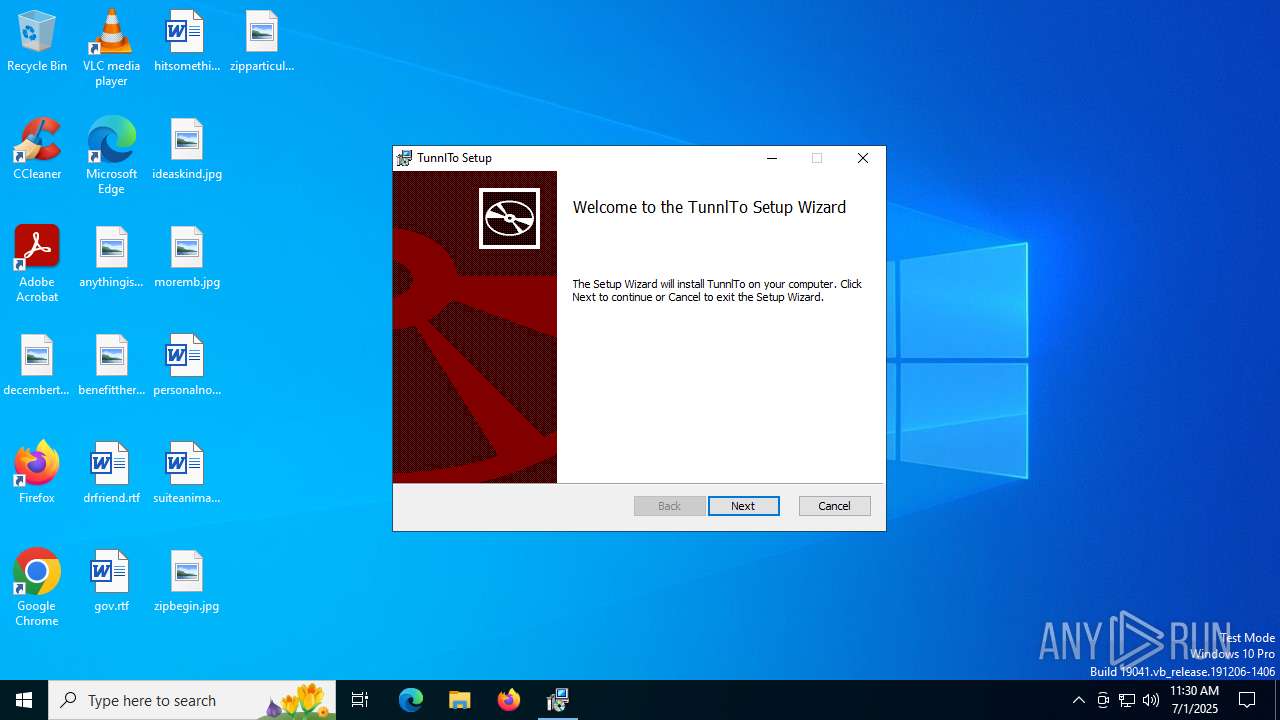
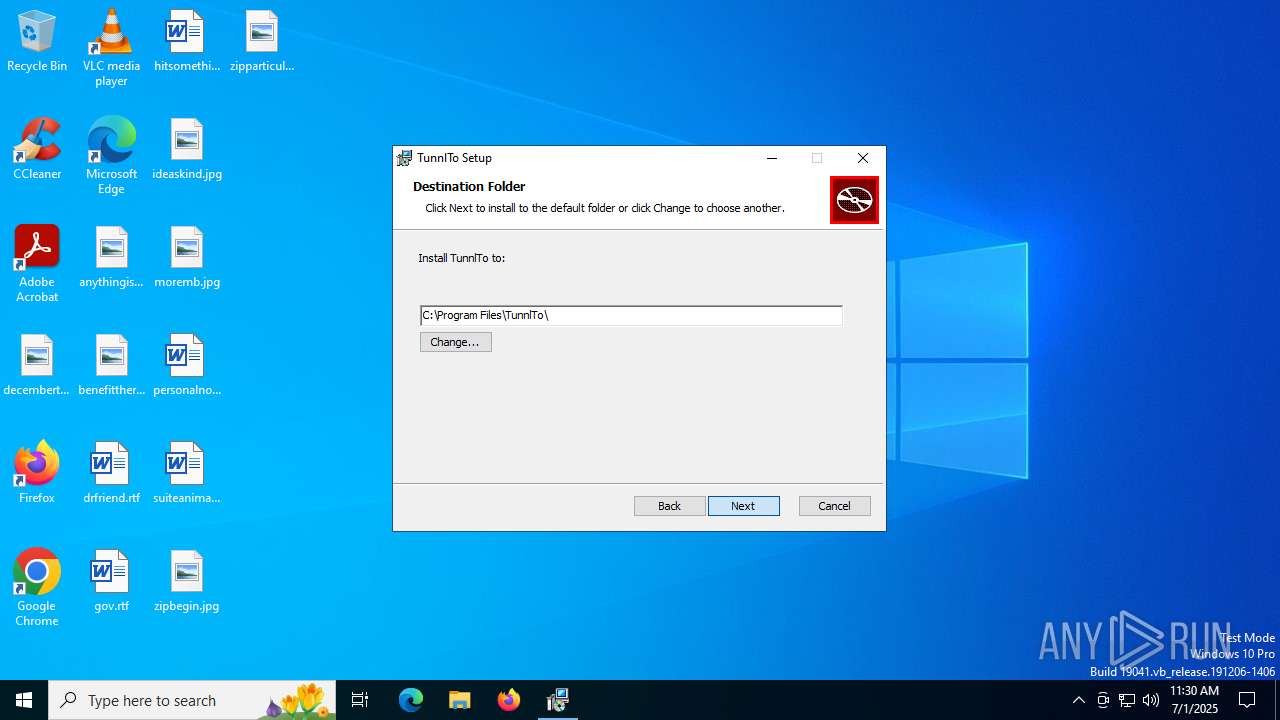
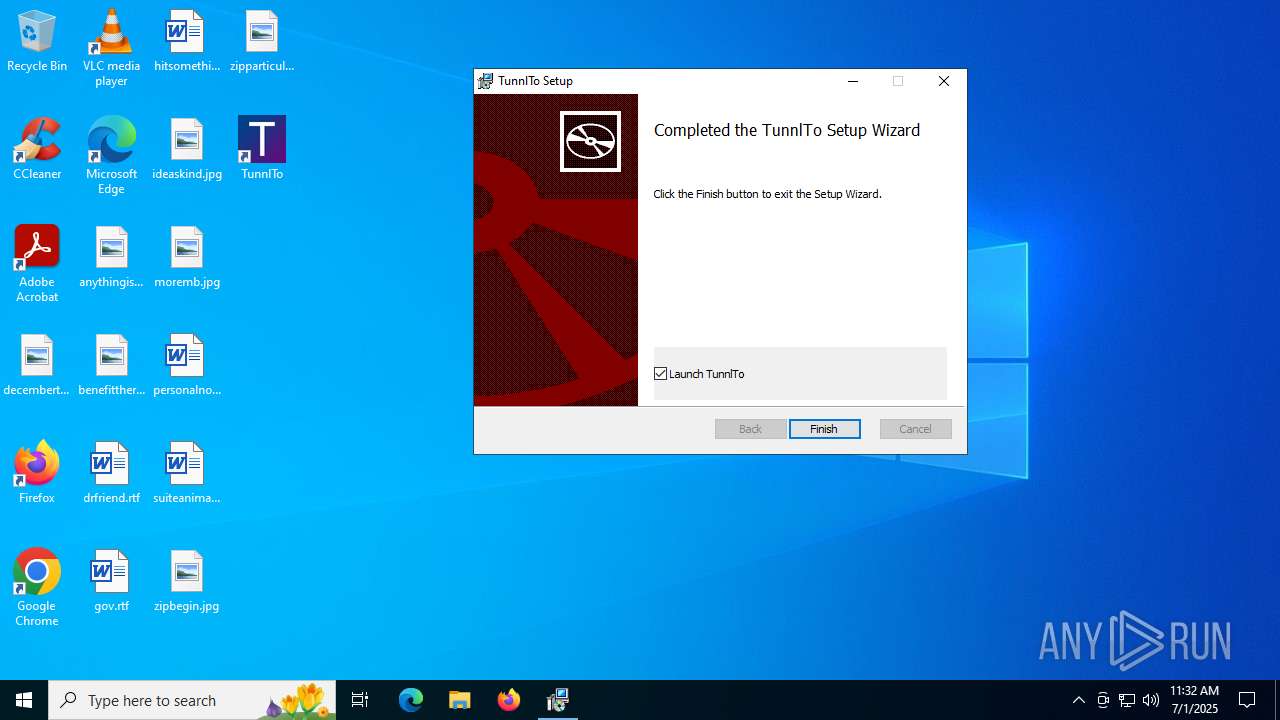
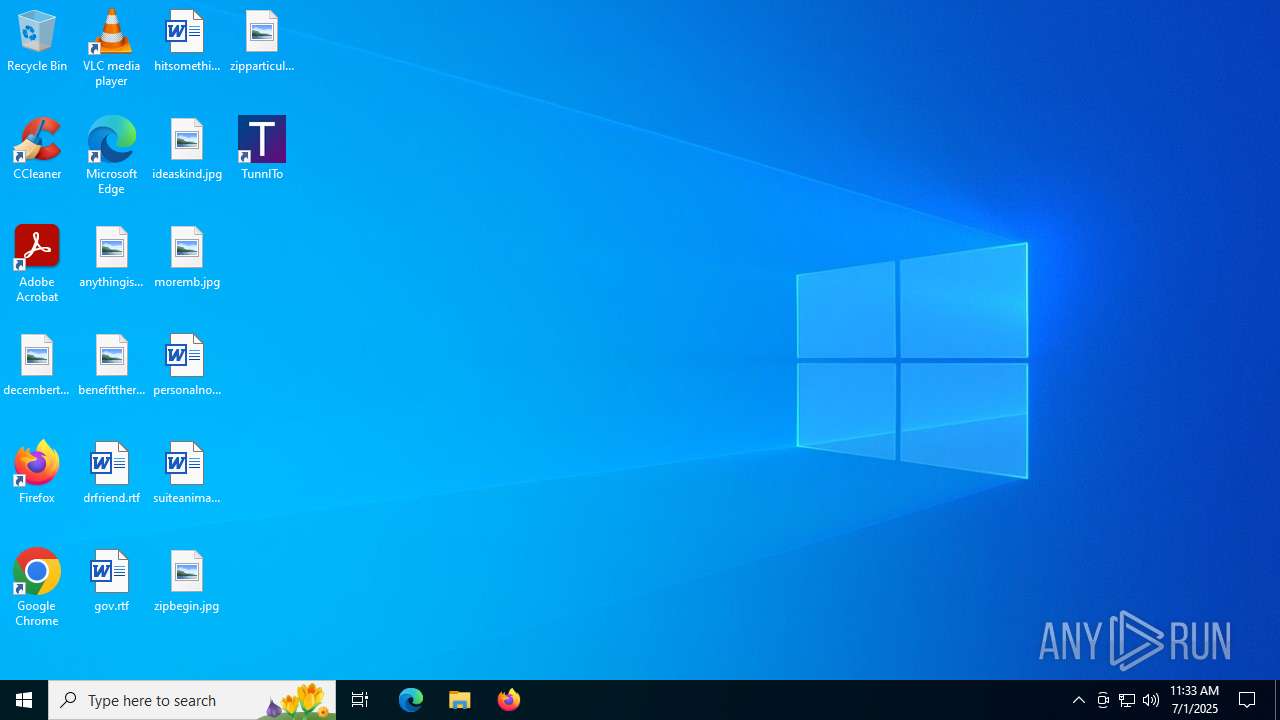
| File name: | TunnlTo_1.0.7_x64_en-US.msi |
| Full analysis: | https://app.any.run/tasks/a4ab862a-ee05-45cf-b64d-451330b4f9ee |
| Verdict: | Malicious activity |
| Analysis date: | July 01, 2025, 11:30:41 |
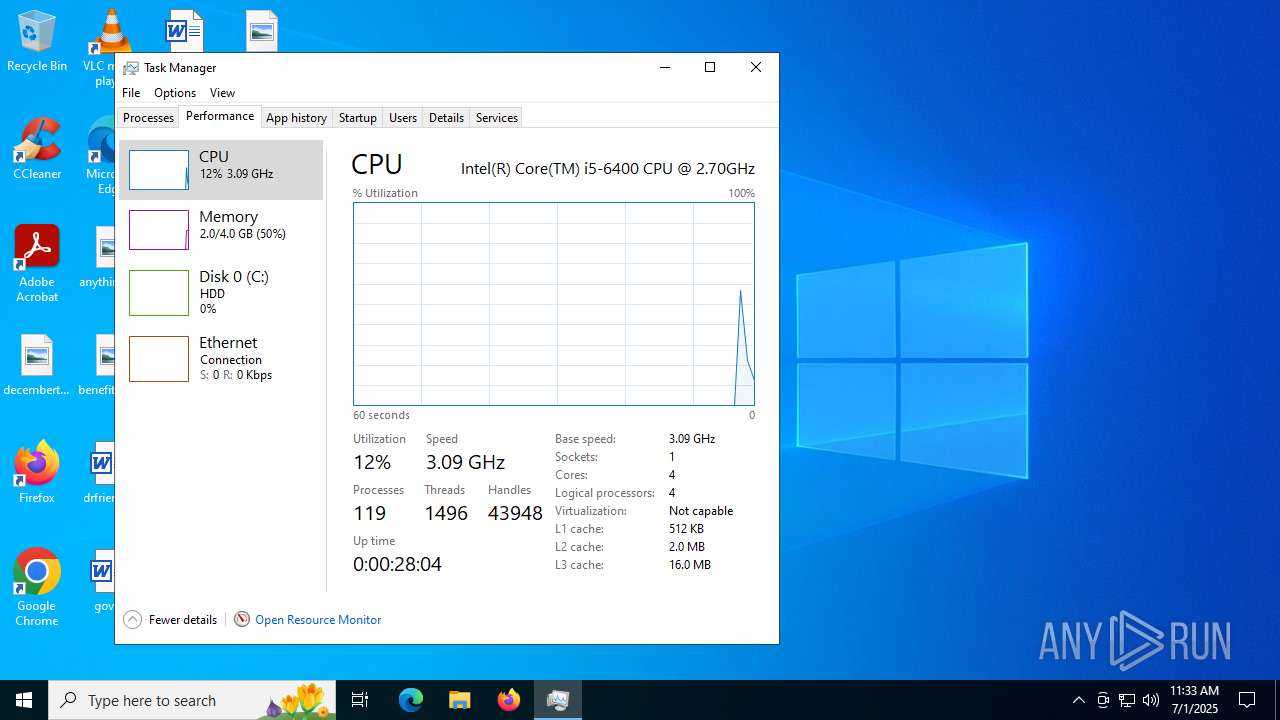
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, MSI Installer, Code page: 1252, Title: Installation Database, Subject: TunnlTo, Author: tunnl, Keywords: Installer, Comments: This installer database contains the logic and data required to install TunnlTo., Template: x64;0, Revision Number: {61FF8CDE-2F35-44D5-A379-E4CE8CE75A15}, Create Time/Date: Mon May 20 02:16:42 2024, Last Saved Time/Date: Mon May 20 02:16:42 2024, Number of Pages: 450, Number of Words: 2, Name of Creating Application: Windows Installer XML Toolset (3.11.2.4516), Security: 2 |
| MD5: | ABA32A1DCD826CFFEF0DD1832F0FC882 |
| SHA1: | DF44CD8BAF537D3543BE0D5AE2B773866DE502D8 |
| SHA256: | 2C4177EE75B4297E31EA834C1BD140FA7422C8F2049347141C2B83E8C255C48C |
| SSDEEP: | 98304:k2Lax6gp2bSMoRfkcYJ3faC2z5lRAEkRS1jx4ZvHBGu0gGw+XtY782Un6yXoDhxx:gz |
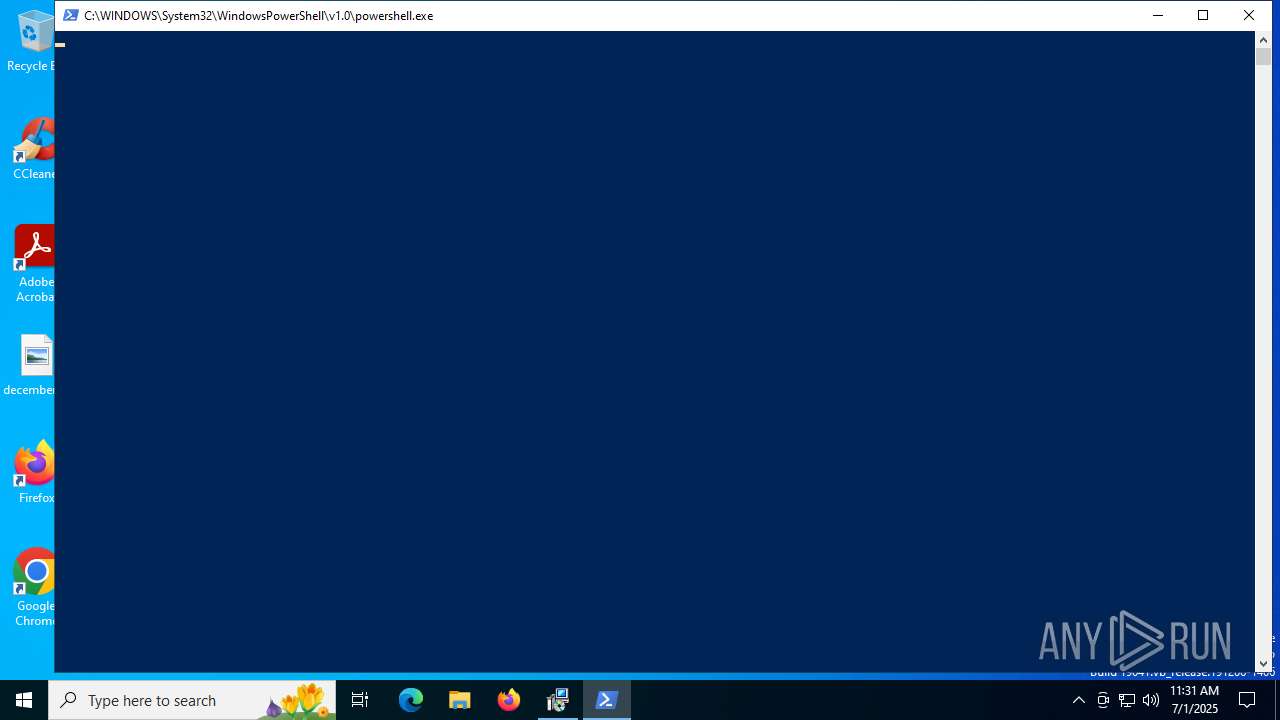
MALICIOUS
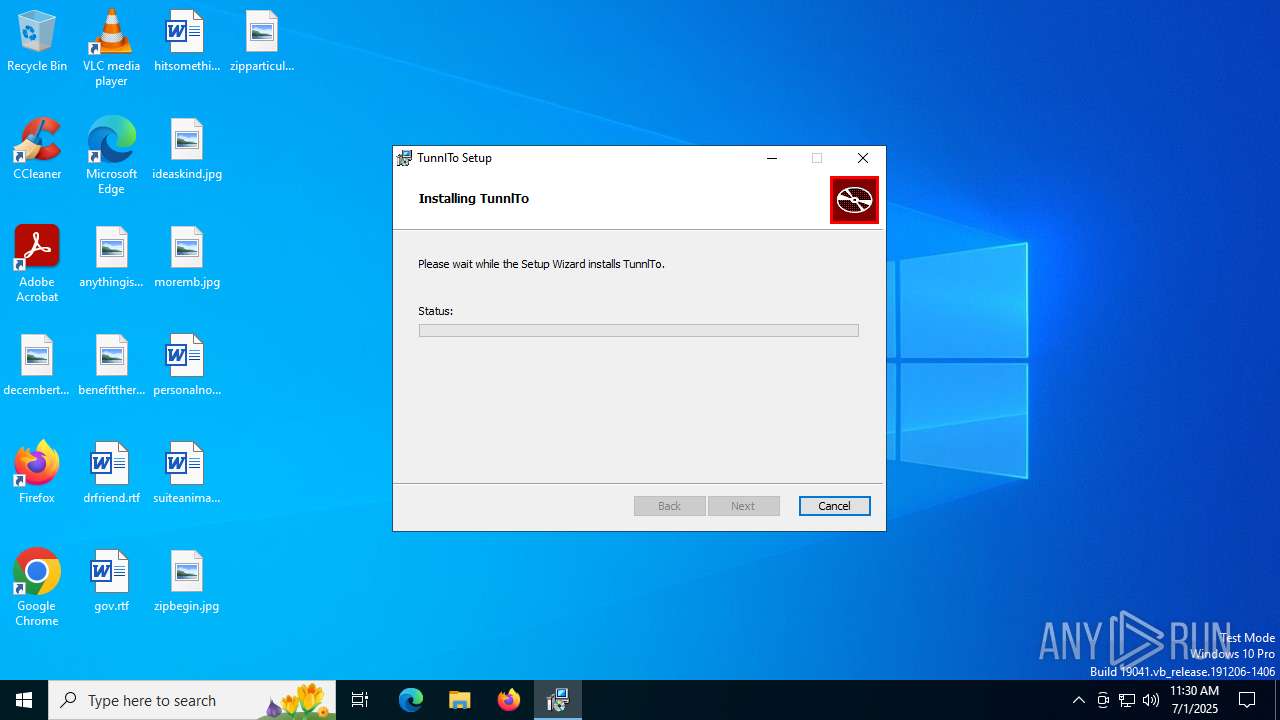
Run PowerShell with an invisible window
- powershell.exe (PID: 4312)
GENERIC has been found (auto)
- msiexec.exe (PID: 4948)
- netcfg.exe (PID: 2508)
- drvinst.exe (PID: 5020)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 2148)
The DLL Hijacking
- msedgewebview2.exe (PID: 2168)
- msedgewebview2.exe (PID: 7520)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 6724)
The process bypasses the loading of PowerShell profile settings
- msiexec.exe (PID: 4948)
Starts process via Powershell
- powershell.exe (PID: 4312)
- powershell.exe (PID: 5652)
- powershell.exe (PID: 7620)
Manipulates environment variables
- powershell.exe (PID: 4312)
Process drops legitimate windows executable
- msiexec.exe (PID: 4948)
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
- powershell.exe (PID: 4312)
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdge_X64_138.0.3351.55.exe (PID: 2804)
- setup.exe (PID: 1852)
- msedgewebview2.exe (PID: 8124)
- msedgewebview2.exe (PID: 4048)
Starts POWERSHELL.EXE for commands execution
- msiexec.exe (PID: 4948)
