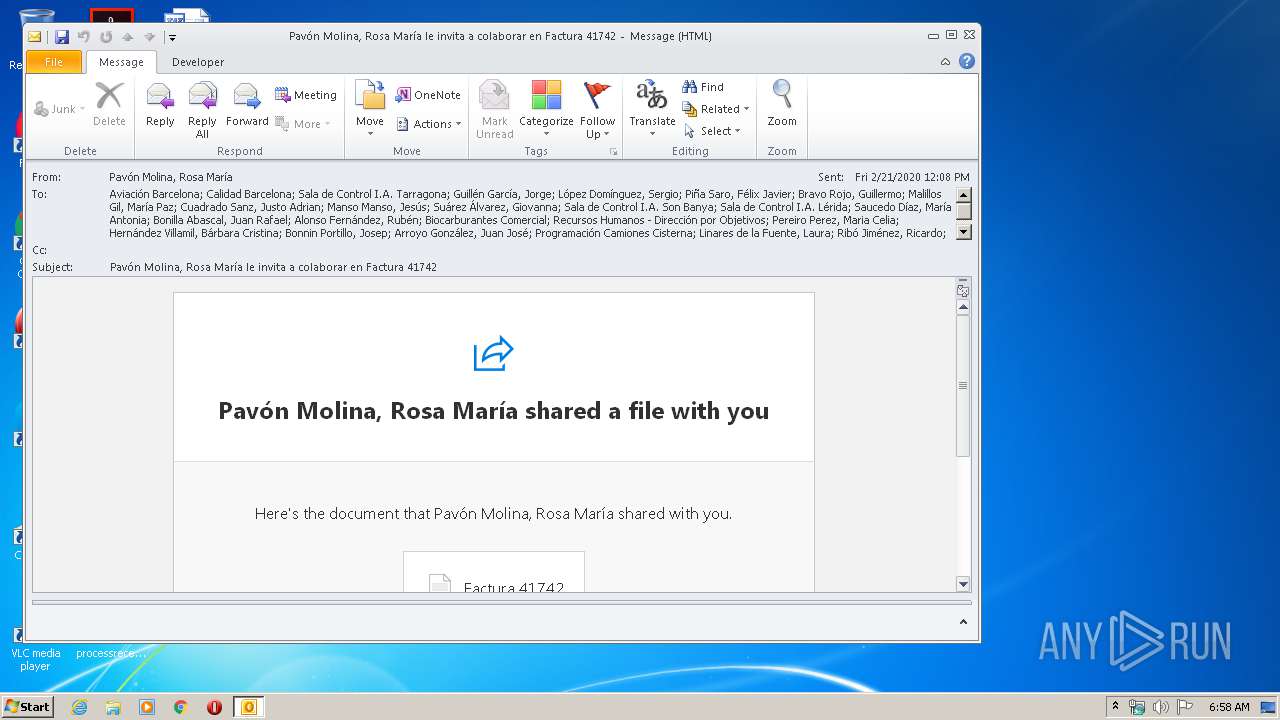
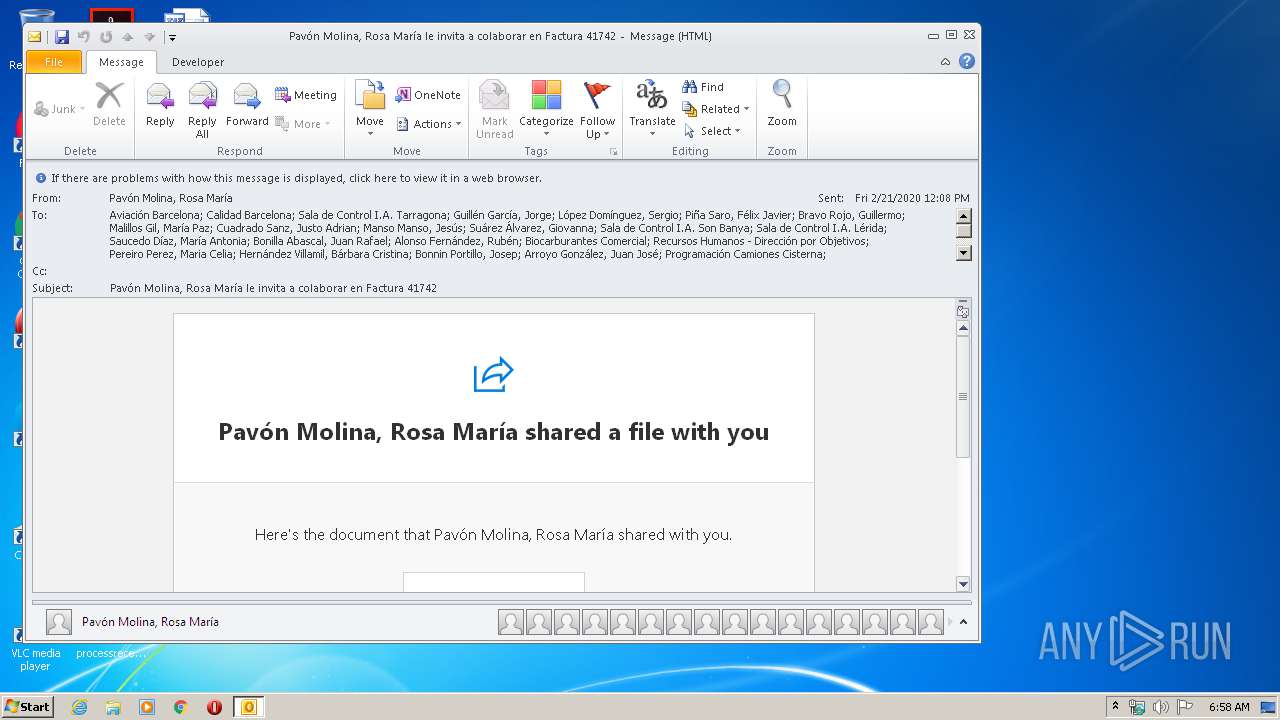
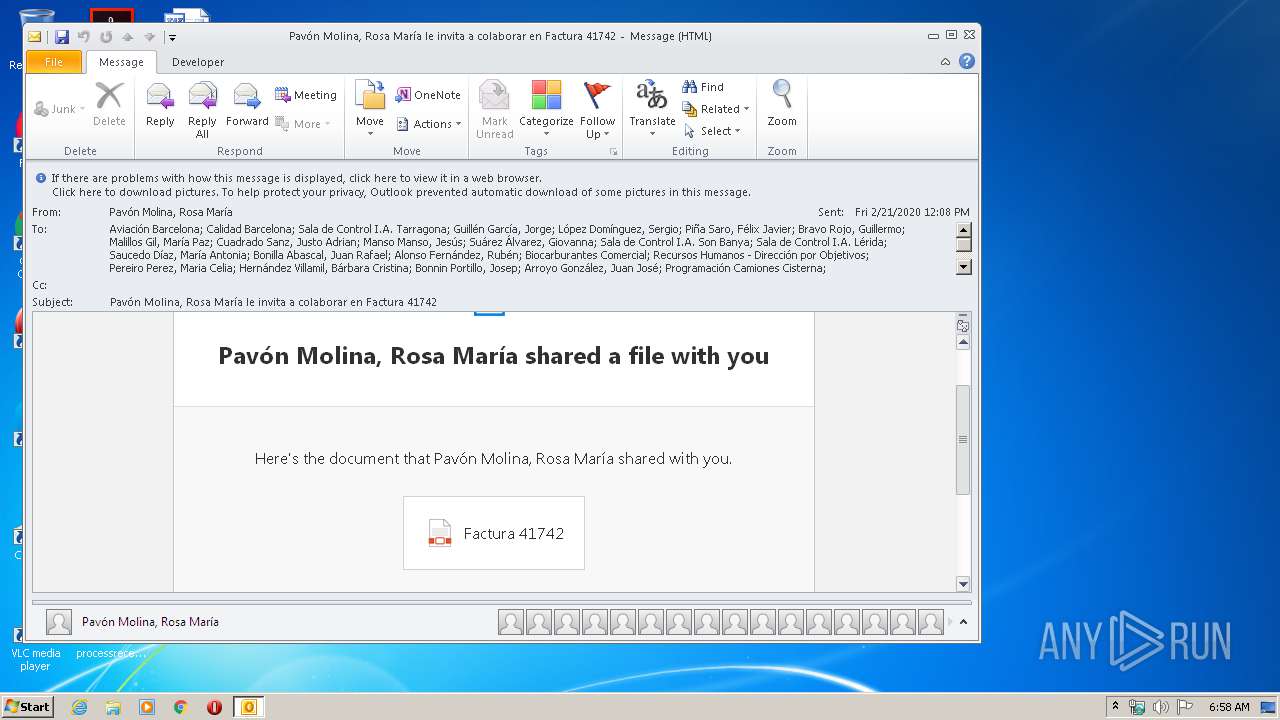
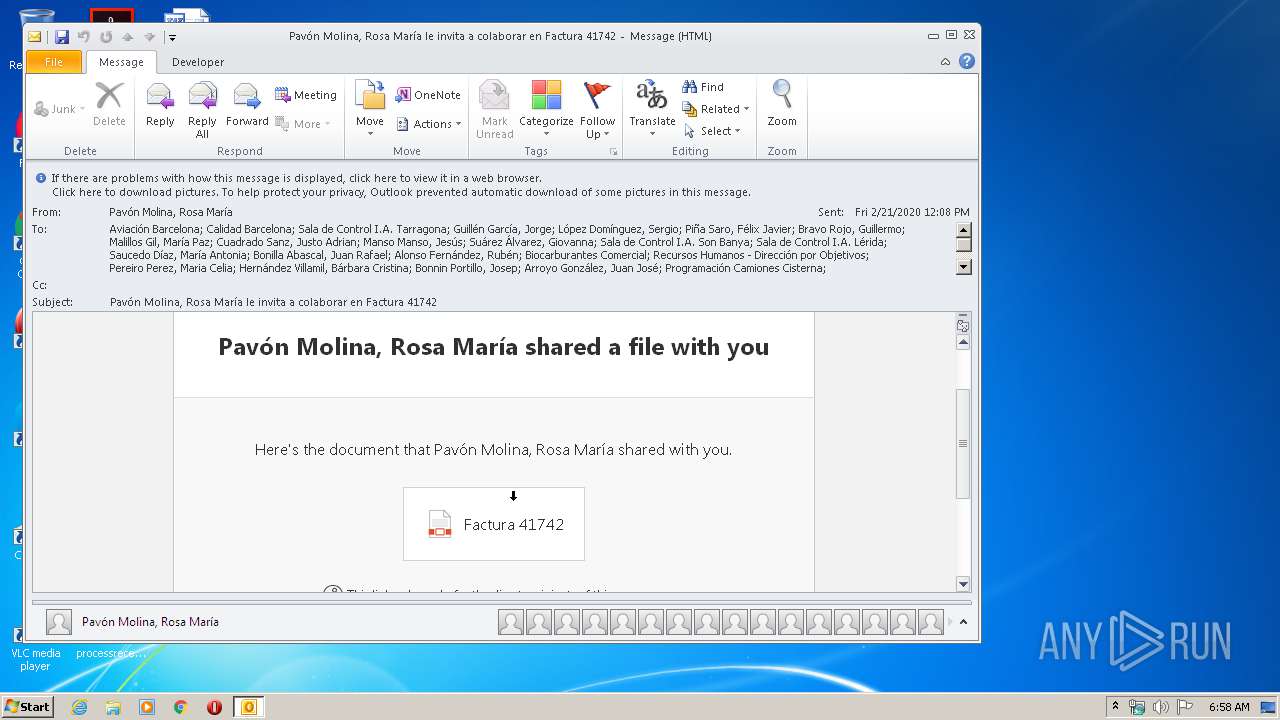
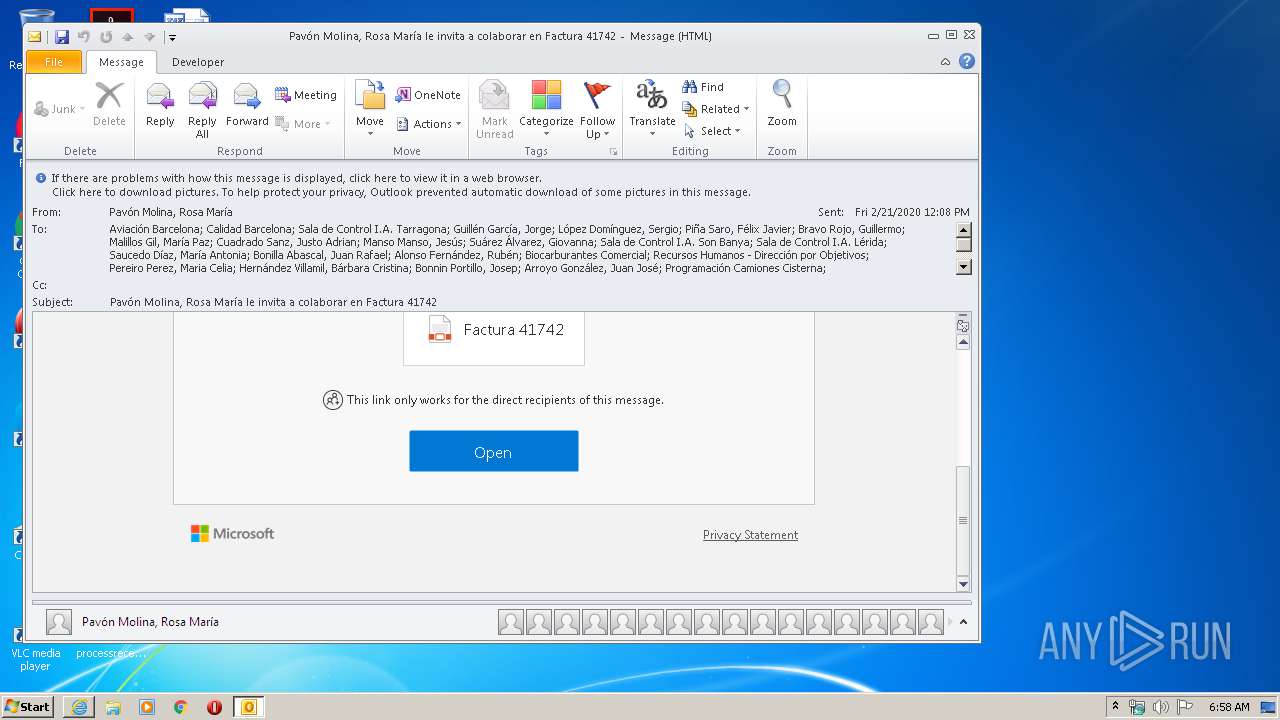
| File name: | Pavón Molina Rosa María le invita a colaborar en Factura 41742.msg |
| Full analysis: | https://app.any.run/tasks/a6846ced-76ba-4363-b073-4af85b633889 |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2020, 06:58:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 379159D79F59B3BDB4D7BD0D3C0FBE92 |
| SHA1: | 6975467A27763ACF3B8B2CAA8B2A98A74BBF5B57 |
| SHA256: | 2BF3F64FF6E2A8823E6C88BE114E73631BDA72ED9CEF9F195A9223DB8AB4D6D0 |
| SSDEEP: | 1536:fwxeK/LU5c5dAektHfyqMbr+xAduektHfCWUW2WKW3A9qoaPCufW0sW/xq3DZ3on:adCd/M/ZdEdqgovcxqTZ3BRIvvfIS |
MALICIOUS
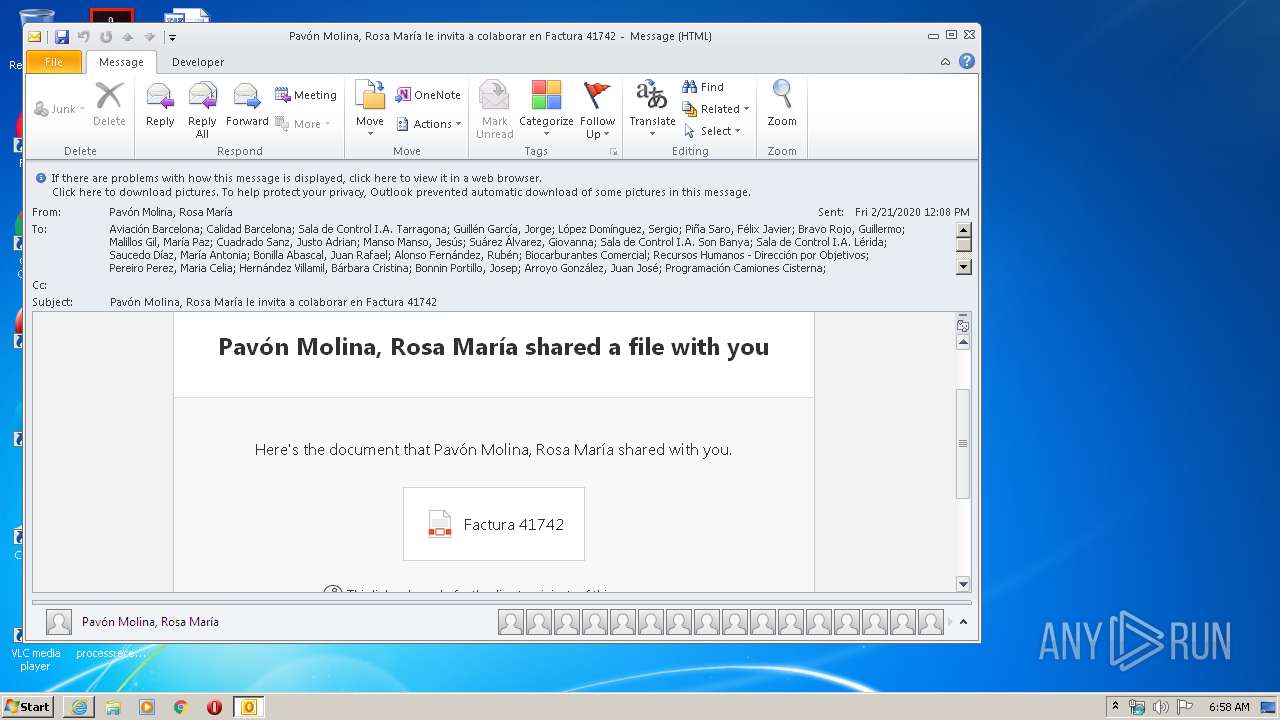
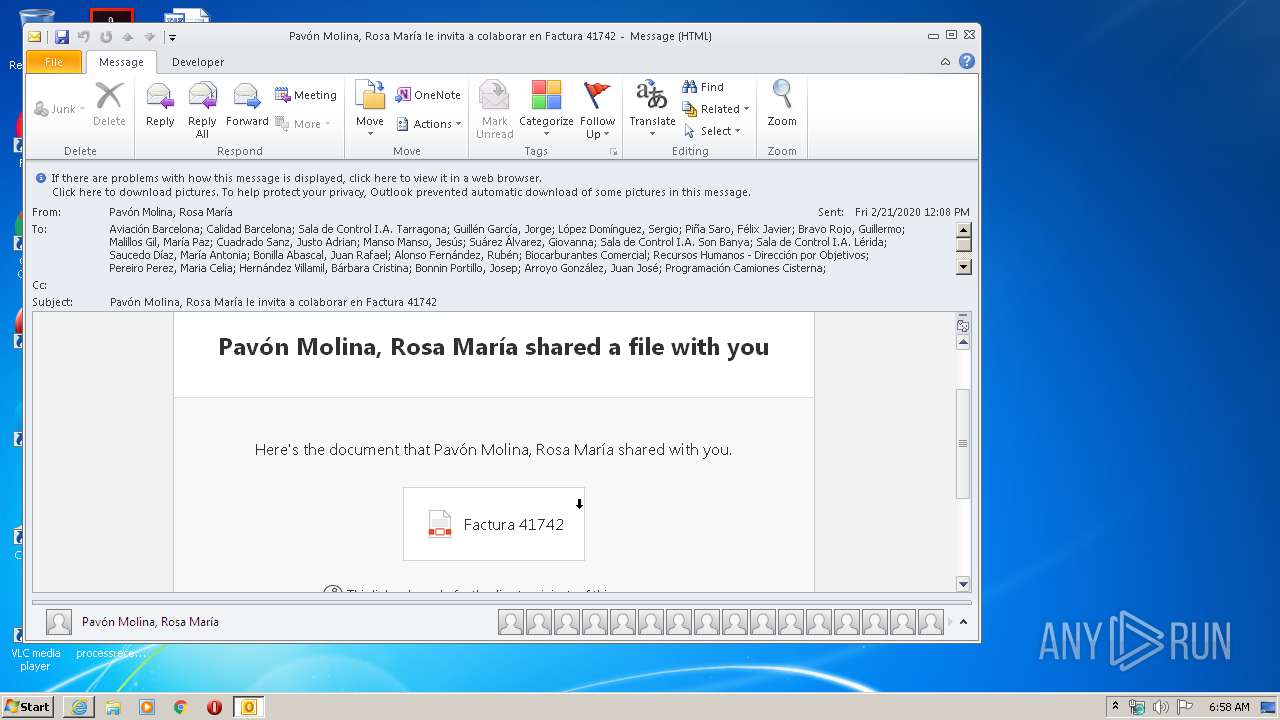
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 2884)
SUSPICIOUS
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2884)
Creates files in the user directory
- OUTLOOK.EXE (PID: 2884)
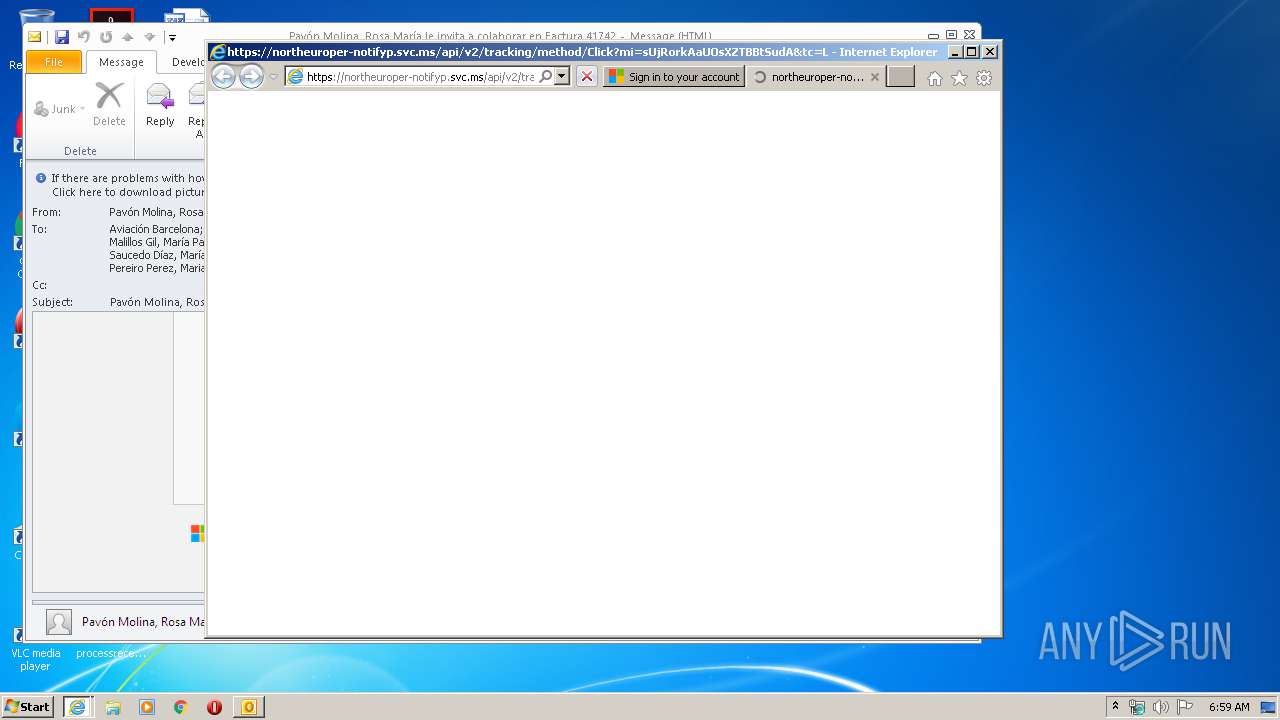
Starts Internet Explorer
- OUTLOOK.EXE (PID: 2884)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 2500)
Reads Internet Cache Settings
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2052)
- iexplore.exe (PID: 2500)
Reads internet explorer settings
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2052)
Application launched itself
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 2500)
Creates files in the user directory
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 3508)
- iexplore.exe (PID: 2052)
Reads settings of System Certificates
- iexplore.exe (PID: 3148)
- iexplore.exe (PID: 2520)
- iexplore.exe (PID: 2052)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2884)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2520)
Changes settings of System certificates
- iexplore.exe (PID: 2520)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2520)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
43
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2052 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2500 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
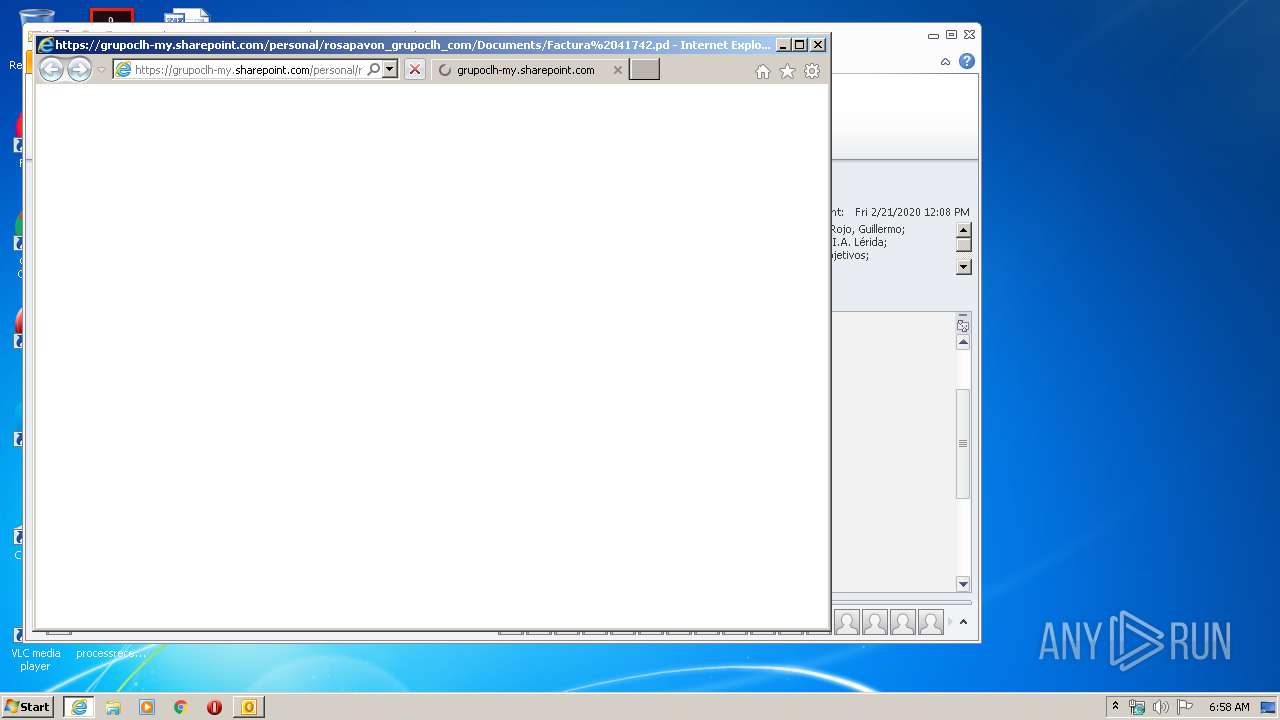
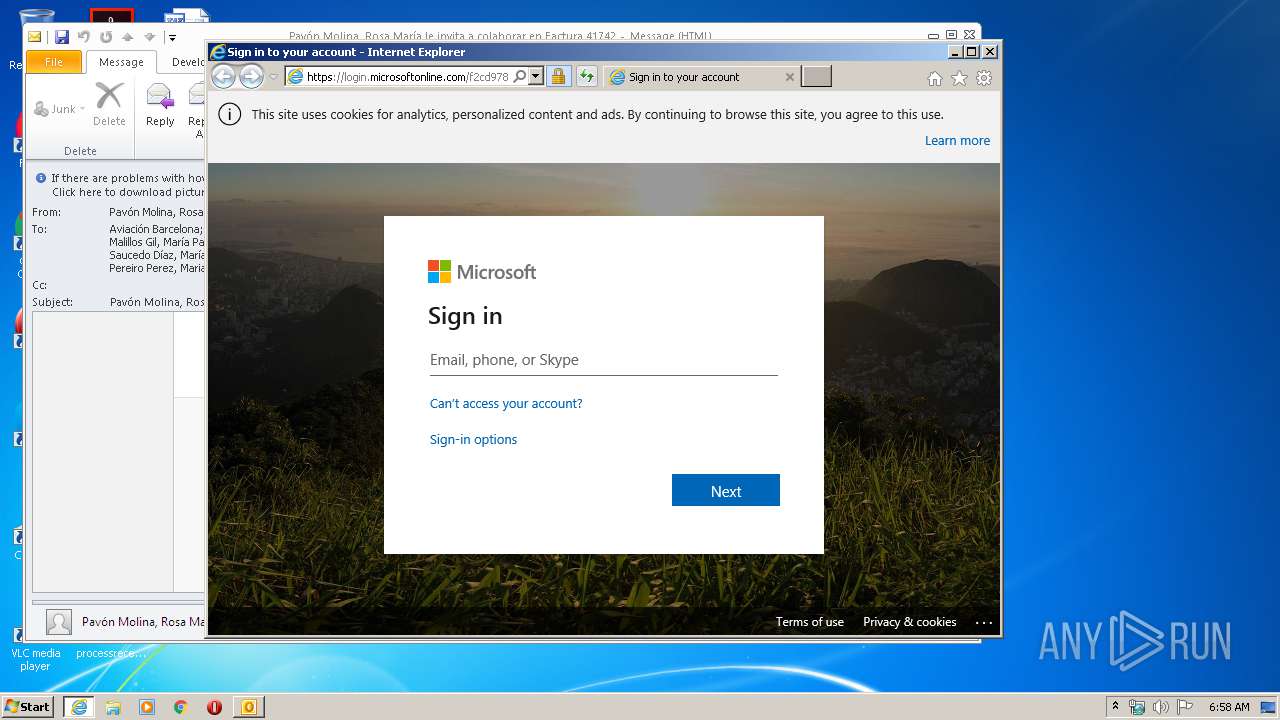
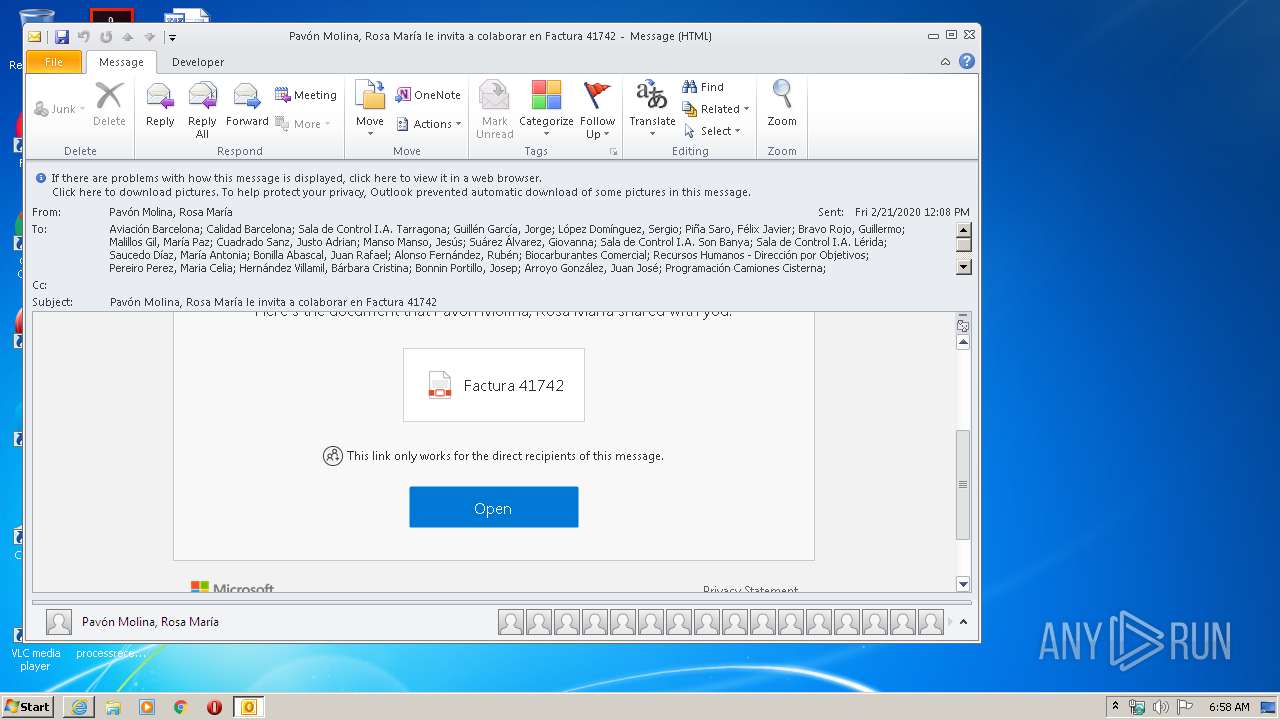
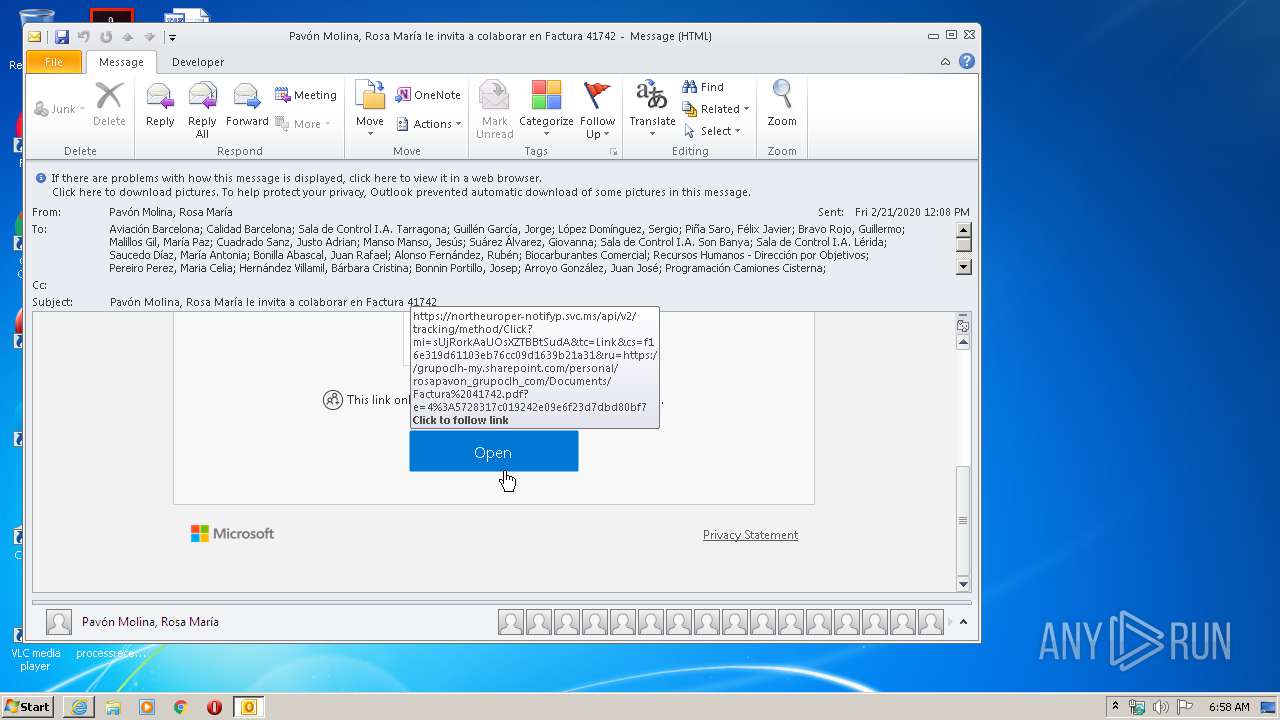
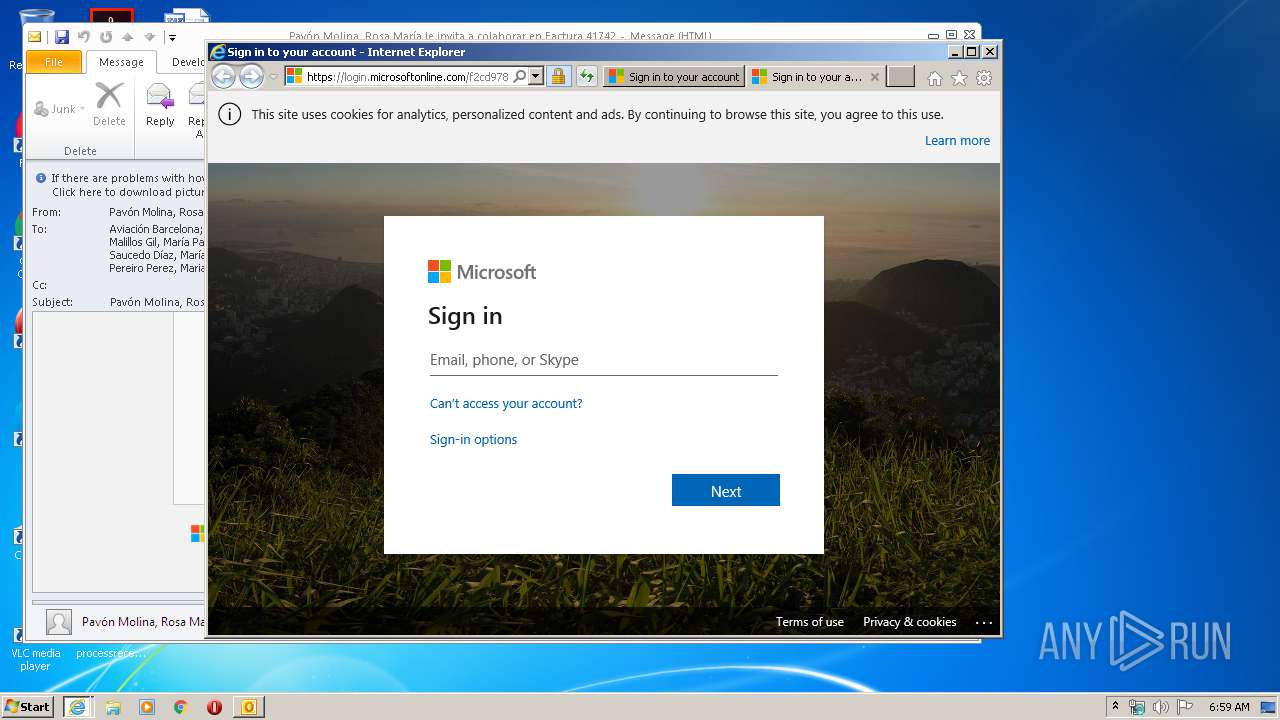
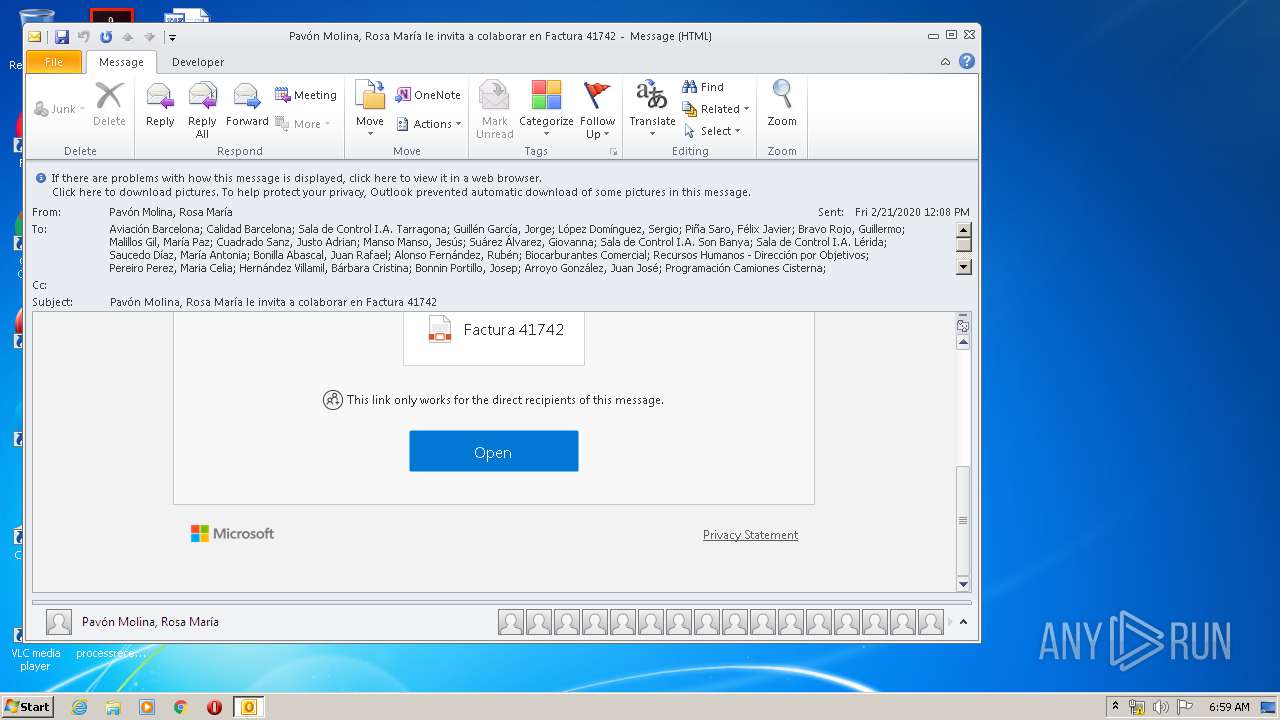
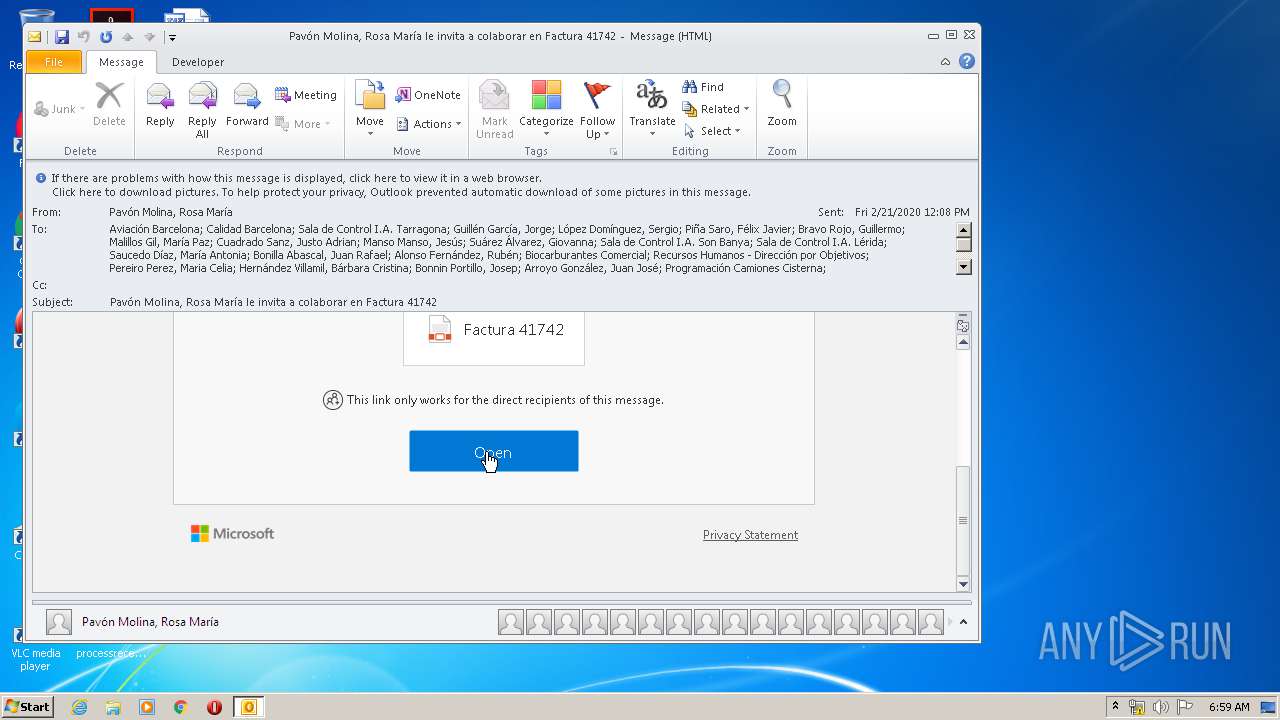
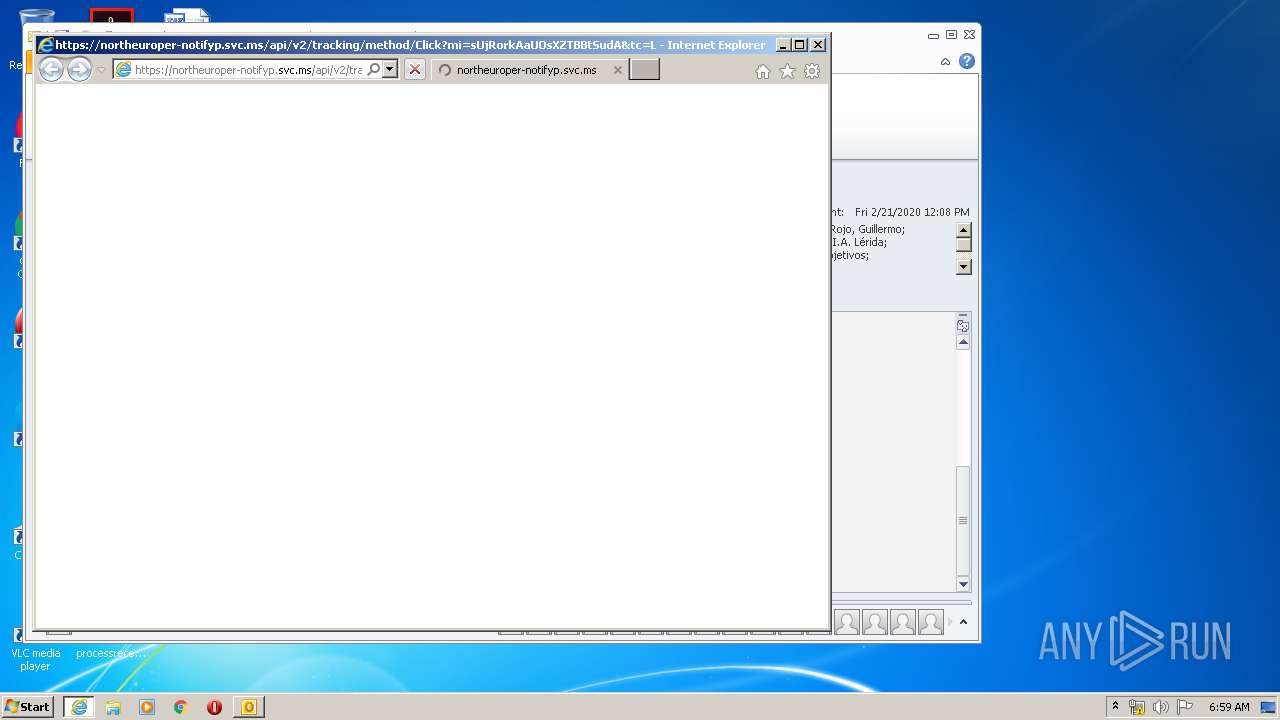
| 2500 | "C:\Program Files\Internet Explorer\iexplore.exe" https://northeuroper-notifyp.svc.ms/api/v2/tracking/method/Click?mi=sUjRorkAaUOsXZTBBtSudA&tc=Link&cs=f16e319d61103eb76cc09d1639b21a31&ru=https%3a%2f%2fgrupoclh-my.sharepoint.com%2fpersonal%2frosapavon_grupoclh_com%2fDocuments%2fFactura%252041742.pdf%3fe%3d4%253A5728317c019242e09e6f23d7dbd80bf7 | C:\Program Files\Internet Explorer\iexplore.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2520 | "C:\Program Files\Internet Explorer\iexplore.exe" https://grupoclh-my.sharepoint.com/personal/rosapavon_grupoclh_com/Documents/Factura%2041742.pdf?e=4%3a5728317c019242e09e6f23d7dbd80bf7&at=9 | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2884 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Pavón Molina Rosa María le invita a colaborar en Factura 41742.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2520 CREDAT:3347732 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3508 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2520 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
9 037
Read events
3 209
Write events
4 089
Delete events
1 739
Modification events
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (2884) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
34
Text files
58
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2884 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR5EC2.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab9449.tmp | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar944A.tmp | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\U3LCW29U.txt | — | |
MD5:— | SHA256:— | |||
| 3508 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\S5BJGCLW.txt | — | |
MD5:— | SHA256:— | |||
| 2884 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2884 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 2884 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\FB1EDC9F.dat | image | |
MD5:1E13EE0ED09C4AF1ADFB6C0D280879B0 | SHA256:E2395FBA25D3FB8A971345CA65D144F7D9C9D933F70409165446E63D18C0958D | |||
| 2884 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\{152C909C-203F-4553-9441-F0B169368B6D}\{1C306CB1-771E-4B4B-A902-86E897877F5B}.png | image | |
MD5:4C61C12EDBC453D7AE184976E95258E1 | SHA256:296526F9A716C1AA91BA5D6F69F0EB92FDF79C2CB2CFCF0CEB22B7CCBC27035F | |||
| 2884 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\F3D6142.dat | image | |
MD5:10756BD9D810A0202CF4B5E7828160C0 | SHA256:8BA923AECE3E1731B7CDF398D30EEE632B285A5CC91F3E6A062BB72713F38644 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
42
DNS requests
20
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
3508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAiIzVJfGSRETRSlgpHeuVI%3D | US | der | 1.47 Kb | whitelisted |
2884 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
2520 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAi4elAbvpzaLRZNPjlRv1U%3D | US | der | 1.47 Kb | whitelisted |
3508 | iexplore.exe | GET | 200 | 104.18.24.243:80 | http://ocsp.msocsp.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPC1vZt9qvn7bzY3Iidtbhla4mKQQUWIif1tycSCK3FD7%2FhIjo5oX%2F%2Bn0CE3sAAvTsRon4%2BRVzrdwAAAAC9Ow%3D | US | der | 1.79 Kb | whitelisted |
3508 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAtqs7A%2Bsan2xGCSaqjN%2FrM%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
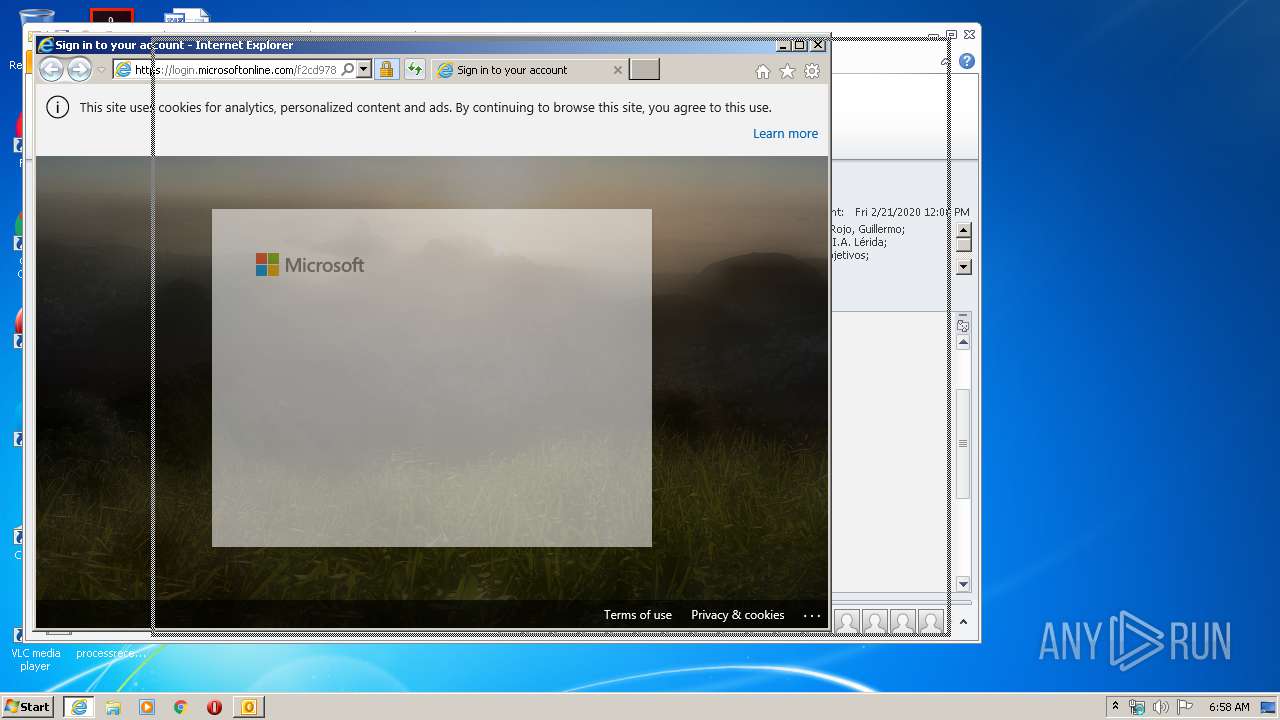
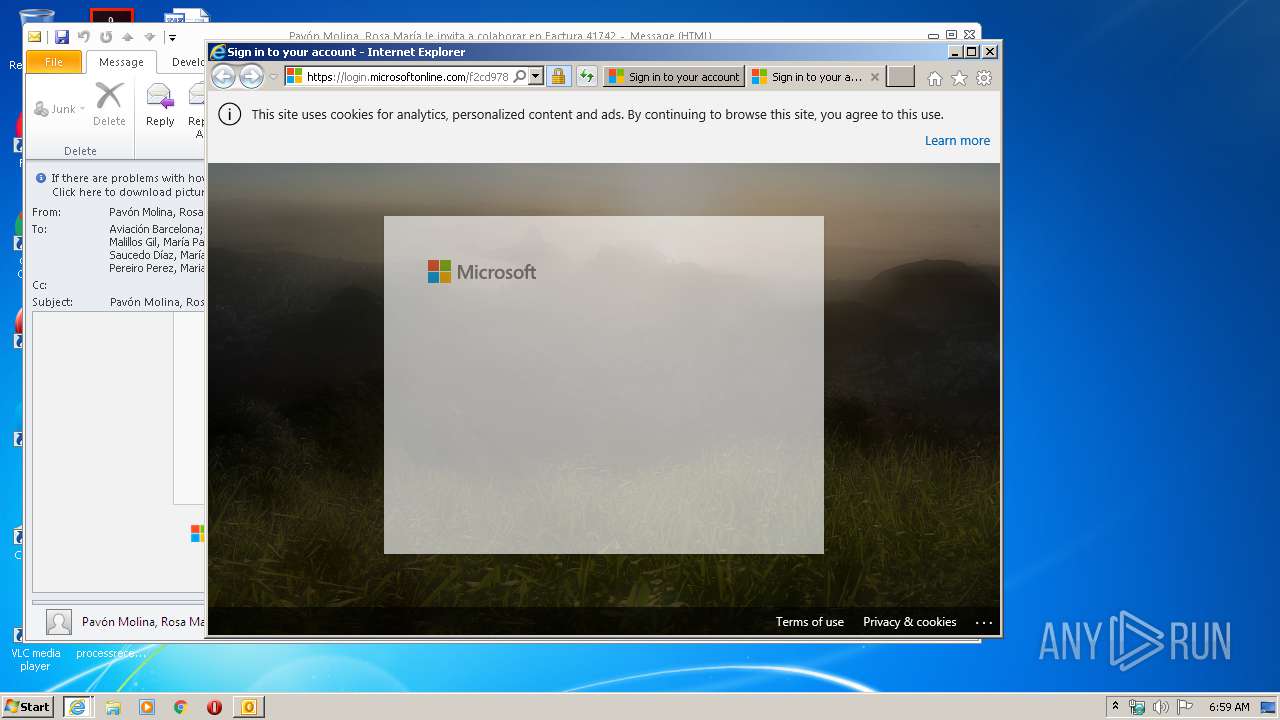
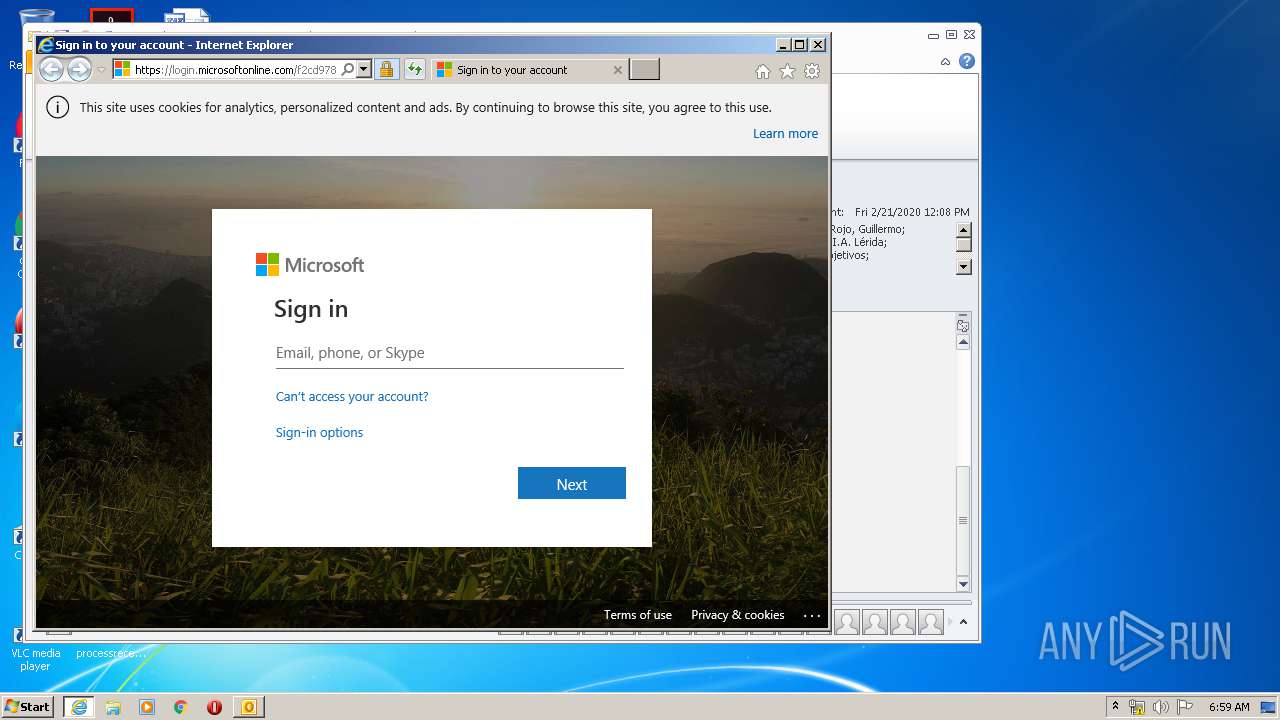
3148 | iexplore.exe | 20.190.129.162:443 | login.windows.net | Microsoft Corporation | US | unknown |
3148 | iexplore.exe | 13.107.246.10:443 | aadcdn.msauth.net | Microsoft Corporation | US | whitelisted |
3148 | iexplore.exe | 40.126.1.136:443 | login.windows.net | Microsoft Corporation | US | unknown |
2520 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2052 | iexplore.exe | 40.126.1.136:443 | login.windows.net | Microsoft Corporation | US | unknown |
2520 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2052 | iexplore.exe | 20.190.129.162:443 | login.windows.net | Microsoft Corporation | US | unknown |
2884 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3508 | iexplore.exe | 13.107.136.9:443 | grupoclh-my.sharepoint.com | Microsoft Corporation | US | whitelisted |
3508 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
grupoclh-my.sharepoint.com |
| suspicious |
ocsp.digicert.com |
| whitelisted |
login.windows.net |
| whitelisted |
login.microsoftonline.com |
| whitelisted |
ocsp.msocsp.com |
| whitelisted |
aadcdn.msauth.net |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
northeuroper-notifyp.svc.ms |
| suspicious |