| File name: | KMS_VL_ALL_AIO.txt |
| Full analysis: | https://app.any.run/tasks/eb916403-0bae-4a11-85ce-b1f0902bb794 |
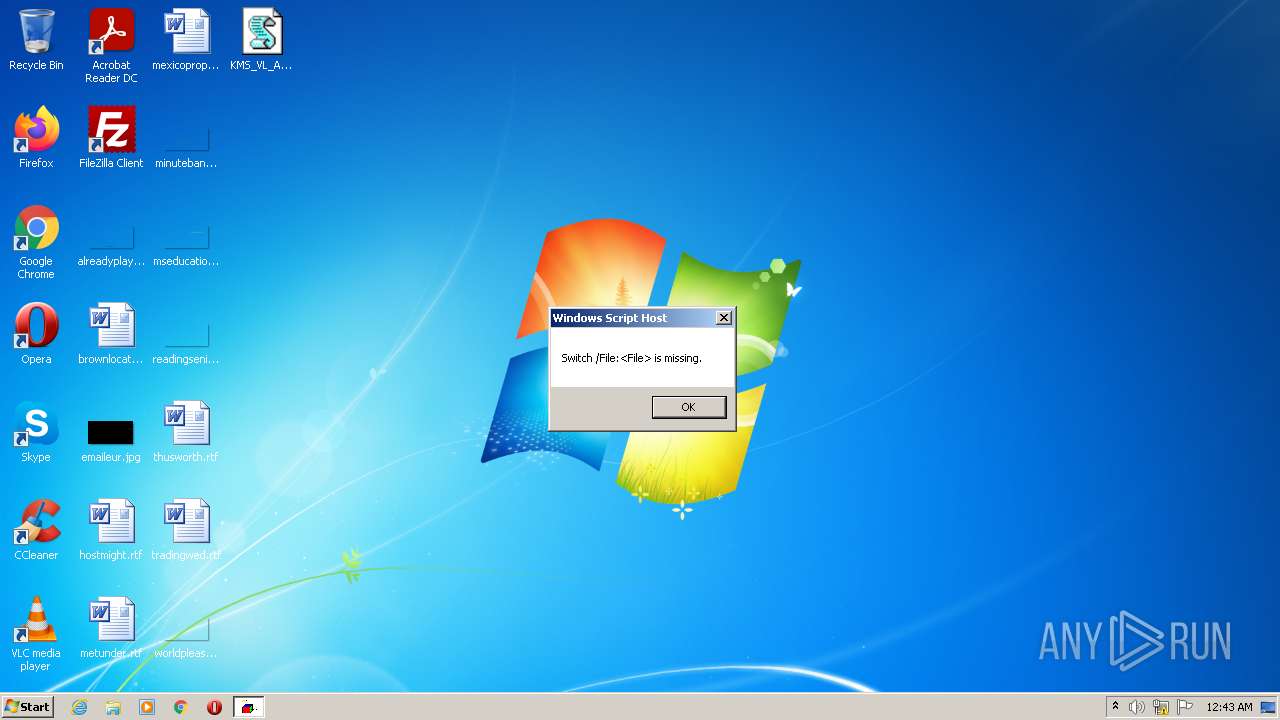
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2022, 00:43:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | exported SGML document, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | A69574ADE11A89DC1D964049794E4FC9 |
| SHA1: | 80D43762FE7F799CB095DF5F71ADB39967EC8DB3 |
| SHA256: | 2C6145223B87F84CFF2A3C375CAE1B0371D2F5CC60FF83811430AA4517612477 |
| SSDEEP: | 6144:uJKJ/nu6Syp0z/GnkSzM4fKn5pw9rIjEUqbj8HmAkzvlv:uJKJ/BSyp00M4yn5pmUjE/j8GAk7lv |
MALICIOUS
Starts Visual C# compiler
- powershell.exe (PID: 1668)
Drops the executable file immediately after the start
- csc.exe (PID: 2248)
- powershell.exe (PID: 1668)
Creates a writable file the system directory
- powershell.exe (PID: 1668)
Loads dropped or rewritten executable
- sppsvc.exe (PID: 780)
- OSPPSVC.EXE (PID: 3724)
Loads the Task Scheduler COM API
- sppsvc.exe (PID: 780)
- OSPPSVC.EXE (PID: 3724)
Starts NET.EXE for service management
- cmd.exe (PID: 2340)
SUSPICIOUS