- TunnlTo.exe (PID: 4836)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4948)
Executable content was dropped or overwritten
- powershell.exe (PID: 4312)
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
- MicrosoftEdge_X64_138.0.3351.55.exe (PID: 2804)
- setup.exe (PID: 1852)
- netcfg.exe (PID: 2508)
- drvinst.exe (PID: 5020)
- drvinst.exe (PID: 6412)
- msedgewebview2.exe (PID: 8124)
- msedgewebview2.exe (PID: 4048)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
- MicrosoftEdgeUpdate.exe (PID: 2148)
Downloads file from URI via Powershell
- powershell.exe (PID: 4312)
Gets or sets the security protocol (POWERSHELL)
- powershell.exe (PID: 4312)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 2148)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdate.exe (PID: 5952)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6516)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4916)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4844)
Reads security settings of Internet Explorer
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- msiexec.exe (PID: 3948)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 7492)
Application launched itself
- MicrosoftEdgeUpdate.exe (PID: 4680)
- setup.exe (PID: 1852)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 7492)
Searches for installed software
- setup.exe (PID: 1852)
- TunnlTo.exe (PID: 4836)
- msedgewebview2.exe (PID: 6388)
- TunnlTo.exe (PID: 1332)
- msedgewebview2.exe (PID: 7492)
Creates a software uninstall entry
- setup.exe (PID: 1852)
Found IP address in command line
- powershell.exe (PID: 5652)
- powershell.exe (PID: 7620)
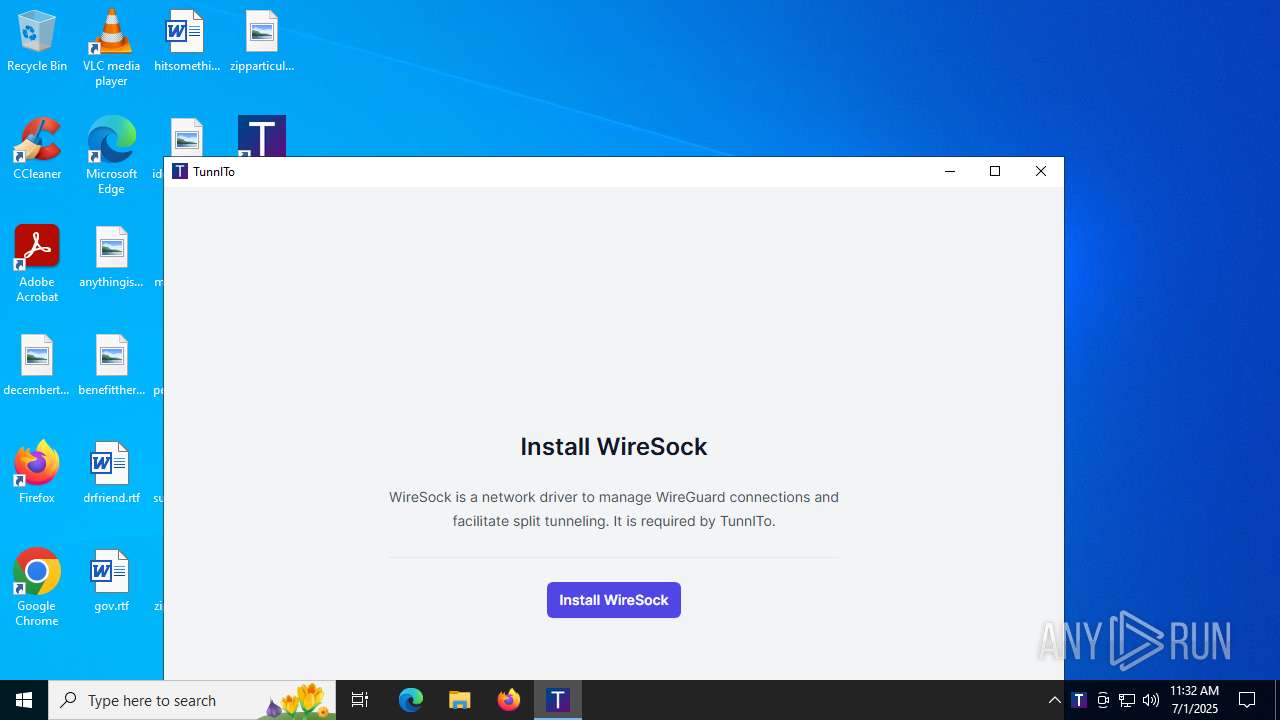
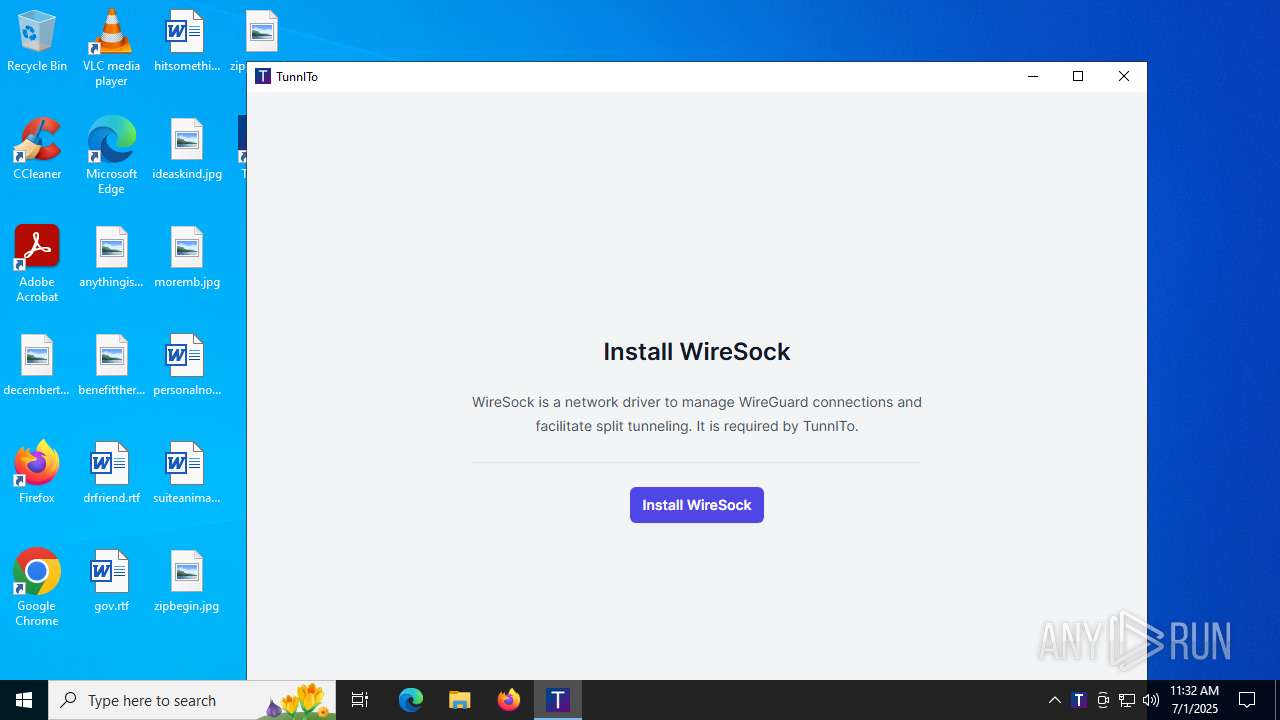
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 4948)
- drvinst.exe (PID: 5020)
- netcfg.exe (PID: 2508)
- drvinst.exe (PID: 6412)
Adds/modifies Windows certificates
- certutil.exe (PID: 2668)
- certutil.exe (PID: 4324)
Starts SC.EXE for service management
- msiexec.exe (PID: 4576)
Windows service management via SC.EXE
- sc.exe (PID: 856)
Creates files in the driver directory
- drvinst.exe (PID: 5020)
- drvinst.exe (PID: 6412)
- devcon.exe (PID: 2032)
Creates or modifies Windows services
- drvinst.exe (PID: 7216)
INFO
The sample compiled with english language support
- msiexec.exe (PID: 5980)
- msiexec.exe (PID: 4948)
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
- powershell.exe (PID: 4312)
