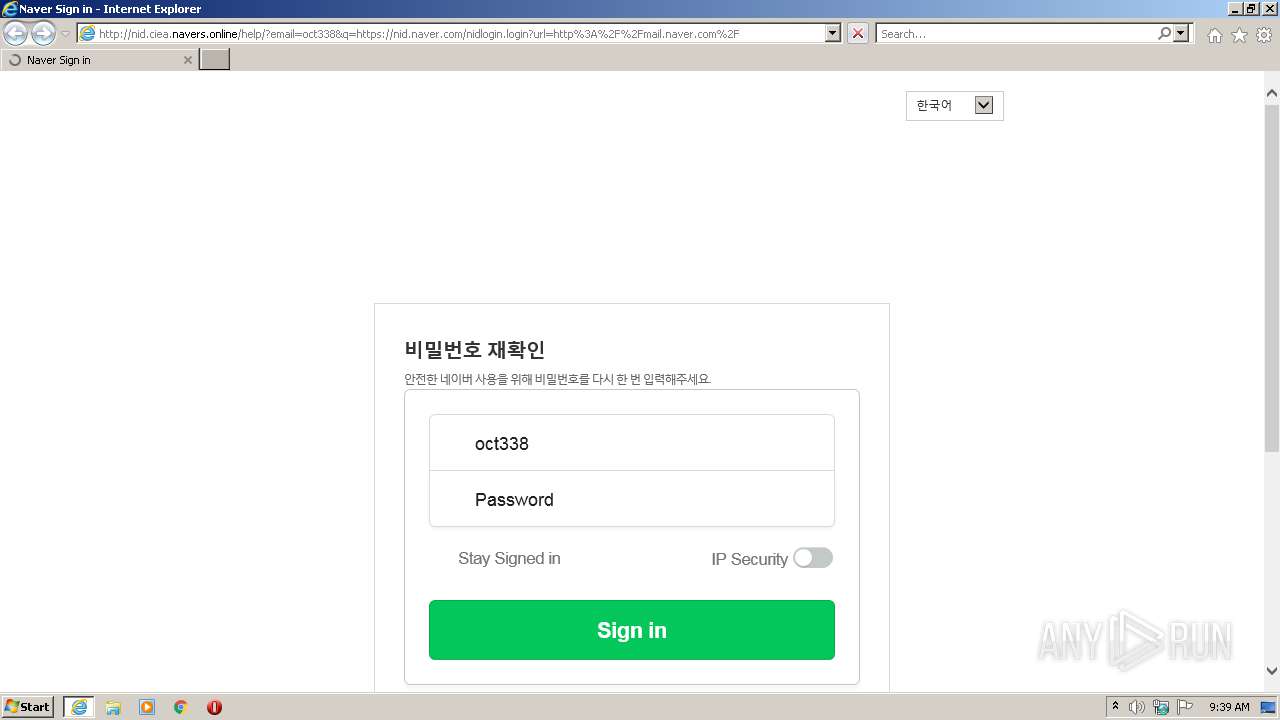
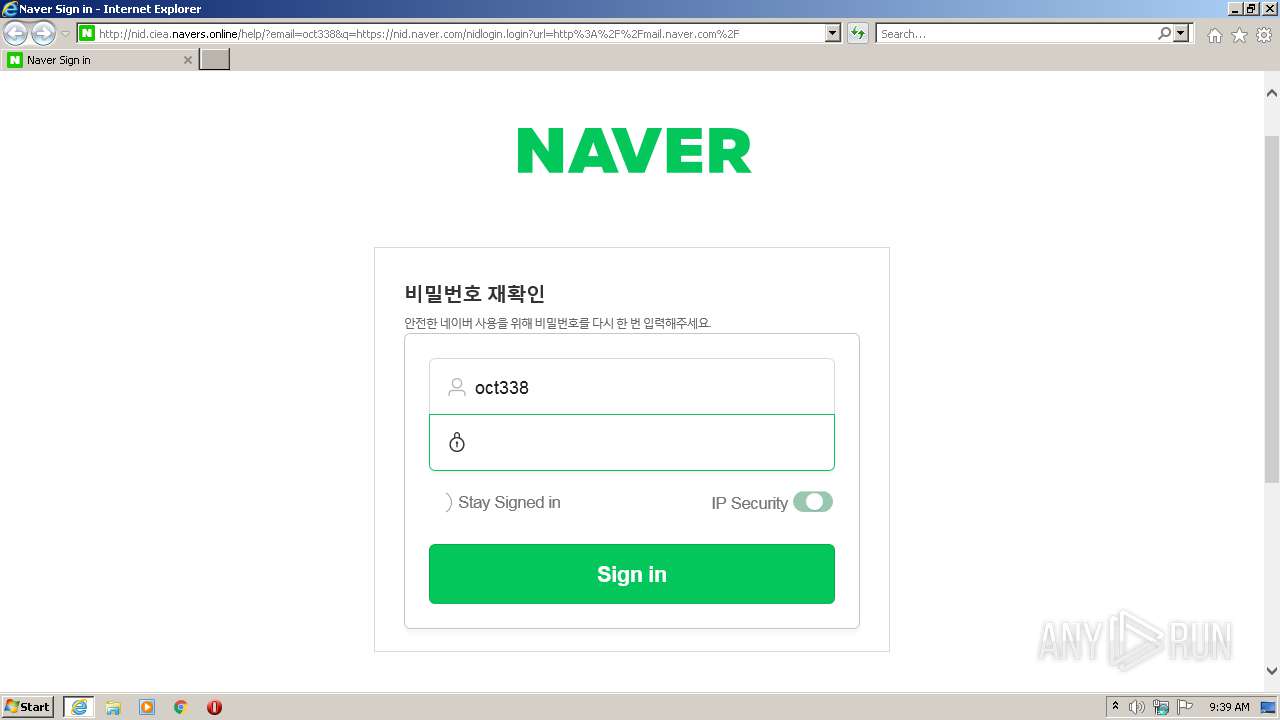
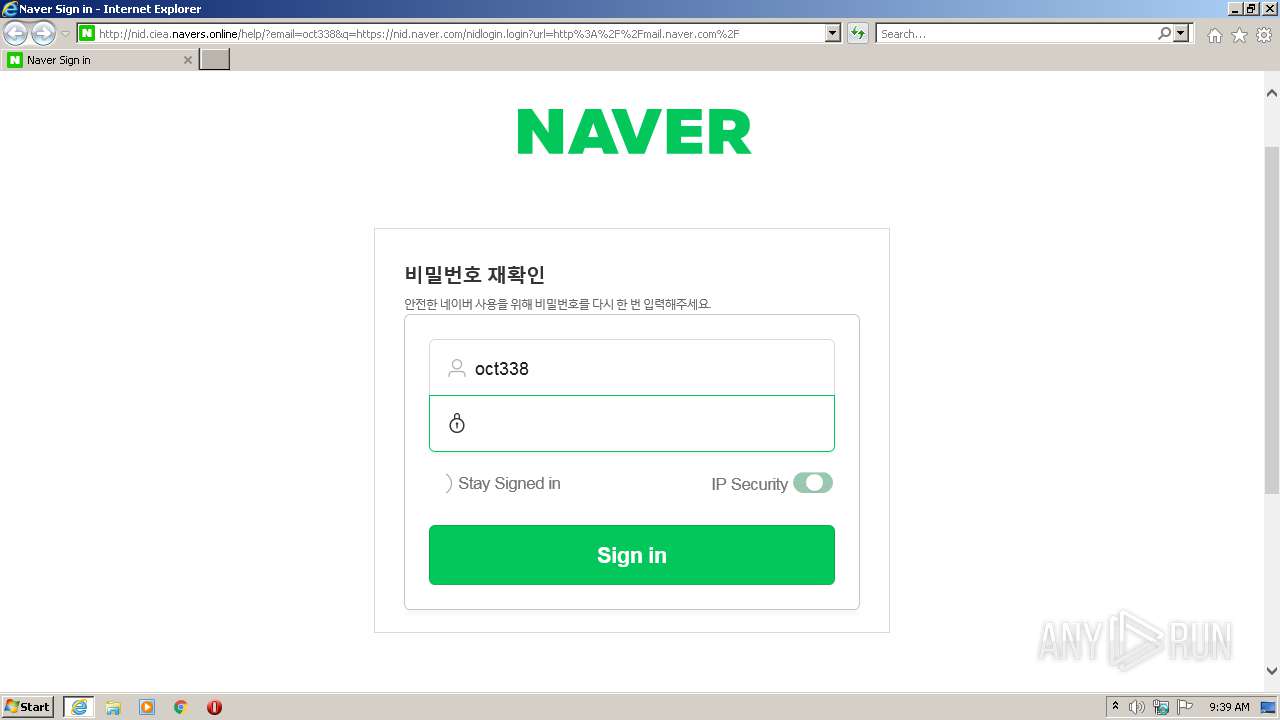
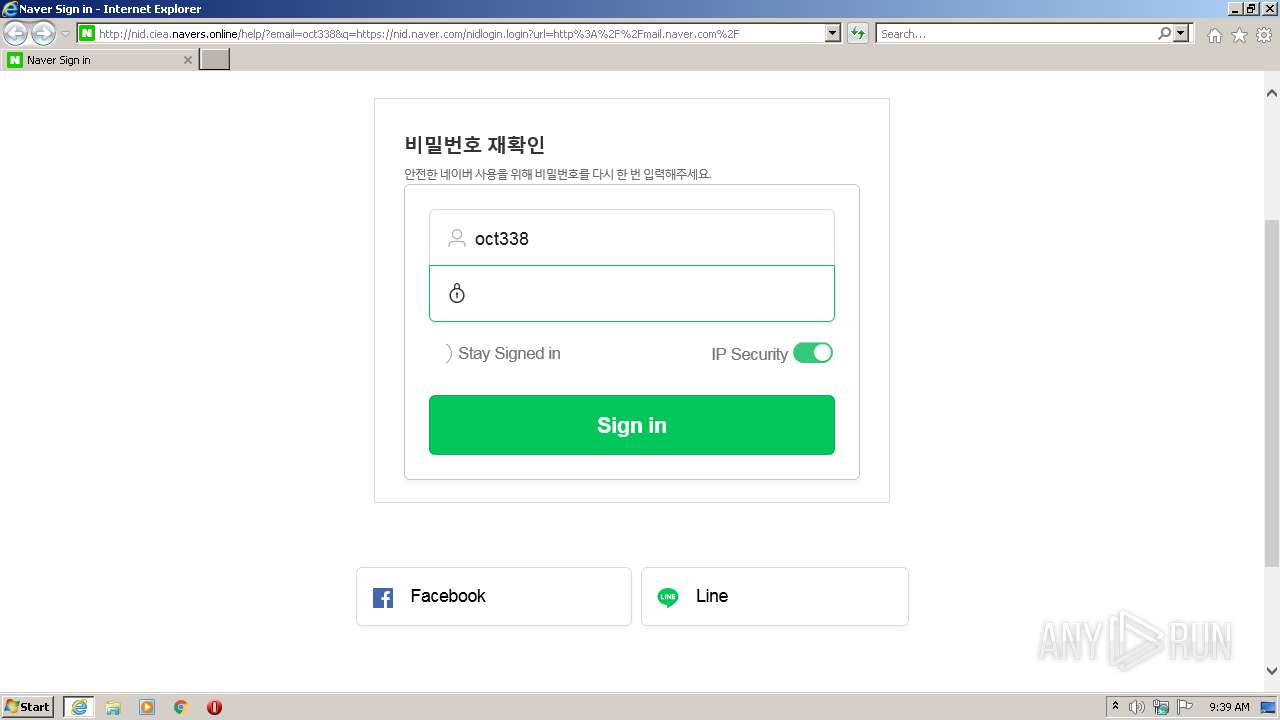
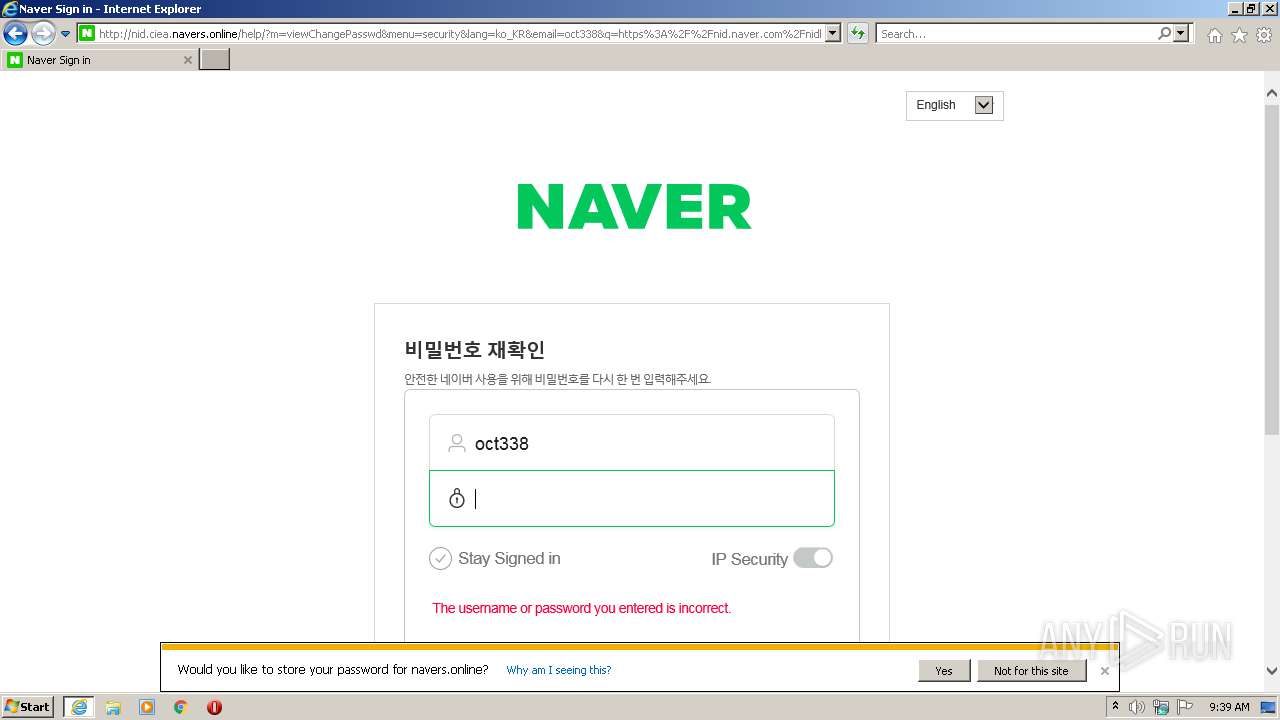
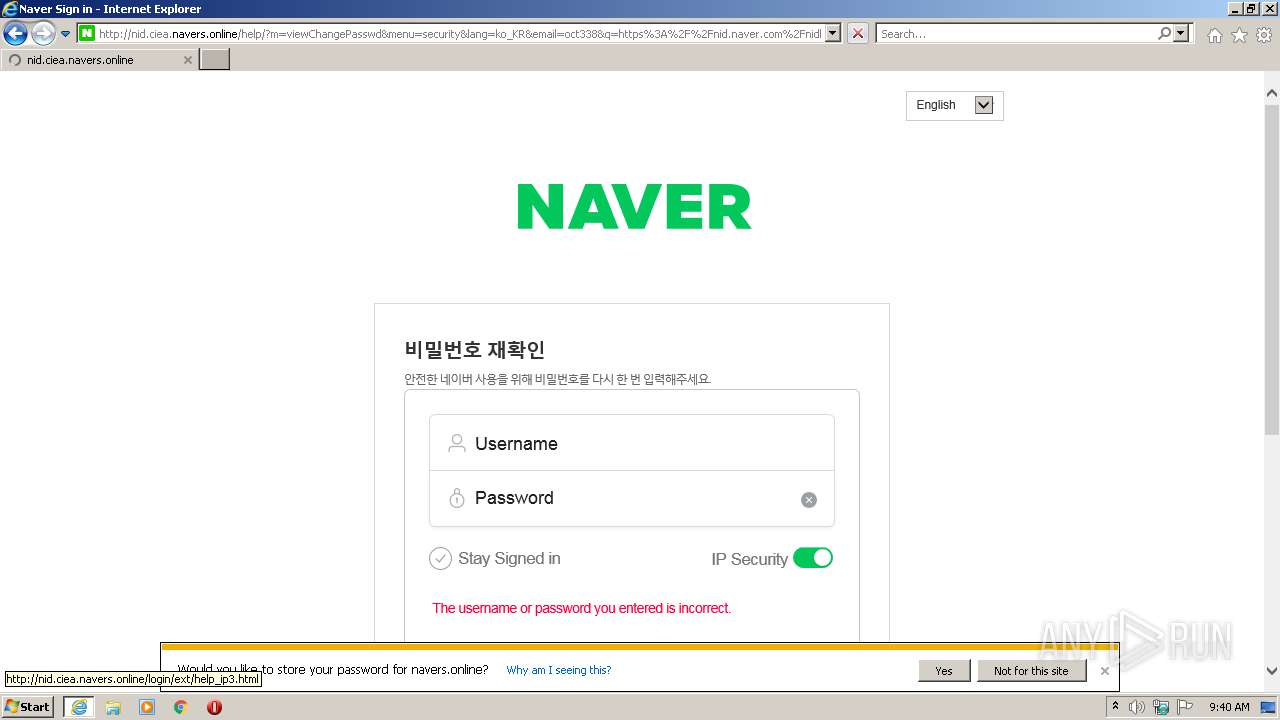
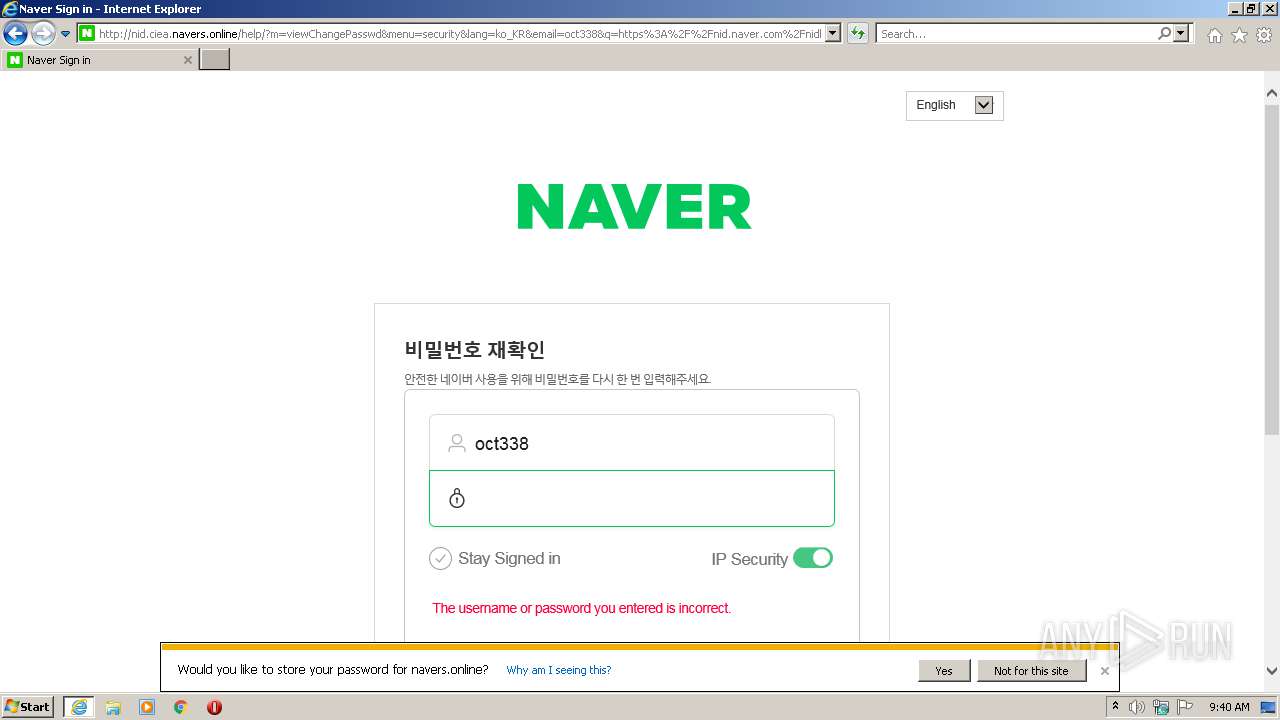
| URL: | http://nid.ciea.navers.online/help/?email=oct338&q=https://nid.naver.com/nidlogin.login?url=http%3A%2F%2Fmail.naver.com%2F |
| Full analysis: | https://app.any.run/tasks/3daca0df-3346-414a-b319-9efe60b6c590 |
| Verdict: | Malicious activity |
| Analysis date: | October 08, 2021, 08:39:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 5AC56385AA5A53207A8AEDBBB00A289C |
| SHA1: | 368EF2987E9A8406C16D51DCF33649FD9B655DB1 |
| SHA256: | 2C82C4B5462F599CC41366F5FE0AFF3F77C78348508B9813F6E5448BEA4AD061 |
| SSDEEP: | 3:N1KQAfh/EMG0IAHb2ITnGwWf0DAm/EC72hVzJsXjSJSy2w:CQYMR0Iqb2ITGD0cm/EvHszSYw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Checks supported languages