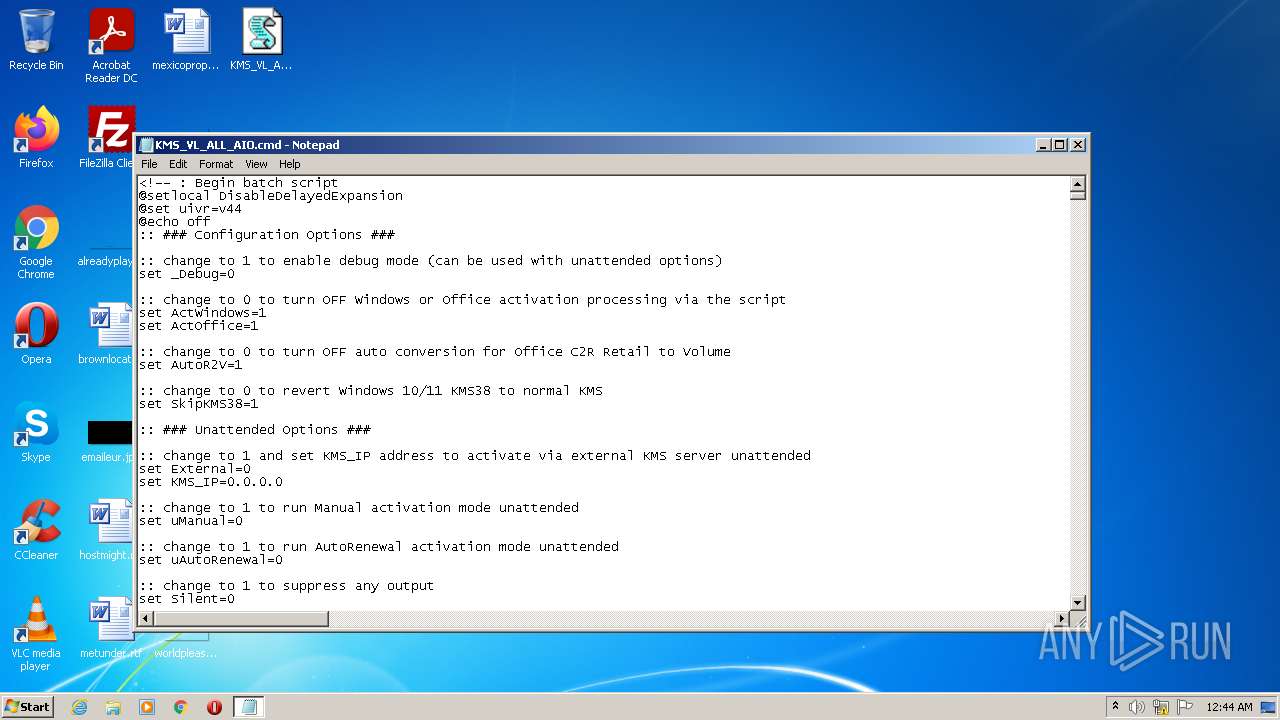
Executes scripts
- cmd.exe (PID: 2840)
Starts CMD.EXE for commands execution
- cscript.exe (PID: 1228)
- cmd.exe (PID: 2340)
Application launched itself
- cmd.exe (PID: 2340)
Executable content was dropped or overwritten
- csc.exe (PID: 2248)
- powershell.exe (PID: 1668)
Starts SC.EXE for service management
- cmd.exe (PID: 2340)
Executes PowerShell scripts
- cmd.exe (PID: 2340)
Starts CHOICE.EXE to create a delay
- cmd.exe (PID: 2340)
Creates files in the Windows directory
- powershell.exe (PID: 1668)
Drops a file with too old compile date
- powershell.exe (PID: 1668)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 2340)
Uses WMIC.EXE to obtain a system information
- cmd.exe (PID: 2340)
- cmd.exe (PID: 1436)
- cmd.exe (PID: 836)
- cmd.exe (PID: 2088)
Removes files from Windows the directory
- cmd.exe (PID: 2340)
INFO
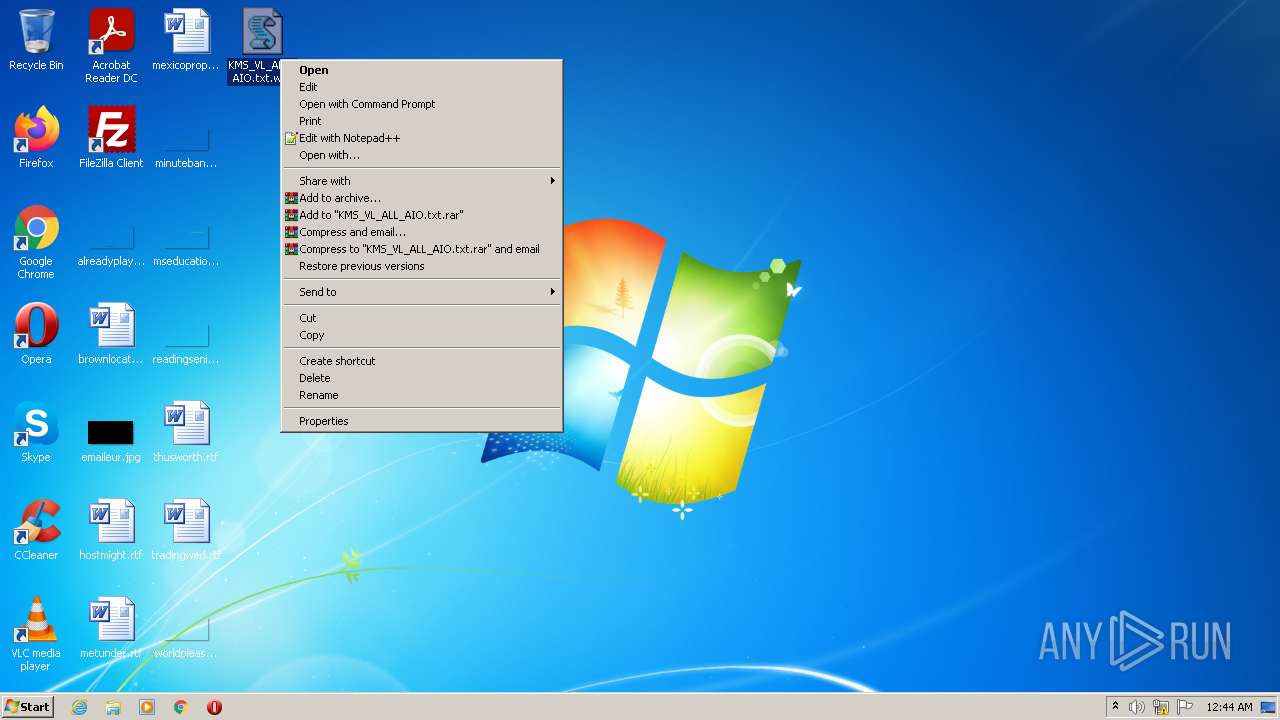
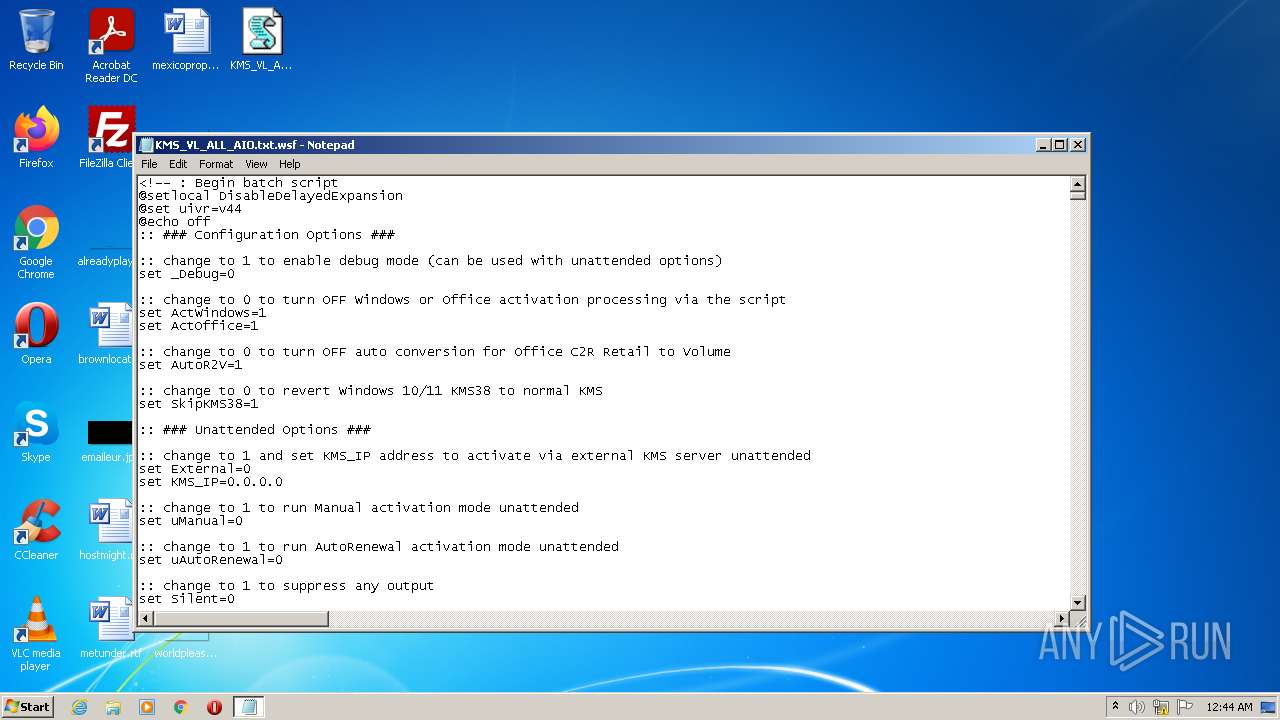
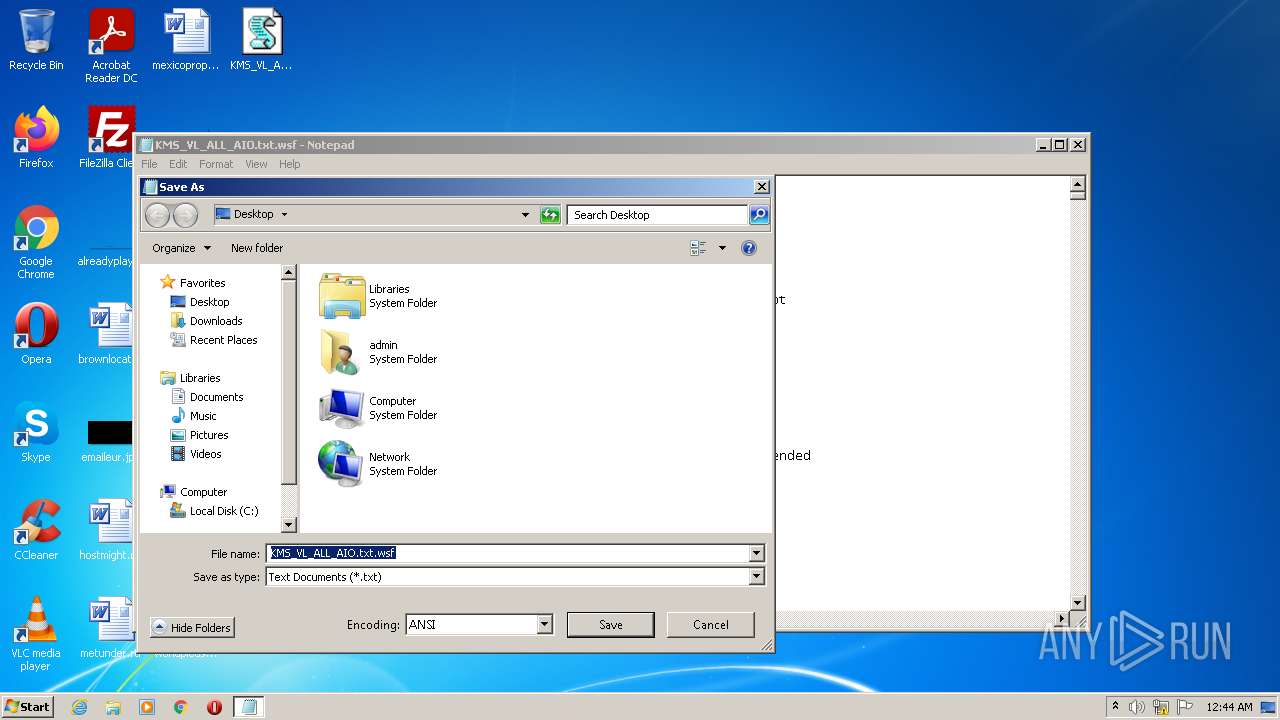
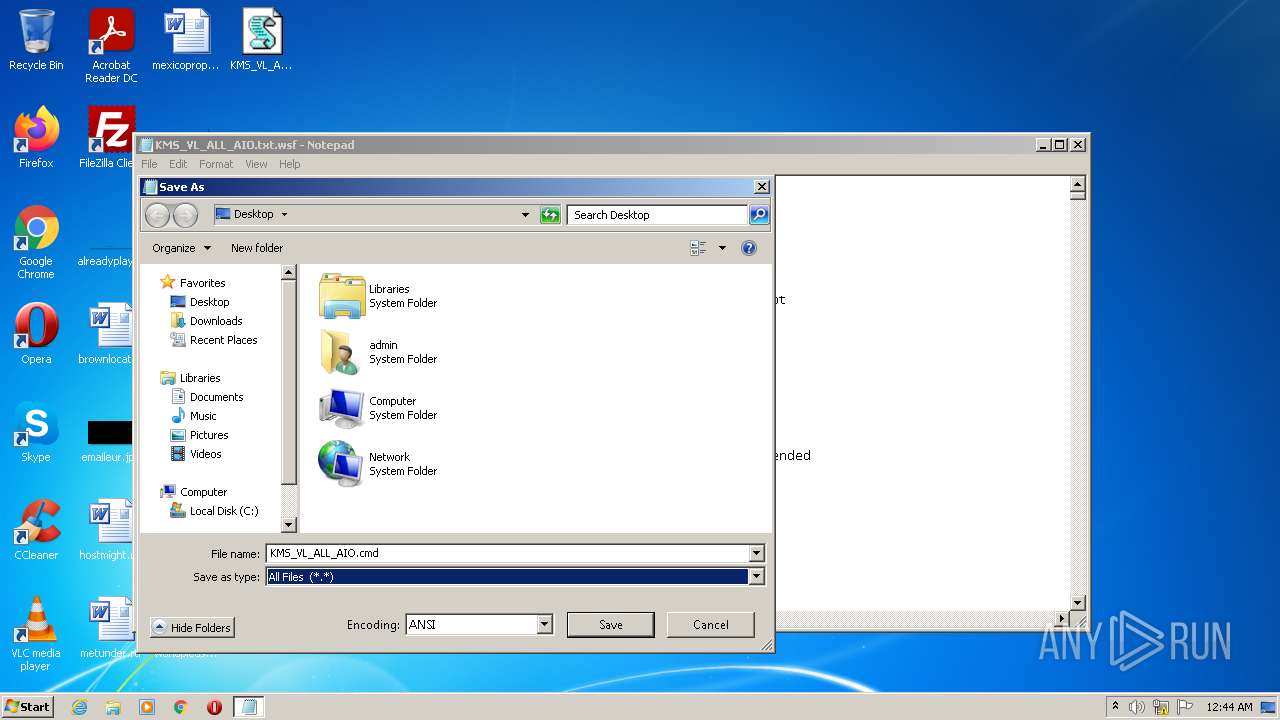
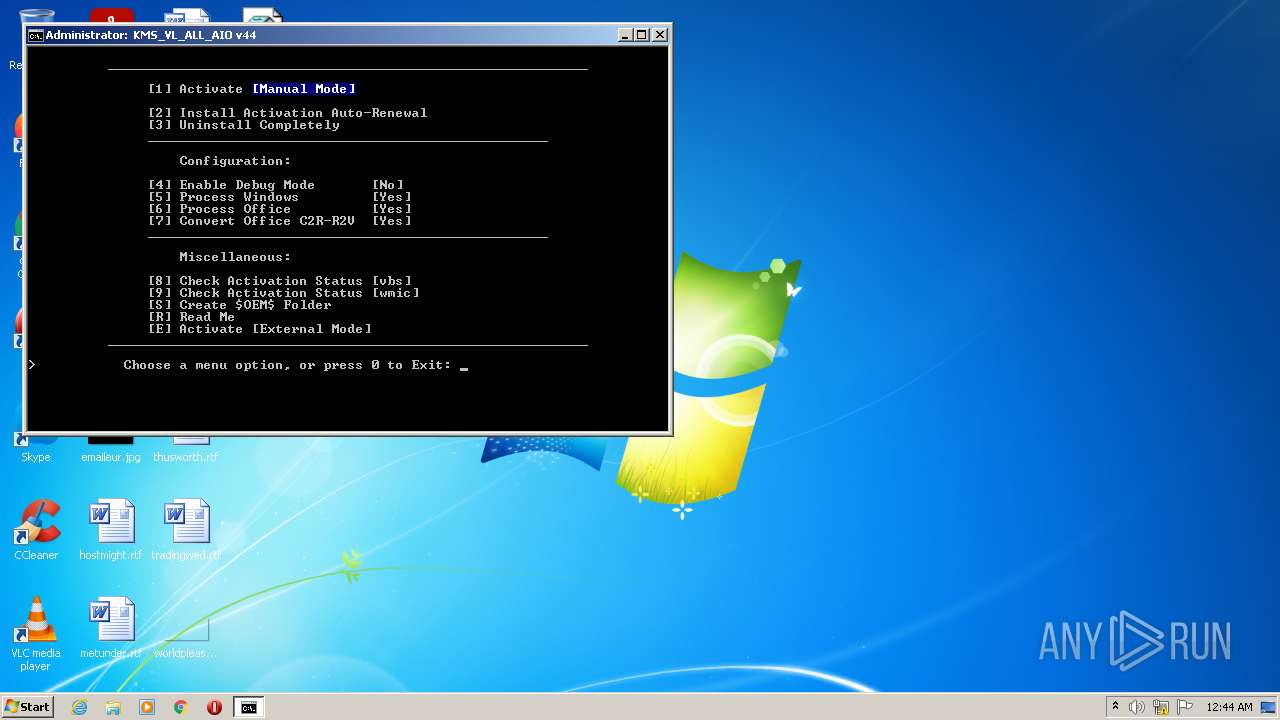
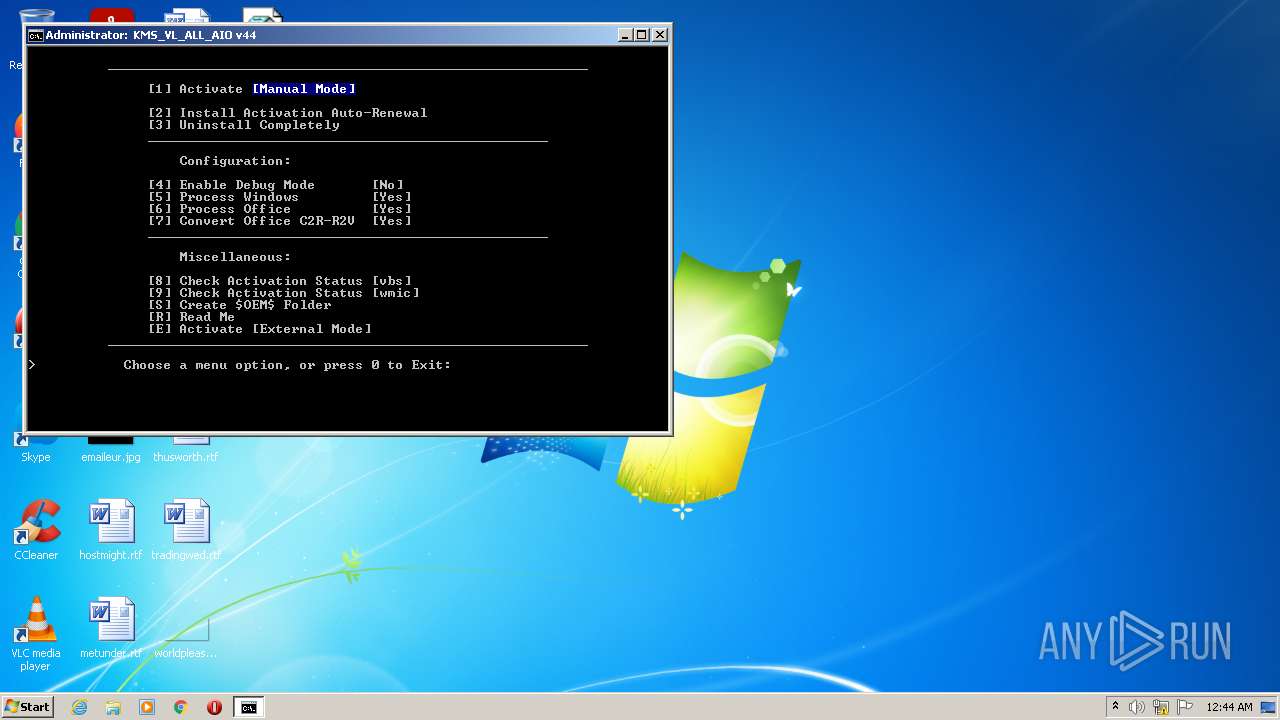
