| File name: | AdskNLM.exe |
| Full analysis: | https://app.any.run/tasks/9bd071cc-663c-49db-bea0-d60bfe80f5c9 |
| Verdict: | Malicious activity |
| Analysis date: | July 31, 2024, 21:35:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows |
| MD5: | 111B26F9FEAF4939A13E5559675C6917 |
| SHA1: | 924140D41D561026BDD9DAFDED8D2CDE7B23D7A4 |
| SHA256: | 2BE770432AB33A05000C0493D053F6DE792673E1680544C3EAE6C4B2E62BC13B |
| SSDEEP: | 98304:a4/ARKNzyUjS9zZB7T4R7IepI3shp5Cam5Im8yoqHNQTw380P7sFrMQQIqz9r0MO:VpYbBxoY9fOWJv0IsKe/tsq7 |
MALICIOUS
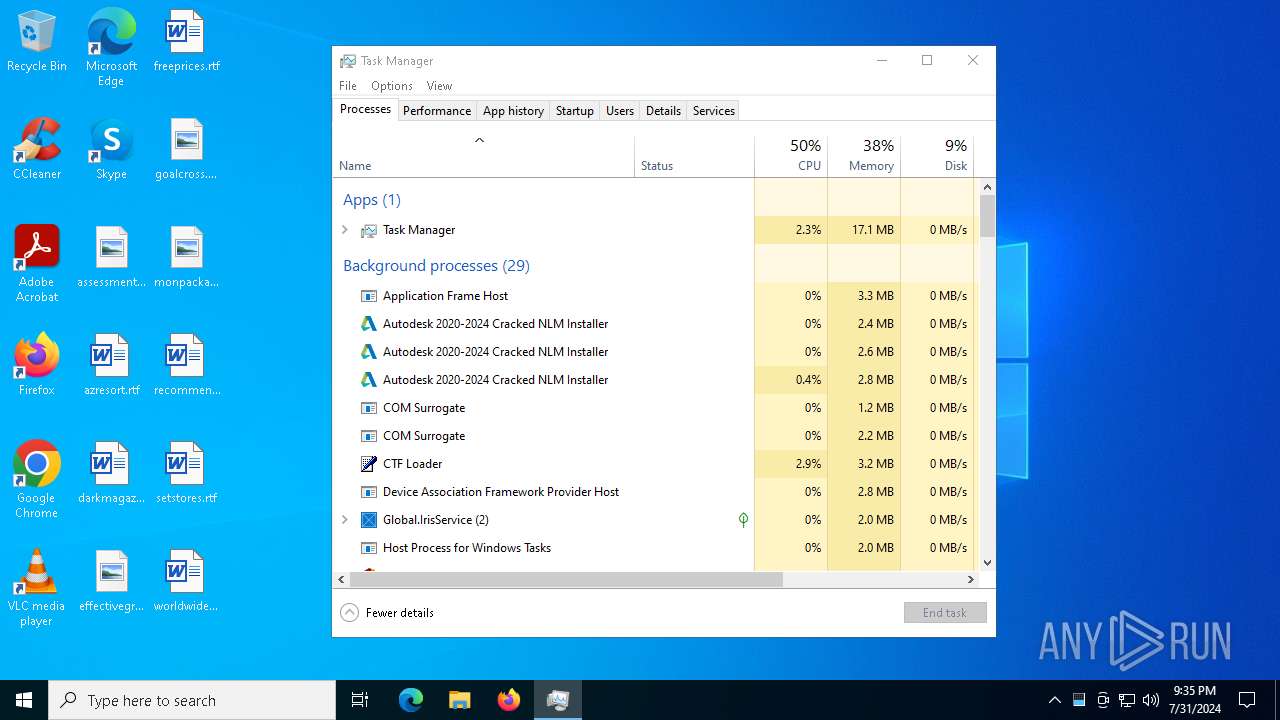
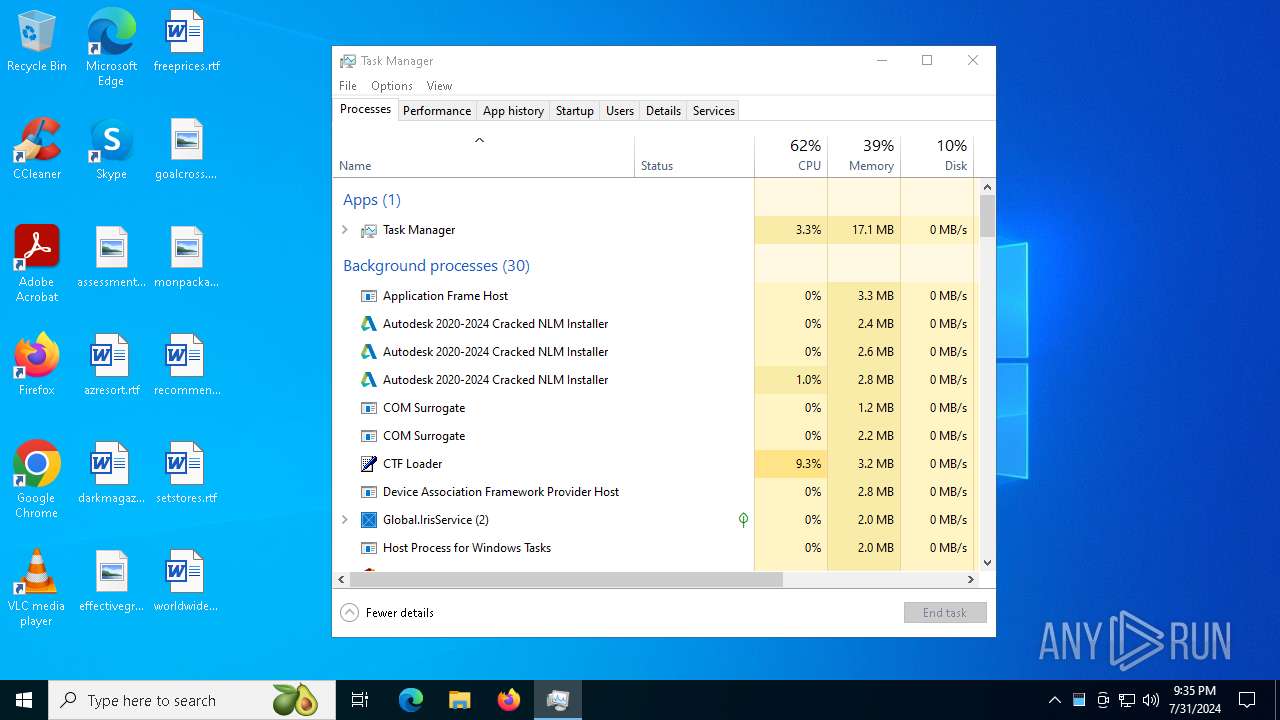
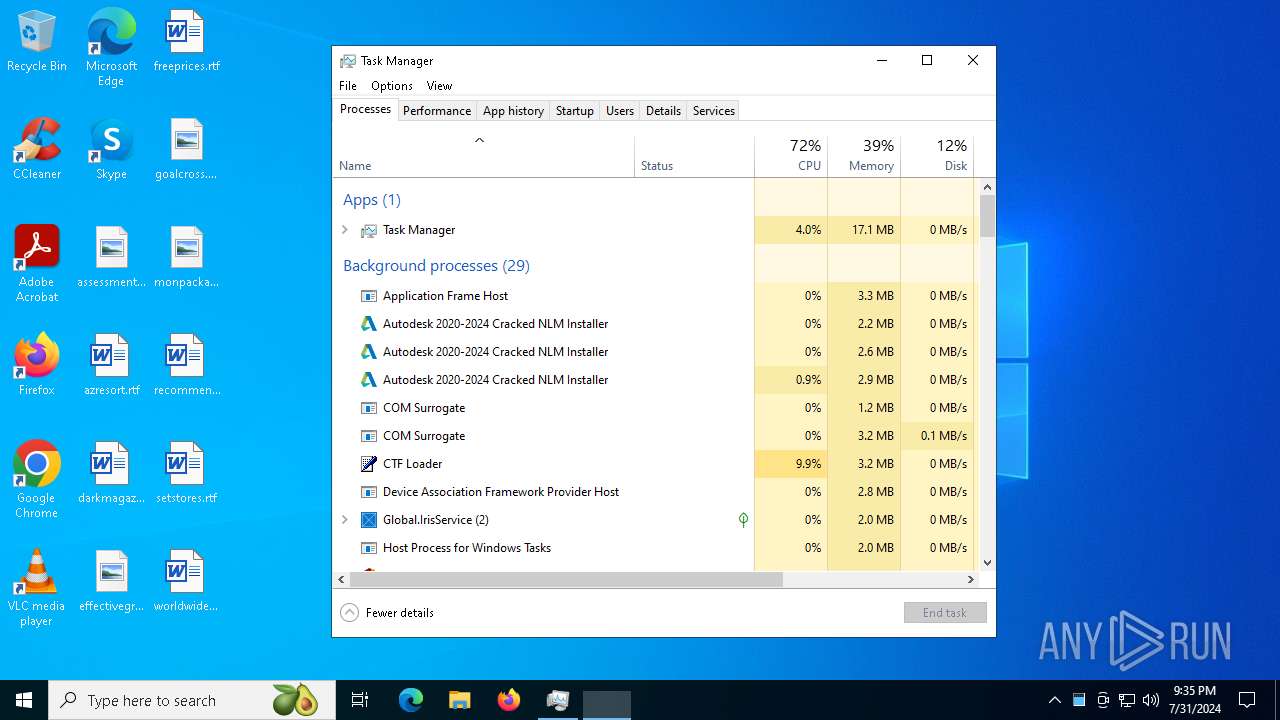
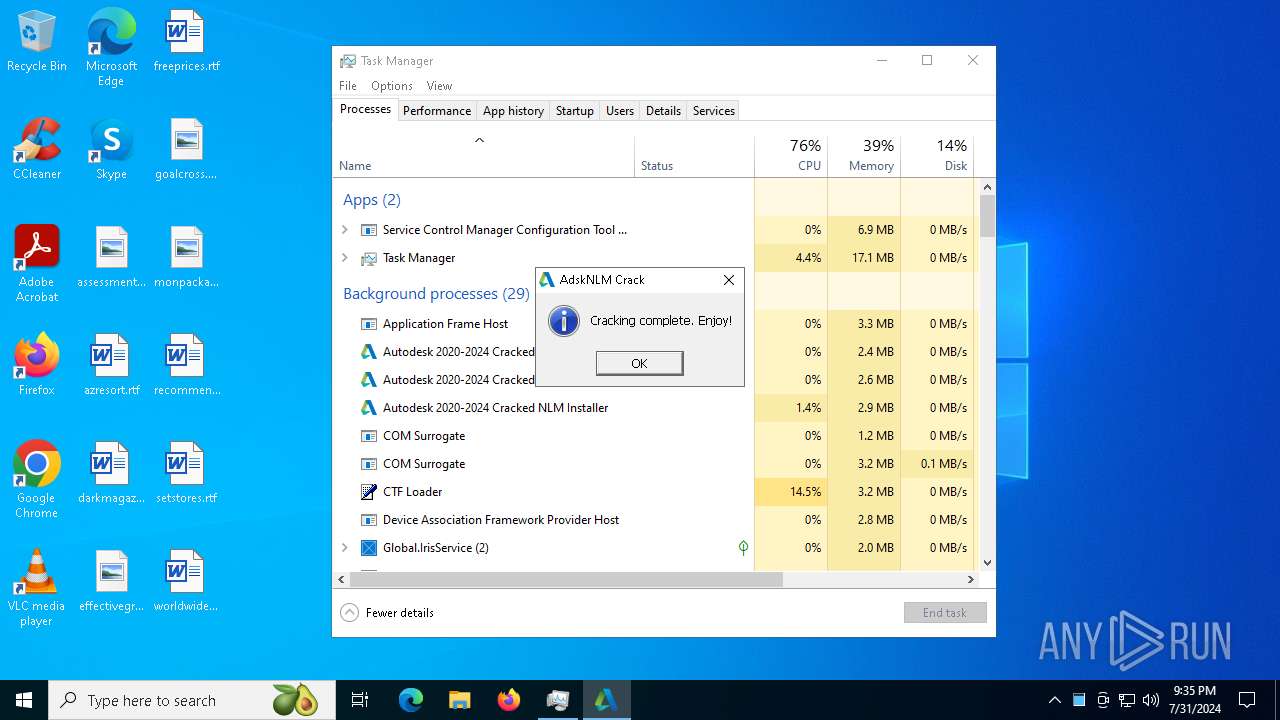
Drops the executable file immediately after the start
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6380)
- msiexec.exe (PID: 4844)
Modifies hosts file to block updates
- cmd.exe (PID: 2628)
SUSPICIOUS
Reads the date of Windows installation
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6416)
- AdskNLM.exe (PID: 6528)
- AdskNLM.exe (PID: 6716)
- AdskNLM.exe (PID: 6876)
- AdskNLM.exe (PID: 6988)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 6268)
- AdskNLM.exe (PID: 3180)
- AdskNLM.exe (PID: 4344)
- AdskNLM.exe (PID: 5920)
- AdskNLM.exe (PID: 6428)
- AdskNLM.exe (PID: 6352)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 6540)
- AdskNLM.exe (PID: 7052)
- AdskNLM.exe (PID: 6228)
- AdskNLM.exe (PID: 2608)
- AdskNLM.exe (PID: 6476)
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 2584)
- AdskNLM.exe (PID: 6176)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 6896)
- AdskNLM.exe (PID: 1116)
- AdskNLM.exe (PID: 7072)
- AdskNLM.exe (PID: 936)
- AdskNLM.exe (PID: 2960)
- AdskNLM.exe (PID: 2080)
- AdskNLM.exe (PID: 5908)
- AdskNLM.exe (PID: 6576)
- AdskNLM.exe (PID: 1964)
Reads security settings of Internet Explorer
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6416)
