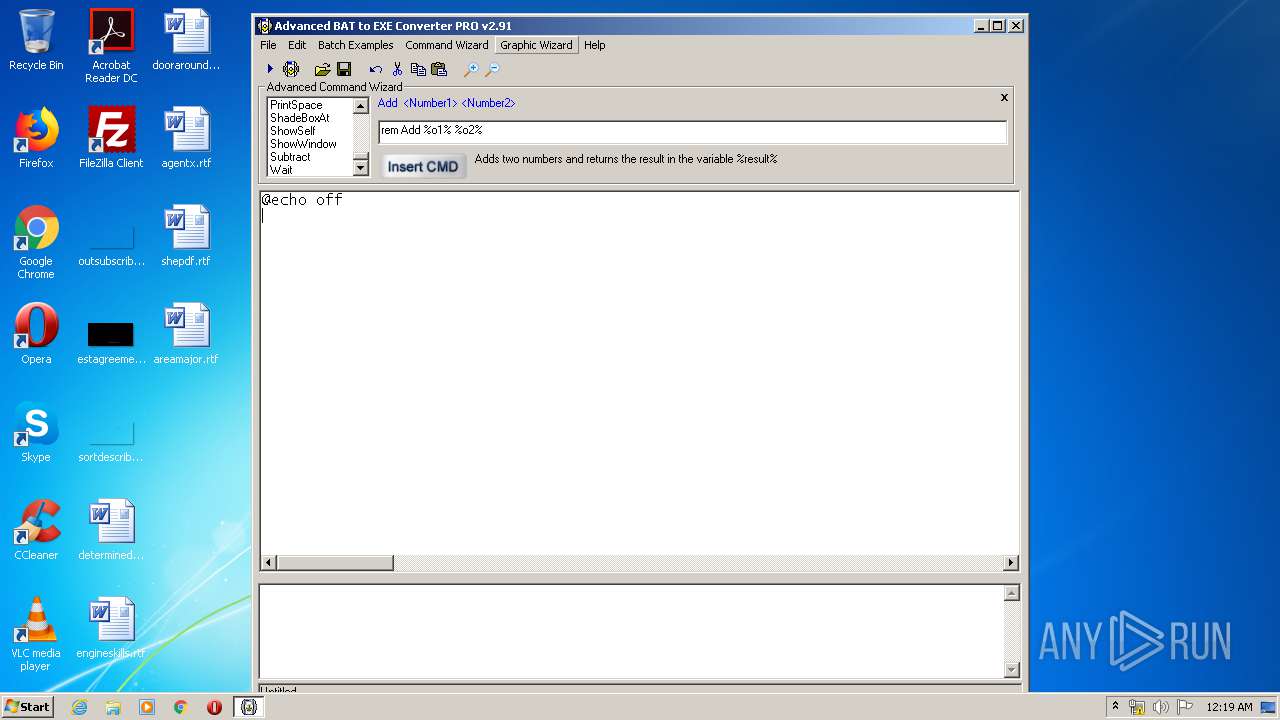
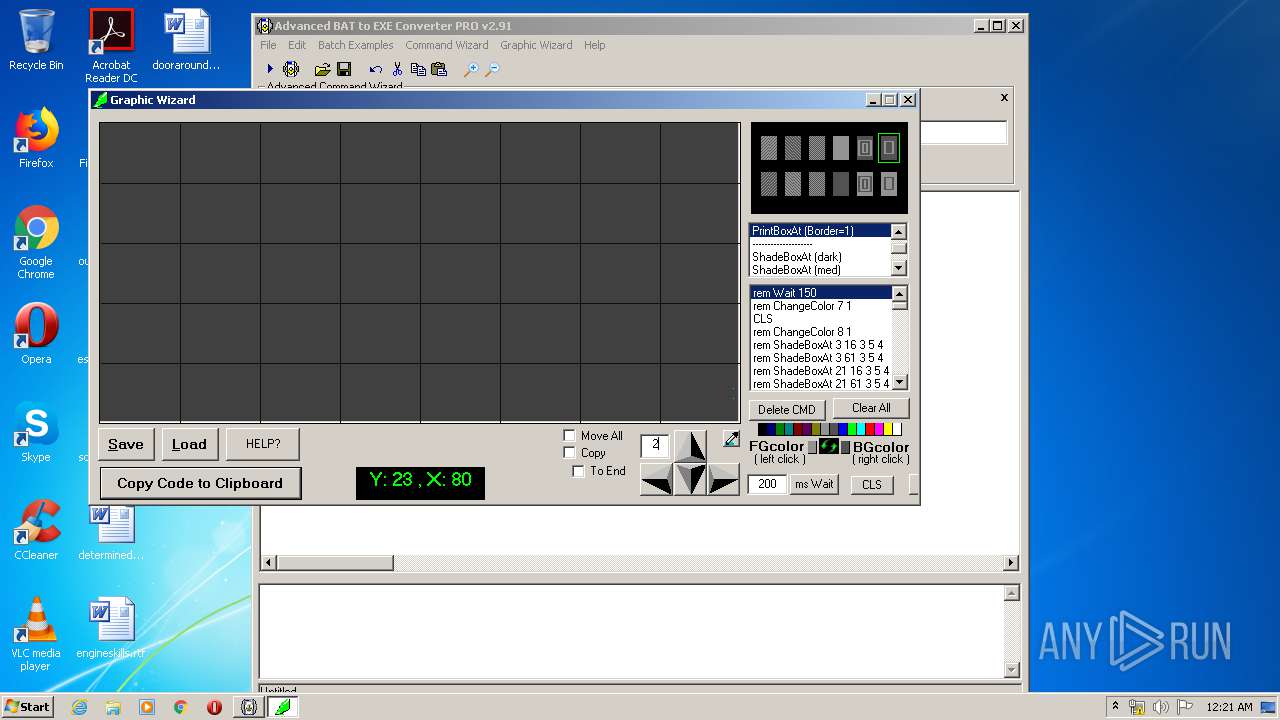
| File name: | advbattoexepro.exe |
| Full analysis: | https://app.any.run/tasks/39a3ea2e-8149-4ee1-9a55-d1a21e3cba7b |
| Verdict: | Malicious activity |
| Analysis date: | May 09, 2020, 23:16:48 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | BBBAACA2B5255ADEA522C4F10C7BE081 |
| SHA1: | B55B0AEC4310FDF13B0FB1162F4536BCBAFD966C |
| SHA256: | 2BC5AC616A0D609E602E92AC479FB67E41463EFEB7741821D6FE97162B549EC1 |
| SSDEEP: | 12288:dSGxFfe7DU9+XbRnoXbCZrT5tmOMvZ73hRqs+gxI8RN09EVTwZ1LRjNnoojz:9xFj9+XbRnoXbA5gC/gxI8RN09EG99oi |
MALICIOUS
