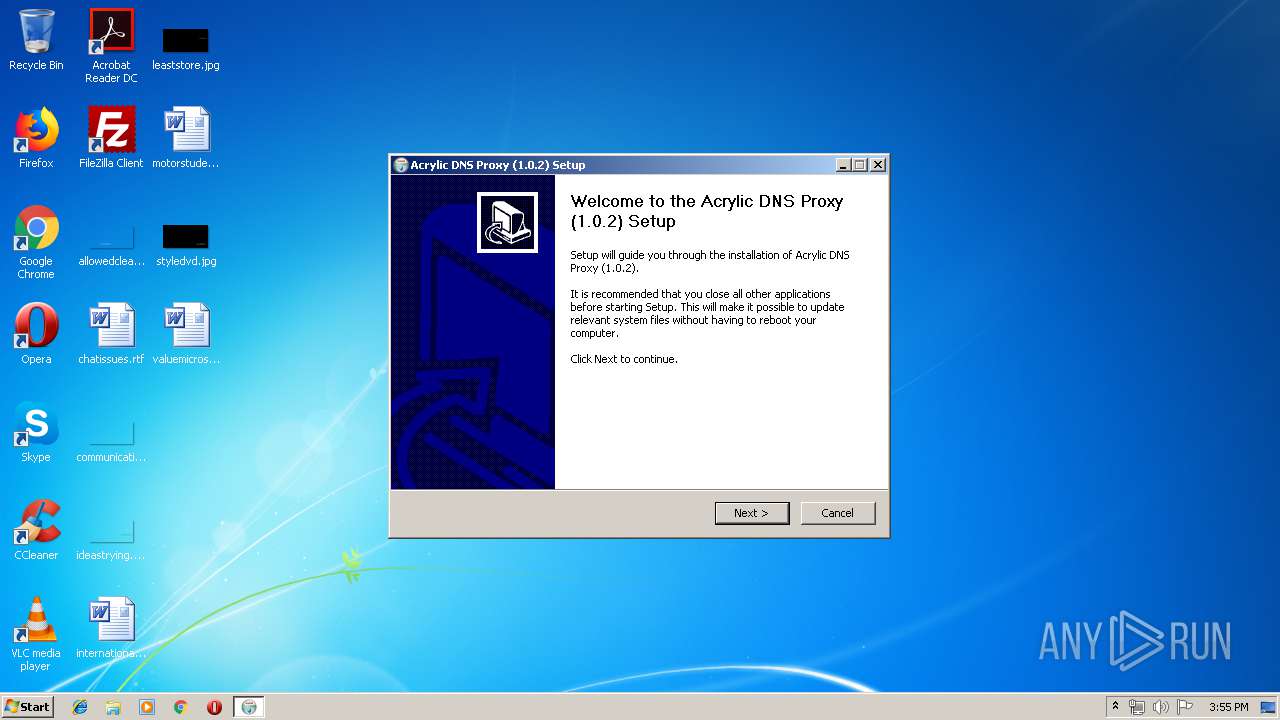
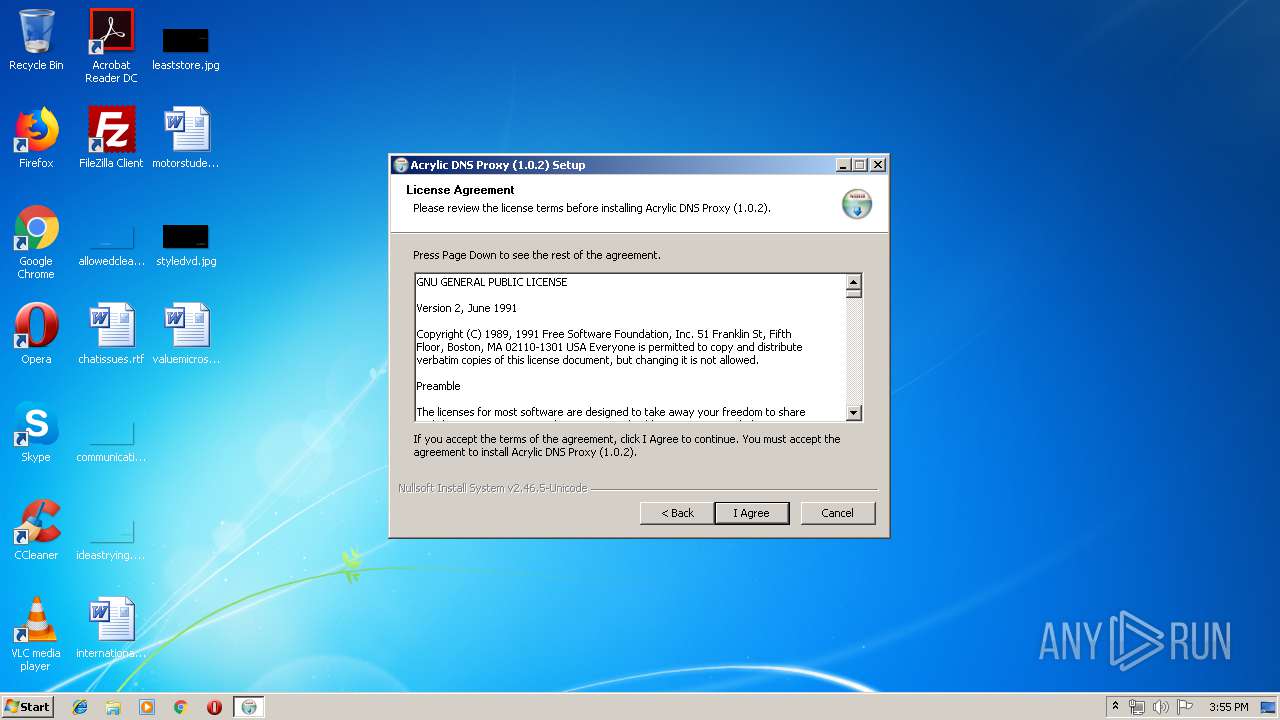
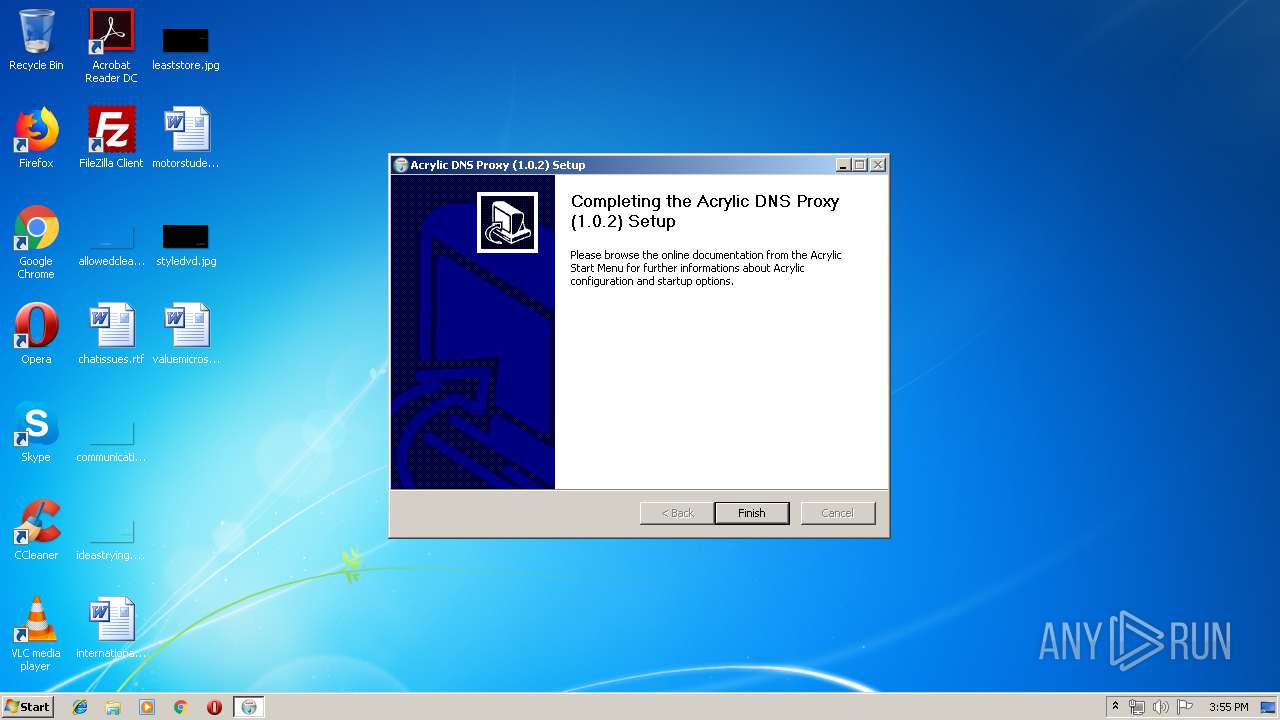
| File name: | Acrylic.exe |
| Full analysis: | https://app.any.run/tasks/e75397ff-5258-4fed-b62f-3ff487b99d95 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2019, 14:55:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | DE9E82DBDADB40A157D245B8ED576A79 |
| SHA1: | 4893EB06144CA2B3FE8587FAD1F251C162173F3C |
| SHA256: | 2BFCC72A1F255285448A31A4C45F65FA518ADCC1938A76E71417D2EBEEE5151E |
| SSDEEP: | 12288:oC07pq6noejcce1SQan9ZXmImMqbVQobP84uizj7HjTwLplk5RnwBzn/:ov7fnN2rGQInqbVo4uAvynzn/ |
MALICIOUS
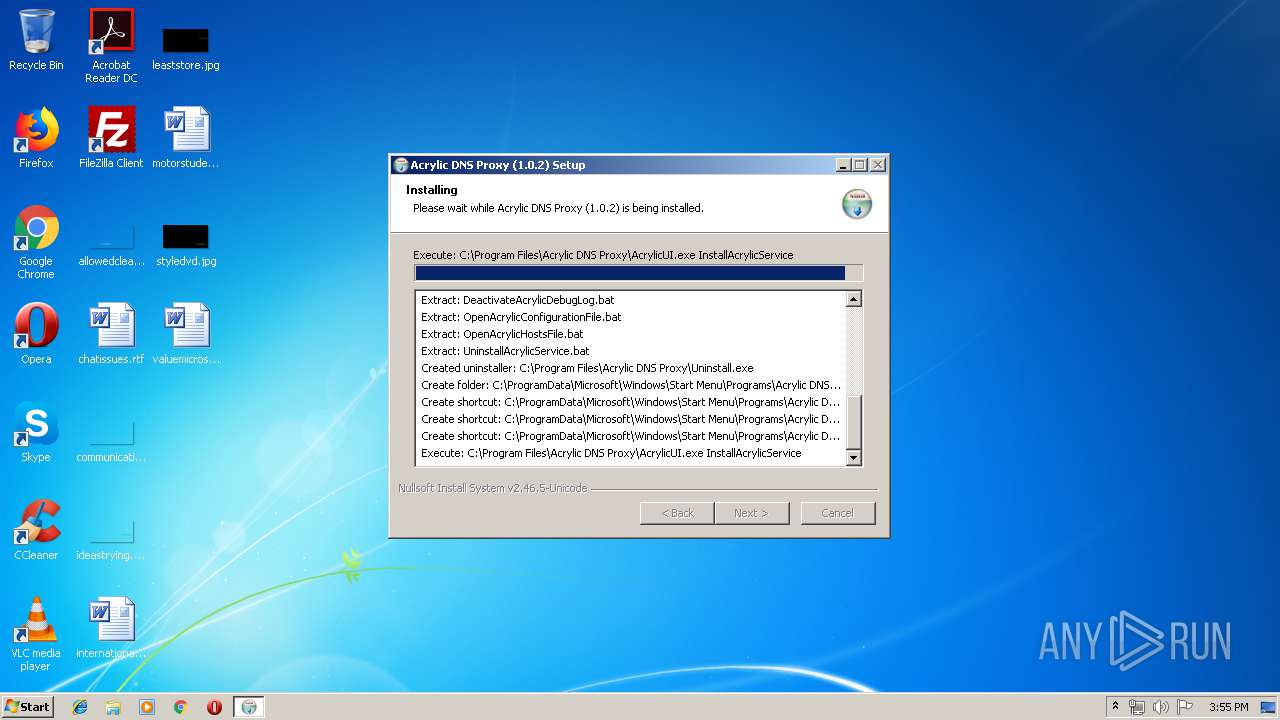
Loads dropped or rewritten executable
- Acrylic.exe (PID: 3700)
Application was dropped or rewritten from another process
- AcrylicUI.exe (PID: 3032)
- AcrylicService.exe (PID: 3960)
- AcrylicService.exe (PID: 3756)
Starts NET.EXE for service management
- AcrylicUI.exe (PID: 3032)
SUSPICIOUS
Executable content was dropped or overwritten
- Acrylic.exe (PID: 3700)
Executed as Windows Service
- AcrylicService.exe (PID: 3756)
Uses NETSH.EXE for network configuration
- AcrylicUI.exe (PID: 3032)
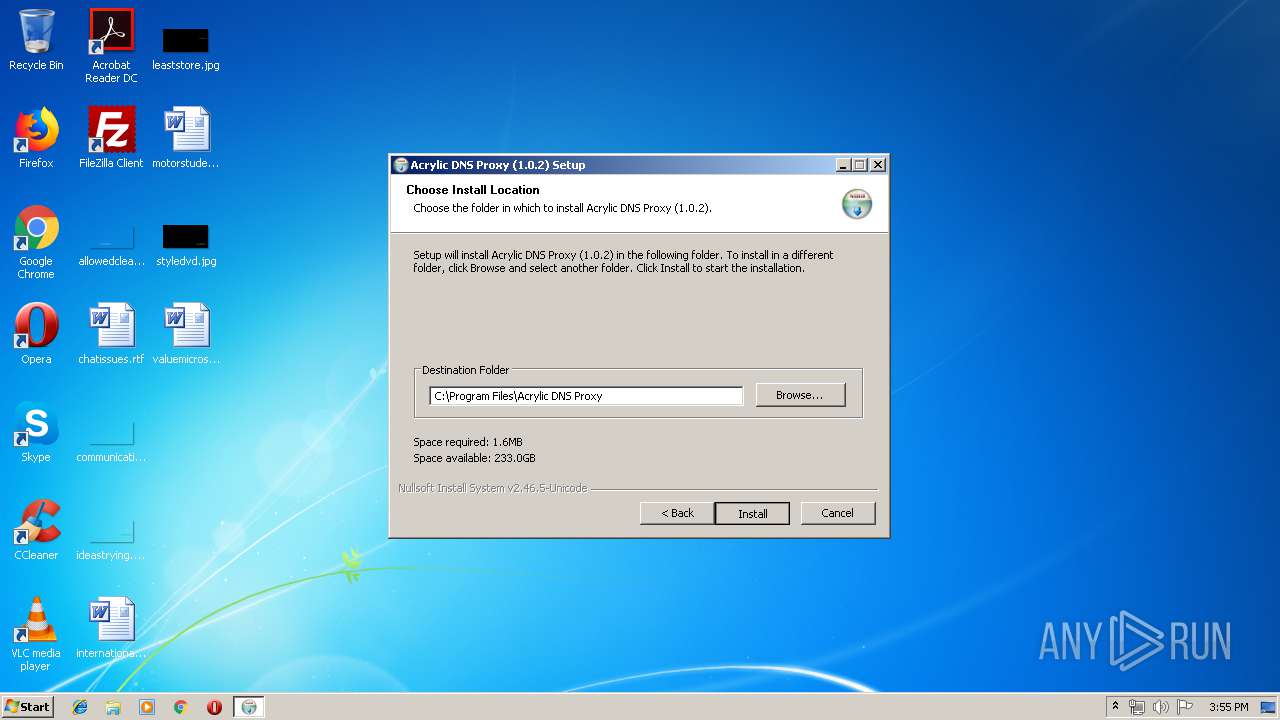
Creates files in the program directory
- Acrylic.exe (PID: 3700)
Creates or modifies windows services