- AdskNLM.exe (PID: 6528)
- AdskNLM.exe (PID: 6716)
- AdskNLM.exe (PID: 6876)
- AdskNLM.exe (PID: 6988)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 6268)
- AdskNLM.exe (PID: 3180)
- AdskNLM.exe (PID: 4344)
- AdskNLM.exe (PID: 5920)
- AdskNLM.exe (PID: 6352)
- AdskNLM.exe (PID: 6428)
- AdskNLM.exe (PID: 6540)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 7052)
- AdskNLM.exe (PID: 2584)
- AdskNLM.exe (PID: 6228)
- AdskNLM.exe (PID: 2608)
- AdskNLM.exe (PID: 6476)
- AdskNLM.exe (PID: 6176)
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 7072)
- AdskNLM.exe (PID: 6896)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 936)
- AdskNLM.exe (PID: 1116)
- AdskNLM.exe (PID: 2960)
- AdskNLM.exe (PID: 2080)
- AdskNLM.exe (PID: 6576)
- AdskNLM.exe (PID: 5908)
- AdskNLM.exe (PID: 1964)
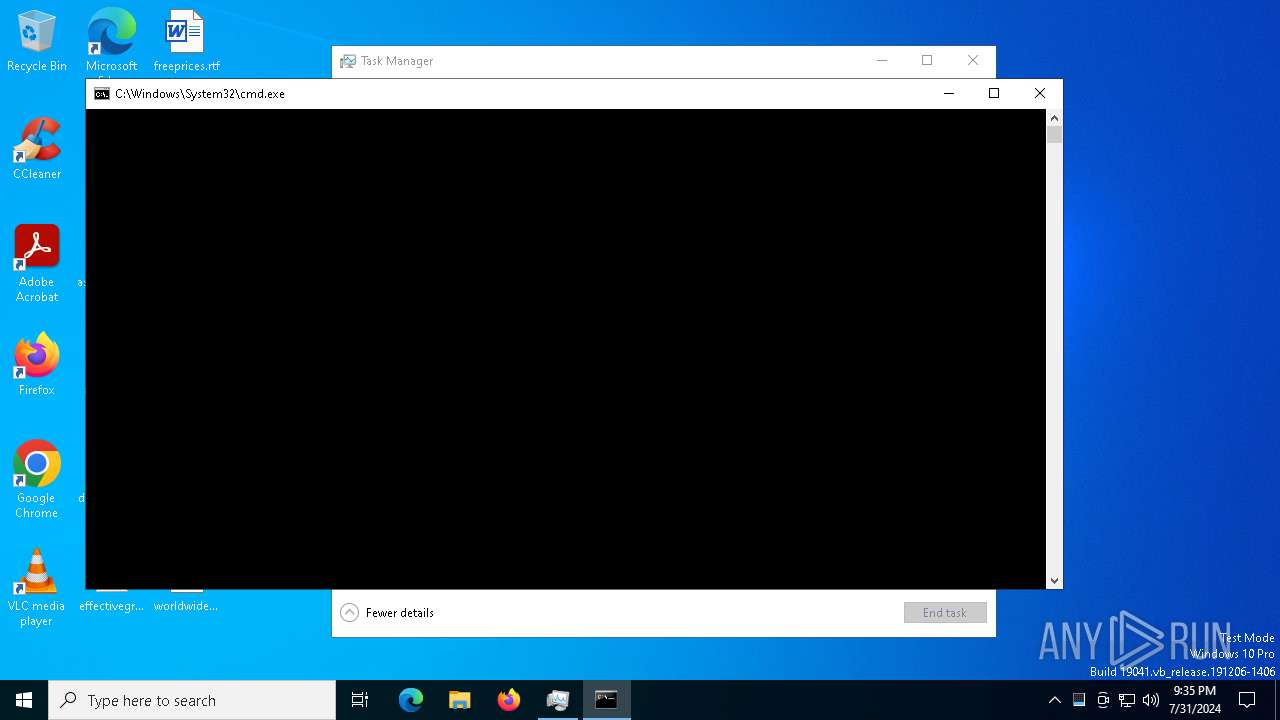
Application launched itself
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6380)
- cmd.exe (PID: 6756)
- cmd.exe (PID: 7020)
- cmd.exe (PID: 6908)
- cmd.exe (PID: 6212)
- lmgrd.exe (PID: 2044)
Executable content was dropped or overwritten
- AdskNLM.exe (PID: 6380)
- xcopy.exe (PID: 6832)
Starts SC.EXE for service management
- AdskNLM.exe (PID: 6416)
- AdskNLM.exe (PID: 7052)
- AdskNLM.exe (PID: 6896)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 6576)
- AdskNLM.exe (PID: 7056)
- AdskNLM.exe (PID: 4708)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 6756)
- AdskNLM.exe (PID: 6716)
- AdskNLM.exe (PID: 6876)
- AdskNLM.exe (PID: 6988)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 3180)
- AdskNLM.exe (PID: 4344)
- AdskNLM.exe (PID: 5920)
- AdskNLM.exe (PID: 6268)
- AdskNLM.exe (PID: 6352)
- AdskNLM.exe (PID: 6428)
- AdskNLM.exe (PID: 6540)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 936)
- AdskNLM.exe (PID: 1116)
- AdskNLM.exe (PID: 7072)
- AdskNLM.exe (PID: 2960)
- AdskNLM.exe (PID: 2080)
