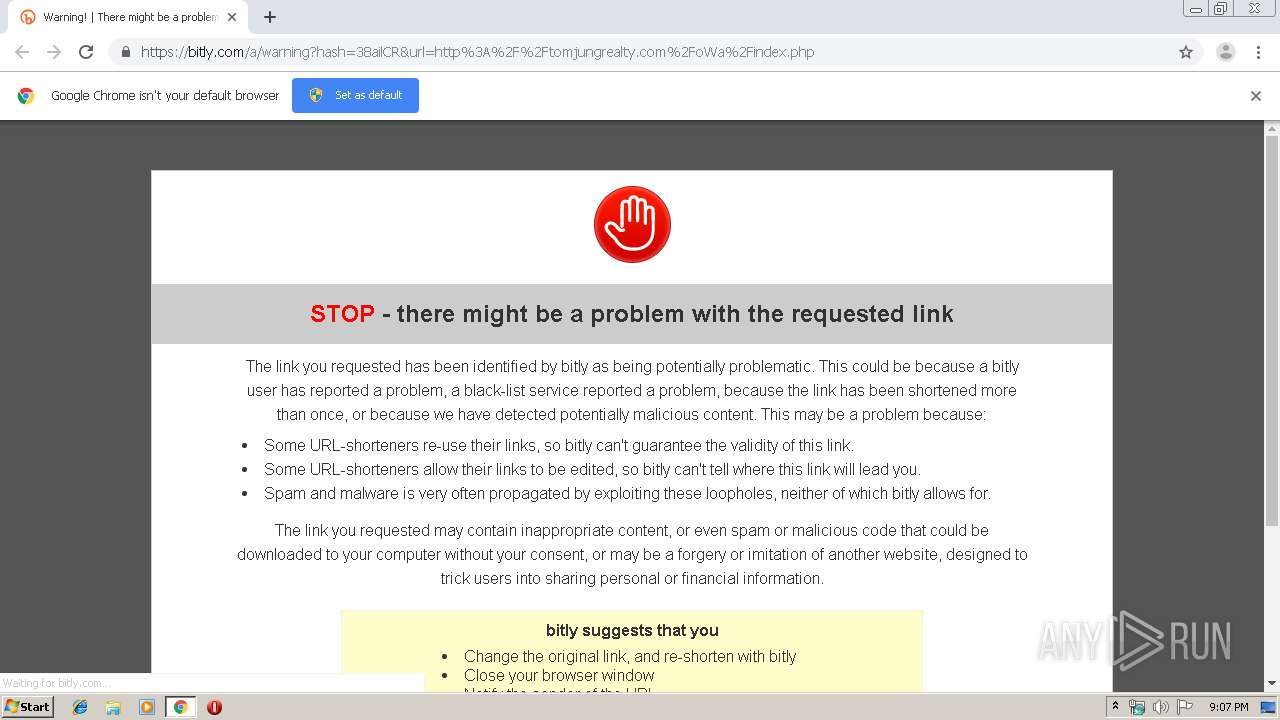
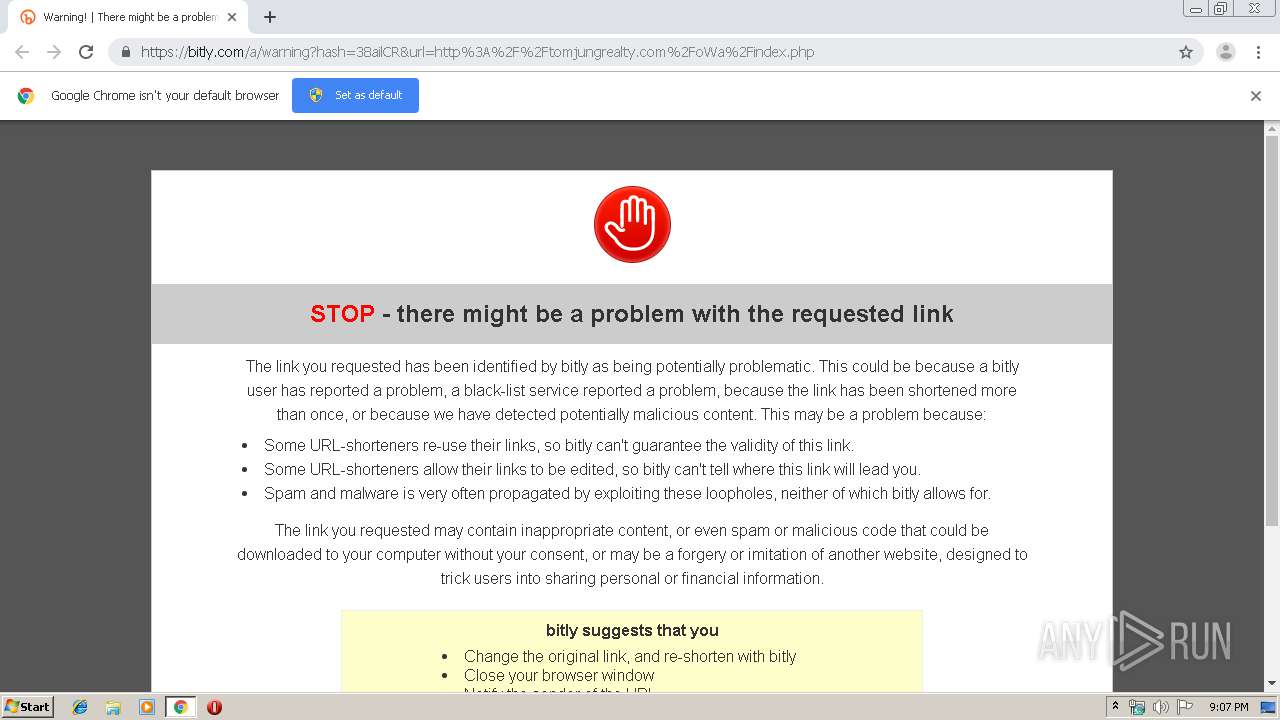
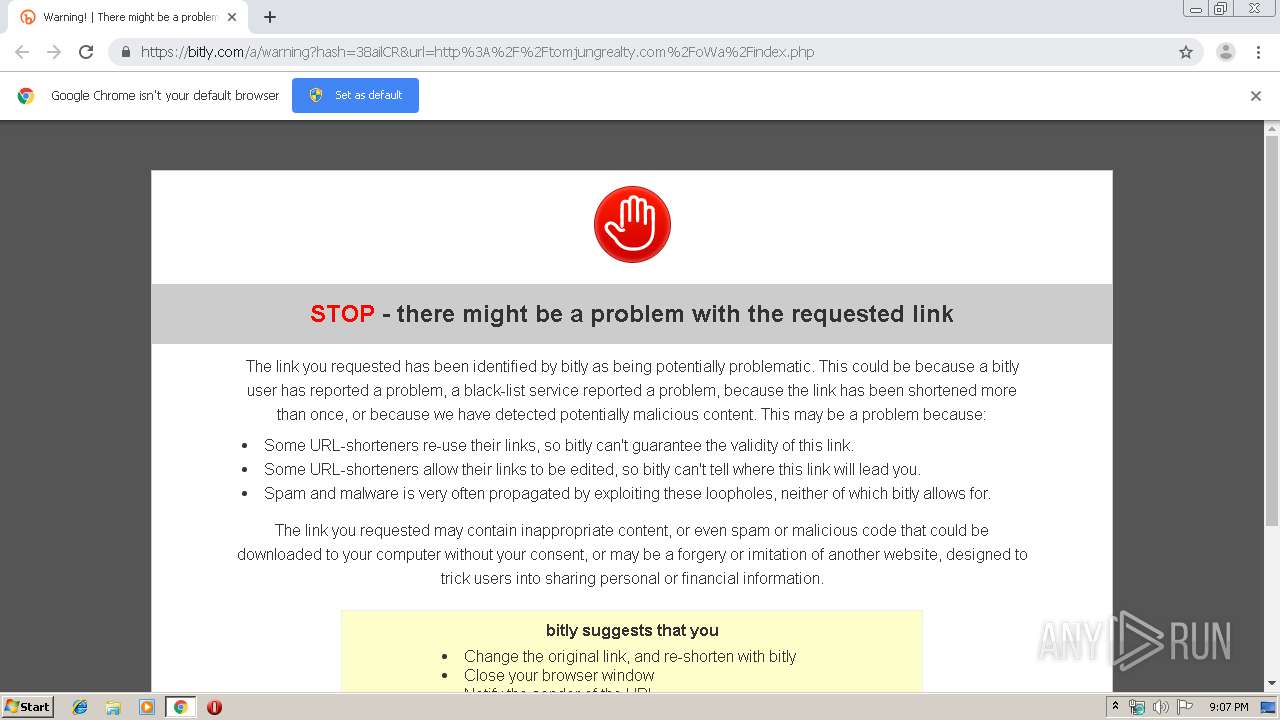
| URL: | http://bit.ly/Wabash-Financial-Strategies-J-Schwartz |
| Full analysis: | https://app.any.run/tasks/fe097af4-c12c-4b81-a786-5ead62dd808f |
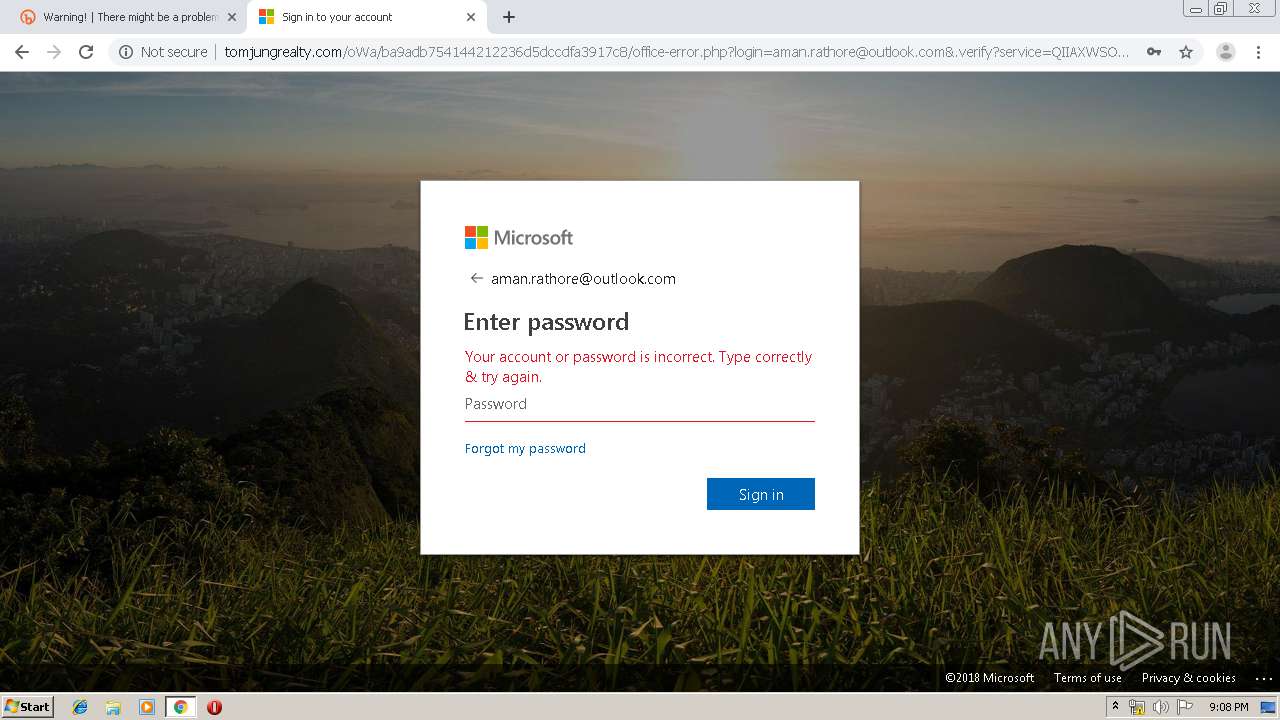
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2019, 21:06:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | C4C6485EE7283583B9CBC6CB541BEBBF |
| SHA1: | 132FC63BCFB2B8276CA45DB64FE3A14518610C77 |
| SHA256: | 2BCA56F9E00BB3DAD987E4358703CA303EEC88C0D10615D5D88ABE691187359E |
| SSDEEP: | 3:N1KcQ9jHFIw5ZXQgn5:CcmS+Gg5 |
MALICIOUS
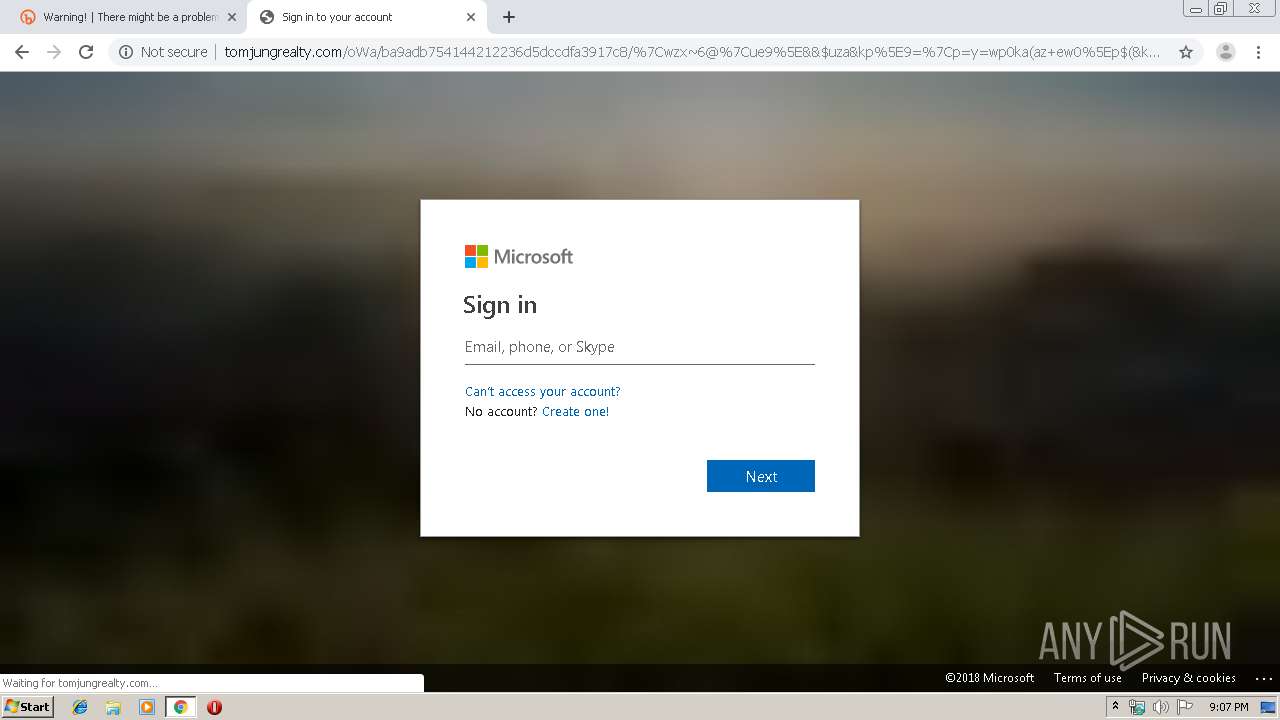
Loads Microsoft favicon from HTTP
- chrome.exe (PID: 716)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1404)
INFO
Reads the hosts file
- chrome.exe (PID: 1404)
- chrome.exe (PID: 716)
Application launched itself