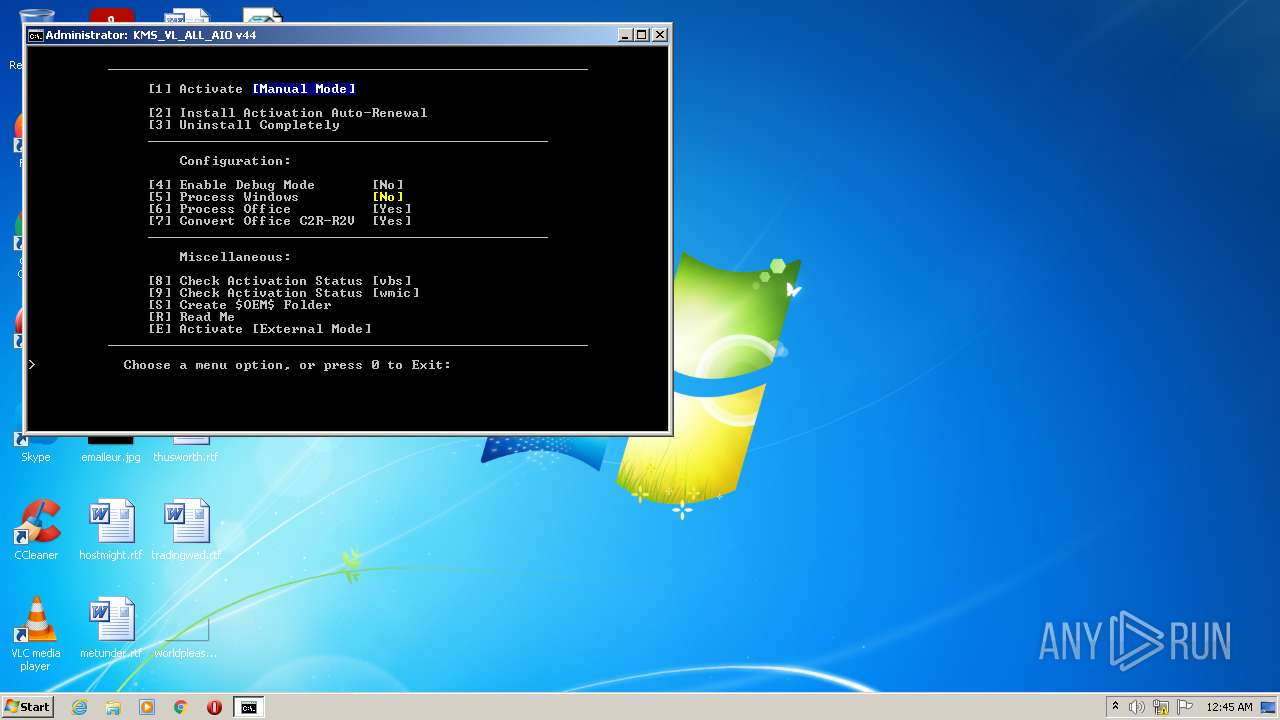
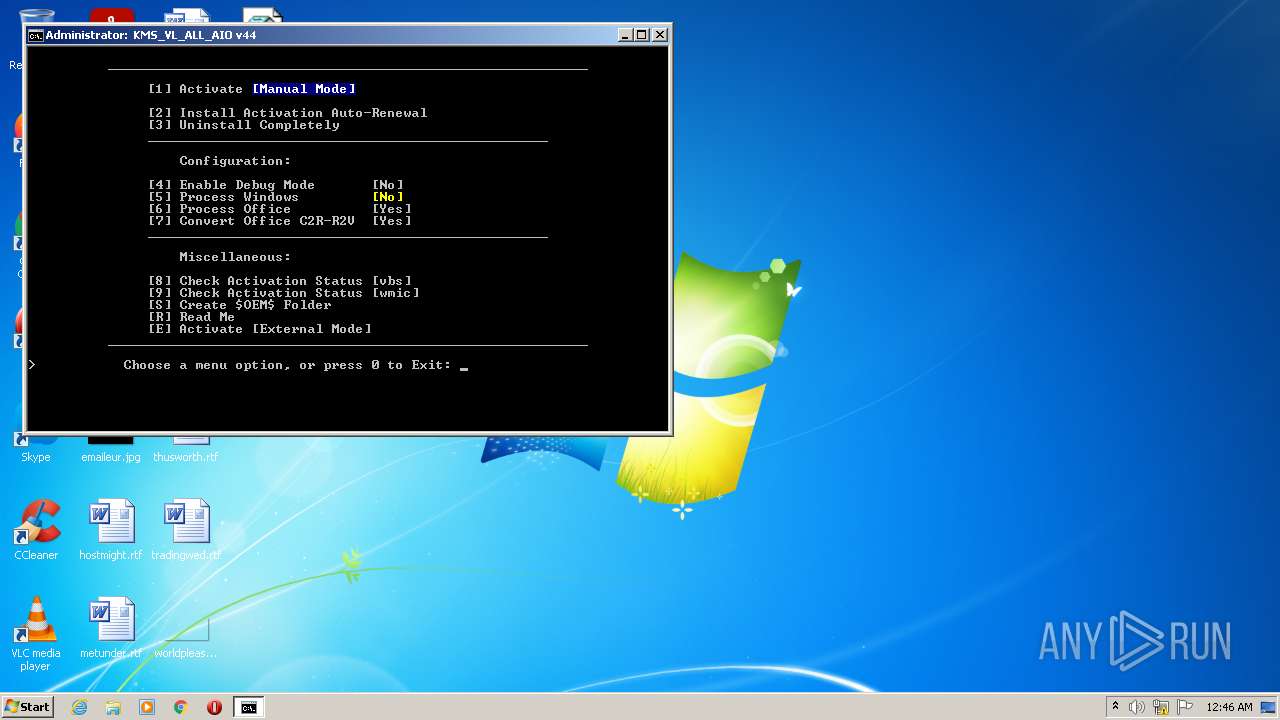
Manual execution by user
- cmd.exe (PID: 2840)
- Notepad.exe (PID: 3984)
Checks supported languages
- mode.com (PID: 3180)
- csc.exe (PID: 2248)
- cvtres.exe (PID: 3488)
- OSPPSVC.EXE (PID: 3724)
- mode.com (PID: 1764)
- mode.com (PID: 3652)
- mode.com (PID: 3304)
Process checks LSA protection
- csc.exe (PID: 2248)
- cvtres.exe (PID: 3488)
- OSPPSVC.EXE (PID: 3724)
Reads security settings of Internet Explorer
- cscript.exe (PID: 1228)
Reads the machine GUID from the registry
- csc.exe (PID: 2248)
- cvtres.exe (PID: 3488)
- OSPPSVC.EXE (PID: 3724)
Creates a file in a temporary directory
- csc.exe (PID: 2248)
Reads Microsoft Office registry keys
- reg.exe (PID: 3052)
- OSPPSVC.EXE (PID: 3724)
- reg.exe (PID: 3512)
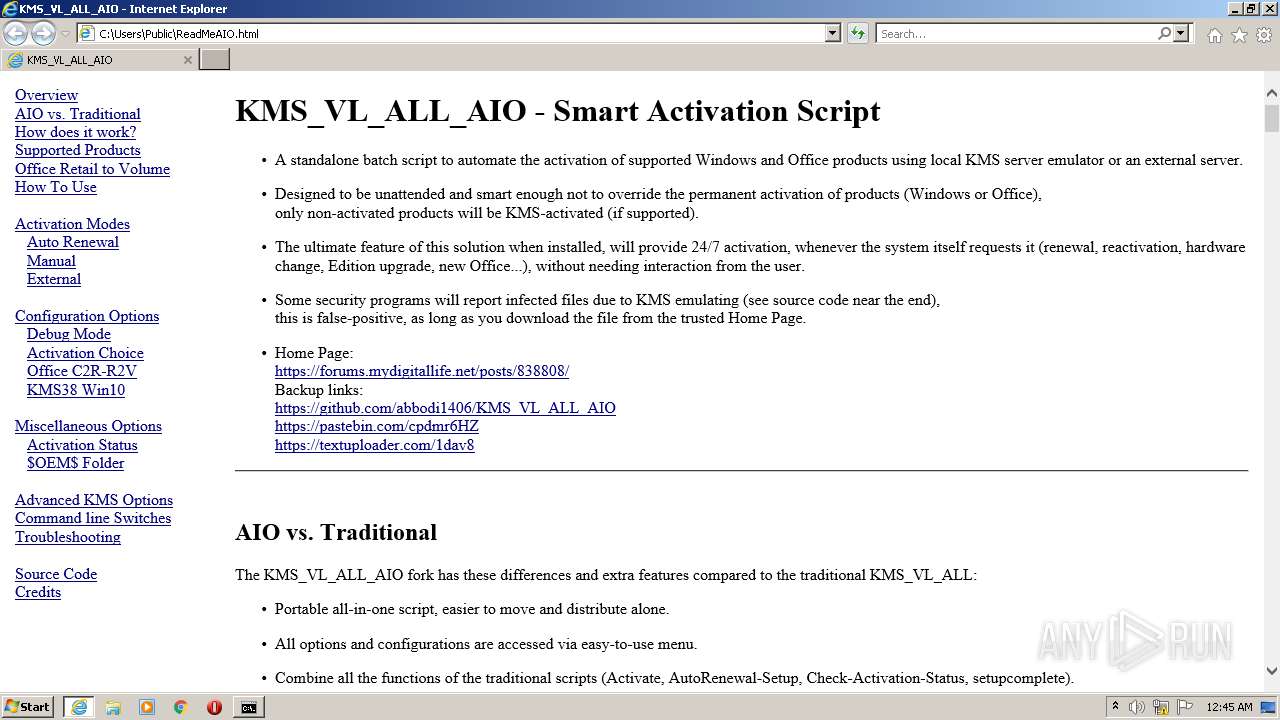
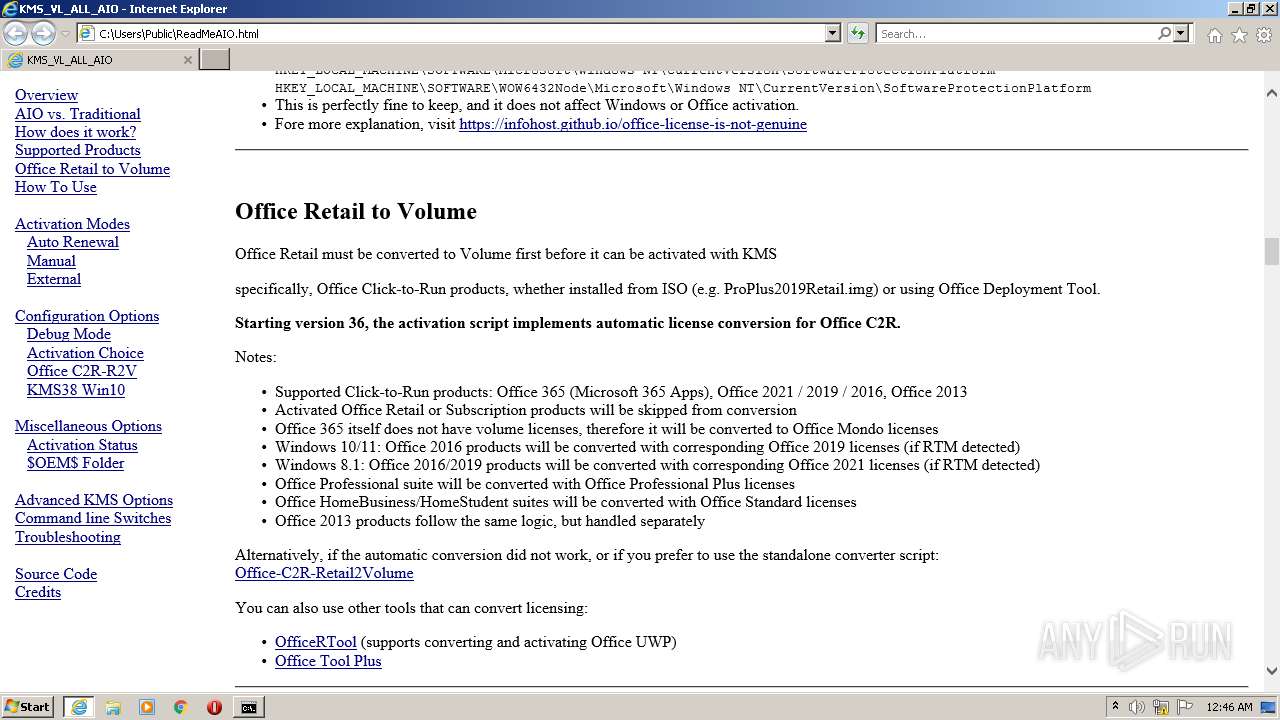
Starts Internet Explorer
- cmd.exe (PID: 2340)
Application launched itself
- iexplore.exe (PID: 1788)
Reads the computer name
- OSPPSVC.EXE (PID: 3724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .wsf | | | Windows Script File (72.7) |
|---|---|---|
| .html | | | HyperText Markup Language (27.2) |
Total processes
216
Monitored processes
171
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 116 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /v KMS_Emulation /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 276 | reg add "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\sppsvc.exe" /f /v GlobalFlag /t REG_DWORD /d 0x00000100 | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 284 | reg query "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion" /v ProductName | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 288 | sc query sppsvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 328 | reg delete "HKLM\SOFTWARE\Microsoft\OfficeSoftwareProtectionPlatform" /f /v KeyManagementServicePort | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 380 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SoftwareProtectionPlatform\55c92734-d682-4d71-983e-d6ec3f16059f" /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 472 | find /i "R_Retail" "C:\Windows\Temp\sppchk.txt" | C:\Windows\System32\find.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (grep) Utility Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 524 | sc query ClickToRunSvc | C:\Windows\System32\sc.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 1060 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 532 | reg delete "HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Image File Execution Options\osppsvc.exe" /v VerifierFlags /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 544 | reg query HKLM\SOFTWARE\Wow6432Node\Microsoft\Office\16.0\Common\InstallRoot /v Path | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
20 244
Read events
20 014
Write events
218
Delete events
12
Modification events
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 0202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 01000000020000000D0000000C000000000000000B00000007000000060000000A0000000900000008000000030000000500000004000000FFFFFFFF | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | 3 |
Value: 4E006F00740065007000610064002E0065007800650000000000 | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\LastVisitedPidlMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\cmd |