- AdskNLM.exe (PID: 5908)
- AdskNLM.exe (PID: 1964)
- AdskNLM.exe (PID: 2424)
- AdskNLM.exe (PID: 6276)
- cmd.exe (PID: 7020)
- AdskNLM.exe (PID: 1132)
- cmd.exe (PID: 6908)
- AdskNLM.exe (PID: 1964)
- AdskNLM.exe (PID: 1432)
- cmd.exe (PID: 6212)
- AdskNLM.exe (PID: 1124)
- AdskNLM.exe (PID: 6504)
Uses TASKKILL.EXE to kill process
- AdskNLM.exe (PID: 6528)
- AdskNLM.exe (PID: 2584)
- AdskNLM.exe (PID: 6228)
- AdskNLM.exe (PID: 2608)
- AdskNLM.exe (PID: 6176)
- AdskNLM.exe (PID: 6476)
Process copies executable file
- cmd.exe (PID: 6756)
- cmd.exe (PID: 7020)
Uses REG/REGEDIT.EXE to modify registry
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 3508)
- AdskNLM.exe (PID: 5088)
- AdskNLM.exe (PID: 5140)
- AdskNLM.exe (PID: 3032)
- AdskNLM.exe (PID: 2928)
- AdskNLM.exe (PID: 2080)
- AdskNLM.exe (PID: 6972)
- AdskNLM.exe (PID: 6644)
- AdskNLM.exe (PID: 5180)
- AdskNLM.exe (PID: 5088)
- AdskNLM.exe (PID: 4100)
- AdskNLM.exe (PID: 2648)
Uses WMIC.EXE to obtain Windows Installer data
- cmd.exe (PID: 5180)
- cmd.exe (PID: 5056)
Uses WMIC.EXE to obtain service application data
- cmd.exe (PID: 3032)
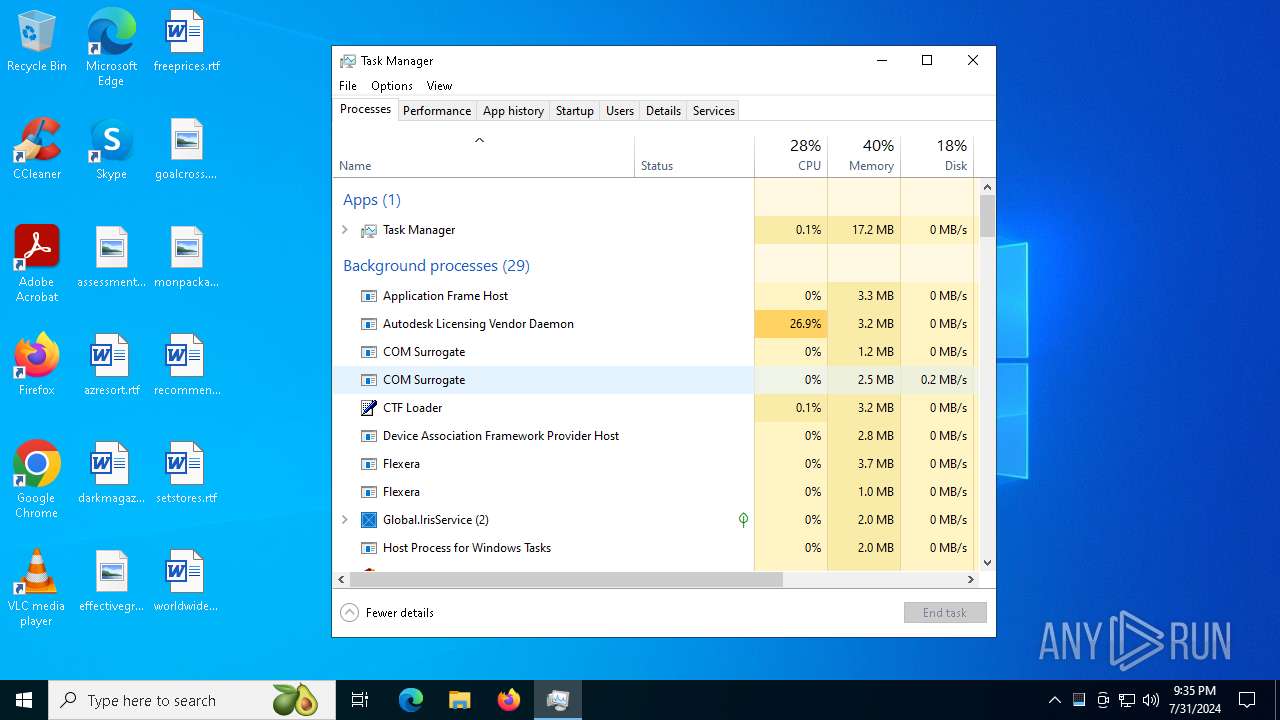
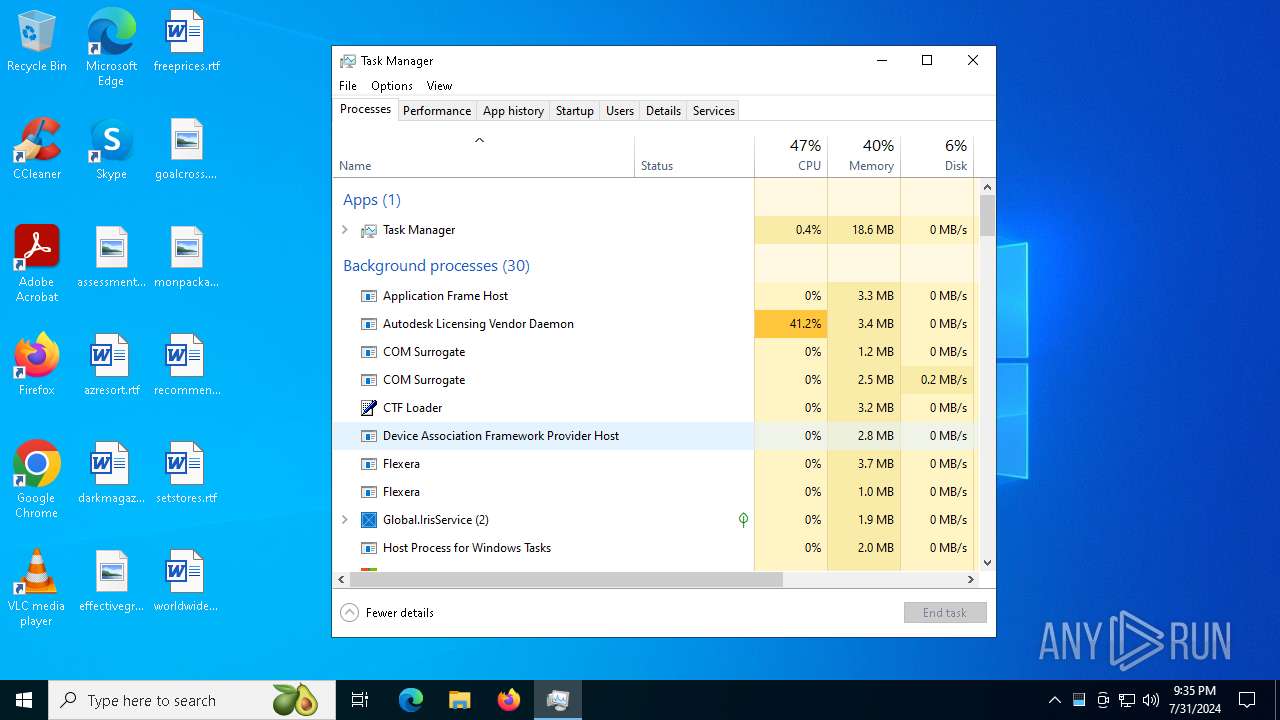
Executes as Windows Service
- lmgrd.exe (PID: 2044)
INFO
Checks supported languages
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 6416)
- AdskNLM.exe (PID: 6528)
- AdskNLM.exe (PID: 6716)
- AdskNLM.exe (PID: 6876)
- AdskNLM.exe (PID: 6268)
- AdskNLM.exe (PID: 6988)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 3180)
- AdskNLM.exe (PID: 4344)
- AdskNLM.exe (PID: 5920)
- AdskNLM.exe (PID: 6428)
- AdskNLM.exe (PID: 6352)
- AdskNLM.exe (PID: 6540)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 7052)
- AdskNLM.exe (PID: 6228)
- AdskNLM.exe (PID: 2608)
- AdskNLM.exe (PID: 2584)
- AdskNLM.exe (PID: 6476)
- AdskNLM.exe (PID: 6176)
- AdskNLM.exe (PID: 7072)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 6896)