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdge_X64_138.0.3351.55.exe (PID: 2804)
- setup.exe (PID: 1852)
- drvinst.exe (PID: 6412)
- msedgewebview2.exe (PID: 8124)
Checks proxy server information
- msiexec.exe (PID: 5980)
- powershell.exe (PID: 4312)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- MicrosoftEdgeUpdate.exe (PID: 4456)
- MicrosoftEdgeUpdate.exe (PID: 4264)
- msedgewebview2.exe (PID: 6388)
- TunnlTo.exe (PID: 4836)
- slui.exe (PID: 3636)
- msedgewebview2.exe (PID: 7492)
- TunnlTo.exe (PID: 1332)
Creates files or folders in the user directory
- msiexec.exe (PID: 5980)
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- MicrosoftEdge_X64_138.0.3351.55.exe (PID: 2804)
- setup.exe (PID: 1852)
- setup.exe (PID: 6772)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 5080)
- msedgewebview2.exe (PID: 4844)
- msedgewebview2.exe (PID: 7492)
- msedgewebview2.exe (PID: 7560)
- msedgewebview2.exe (PID: 5620)
Reads the software policy settings
- msiexec.exe (PID: 5980)
- msiexec.exe (PID: 4948)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- MicrosoftEdgeUpdate.exe (PID: 4456)
- MicrosoftEdgeUpdate.exe (PID: 4264)
- TunnlTo.exe (PID: 4836)
- drvinst.exe (PID: 5020)
- devcon.exe (PID: 2032)
- drvinst.exe (PID: 6412)
- slui.exe (PID: 3636)
- TunnlTo.exe (PID: 1332)
Checks supported languages
- msiexec.exe (PID: 4948)
- msiexec.exe (PID: 3948)
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdgeUpdate.exe (PID: 5952)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4844)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4916)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6516)
- MicrosoftEdgeUpdate.exe (PID: 4960)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- MicrosoftEdge_X64_138.0.3351.55.exe (PID: 2804)
- MicrosoftEdgeUpdate.exe (PID: 4456)
- setup.exe (PID: 1852)
- setup.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 6652)
- MicrosoftEdgeUpdateCore.exe (PID: 1752)
- MicrosoftEdgeUpdate.exe (PID: 4264)
- TunnlTo.exe (PID: 4836)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 5080)
- msedgewebview2.exe (PID: 2168)
- msedgewebview2.exe (PID: 4844)
- msedgewebview2.exe (PID: 6352)
- msedgewebview2.exe (PID: 6336)
- drvinst.exe (PID: 5020)
- msiexec.exe (PID: 4576)
- drvinst.exe (PID: 6412)
- devcon.exe (PID: 2032)
- drvinst.exe (PID: 7216)
- TunnlTo.exe (PID: 7816)
- TunnlTo.exe (PID: 7884)
- msedgewebview2.exe (PID: 8180)
