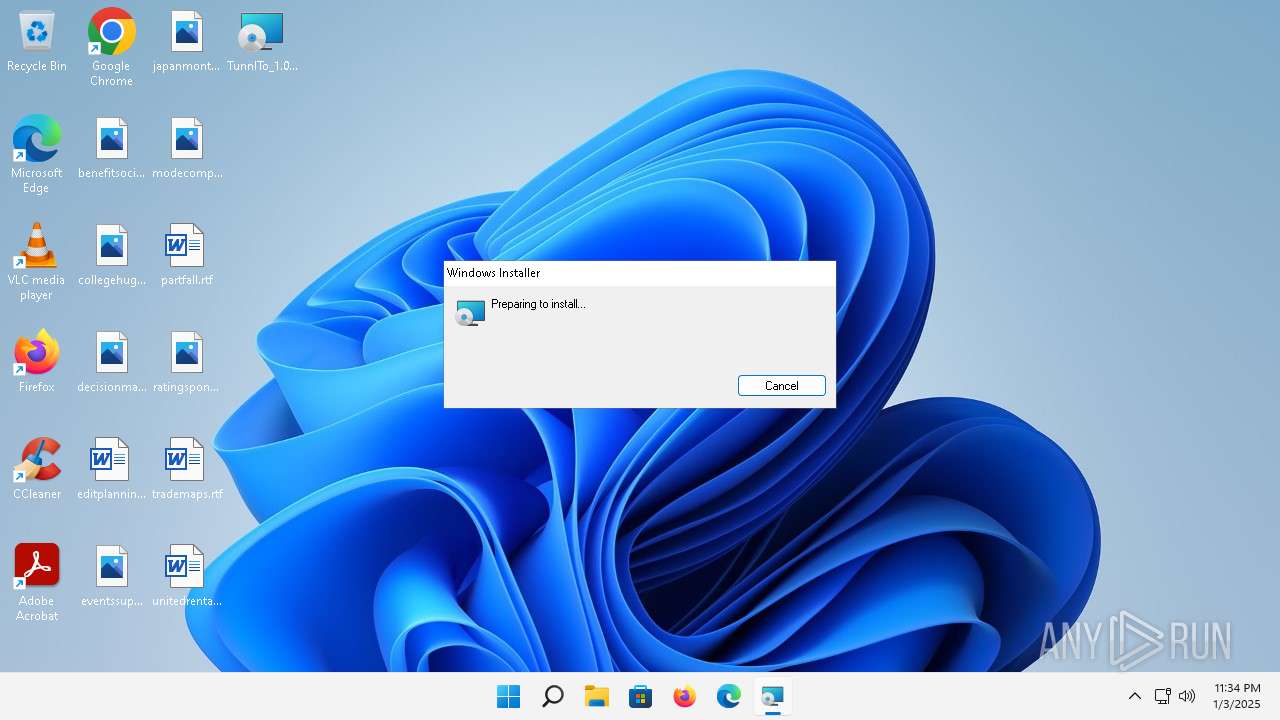
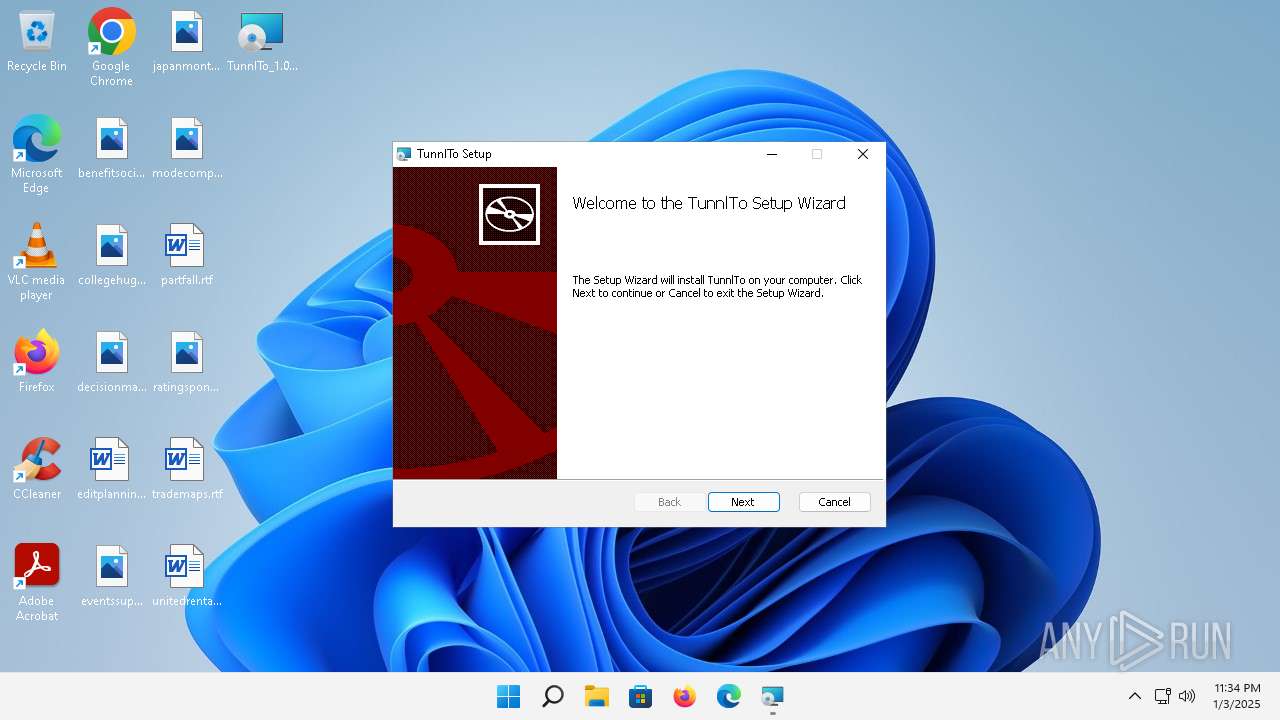
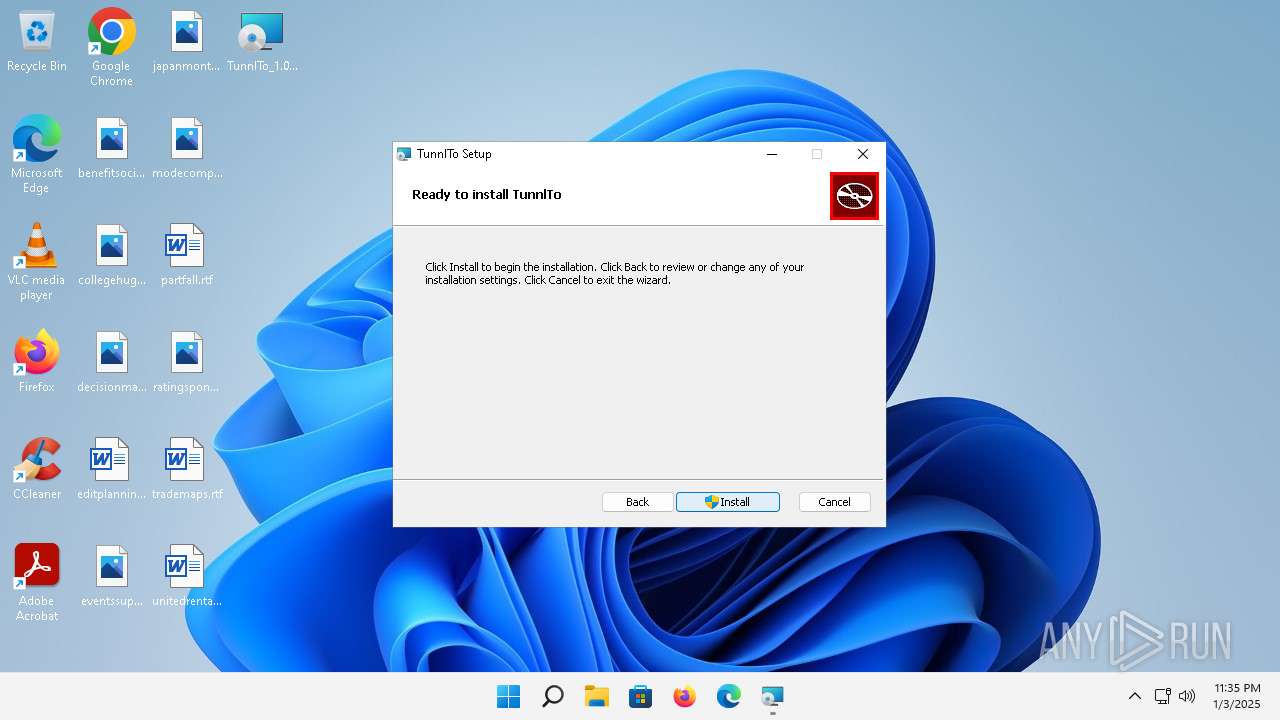
| File name: | TunnlTo_1.0.7_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/d9795db6-0e4b-4f29-92db-505e19f66cc8 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2025, 23:34:38 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: TunnlTo, Author: tunnl, Keywords: Installer, Comments: This installer database contains the logic and data required to install TunnlTo., Template: x64;0, Revision Number: {61FF8CDE-2F35-44D5-A379-E4CE8CE75A15}, Create Time/Date: Mon May 20 02:16:42 2024, Last Saved Time/Date: Mon May 20 02:16:42 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | ABA32A1DCD826CFFEF0DD1832F0FC882 |
| SHA1: | DF44CD8BAF537D3543BE0D5AE2B773866DE502D8 |
| SHA256: | 2C4177EE75B4297E31EA834C1BD140FA7422C8F2049347141C2B83E8C255C48C |
| SSDEEP: | 98304:k2Lax6gp2bSMoRfkcYJ3faC2z5lRAEkRS1jx4ZvHBGu0gGw+XtY782Un6yXoDhxx:gz |
MALICIOUS
The DLL Hijacking
- msedgewebview2.exe (PID: 1768)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 5140)
- msiexec.exe (PID: 5452)
Reads the Internet Settings
- msiexec.exe (PID: 5140)
- msiexec.exe (PID: 2676)
- msedgewebview2.exe (PID: 7084)
- TunnlTo.exe (PID: 4080)
- powershell.exe (PID: 5072)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 1912)
- powershell.exe (PID: 6500)
- powershell.exe (PID: 1900)
Executes as Windows Service
- VSSVC.exe (PID: 704)
Checks Windows Trust Settings
- msiexec.exe (PID: 5452)
- drvinst.exe (PID: 3636)
- devcon.exe (PID: 1864)
- drvinst.exe (PID: 3976)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 2676)
- msedgewebview2.exe (PID: 7084)
Application launched itself
- msedgewebview2.exe (PID: 7084)
Reads settings of System Certificates
- msedgewebview2.exe (PID: 7084)
- TunnlTo.exe (PID: 4080)
Searches for installed software
- TunnlTo.exe (PID: 4080)
Found IP address in command line
- powershell.exe (PID: 5072)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 1912)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 1900)