- chrome.exe (PID: 1404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
32
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 320 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3957949572479962618 --mojo-platform-channel-handle=4308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 532 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=138554183018565820 --mojo-platform-channel-handle=4332 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=1912 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 716 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=7971574373412660034 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1245964940888935820 --mojo-platform-channel-handle=3120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=2003564787021125216 --mojo-platform-channel-handle=3584 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 820 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8324610466826584301 --renderer-client-id=28 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=16467437626104133629 --renderer-client-id=27 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1065875996314365459 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,2249942421517559100,7704110724703682479,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13425366617403747806 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3284 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
619
Read events
517
Write events
97
Delete events
5
Modification events
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1404) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1404-13220140020237000 |
Value: 259 | |||
Executable files
0
Suspicious files
30
Text files
257
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39ba90.TMP | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39ba90.TMP | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\67c01108-2d30-47cd-b3ac-e1e4088a3144.tmp | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 1404 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
27
TCP/UDP connections
47
DNS requests
21
Threats
13
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
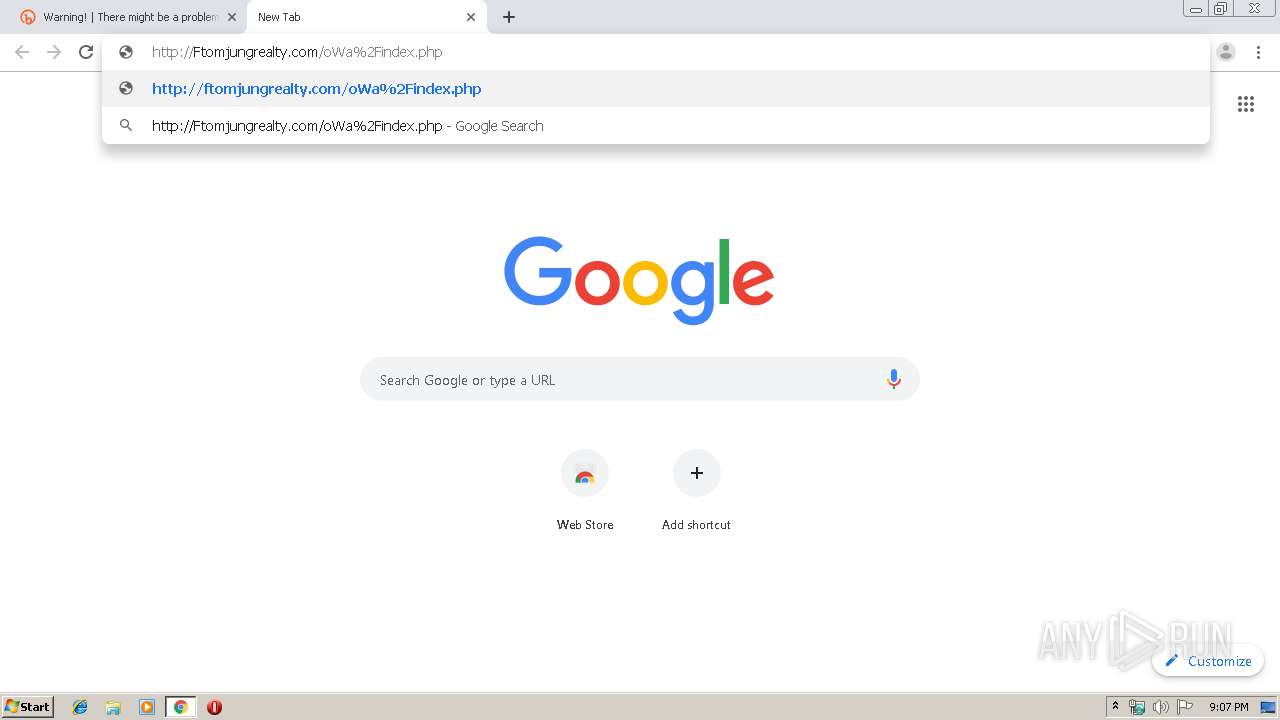
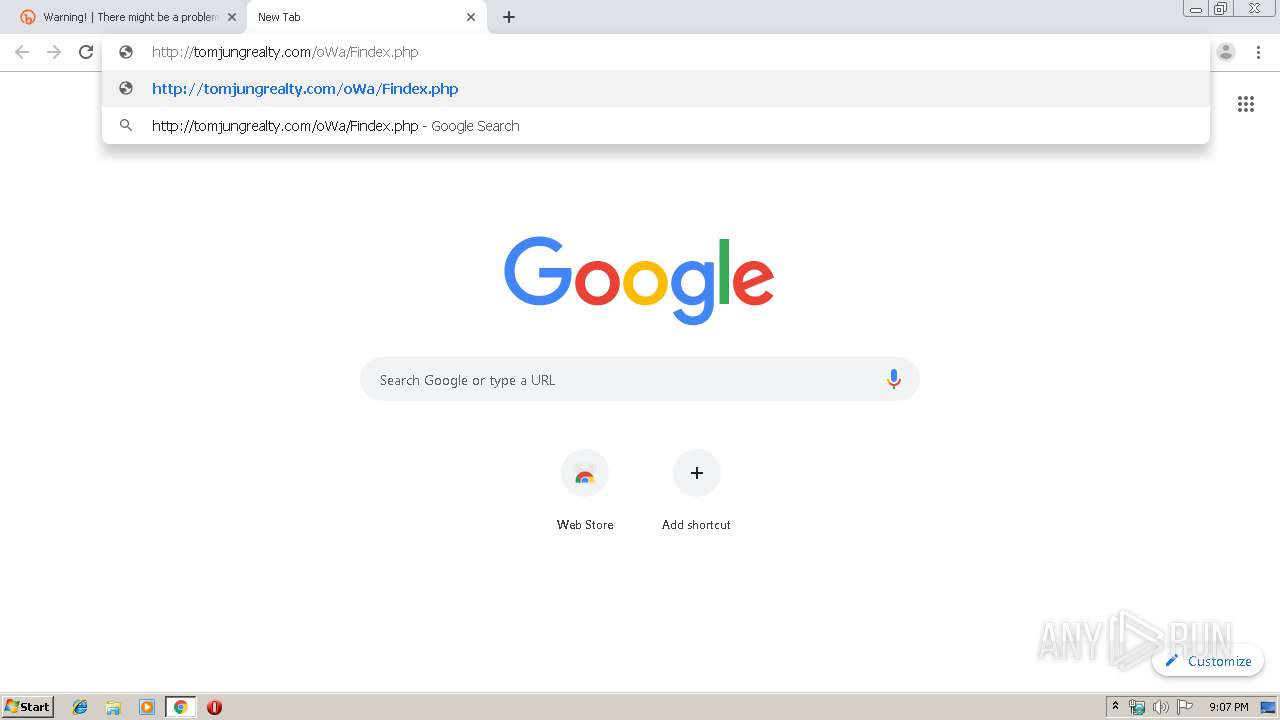
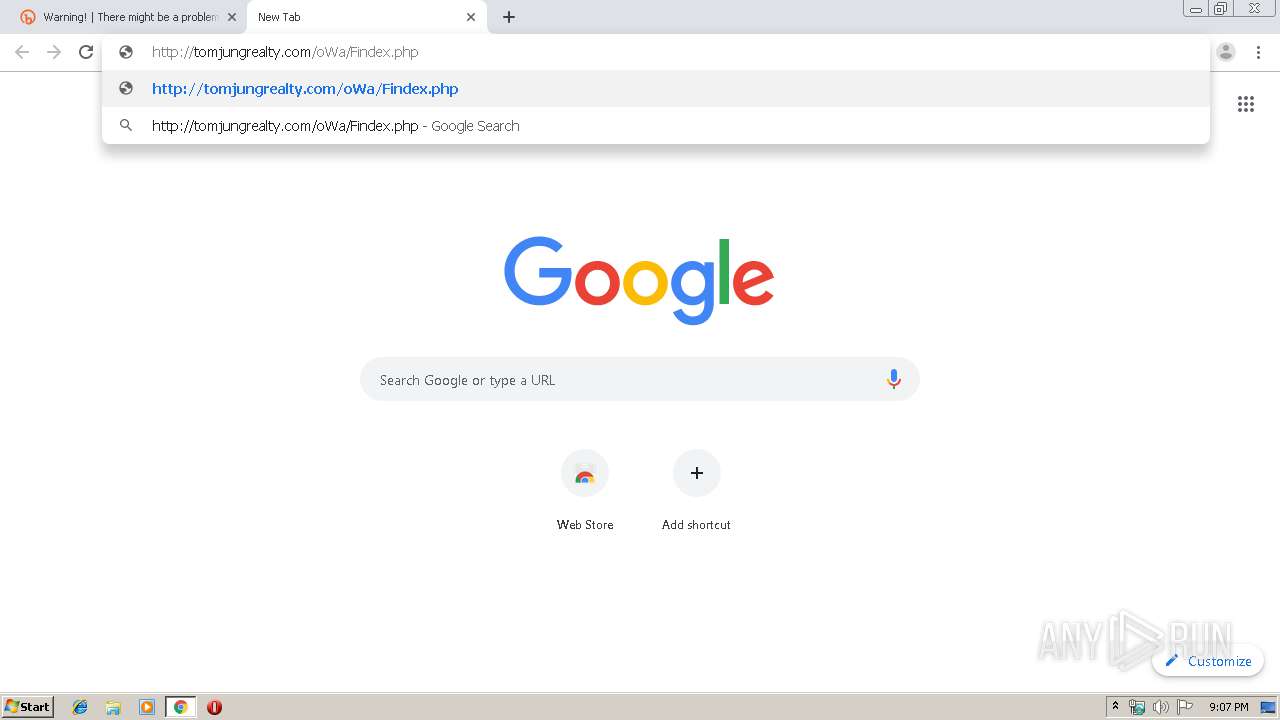
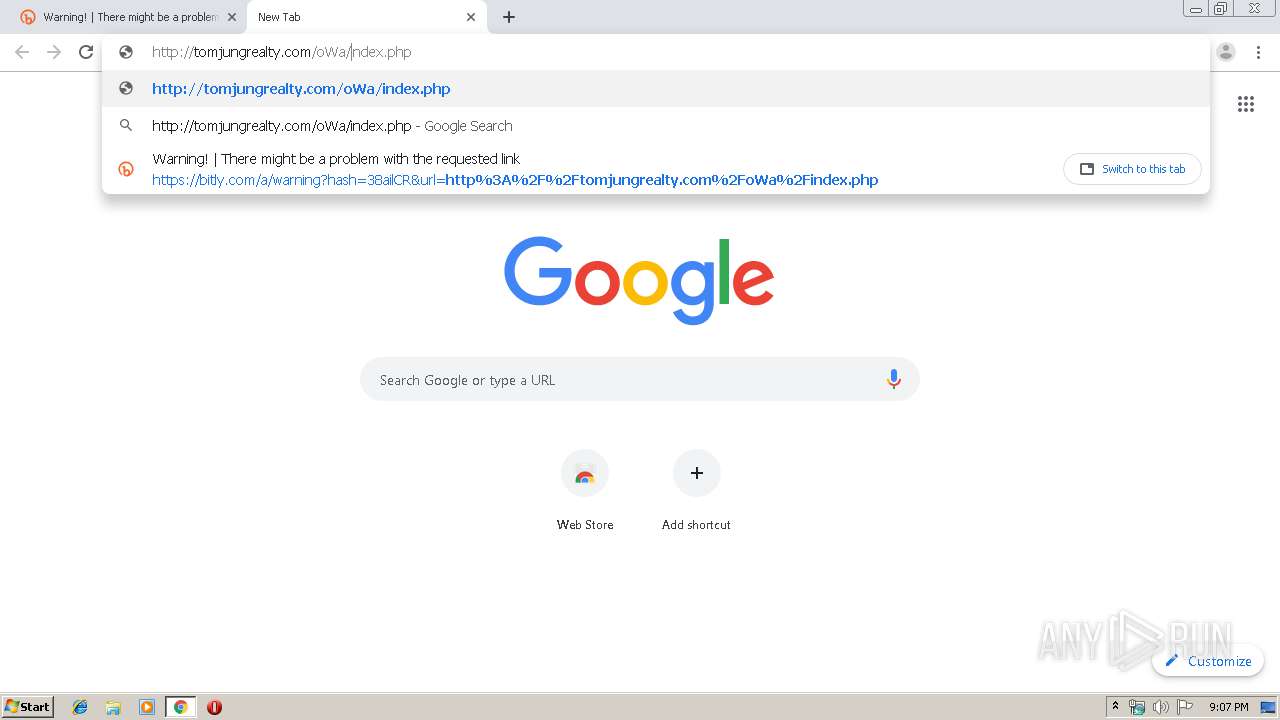
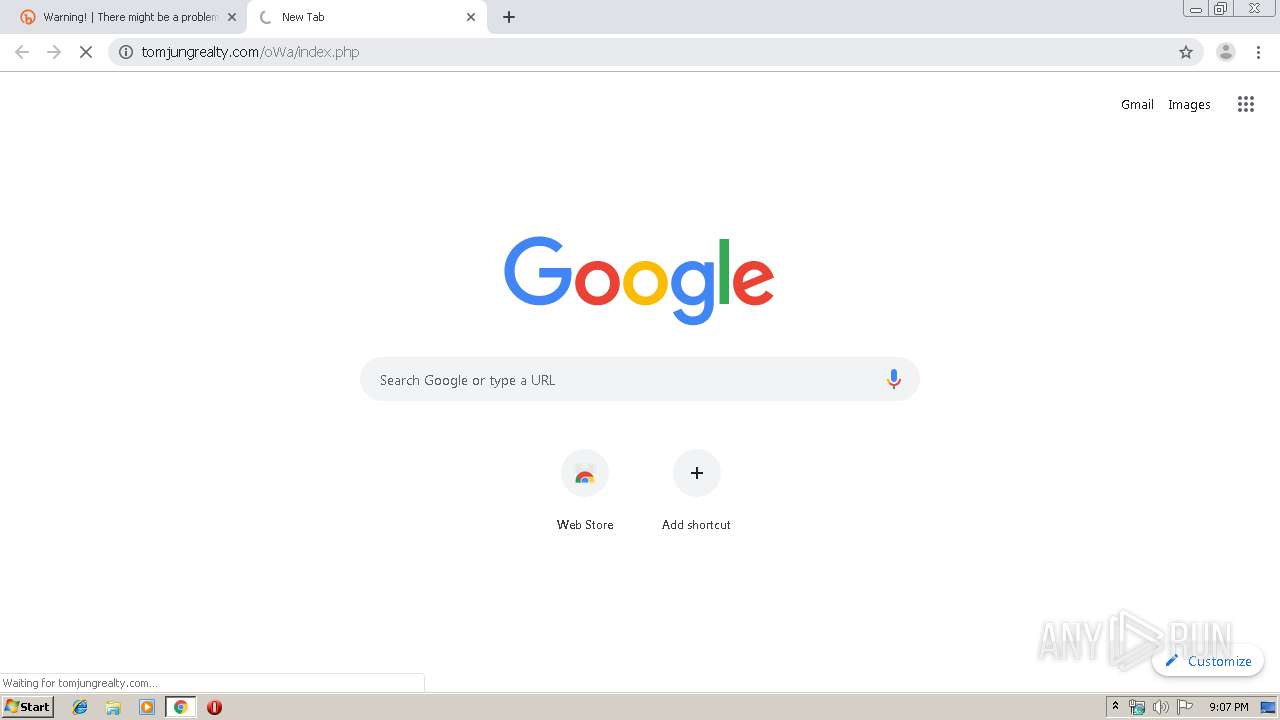
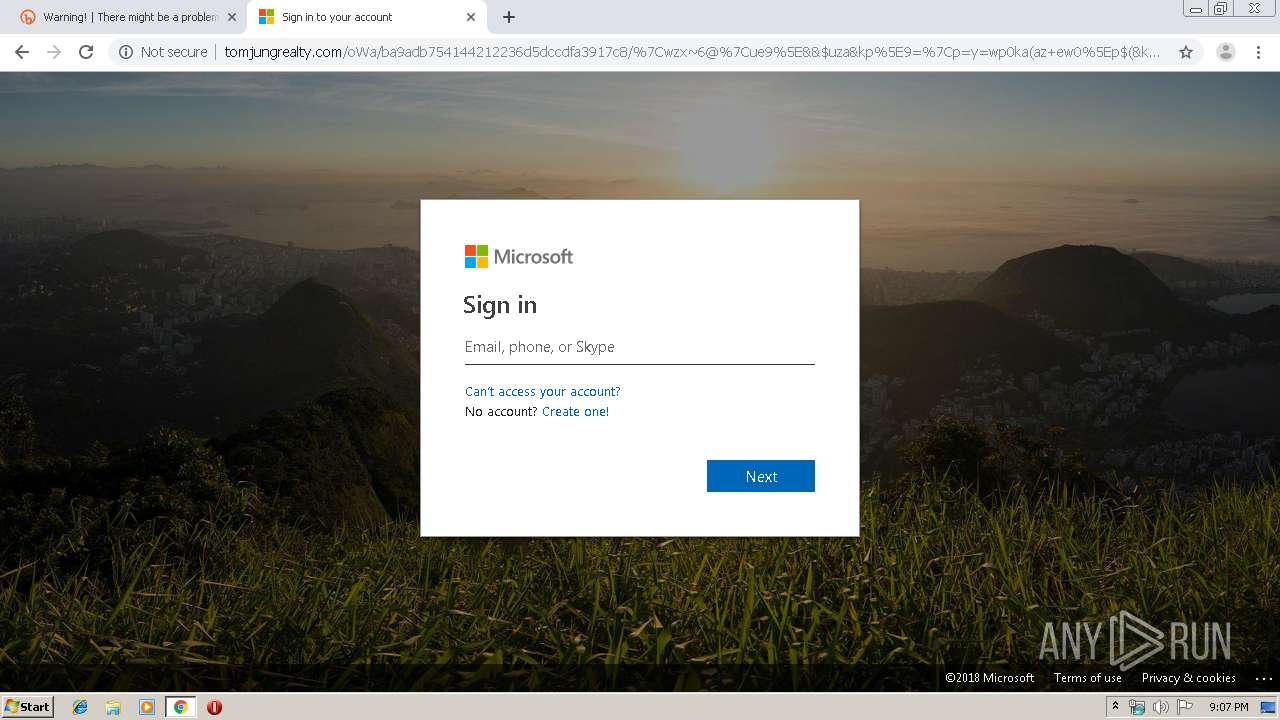
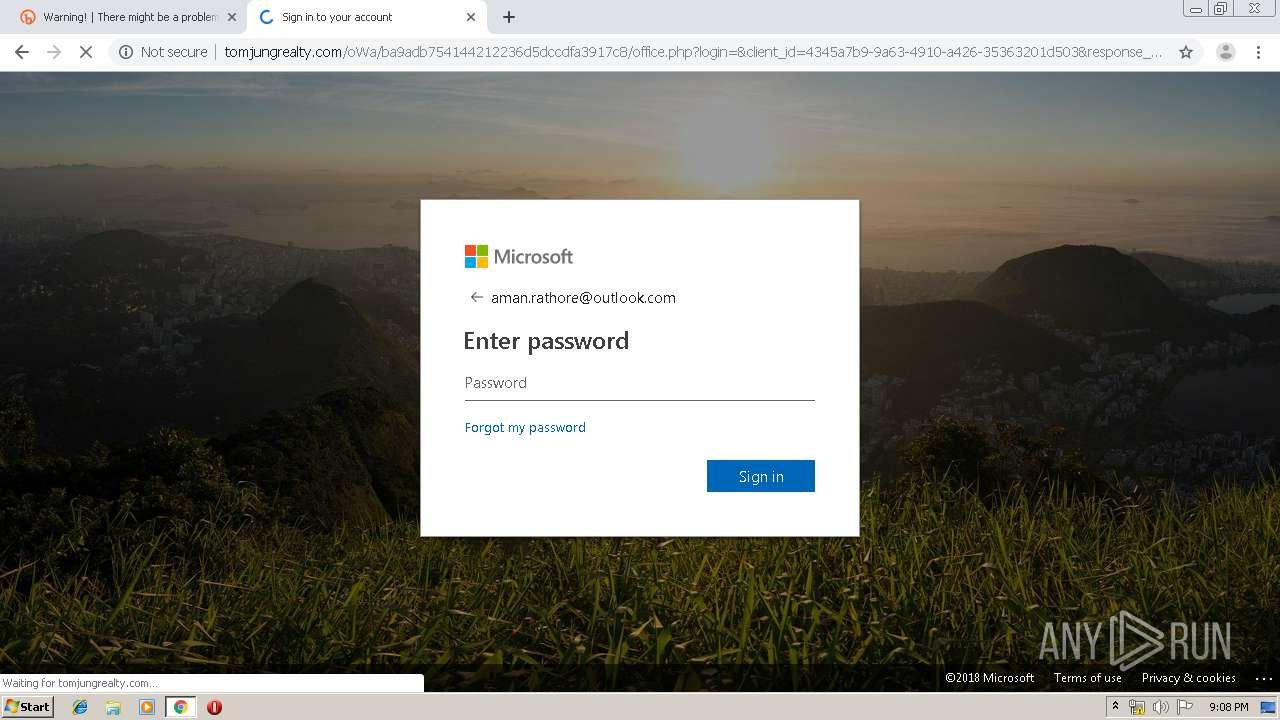
716 | chrome.exe | GET | 302 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/index.php | US | — | — | suspicious |
716 | chrome.exe | GET | 304 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/converged.v2.login.min.css | US | — | — | suspicious |
716 | chrome.exe | GET | 304 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/converged.v2.login.min.css | US | — | — | suspicious |
716 | chrome.exe | GET | 302 | 172.217.16.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 509 b | whitelisted |
716 | chrome.exe | GET | 301 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8?login=&?auth=2&home=1&from=PortalLanding&client-request-id=bcc7c79d-ad79-43ec-9c70-d12e378805d20cDovL3d3dy5hc@ | US | html | 397 b | suspicious |
716 | chrome.exe | GET | 200 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/converged.v2.login.min.css | US | text | 92.8 Kb | suspicious |
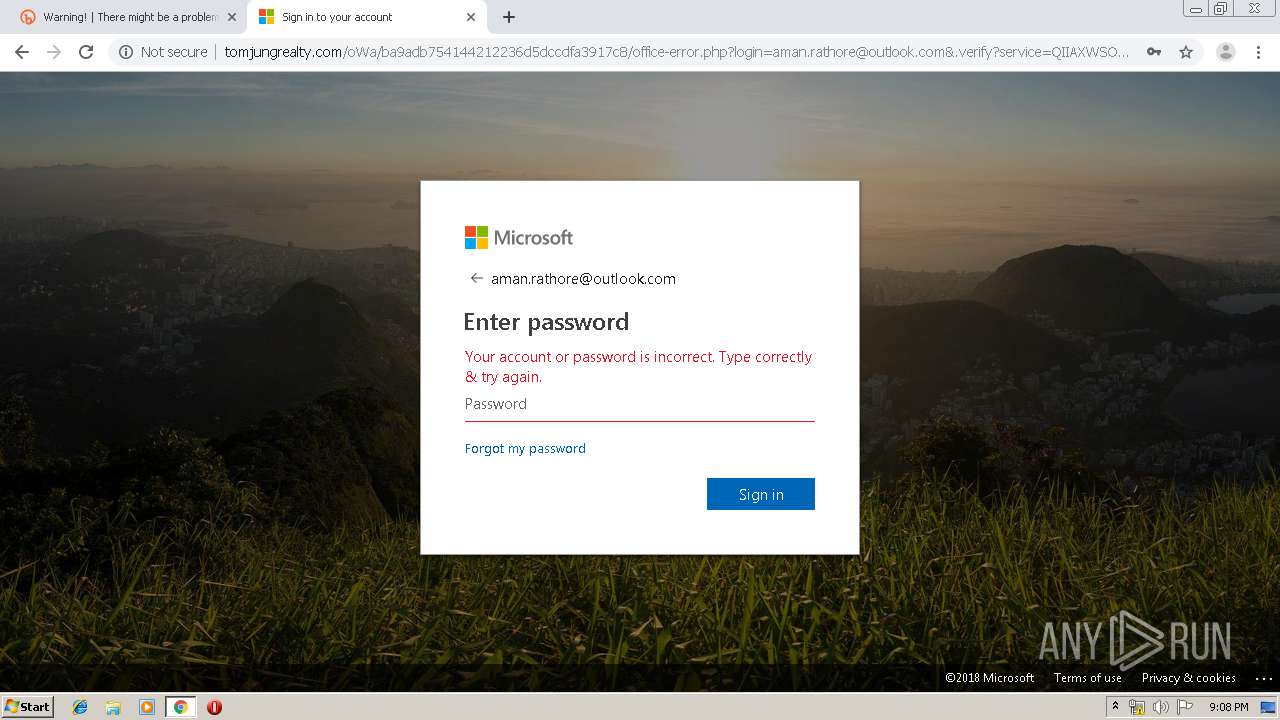
716 | chrome.exe | GET | 200 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/%7Cwzx~6@%7Cue9%5E&&$uza&kp%5E9=%7Cp=y=wp0ka(az+ew0%5Ep$(&kuk%5E%7C%5E+)x=@z=0u6w&pp%7C=~a%7C%5E%5Eyay~99%7C0w(w=$6z%60e.php?login=&.verify?service=mail&data:text/html;js6/main.jsp?sid=CAgbePXXjcVpfthPNgXXCcgDQZImqqTE&df=webmail126 | US | html | 10.6 Kb | suspicious |
