| File name: | AntiOS_1.1.1_Setup.exe |
| Full analysis: | https://app.any.run/tasks/e11a0270-5bc6-469d-bc5e-df9249b38b8d |
| Verdict: | No threats detected |
| Analysis date: | October 03, 2019, 16:40:05 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | E4F80DDF14F2EAF45BEEE383D2533182 |
| SHA1: | 76C41E6109AE39F4EE7654CA086F17D917863BC6 |
| SHA256: | 2C5493DD23F4B6466194FA4CACF277227DE70ACC82F62F582CE6212565C327C7 |
| SSDEEP: | 98304:pAI+zGuf+HE3PNZ4zdrHjbnoNNM8IU/PqD6S00QB:itjf+HE3VZ4JrD7rU3f0s |
MALICIOUS
No malicious indicators.SUSPICIOUS
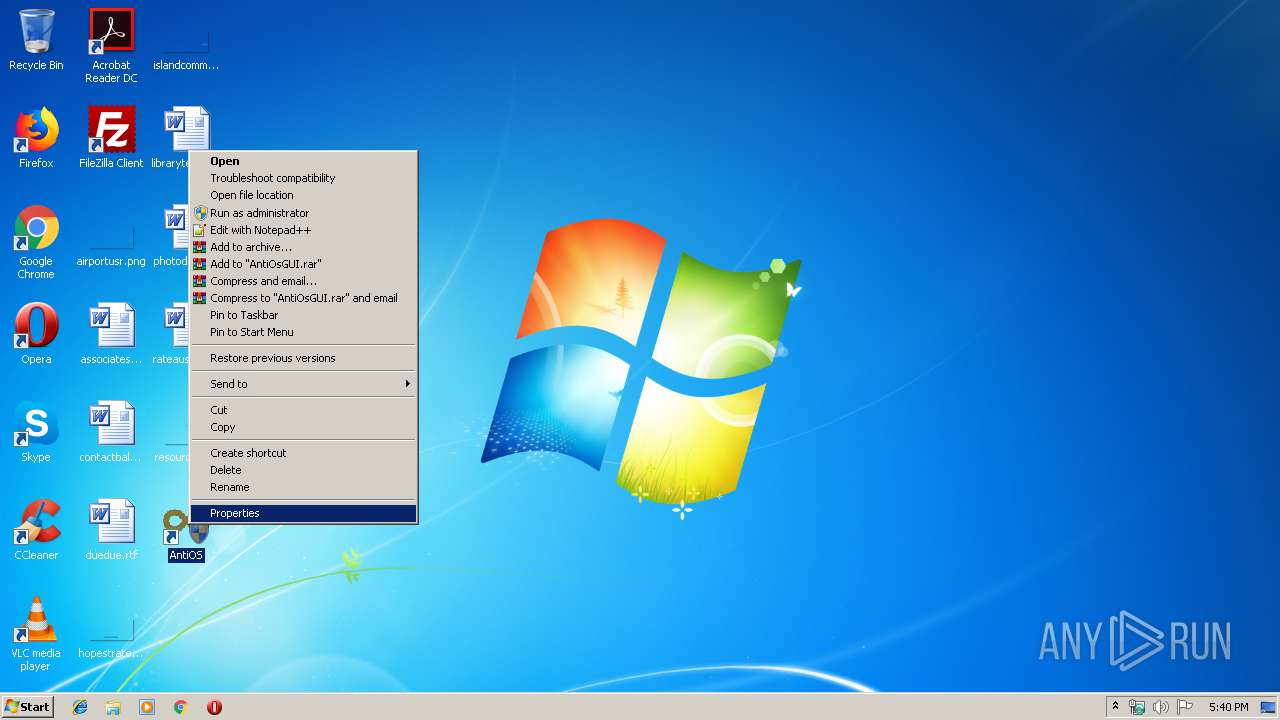
Creates files in the program directory
- AntiOS_1.1.1_Setup.exe (PID: 1636)
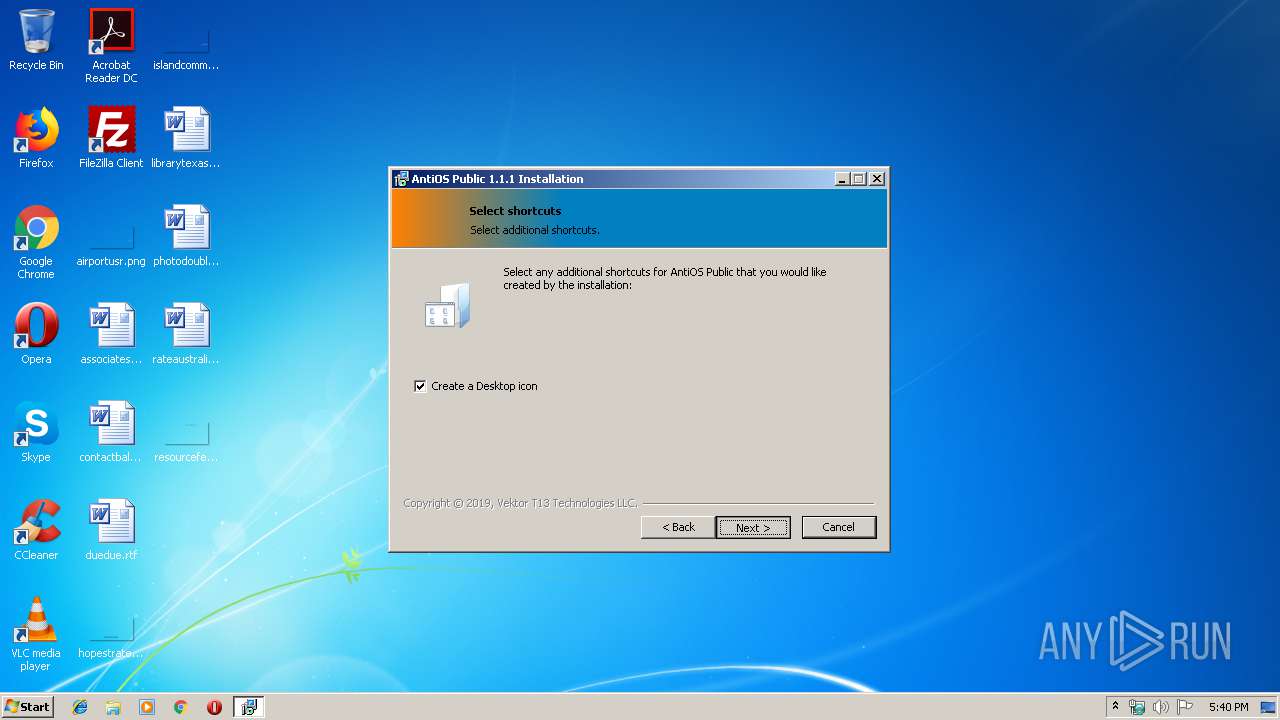
Creates a software uninstall entry
- AntiOS_1.1.1_Setup.exe (PID: 1636)
Executable content was dropped or overwritten
- AntiOS_1.1.1_Setup.exe (PID: 1636)
INFO
Dropped object may contain Bitcoin addresses
- AntiOS_1.1.1_Setup.exe (PID: 1636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .odttf | | | Obfuscated subsetted Font (28.7) |
|---|---|---|
| .exe | | | InstallShield setup (23.7) |
| .exe | | | Win32 EXE PECompact compressed (generic) (22.9) |
| .exe | | | Win32 Executable Delphi generic (7.8) |
| .scr | | | Windows screen saver (7.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 148992 |
| InitializedDataSize: | 31744 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x25468 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.1.1.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| Comments: | - |
| CompanyName: | Vektor T13 Technologies LLC. |
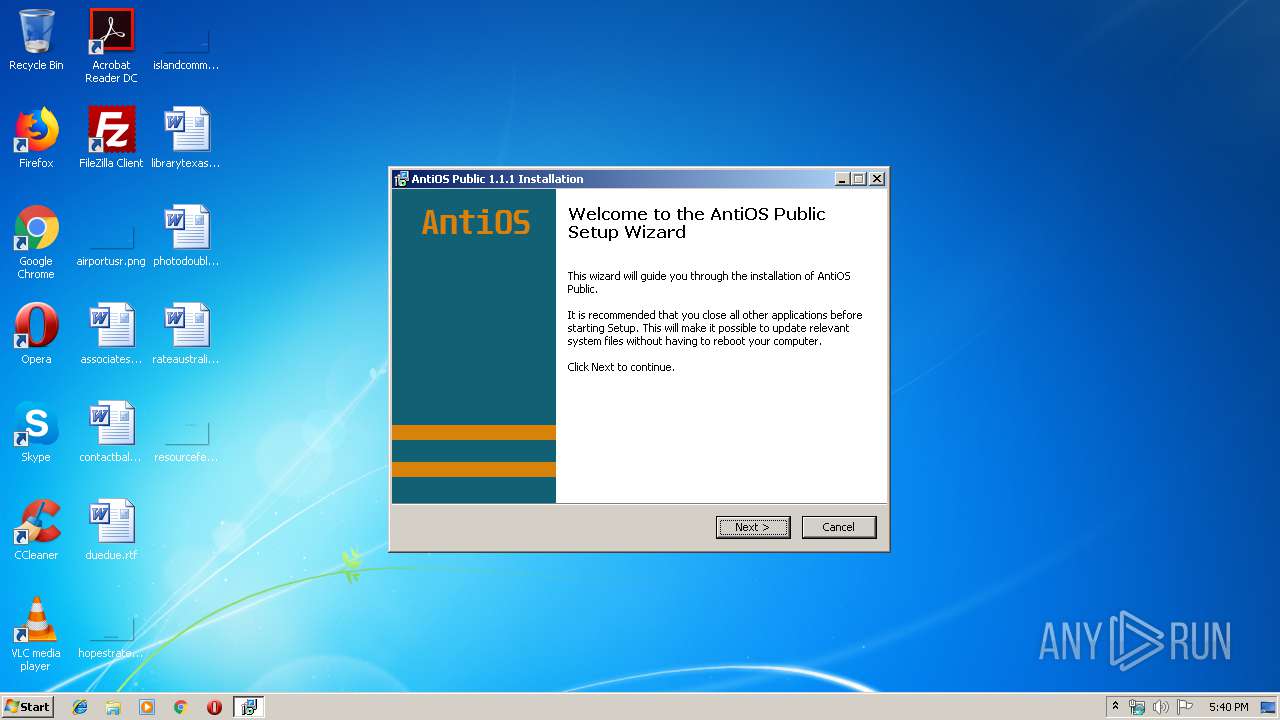
| FileDescription: | AntiOS Public 1.1.1 Installation |
| FileVersion: | 1.1.1 |
| LegalCopyright: | Vektor T13 Technologies LLC. |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Vektor T13 Technologies LLC. |
| FileDescription: | AntiOS Public 1.1.1 Installation |
| FileVersion: | 1.1.1 |
| LegalCopyright: | Vektor T13 Technologies LLC. |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x000244CC | 0x00024600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.59443 |
DATA | 0x00026000 | 0x00002894 | 0x00002A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.79376 |
BSS | 0x00029000 | 0x000010F5 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002B000 | 0x00001798 | 0x00001800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88555 |
.tls | 0x0002D000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0002E000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x0002F000 | 0x00001884 | 0x00001A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 6.58665 |
.rsrc | 0x00031000 | 0x00001CDC | 0x00001E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 4.77115 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93923 | 886 | UNKNOWN | Russian - Russia | RT_MANIFEST |
50 | 3.25755 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
51 | 4.01345 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
52 | 3.92897 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
53 | 4.27475 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
DVCLAL | 4 | 16 | UNKNOWN | UNKNOWN | RT_RCDATA |
PACKAGEINFO | 5.28362 | 272 | UNKNOWN | UNKNOWN | RT_RCDATA |
MAINICON | 2.57938 | 62 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
advapi32.dll |
cabinet.dll |
comctl32.dll |
gdi32.dll |
kernel32.dll |
ole32.dll |
oleaut32.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
41
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1636 | "C:\Users\admin\AppData\Local\Temp\AntiOS_1.1.1_Setup.exe" | C:\Users\admin\AppData\Local\Temp\AntiOS_1.1.1_Setup.exe | explorer.exe | ||||||||||||
User: admin Company: Vektor T13 Technologies LLC. Integrity Level: HIGH Description: AntiOS Public 1.1.1 Installation Exit code: 0 Version: 1.1.1 Modules
| |||||||||||||||
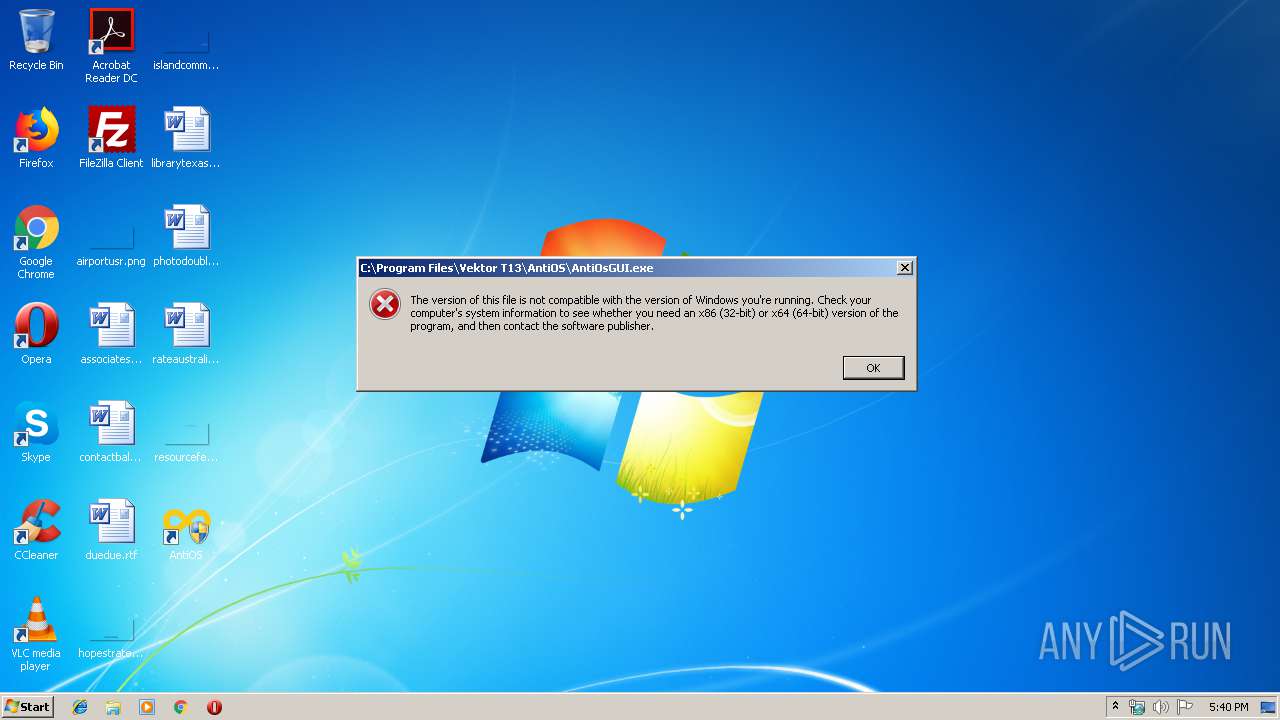
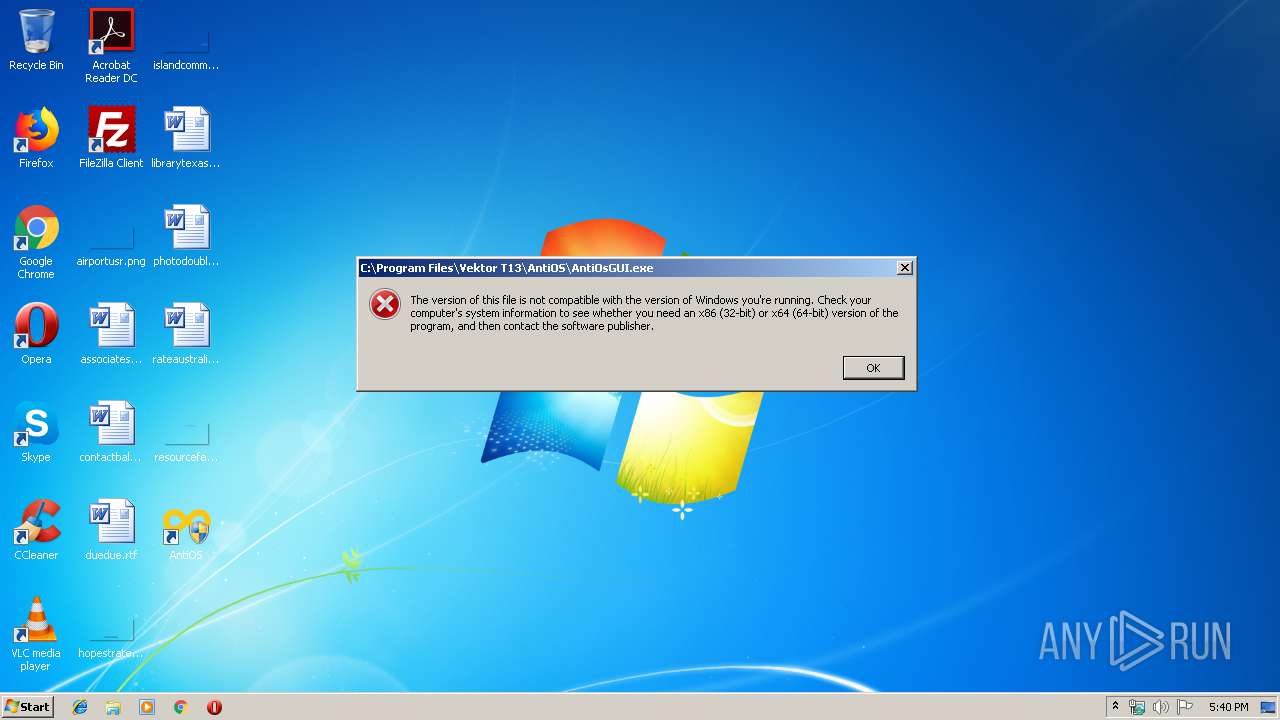
| 3584 | "C:\Users\admin\AppData\Local\Temp\AntiOS_1.1.1_Setup.exe" | C:\Users\admin\AppData\Local\Temp\AntiOS_1.1.1_Setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Vektor T13 Technologies LLC. Integrity Level: MEDIUM Description: AntiOS Public 1.1.1 Installation Exit code: 3221226540 Version: 1.1.1 Modules
| |||||||||||||||
Total events
183
Read events
162
Write events
21
Delete events
0
Modification events
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | DisplayName |
Value: AntiOS Public 1.1.1 | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.1.1 | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | VersionMajor |
Value: 1 | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | VersionMinor |
Value: 1 | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | Publisher |
Value: Vektor T13 Technologies LLC. | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Vektor T13\AntiOS\Uninstall.exe | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Vektor T13\AntiOS\Uninstall.exe | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | URLInfoAbout |
Value: https://vektort13.pro/ | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | HelpLink |
Value: mailto:vektort13@antidetect.online | |||
| (PID) Process: | (1636) AntiOS_1.1.1_Setup.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\AntiOS Public 1.1.1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Vektor T13\AntiOS\ | |||
Executable files
6
Suspicious files
0
Text files
4
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Fonts\Anatolian.otf | ttf | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\AntiOsGUI.exe | executable | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Users\admin\AppData\Local\Temp\$inst\5.tmp | image | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Fonts\Padauk-Regular.ttf | ttf | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Fonts\vijaya.ttf | ttf | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\firewall_rules_3.wfw | hiv | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Fonts\Padauk-Bold.ttf | ttf | |
MD5:— | SHA256:— | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Fonts\Symbola.ttf | ttf | |
MD5:2F6DC0F18577B04573D407D6D0348D41 | SHA256:9AED2C77547D9D3AC95BE6EC757A6DD7119B3725959D712CAFB01017E8ECDC14 | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Volumeid64.exe | executable | |
MD5:81A45F1A91448313B76D2E6D5308AA7A | SHA256:FB0D02EA26BB1E5DF5A07147931CAF1AE3D7D1D9B4D83F168B678E7F3A1C0ECD | |||
| 1636 | AntiOS_1.1.1_Setup.exe | C:\Program Files\Vektor T13\AntiOS\Uninstall.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report