- powershell.exe (PID: 1600)
- powershell.exe (PID: 6500)
Starts POWERSHELL.EXE for commands execution
- TunnlTo.exe (PID: 4080)
Starts process via Powershell
- powershell.exe (PID: 5072)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 1912)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 1900)
- powershell.exe (PID: 1600)
- powershell.exe (PID: 6500)
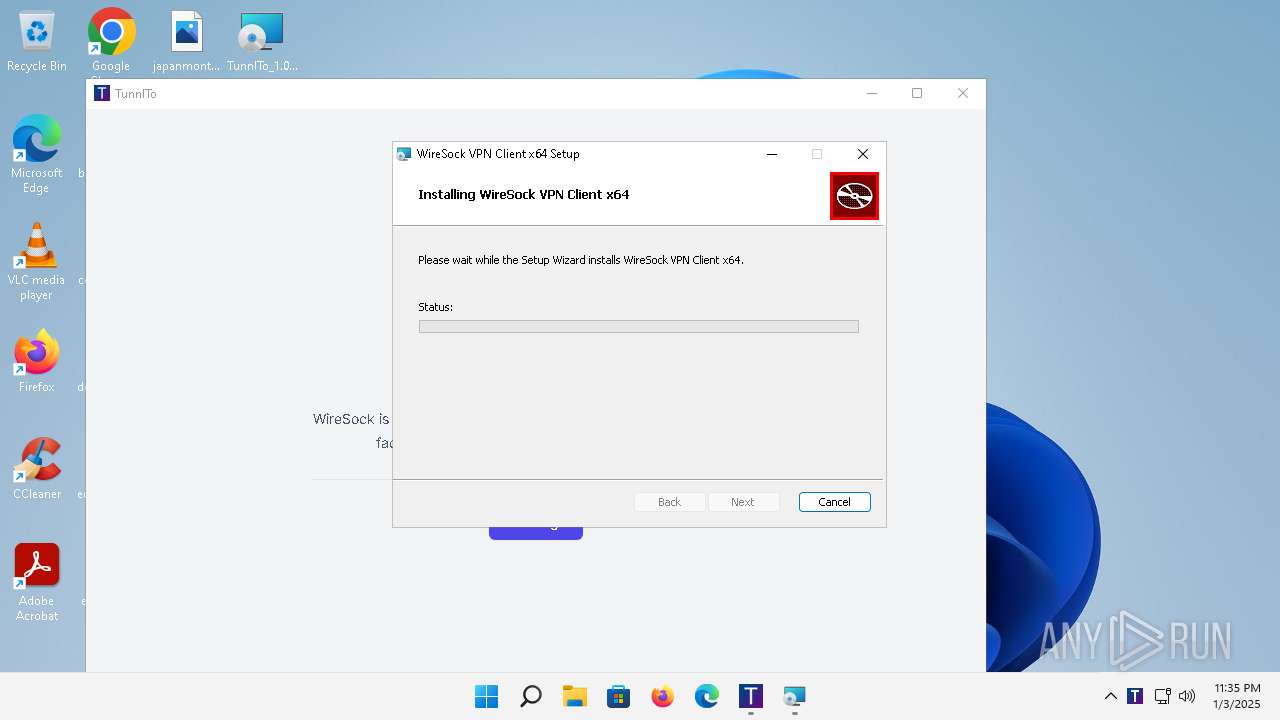
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 5452)
- drvinst.exe (PID: 3636)
- netcfg.exe (PID: 3684)
- drvinst.exe (PID: 3976)
Adds/modifies Windows certificates
- certutil.exe (PID: 2944)
- certutil.exe (PID: 4772)
Windows service management via SC.EXE
- sc.exe (PID: 5800)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 5452)
Executable content was dropped or overwritten
- drvinst.exe (PID: 3636)
- netcfg.exe (PID: 3684)
- drvinst.exe (PID: 3976)
Creates files in the driver directory
- drvinst.exe (PID: 3636)
- drvinst.exe (PID: 3976)
- devcon.exe (PID: 1864)
Creates or modifies Windows services
- drvinst.exe (PID: 6836)
Starts SC.EXE for service management
- msiexec.exe (PID: 4064)
INFO
Reads the software policy settings
- msiexec.exe (PID: 5140)
- msiexec.exe (PID: 5452)
- msedgewebview2.exe (PID: 7084)
- TunnlTo.exe (PID: 4080)
- drvinst.exe (PID: 3636)
- devcon.exe (PID: 1864)
- drvinst.exe (PID: 3976)
Checks supported languages
- msiexec.exe (PID: 5452)
- msiexec.exe (PID: 2676)
- msedgewebview2.exe (PID: 3308)
- msedgewebview2.exe (PID: 2152)
- TunnlTo.exe (PID: 4080)
- msedgewebview2.exe (PID: 5632)
- msedgewebview2.exe (PID: 3152)
- msedgewebview2.exe (PID: 1768)
- msedgewebview2.exe (PID: 2028)
- msiexec.exe (PID: 4064)
- drvinst.exe (PID: 3636)
- devcon.exe (PID: 1864)
- drvinst.exe (PID: 3976)
- msedgewebview2.exe (PID: 7084)
- drvinst.exe (PID: 6836)
- msedgewebview2.exe (PID: 3804)
- msedgewebview2.exe (PID: 5896)
The sample compiled with english language support
- msiexec.exe (PID: 5140)