716 | chrome.exe | GET | 302 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/?login=&?auth=2&home=1&from=PortalLanding&client-request-id=bcc7c79d-ad79-43ec-9c70-d12e378805d20cDovL3d3dy5hc@ | US | html | 397 b | suspicious |
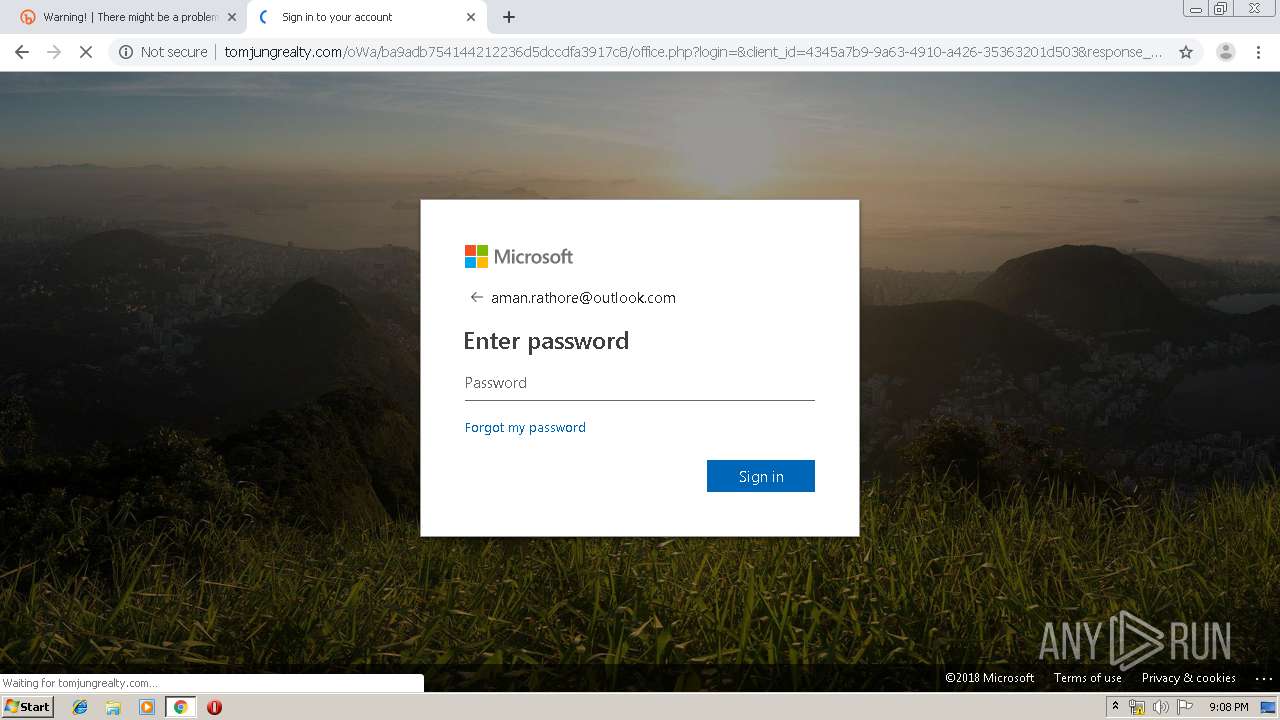
716 | chrome.exe | GET | 302 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/office.php?login=&client_id=4345a7b9-9a63-4910-a426-35363201d503&response_mode=form_post&response_type=code+id_token&scope=openid+profile&state=OpenIdConnect.AuthenticationProperties%3d-JJQNCNQ2z0ksmhozaEZ0BAbXmlhmEFKLfuuyzsjXAh36_lJevZlZV067KNNYAWjDxvsqLUzHdkt0L9dTPP5L1qlr4t02CYL2zfoM6553u5dm3xPVyUAJkHJYbTr1nZX&nonce=636662974340260123.YmQzNzg1ZTItNDhmMy00MDkzLWFhODMtZDZjNjQ0ODE5MTgyYmZiMmJkYWYtZmYwYy00MmJhLWI4OGQtNGZhNTVmNjNkYzI0&redirect_uri=https%3a%2f%2fwww.office.com%2f&ui_locales=en-US&mkt=en-US | US | html | 12.0 Kb | suspicious |
