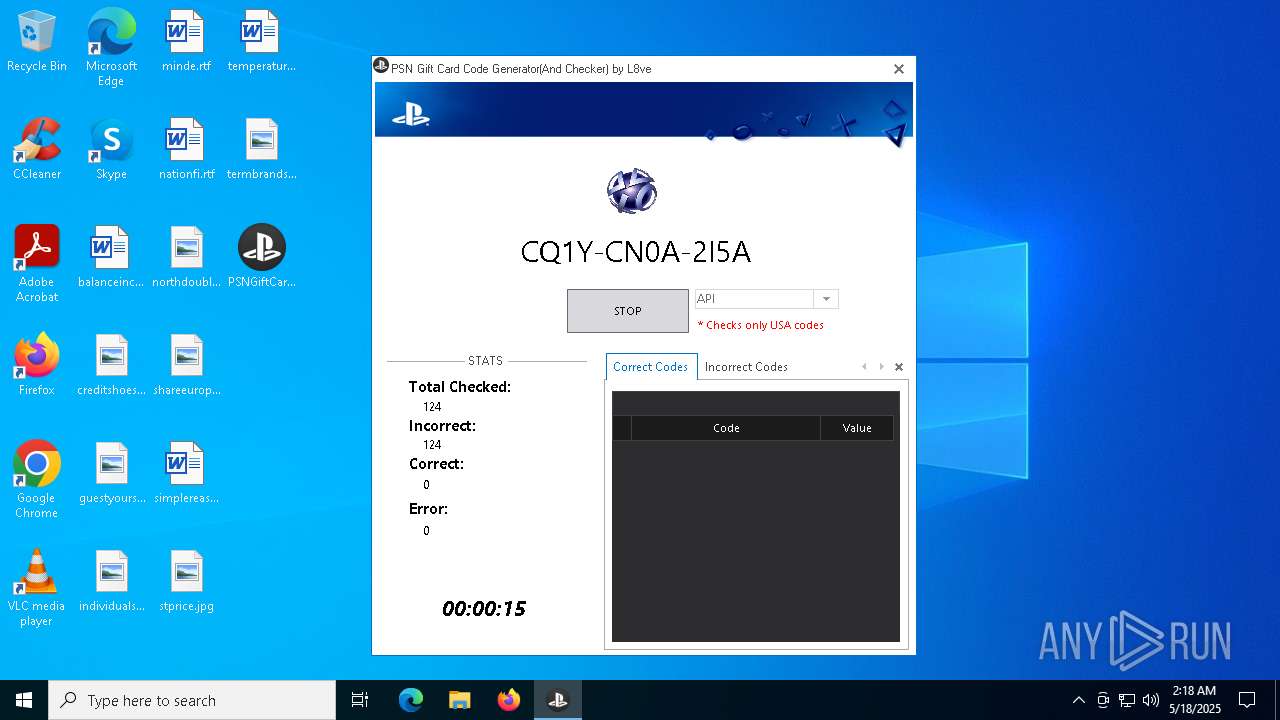
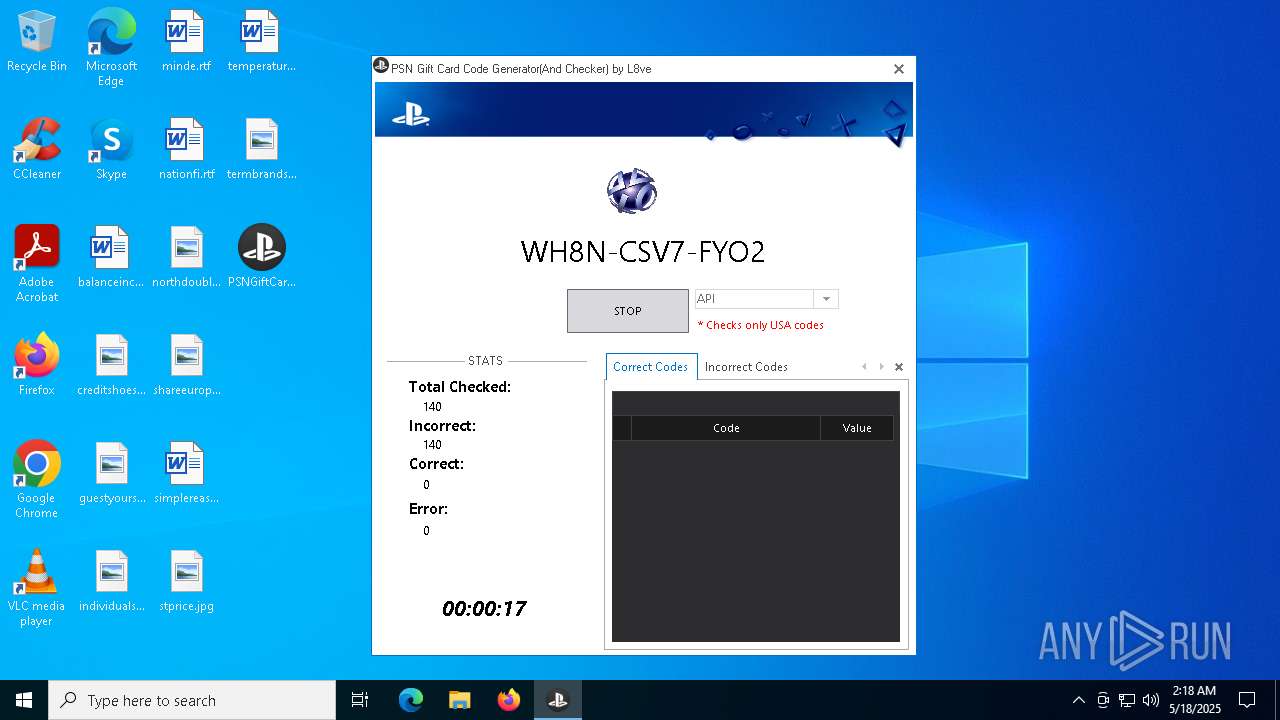
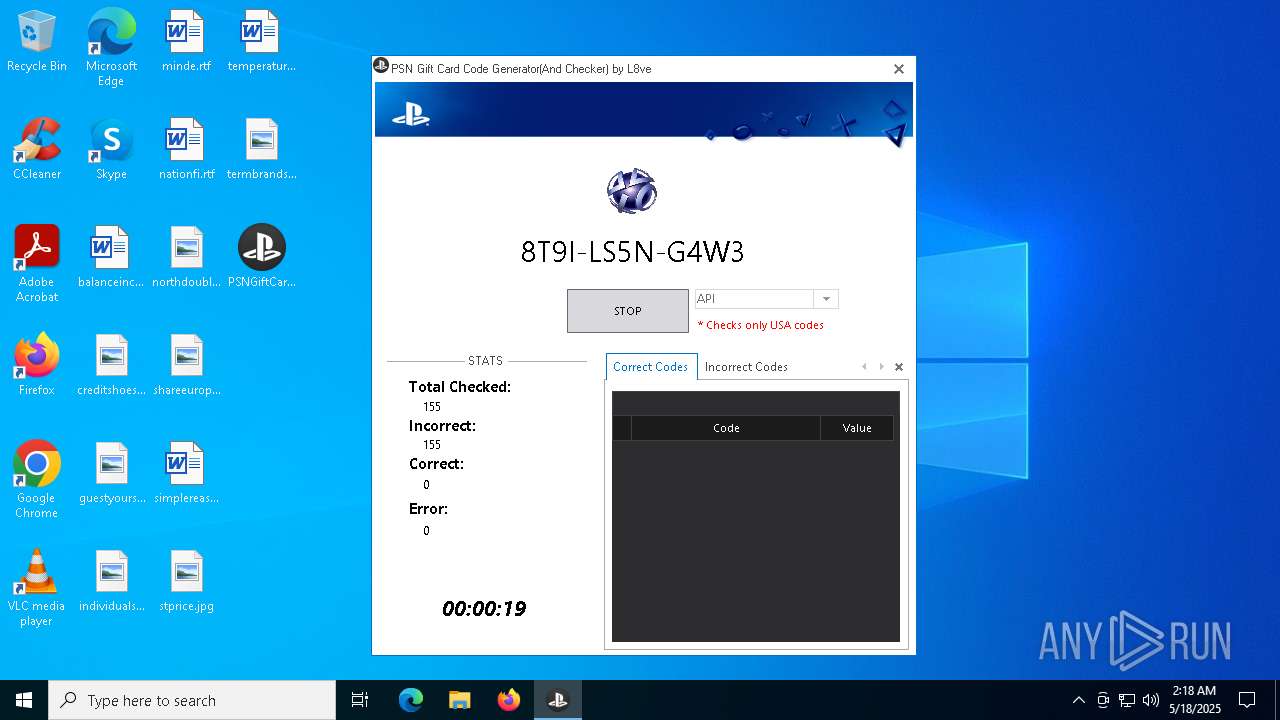
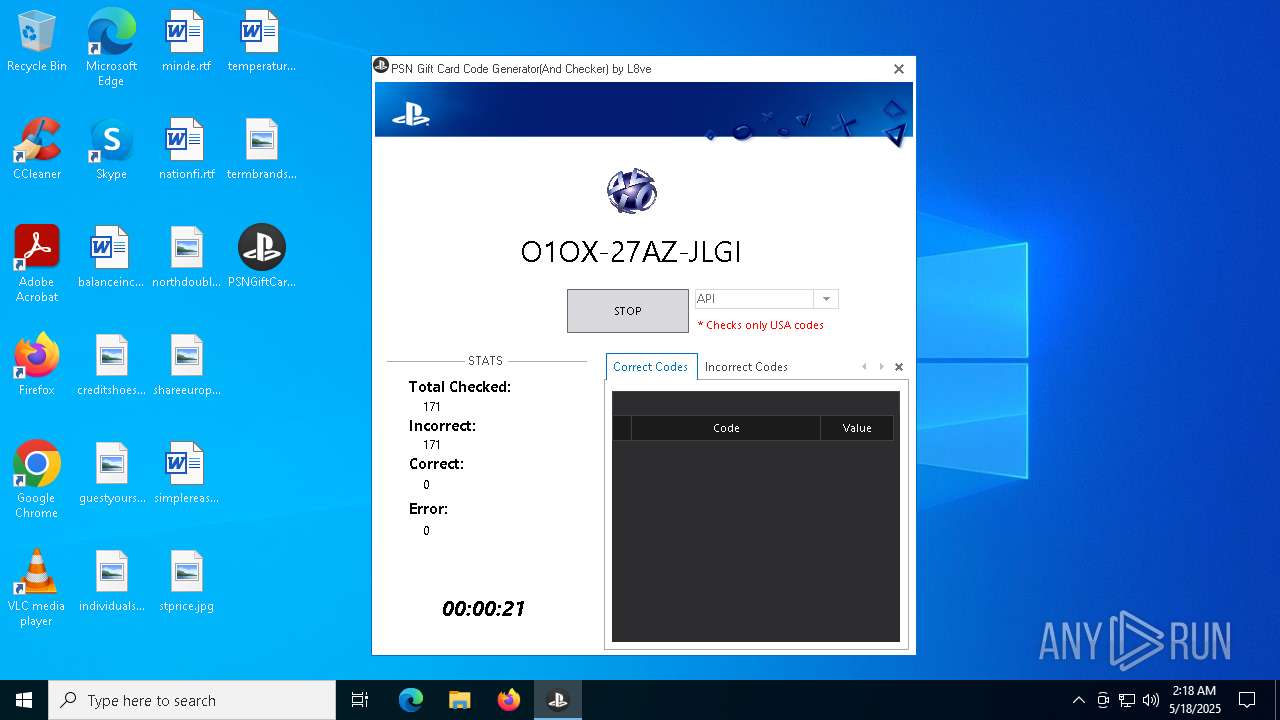
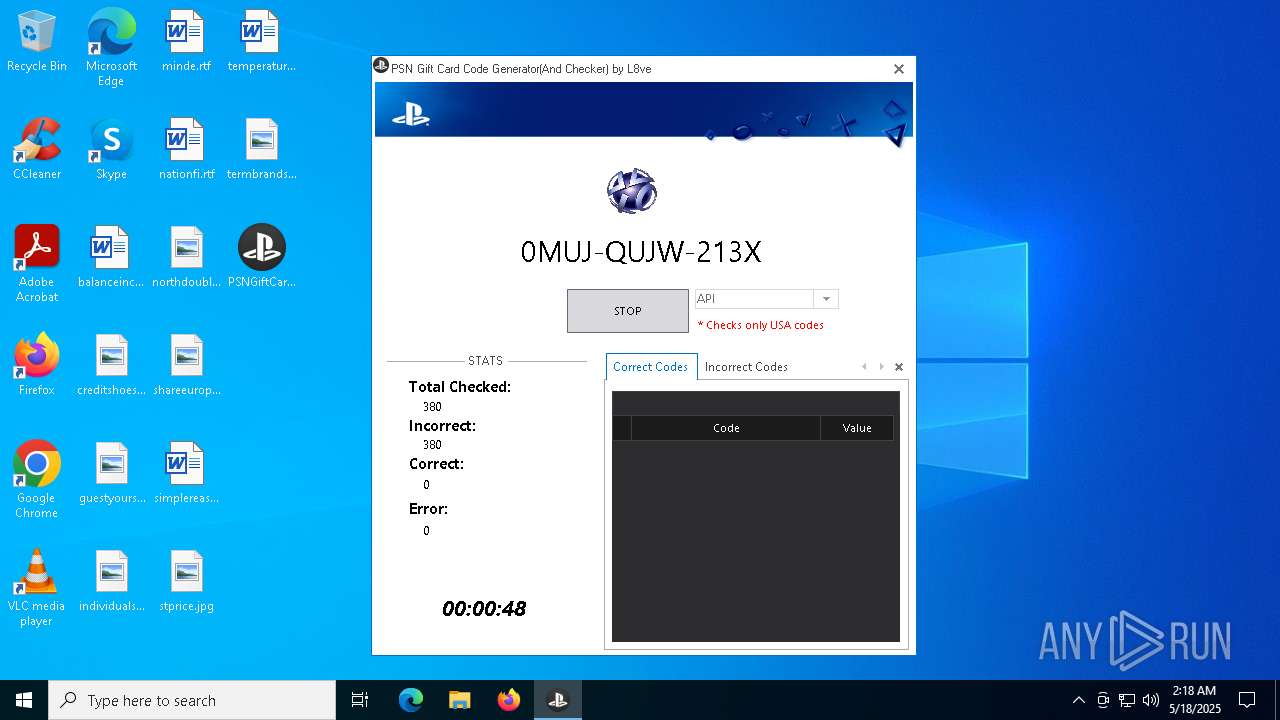
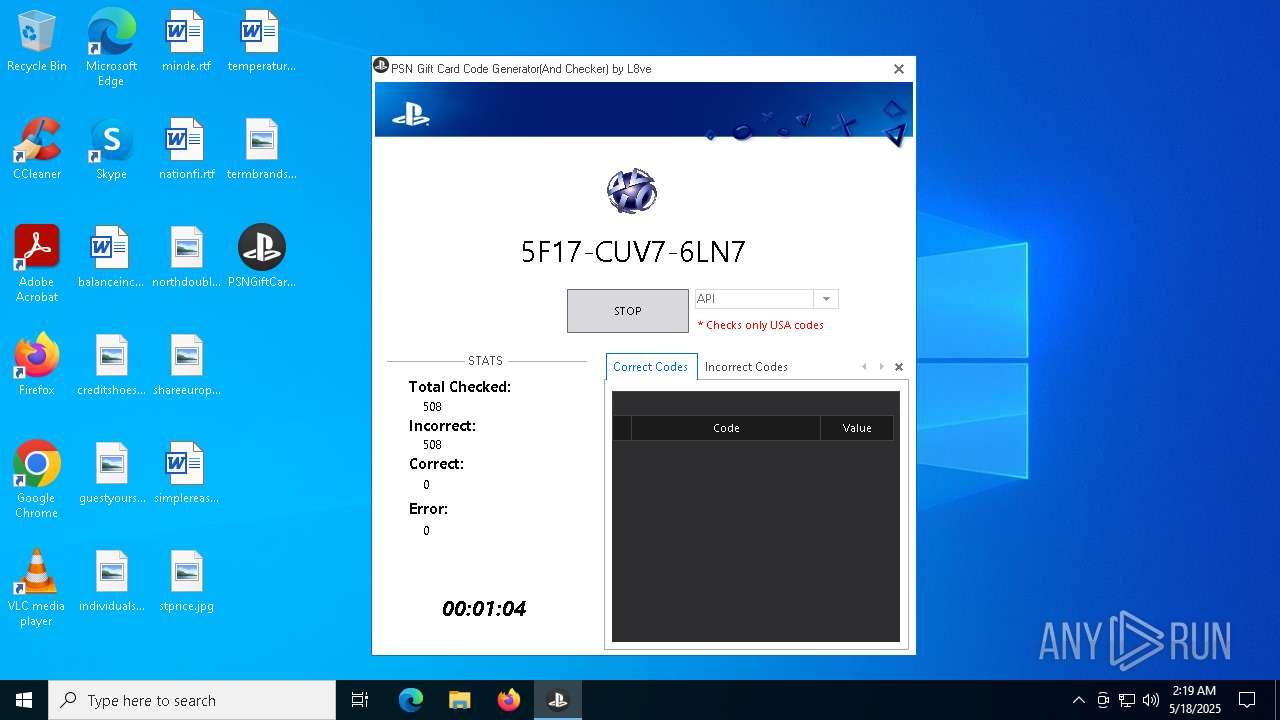
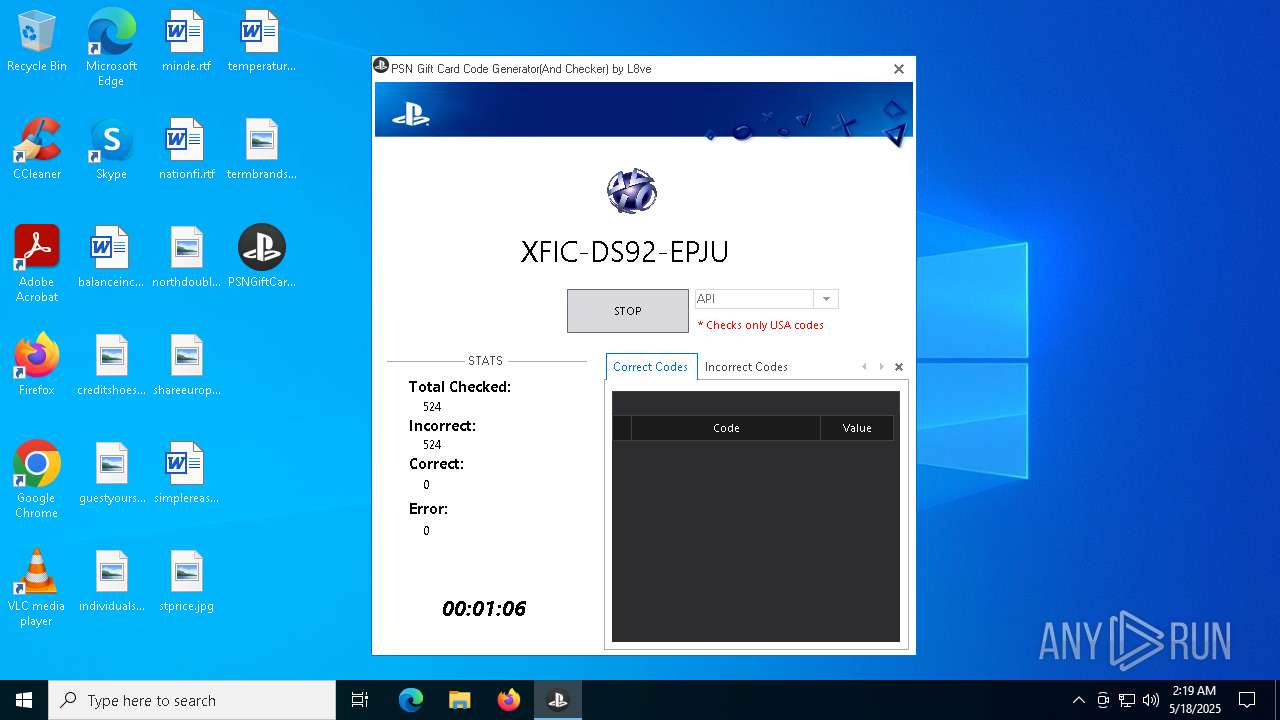
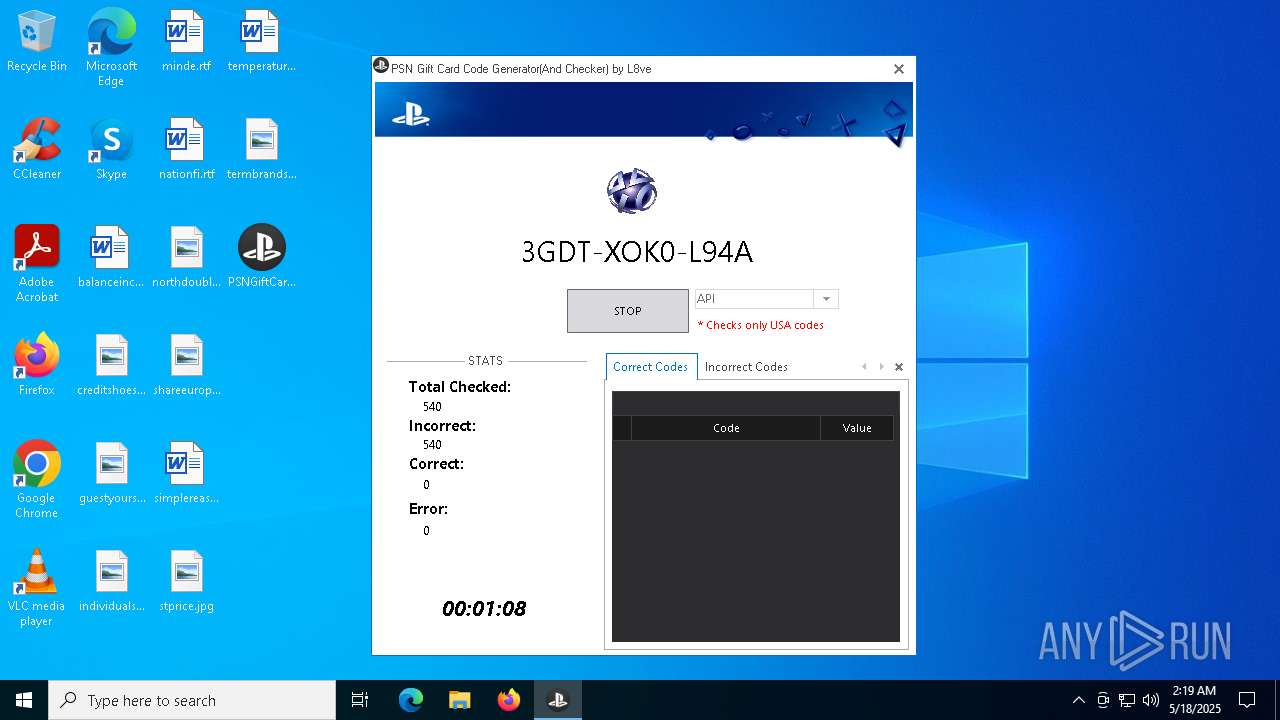
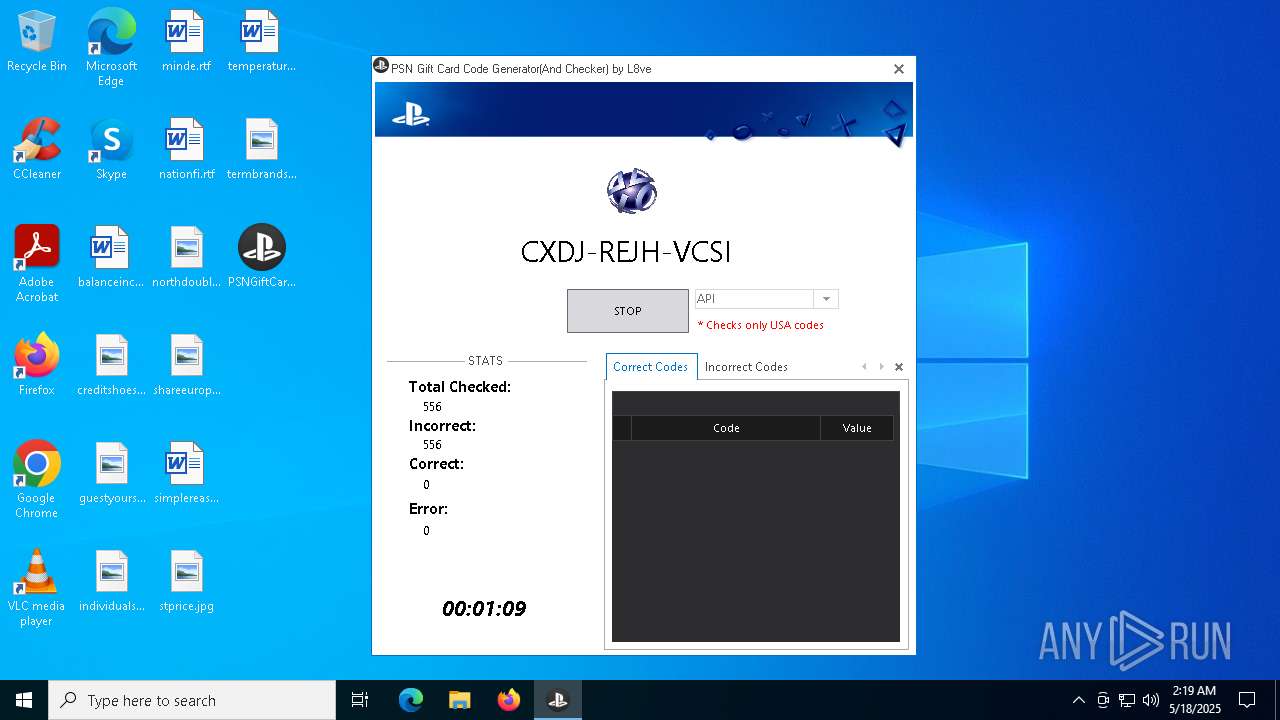
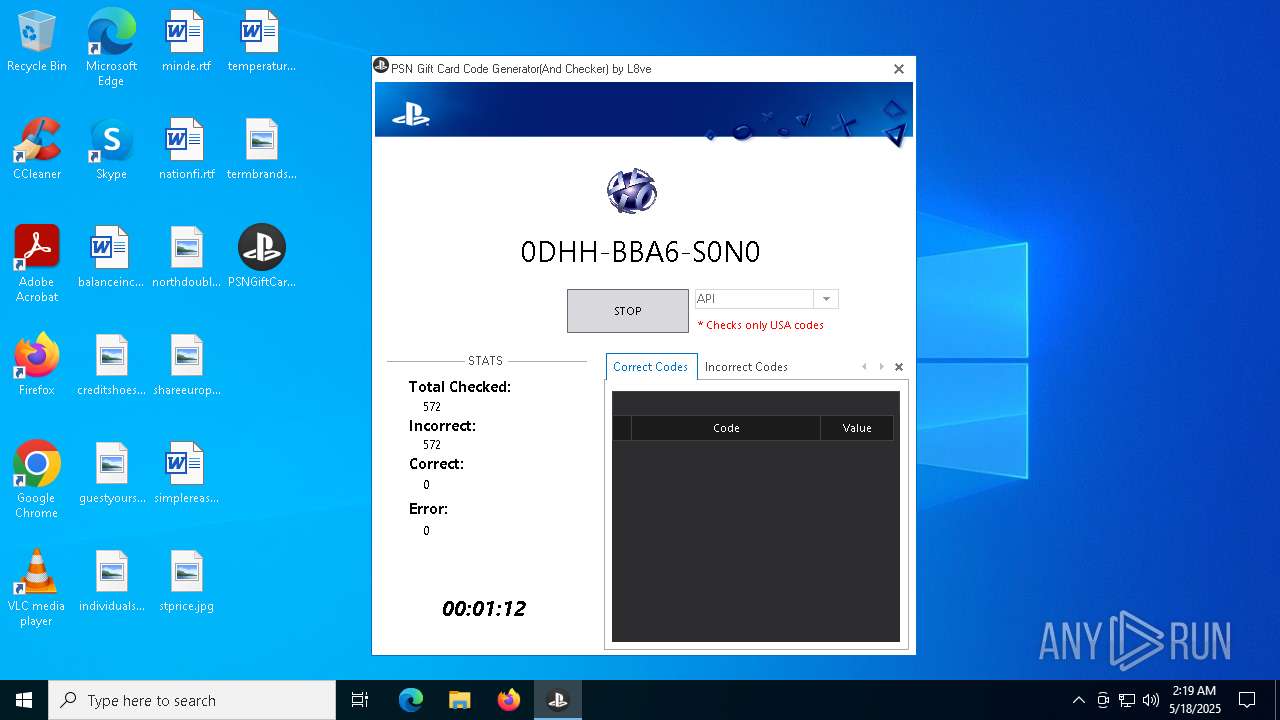
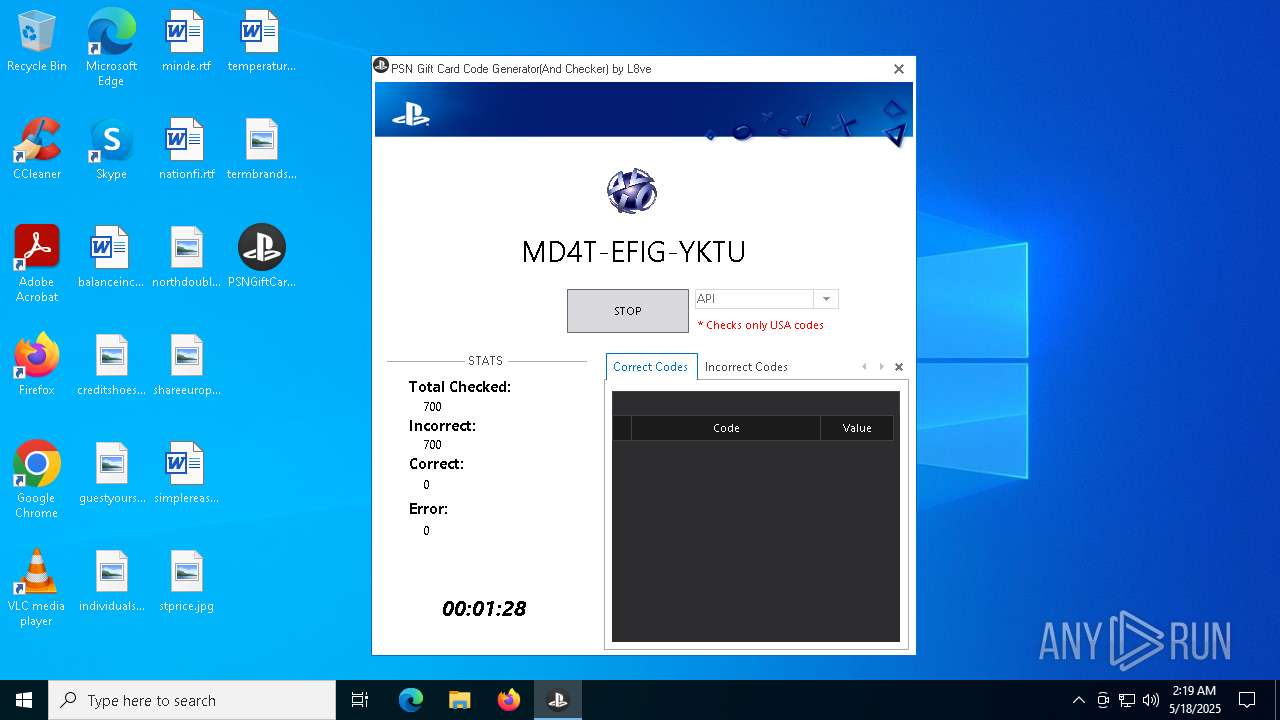
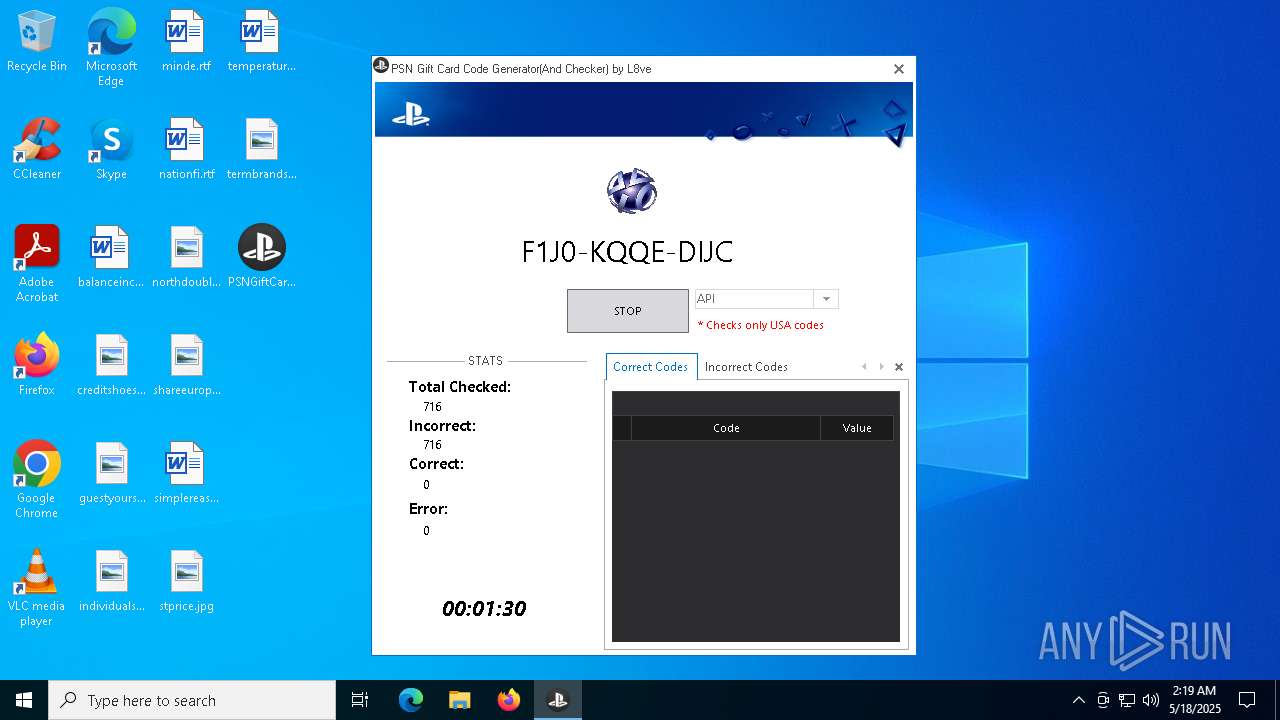
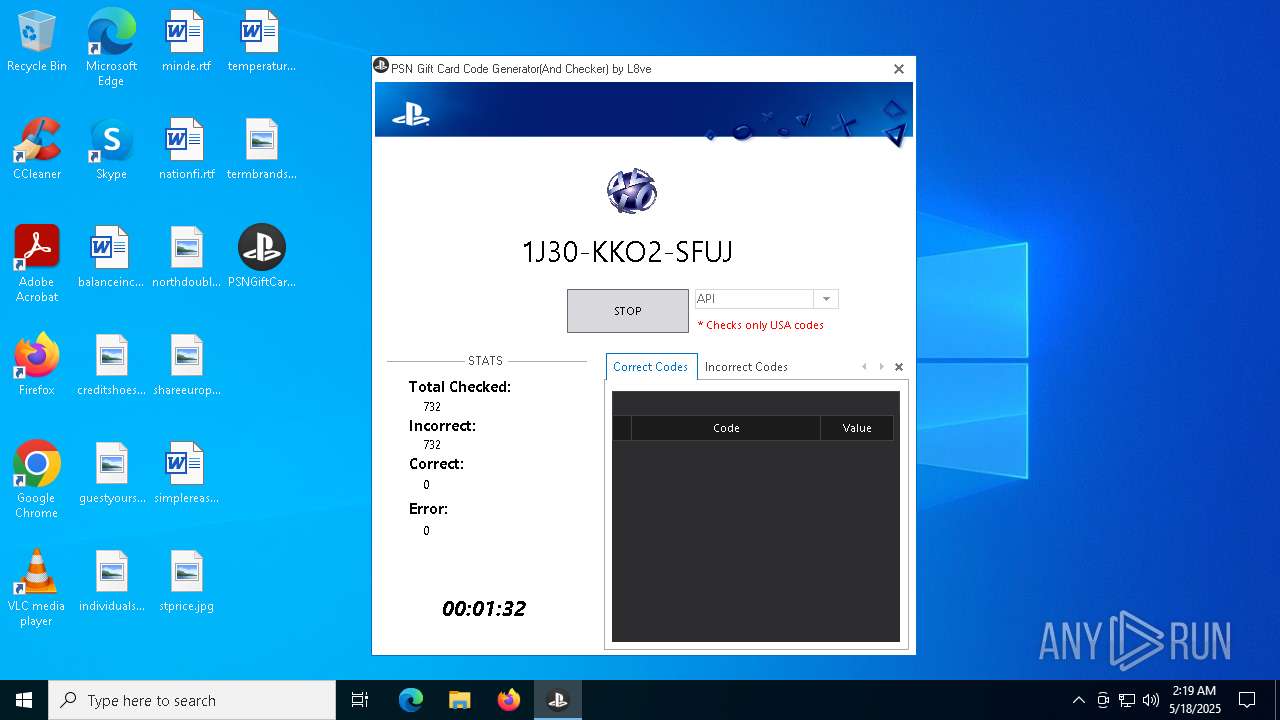
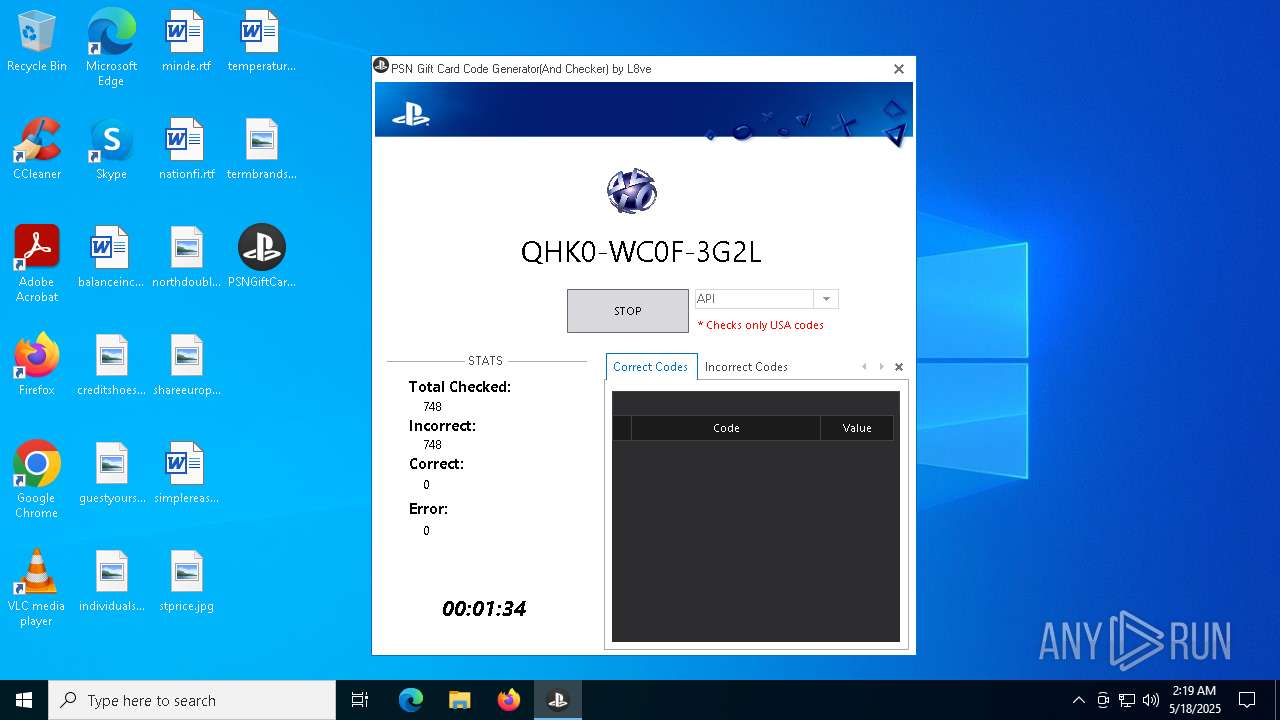
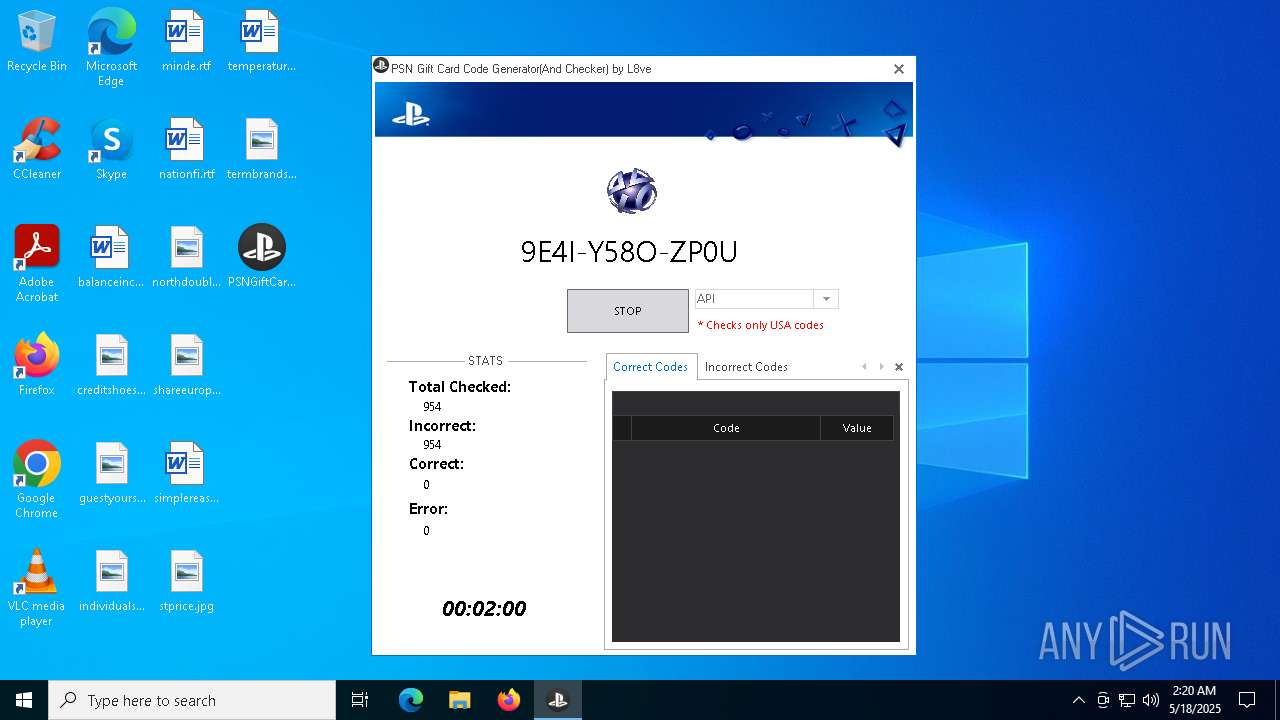
| File name: | PSNGiftCardCodeGeneratorandCheckerV1.exe |
| Full analysis: | https://app.any.run/tasks/e2b1f264-bba2-4bd0-8d93-78a156d89fbf |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 02:17:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 6 sections |
| MD5: | 0869DE165AB06851122101EF8BF4669E |
| SHA1: | 4CDC5EBD366FFF1BBF43B61AFEE3BF428CFB2E15 |
| SHA256: | 2C9D330D1215F8FEB174C729A31CF76F970D975B8FB62E40B974C4AD89E93381 |
| SSDEEP: | 98304:5hg4P8XbuFICm6yPAjEN6rBk35BjsThPudR9udr8WYU9VuBtkDulsc+LnS5sCyri:cX5GLYzBwCXLtCU2y2D |