- msiexec.exe (PID: 5452)
- drvinst.exe (PID: 3976)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5140)
Reads the computer name
- msiexec.exe (PID: 2676)
- msiexec.exe (PID: 5452)
- TunnlTo.exe (PID: 4080)
- msedgewebview2.exe (PID: 7084)
- msedgewebview2.exe (PID: 1768)
- msiexec.exe (PID: 4064)
- drvinst.exe (PID: 3636)
- devcon.exe (PID: 1864)
- msedgewebview2.exe (PID: 5632)
- drvinst.exe (PID: 6836)
- drvinst.exe (PID: 3976)
Reads the machine GUID from the registry
- msiexec.exe (PID: 5452)
- msedgewebview2.exe (PID: 7084)
- TunnlTo.exe (PID: 4080)
- drvinst.exe (PID: 3636)
- devcon.exe (PID: 1864)
- drvinst.exe (PID: 3976)
Checks proxy server information
- msiexec.exe (PID: 5140)
- msedgewebview2.exe (PID: 7084)
- TunnlTo.exe (PID: 4080)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5452)
- msiexec.exe (PID: 5140)
Manages system restore points
- SrTasks.exe (PID: 5932)
- SrTasks.exe (PID: 1600)
Creates a software uninstall entry
- msiexec.exe (PID: 5452)
The process uses the downloaded file
- msiexec.exe (PID: 2676)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 4164)
- powershell.exe (PID: 6500)
Sends debugging messages
- msedgewebview2.exe (PID: 7084)
Creates files or folders in the user directory
- msedgewebview2.exe (PID: 3308)
- msedgewebview2.exe (PID: 7084)
- msedgewebview2.exe (PID: 5632)
Application based on Rust
- TunnlTo.exe (PID: 4080)
Creates files in the driver directory
- netcfg.exe (PID: 3684)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5072)
- powershell.exe (PID: 6388)
- powershell.exe (PID: 1912)
- powershell.exe (PID: 6500)
- powershell.exe (PID: 3856)
- powershell.exe (PID: 1900)
- powershell.exe (PID: 4164)
Create files in a temporary directory
- msedgewebview2.exe (PID: 7084)
Reads Environment values
- msedgewebview2.exe (PID: 7084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | TunnlTo |
| Author: | tunnl |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install TunnlTo. |
| Template: | x64;0 |