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3400)
Reads the computer name
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3400)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 880)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3400)
Creates files in the user directory
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3400)
INFO
Checks supported languages
- iexplore.exe (PID: 2832)
- iexplore.exe (PID: 880)
Reads the computer name
- iexplore.exe (PID: 880)
- iexplore.exe (PID: 2832)
Reads settings of System Certificates
- iexplore.exe (PID: 880)
- iexplore.exe (PID: 2832)
Application launched itself
- iexplore.exe (PID: 2832)
Changes internet zones settings
- iexplore.exe (PID: 2832)
Reads CPU info
- iexplore.exe (PID: 880)
Checks Windows Trust Settings
- iexplore.exe (PID: 880)
- iexplore.exe (PID: 2832)
Reads internet explorer settings
- iexplore.exe (PID: 880)
Creates files in the user directory
- iexplore.exe (PID: 880)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
38
Monitored processes
3
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 880 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2832 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2832 | "C:\Program Files\Internet Explorer\iexplore.exe" "http://nid.ciea.navers.online/help/?email=oct338&q=https://nid.naver.com/nidlogin.login?url=http%3A%2F%2Fmail.naver.com%2F" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3400 | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe -Embedding | C:\Windows\system32\Macromed\Flash\FlashUtil32_32_0_0_453_ActiveX.exe | — | svchost.exe | |||||||||||
User: admin Company: Adobe Integrity Level: MEDIUM Description: Adobe� Flash� Player Installer/Uninstaller 32.0 r0 Exit code: 0 Version: 32,0,0,453 Modules
| |||||||||||||||
Total events
12 221
Read events
12 003
Write events
216
Delete events
2
Modification events