- TunnlTo.exe (PID: 8040)
- TunnlTo.exe (PID: 8140)
- msedgewebview2.exe (PID: 7256)
- TunnlTo.exe (PID: 1332)
- msedgewebview2.exe (PID: 7484)
- msedgewebview2.exe (PID: 7492)
- msedgewebview2.exe (PID: 7560)
- msedgewebview2.exe (PID: 7584)
- msedgewebview2.exe (PID: 5432)
- msedgewebview2.exe (PID: 7520)
- msedgewebview2.exe (PID: 7404)
- msedgewebview2.exe (PID: 8144)
- msedgewebview2.exe (PID: 8124)
- msedgewebview2.exe (PID: 6528)
- msedgewebview2.exe (PID: 7984)
- msedgewebview2.exe (PID: 5620)
- msedgewebview2.exe (PID: 4048)
Reads the computer name
- msiexec.exe (PID: 4948)
- msiexec.exe (PID: 3948)
- MicrosoftEdgeUpdate.exe (PID: 2148)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6516)
- MicrosoftEdgeUpdate.exe (PID: 5952)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4844)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 4916)
- MicrosoftEdgeUpdate.exe (PID: 4960)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- MicrosoftEdge_X64_138.0.3351.55.exe (PID: 2804)
- MicrosoftEdgeUpdate.exe (PID: 4456)
- MicrosoftEdgeUpdateCore.exe (PID: 1752)
- MicrosoftEdgeUpdate.exe (PID: 6652)
- setup.exe (PID: 1852)
- MicrosoftEdgeUpdate.exe (PID: 4264)
- TunnlTo.exe (PID: 4836)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 2168)
- msedgewebview2.exe (PID: 4844)
- msiexec.exe (PID: 4576)
- drvinst.exe (PID: 5020)
- devcon.exe (PID: 2032)
- drvinst.exe (PID: 6412)
- drvinst.exe (PID: 7216)
- TunnlTo.exe (PID: 1332)
- msedgewebview2.exe (PID: 7492)
- msedgewebview2.exe (PID: 7560)
- msedgewebview2.exe (PID: 7520)
- msedgewebview2.exe (PID: 5620)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5980)
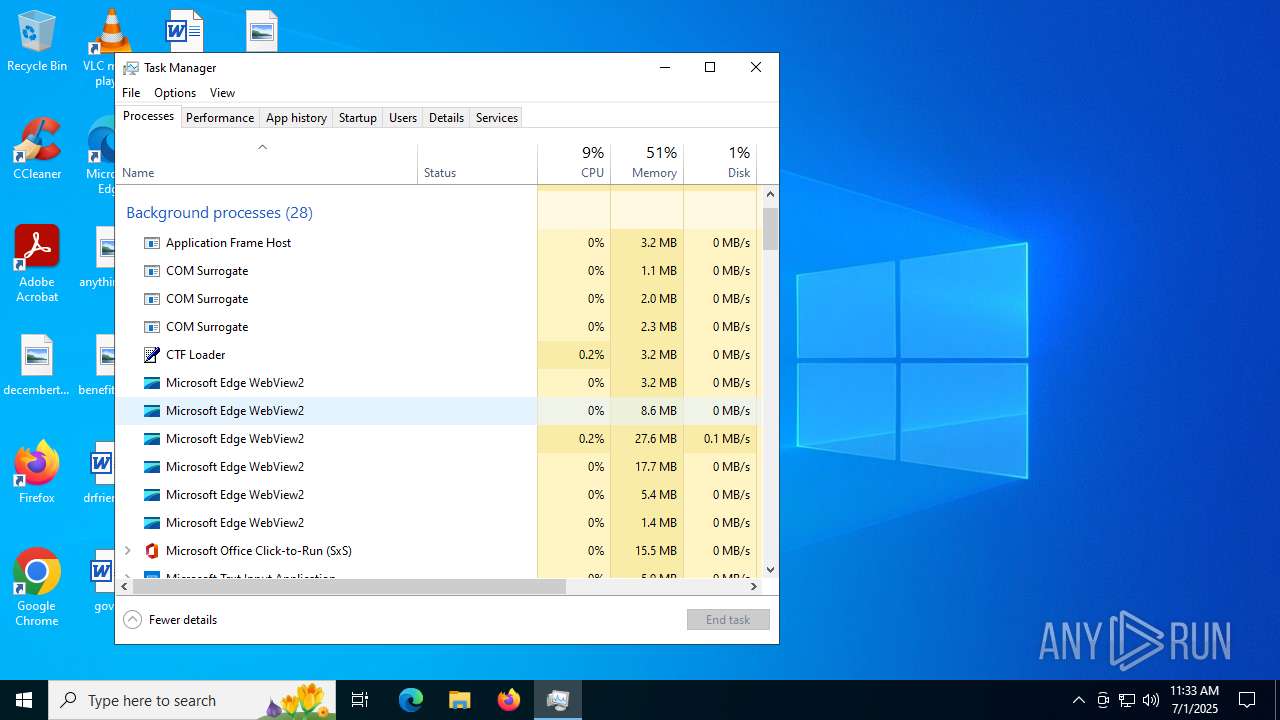
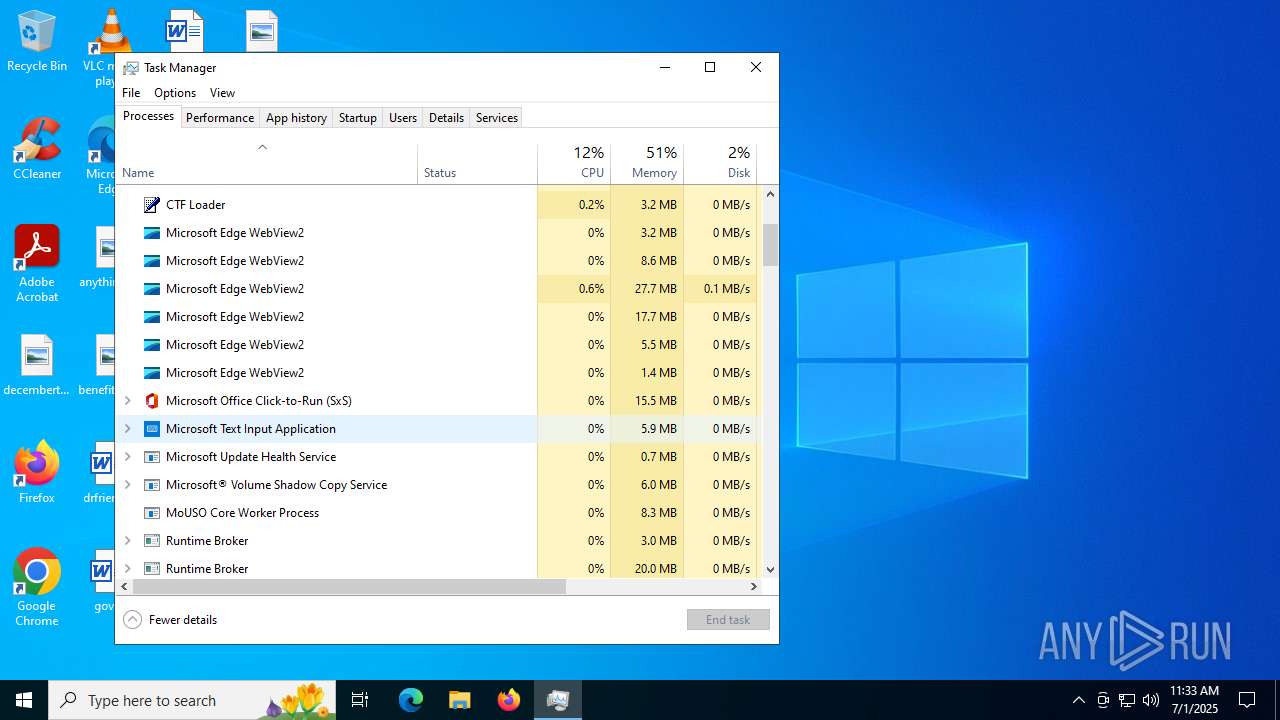
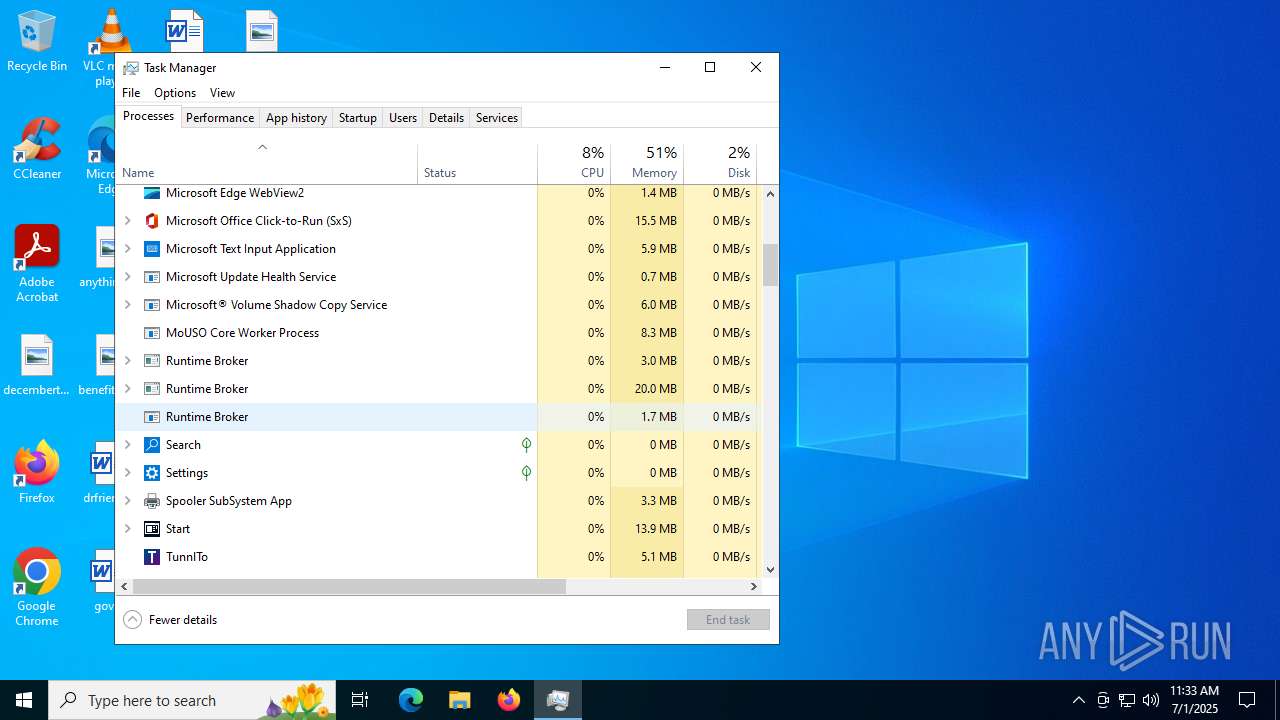
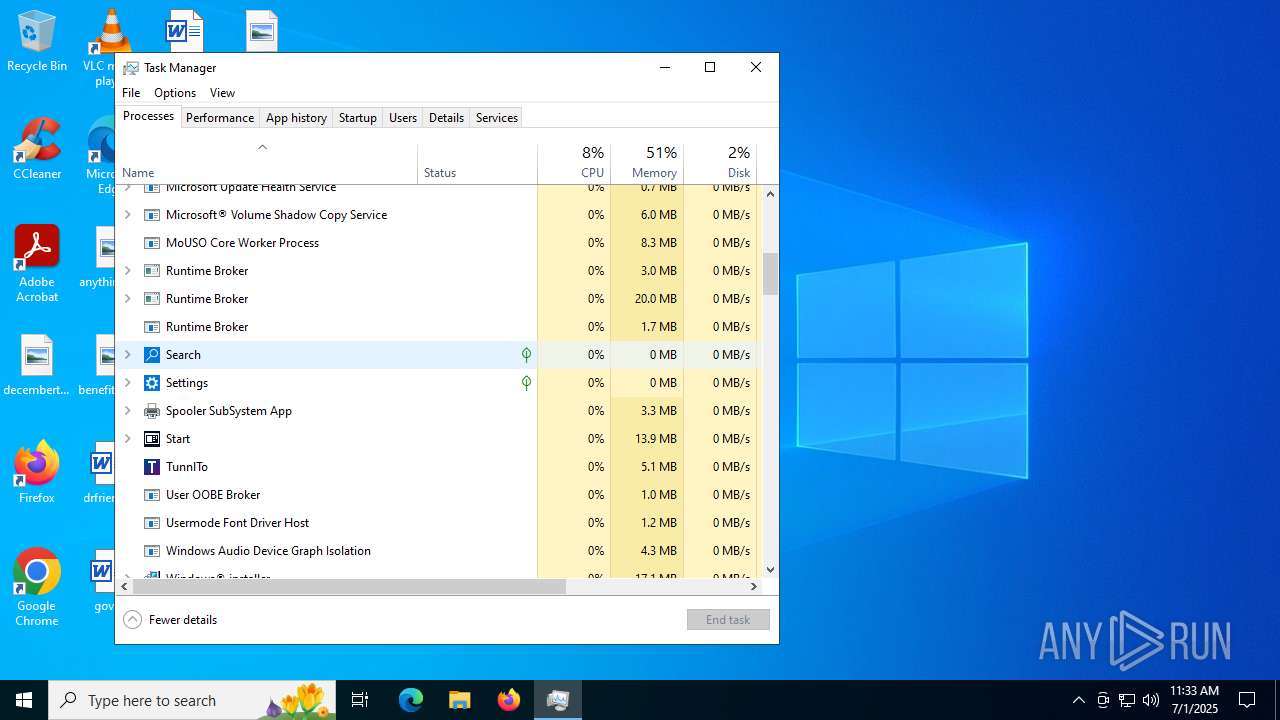
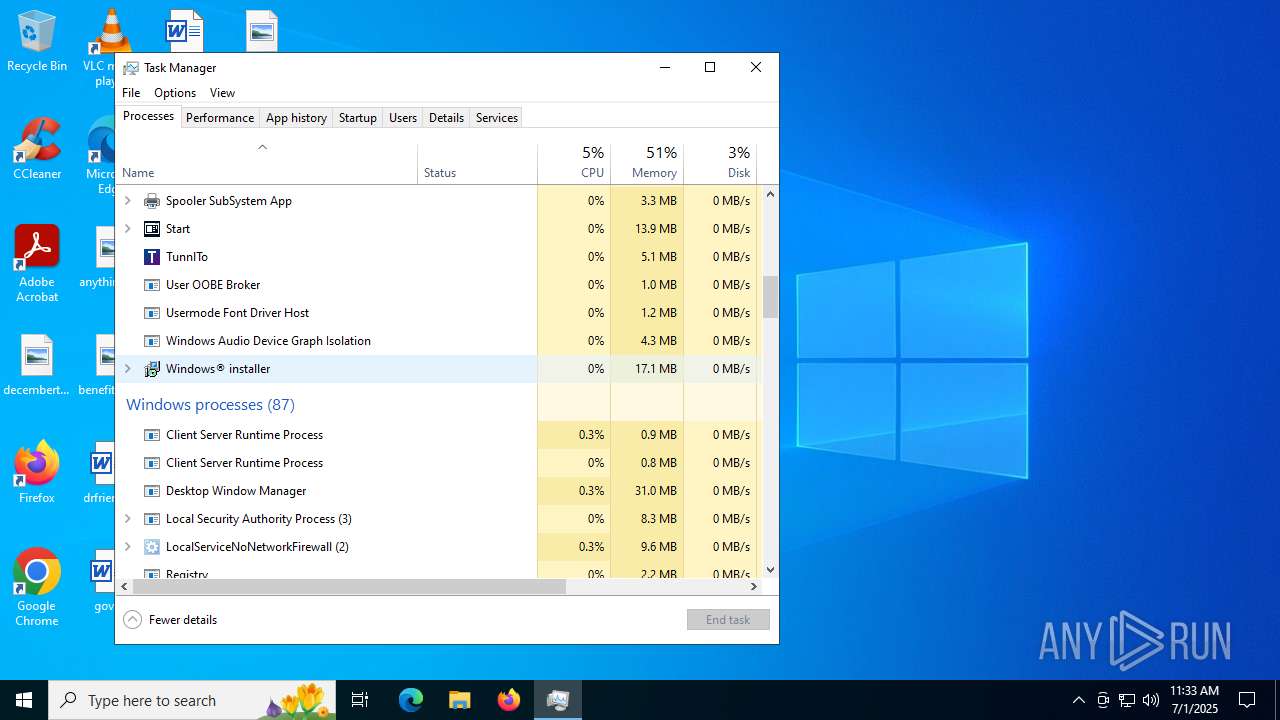
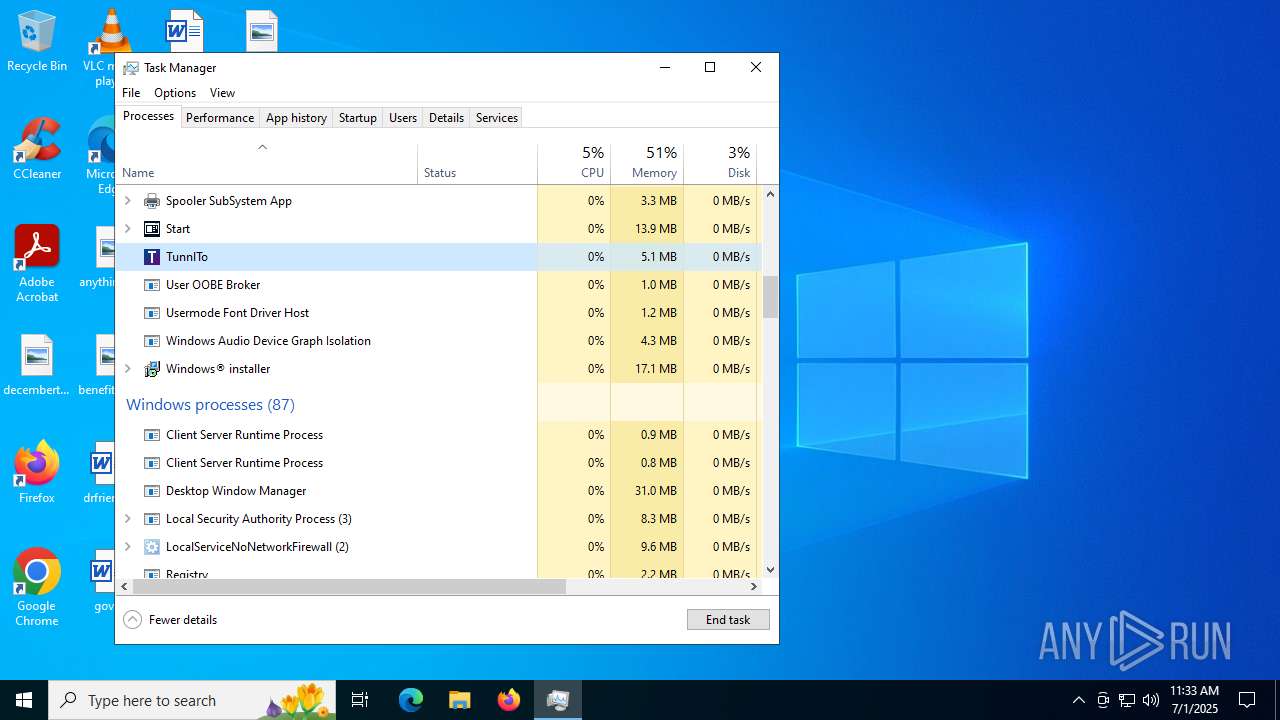
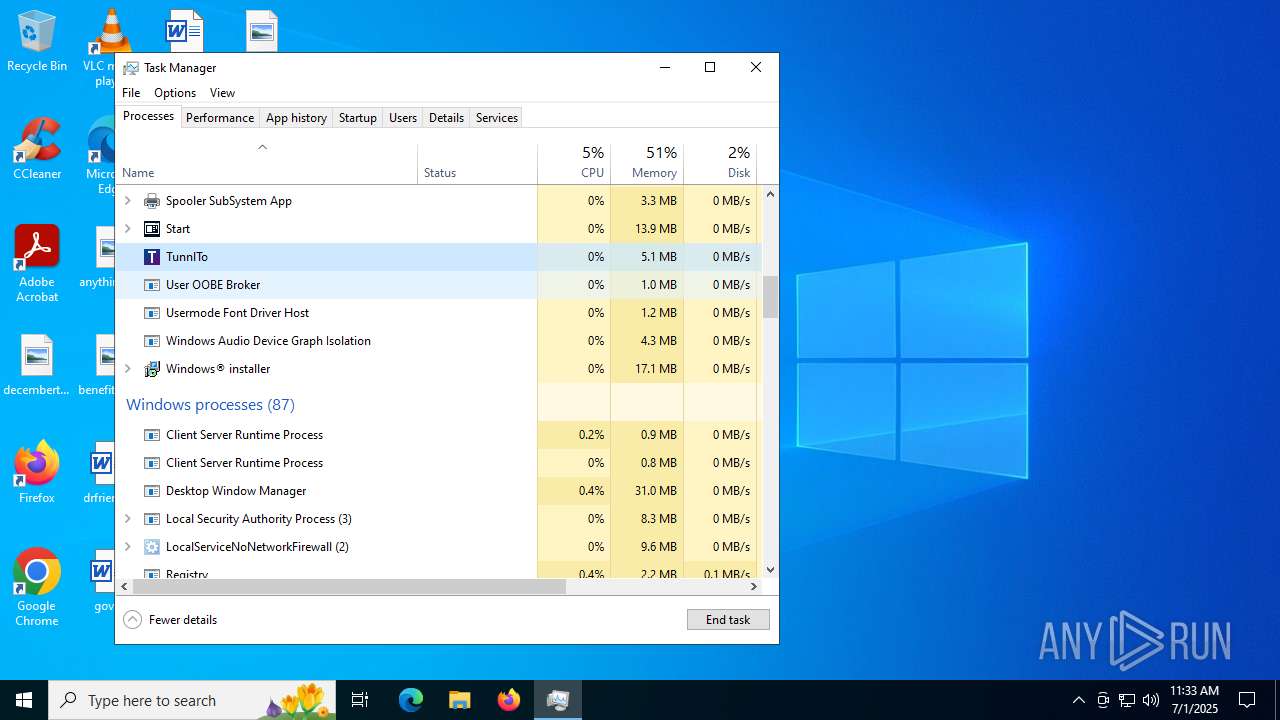
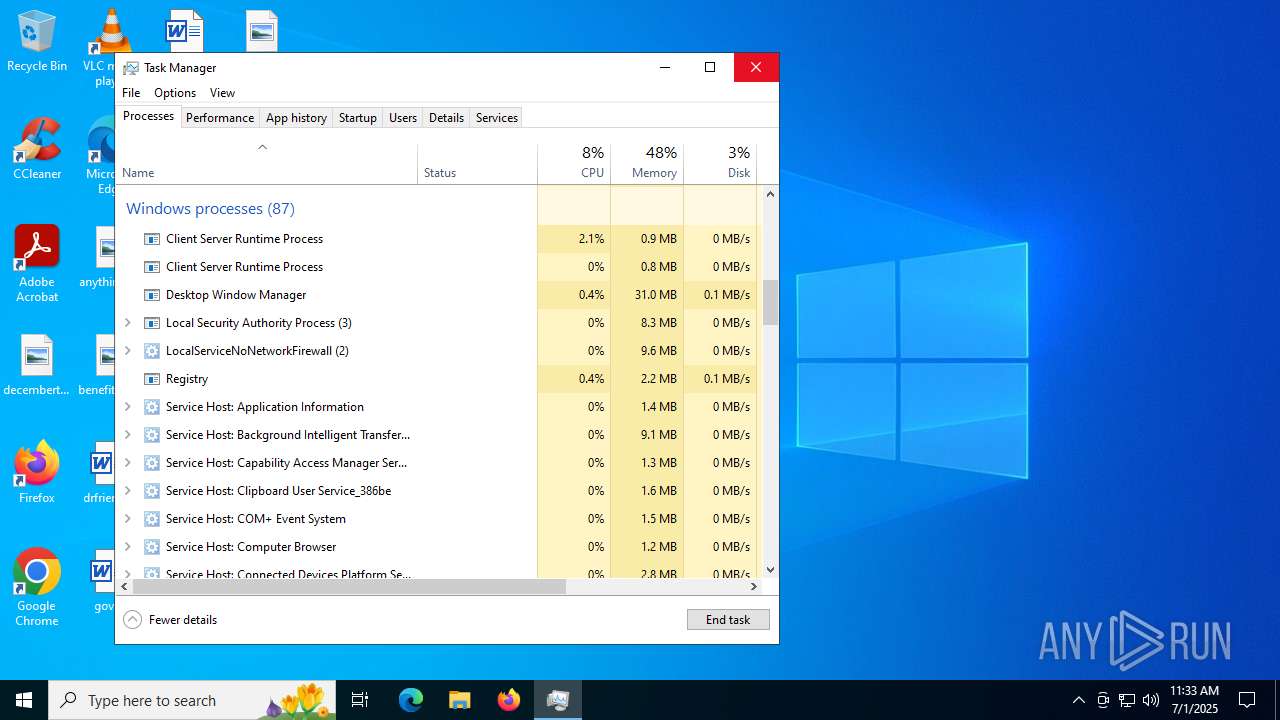
- Taskmgr.exe (PID: 7216)
Manages system restore points
- SrTasks.exe (PID: 2032)
- SrTasks.exe (PID: 1564)
Executable content was dropped or overwritten
- msiexec.exe (PID: 5980)
- msiexec.exe (PID: 4948)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4948)
- MicrosoftEdgeUpdate.exe (PID: 4680)
- msedgewebview2.exe (PID: 6388)
- drvinst.exe (PID: 5020)
- devcon.exe (PID: 2032)
- drvinst.exe (PID: 6412)