| RevisionNumber: | {61FF8CDE-2F35-44D5-A379-E4CE8CE75A15} |
| CreateDate: | 2024:05:20 02:16:42 |
| ModifyDate: | 2024:05:20 02:16:42 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
Total processes
175
Monitored processes
57
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 704 | C:\Windows\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | devcon.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1600 | C:\Windows\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:15 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
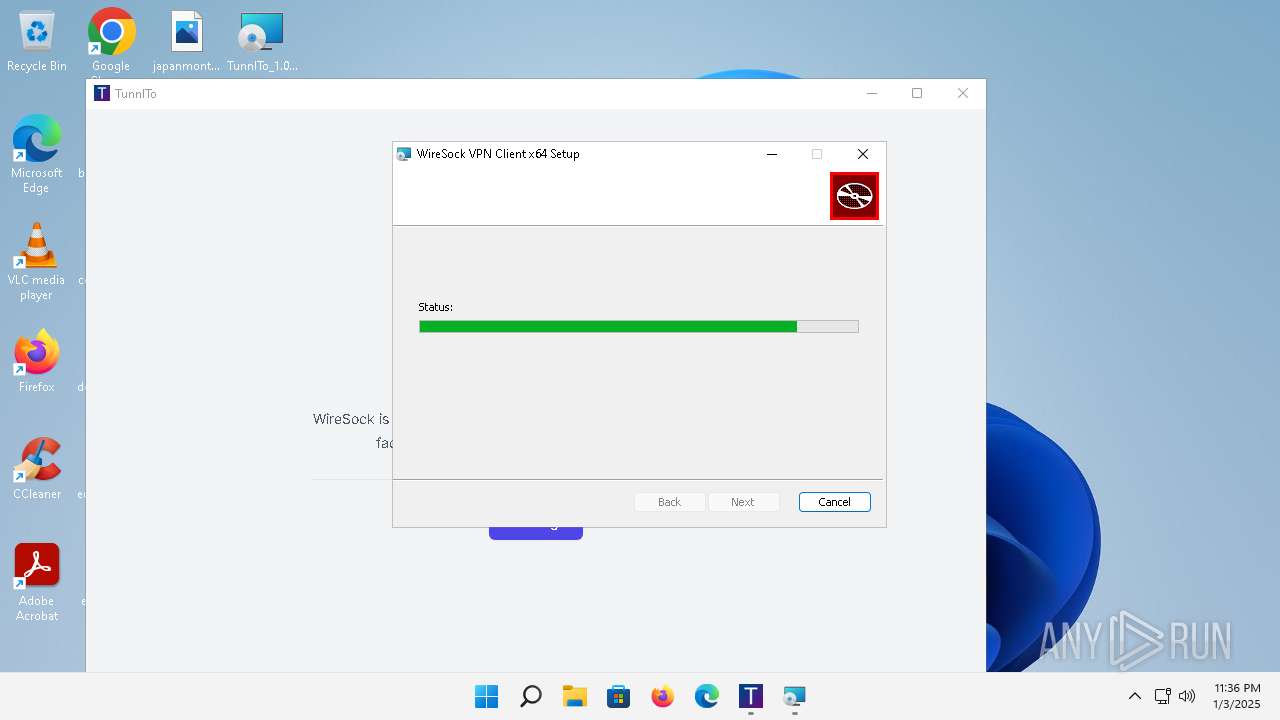
| 1600 | "powershell" -command "(Start-Process -FilePath \"msiexec.exe\" -ArgumentList \"/i\", '\"C:\Program Files\TunnlTo\wiresock\wiresock-vpn-client-x64-1.2.37.1.msi\"', \"/qr\" -Wait -Passthru).ExitCode" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | TunnlTo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | "C:\Windows\system32\msiexec.exe" /i "C:\Program Files\TunnlTo\wiresock\wiresock-vpn-client-x64-1.2.37.1.msi" /qr | C:\Windows\System32\msiexec.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1616 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1768 | "C:\Program Files (x86)\Microsoft\EdgeWebView\Application\103.0.1264.77\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Local\com.tunnl.to\EBWebView" --webview-exe-name=TunnlTo.exe --webview-exe-version=1.0.7 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --mojo-platform-channel-handle=1816 --field-trial-handle=1864,i,161121519372870257,12022259221583942188,131072 --disable-features=msPdfOOUI,msSmartScreenProtection,msWebOOUI /prefetch:2 | C:\Program Files (x86)\Microsoft\EdgeWebView\Application\103.0.1264.77\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 103.0.1264.77 Modules
| |||||||||||||||