- AdskNLM.exe (PID: 1116)
- AdskNLM.exe (PID: 936)
- AdskNLM.exe (PID: 2080)
- msiexec.exe (PID: 4844)
- AdskNLM.exe (PID: 2960)
- AdskNLM.exe (PID: 6576)
- AdskNLM.exe (PID: 5908)
- AdskNLM.exe (PID: 1964)
Reads the computer name
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 6416)
- AdskNLM.exe (PID: 6528)
- AdskNLM.exe (PID: 6716)
- AdskNLM.exe (PID: 6876)
- AdskNLM.exe (PID: 6988)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 6268)
- AdskNLM.exe (PID: 3180)
- AdskNLM.exe (PID: 4344)
- AdskNLM.exe (PID: 5920)
- AdskNLM.exe (PID: 6352)
- AdskNLM.exe (PID: 6428)
- AdskNLM.exe (PID: 6540)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 7052)
- AdskNLM.exe (PID: 6228)
- AdskNLM.exe (PID: 2584)
- AdskNLM.exe (PID: 2608)
- AdskNLM.exe (PID: 6476)
- AdskNLM.exe (PID: 6176)
- AdskNLM.exe (PID: 6896)
- AdskNLM.exe (PID: 7072)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 936)
- AdskNLM.exe (PID: 1116)
- AdskNLM.exe (PID: 2080)
- msiexec.exe (PID: 4844)
- AdskNLM.exe (PID: 2960)
- AdskNLM.exe (PID: 5908)
- AdskNLM.exe (PID: 6576)
- AdskNLM.exe (PID: 1964)
Process checks computer location settings
- AdskNLM.exe (PID: 6304)
- AdskNLM.exe (PID: 6416)
- AdskNLM.exe (PID: 6528)
- AdskNLM.exe (PID: 6716)
- AdskNLM.exe (PID: 6876)
- AdskNLM.exe (PID: 6988)
- AdskNLM.exe (PID: 7100)
- AdskNLM.exe (PID: 3180)
- AdskNLM.exe (PID: 4344)
- AdskNLM.exe (PID: 5920)
- AdskNLM.exe (PID: 6268)
- AdskNLM.exe (PID: 6352)
- AdskNLM.exe (PID: 6428)
- AdskNLM.exe (PID: 6540)
- AdskNLM.exe (PID: 6752)
- AdskNLM.exe (PID: 7052)
- AdskNLM.exe (PID: 2584)
- AdskNLM.exe (PID: 6228)
- AdskNLM.exe (PID: 2608)
- AdskNLM.exe (PID: 6176)
- AdskNLM.exe (PID: 6476)
- AdskNLM.exe (PID: 6380)
- AdskNLM.exe (PID: 6792)
- AdskNLM.exe (PID: 6896)
- AdskNLM.exe (PID: 936)
- AdskNLM.exe (PID: 1116)
- AdskNLM.exe (PID: 7072)
- AdskNLM.exe (PID: 2960)
- AdskNLM.exe (PID: 5908)
- AdskNLM.exe (PID: 6576)
- AdskNLM.exe (PID: 2080)
- AdskNLM.exe (PID: 1964)
Create files in a temporary directory
- AdskNLM.exe (PID: 6380)
Creates files in the program directory
- xcopy.exe (PID: 6832)
Drops the executable file immediately after the start
- xcopy.exe (PID: 6832)
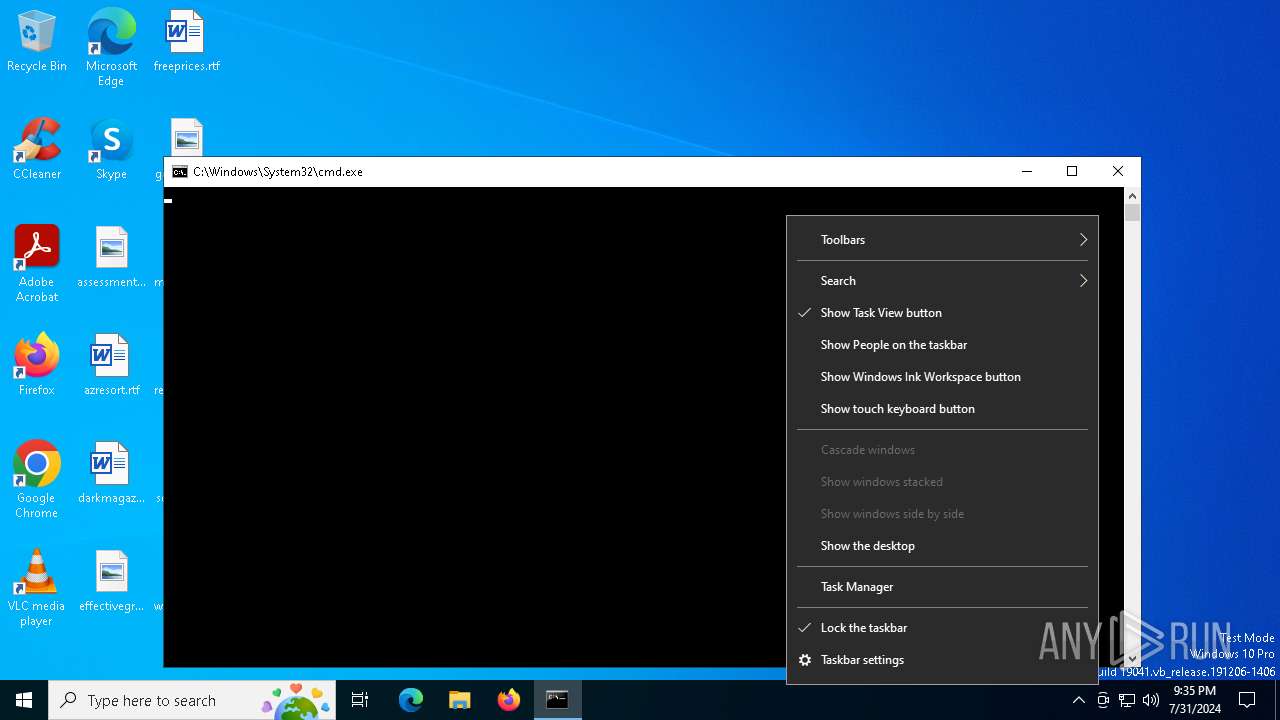
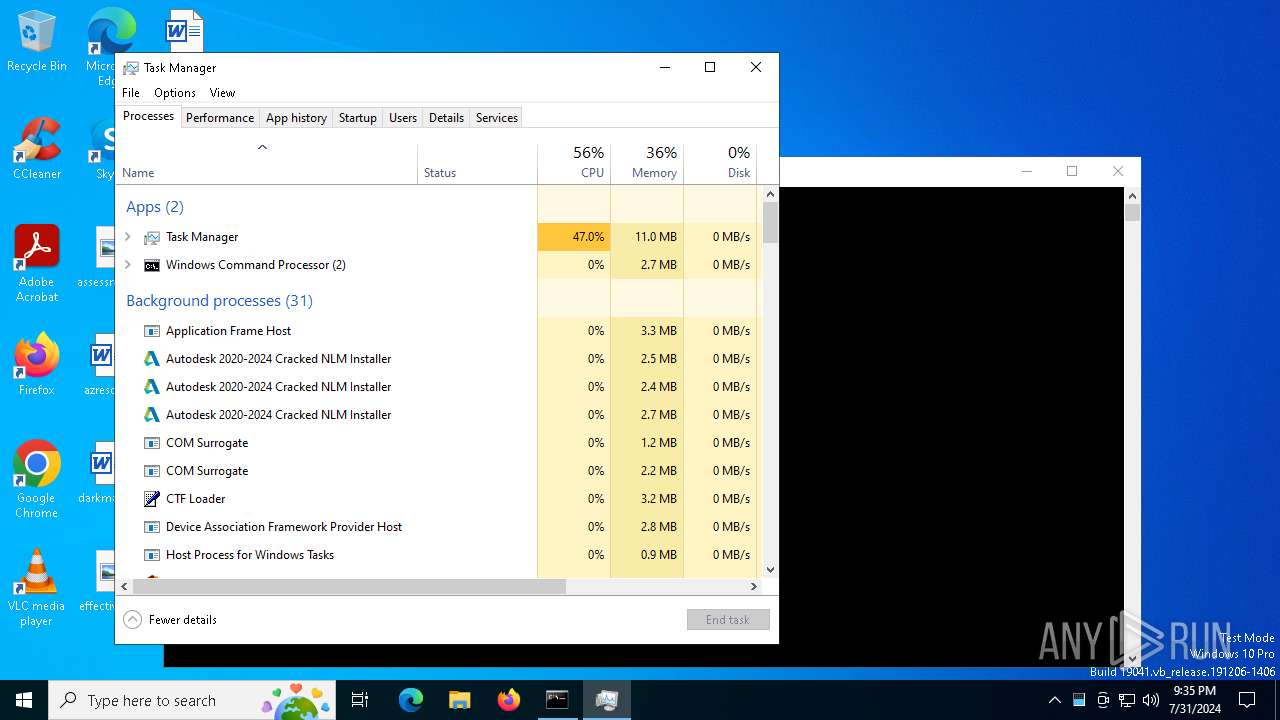
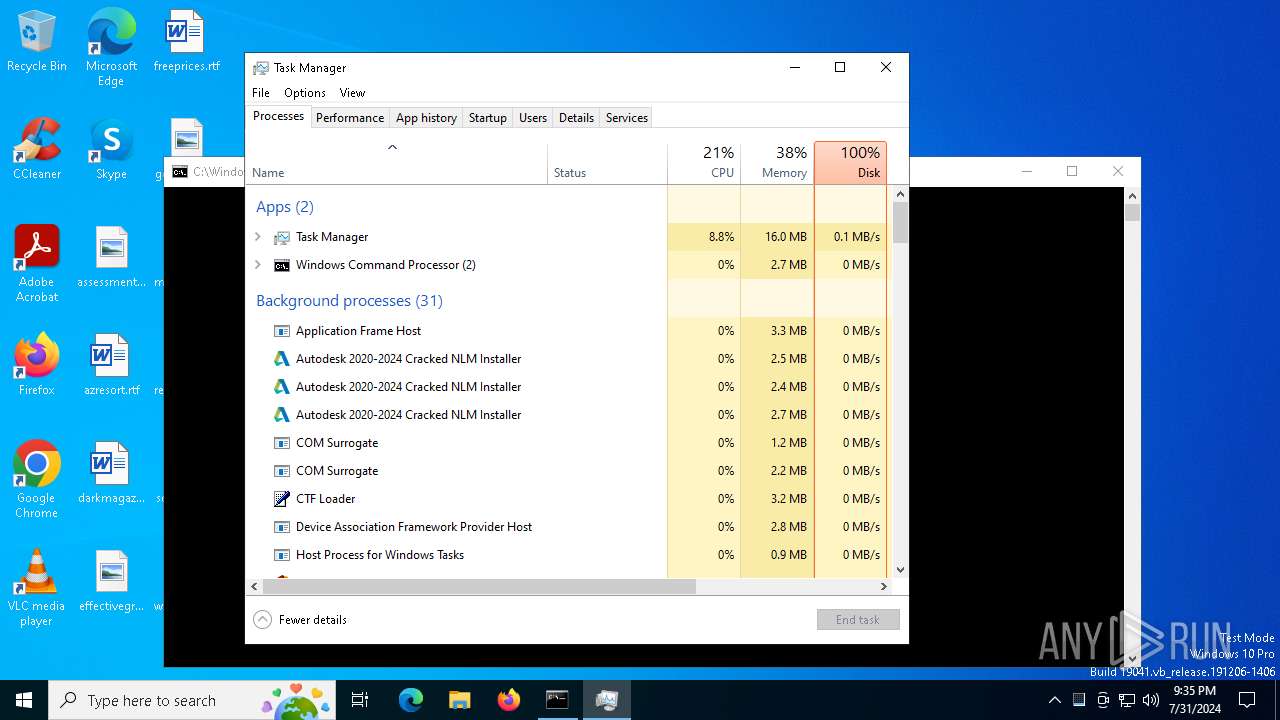
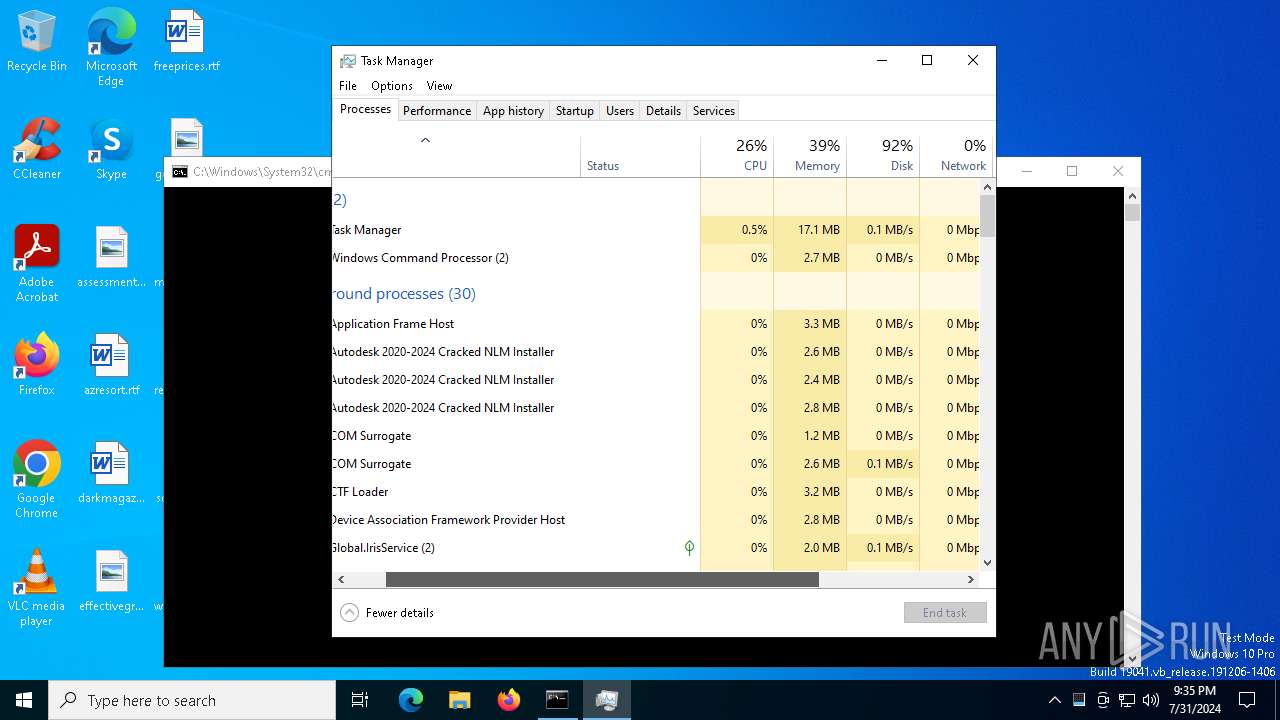
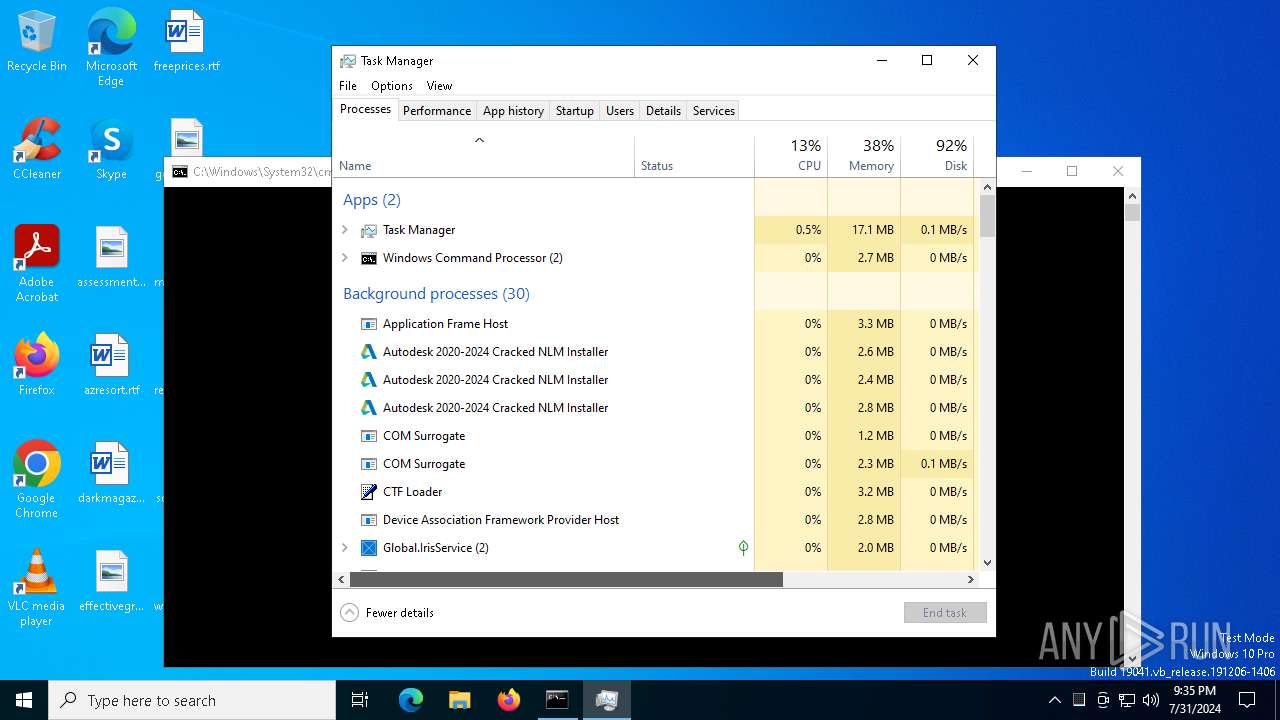
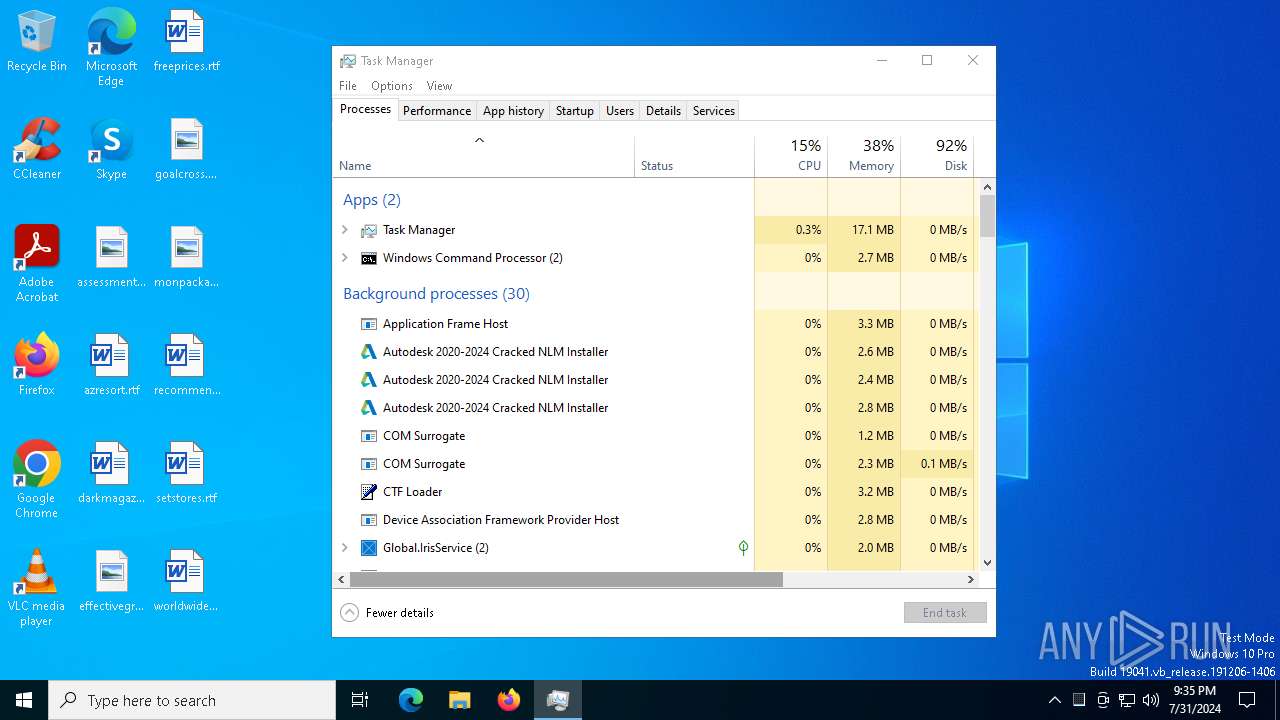
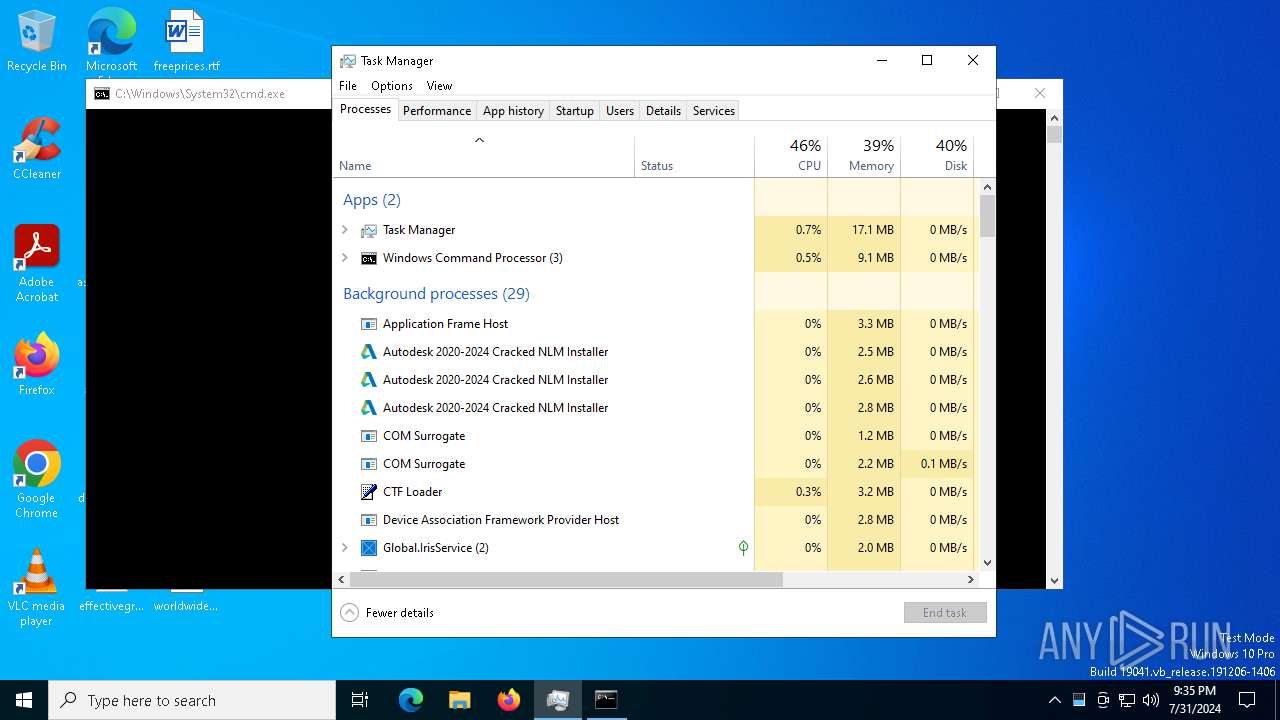
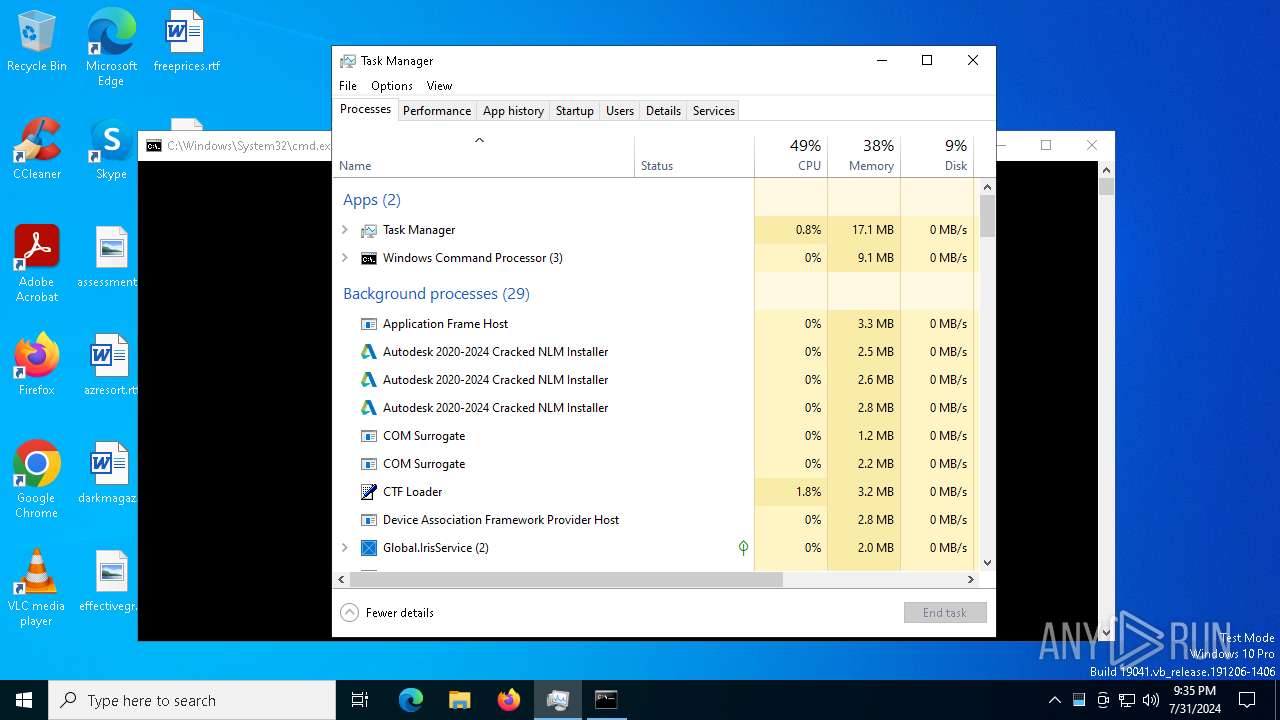
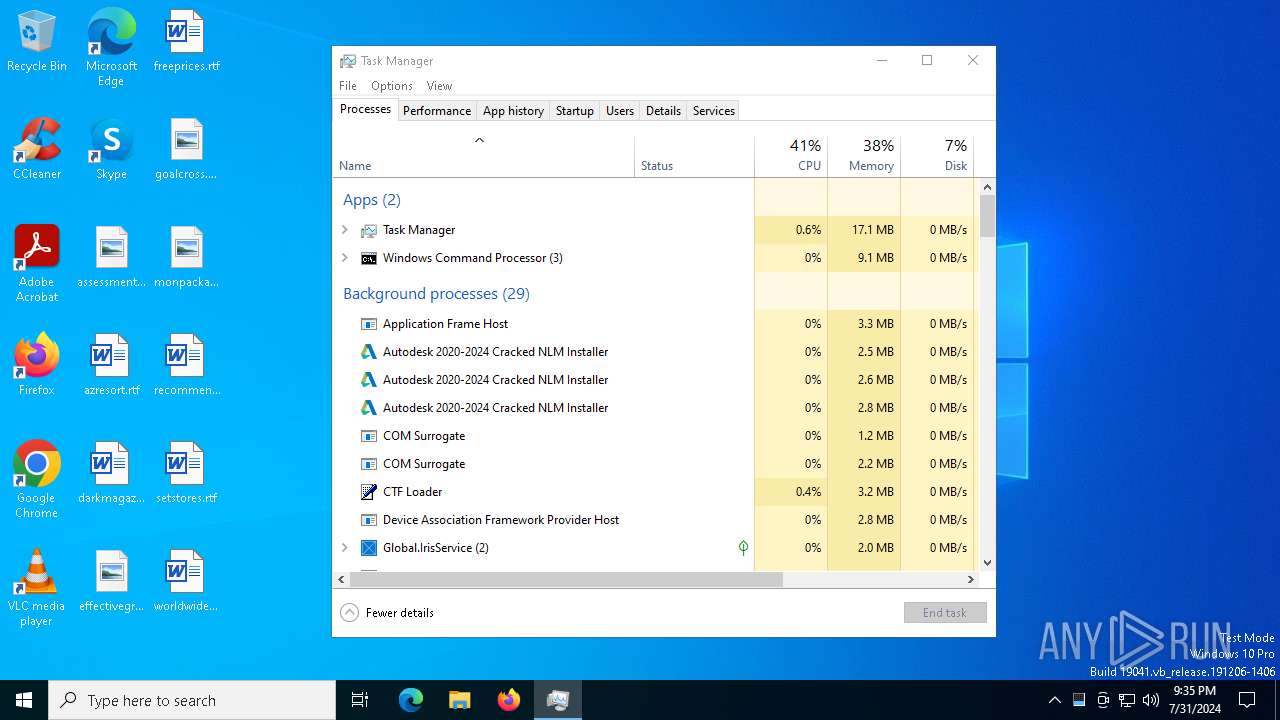
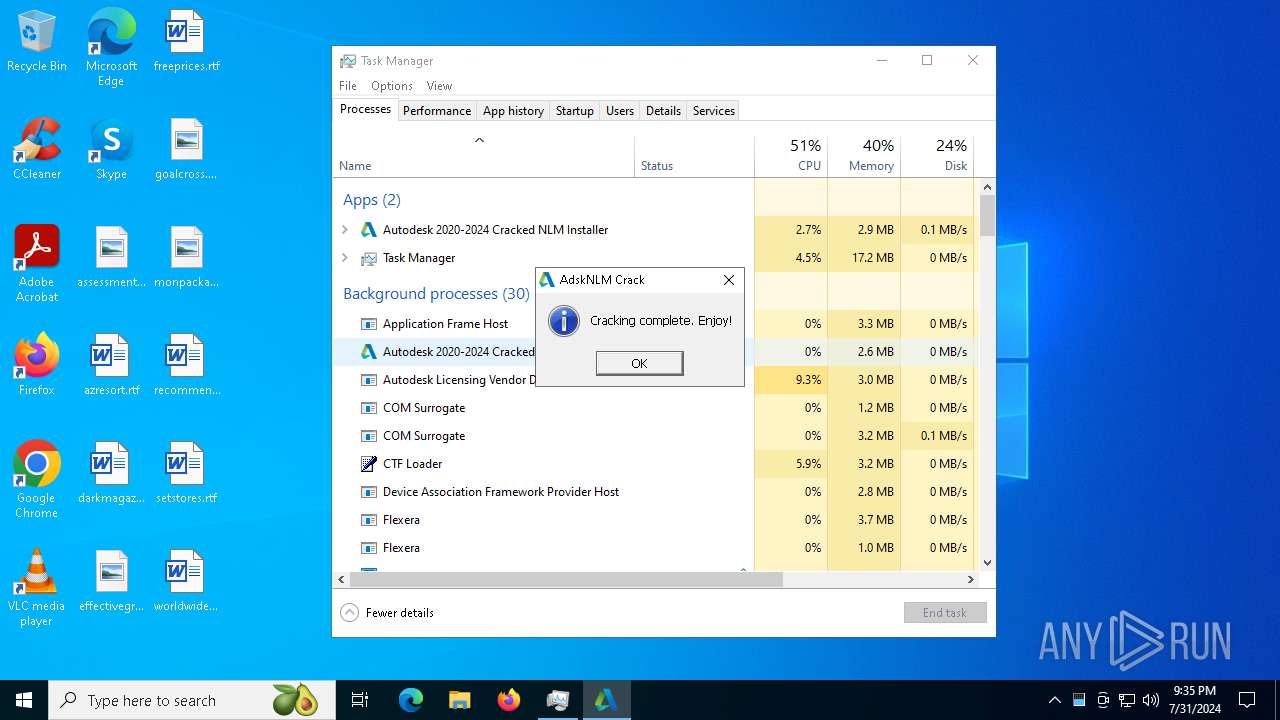
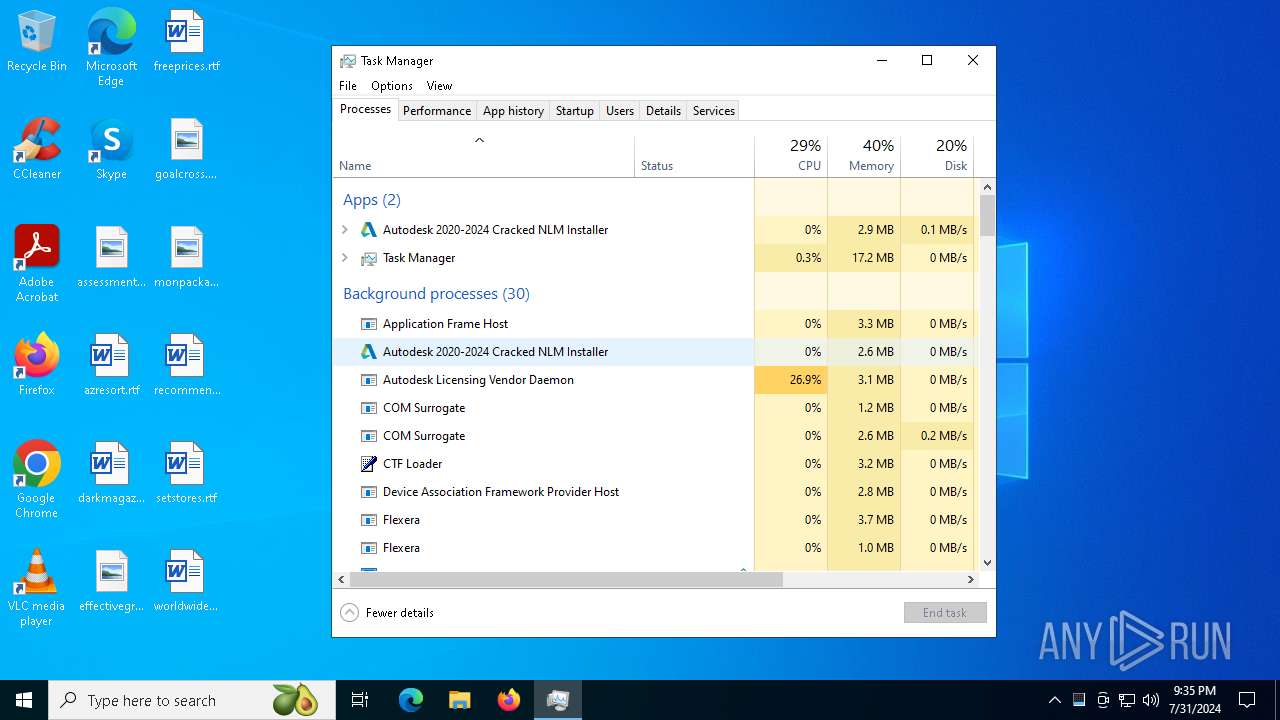
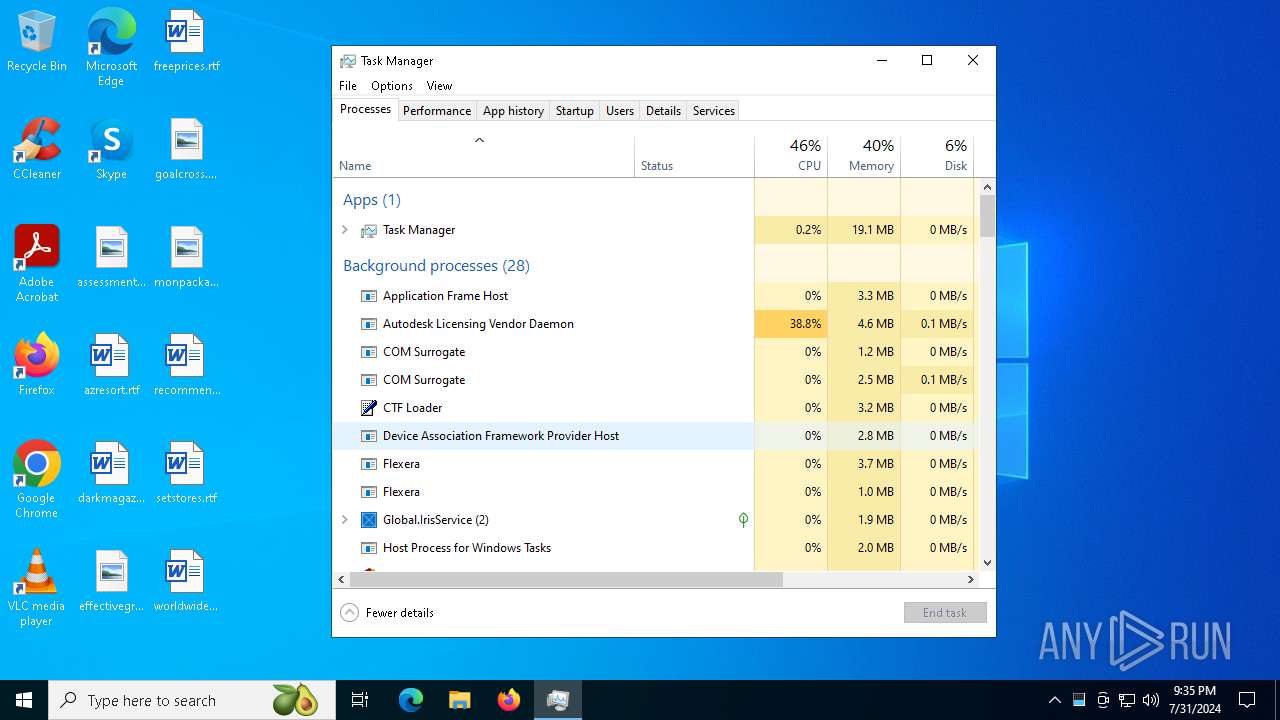
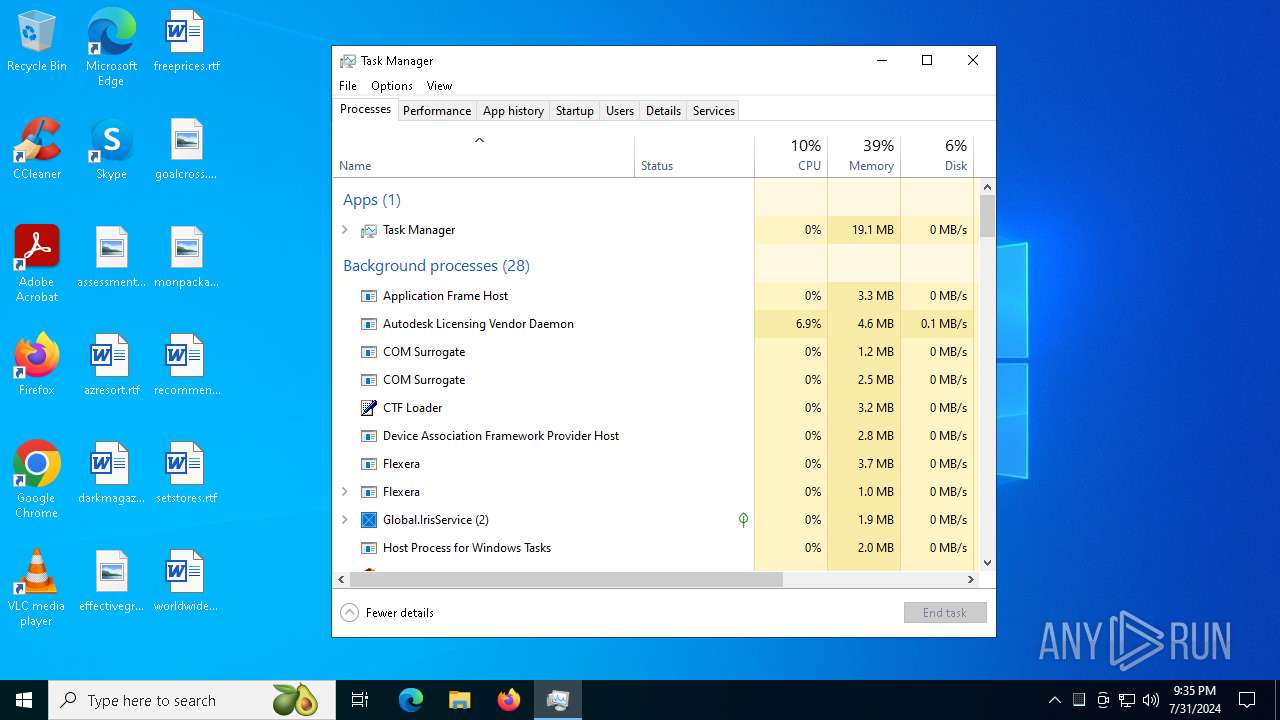
Manual execution by a user
- Taskmgr.exe (PID: 6468)
- Taskmgr.exe (PID: 6444)
Reads security settings of Internet Explorer
- Taskmgr.exe (PID: 6468)
- WMIC.exe (PID: 1656)
- WMIC.exe (PID: 2804)
Changes file name
- cmd.exe (PID: 1860)
- cmd.exe (PID: 5760)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4844)
Application launched itself
- msiexec.exe (PID: 4844)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2018:05:21 01:49:42+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 10 |
| CodeSize: | 130560 |
| InitializedDataSize: | 308736 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20360 |
| OSVersion: | 5.2 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 9.0.0.0 |
| ProductVersionNumber: | 9.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | MAGNiTUDE & m0nkrus |
| FileDescription: | Autodesk 2020-2024 Cracked NLM Installer |
| FileVersion: | 9.0.0.0 |
| InternalName: | AdskNLM |
| LegalCopyright: | Copyright © 2022-2024 MAGNiTUDE & m0nkrus |
| OriginalFileName: | AdskNLM.exe |
| PrivateBuild: | November 15, 2024 |
| ProductName: | Autodesk Cracked NLM |
| ProductVersion: | 9.0.0.0 |
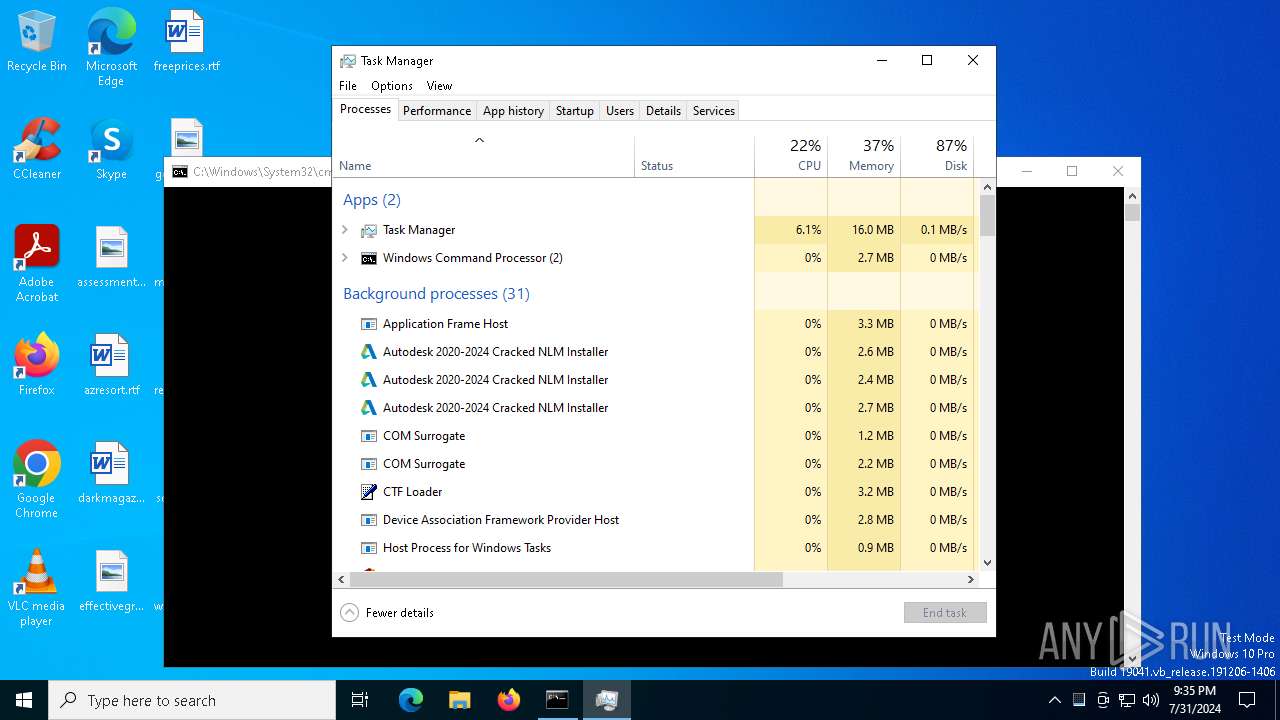
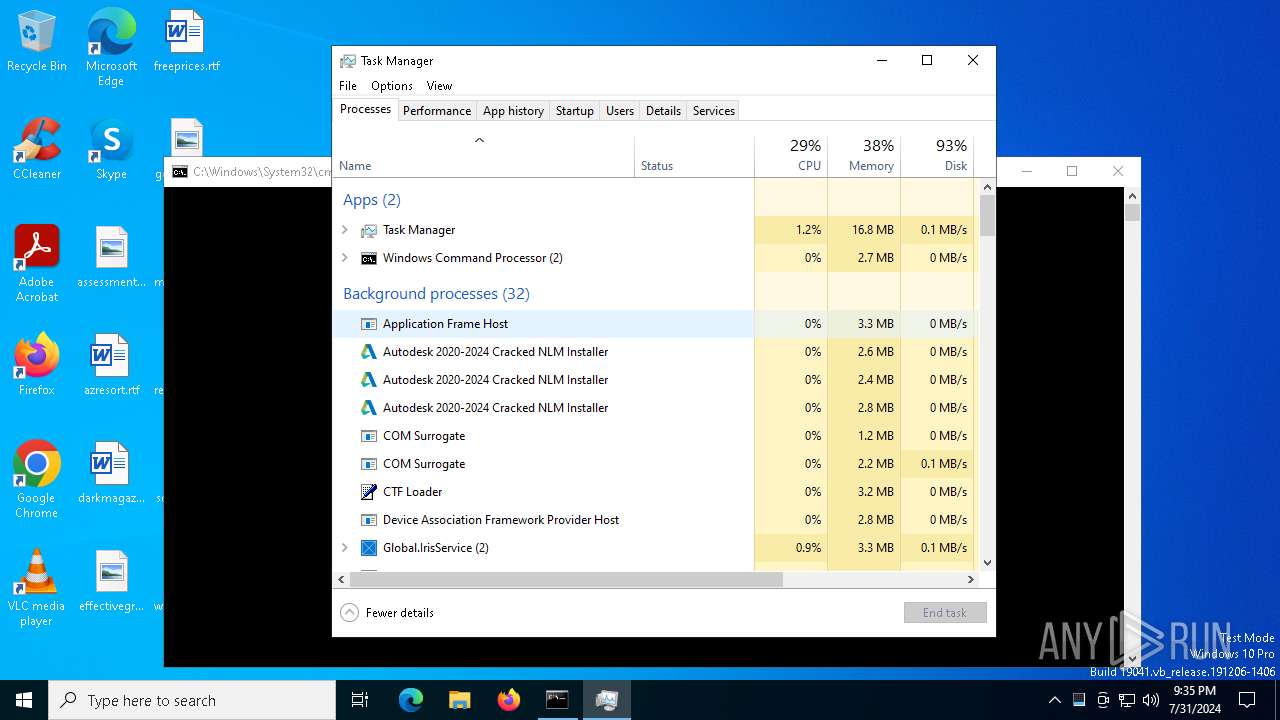
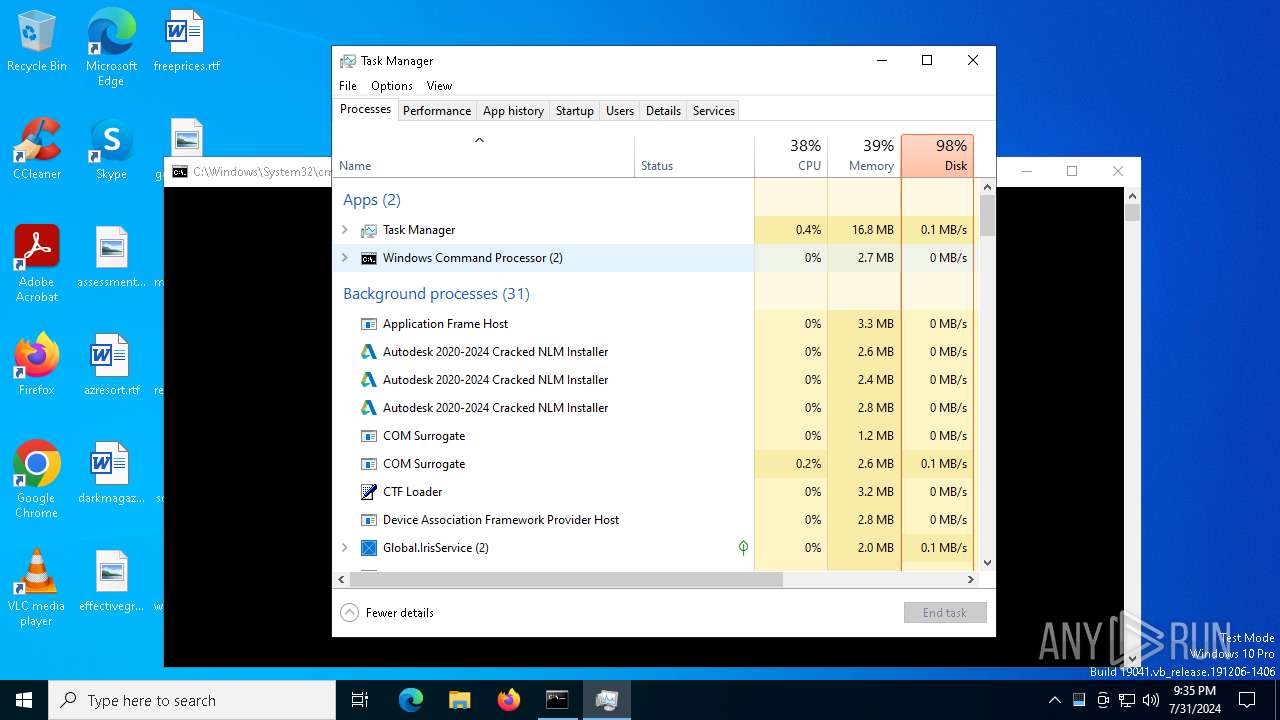
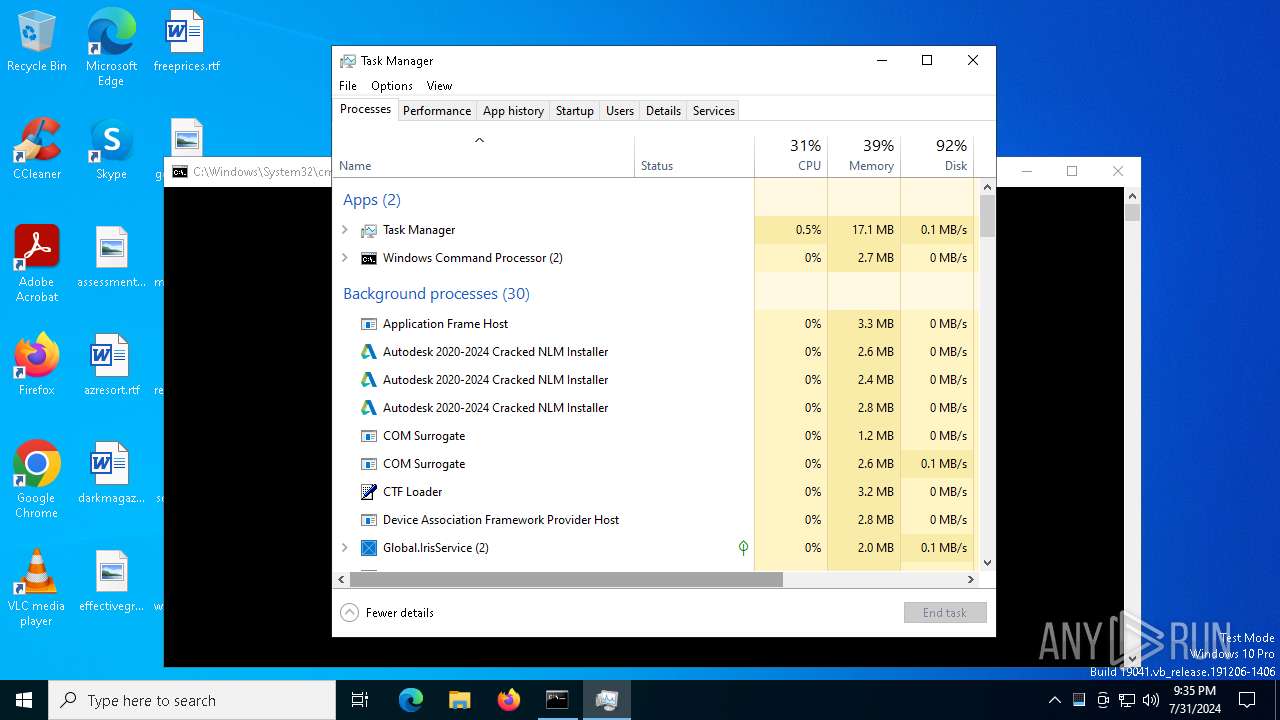
Total processes
319
Monitored processes
183
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 32 | "C:\Windows\System32\reg.exe" add "HKCU\SOFTWARE\Autodesk\MC3" /v "OverridedByHKLM" /t "REG_DWORD" /d "0" /f | C:\Windows\System32\reg.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 252 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | reg.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 300 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 320 | "C:\Windows\System32\sc.exe" stop AdskNLM | C:\Windows\System32\sc.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Service Control Manager Configuration Tool Exit code: 1060 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 532 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo D " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 532 | "C:\Windows\System32\reg.exe" add "HKLM\SOFTWARE\FLEXlm License Manager\AdskNLM" /v "License" /d "C:\Program Files (x86)\Common Files\Autodesk Shared\Network License Manager\licenses.lic" /f | C:\Windows\System32\reg.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 532 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo D " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 936 | "C:\Users\admin\AppData\Local\Temp\AdskNLM.exe" -sfxwaitall:0 "cmd" /c "C:\Program Files (x86)\Autodesk\Autodesk Desktop App\removeAdAppMgr.exe" --mode unattended | C:\Users\admin\AppData\Local\Temp\AdskNLM.exe | — | AdskNLM.exe | |||||||||||
User: admin Company: MAGNiTUDE & m0nkrus Integrity Level: HIGH Description: Autodesk 2020-2024 Cracked NLM Installer Exit code: 0 Version: 9.0.0.0 Modules
| |||||||||||||||
| 964 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
72 904
Read events
72 645
Write events
257
Delete events
2
Modification events
| (PID) Process: | (6304) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6304) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6304) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6304) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6416) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6416) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (6416) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (6416) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (6528) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (6528) AdskNLM.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
Executable files
15
Suspicious files
20
Text files
8
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6380 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm11-19-4-1-ipv4-ipv6-win64.msi | — | |
MD5:— | SHA256:— | |||
| 4844 | msiexec.exe | C:\Windows\Installer\edb29.msi | — | |
MD5:— | SHA256:— | |||
| 6380 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\nlm.mst | binary | |
MD5:29810BAB1EF69A3D26872093EF09372B | SHA256:90E413CD675EE085C441DF6327F6661A3459F4E109E0684B1A361C050D672BDB | |||
| 4844 | msiexec.exe | C:\Windows\Installer\MSIDC82.tmp | executable | |
MD5:A3AE5D86ECF38DB9427359EA37A5F646 | SHA256:C8D190D5BE1EFD2D52F72A72AE9DFA3940AB3FACEB626405959349654FE18B74 | |||
| 6468 | Taskmgr.exe | C:\Users\admin\AppData\Local\D3DSCache\3534848bb9f4cb71\F4EB2D6C-ED2B-4BDD-AD9D-F913287E6768.lock | text | |
MD5:F49655F856ACB8884CC0ACE29216F511 | SHA256:7852FCE59C67DDF1D6B8B997EAA1ADFAC004A9F3A91C37295DE9223674011FBA | |||
| 6380 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\netapi32.dll | executable | |
MD5:5C51CC926C76B23830D27A97445BF734 | SHA256:655181D13D9707500BF77FF88B0B6C2595459B475ADE7B919A2B1E00402C1CEB | |||
| 4844 | msiexec.exe | C:\Windows\Installer\edb2a.mst | binary | |
MD5:29810BAB1EF69A3D26872093EF09372B | SHA256:90E413CD675EE085C441DF6327F6661A3459F4E109E0684B1A361C050D672BDB | |||
| 6380 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version.dll | executable | |
MD5:44774FAFD716FA45C7A0CCB3B14D59A6 | SHA256:4739ABFF4DA13A27F2421452007C9D2340BF4F9E9A601EF0EC9F1B9D64D1D365 | |||
| 6380 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\version_old.dll | executable | |
MD5:51F0E19B4CF164ECBA9A006C4CF3B2A5 | SHA256:6F13E52D797A732435C8BB456BE08C64D0B6FADEA29F85486F4B44559D6CC95F | |||
| 6380 | AdskNLM.exe | C:\Users\admin\AppData\Local\Temp\Adsk-NLM\delnowmic.ps1 | text | |
MD5:67924FF023F149E8B467A8905FF1B4FC | SHA256:4B5EF379990A4663A3341913B0BD4FEDF906B9F6AF8D8FA0CB8BEE4A09FF92F9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
45
DNS requests
18
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4296 | WmiPrvSE.exe | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | unknown | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 23.211.9.92:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | unknown | — | — | whitelisted |
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAkQWITrlZ07yLmU%2BRintu4%3D | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 95.101.54.128:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | unknown | — | — | whitelisted |
4296 | WmiPrvSE.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAPxtOFfOoLxFJZ4s9fYR1w%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
876 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4296 | WmiPrvSE.exe | 23.211.9.92:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4296 | WmiPrvSE.exe | 95.101.54.128:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
4296 | WmiPrvSE.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | unknown |
5336 | SearchApp.exe | 150.171.27.10:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |
th.bing.com |
| whitelisted |