- msedgewebview2.exe (PID: 7492)
- msedgewebview2.exe (PID: 5620)
Creates a software uninstall entry
- msiexec.exe (PID: 4948)
The executable file from the user directory is run by the Powershell process
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
Create files in a temporary directory
- MicrosoftEdgeWebview2Setup.exe (PID: 1632)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 7492)
Disables trace logs
- powershell.exe (PID: 4312)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 2148)
Reads Environment values
- MicrosoftEdgeUpdate.exe (PID: 4456)
- MicrosoftEdgeUpdate.exe (PID: 4264)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 7492)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 2148)
- setup.exe (PID: 1852)
- msiexec.exe (PID: 3948)
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 6336)
- msedgewebview2.exe (PID: 7492)
- msedgewebview2.exe (PID: 5432)
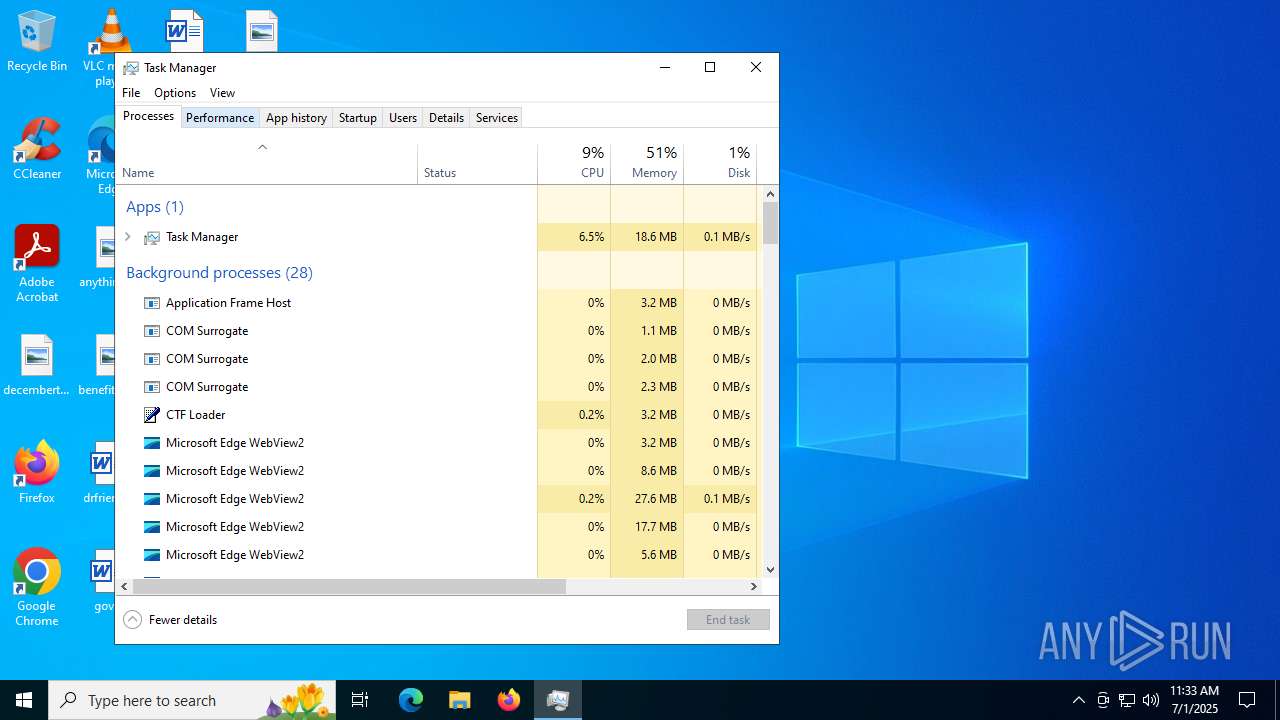
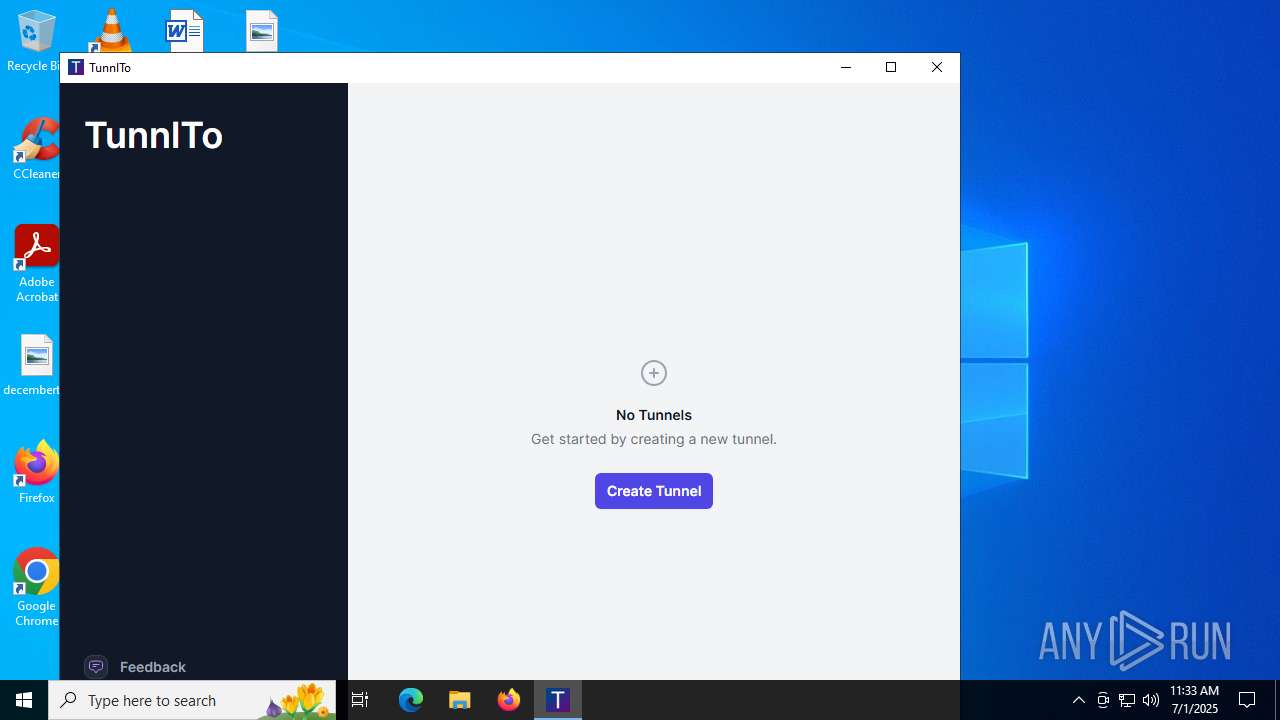
Manual execution by a user
- MicrosoftEdgeUpdateCore.exe (PID: 1752)
- TunnlTo.exe (PID: 8040)
- TunnlTo.exe (PID: 7816)
- TunnlTo.exe (PID: 7884)
- Taskmgr.exe (PID: 7216)
- TunnlTo.exe (PID: 8140)
- Taskmgr.exe (PID: 3100)
- TunnlTo.exe (PID: 1332)
Creates files in the driver directory
- netcfg.exe (PID: 2508)
Reads CPU info
- msedgewebview2.exe (PID: 6388)
- msedgewebview2.exe (PID: 7492)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 5652)
- powershell.exe (PID: 7620)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (98.5) |
|---|---|---|
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| CodePage: | Windows Latin 1 (Western European) |
|---|---|
| Title: | Installation Database |
| Subject: | TunnlTo |
| Author: | tunnl |
| Keywords: | Installer |
| Comments: | This installer database contains the logic and data required to install TunnlTo. |
| Template: | x64;0 |
| RevisionNumber: | {61FF8CDE-2F35-44D5-A379-E4CE8CE75A15} |
| CreateDate: | 2024:05:20 02:16:42 |
| ModifyDate: | 2024:05:20 02:16:42 |
| Pages: | 450 |
| Words: | 2 |
| Software: | Windows Installer XML Toolset (3.11.2.4516) |
| Security: | Read-only recommended |
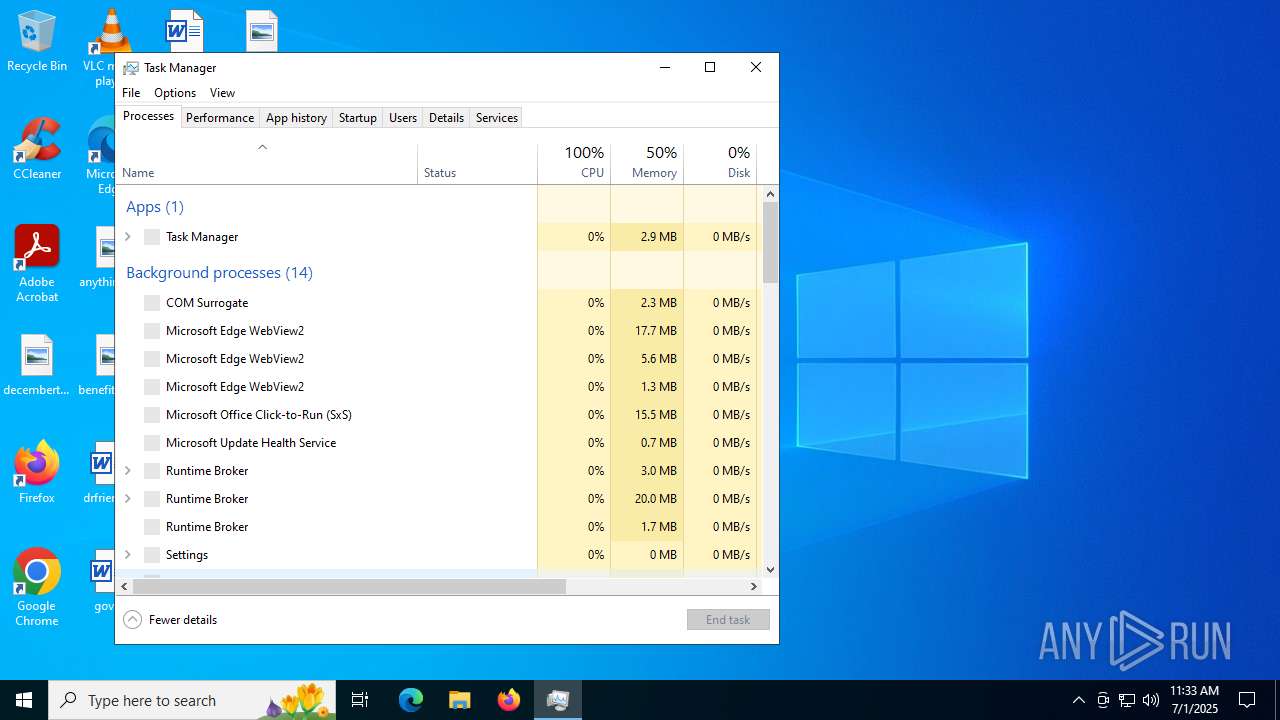
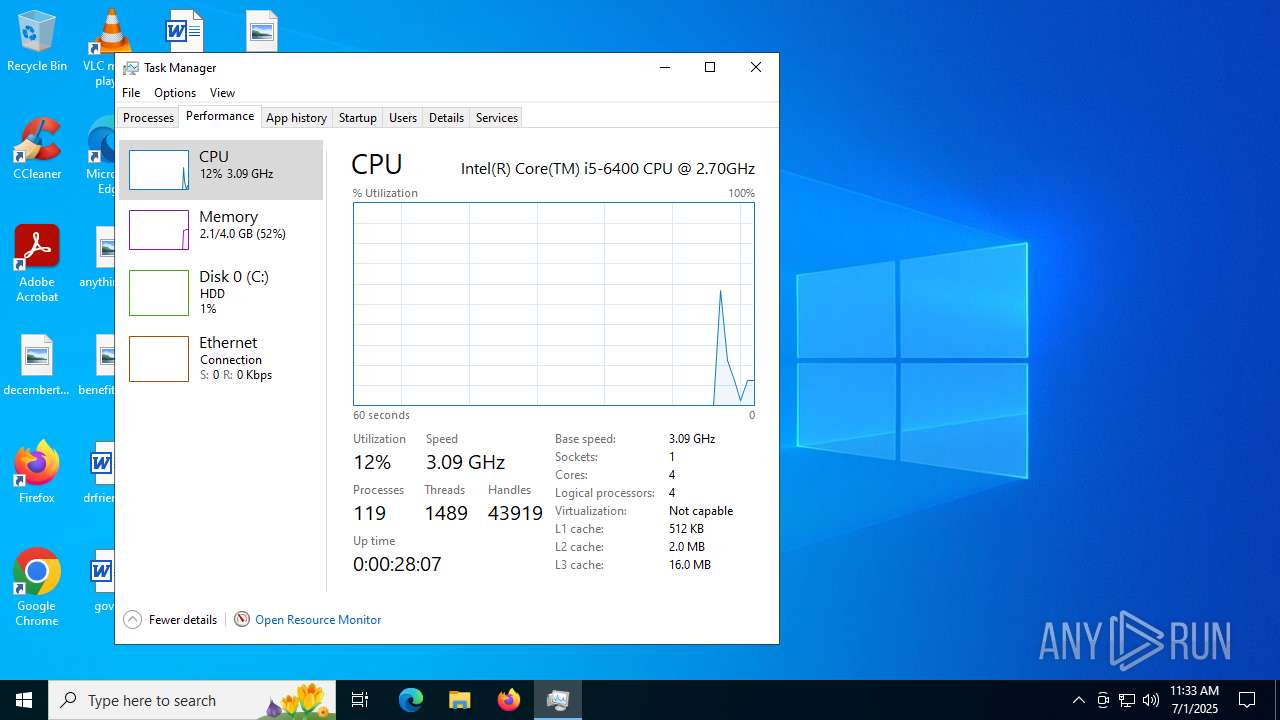
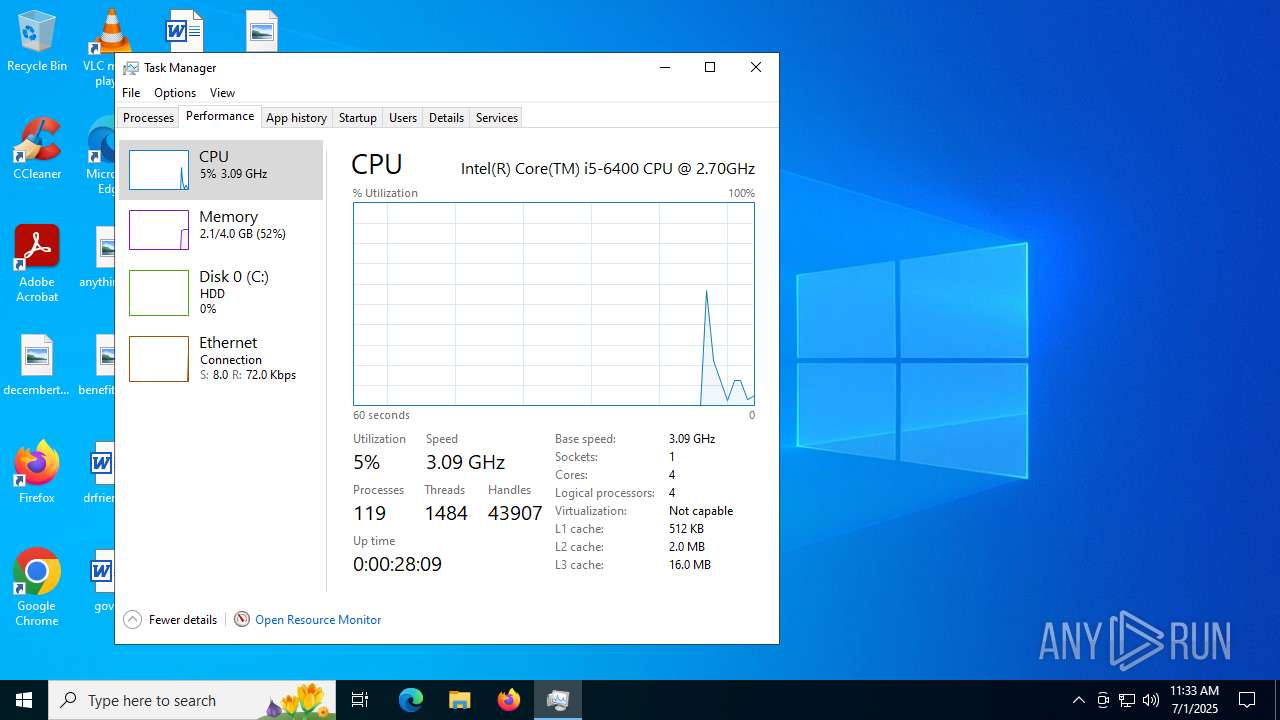
Total processes
240
Monitored processes
75
Malicious processes
16
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 856 | "C:\WINDOWS\system32\sc.exe" query ndiswgc | C:\Windows\System32\sc.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | sc.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1332 | "C:\Program Files\TunnlTo\TunnlTo.exe" | C:\Program Files\TunnlTo\TunnlTo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: TunnlTo Version: 1.0.7 Modules
| |||||||||||||||
| 1440 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | certutil.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:12 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1632 | "C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe" /silent /install | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Setup Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1752 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateCore.exe" | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\1.3.195.61\MicrosoftEdgeUpdateCore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1852 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{3DCB48DA-3538-48F4-AE56-273963108EEE}\EDGEMITMP_988CB.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{3DCB48DA-3538-48F4-AE56-273963108EEE}\MicrosoftEdge_X64_138.0.3351.55.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{3DCB48DA-3538-48F4-AE56-273963108EEE}\EDGEMITMP_988CB.tmp\setup.exe | MicrosoftEdge_X64_138.0.3351.55.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 138.0.3351.55 Modules
| |||||||||||||||
| 2032 | C:\WINDOWS\system32\srtasks.exe ExecuteScopeRestorePoint /WaitForRestorePoint:11 | C:\Windows\System32\SrTasks.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Windows System Protection background tasks. Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2032 | "C:\Program Files\WireSock VPN Client\wiresock-adapter\devcon.exe" install "C:\Program Files\WireSock VPN Client\wiresock-adapter\wiresock.inf" wiresock | C:\Program Files\WireSock VPN Client\wiresock-adapter\devcon.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Device Console Exit code: 0 Version: 10.0.19041.685 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
55 849
Read events
53 540
Write events
2 183
Delete events
126
Modification events
| (PID) Process: | (4948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000B252889A7BEADB0154130000DC140000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4948) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000B252889A7BEADB0154130000DC140000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{9dea862c-5cdd-4e70-acc1-f32b344d4795}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Microsoft\Boot\bootmgfw.efi | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | write | Name: | Element |
Value: 0000000000000000000000000000000006000000000000004800000000000000715E5C2FA985EB1190A89A9B763584210000000000000000745E5C2FA985EB1190A89A9B7635842100000000000000000000000000000000 | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (6724) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\12000002 |
| Operation: | write | Name: | Element |
Value: \EFI\Boot\Loader.efi | |||
Executable files
230
Suspicious files
249
Text files
77
Unknown types
87
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4948 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4948 | msiexec.exe | C:\Windows\Installer\178973.msi | — | |
MD5:— | SHA256:— | |||
| 5980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B039FEA45CB4CC4BBACFC013C7C55604_50385F8EB1F713E33924A830D7A2A41C | binary | |
MD5:37EF0645473C52EB0D6601BFEB92D710 | SHA256:63FE49C285BC31DCDCBA75D3A91DB41DF18F507066A609C13E9BF11A64709EEA | |||
| 5980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\357F04AD41BCF5FE18FCB69F60C6680F_CBBFF7A51C21E740C38443A74DDFD727 | der | |
MD5:56455A1BB3B06ACD497FCC207343D78A | SHA256:BC65B887D459E87D276131AAB5546B9AB0489F22DF05E7F7D87B190A4113815F | |||
| 5980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | der | |
MD5:EFB8E5790499D1CE7E531653DAB86456 | SHA256:CAC3A9C53E1923477F2347D2B4696725129309A9353B2973A0D13BB3FDF24AE6 | |||
| 5980 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI5A07.tmp | executable | |
MD5:4FDD16752561CF585FED1506914D73E0 | SHA256:AECD2D2FE766F6D439ACC2BBF1346930ECC535012CF5AD7B3273D2875237B7E7 | |||
| 4948 | msiexec.exe | C:\Windows\Installer\178975.msi | — | |
MD5:— | SHA256:— | |||
| 5980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\9CB4373A4252DE8D2212929836304EC5_1AB74AA2E3A56E1B8AD8D3FEC287554E | binary | |
MD5:3C17BE30DB9CFC6EB488A7AB90BA87CA | SHA256:CAAA58EEC934D72FA43837EBB253ABCAC989620E177C57A756CB4599F4707E51 | |||
| 5980 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\357F04AD41BCF5FE18FCB69F60C6680F_CBBFF7A51C21E740C38443A74DDFD727 | binary | |
MD5:7F615315456EF54B2C89122022D8F231 | SHA256:225E5C45B46E1277D268532F9D9A43A9B93359526578D2C00BE390CF7D1C4232 | |||