| 1864 | "C:\Program Files\WireSock VPN Client\wiresock-adapter\devcon.exe" install "C:\Program Files\WireSock VPN Client\wiresock-adapter\wiresock.inf" wiresock | C:\Program Files\WireSock VPN Client\wiresock-adapter\devcon.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Device Console Exit code: 0 Version: 10.0.19041.685 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1900 | "powershell" -command "(Start-Process -FilePath \"msiexec.exe\" -ArgumentList \"/i\", '\"C:\Program Files\TunnlTo\wiresock\wiresock-vpn-client-x64-1.2.37.1.msi\"', \"/qr\" -Wait -Passthru).ExitCode" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | TunnlTo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1912 | "powershell" -command "(Start-Process -FilePath \"msiexec.exe\" -ArgumentList \"/i\", '\"C:\Program Files\TunnlTo\wiresock\wiresock-vpn-client-x64-1.2.37.1.msi\"', \"/qr\" -Wait -Passthru).ExitCode" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | TunnlTo.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
73 916
Read events
72 952
Write events
831
Delete events
133
Modification events
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 48000000000000004DDF2322385EDB014C15000098170000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 480000000000000065BF5A22385EDB014C15000098170000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 480000000000000065BF5A22385EDB014C15000098170000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000013EB6122385EDB014C15000098170000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000ED422622385EDB014C15000098170000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Leave) |
Value: 480000000000000065875F22385EDB014C15000098170000D10700000100000000000000010000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (5452) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 14 | |||
| (PID) Process: | (704) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000895BD422385EDB01C002000038100000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (704) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000895BD422385EDB01C0020000C8120000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (704) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000895BD422385EDB01C00200000C170000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