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 166275664 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30915616 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 466435351 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30915616 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2832) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
9
Text files
24
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\nidlogin[1].login | html | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | der | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | der | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\50CD3D75D026C82E2E718570BD6F44D0_10B2AA60724E74F27654C4D713F9F202 | binary | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\bvsd.1.3.4.min[1].js | text | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_9487BC0D4381A7CDEB9A8CC43F66D27C | binary | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\nidlogin[1].htm | html | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B398B80134F72209547439DB21AB308D_ADE4E4D3A3BCBCA5C39C54D362D88565 | binary | |
MD5:— | SHA256:— | |||
| 880 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\50CD3D75D026C82E2E718570BD6F44D0_10B2AA60724E74F27654C4D713F9F202 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
25
TCP/UDP connections
34
DNS requests
13
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2832 | iexplore.exe | GET | 304 | 23.32.238.178:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?04f21a29b7923f0c | US | — | — | whitelisted |
880 | iexplore.exe | GET | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?email=oct338&q=https://nid.naver.com/nidlogin.login?url=http%3A%2F%2Fmail.naver.com%2F | US | html | 12.2 Kb | suspicious |
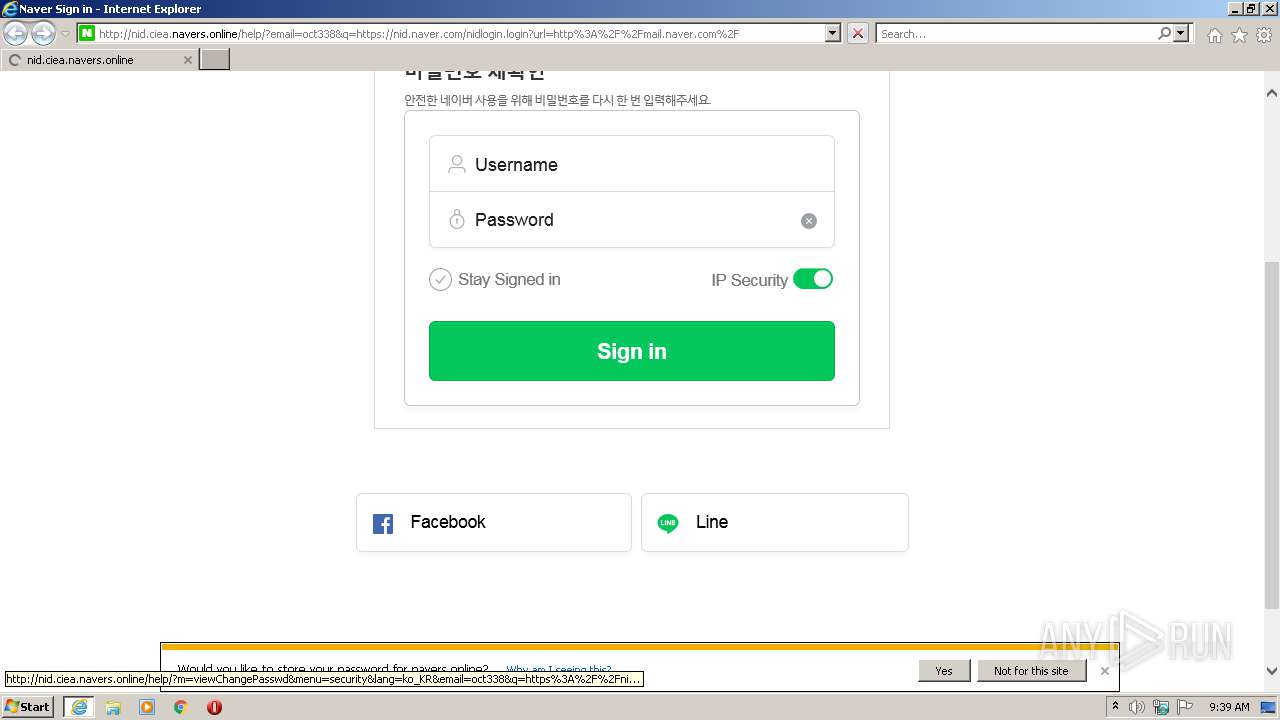
880 | iexplore.exe | GET | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?m=viewChangePasswd&menu=security&lang=ko_KR&email=oct338&q=https%3A%2F%2Fnid.naver.com%2Flogin%2Fjs%2Fbvsd.1.3.4.min.js | US | text | 93.9 Kb | suspicious |