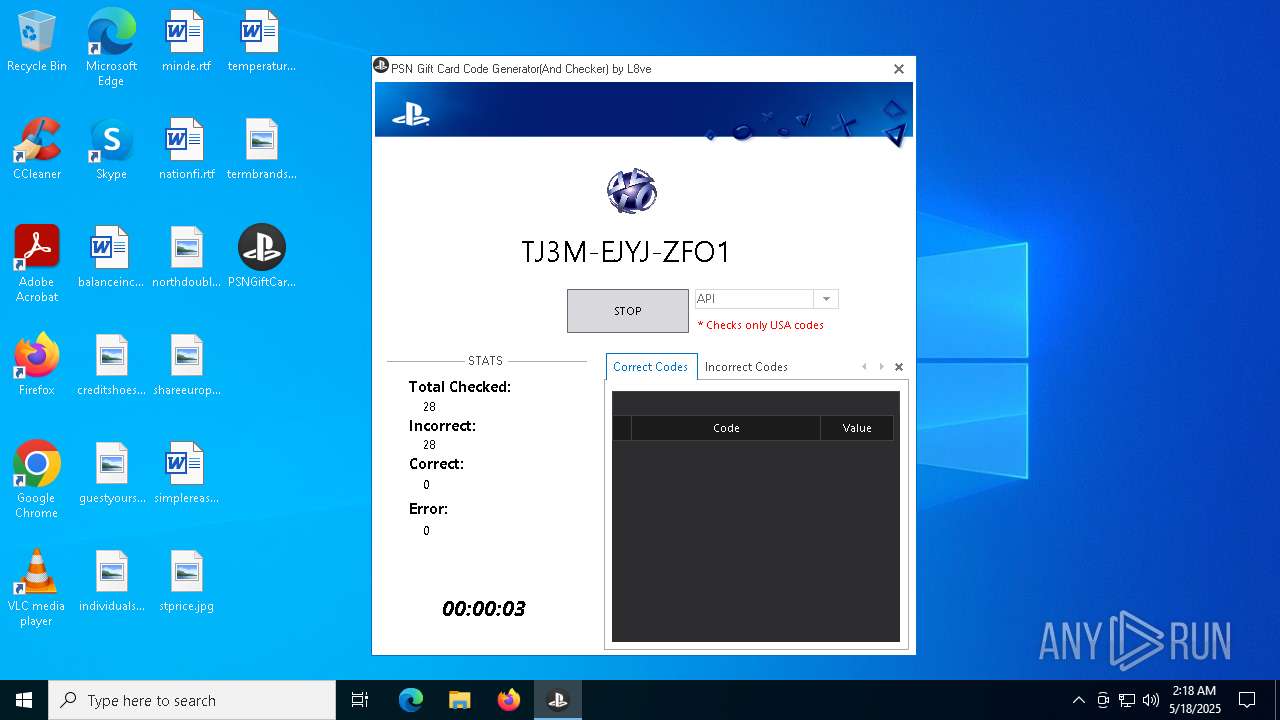
MALICIOUS
Changes the autorun value in the registry
- cvcxxxx.exe (PID: 1804)
Runs injected code in another process
- cvcxxxx.exe (PID: 1804)
Application was injected by another process
- explorer.exe (PID: 5492)
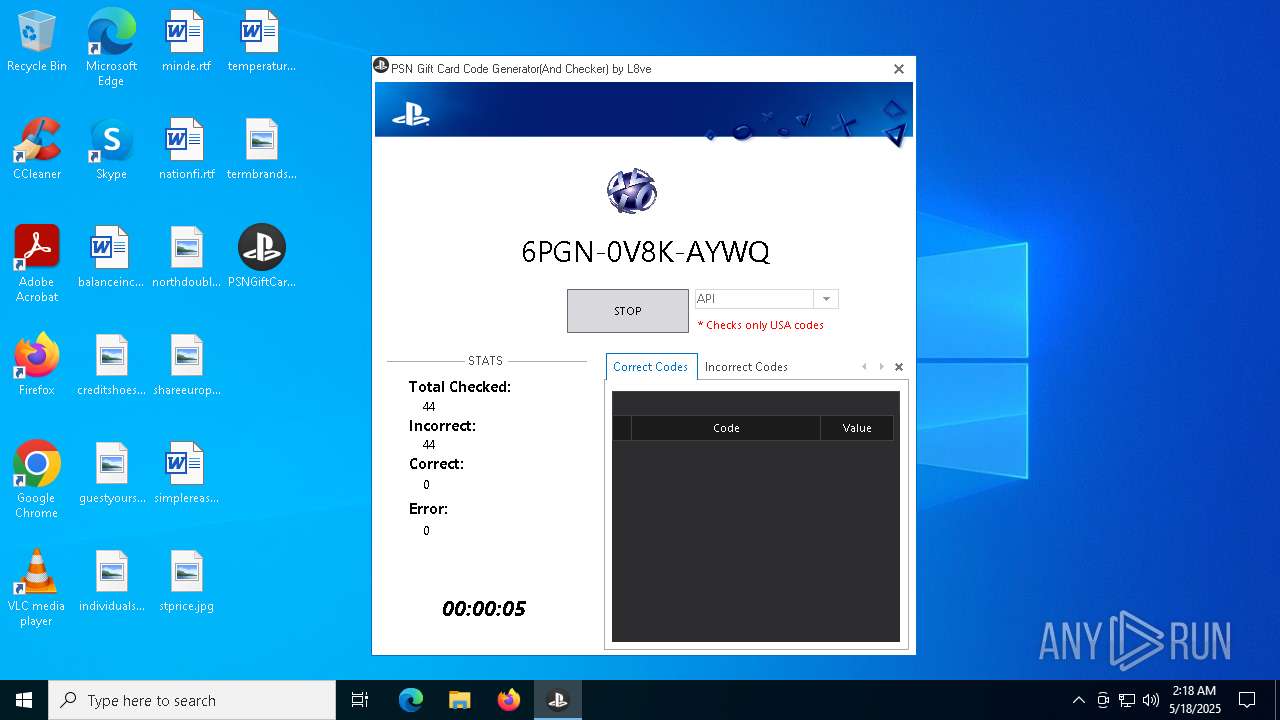
SUSPICIOUS
Executable content was dropped or overwritten
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
- cvcxxxx.exe (PID: 1804)
Reads security settings of Internet Explorer
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
Reads the date of Windows installation
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
The process creates files with name similar to system file names
- cvcxxxx.exe (PID: 1804)
Connects to the server without a host name
- explorer.exe (PID: 5492)
INFO
The sample compiled with english language support
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
Reads the computer name
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
- Launcher.exe (PID: 4408)
Checks supported languages
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
- cvcxxxx.exe (PID: 1804)
- Launcher.exe (PID: 4408)
- System.exe (PID: 5204)
Creates files or folders in the user directory
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
- cvcxxxx.exe (PID: 1804)
Auto-launch of the file from Registry key
- cvcxxxx.exe (PID: 1804)
Disables trace logs
- Launcher.exe (PID: 4408)
Checks proxy server information
- slui.exe (PID: 1164)
- Launcher.exe (PID: 4408)
Process checks computer location settings
- PSNGiftCardCodeGeneratorandCheckerV1.exe (PID: 4040)
Reads the machine GUID from the registry
- Launcher.exe (PID: 4408)
Reads the software policy settings
- slui.exe (PID: 1164)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (46.3) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (41) |
| .exe | | | Win32 Executable (generic) (6.6) |
| .exe | | | Generic Win/DOS Executable (2.9) |
| .exe | | | DOS Executable Generic (2.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:05:17 19:16:54+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.4 |
| CodeSize: | 122880 |
| InitializedDataSize: | 9298944 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x5e78 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.2.1.1 |
| ProductVersionNumber: | 3.1.1.1 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | Opwcv |
| FileVersion: | 6.0.0.0 |
| InternalName: | Opwcv.exe |
| LegalCopyright: | (C) 2026 |
| OriginalFileName: | Opwcv.exe |
| ProductName: | Opwcv |
| ProductVersion: | 3.1.1.1 |
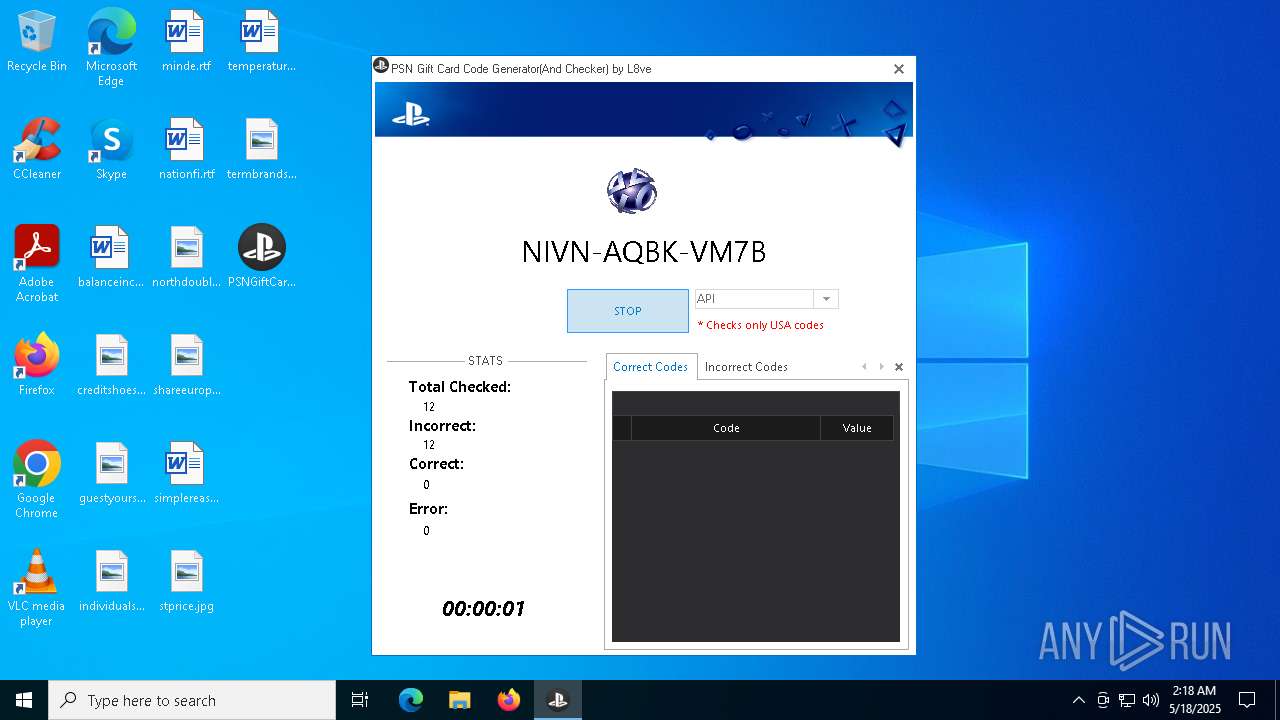
Total processes
126
Monitored processes
6
Malicious processes
2
Suspicious processes
1
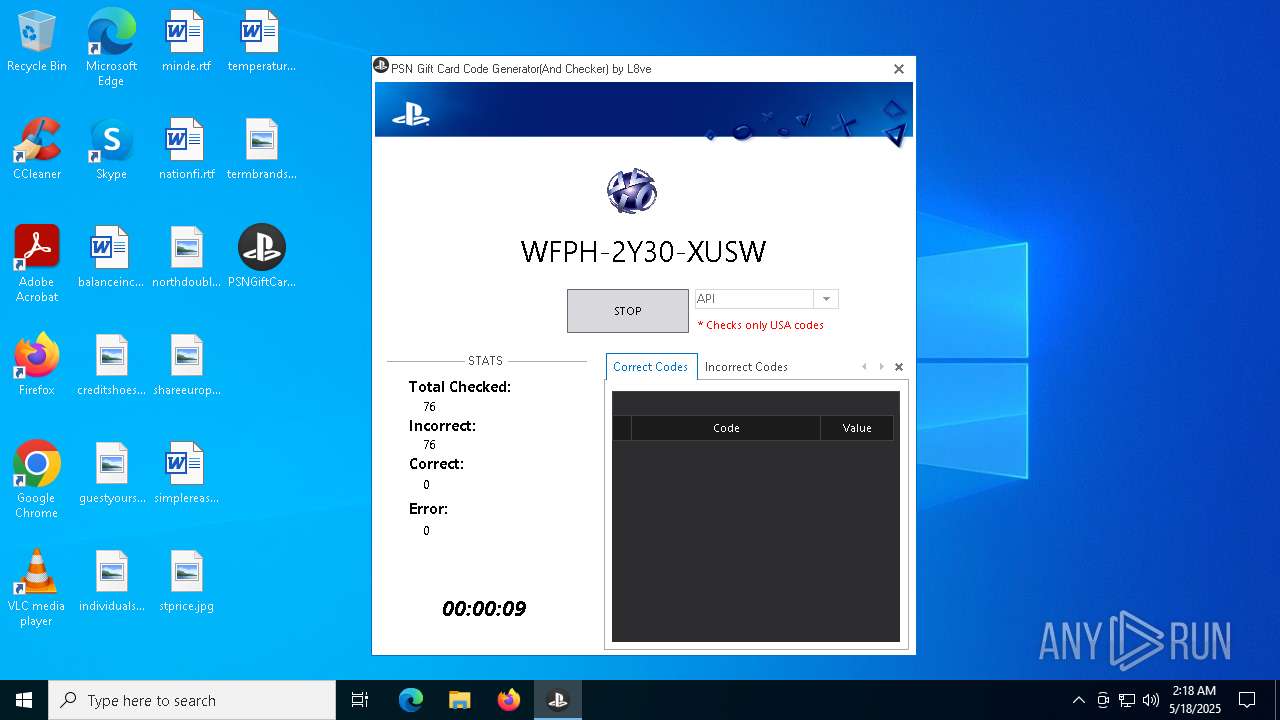
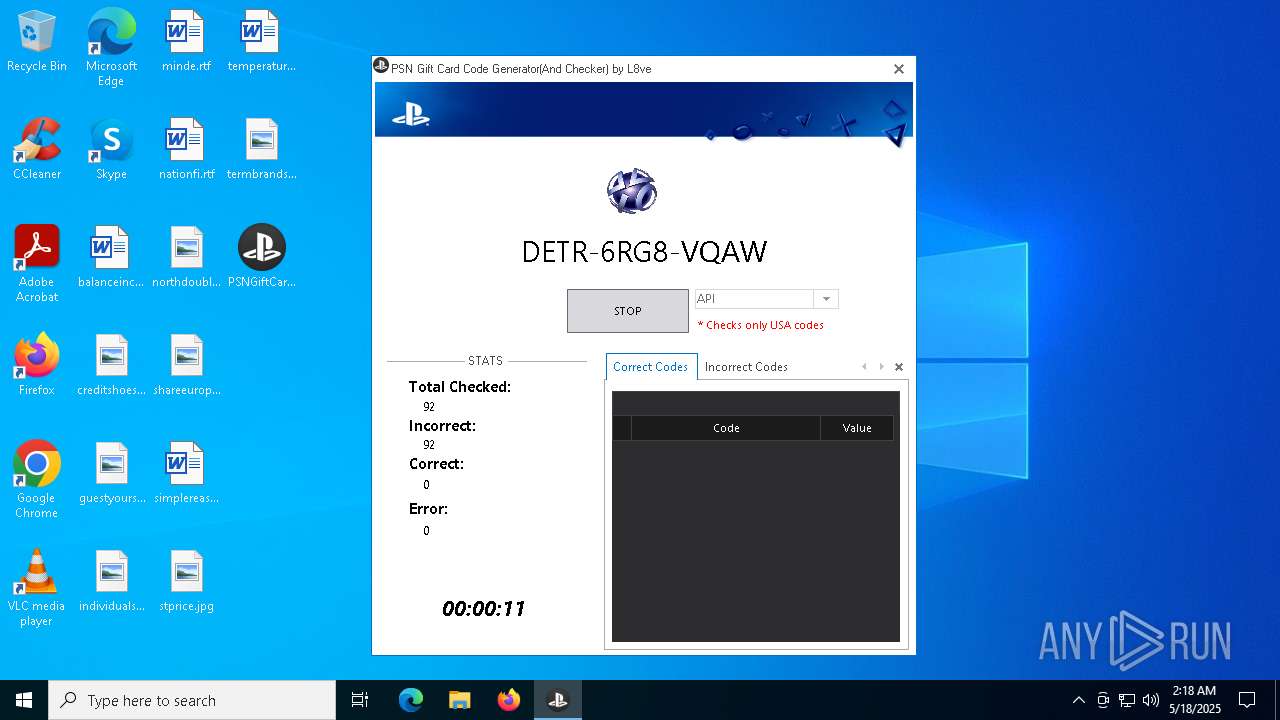
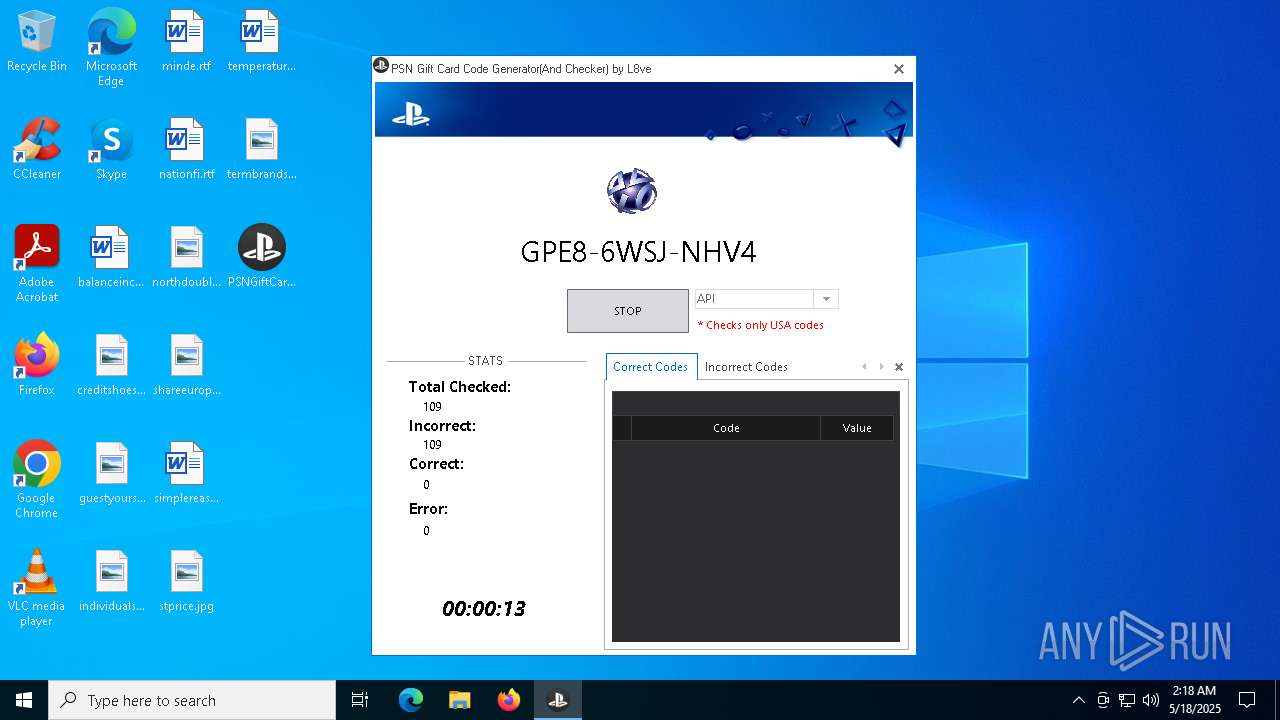
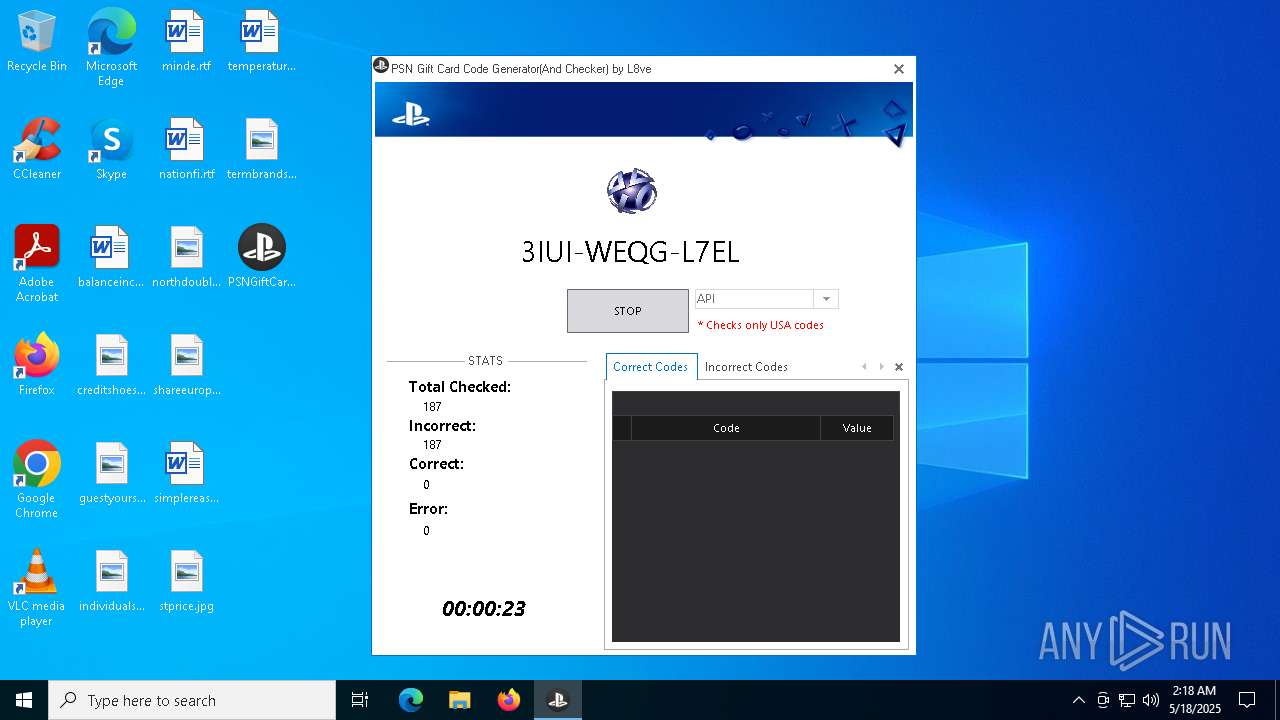
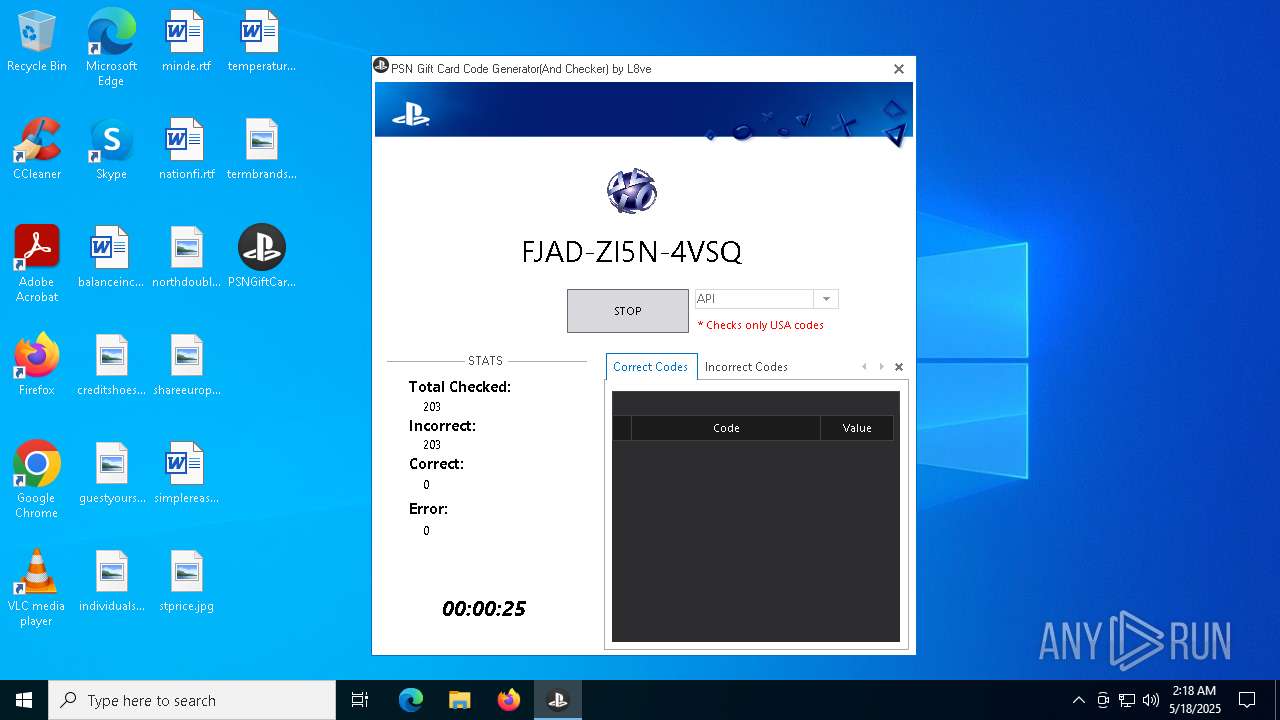
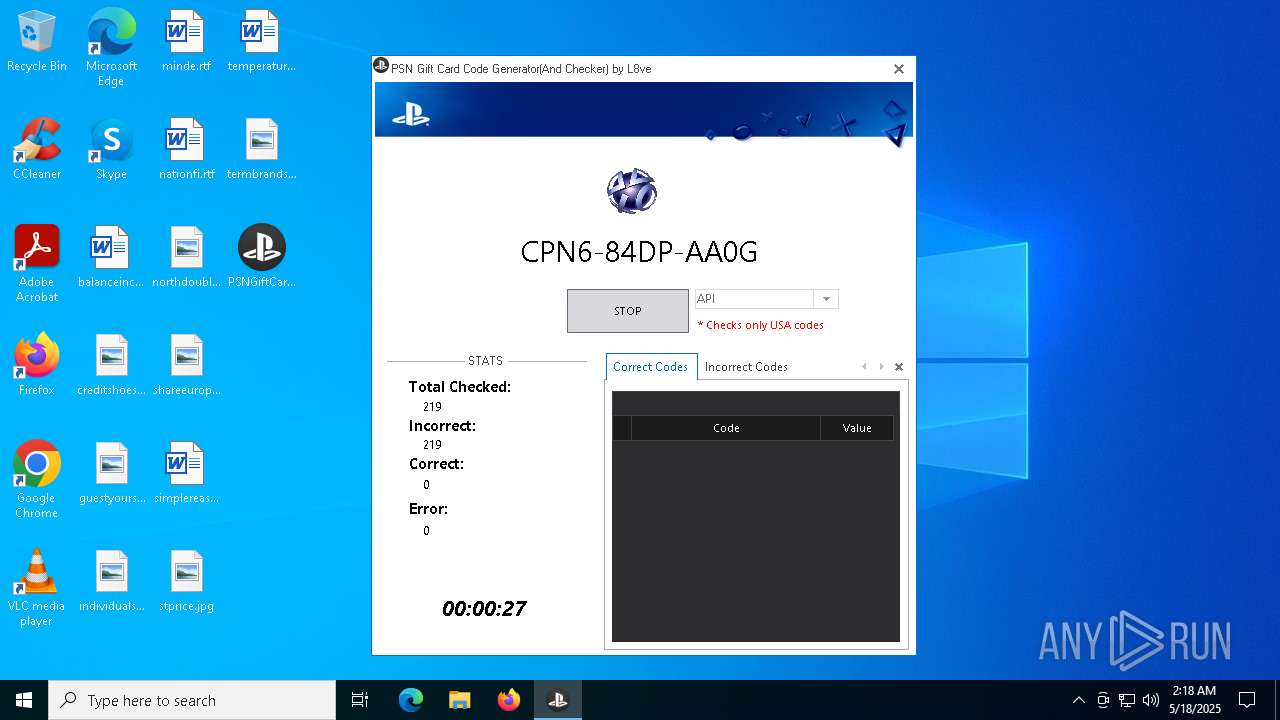
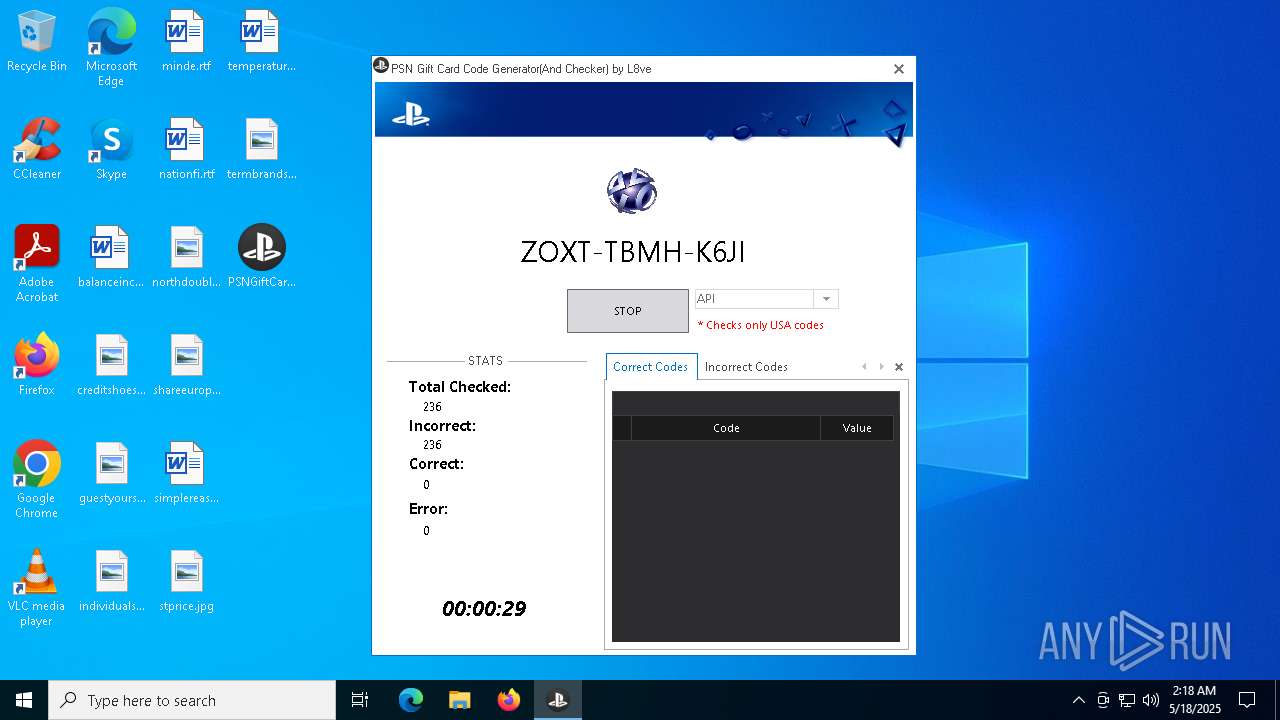
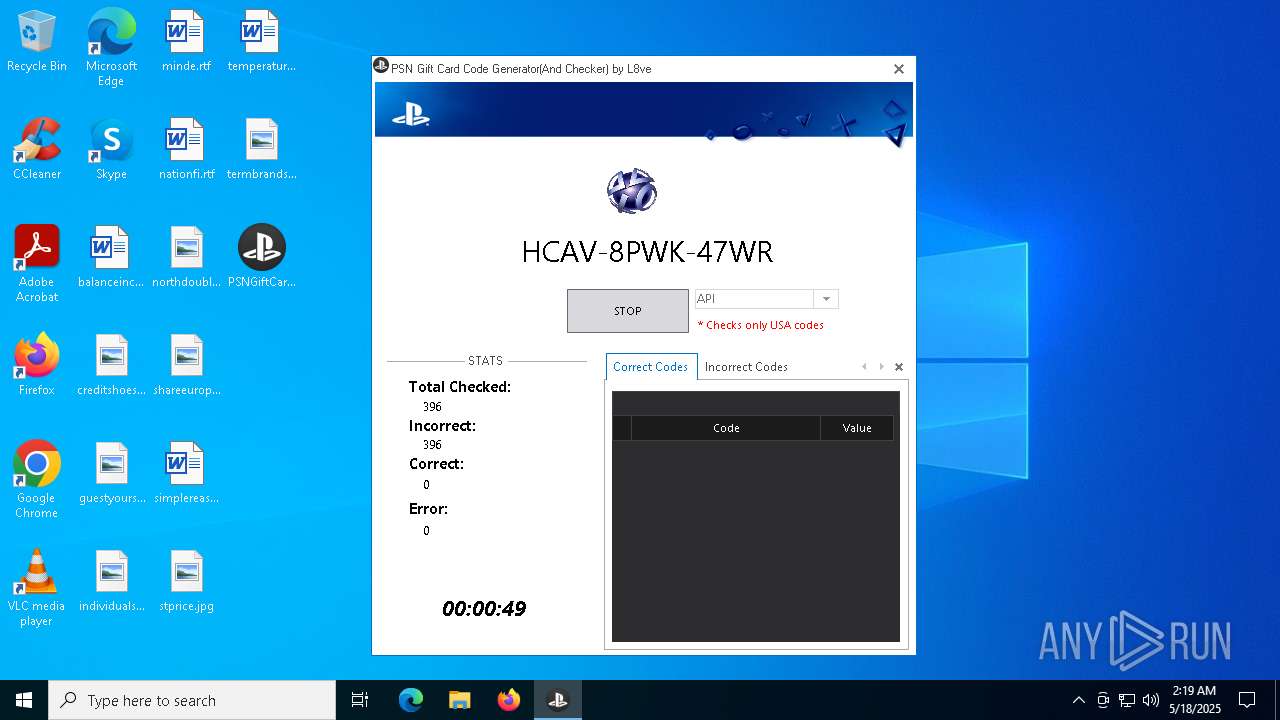
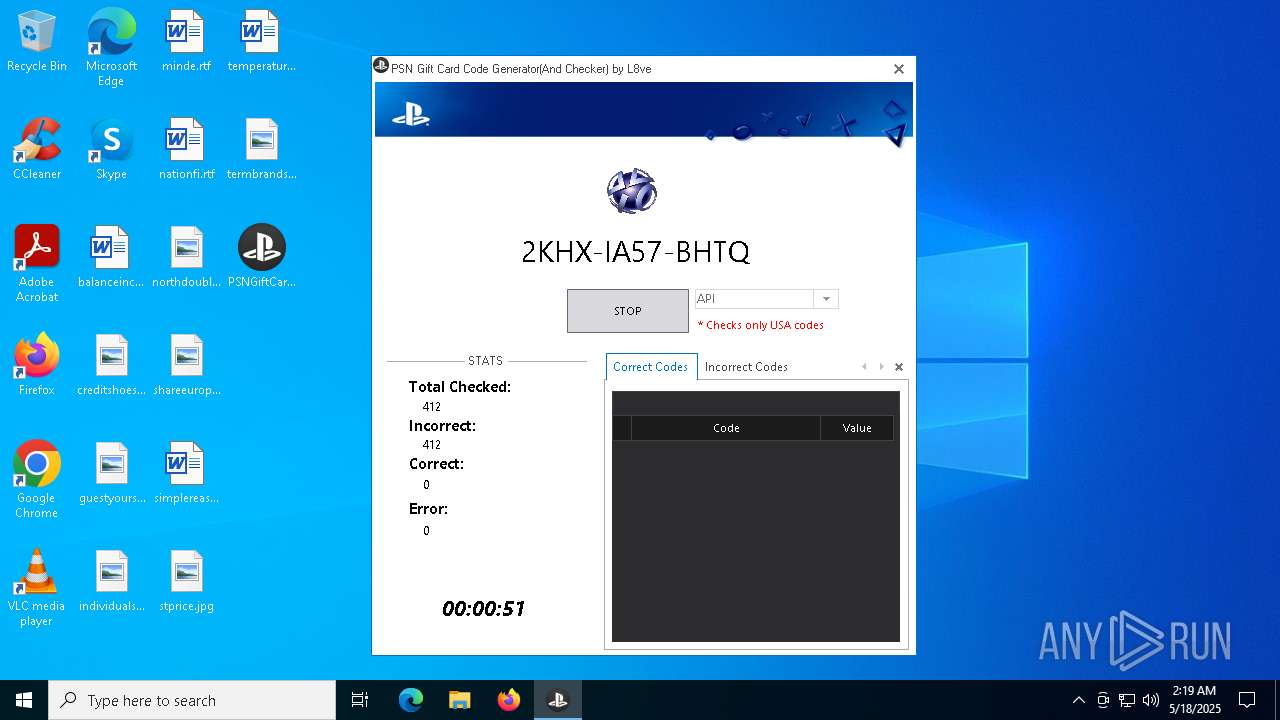
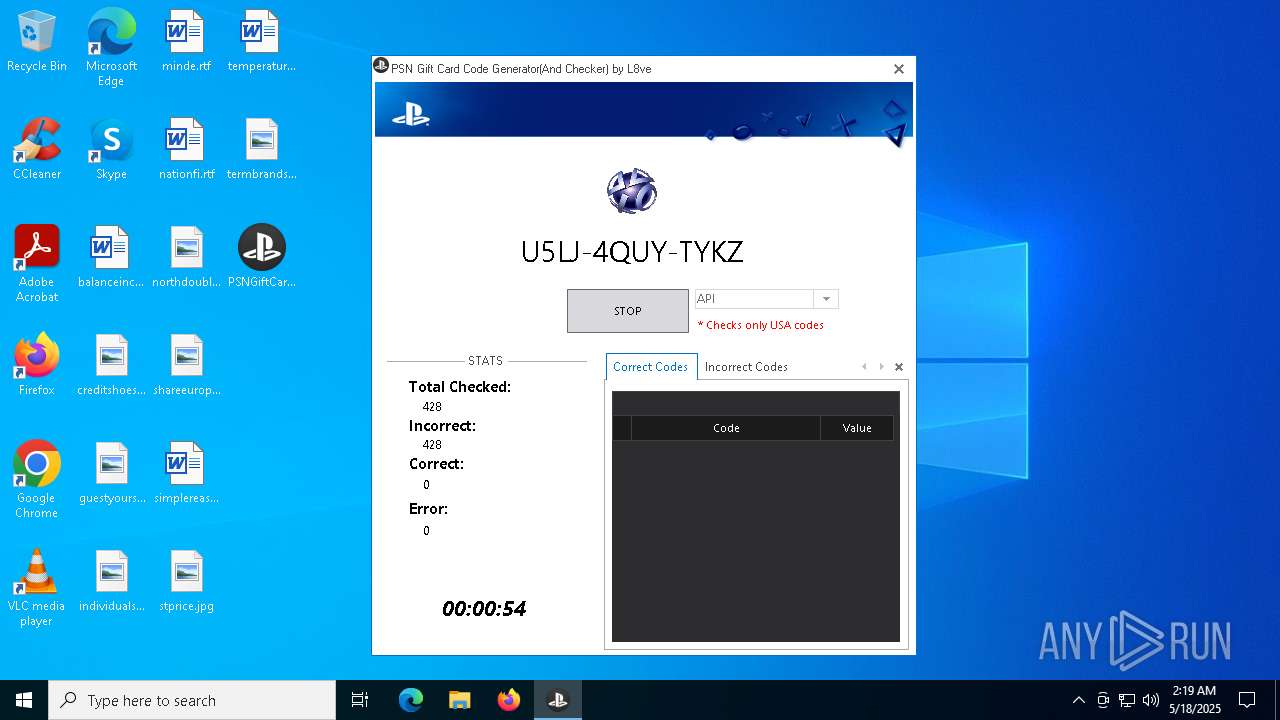
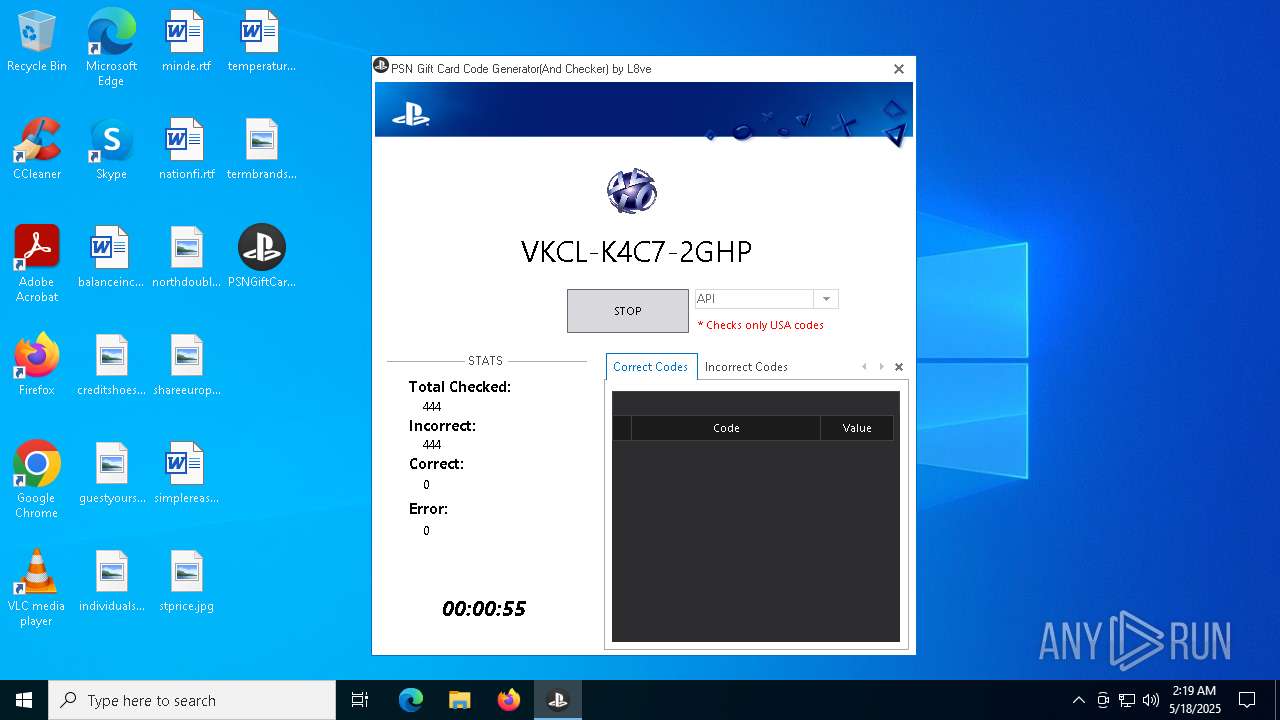
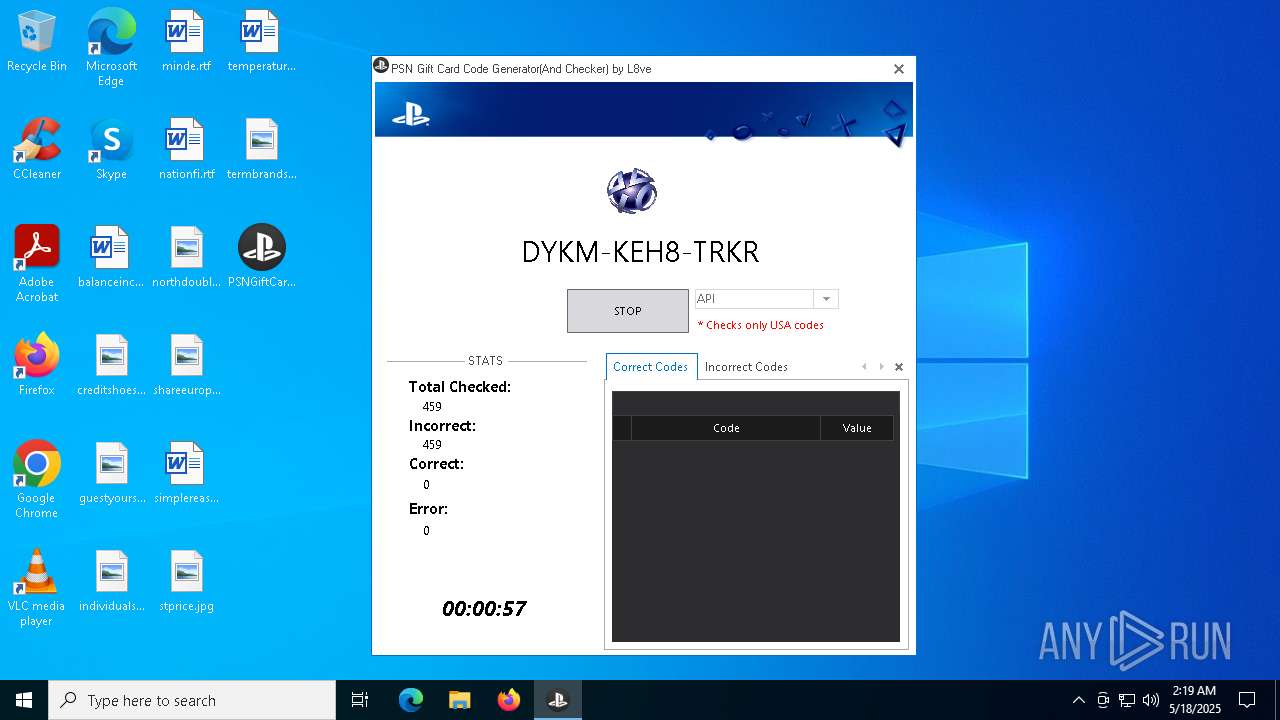
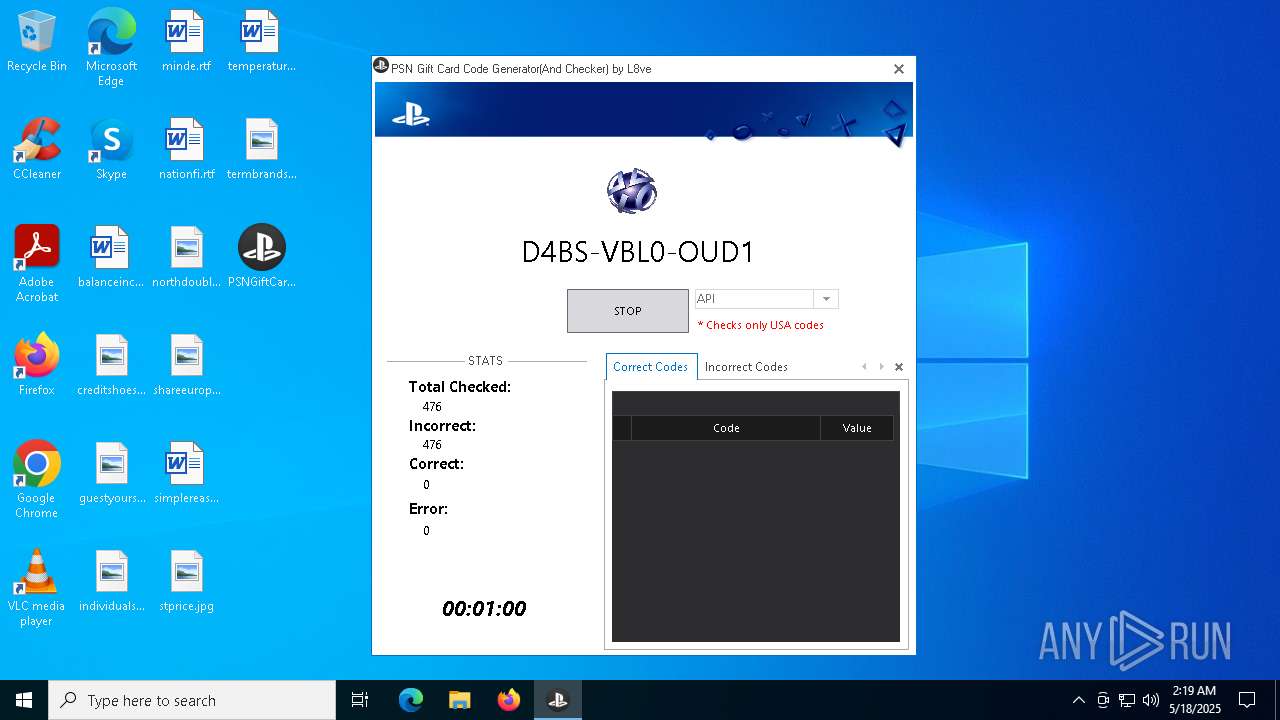
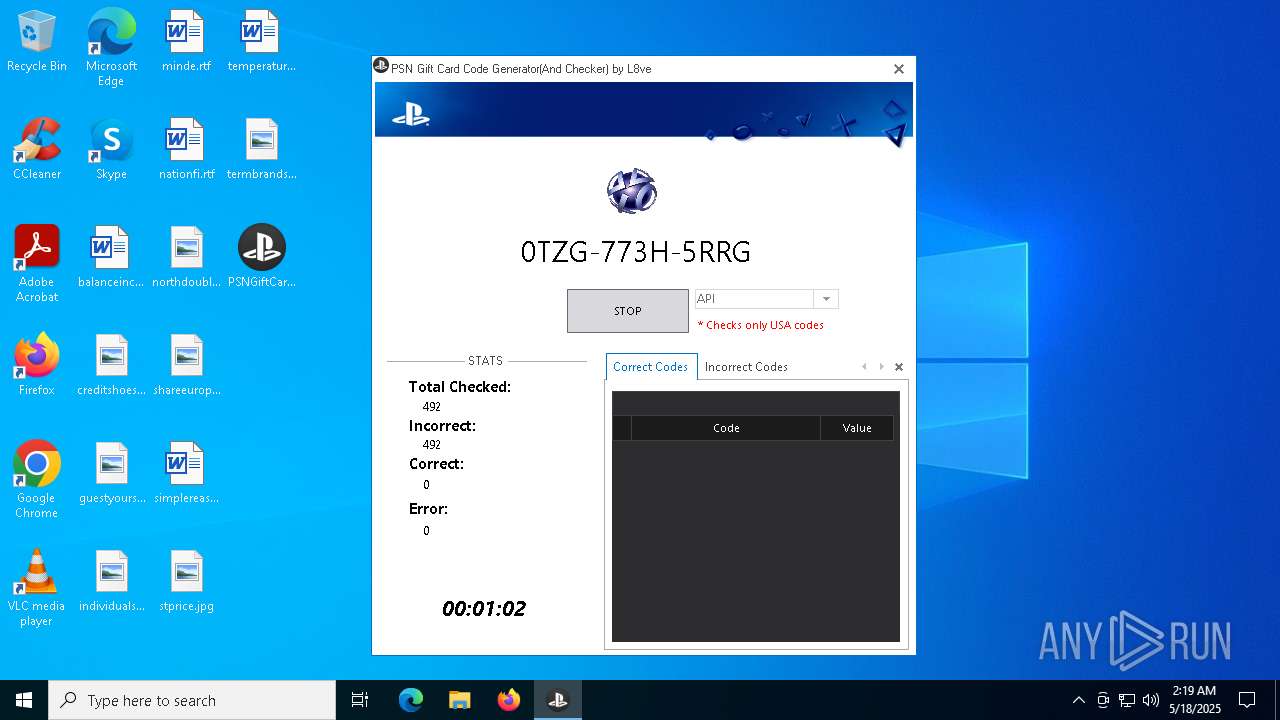
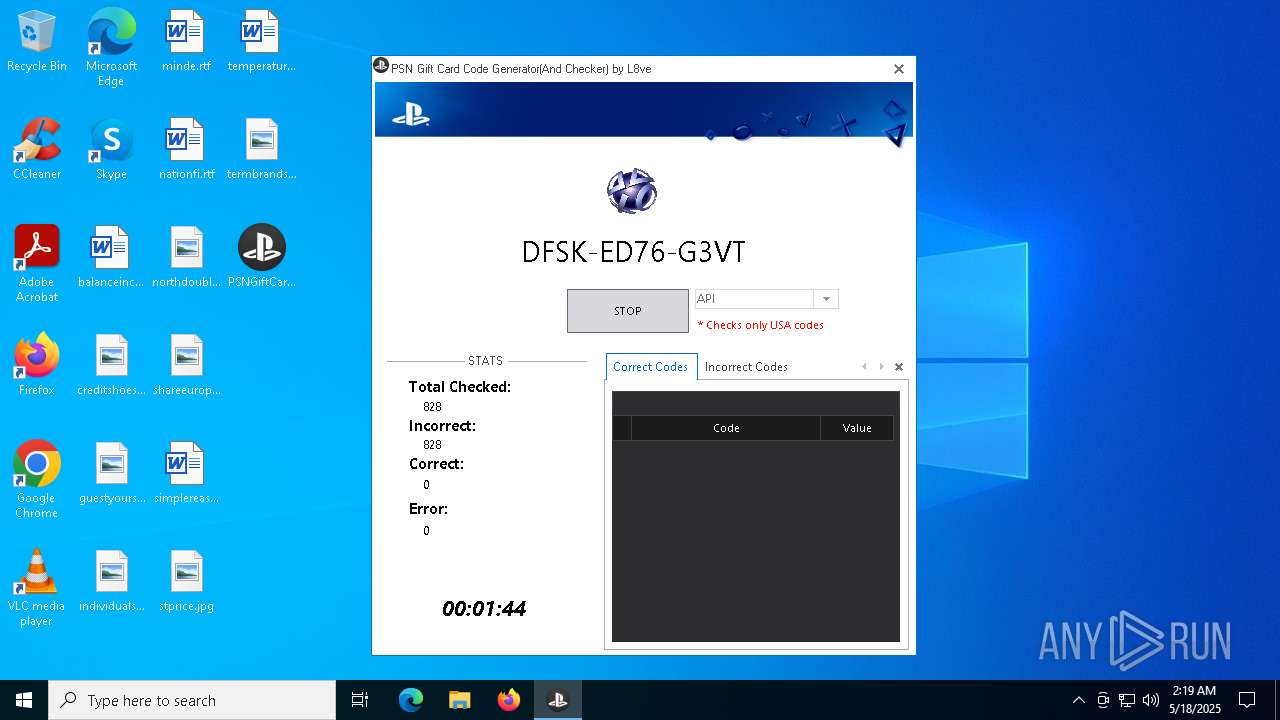
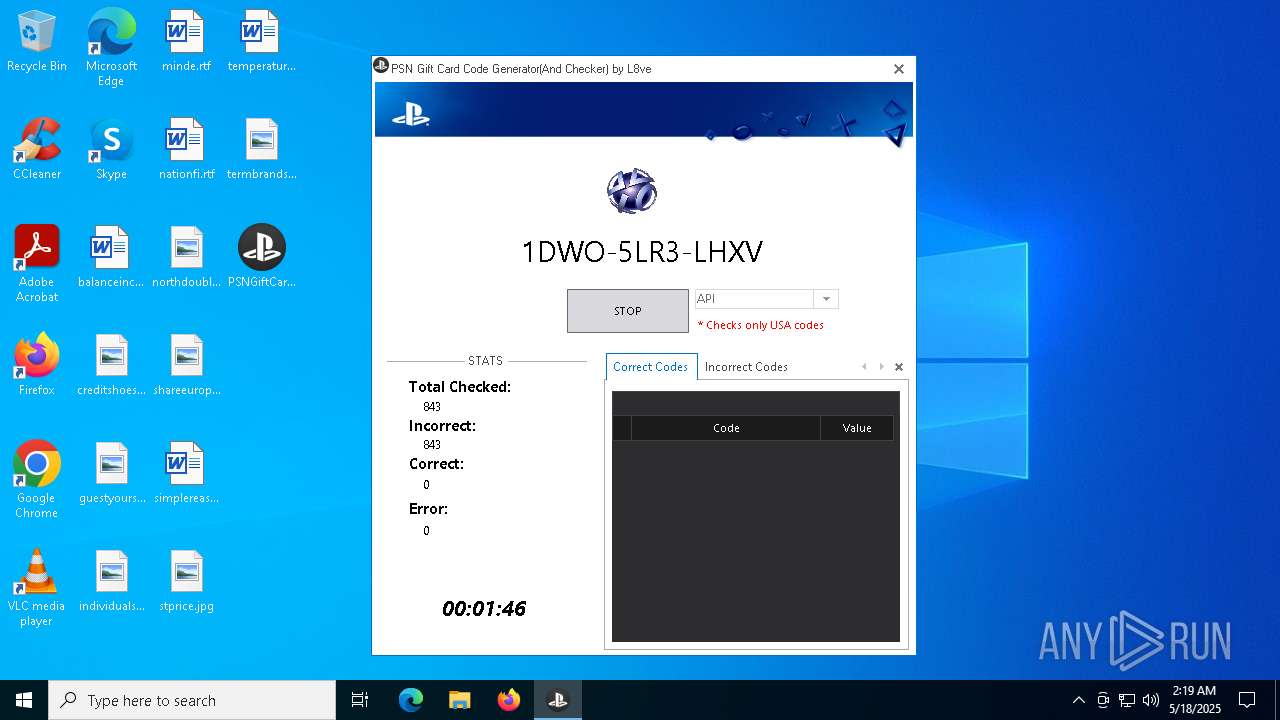