26
Suspicious files
261
Text files
47
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 5452 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 5452 | msiexec.exe | C:\Windows\Installer\258539.msi | — | |
MD5:— | SHA256:— | |||
| 5140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:44EDDD67A563118FD4452D5543E46BD3 | SHA256:ED63F957ADF96AFC755A2225DD23BC2C97361FD6F86B0DE162F5EDD1B7D8639E | |||
| 5140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:77B20B5CD41BC6BB475CCA3F91AE6E3C | SHA256:5511A9B9F9144ED7BDE4CCB074733B7C564D918D2A8B10D391AFC6BE5B3B1509 | |||
| 5140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\0DA515F703BB9B49479E8697ADB0B955_4136D3715888E22D65EBE484B233D81B | binary | |
MD5:5D3D8F5474DCD1CB16E4319FB50277AA | SHA256:C6D253A05DF905873956BE129DF6AC0FF67551939C7B45B02B5BC883023107D3 | |||
| 5140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | der | |
MD5:24B0D1FA2D55A899CE8BB09C789A78A7 | SHA256:71D31BABA47E1AB6E543B213F8BC4EF22A52AD2032B01878C2808726A92B9F6A | |||
| 5140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:47833796A49A477D746107BA0FA1F3D9 | SHA256:35919053BEA95FFCE906004635CFEB025B38823A25AD698762308616CF27EADC | |||
| 5452 | msiexec.exe | C:\Windows\Temp\~DFE9357A27D99DCFC9.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 5452 | msiexec.exe | C:\Windows\Installer\25853b.msi | — | |
MD5:— | SHA256:— | |||
| 5140 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_50385F8EB1F713E33924A830D7A2A41C | binary | |
MD5:189078DFD83F2401F4B854346AD06DCC | SHA256:53404AB6DEED6F8373986F85F5FB9012CCC547FB2454104C7BAF88B315EF9BEF | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
27
DNS requests
15
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 104.124.11.219:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
5140 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 2.21.190.26:443 | https://fs.microsoft.com/fs/windows/config.json | unknown | — | — | unknown |