| Operation: | write | Name: | 0 |
Value: 74003200000000000000000080004B4D535F564C5F414C4C5F41494F2E636D640000520008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000004B004D0053005F0056004C005F0041004C004C005F00410049004F002E0063006D006400000022000000 | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\cmd |
| Operation: | write | Name: | MRUListEx |
Value: 00000000FFFFFFFF | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | 7 |
Value: 74003200000000000000000080004B4D535F564C5F414C4C5F41494F2E636D640000520008000400EFBE00000000000000002A000000000000000000000000000000000000000000000000004B004D0053005F0056004C005F0041004C004C005F00410049004F002E0063006D006400000022000000 | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSavePidlMRU\* |
| Operation: | write | Name: | MRUListEx |
Value: 0700000006000000050000000400000003000000020000000100000000000000FFFFFFFF | |||
| (PID) Process: | (3984) Notepad.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\CIDSizeMRU |
| Operation: | write | Name: | 4 |
Value: 4E006F00740065007000610064002E00650078006500000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000100000000000000 | |||
Executable files
2
Suspicious files
22
Text files
9
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3488 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES69F1.tmp | o | |
MD5:— | SHA256:— | |||
| 2248 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCA8D7A7C6117C4DBABEB681DEDBF0433E.TMP | res | |
MD5:— | SHA256:— | |||
| 1668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ilrhd4mm.cmdline | text | |
MD5:— | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\drwg5yxl.oqq.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3876 | powershell.exe | C:\Users\admin\AppData\Local\Temp\dvxjx3u2.x45.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2340 | cmd.exe | C:\Windows\Temp\`.txt | text | |
MD5:FFE40BE0916C7302AE237FEEBE53CF4B | SHA256:6EF78A8EF8E0752565DCC75E10DB254A573A51EAA183F0BFF99494E62F0B57C6 | |||
| 1668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\ya3tsujf.vml.ps1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 1668 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bkisewny.tdv.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 3724 | OSPPSVC.EXE | C:\ProgramData\Microsoft\OfficeSoftwareProtectionPlatform\Cache\cache.dat | binary | |
MD5:— | SHA256:— | |||
| 2248 | csc.exe | C:\Users\admin\AppData\Local\Temp\ilrhd4mm.out | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
10
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2528 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1788 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?c06075f4b7c1af06 | US | compressed | 4.70 Kb | whitelisted |
1788 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?6b8e310a5dfe1f15 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1788 | iexplore.exe | 13.107.21.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1788 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
1788 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
2528 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
2528 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
1788 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |