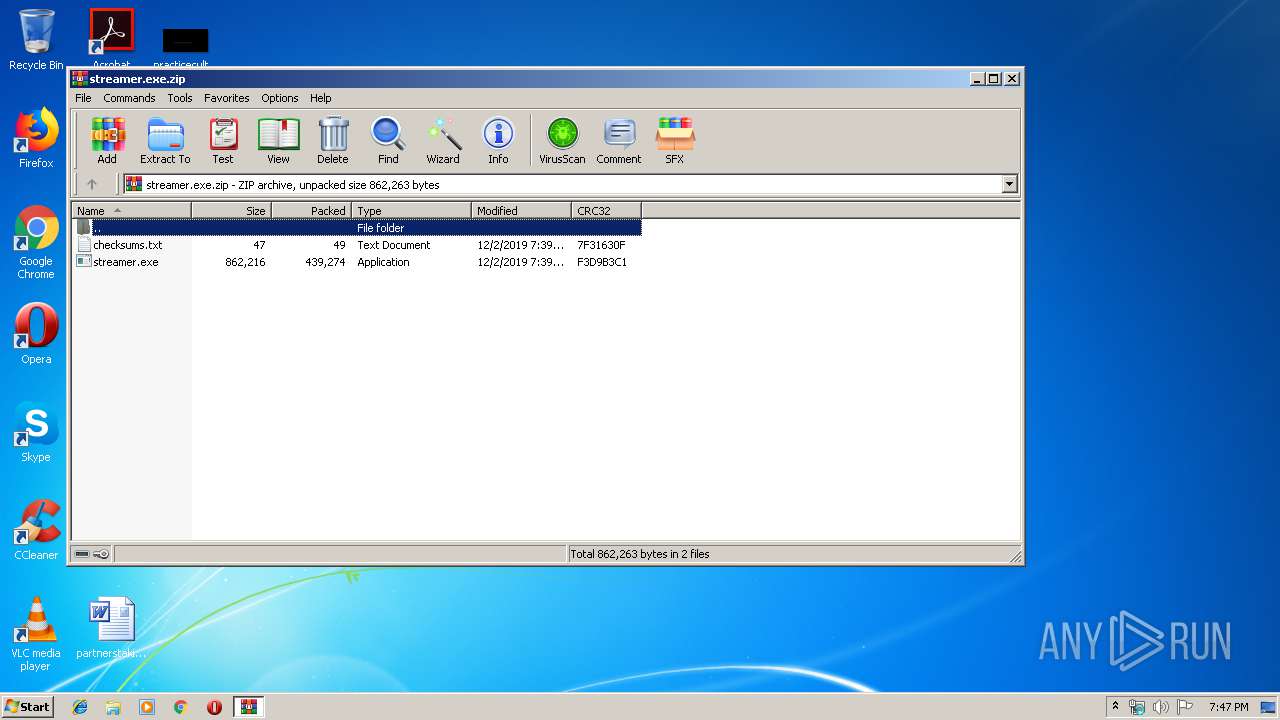
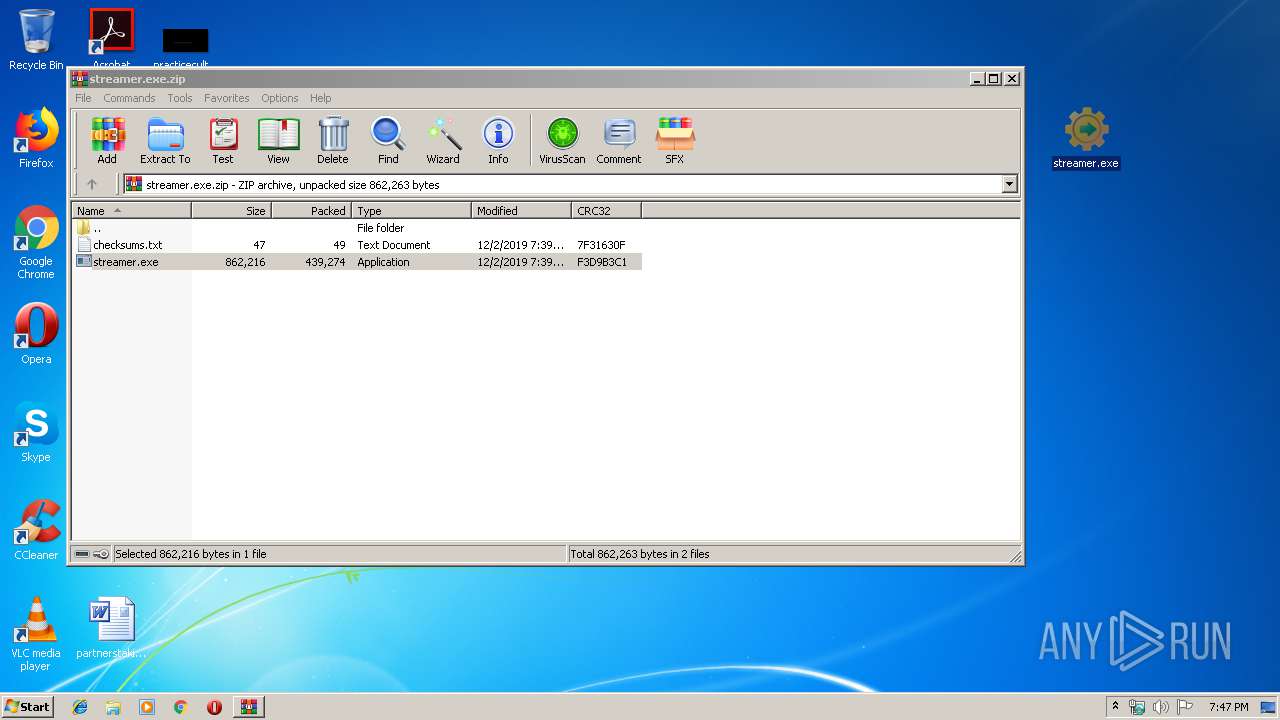
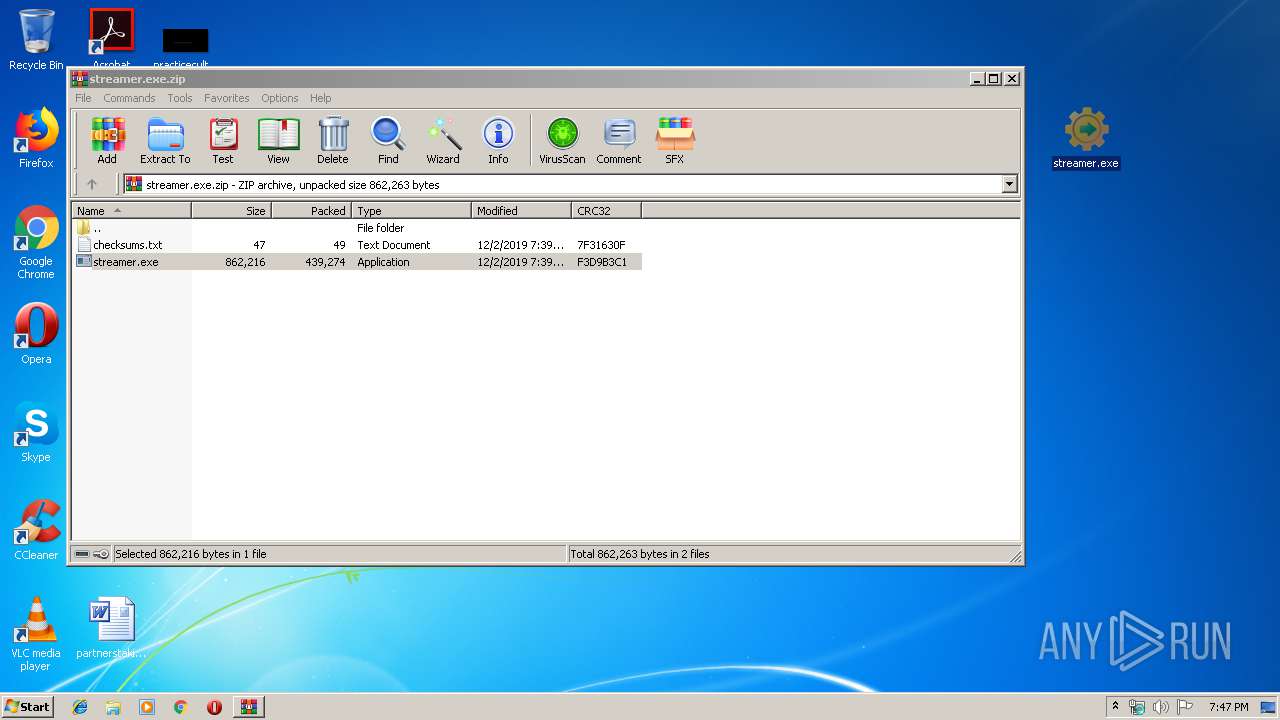
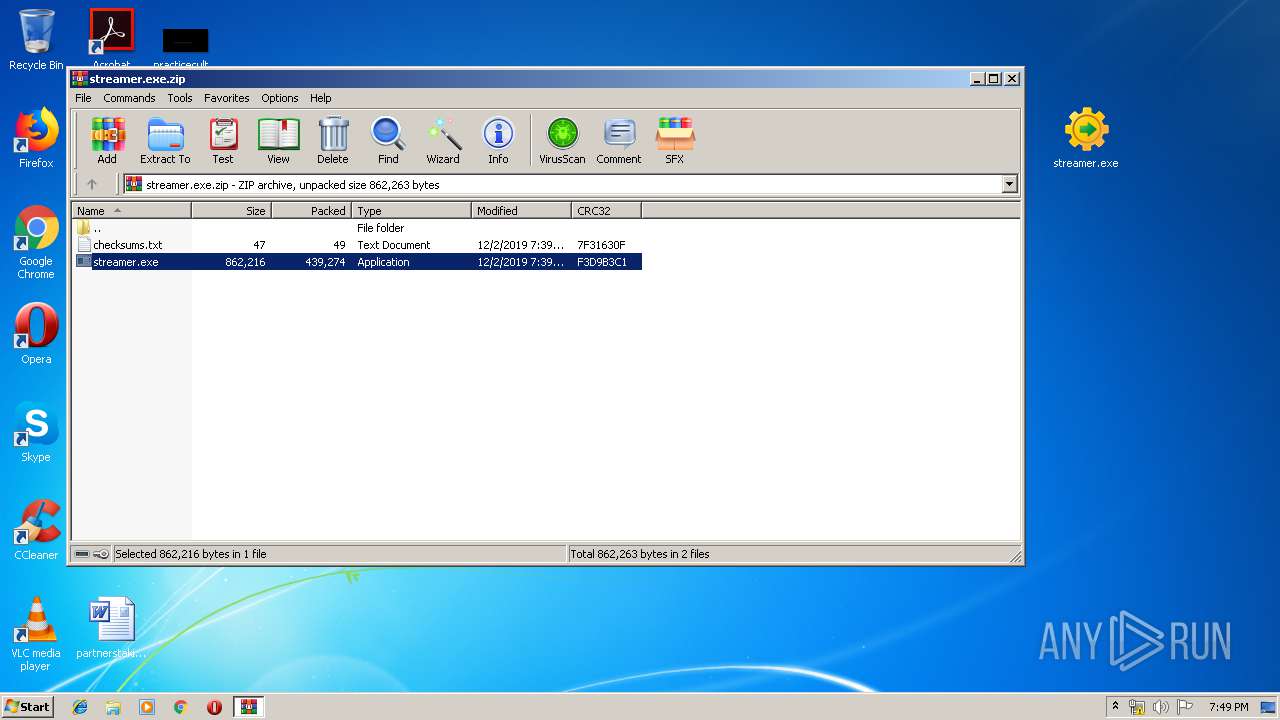
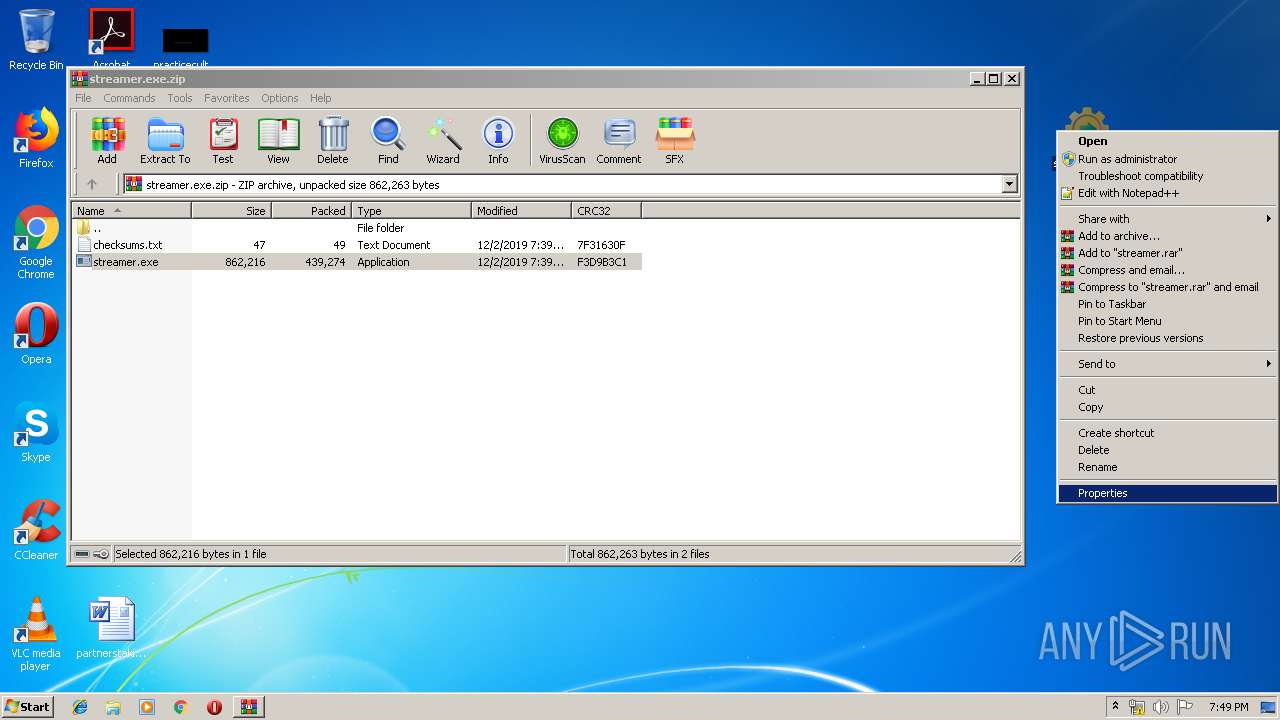
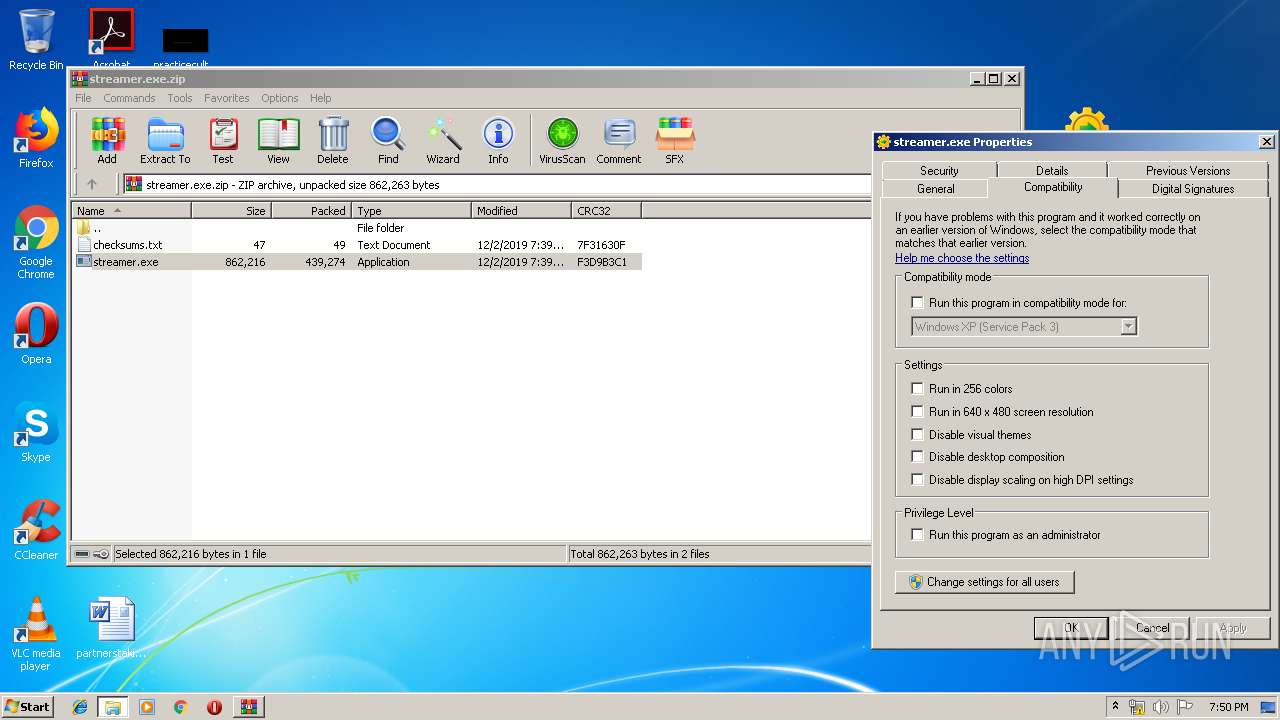
| File name: | streamer.exe.zip |
| Full analysis: | https://app.any.run/tasks/259c252c-9219-4873-ad34-947845238592 |
| Verdict: | Malicious activity |
| Analysis date: | December 02, 2019, 19:47:15 |
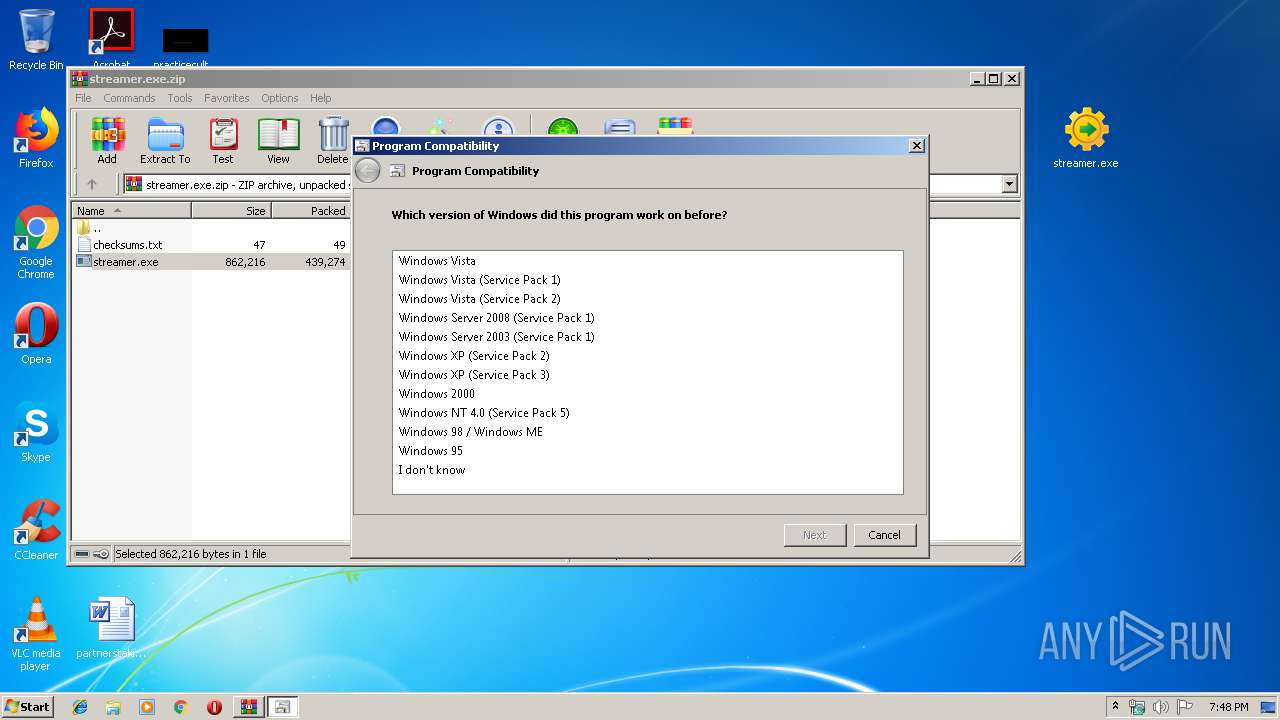
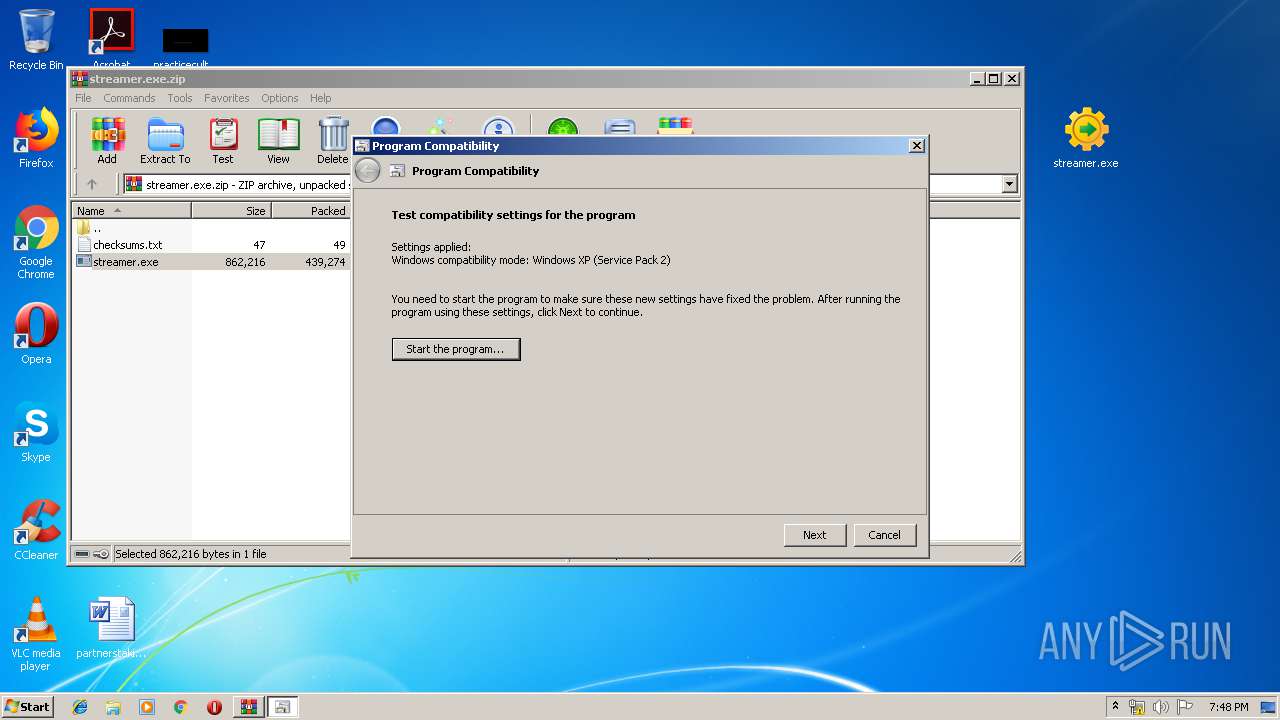
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 9128DF388886D65336CBF242DED529AE |
| SHA1: | B6D51FC987C8BAF30F972809D4359305BEF0389A |
| SHA256: | 2C06A3F5FF262B96D7CC4132C9D1743FBCFF146135404B23B2C43A6AEF62C36B |
| SSDEEP: | 12288:RZ16PCVK55cc2y+OJ4A/U23RhdtXFwcY2+1tFvOh52yin0tXc:r16PCIUgbUYREc3+vEmyin0tM |
MALICIOUS
Starts Visual C# compiler
- sdiagnhost.exe (PID: 516)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2388)
- rundll32.exe (PID: 928)
- rundll32.exe (PID: 584)
- rundll32.exe (PID: 2152)
- rundll32.exe (PID: 1096)
- rundll32.exe (PID: 3800)
Application was dropped or rewritten from another process
- streamer.exe (PID: 2488)
- streamer.exe (PID: 2336)
- streamer.exe (PID: 3400)
- streamer.exe (PID: 3292)
- streamer.exe (PID: 3504)
- streamer.exe (PID: 3480)
- streamer.exe (PID: 1816)
- streamer.exe (PID: 3544)
- streamer.exe (PID: 2640)
- streamer.exe (PID: 1516)
- streamer.exe (PID: 3896)
SUSPICIOUS
Creates files in the user directory
- notepad++.exe (PID: 1928)
Executable content was dropped or overwritten
- msdt.exe (PID: 2764)
Executed via COM
- sdiagnhost.exe (PID: 516)
Executed via Task Scheduler
- streamer.exe (PID: 2488)
- streamer.exe (PID: 2336)
- streamer.exe (PID: 1816)
- streamer.exe (PID: 3292)
- streamer.exe (PID: 3504)
- streamer.exe (PID: 3480)
- streamer.exe (PID: 3544)
- streamer.exe (PID: 2640)
- streamer.exe (PID: 3896)
- streamer.exe (PID: 1516)
- streamer.exe (PID: 3400)
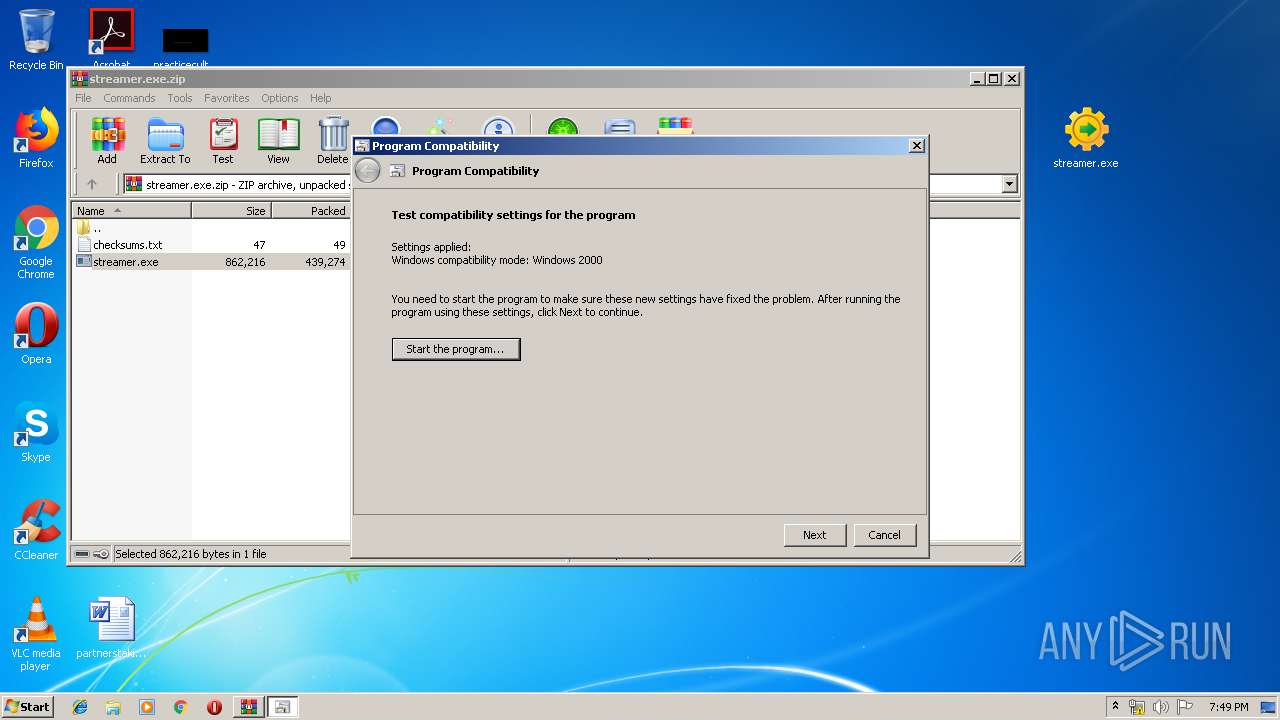
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 2764)
INFO
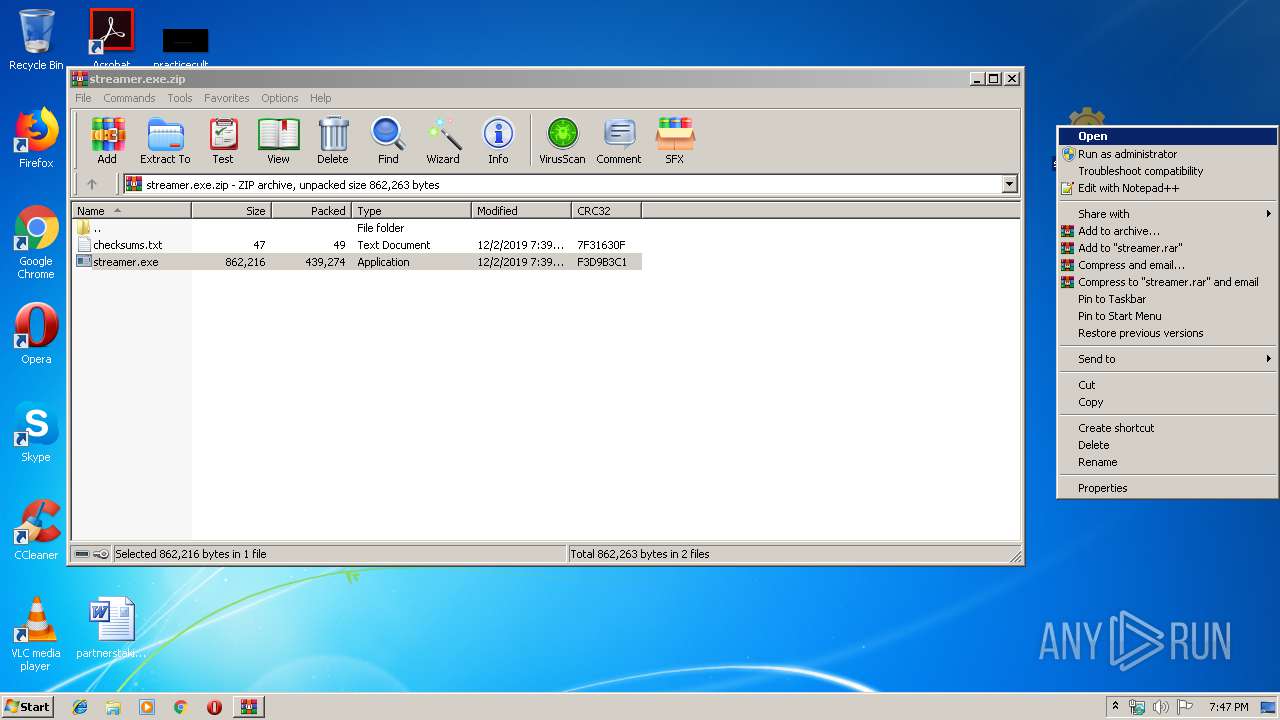
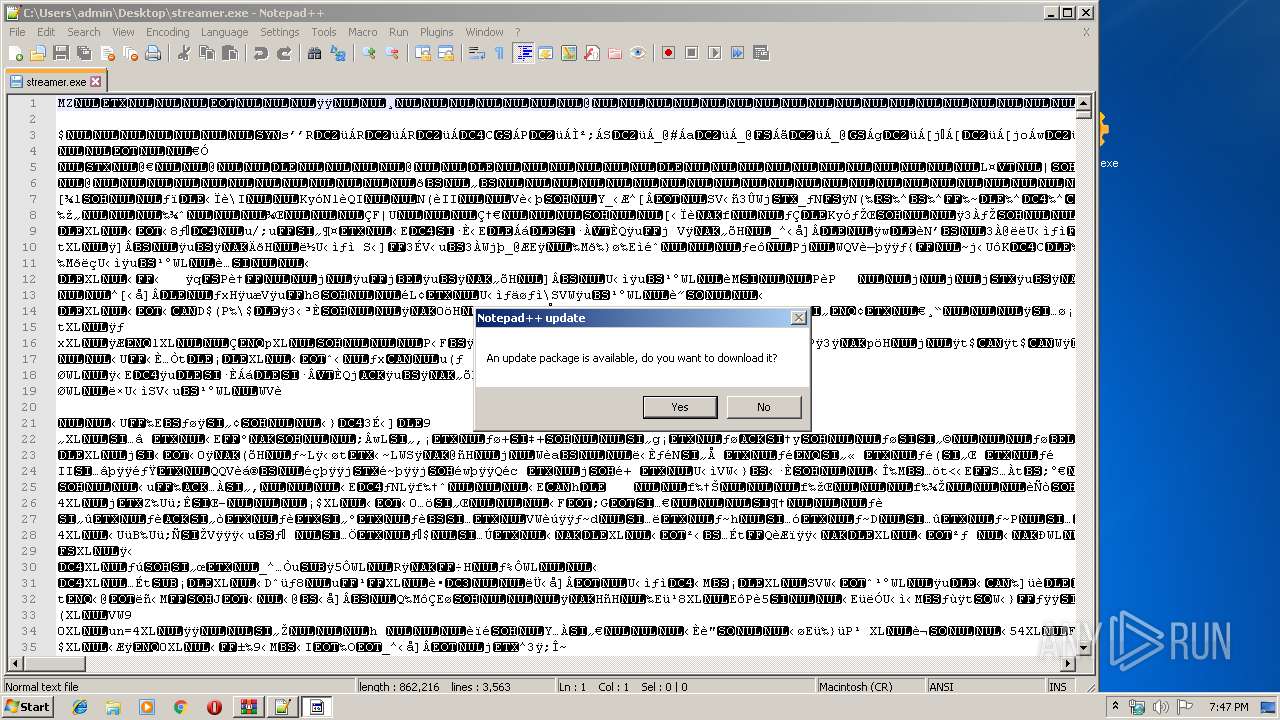
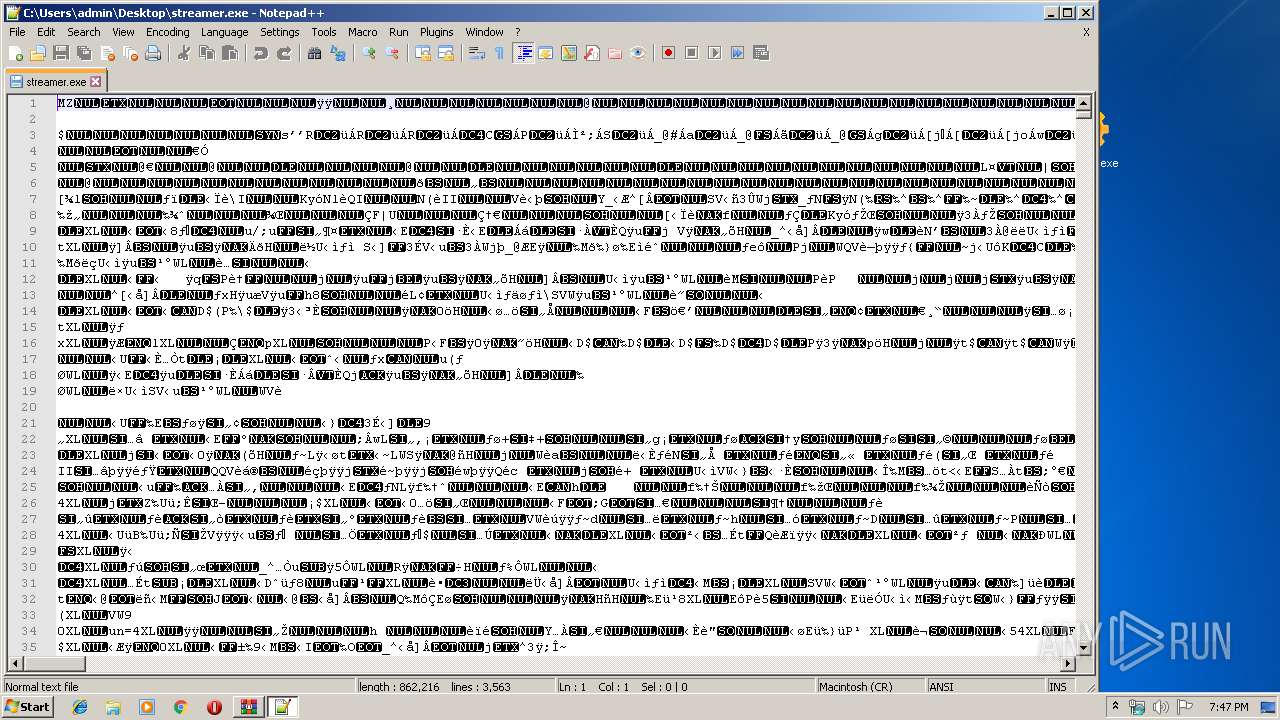
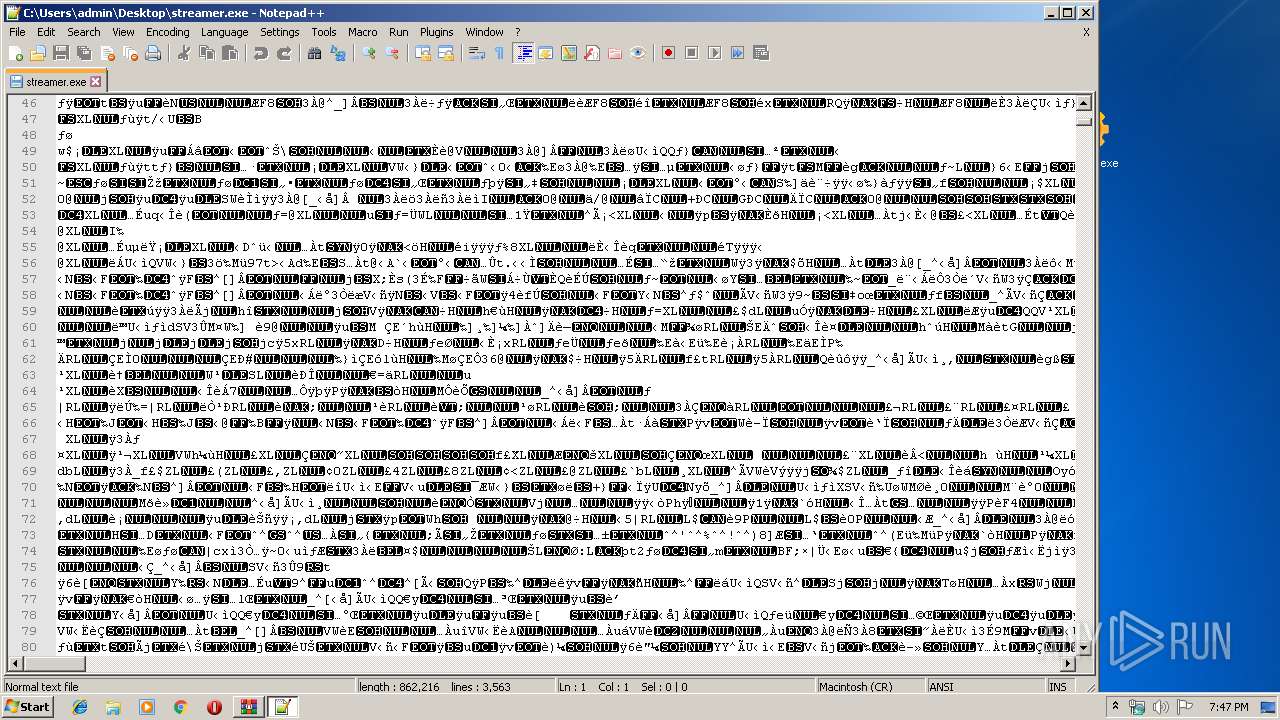
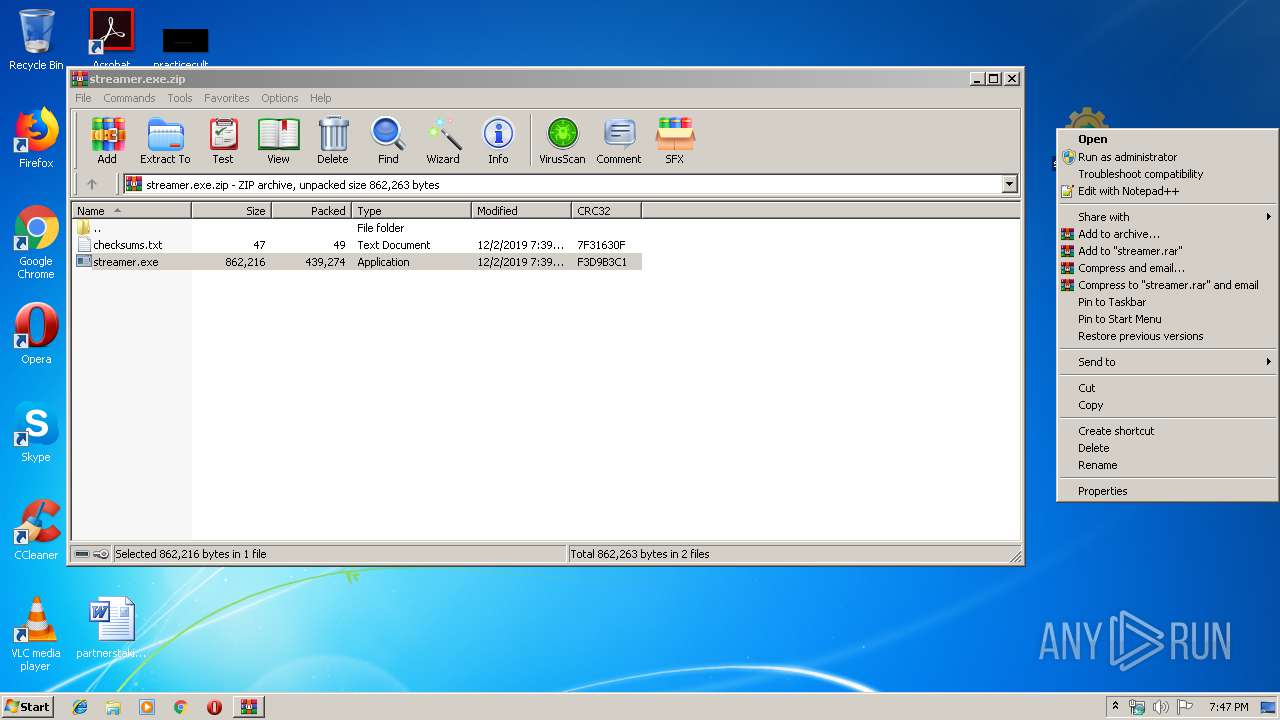
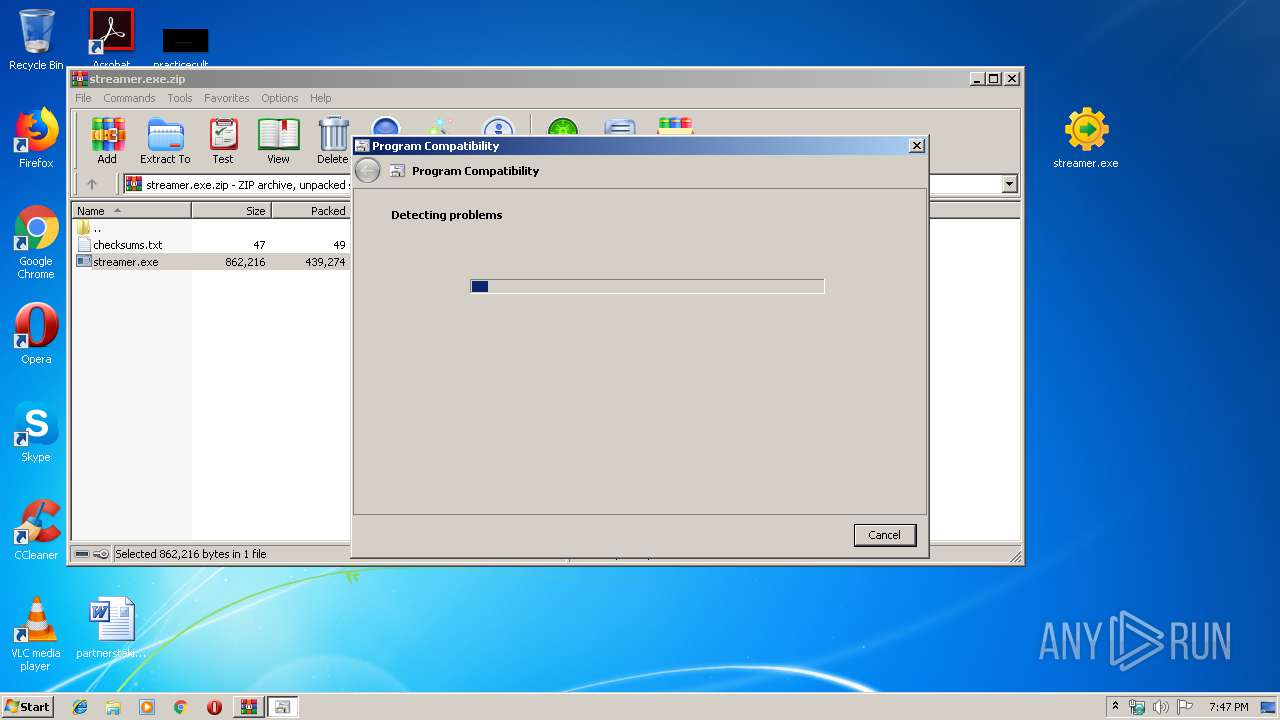
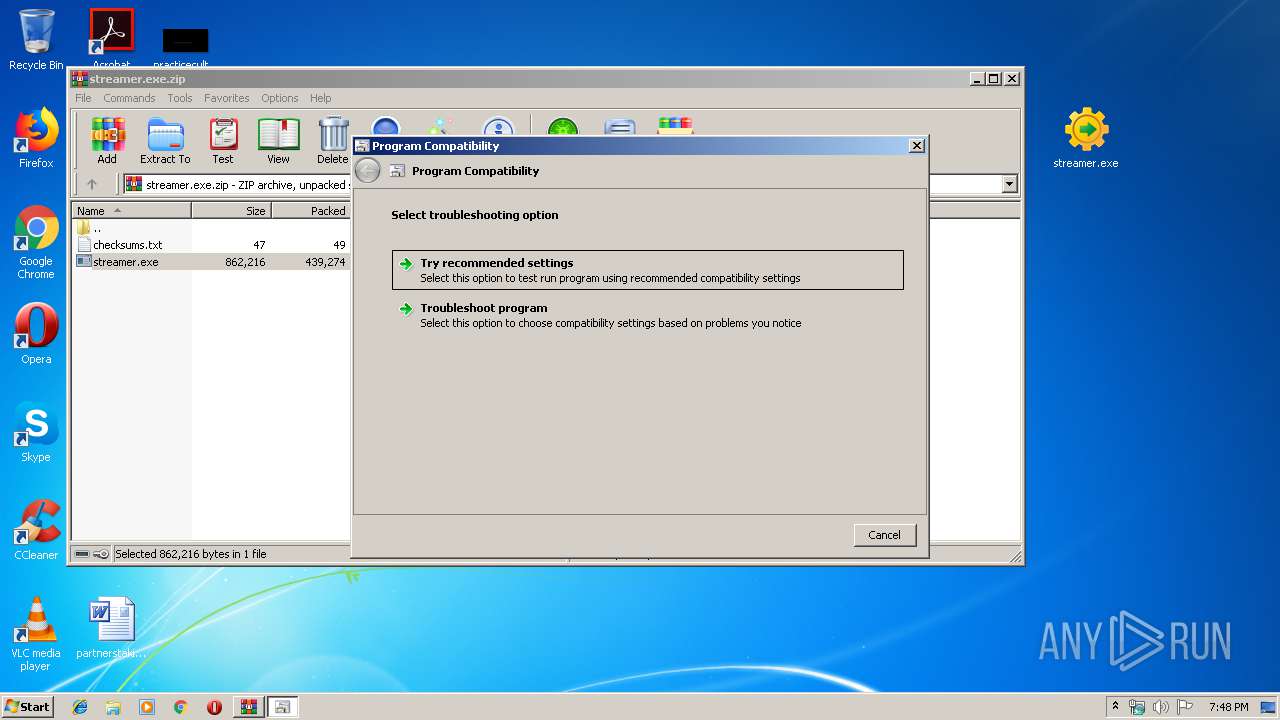
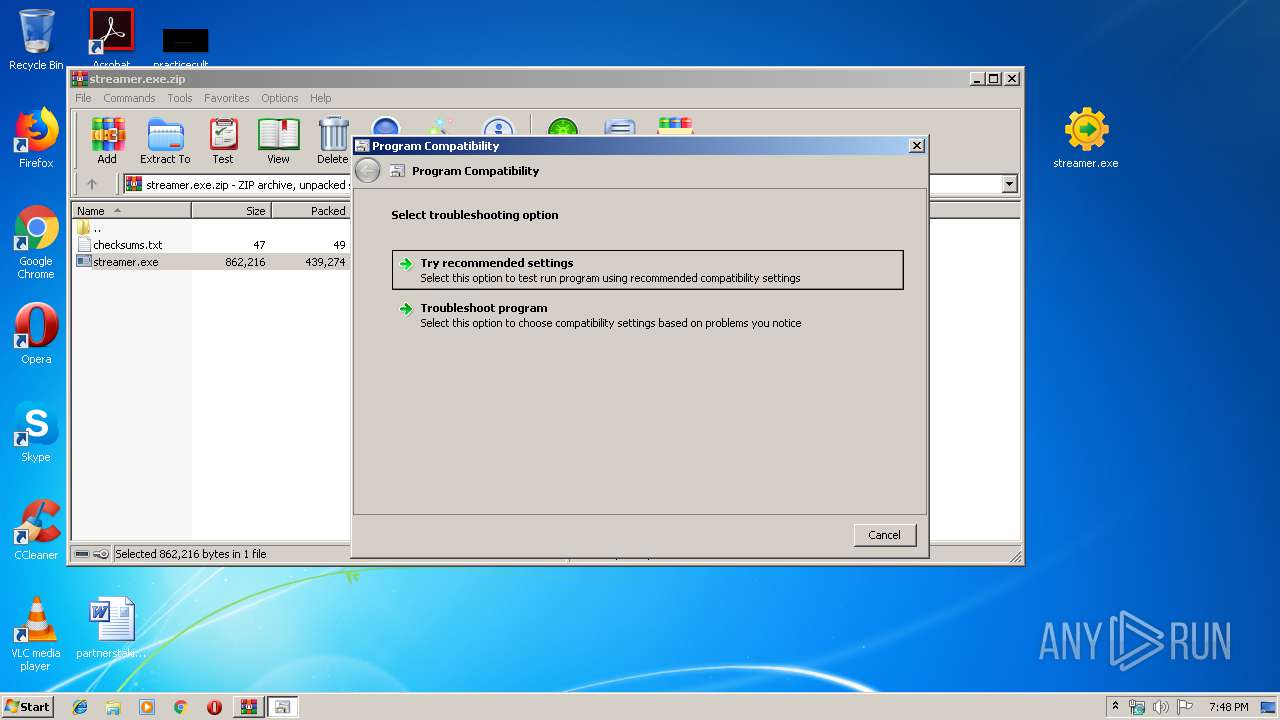
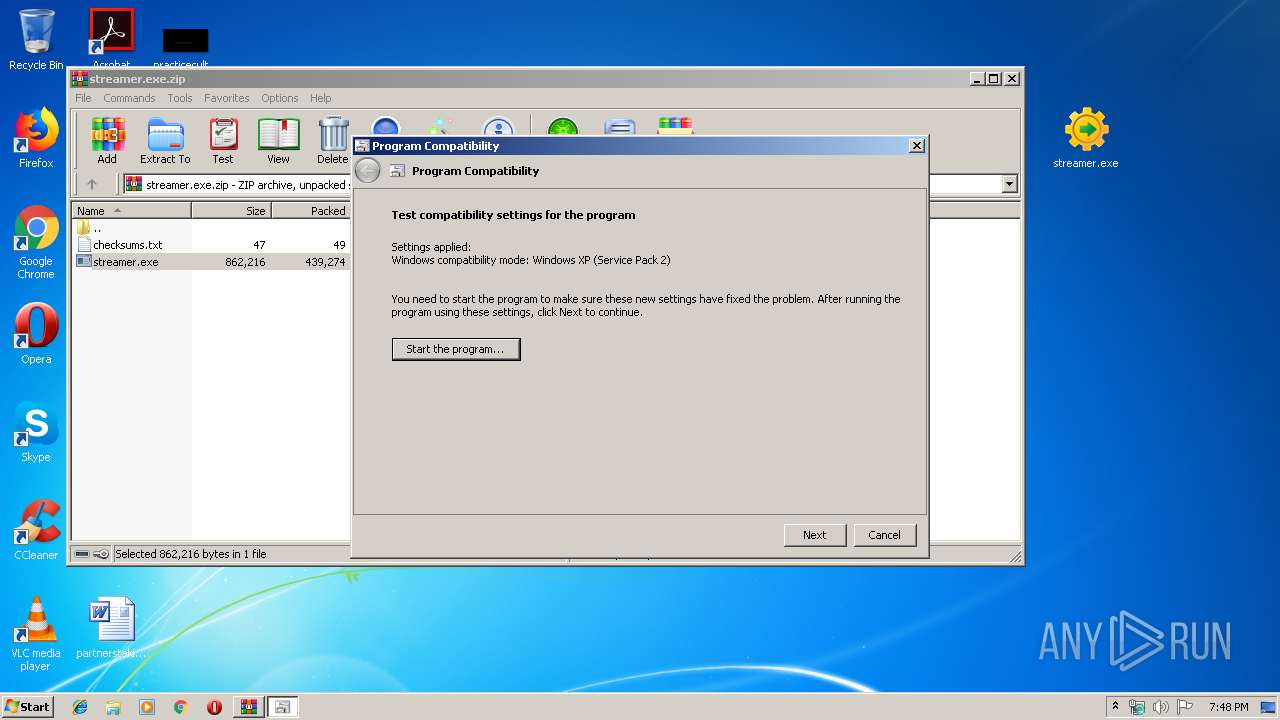
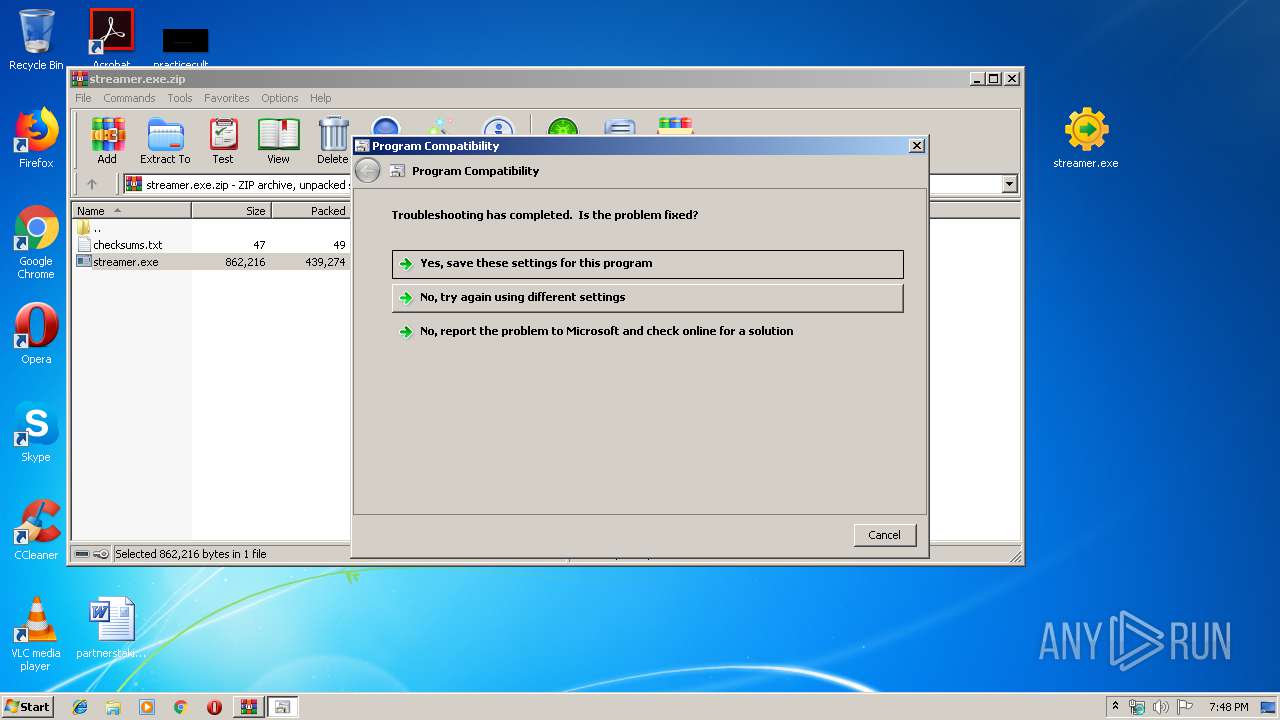
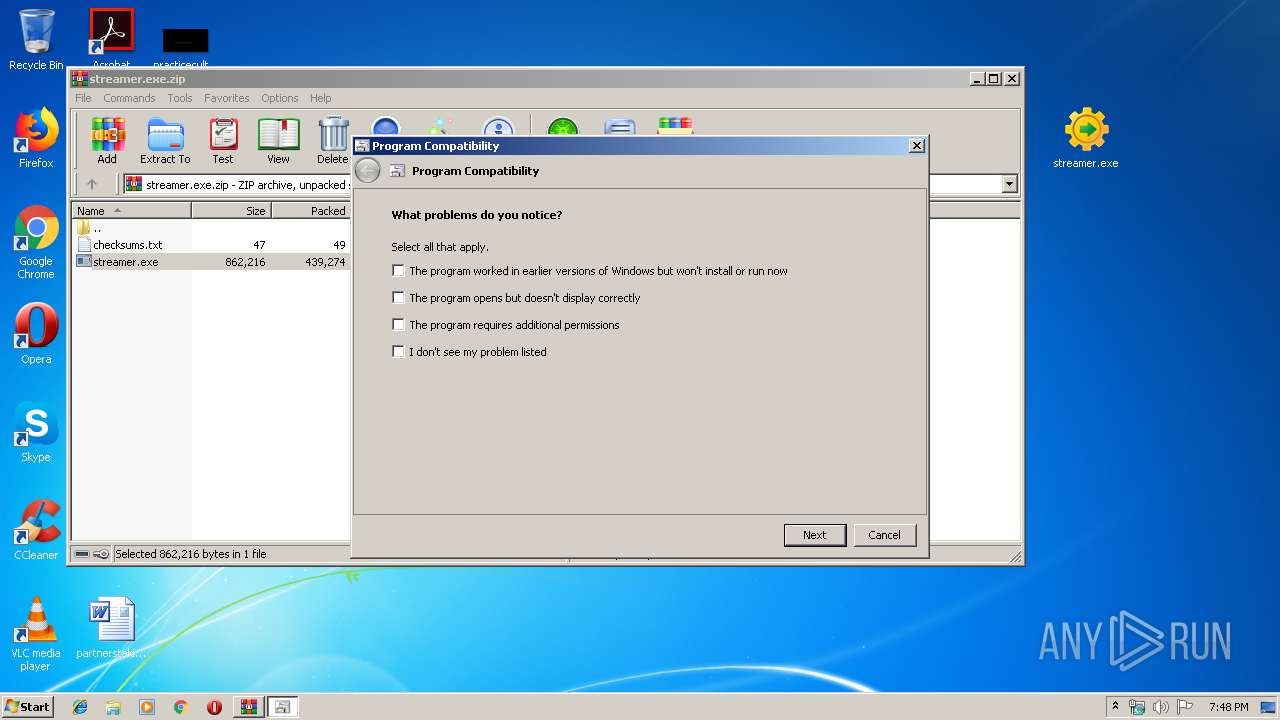
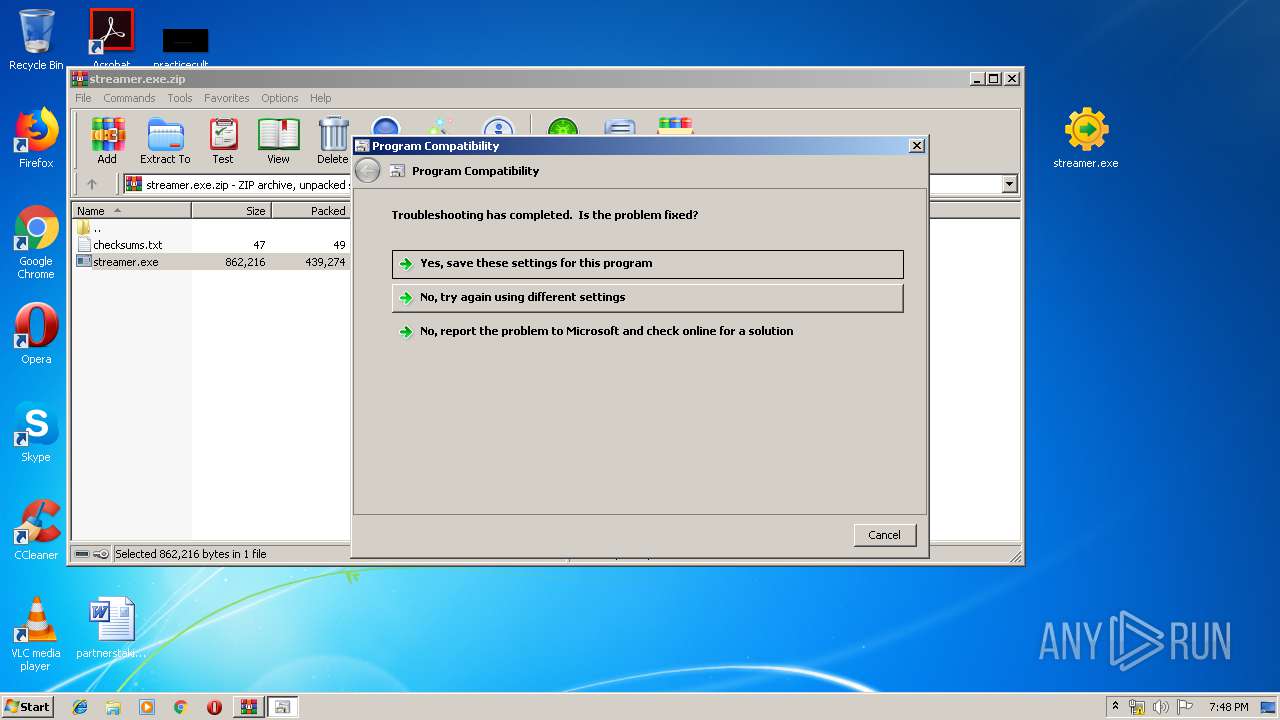
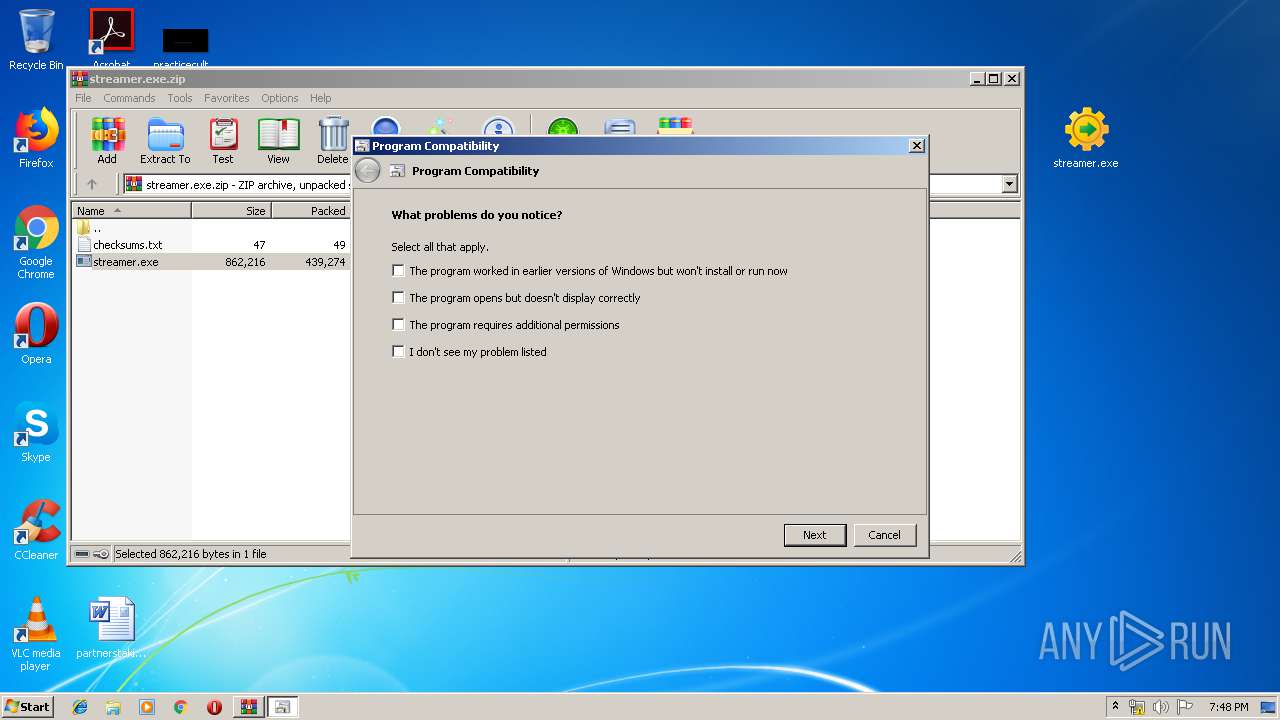
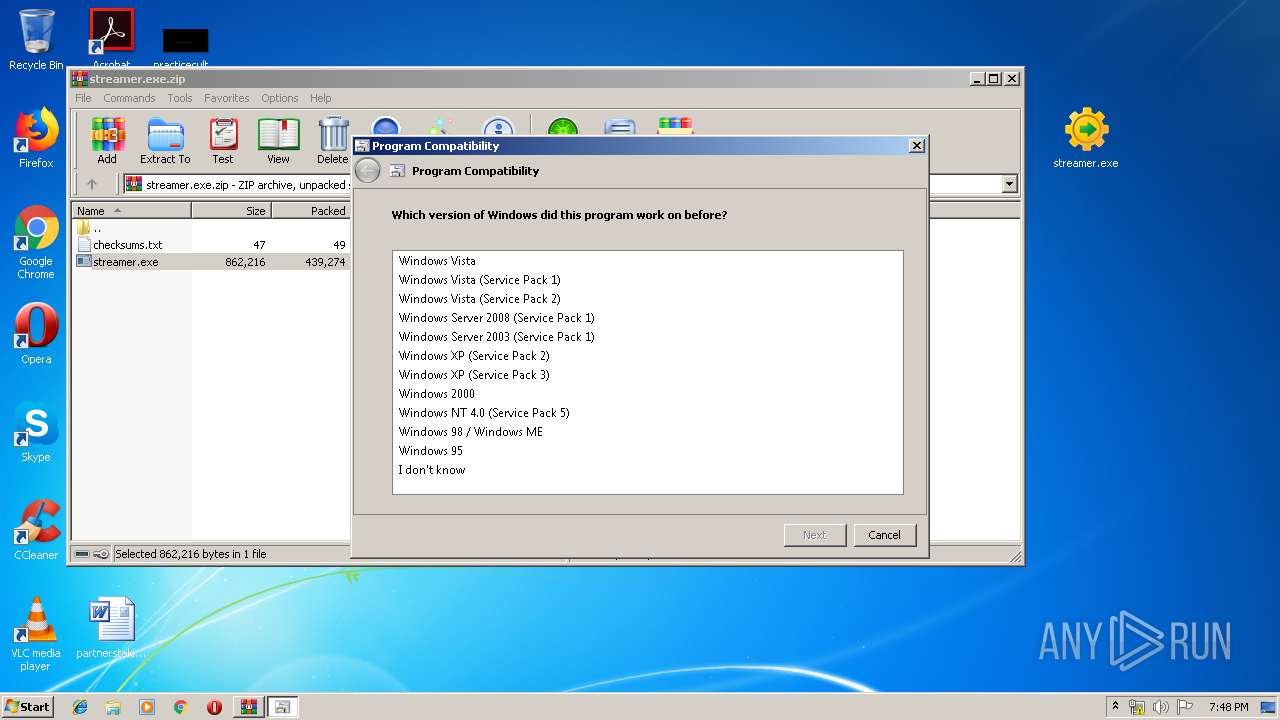
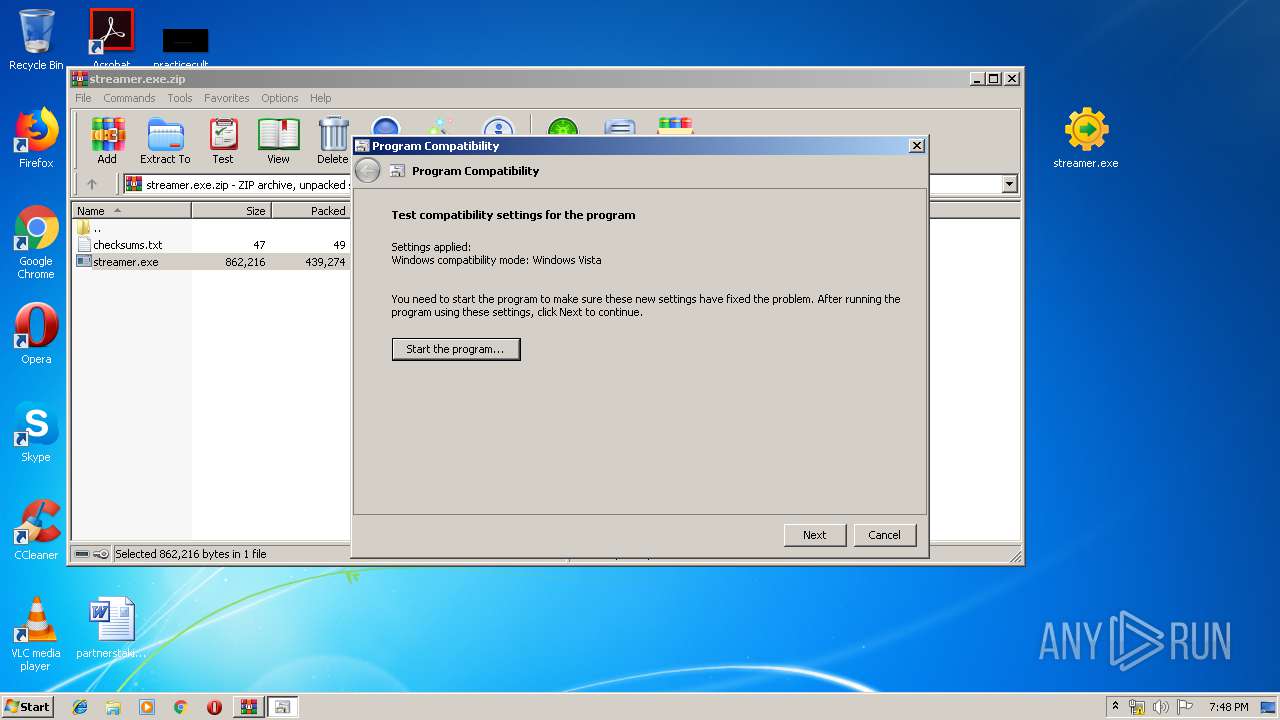
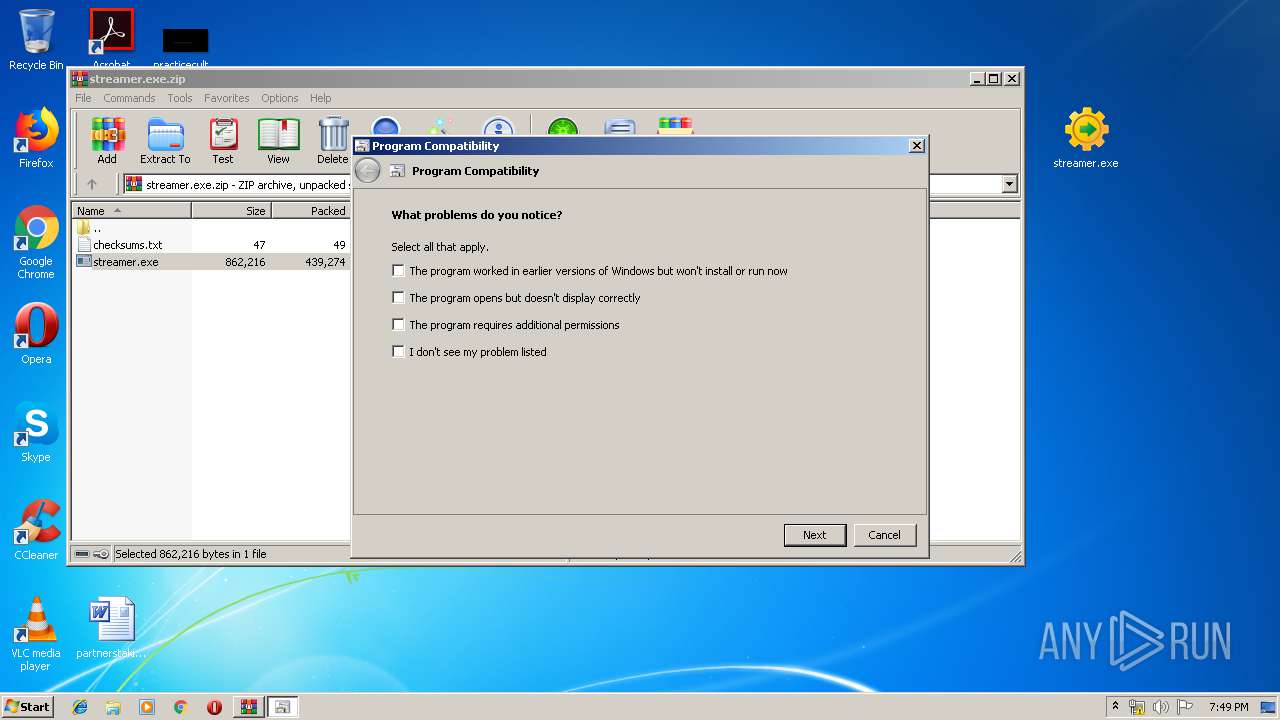
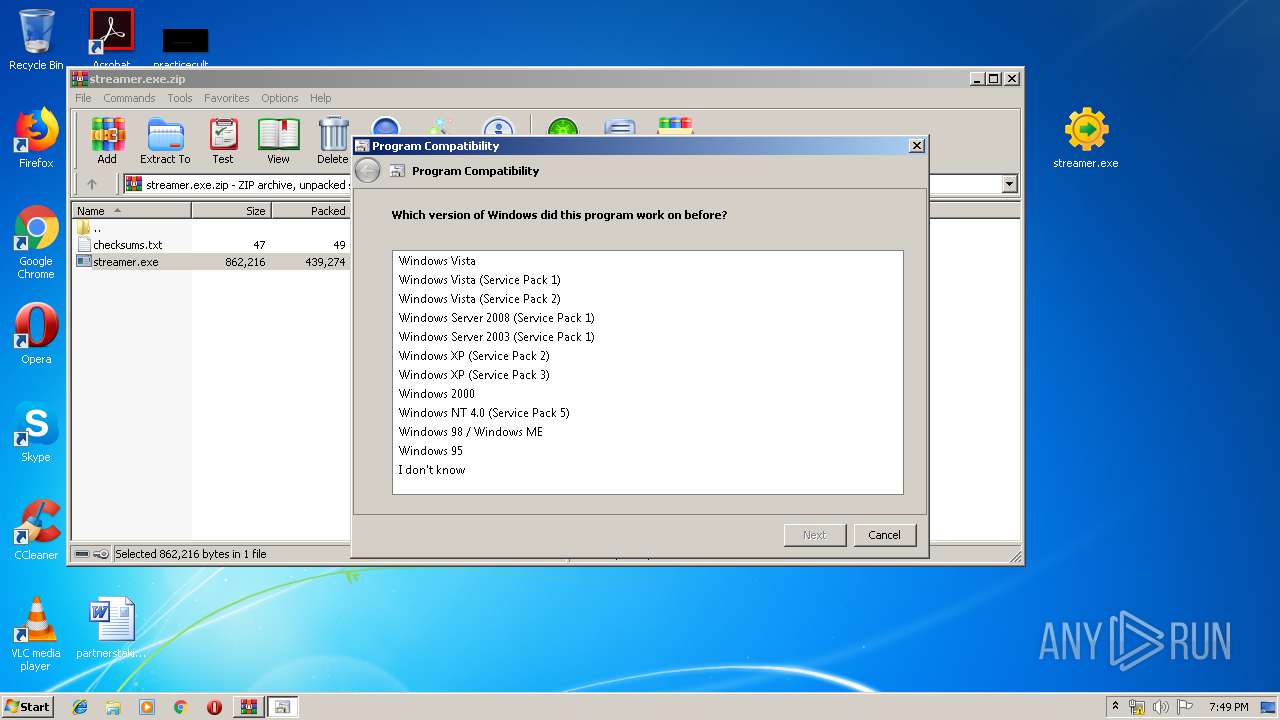
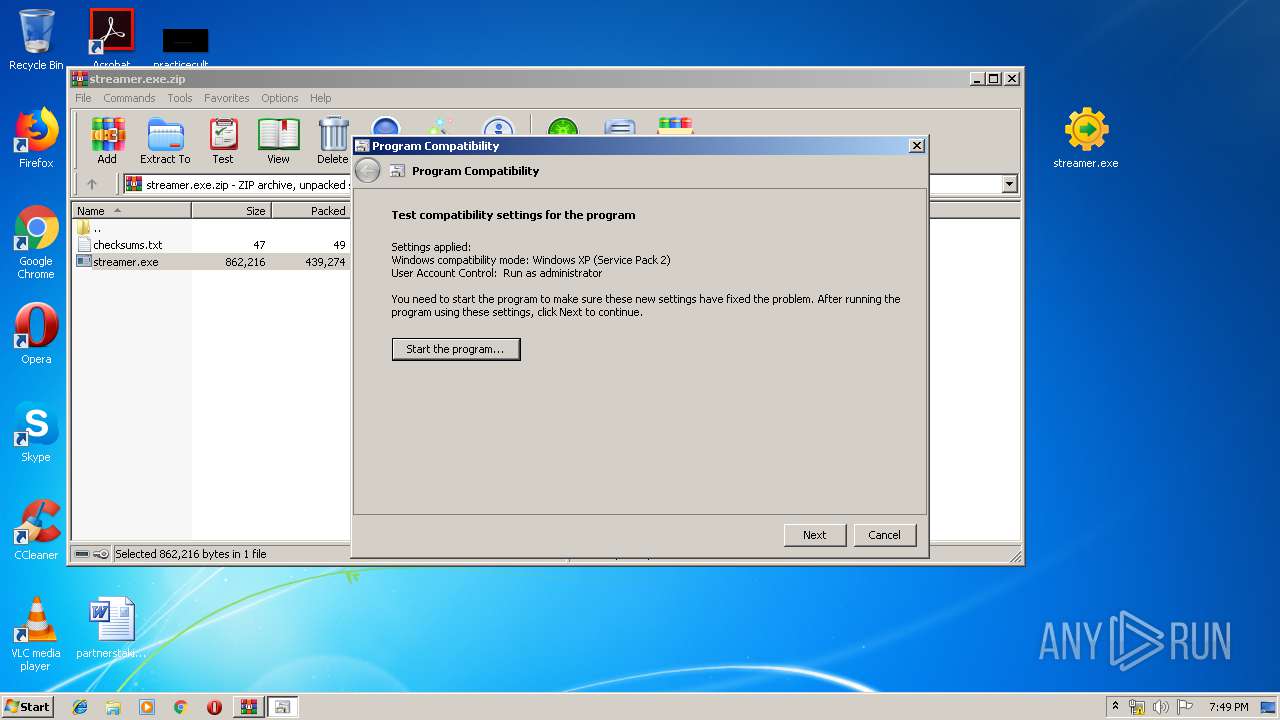
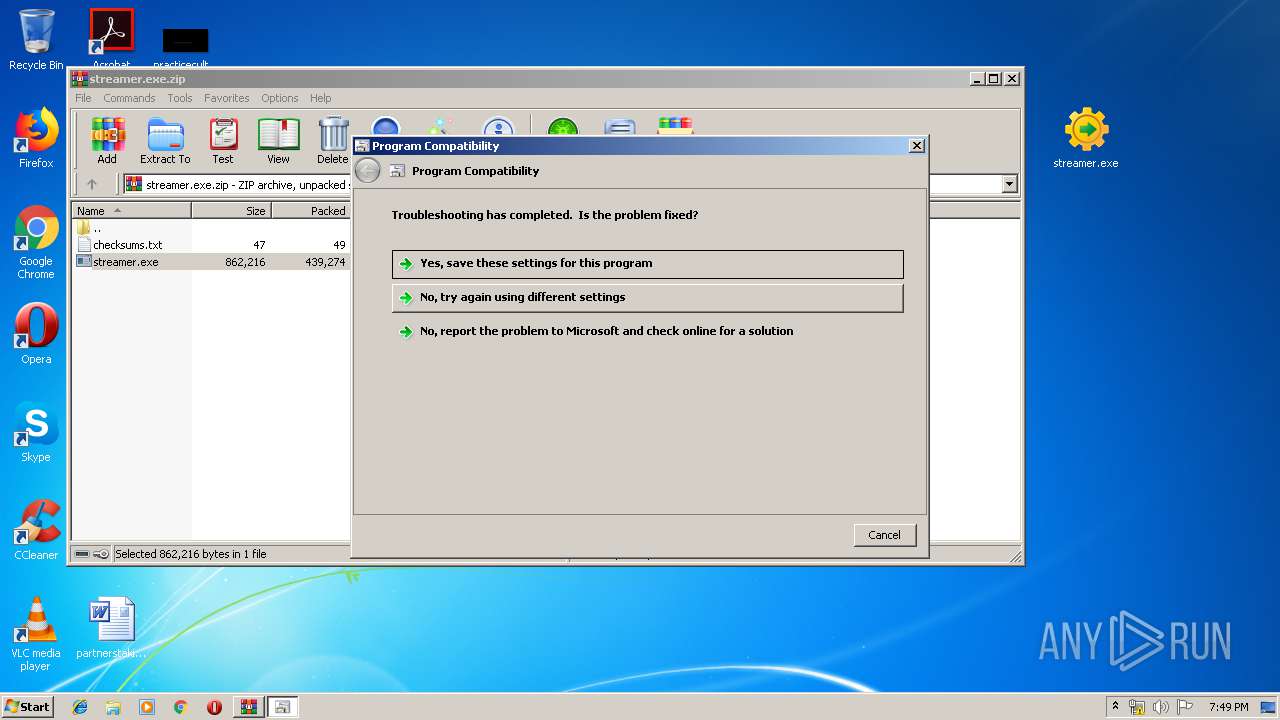
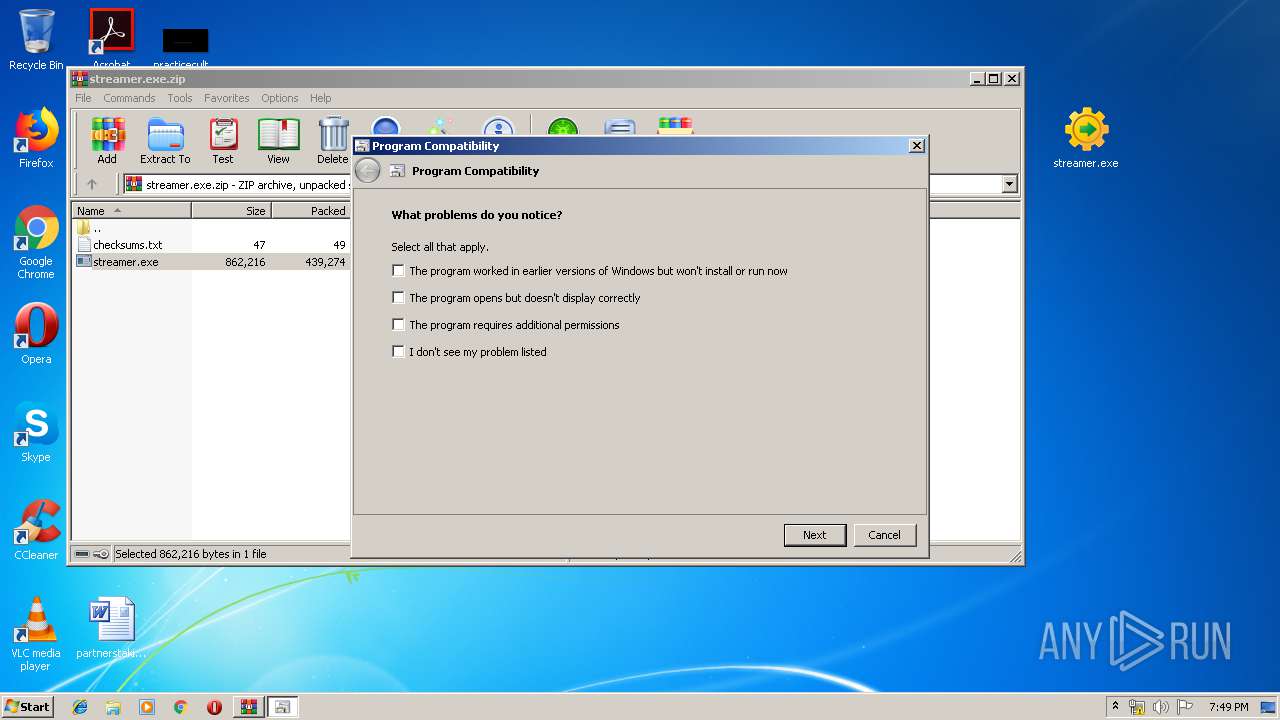
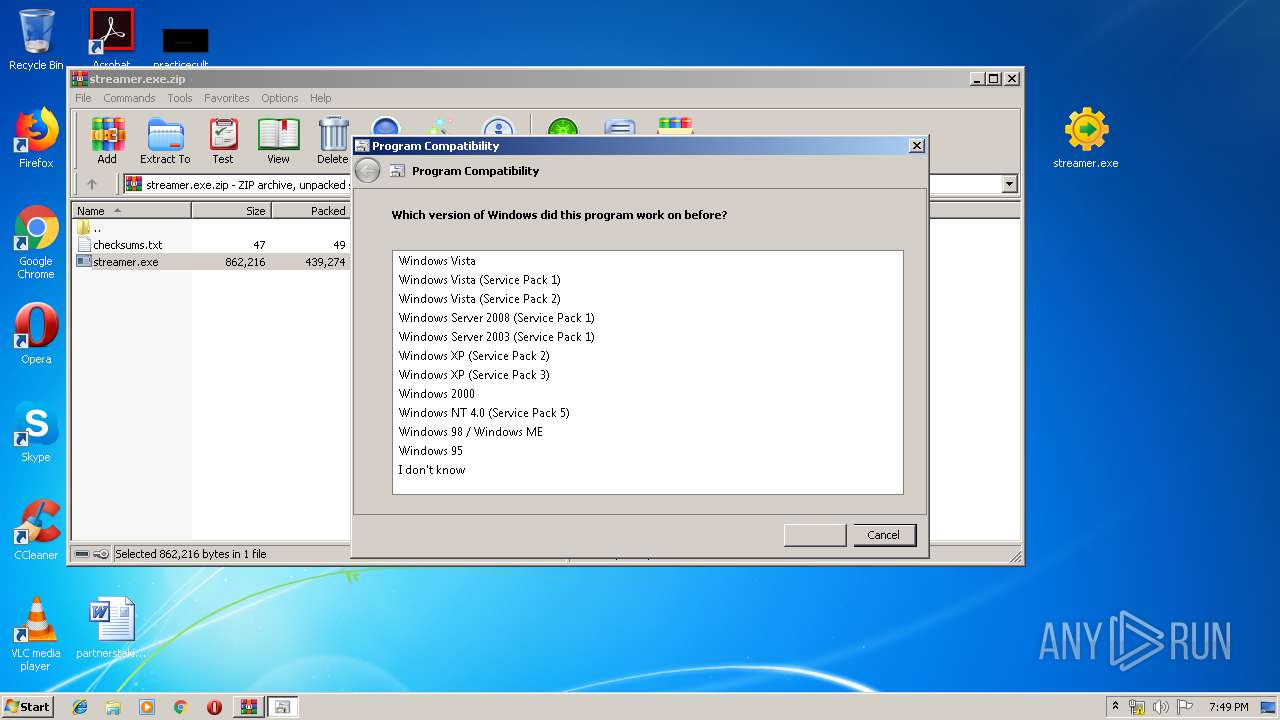
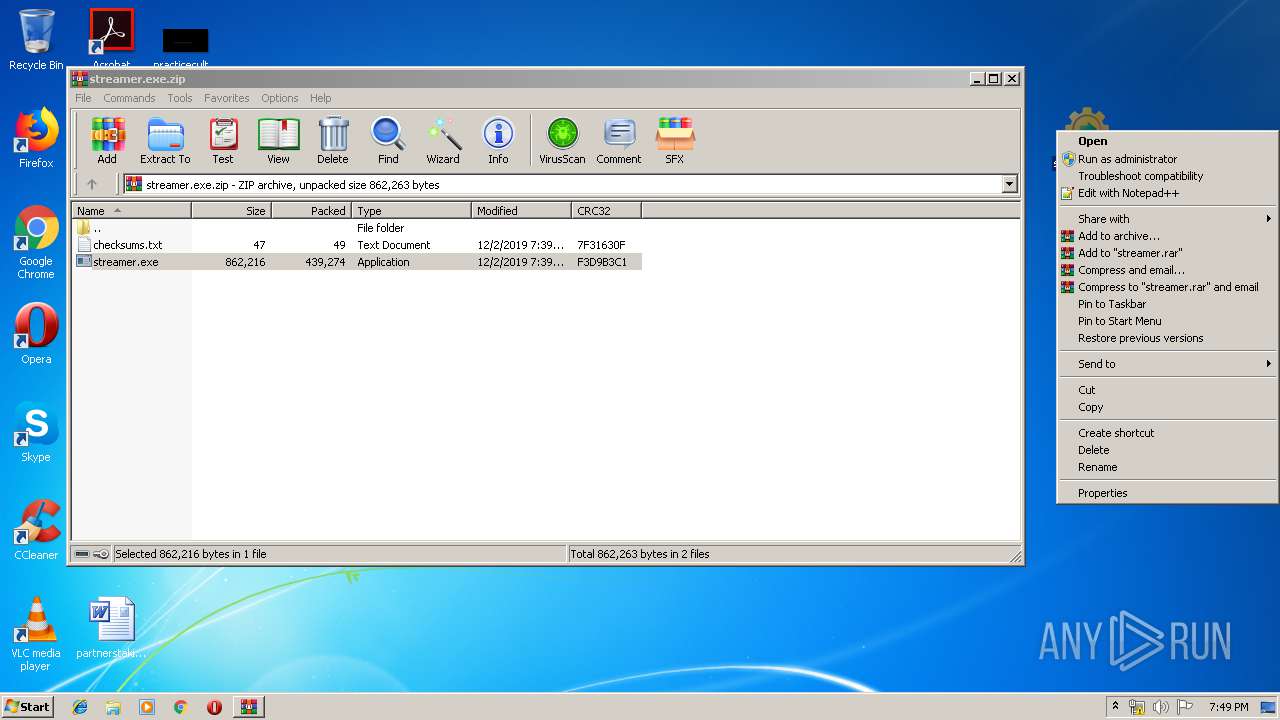
Manual execution by user
- notepad++.exe (PID: 1928)
- pcwrun.exe (PID: 3852)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
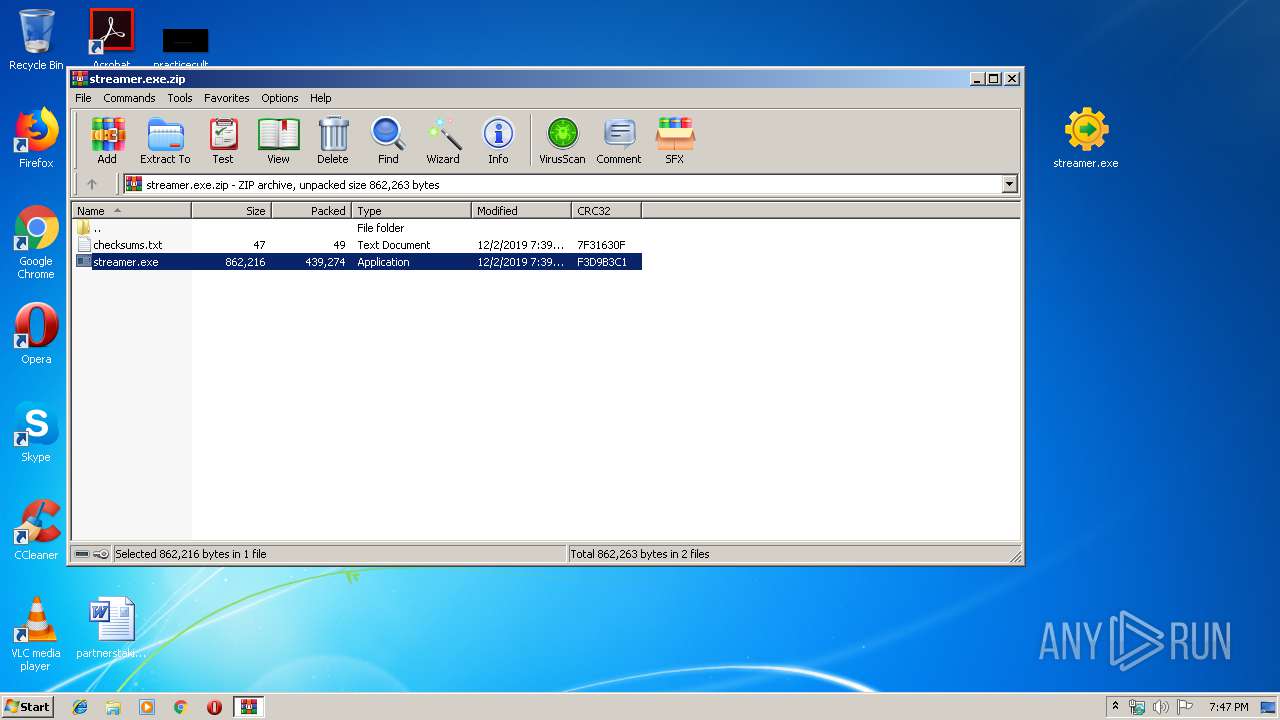
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:12:02 19:39:20 |
| ZipCRC: | 0xf3d9b3c1 |
| ZipCompressedSize: | 439274 |
| ZipUncompressedSize: | 862216 |
| ZipFileName: | streamer.exe |
Total processes
75
Monitored processes
29
Malicious processes
3
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 584 | "C:\Windows\System32\rundll32.exe" C:\Windows\system32\pcwutl.dll,CreateAndRunTask -path "C:\Users\admin\Desktop\streamer.exe" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 928 | "C:\Windows\System32\rundll32.exe" C:\Windows\system32\pcwutl.dll,CreateAndRunTask -path "C:\Users\admin\Desktop\streamer.exe" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1096 | "C:\Windows\System32\rundll32.exe" C:\Windows\system32\pcwutl.dll,CreateAndRunTask -path "C:\Users\admin\Desktop\streamer.exe" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
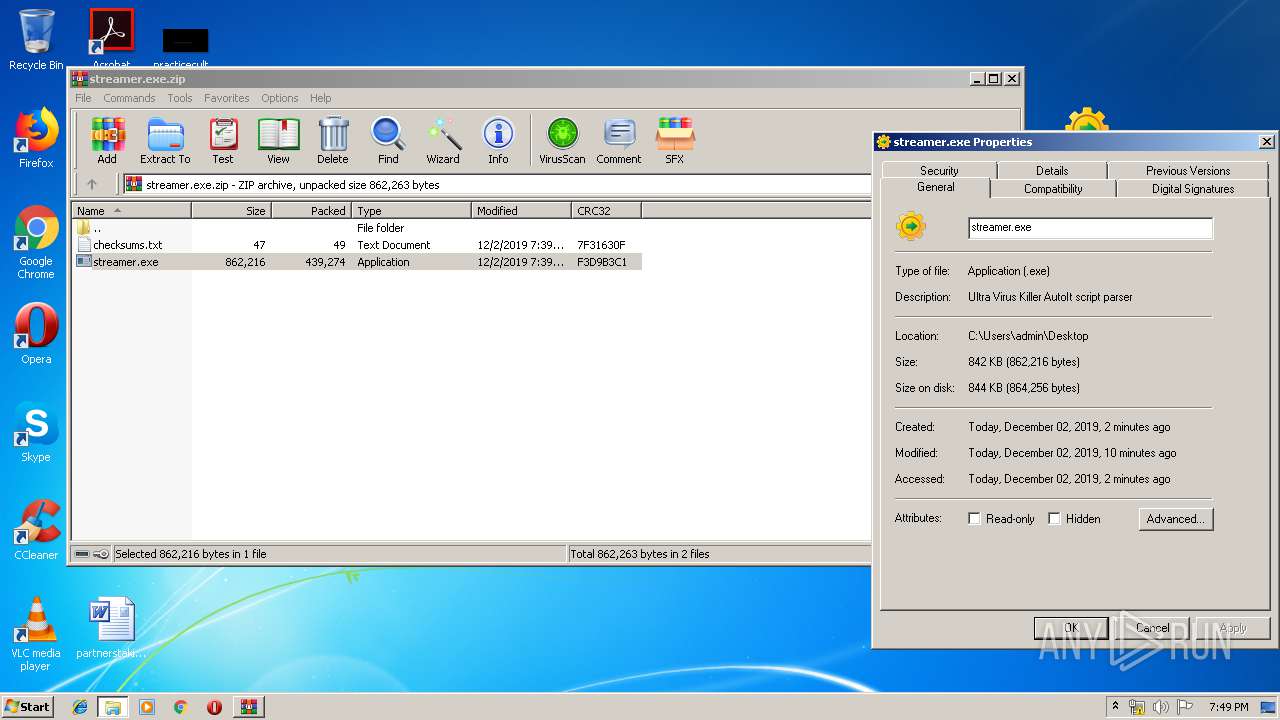
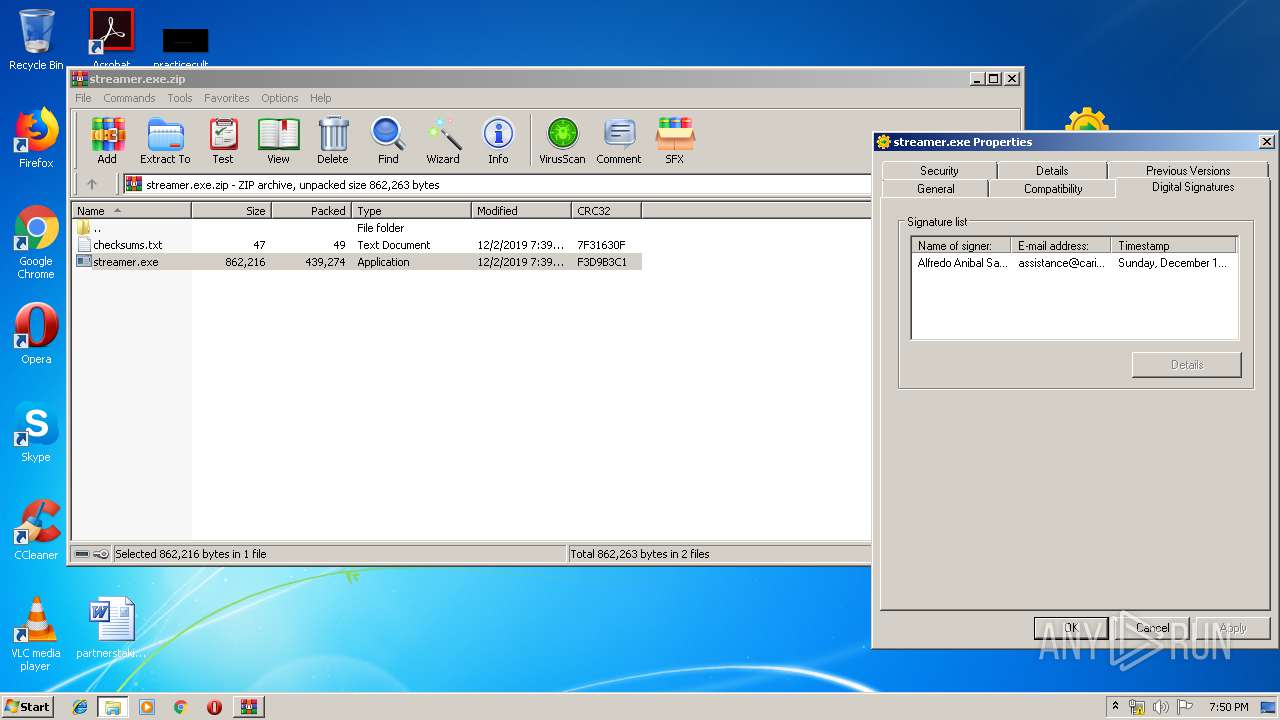
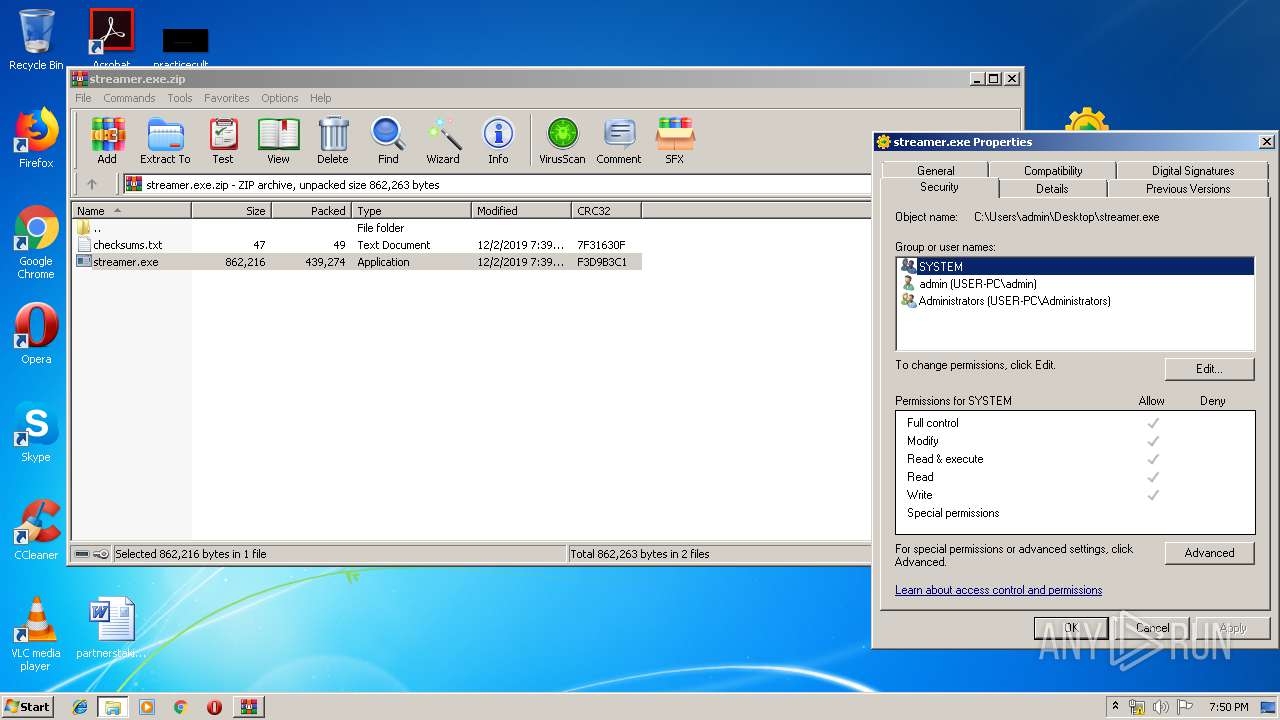
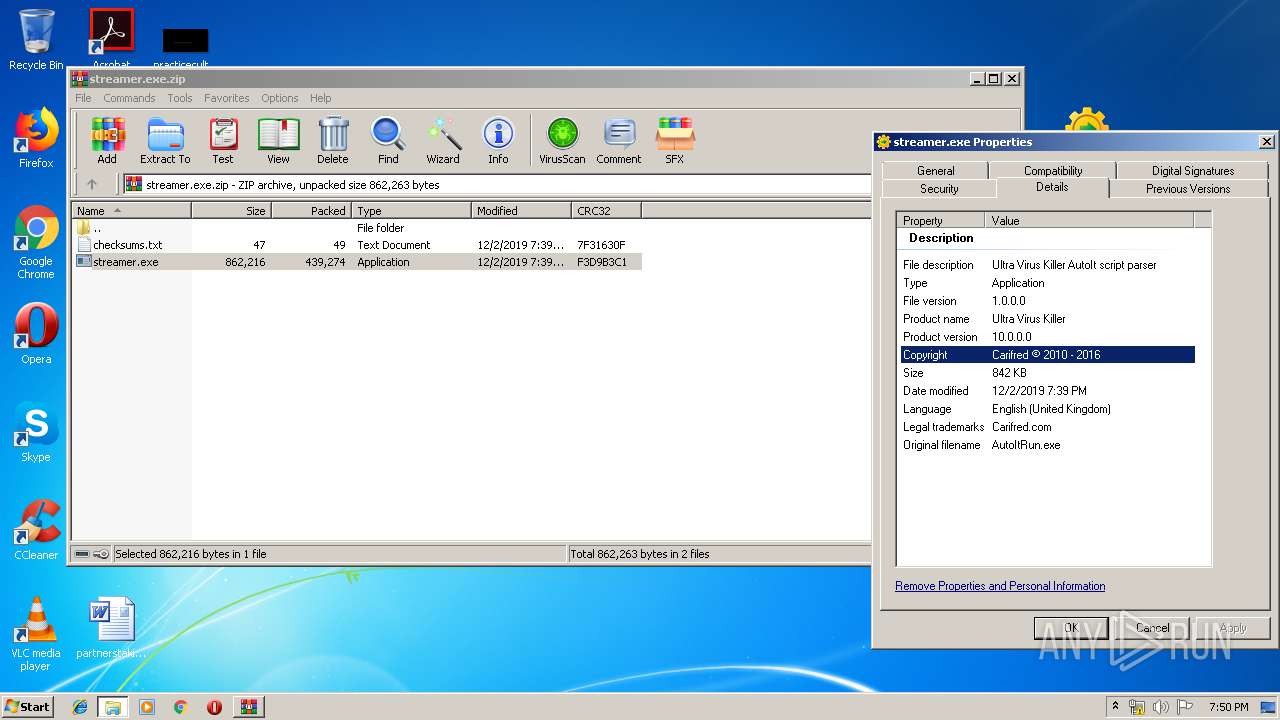
| 1516 | C:\Users\admin\Desktop\streamer.exe | C:\Users\admin\Desktop\streamer.exe | taskeng.exe | ||||||||||||
User: admin Company: Carifred Integrity Level: HIGH Description: Ultra Virus Killer AutoIt script parser Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1812 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES1014.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1013.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1816 | C:\Users\admin\Desktop\streamer.exe | C:\Users\admin\Desktop\streamer.exe | — | taskeng.exe | |||||||||||
User: admin Company: Carifred Integrity Level: MEDIUM Description: Ultra Virus Killer AutoIt script parser Exit code: 3221226540 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1928 | "C:\Program Files\Notepad++\notepad++.exe" "C:\Users\admin\Desktop\streamer.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2064 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\hc2vrsiw.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2128 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\streamer.exe.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
662
Read events
589
Write events
68
Delete events
5
Modification events
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\streamer.exe.zip | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2128) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1928) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1928) notepad++.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\p2pcollab.dll,-8042 |
Value: Peer to Peer Trust | |||
Executable files
2
Suspicious files
1
Text files
24
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2128 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa2128.6541\streamer.exe | — | |
MD5:— | SHA256:— | |||
| 2956 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC1013.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | csc.exe | C:\Users\admin\AppData\Local\Temp\uxejne2w.pdb | — | |
MD5:— | SHA256:— | |||
| 1812 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES1014.tmp | — | |
MD5:— | SHA256:— | |||
| 2956 | csc.exe | C:\Users\admin\AppData\Local\Temp\uxejne2w.dll | — | |
MD5:— | SHA256:— | |||
| 2956 | csc.exe | C:\Users\admin\AppData\Local\Temp\uxejne2w.out | — | |
MD5:— | SHA256:— | |||
| 2176 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSC115B.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | csc.exe | C:\Users\admin\AppData\Local\Temp\w2fvyhxu.pdb | — | |
MD5:— | SHA256:— | |||
| 3948 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RES115C.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | csc.exe | C:\Users\admin\AppData\Local\Temp\w2fvyhxu.dll | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2Fz5hY5qj0aEmX0H4s05bY%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3940 | gup.exe | 104.31.88.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|