5140 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDDIt6H%2BXfAETa93iEg%3D%3D | unknown | — | — | whitelisted |
5140 | msiexec.exe | GET | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
4272 | MoUsoCoreWorker.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?97b795836009ca1f | unknown | — | — | whitelisted |
2860 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?f18bf237da1ef01e | unknown | — | — | whitelisted |
— | — | GET | 200 | 13.107.246.45:443 | https://edgeassetservice.azureedge.net/assets/signal_triggers/1.3.2/asset?assetgroup=TriggeringSignals | unknown | — | — | unknown |
2860 | svchost.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/pinrulesstl.cab?0ab3f725da671922 | unknown | — | — | whitelisted |
528 | svchost.exe | POST | 403 | 2.21.189.164:80 | http://go.microsoft.com/fwlink/?LinkID=252669&clcid=0x409 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 104.124.11.219:80 | — | Akamai International B.V. | DE | unknown |
4272 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5140 | msiexec.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
4272 | MoUsoCoreWorker.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
5140 | msiexec.exe | 104.18.21.226:80 | ocsp.globalsign.com | CLOUDFLARENET | — | whitelisted |
5552 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
5632 | msedgewebview2.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4080 | TunnlTo.exe | 185.199.111.133:443 | gist.githubusercontent.com | FASTLY | US | shared |
6184 | svchost.exe | 2.21.190.26:443 | fs.microsoft.com | Akamai International B.V. | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
gist.githubusercontent.com |
| shared |
fs.microsoft.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
edgeassetservice.azureedge.net |
| whitelisted |
www.msftconnecttest.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Microsoft Connection Test |
1296 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\com.tunnl.to directory exists )
|