716 | chrome.exe | GET | 302 | 162.241.67.217:80 | http://tomjungrealty.com/oWa/ba9adb754144212236d5dccdfa3917c8/office.php?login=&client_id=4345a7b9-9a63-4910-a426-35363201d503&response_mode=form_post&response_type=code+id_token&scope=openid+profile&state=OpenIdConnect.AuthenticationProperties%3d-JJQNCNQ2z0ksmhozaEZ0BAbXmlhmEFKLfuuyzsjXAh36_lJevZlZV067KNNYAWjDxvsqLUzHdkt0L9dTPP5L1qlr4t02CYL2zfoM6553u5dm3xPVyUAJkHJYbTr1nZX&nonce=636662974340260123.YmQzNzg1ZTItNDhmMy00MDkzLWFhODMtZDZjNjQ0ODE5MTgyYmZiMmJkYWYtZmYwYy00MmJhLWI4OGQtNGZhNTVmNjNkYzI0&redirect_uri=https%3a%2f%2fwww.office.com%2f&ui_locales=en-US&mkt=en-US | US | html | 12.0 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
716 | chrome.exe | 172.217.18.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 67.199.248.10:80 | bit.ly | Bitly Inc | US | shared |
716 | chrome.exe | 67.199.248.15:443 | bitly.com | Bitly Inc | US | shared |
716 | chrome.exe | 172.217.23.132:443 | www.google.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 172.217.23.174:443 | clients2.google.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 172.217.16.142:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 216.58.206.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 209.85.226.106:80 | r5---sn-5hne6ns6.gvt1.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 172.217.132.106:80 | r5---sn-5hne6nsy.gvt1.com | Google Inc. | US | whitelisted |
716 | chrome.exe | 172.217.18.163:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
bit.ly |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
bitly.com |
| shared |
www.google.com |
| malicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r5---sn-5hne6ns6.gvt1.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
r5---sn-5hne6nsy.gvt1.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
716 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
716 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Http Client Body contains passwd= in cleartext |
11 ETPRO signatures available at the full report