880 | iexplore.exe | GET | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?m=viewChangePasswd&menu=security&lang=ko_KR&email=oct338&q=https%3A%2F%2Fnid.naver.com%2F%2Flogin%2Fjs%2Fv2%2Fdefault%2Fcommon_202105.js%3Fv%3D20210813 | US | text | 91.4 Kb | suspicious |
880 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAVG%2Fhgj9%2BGUHaOfzhTEYXM%3D | US | der | 471 b | whitelisted |
880 | iexplore.exe | GET | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?m=viewChangePasswd&menu=security&lang=ko_KR&email=oct338&q=https%3A%2F%2Fnid.naver.com%2FdynamicKey%2FzDHHQMrYhlxBIGN3TkBFPb8s9E68fxFg9CcgMAb5PhaX3Gkaj7Y1utmUWPbMAUjDWX8mwn2jfm73xIsoU3b8RacE2a9yMQJMkMKINqhoOZY | US | text | 306 b | suspicious |
2832 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://crl3.digicert.com/Omniroot2025.crl | US | der | 7.68 Kb | whitelisted |
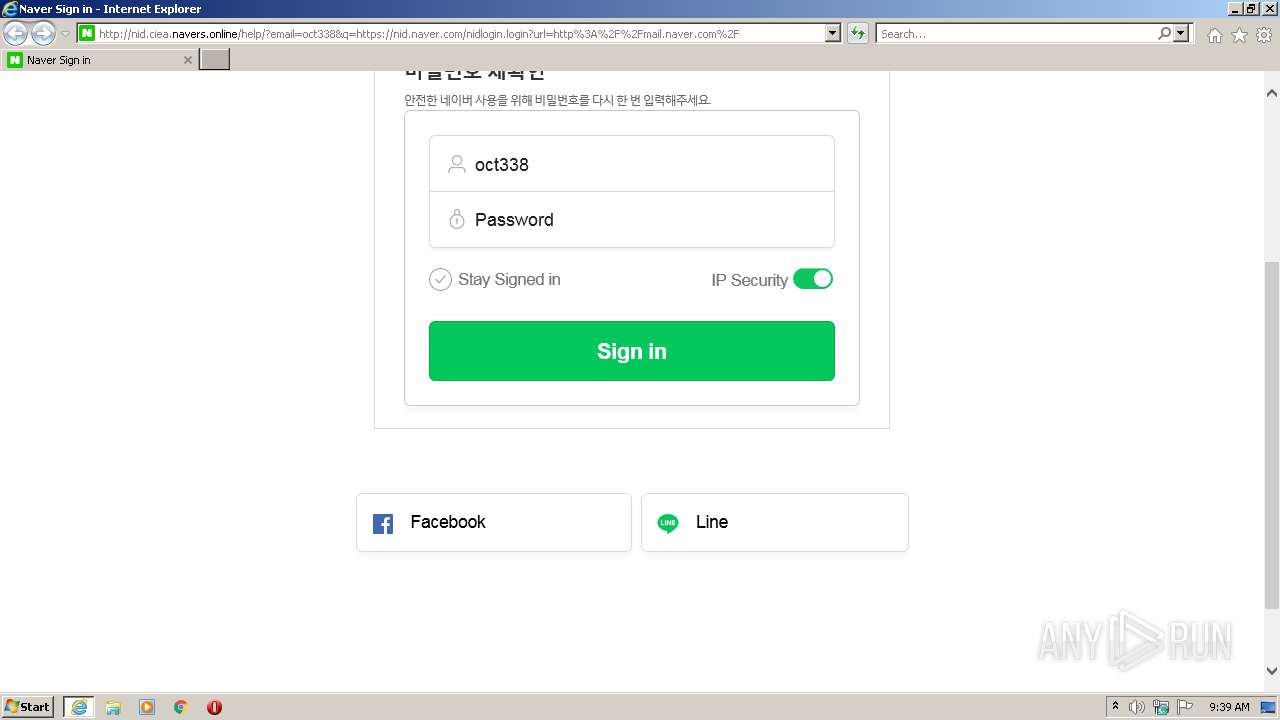
880 | iexplore.exe | POST | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?m=viewChangePasswd&menu=security&lang=ko_KR&email=oct338&q=https%3A%2F%2Fnid.naver.com%2Fnidlogin.login | US | html | 12.3 Kb | suspicious |
880 | iexplore.exe | GET | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?m=viewChangePasswd&menu=security&lang=ko_KR&email=oct338&q=https%3A%2F%2Fnid.naver.com%2FdynamicKey%2FKSk1MP-kwNYaONdRiOLDGNLVlqiYasVxktah4c3FHZqeNEYup7kJ9_8HoJhxYTDFqmwKZjS194js1KQy0DWMNn6tFcEYhrJDiL4wswaWfMs | US | text | 306 b | suspicious |
880 | iexplore.exe | POST | 200 | 141.164.48.103:80 | http://nid.ciea.navers.online/help/?m=viewChangePasswd&menu=security&lang=ko_KR&email=oct338&q=https%3A%2F%2Fnid.naver.com%2Fnidlogin.login | US | html | 12.3 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
880 | iexplore.exe | 203.104.163.42:443 | nid.naver.com | NBP | KR | unknown |
880 | iexplore.exe | 141.164.48.103:80 | nid.ciea.navers.online | Loyola University New Orleans | US | suspicious |
— | — | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
880 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
880 | iexplore.exe | 184.30.24.182:443 | ssl.pstatic.net | GTT Communications Inc. | US | unknown |
2832 | iexplore.exe | 141.164.48.103:80 | nid.ciea.navers.online | Loyola University New Orleans | US | suspicious |
880 | iexplore.exe | 203.104.163.21:80 | lcs.naver.com | NBP | KR | unknown |
2832 | iexplore.exe | 23.32.238.178:80 | ctldl.windowsupdate.com | XO Communications | US | suspicious |
880 | iexplore.exe | 203.104.163.20:80 | cc.naver.com | NBP | KR | suspicious |
— | — | 203.104.163.20:80 | cc.naver.com | NBP | KR | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nid.ciea.navers.online |
| suspicious |
nid.naver.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ssl.pstatic.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
lcs.naver.com |
| whitelisted |
cc.naver.com |
| whitelisted |
crl3.digicert.com |
| whitelisted |
Threats
9 ETPRO signatures available at the full report