| 4948 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{6c69c31a-fdae-4187-8c1c-6559eeff3565}_OnDiskSnapshotProp | binary | |
MD5:710ECA4B4D6F490BAFEB6A7AC56CC815 | SHA256:14A7A7C7437791E65052413390E3F9C43B92485E8A2EB091AF94DA4C87E15105 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
65
DNS requests
48
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5980 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr3/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCEHgDGEJFcIpBz28BuO60qVQ%3D | unknown | — | — | whitelisted |
5980 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | — | — | whitelisted |
5980 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
5980 | msiexec.exe | GET | 200 | 151.101.2.133:80 | http://ocsp.globalsign.com/gsgccr45evcodesignca2020/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBQaCbVYh07WONuW4e63Ydlu4AlbDAQUJZ3Q%2FFkJhmPF7POxEztXHAOSNhECDDIt6H%2BXfAETa93iEg%3D%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
1964 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1328 | svchost.exe | GET | — | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/f030c6f8-6fe0-478a-a949-e9fea166a192?P1=1751974275&P2=404&P3=2&P4=Fcu%2bNW8y6rHRdqt1QWJS0AznmmBBR8XJ9XKQwbvL63wwbzS0KAlYahiCgHyYmWvdJTYDvA%2fDWRulDGDq1nKjOQ%3d%3d | unknown | — | — | whitelisted |
1328 | svchost.exe | HEAD | 200 | 199.232.210.172:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/f030c6f8-6fe0-478a-a949-e9fea166a192?P1=1751974275&P2=404&P3=2&P4=Fcu%2bNW8y6rHRdqt1QWJS0AznmmBBR8XJ9XKQwbvL63wwbzS0KAlYahiCgHyYmWvdJTYDvA%2fDWRulDGDq1nKjOQ%3d%3d | unknown | — | — | whitelisted |
1752 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2432 | RUXIMICS.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5980 | msiexec.exe | 151.101.2.133:80 | ocsp.globalsign.com | FASTLY | US | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1964 | svchost.exe | 20.190.160.65:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
ocsp.globalsign.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1328 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\com.tunnl.to directory exists )
|
TunnlTo.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |
TunnlTo.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Local\com.tunnl.to\EBWebView directory exists )
|
TunnlTo.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |
TunnlTo.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |