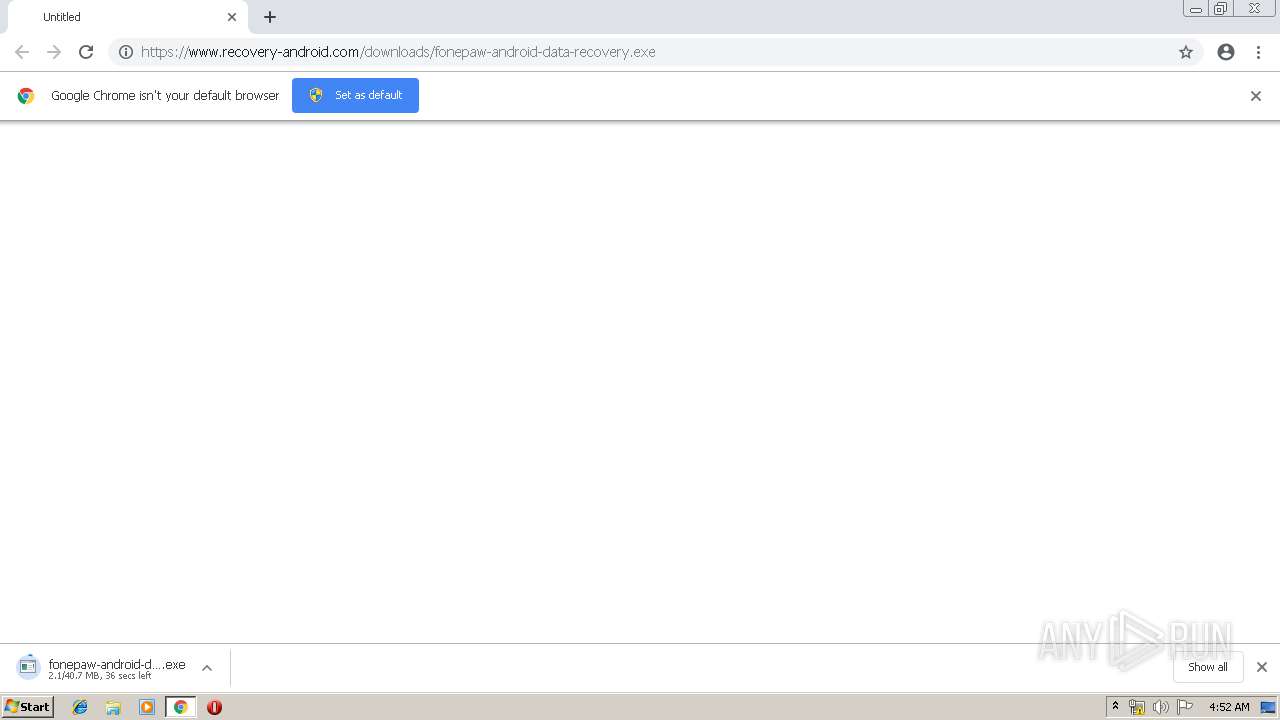
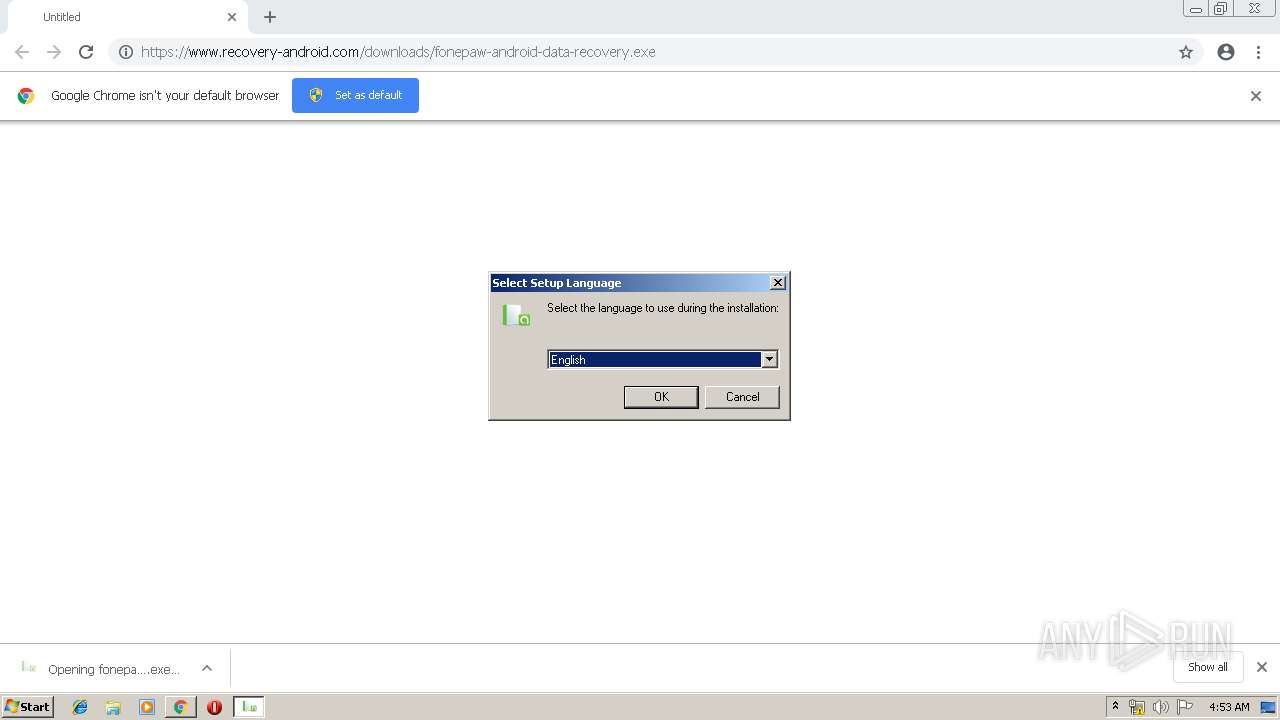
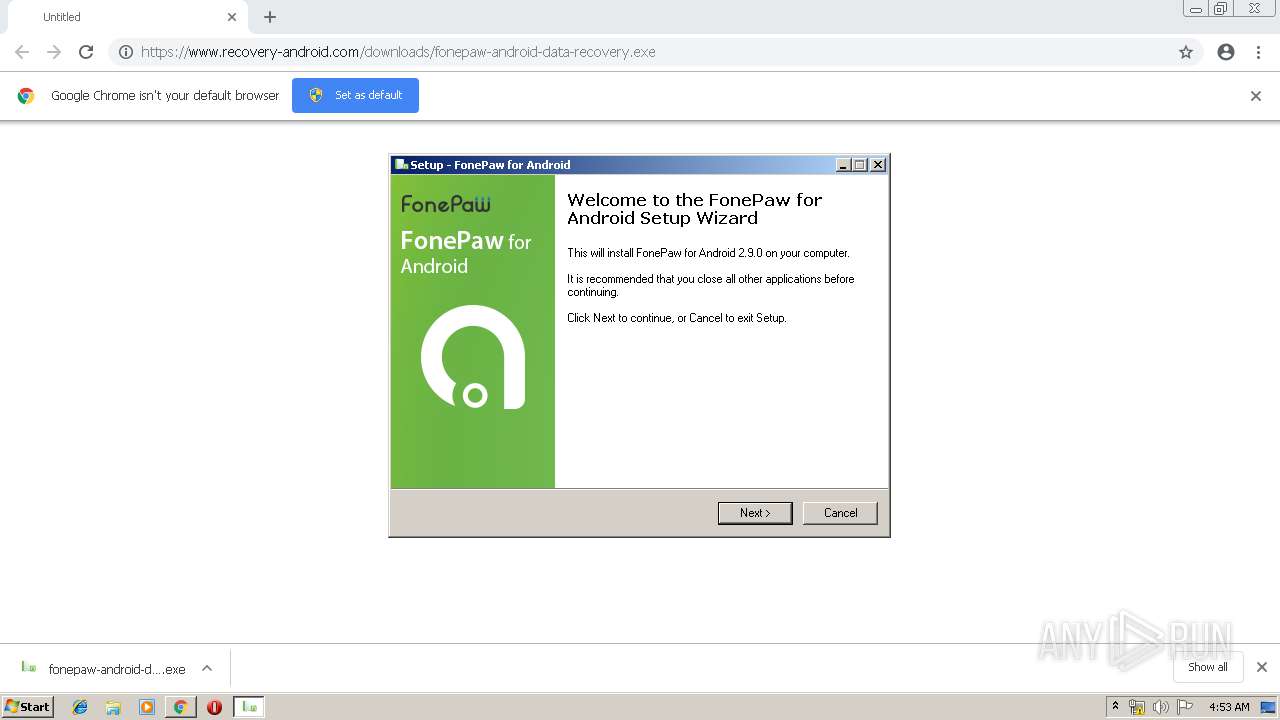
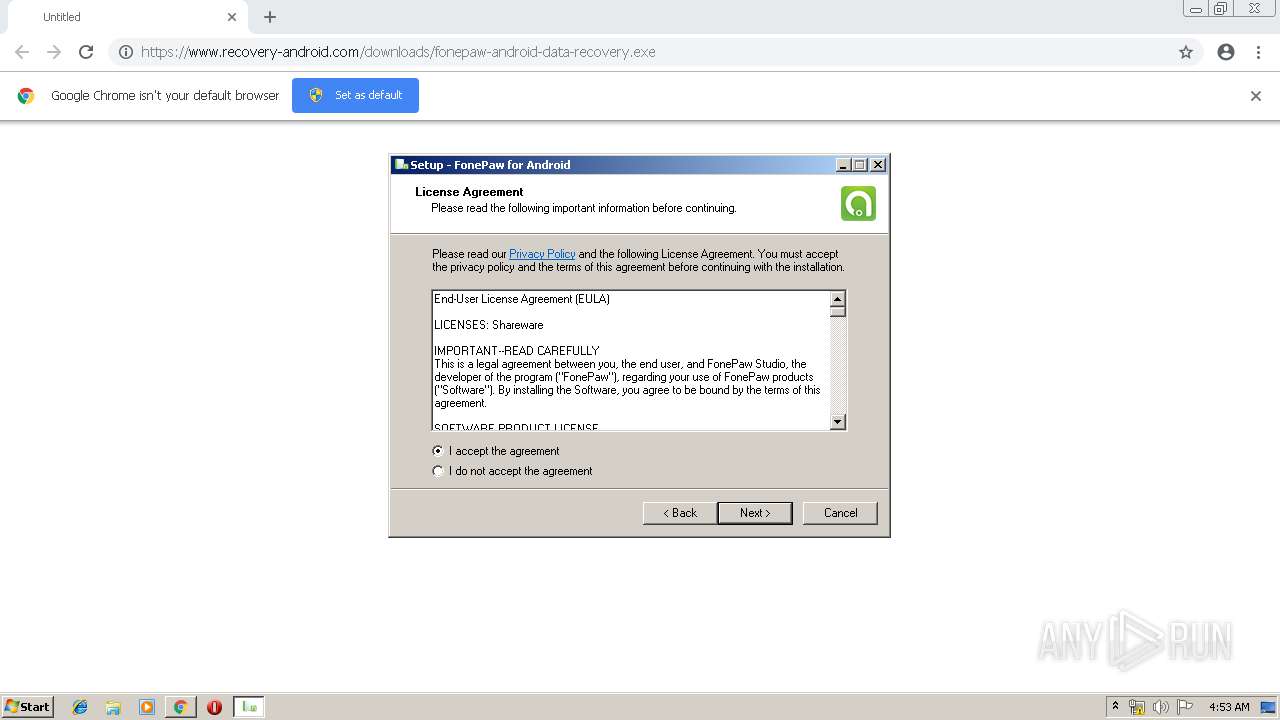
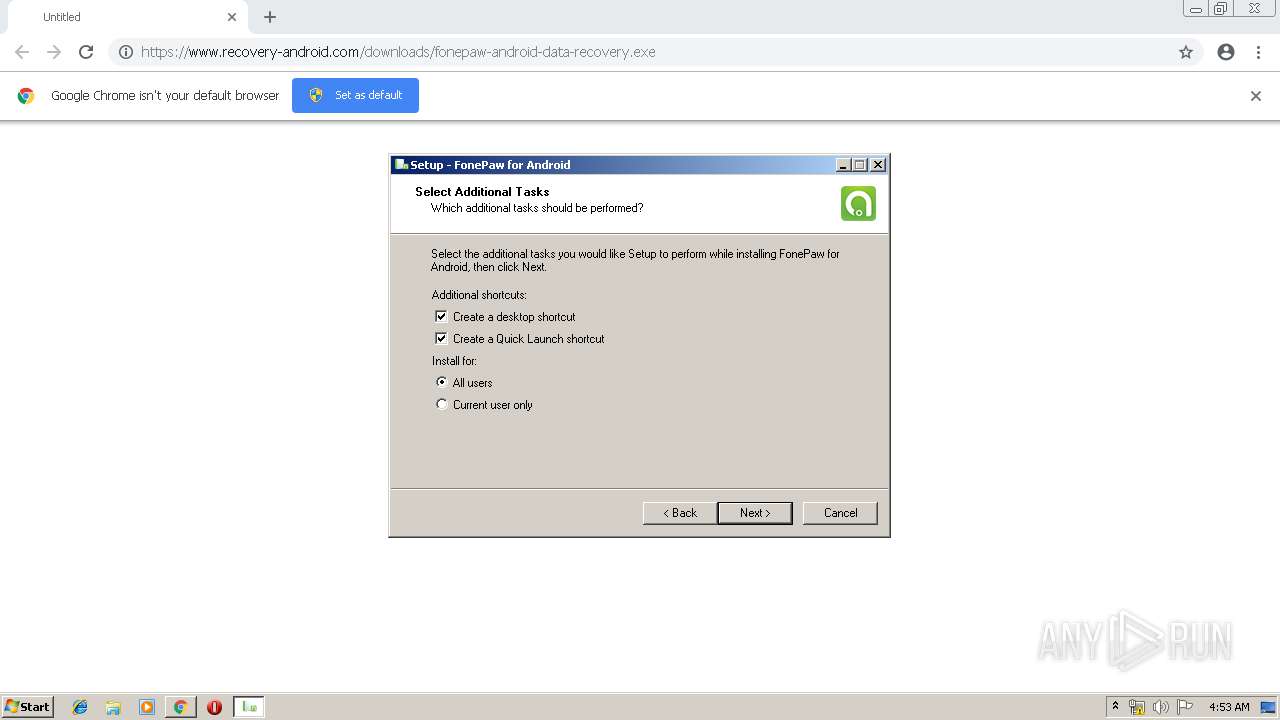
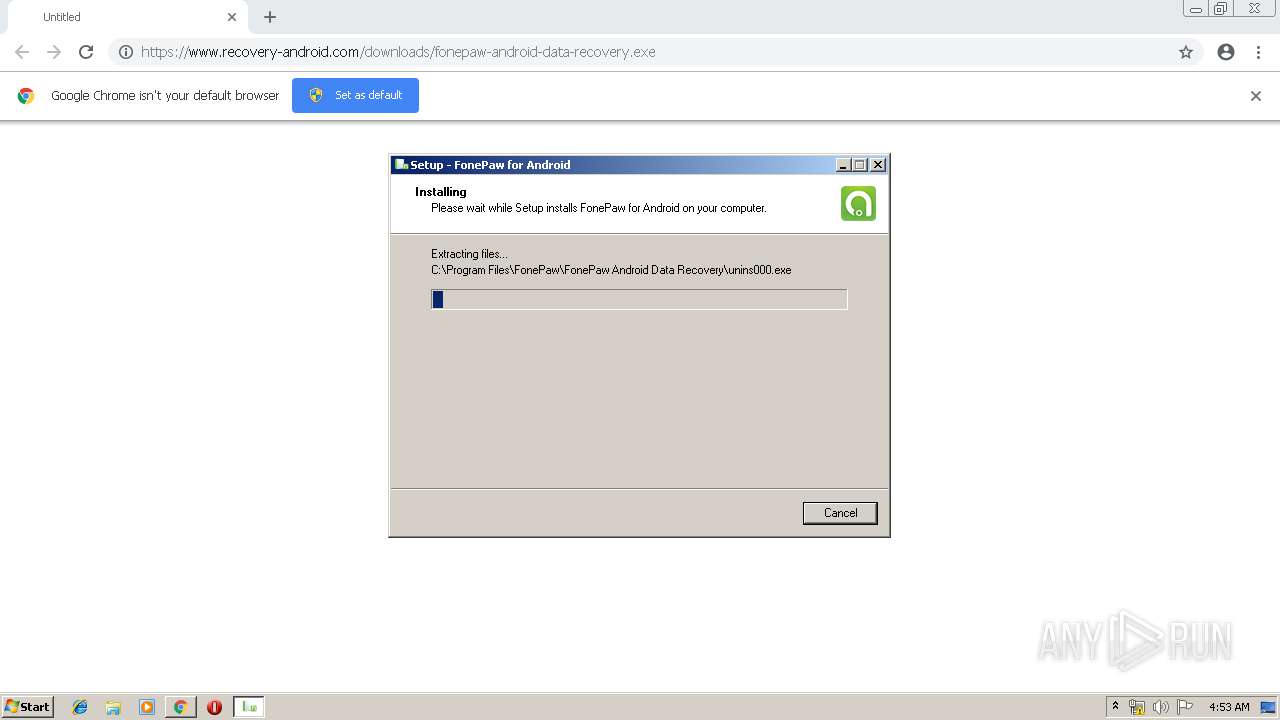
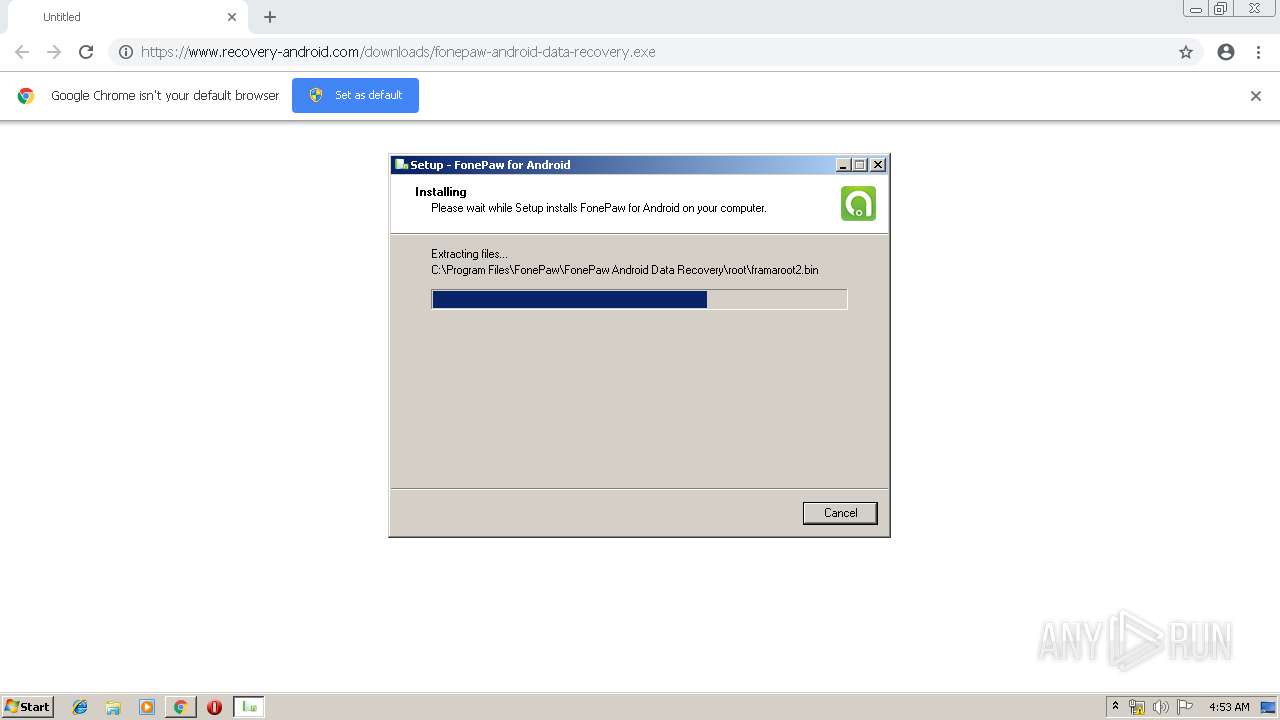
| URL: | https://www.recovery-android.com/downloads/fonepaw-android-data-recovery.exe |
| Full analysis: | https://app.any.run/tasks/2abfa9d6-08c8-4947-853b-c8c3a823cb9b |
| Verdict: | Malicious activity |
| Analysis date: | March 26, 2019, 04:51:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A7C74C0907F3D42430B680E90D14B879 |
| SHA1: | 18C322A7A359141B89C149D42788177D0F56B1D8 |
| SHA256: | 2BE9CE12EC820A4F4916C0F3E079CFD22C1D760D6A57E0742C1E709B2180411F |
| SSDEEP: | 3:N8DSLQRNcAmXK4S18JCU:2OLQ3jma4gACU |
MALICIOUS
Application was dropped or rewritten from another process
- fonepaw-android-data-recovery.exe (PID: 4012)
- SDInst.exe (PID: 1400)
- fonepaw-android-data-recovery.exe (PID: 3664)
- FonePaw Android Data Recovery.exe (PID: 2156)
- SDInst.exe (PID: 636)
- SDInst.exe (PID: 3828)
- SDInst86.exe (PID: 2528)
- SDInst86.exe (PID: 3492)
- SDInst86.exe (PID: 3596)
- FonePaw Android Data Recovery.exe (PID: 1096)
- FonePaw Android Data Recovery.exe (PID: 3964)
- FonePaw Android Data Recovery.exe (PID: 2520)
- splashScreen.exe (PID: 3656)
- adb.exe (PID: 1248)
- adb.exe (PID: 2824)
Loads dropped or rewritten executable
- FonePaw Android Data Recovery.exe (PID: 2156)
- SDInst.exe (PID: 3828)
- SDInst.exe (PID: 1400)
- SDInst.exe (PID: 636)
- FonePaw Android Data Recovery.exe (PID: 1096)
- FonePaw Android Data Recovery.exe (PID: 3964)
- FonePaw Android Data Recovery.exe (PID: 2520)
- splashScreen.exe (PID: 3656)
- adb.exe (PID: 1248)
- adb.exe (PID: 2824)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1952)
- fonepaw-android-data-recovery.exe (PID: 4012)
- fonepaw-android-data-recovery.tmp (PID: 2728)
- SDInst86.exe (PID: 2528)
- DrvInst.exe (PID: 1892)
- SDInst86.exe (PID: 3492)
- SDInst86.exe (PID: 3596)
- DrvInst.exe (PID: 3728)
- DrvInst.exe (PID: 2236)
Reads the Windows organization settings
- fonepaw-android-data-recovery.tmp (PID: 2728)
Reads Windows owner or organization settings
- fonepaw-android-data-recovery.tmp (PID: 2728)
Creates files in the user directory
- fonepaw-android-data-recovery.tmp (PID: 2728)
Removes files from Windows directory
- DrvInst.exe (PID: 1892)
- DrvInst.exe (PID: 3728)
- DrvInst.exe (PID: 2236)
Creates files in the Windows directory
- DrvInst.exe (PID: 1892)
- DrvInst.exe (PID: 3728)
- DrvInst.exe (PID: 2236)
- SDInst86.exe (PID: 2528)
Creates files in the driver directory
- DrvInst.exe (PID: 1892)
- DrvInst.exe (PID: 2236)
- DrvInst.exe (PID: 3728)
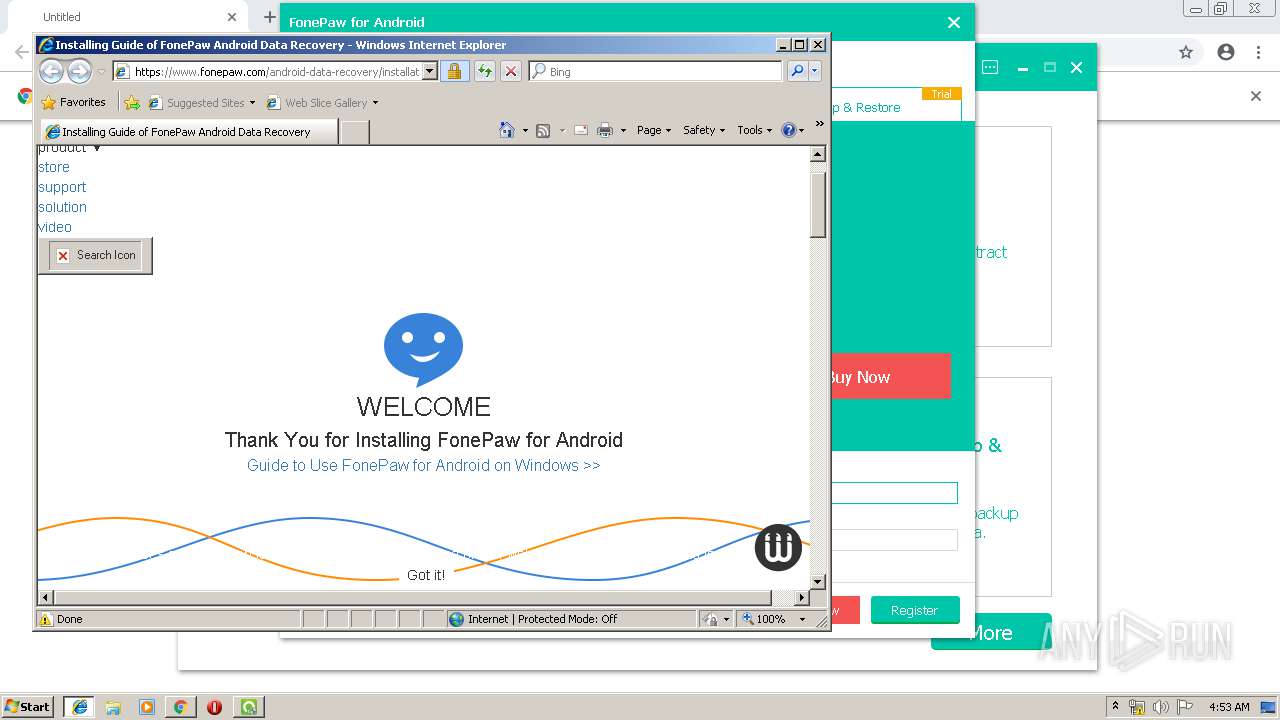
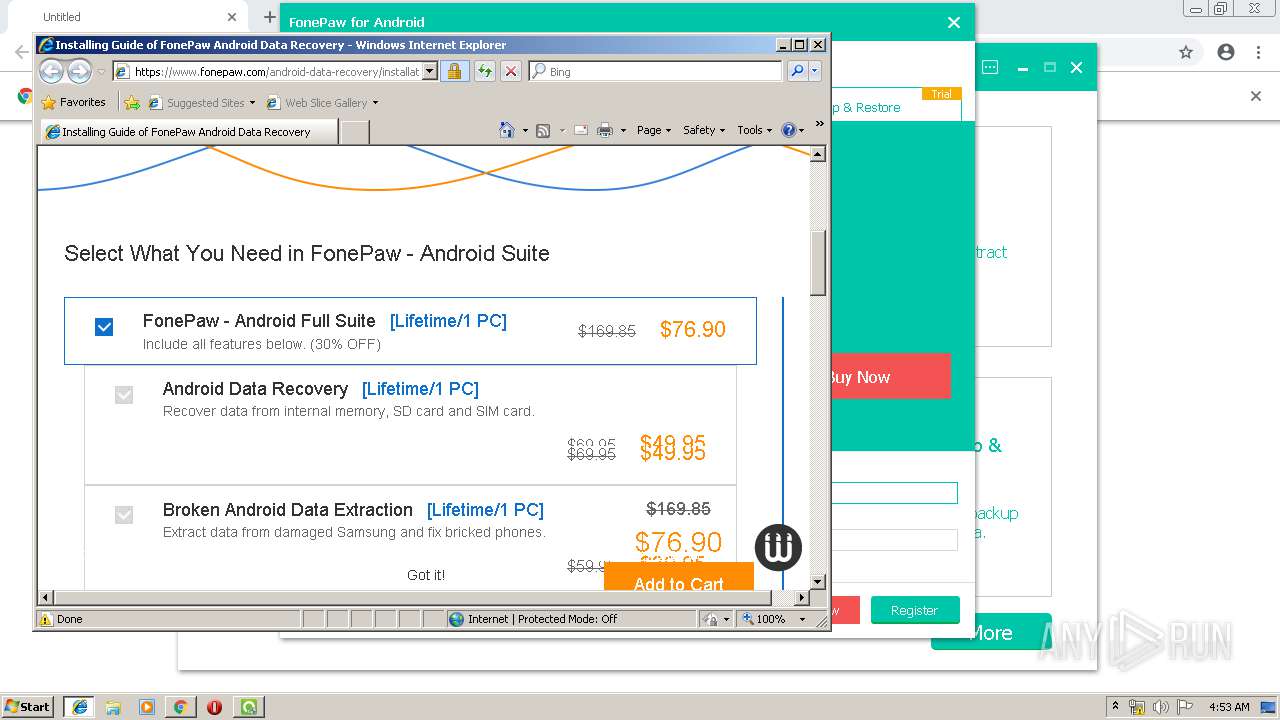
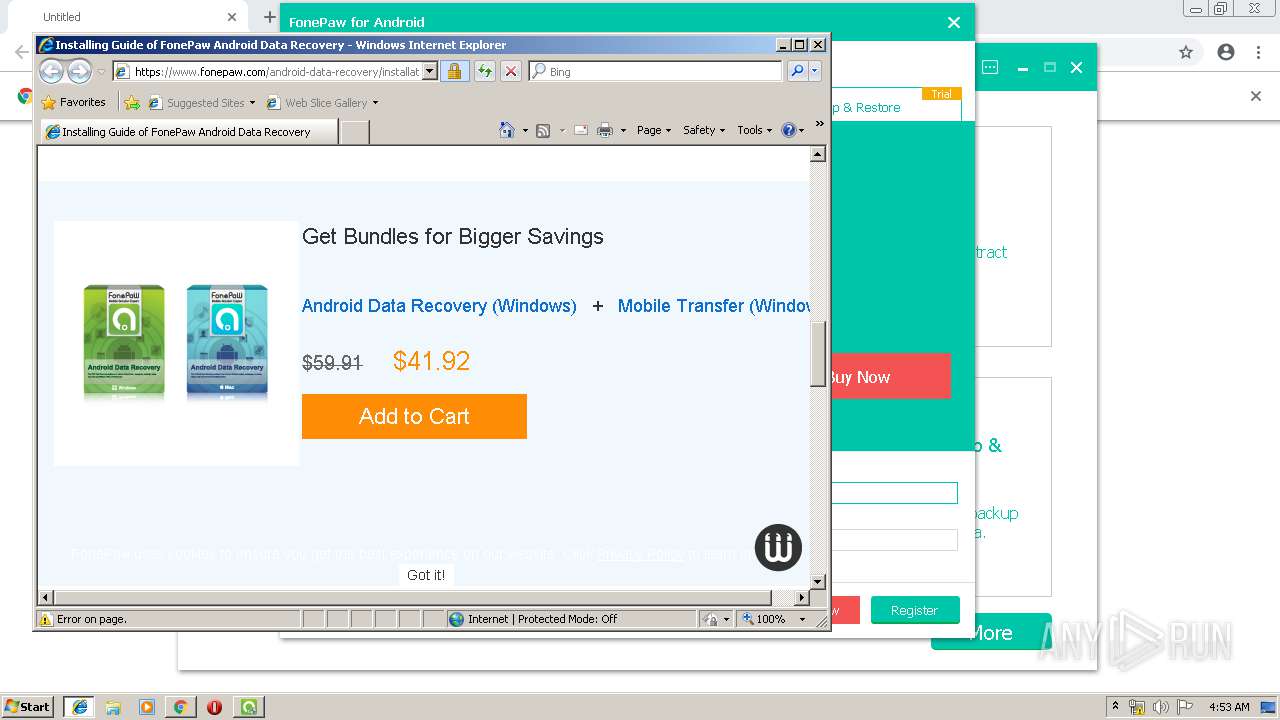
Starts Internet Explorer
- FonePaw Android Data Recovery.exe (PID: 3964)
Application launched itself
- adb.exe (PID: 1248)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1952)
Creates files in the program directory
- iexplore.exe (PID: 3376)
INFO
Application launched itself
- chrome.exe (PID: 1952)
- iexplore.exe (PID: 3412)
Reads settings of System Certificates
- chrome.exe (PID: 2884)
- DrvInst.exe (PID: 1892)
Application was dropped or rewritten from another process
- fonepaw-android-data-recovery.tmp (PID: 2728)
Loads dropped or rewritten executable
- fonepaw-android-data-recovery.tmp (PID: 2728)
Dropped object may contain Bitcoin addresses
- fonepaw-android-data-recovery.tmp (PID: 2728)
Creates a software uninstall entry
- fonepaw-android-data-recovery.tmp (PID: 2728)
Creates files in the program directory
- fonepaw-android-data-recovery.tmp (PID: 2728)
Changes settings of System certificates
- DrvInst.exe (PID: 1892)
- iexplore.exe (PID: 3376)
Adds / modifies Windows certificates
- DrvInst.exe (PID: 1892)
- iexplore.exe (PID: 3376)
Creates files in the user directory
- iexplore.exe (PID: 3376)
Reads internet explorer settings
- iexplore.exe (PID: 3376)
Changes internet zones settings
- iexplore.exe (PID: 3412)
Reads Internet Cache Settings
- iexplore.exe (PID: 3376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
77
Monitored processes
38
Malicious processes
16
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1344 --on-initialized-event-handle=308 --parent-handle=312 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 636 | "C:\Program Files\FonePaw\FonePaw Android Data Recovery\SDInst.exe" "C:\Program Files\FonePaw\FonePaw Android Data Recovery\driver\samsung\ssudmdm.inf" | C:\Program Files\FonePaw\FonePaw Android Data Recovery\SDInst.exe | — | fonepaw-android-data-recovery.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: Install drivers from inf Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=11111674734104713905 --mojo-platform-channel-handle=1912 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 932 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=904,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=112456382955431571 --mojo-platform-channel-handle=2764 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=904,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=15219430776544791009 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15219430776544791009 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3864 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
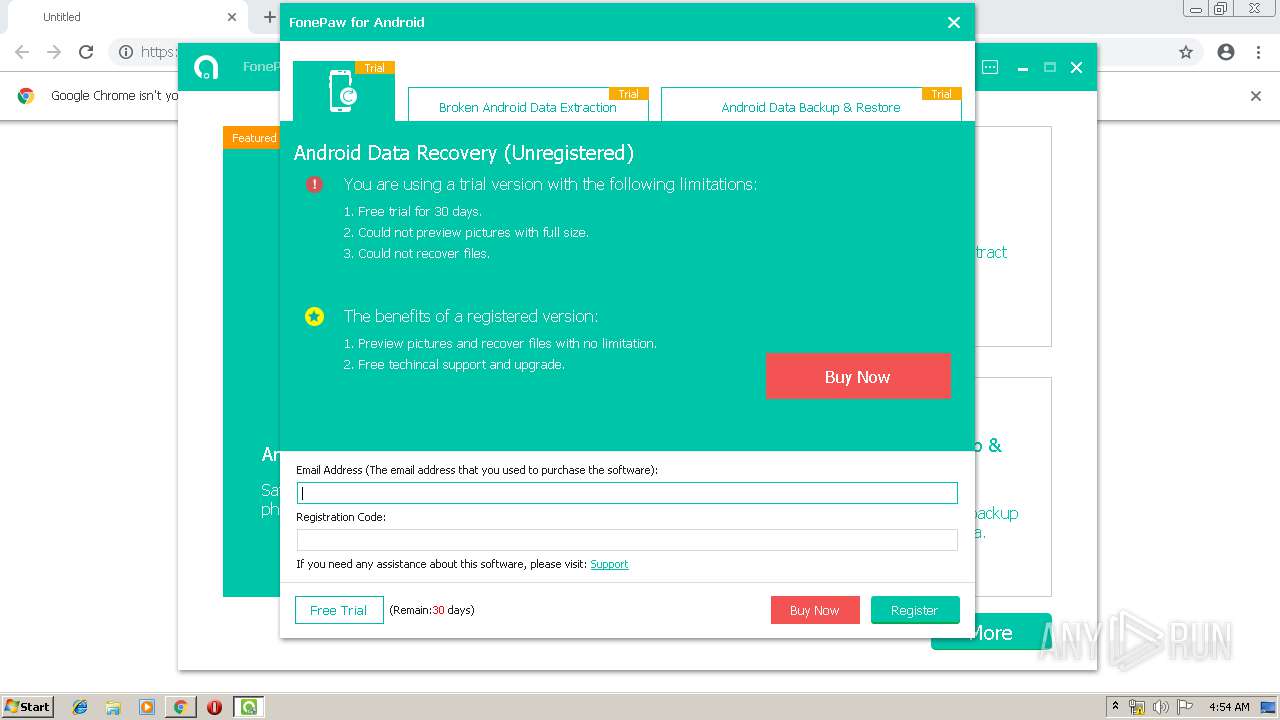
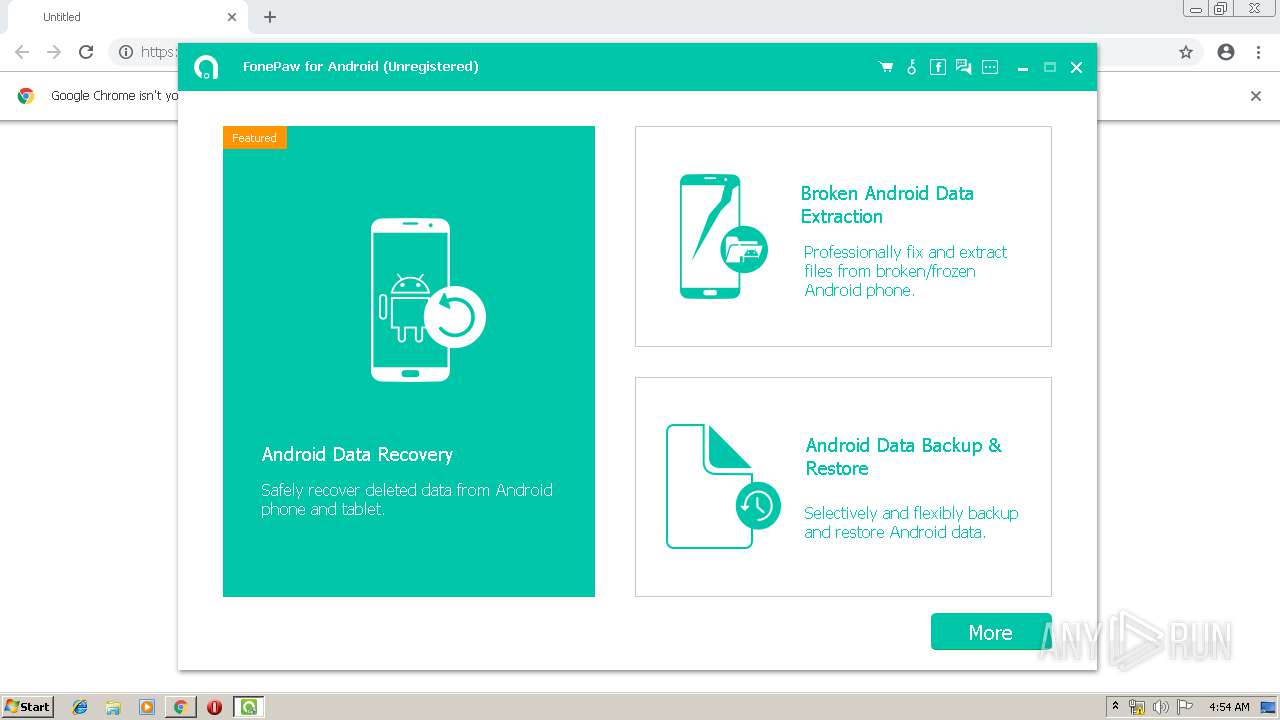
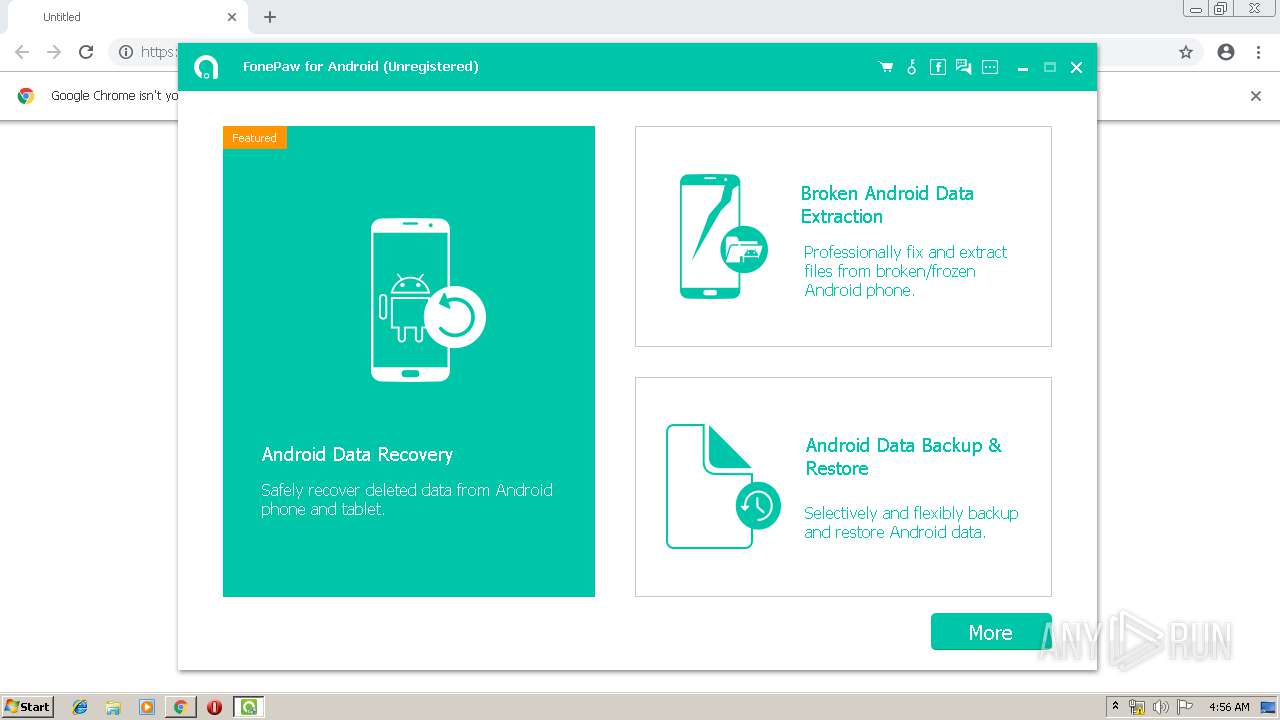
| 1096 | "C:\Program Files\FonePaw\FonePaw Android Data Recovery\FonePaw Android Data Recovery.exe" | C:\Program Files\FonePaw\FonePaw Android Data Recovery\FonePaw Android Data Recovery.exe | fonepaw-android-data-recovery.tmp | ||||||||||||
User: admin Company: FonePaw Integrity Level: HIGH Description: FonePaw for Android Exit code: 0 Version: 2.9.0.81231 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\FonePaw\FonePaw Android Data Recovery\adb\adb" devices | C:\Program Files\FonePaw\FonePaw Android Data Recovery\adb\adb.exe | FonePaw Android Data Recovery.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6f470f18,0x6f470f28,0x6f470f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\FonePaw\FonePaw Android Data Recovery\SDInst.exe" "C:\Program Files\FonePaw\FonePaw Android Data Recovery\driver\samsung\ssudbus.inf" | C:\Program Files\FonePaw\FonePaw Android Data Recovery\SDInst.exe | — | fonepaw-android-data-recovery.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: Install drivers from inf Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1424 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=904,987707299793125473,13128759475607623369,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=322815080611301516 --mojo-platform-channel-handle=880 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 861
Read events
1 499
Write events
352
Delete events
10
Modification events
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1952-13198049525769625 |
Value: 259 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (1952) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
114
Suspicious files
74
Text files
268
Unknown types
75
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7ad0aa7b-9306-424e-a427-8fdbc268989d.tmp | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1952 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
46
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1096 | FonePaw Android Data Recovery.exe | GET | 200 | 50.22.1.104:80 | http://config.aokreg.com/adr/win/root/root.suggest | US | xml | 8.14 Kb | suspicious |
1096 | FonePaw Android Data Recovery.exe | GET | 200 | 50.22.1.104:80 | http://config.aokreg.com/adr/win/purchase.xml | US | xml | 3.10 Kb | suspicious |
2884 | chrome.exe | GET | 302 | 172.217.18.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
1096 | FonePaw Android Data Recovery.exe | GET | 200 | 50.22.1.104:80 | http://config.aokreg.com/adr/win/db/device.sqlite | US | sqlite | 151 Kb | suspicious |
1096 | FonePaw Android Data Recovery.exe | GET | 200 | 50.22.1.104:80 | http://config.aokreg.com/adr/win/extraction/v1/flash.xml | US | xml | 12.4 Kb | suspicious |
1096 | FonePaw Android Data Recovery.exe | GET | 200 | 50.22.1.104:80 | http://config.aokreg.com/adr/recommend/recommend2.xml | US | xml | 165 Kb | suspicious |
3412 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
2884 | chrome.exe | GET | 200 | 173.194.129.231:80 | http://r2---sn-q0c7rn76.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=81.17.242.236&mm=28&mn=sn-q0c7rn76&ms=nvh&mt=1553575313&mv=u&pl=20&shardbypass=yes | US | crx | 842 Kb | whitelisted |
1096 | FonePaw Android Data Recovery.exe | GET | 200 | 50.22.1.104:80 | http://config.aokreg.com/adr/win/db/device.sqlite.md5 | US | text | 48 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1096 | FonePaw Android Data Recovery.exe | 50.22.1.105:443 | reg.aokreg.com | SoftLayer Technologies Inc. | US | suspicious |
1096 | FonePaw Android Data Recovery.exe | 50.22.1.107:443 | update.aokreg.com | SoftLayer Technologies Inc. | US | suspicious |
3412 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3376 | iexplore.exe | 151.139.241.5:443 | www.fonepaw.com | netDNA | US | unknown |
2884 | chrome.exe | 216.58.207.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2884 | chrome.exe | 45.56.67.215:443 | www.recovery-android.com | Linode, LLC | US | unknown |
2884 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2884 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2884 | chrome.exe | 172.217.16.142:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
3376 | iexplore.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.recovery-android.com |
| unknown |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
reg.aokreg.com |
| suspicious |
config.aokreg.com |
| suspicious |
update.aokreg.com |
| suspicious |
www.fonepaw.com |
| malicious |
Threats
Process | Message |
|---|---|
FonePaw Android Data Recovery.exe | libpng warning: iCCP: known incorrect sRGB profile
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#black'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|
FonePaw Android Data Recovery.exe | QCssParser::parseHexColor: Unknown color name '#ccccc'
|