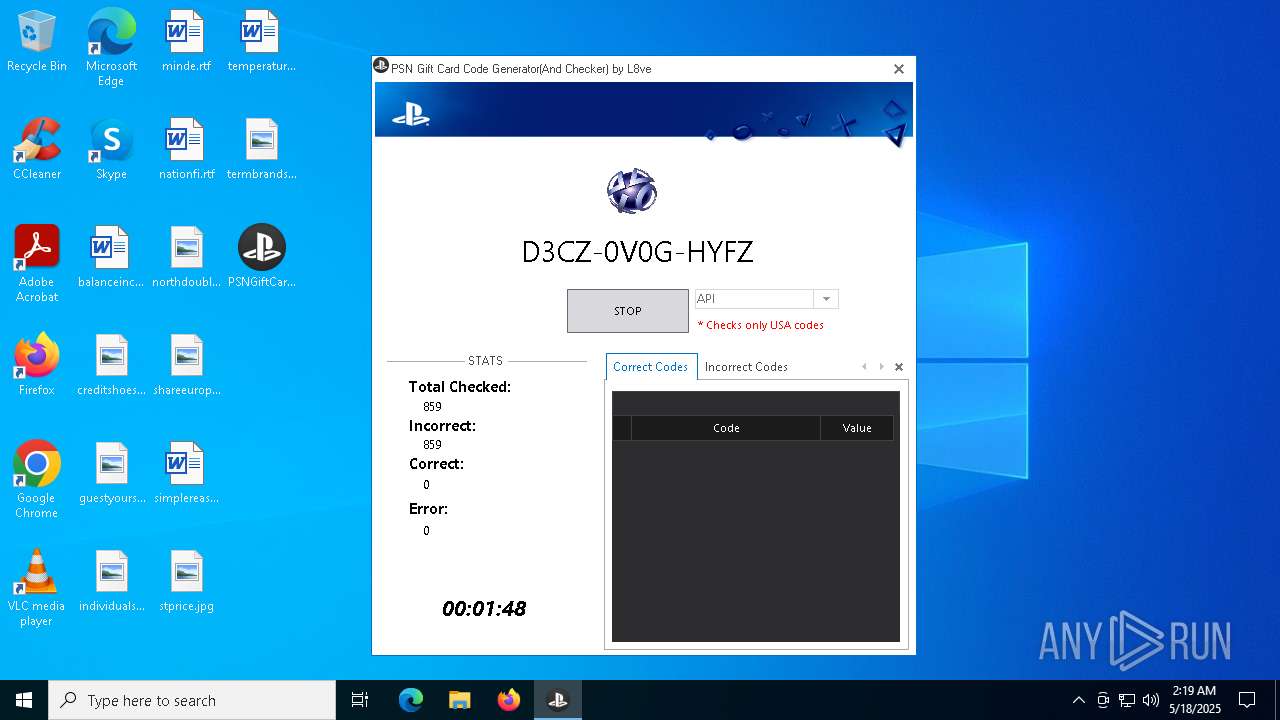
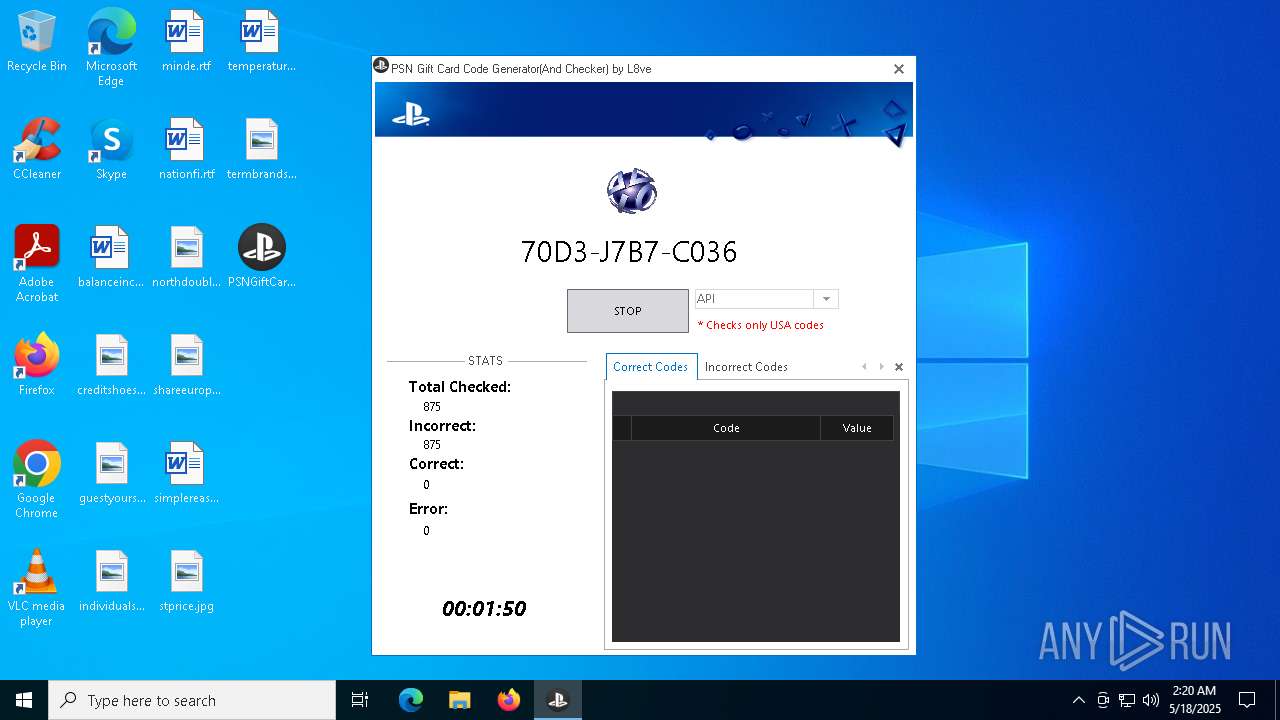
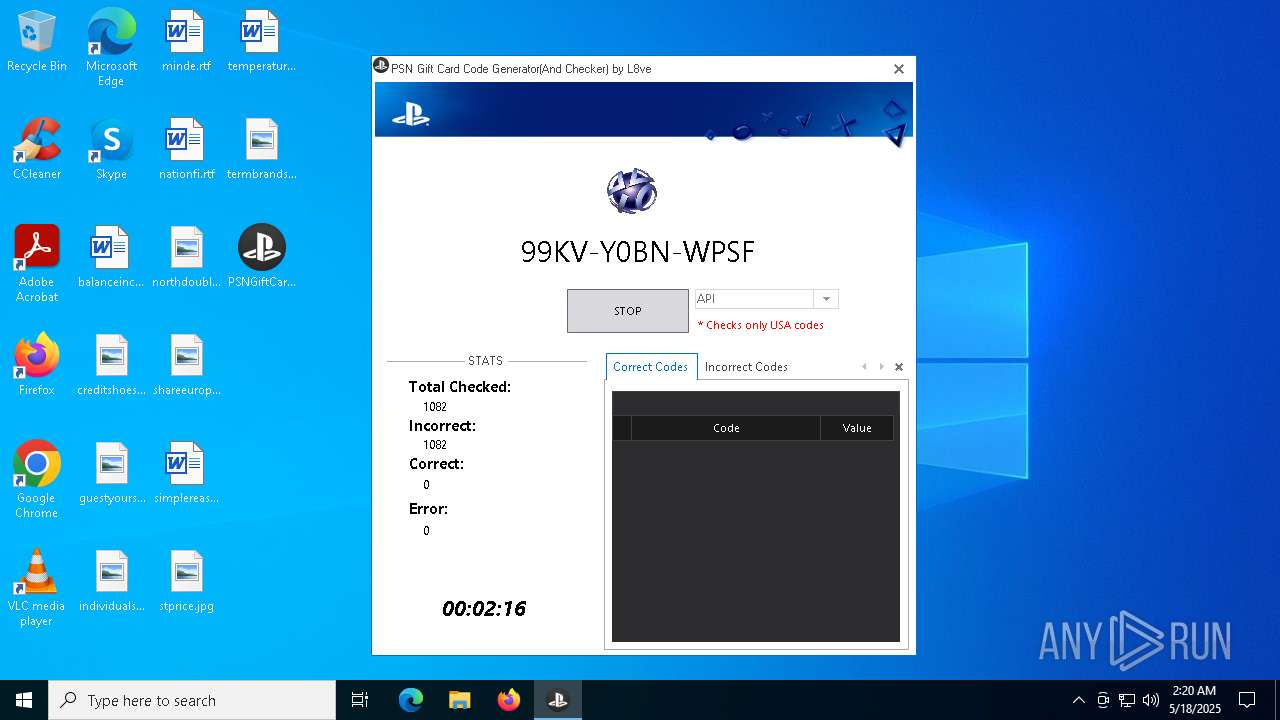
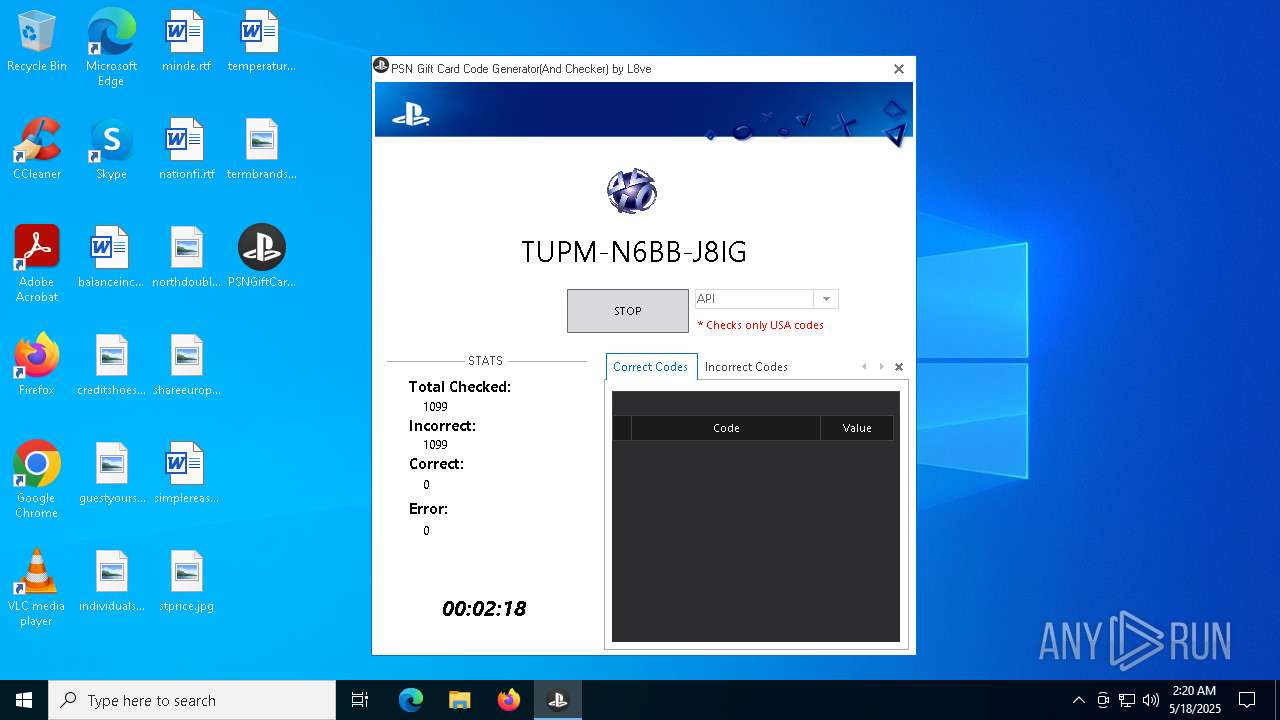
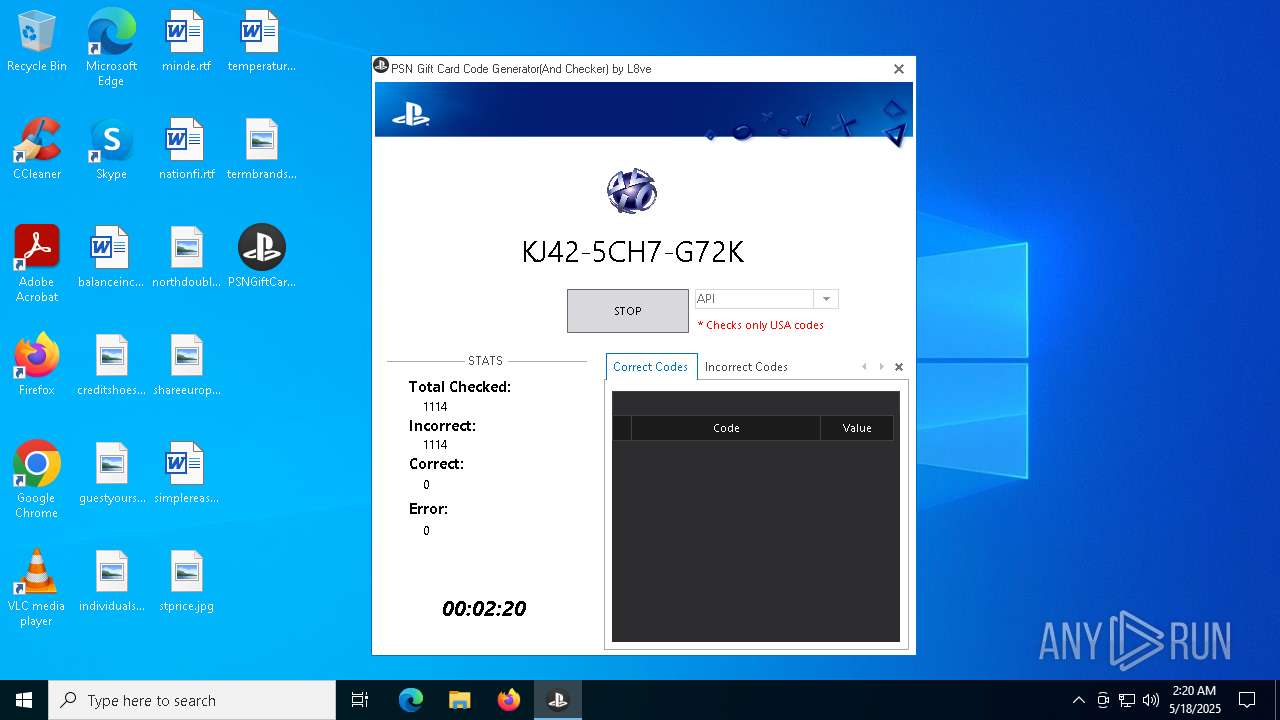
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1164 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1804 | "C:\Users\admin\AppData\Roaming\cvcxxxx.exe" | C:\Users\admin\AppData\Roaming\cvcxxxx.exe | PSNGiftCardCodeGeneratorandCheckerV1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4040 | "C:\Users\admin\Desktop\PSNGiftCardCodeGeneratorandCheckerV1.exe" | C:\Users\admin\Desktop\PSNGiftCardCodeGeneratorandCheckerV1.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: Opwcv Exit code: 0 Version: 6.0.0.0 Modules
| |||||||||||||||
| 4408 | "C:\Users\admin\AppData\Roaming\Launcher.exe" | C:\Users\admin\AppData\Roaming\Launcher.exe | PSNGiftCardCodeGeneratorandCheckerV1.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PSNGiftCardChecker Version: 1.0.0.0 Modules
| |||||||||||||||
| 5204 | C:\Users\admin\AppData\Roaming\2F33566DA0B91573532102\System.exe | C:\Users\admin\AppData\Roaming\2F33566DA0B91573532102\System.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5492 | C:\WINDOWS\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 651
Read events
5 634
Write events
17
Delete events
0
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 5A43296800000000 | |||
| (PID) Process: | (1804) cvcxxxx.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Services |
Value: C:\Users\admin\AppData\Roaming\2F33566DA0B91573532102\System.exe | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\5\ApplicationViewManagement\W32:00000000000302E2 |
| Operation: | write | Name: | VirtualDesktop |
Value: 1000000030304456BFA0DB55E4278845B426357D5B5F97B3 | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (4408) Launcher.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\Launcher_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4040 | PSNGiftCardCodeGeneratorandCheckerV1.exe | C:\Users\admin\AppData\Roaming\Launcher.exe | executable | |
MD5:7333A306F492F5E857F8CF49A546F685 | SHA256:E1E3B904B7B1C1E6DC1E0E630211C9DA4356ECE324567396D358D982C4CF5A8B | |||
| 5492 | explorer.exe | C:\Users\admin\AppData\Local\Microsoft\PenWorkspace\DiscoverCacheData.dat | binary | |
MD5:E49C56350AEDF784BFE00E444B879672 | SHA256:A8BD235303668981563DFB5AAE338CB802817C4060E2C199B7C84901D57B7E1E | |||
| 1804 | cvcxxxx.exe | C:\Users\admin\AppData\Roaming\2F33566DA0B91573532102\System.exe | executable | |
MD5:54A06E27A53DED71F313B12FE186FEDB | SHA256:ED71EF540F741B2A8CA0853A3FB6F77F194D6193D871AB6EDE98BF1850CC917F | |||
| 4040 | PSNGiftCardCodeGeneratorandCheckerV1.exe | C:\Users\admin\AppData\Roaming\cvcxxxx.exe | executable | |
MD5:54A06E27A53DED71F313B12FE186FEDB | SHA256:ED71EF540F741B2A8CA0853A3FB6F77F194D6193D871AB6EDE98BF1850CC917F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1 133
TCP/UDP connections
45
DNS requests
16
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5492 | explorer.exe | POST | 200 | 62.60.226.191:80 | http://62.60.226.191/data.php?2F33566DA0B91573532102 | unknown | — | — | unknown |
5492 | explorer.exe | POST | 200 | 62.60.226.191:80 | http://62.60.226.191/data.php?2F33566DA0B91573532102 | unknown | — | — | unknown |
5492 | explorer.exe | POST | 200 | 62.60.226.191:80 | http://62.60.226.191/data.php?2F33566DA0B91573532102 | unknown | — | — | unknown |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
4408 | Launcher.exe | GET | 204 | 142.250.185.142:80 | http://clients3.google.com/generate_204 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5492 | explorer.exe | 62.60.226.191:80 | — | Iranian Research Organization for Science & Technology | HK | unknown |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4408 | Launcher.exe | 142.250.185.142:80 | clients3.google.com | GOOGLE | US | whitelisted |
2600 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
2600 | SIHClient.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2600 | SIHClient.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2600 | SIHClient.exe | 20.3.187.198:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
clients3.google.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
5492 | explorer.exe | Misc Attack | ET DROP Spamhaus DROP Listed Traffic Inbound group 7 |
4408 | Launcher.exe | Generic Protocol Command Decode | SURICATA HTTP too many warnings |
4408 | Launcher.exe | Generic Protocol Command Decode | SURICATA HTTP too many warnings |