- AcrylicService.exe (PID: 3960)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28160 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3883 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:54 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006DAE | 0x00006E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50853 |
.rdata | 0x00008000 | 0x00002A62 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39054 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.43086 |
.ndata | 0x00073000 | 0x0008D000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00100000 | 0x000043B0 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.93535 |
.reloc | 0x00105000 | 0x00000F32 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 5.93393 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21712 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.9993 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.24459 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.01502 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 6.16057 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.34146 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 3.04232 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.6691 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
45
Monitored processes
8
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 832 | "C:\Users\admin\AppData\Local\Temp\Acrylic.exe" | C:\Users\admin\AppData\Local\Temp\Acrylic.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 | |||||||||||||||
| 1664 | NetSh.exe advfirewall firewall add rule name="Allow Acrylic DNS Proxy Service" dir=in action=allow program="C:\Program Files\Acrylic DNS Proxy\AcrylicService.exe" | C:\Windows\system32\NetSh.exe | — | AcrylicUI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Network Command Shell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1708 | C:\Windows\system32\net1 Start AcrylicDNSProxySvc | C:\Windows\system32\net1.exe | — | Net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2552 | Net.exe Start AcrylicDNSProxySvc | C:\Windows\system32\Net.exe | — | AcrylicUI.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Acrylic DNS Proxy\AcrylicUI.exe" InstallAcrylicService | C:\Program Files\Acrylic DNS Proxy\AcrylicUI.exe | — | Acrylic.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\Acrylic.exe" | C:\Users\admin\AppData\Local\Temp\Acrylic.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3756 | "C:\Program Files\Acrylic DNS Proxy\AcrylicService.exe" | C:\Program Files\Acrylic DNS Proxy\AcrylicService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3960 | "C:\Program Files\Acrylic DNS Proxy\AcrylicService.exe" /INSTALL /SILENT | C:\Program Files\Acrylic DNS Proxy\AcrylicService.exe | — | AcrylicUI.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
418
Read events
359
Write events
59
Delete events
0
Modification events
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-100 |
Value: DHCP Quarantine Enforcement Client | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-101 |
Value: Provides DHCP based enforcement for NAP | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-103 |
Value: 1.0 | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\dhcpqec.dll,-102 |
Value: Microsoft Corporation | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-1 |
Value: IPsec Relying Party | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-2 |
Value: Provides IPsec based enforcement for Network Access Protection | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-4 |
Value: 1.0 | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\napipsec.dll,-3 |
Value: Microsoft Corporation | |||
| (PID) Process: | (1664) NetSh.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\system32\tsgqec.dll,-100 |
Value: RD Gateway Quarantine Enforcement Client | |||
Executable files
5
Suspicious files
0
Text files
41
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3700 | Acrylic.exe | C:\Users\admin\AppData\Local\Temp\nsr1084.tmp\ioSpecial.ini | text | |
MD5:A9629D92421B2018E0A50FA6E9C6D515 | SHA256:1284DD8C29E5A932B8749B7AE5A9F0B5DB4419D14A7911E6D7C611F99C6279C7 | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\AcrylicConfiguration.ini | text | |
MD5:D38AA74EA9C90E01BC065AF57B50741E | SHA256:E33A552506A3705D0EEE221F95A468594A98260C5FE9383EB614D89D4DFBFD6E | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\AcrylicHosts.txt | text | |
MD5:2A9CFA9C51245DD0B0EA67829701DD60 | SHA256:108E2261F8438CA3A23CCA1E32B596F5D3127001706FC1BBA49E279367BF77F5 | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\AcrylicService.exe | executable | |
MD5:F61F1873380411343EFDD72ECF1FBB29 | SHA256:71DBB11E341B877F5C3F08E5A79542E5CED3236395CE64BF82EC21CA8D36670F | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\ReadMe.txt | text | |
MD5:249E0BBBD5986C82B2ECF9138A04C4E7 | SHA256:19BA8F54BBE5B76B455941553E5C4969AA78A0DA95874F586FA3584763AA3ADF | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\StopAcrylicService.bat | text | |
MD5:6B1B906ACA3951F63F8E9D9F47750770 | SHA256:7604D2EF40315A8F751602BFF6D36E4C036857D24DFFDEA35CF8F38C9215C3CD | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\DeactivateAcrylicDebugLog.bat | text | |
MD5:F7C238701C9C86765F07533A6F5E9901 | SHA256:C3BEE43311311FE275CFF0626B4804DDB239330A587D7BF4884F0CC6908B6E51 | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\OpenAcrylicHostsFile.bat | text | |
MD5:EAE9E960F0321DC92B1CEABBFCBD2870 | SHA256:BE0836499A5D92F76B367A41E3AC971330ACB18313C76B4720A0F8480E4BEE9A | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\InstallAcrylicService.bat | text | |
MD5:55EA51628FF67E4EE11A7F2685A32D2F | SHA256:D2F7679E5097ED1A9AEADB7AF86ED7705FE96ACE3A7E58996C0D3AB20B69182E | |||
| 3700 | Acrylic.exe | C:\Program Files\Acrylic DNS Proxy\ActivateAcrylicDebugLog.bat | text | |
MD5:DAC41F46516D6DFC78712A1C0B5578C9 | SHA256:D67ED9F652FB2761E66865A969F8676FF4F8CA5024679DC6B070B53829F434DC | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report