Loads dropped or rewritten executable
- ab2econv.exe (PID: 3496)
- advbattoexepro.exe (PID: 3284)
- aB2Econv.exe (PID: 3328)
Application was dropped or rewritten from another process
- setupinf.exe (PID: 3312)
- gewizold.exe (PID: 2388)
- gewiz.exe (PID: 1504)
- aB2Econv.exe (PID: 3328)
- activate.exe (PID: 2800)
- ab2econv.exe (PID: 3496)
- fastcmd.exe (PID: 2192)
- activate.exe (PID: 3044)
- fastcmd.exe (PID: 3192)
- fastcmd.exe (PID: 2548)
- fastcmd.exe (PID: 3316)
- fastcmd.exe (PID: 2764)
SUSPICIOUS
Executable content was dropped or overwritten
- advbattoexepro.exe (PID: 3284)
- gewiz.exe (PID: 1504)
Creates files in the user directory
- advbattoexepro.exe (PID: 3284)
Creates files in the Windows directory
- advbattoexepro.exe (PID: 3284)
Creates a software uninstall entry
- advbattoexepro.exe (PID: 3284)
Creates files in the program directory
- advbattoexepro.exe (PID: 3284)
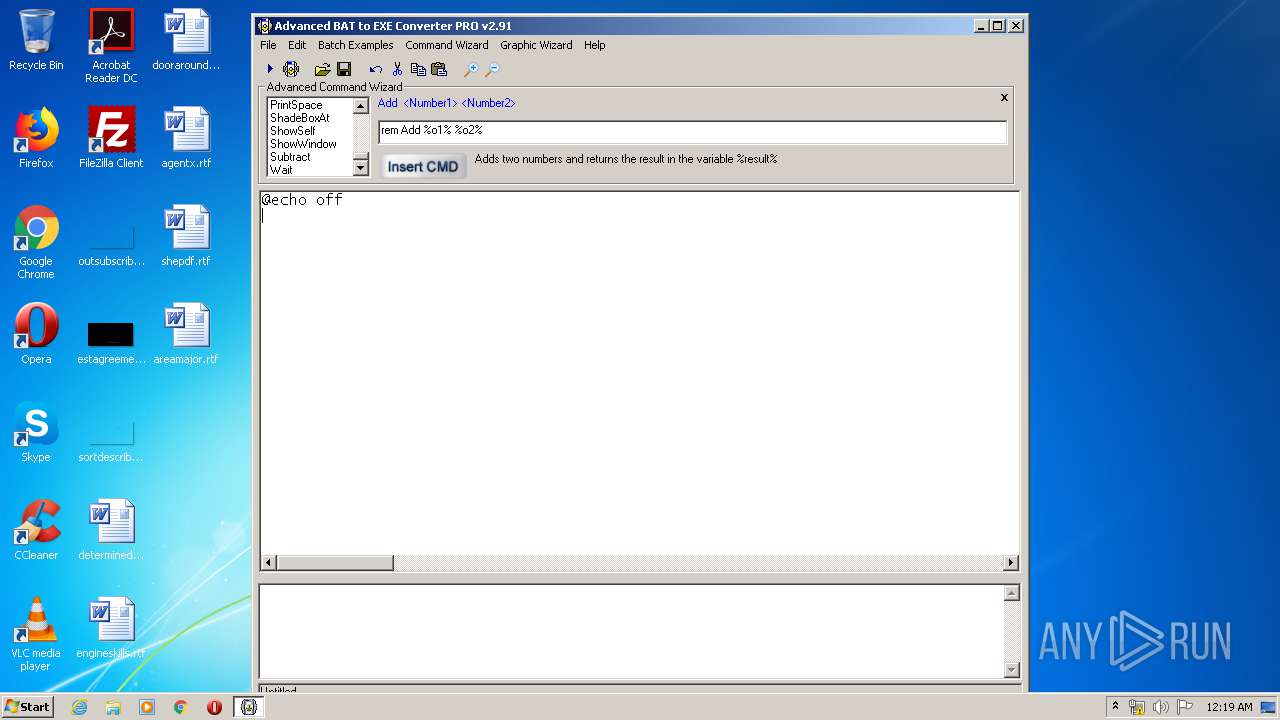
Starts CMD.EXE for commands execution
- gewiz.exe (PID: 1504)
- fastcmd.exe (PID: 3192)
- fastcmd.exe (PID: 2548)
- fastcmd.exe (PID: 3316)
- fastcmd.exe (PID: 2764)
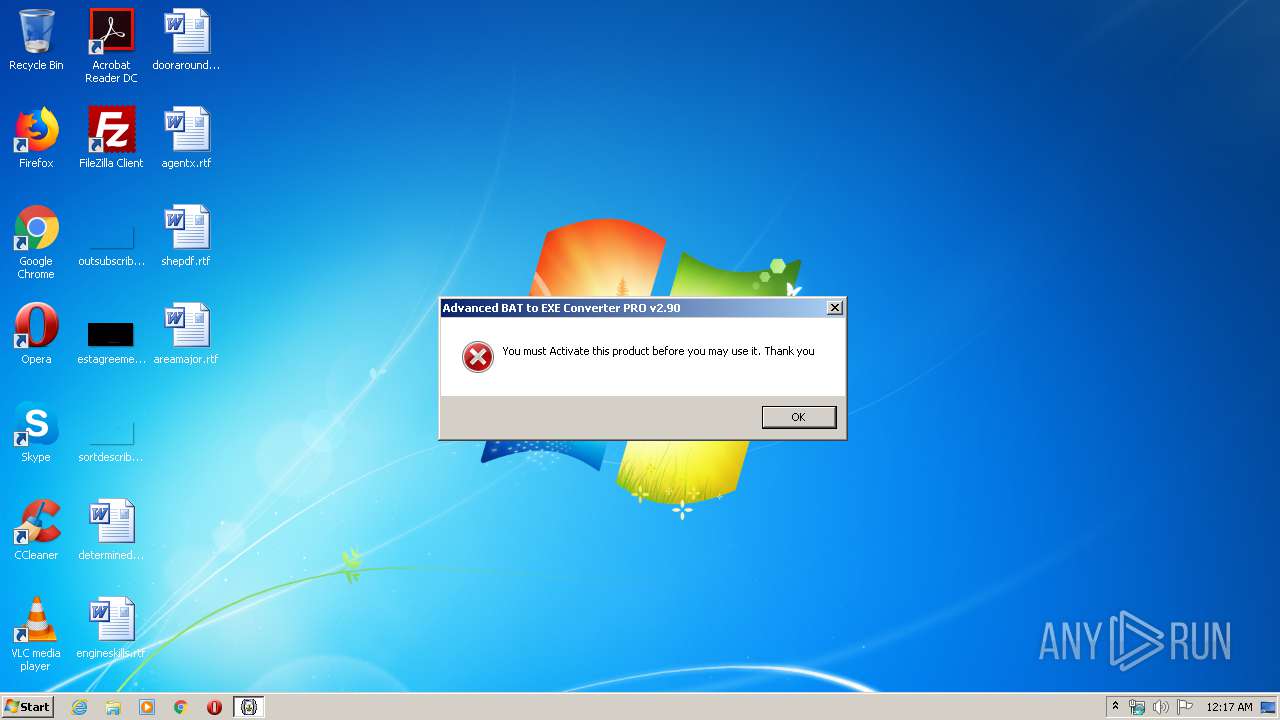
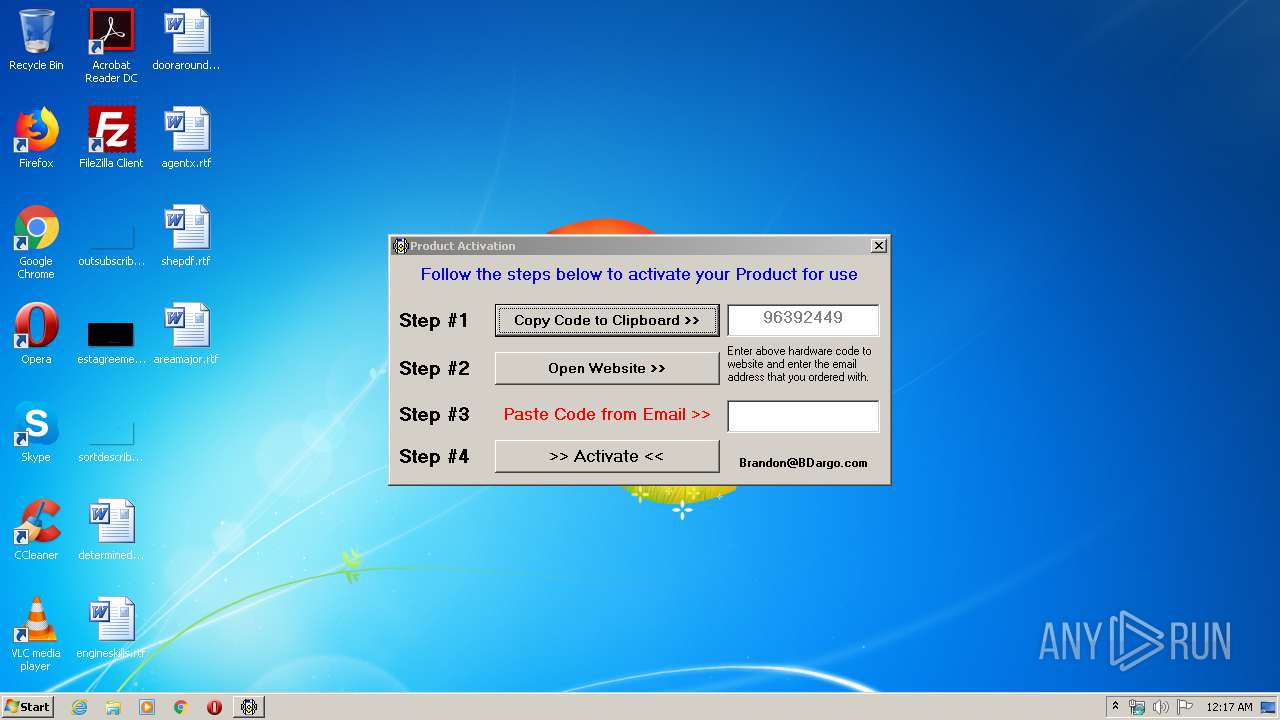
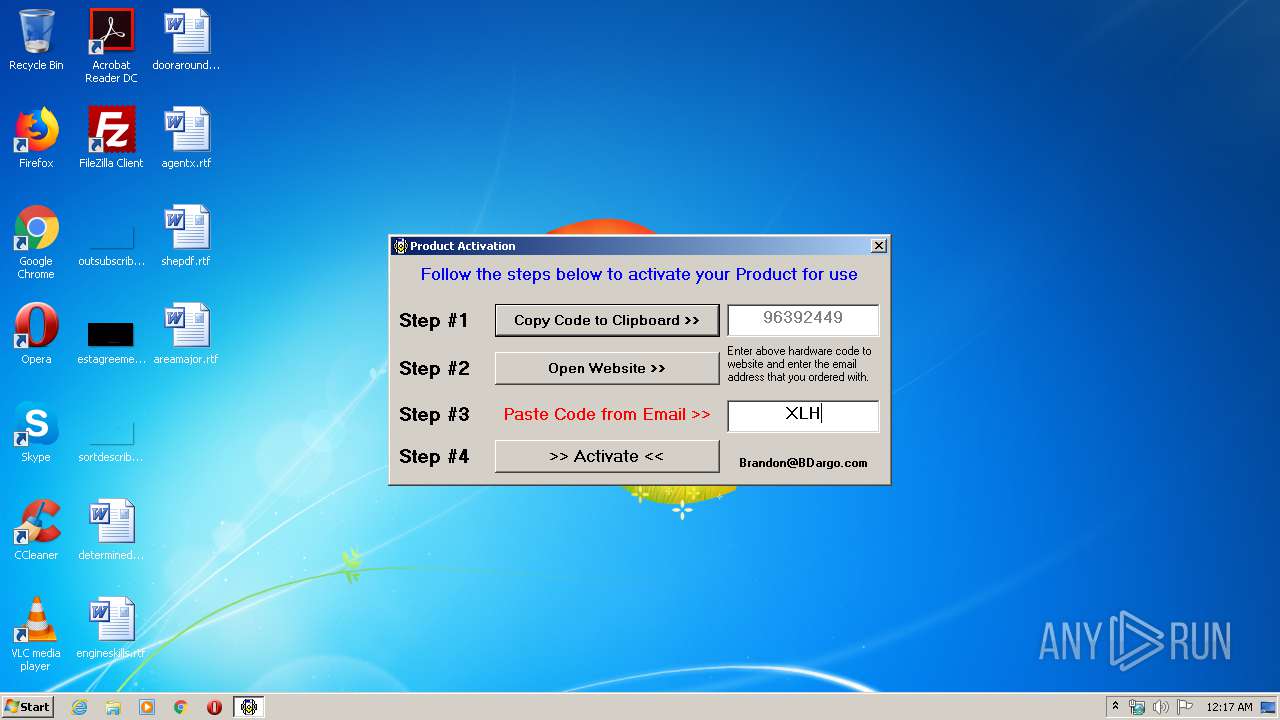
INFO
Manual execution by user
- aB2Econv.exe (PID: 3328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.3) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2006:04:05 10:55:39+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 3 |
| CodeSize: | 3584 |
| InitializedDataSize: | 93696 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1226 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 05-Apr-2006 08:55:39 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 05-Apr-2006 08:55:39 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00000C91 | 0x00000E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.93214 |
.rdata | 0x00002000 | 0x00000078 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.707162 |
.data | 0x00003000 | 0x00000504 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.12782 |
.idata | 0x00004000 | 0x000002B0 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.45462 |
.reloc | 0x00005000 | 0x0000012C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.28756 |
.gentee | 0x00006000 | 0x00013AD6 | 0x00013C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.99589 |
.rsrc | 0x0001A000 | 0x0000259C | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.89601 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.99128 | 784 | Latin 1 / Western European | English - United States | RT_MANIFEST |
1000 | 2.23119 | 54 | Latin 1 / Western European | English - United States | RT_DIALOG |
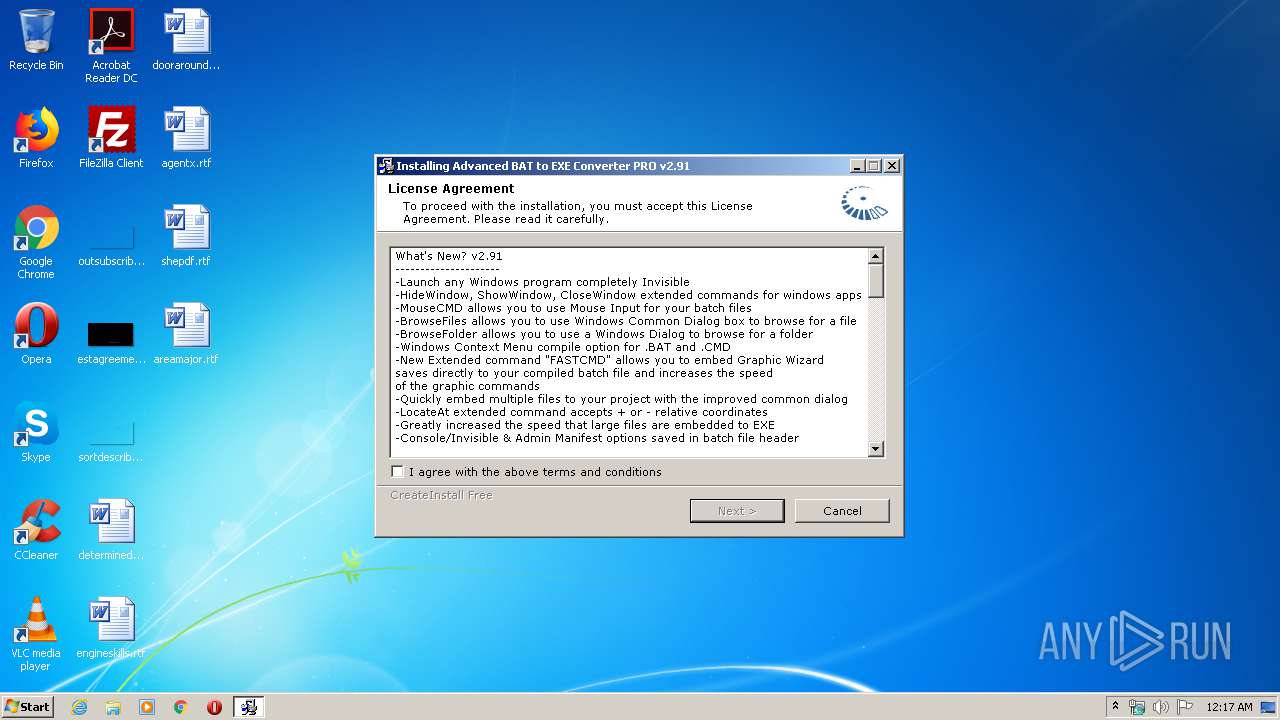
IDD_DLGLIC | 2.66912 | 440 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
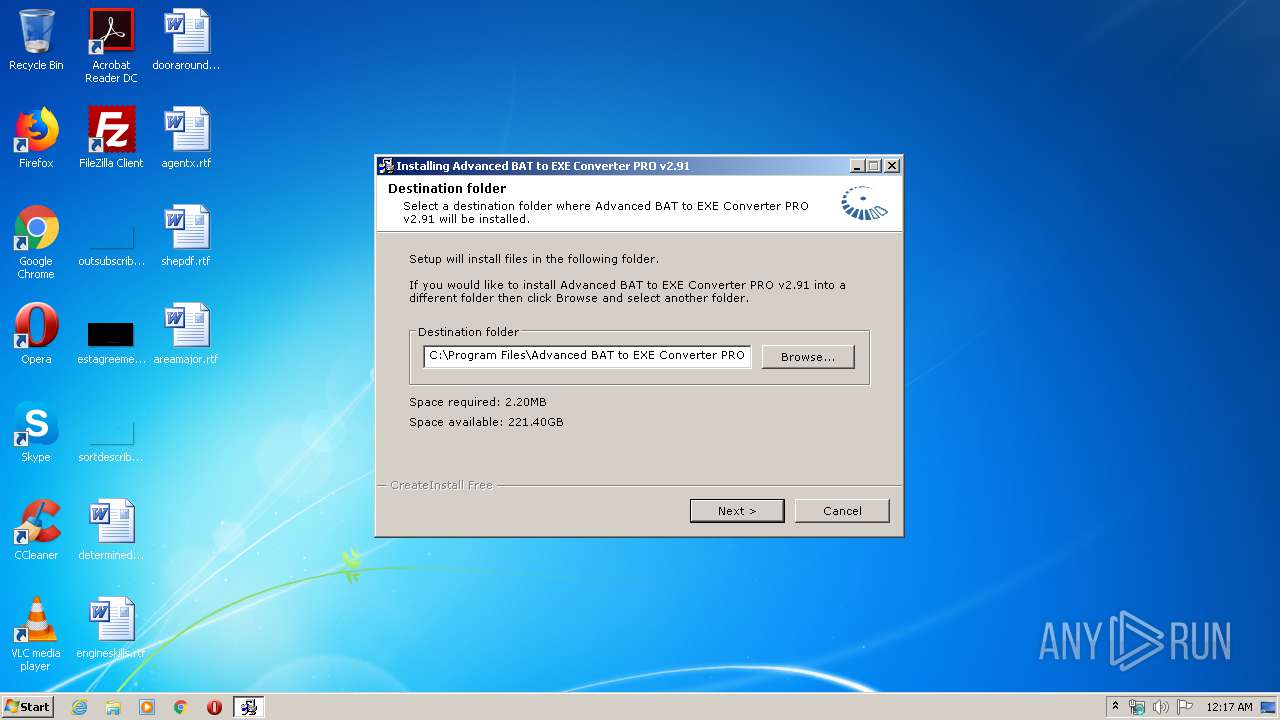
IDD_DLGPATH | 2.69399 | 640 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGPROG | 2.70702 | 568 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGUCONF | 2.54565 | 376 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGUFIN | 2.60408 | 440 | Latin 1 / Western European | English - United States | RT_DIALOG |
IDD_DLGUNDEL | 2.6827 | 504 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
IDD_DLGUPROG | 2.71234 | 504 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
SETUP_TEMP | 7.89598 | 3621 | Latin 1 / Western European | UNKNOWN | RT_RCDATA |
Imports
KERNEL32.dll |
USER32.dll |
Total processes
73
Monitored processes
23
Malicious processes
5
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1340 | cmd /c ""C:\Users\admin\AppData\Local\Temp\bfcwrk\do.bat" " | C:\Windows\system32\cmd.exe | — | gewiz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
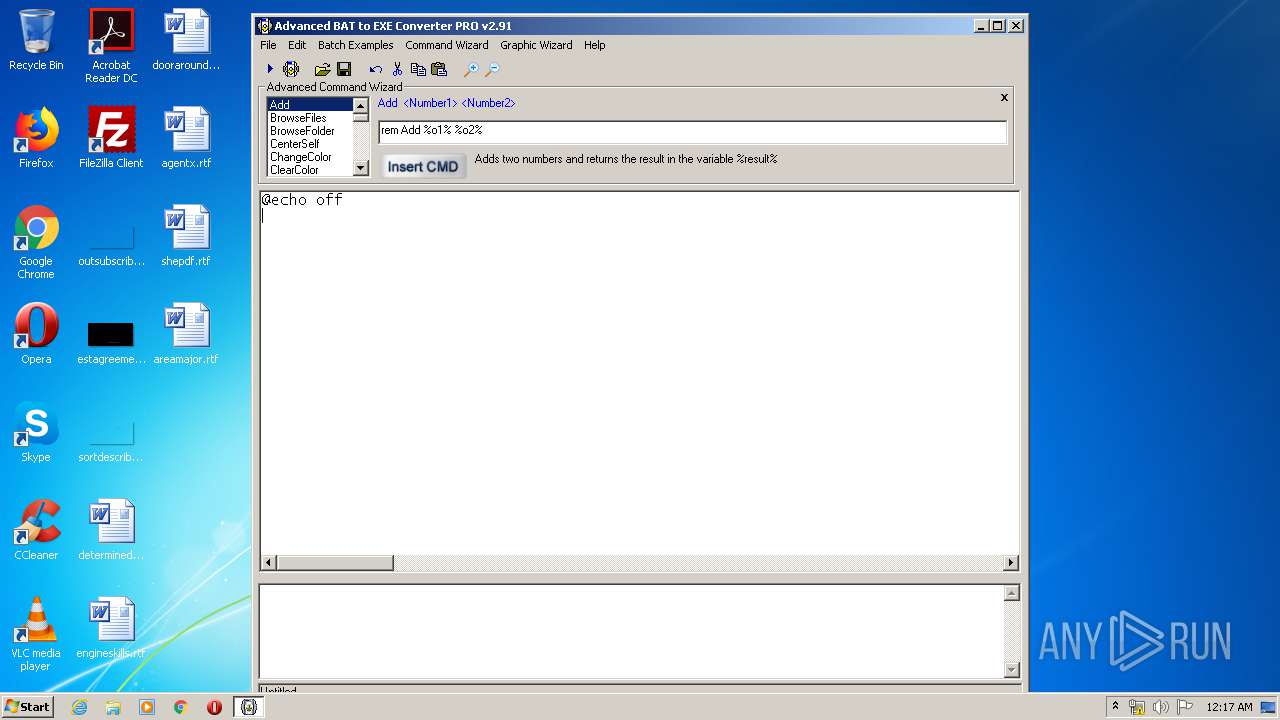
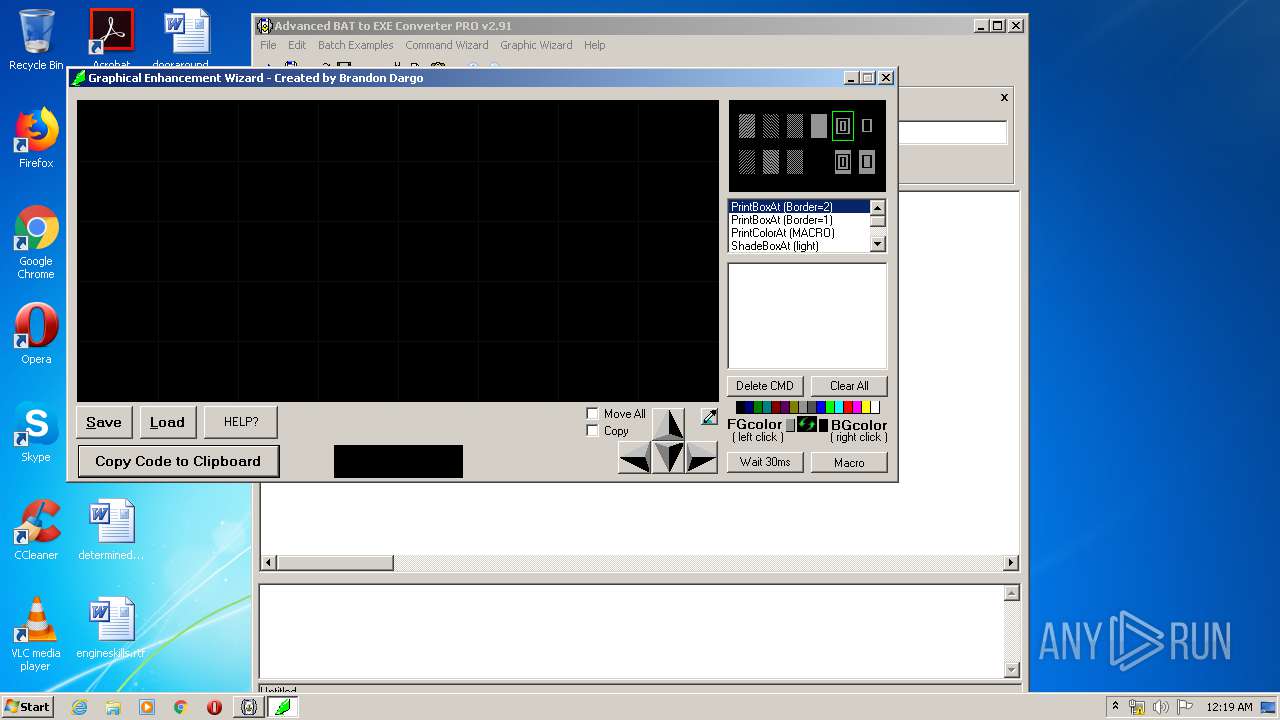
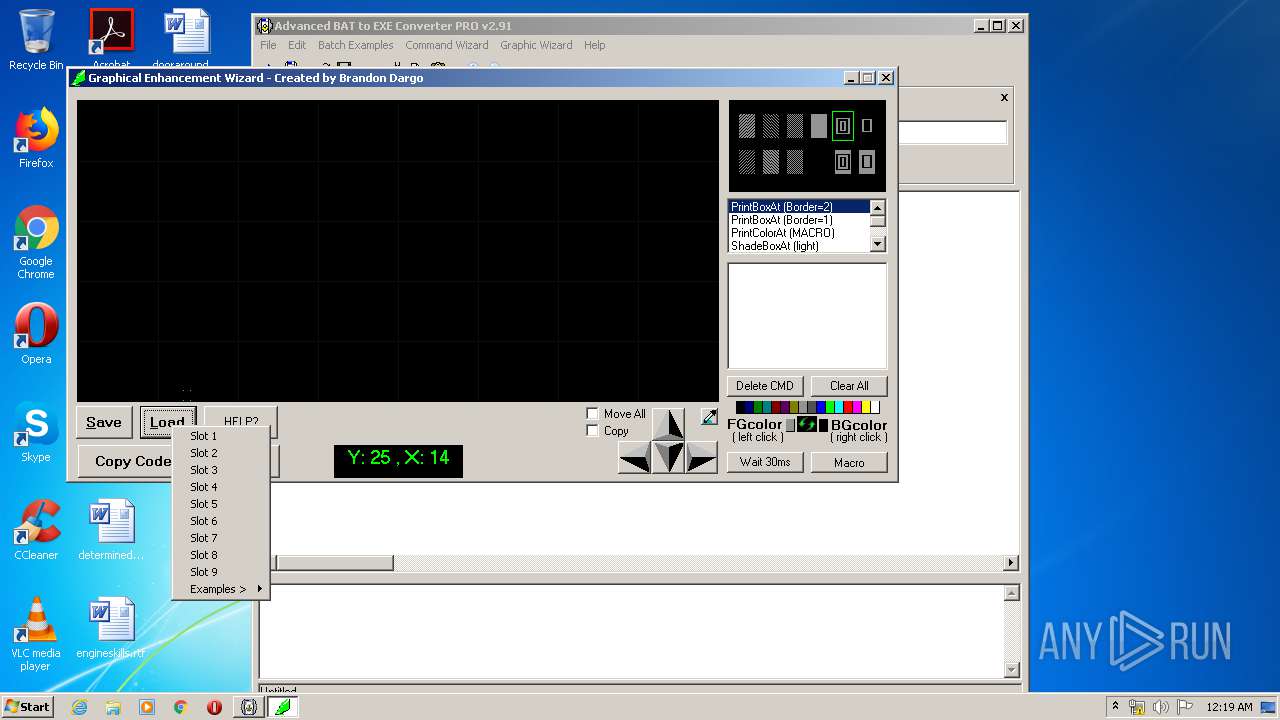
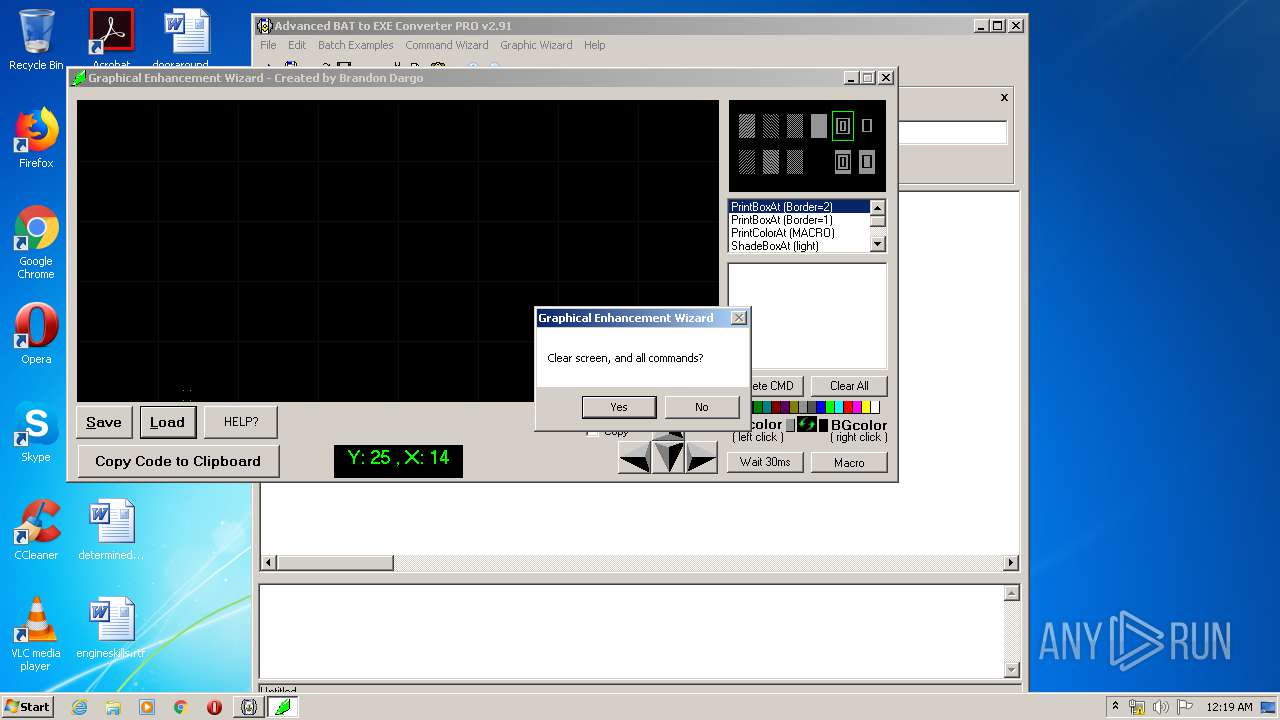
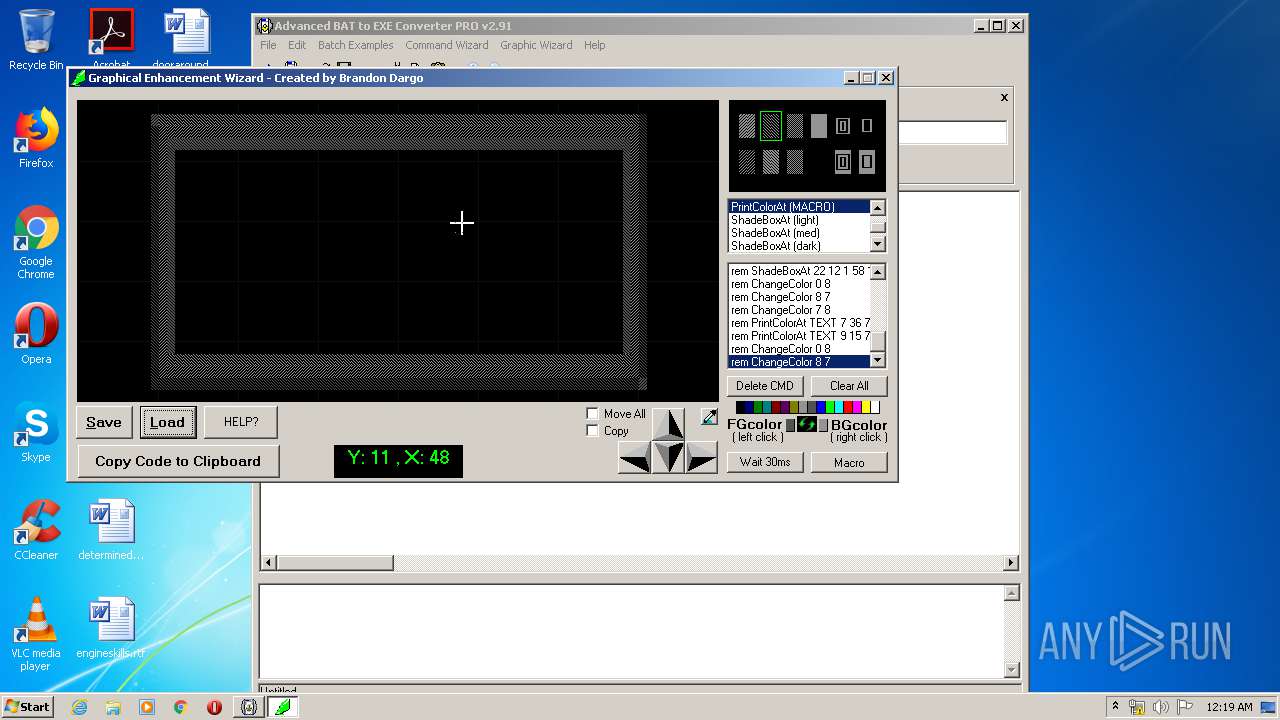
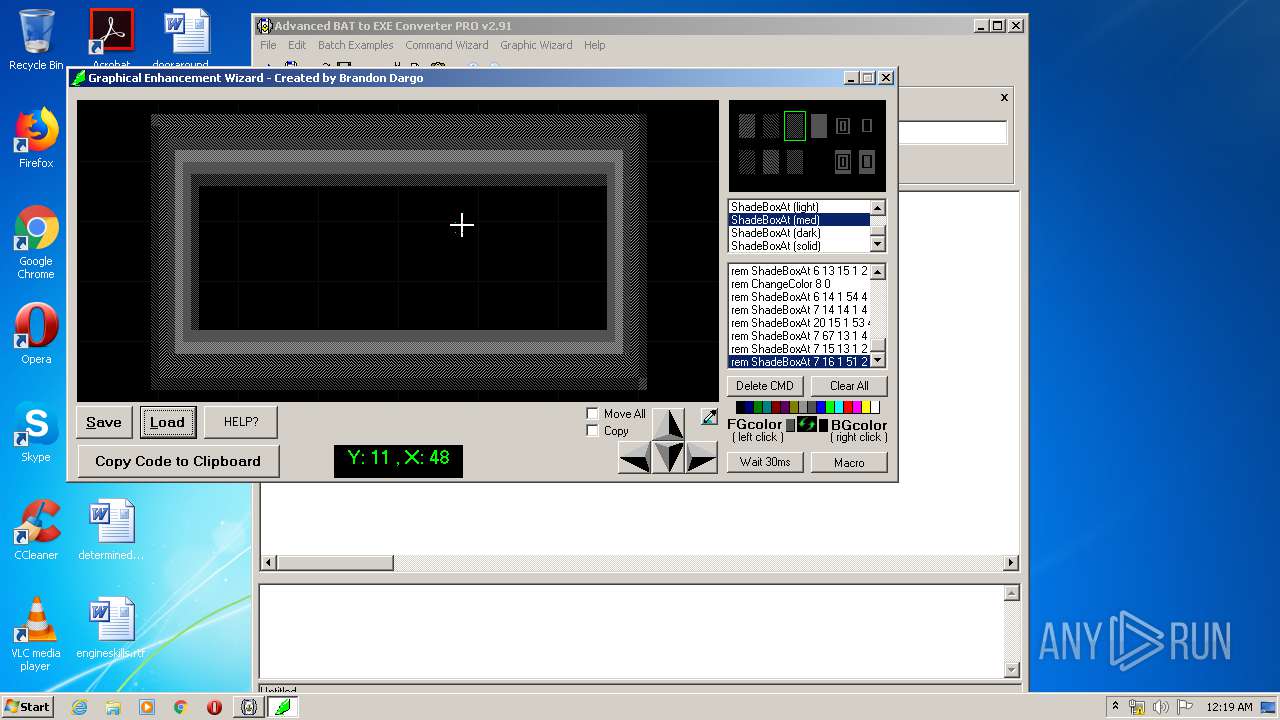
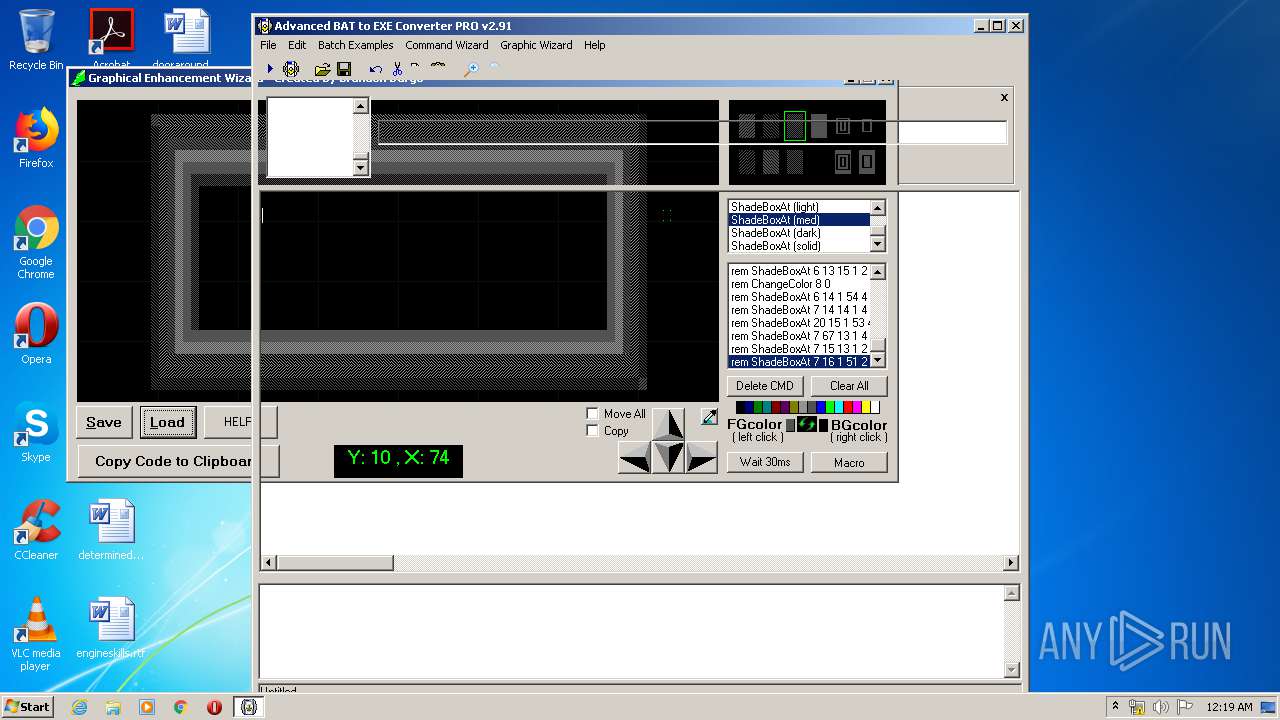
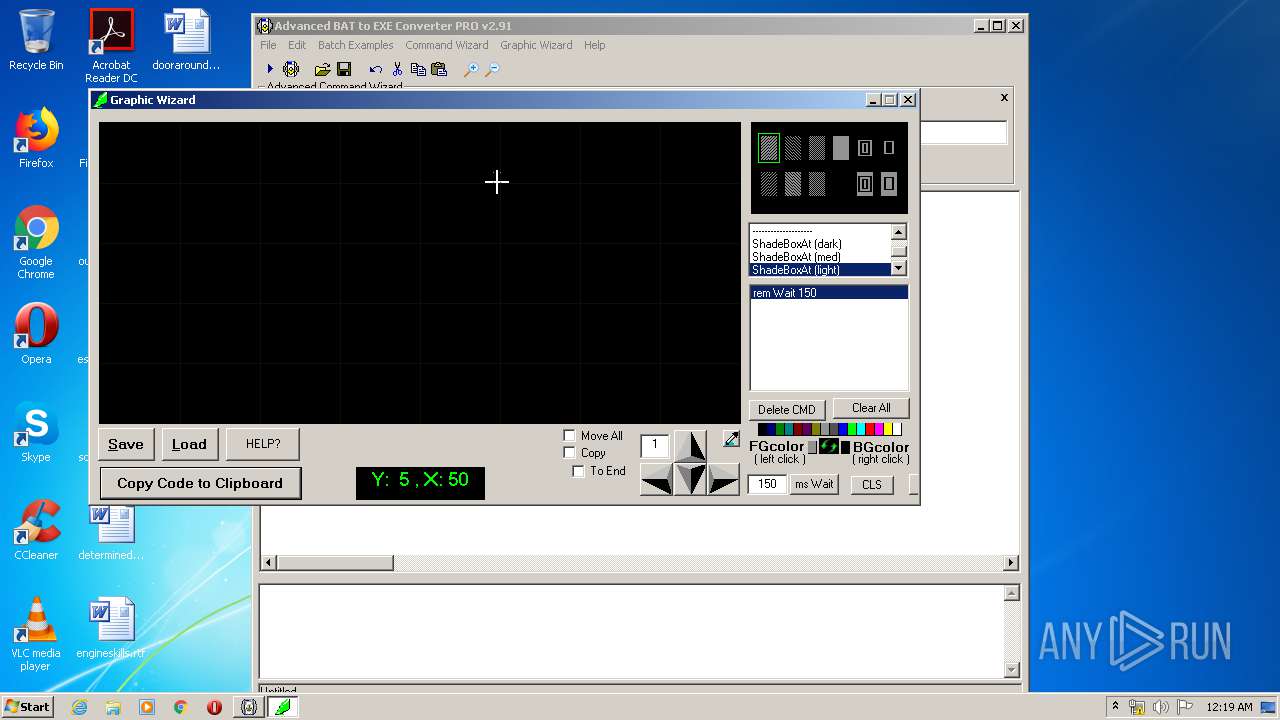
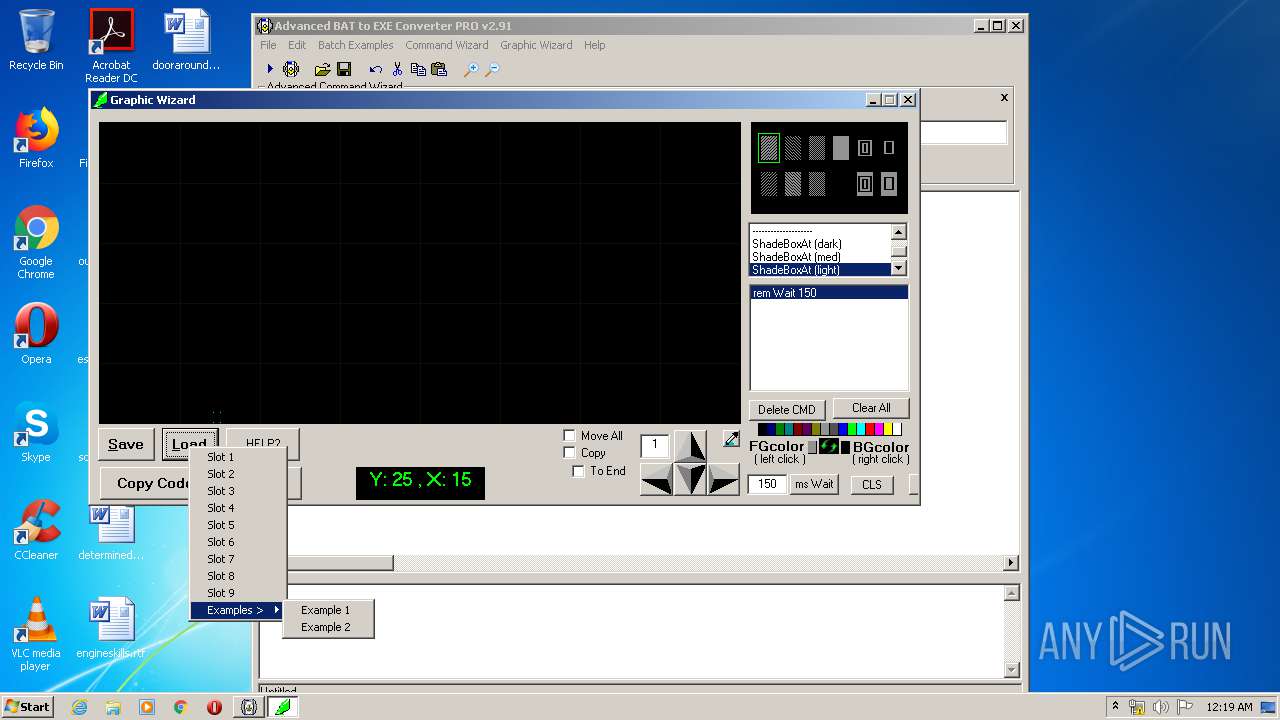
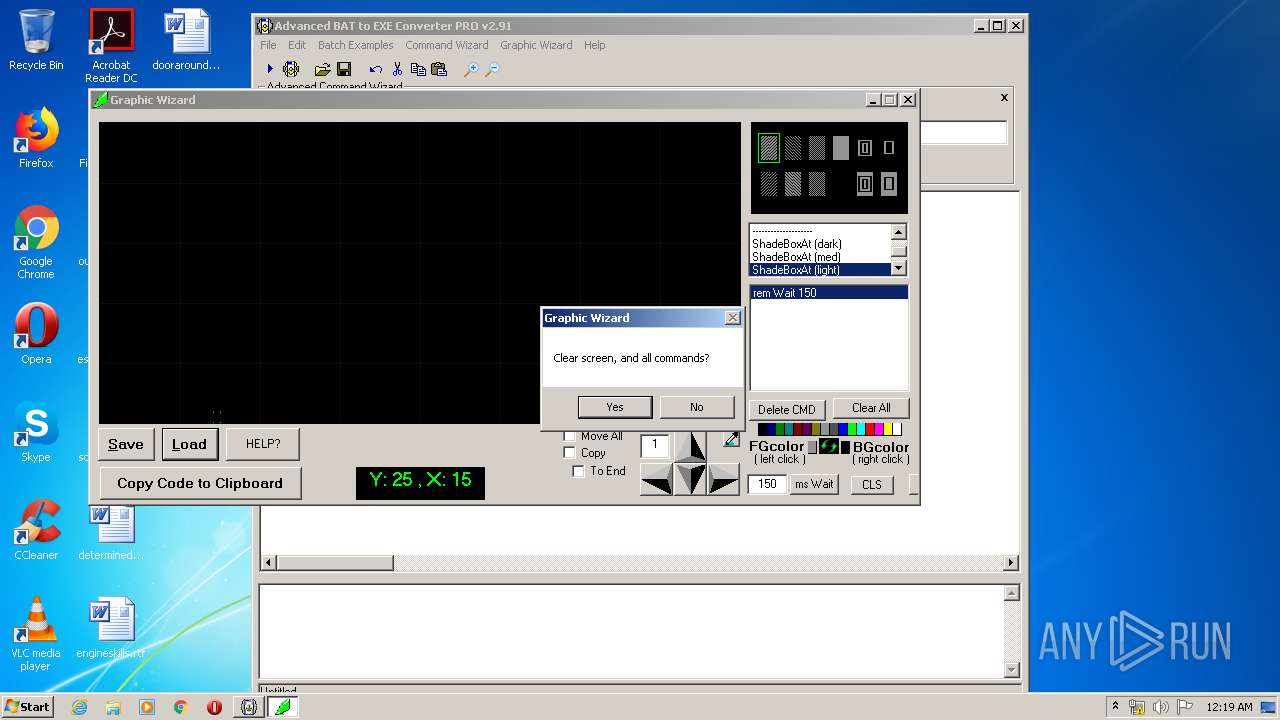
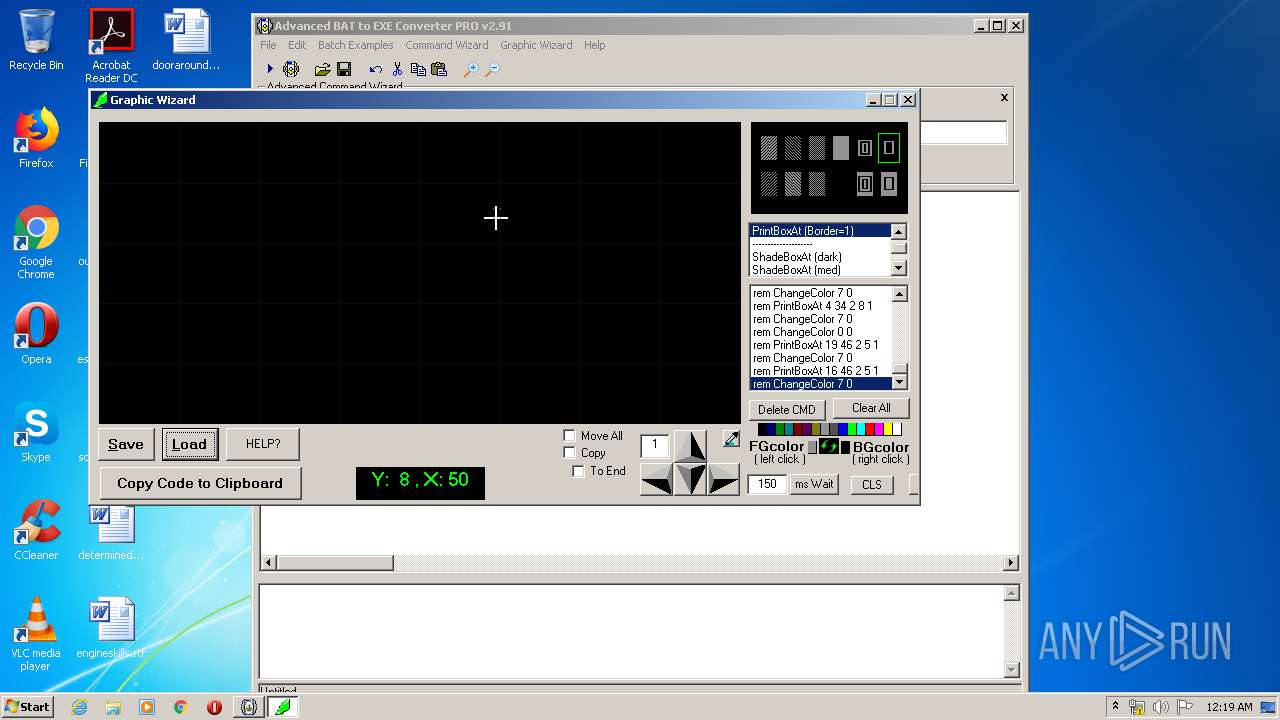
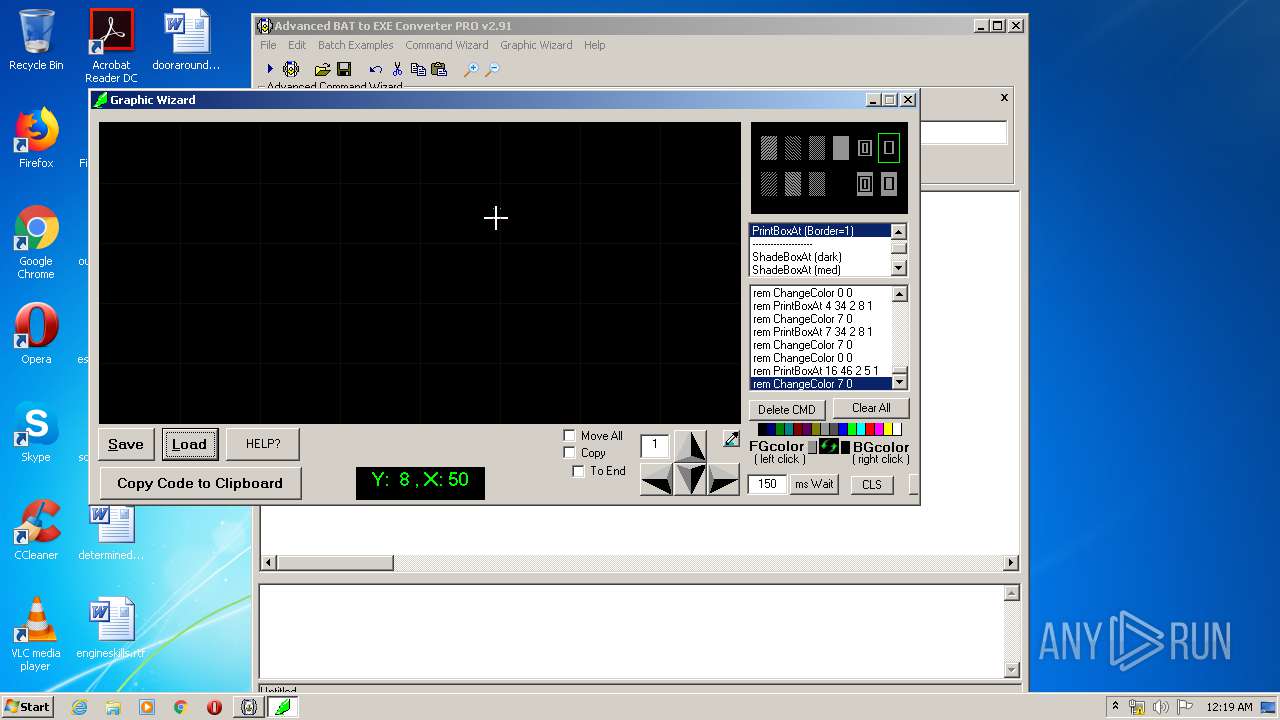
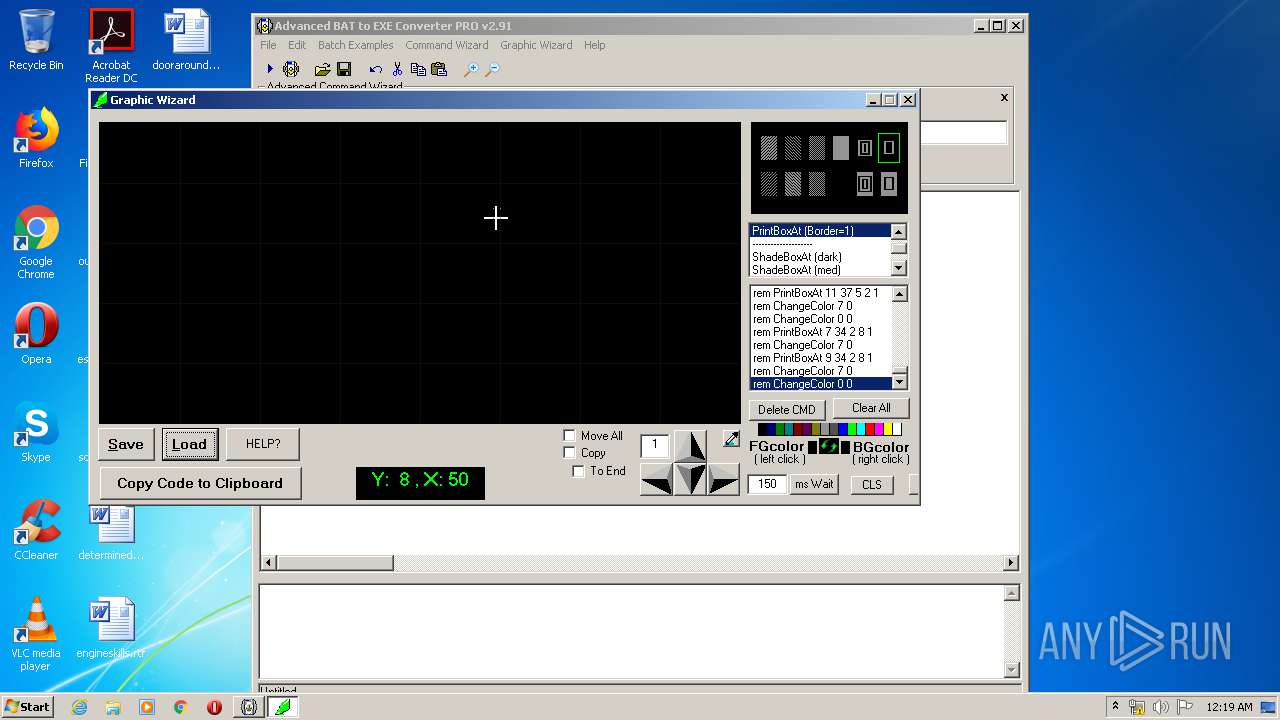
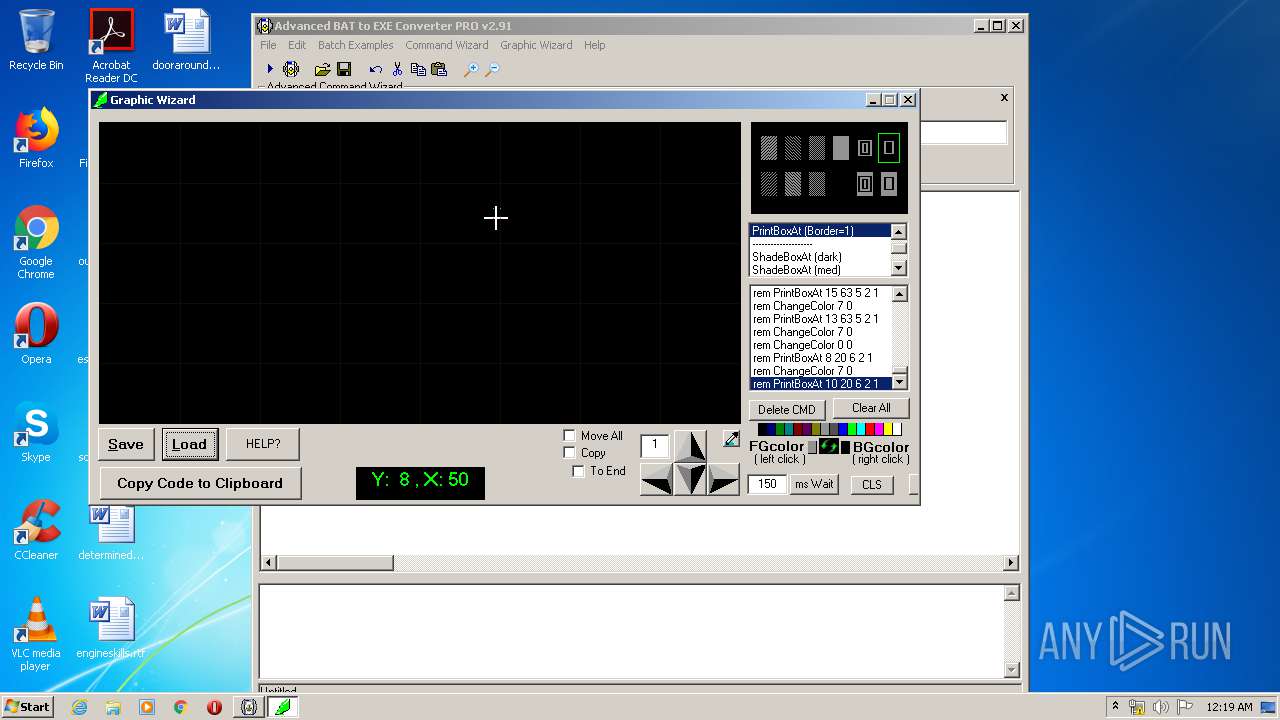
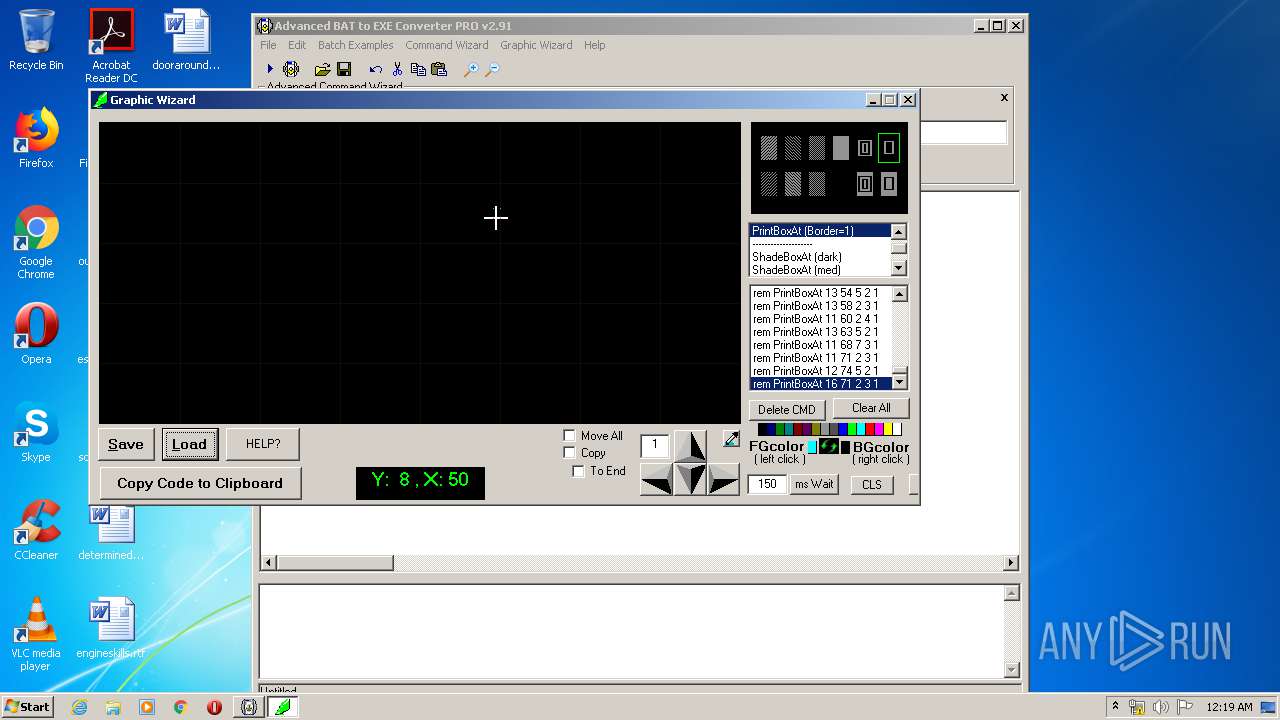
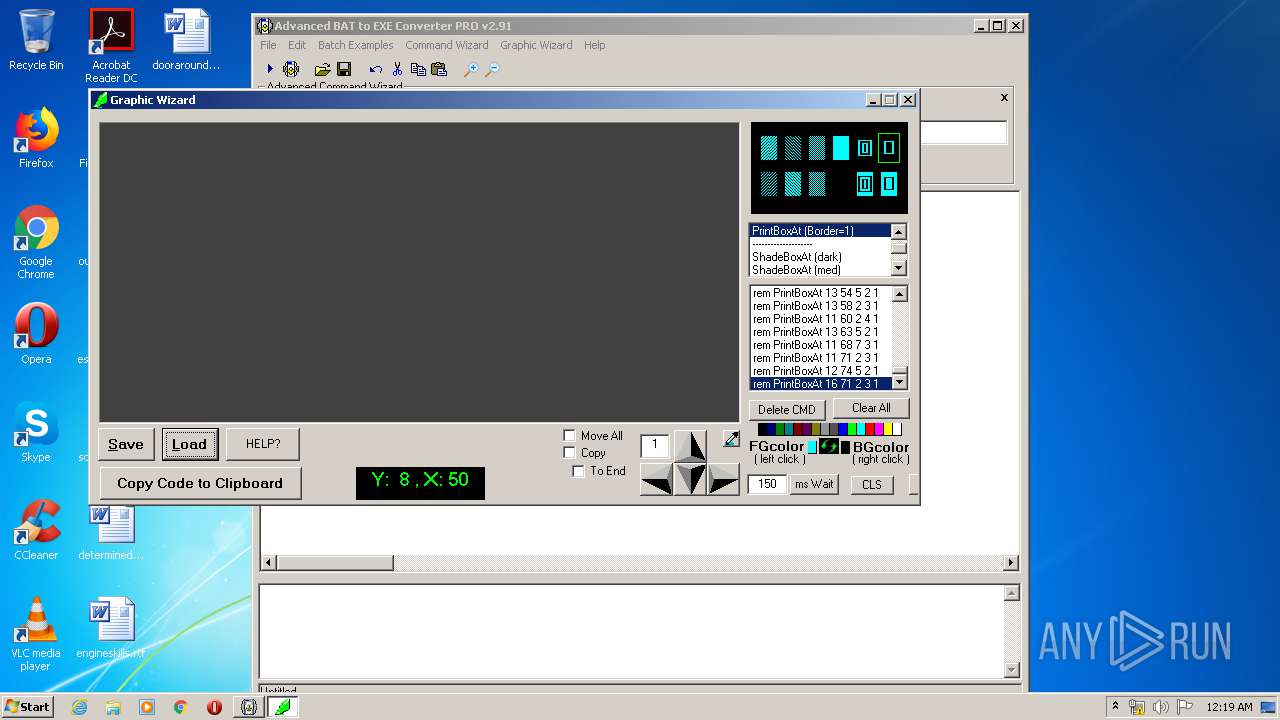
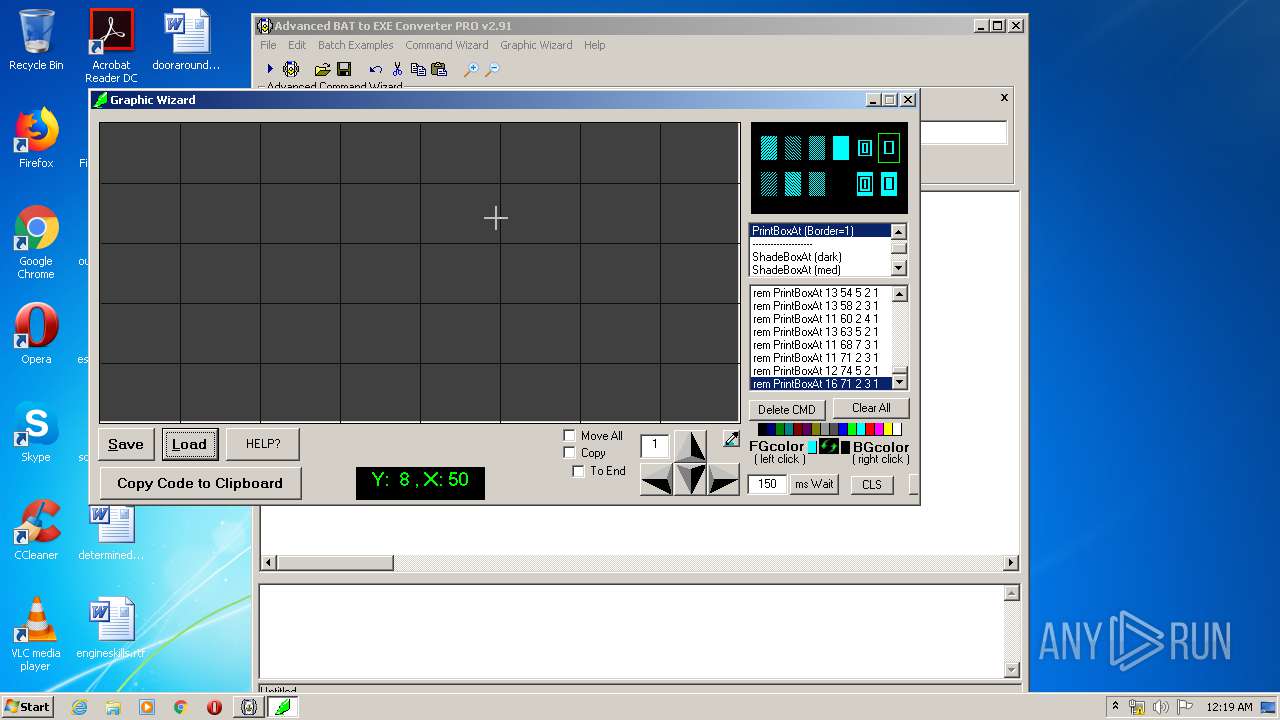
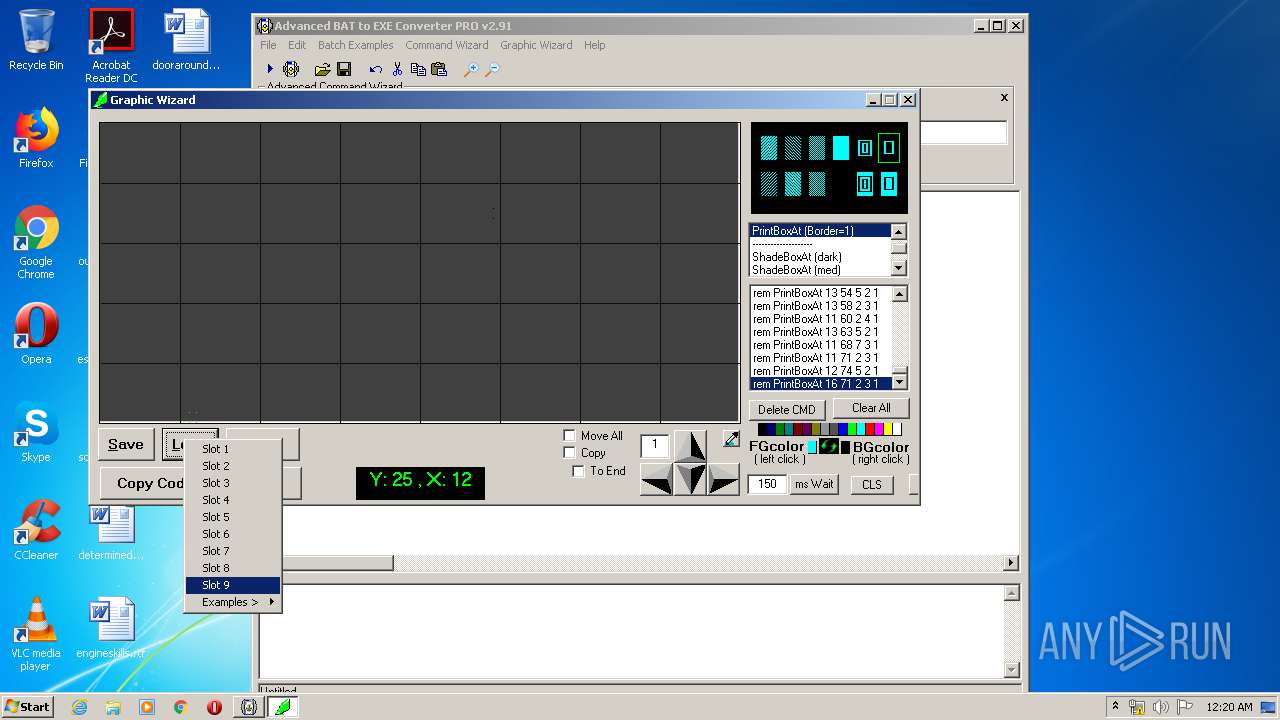
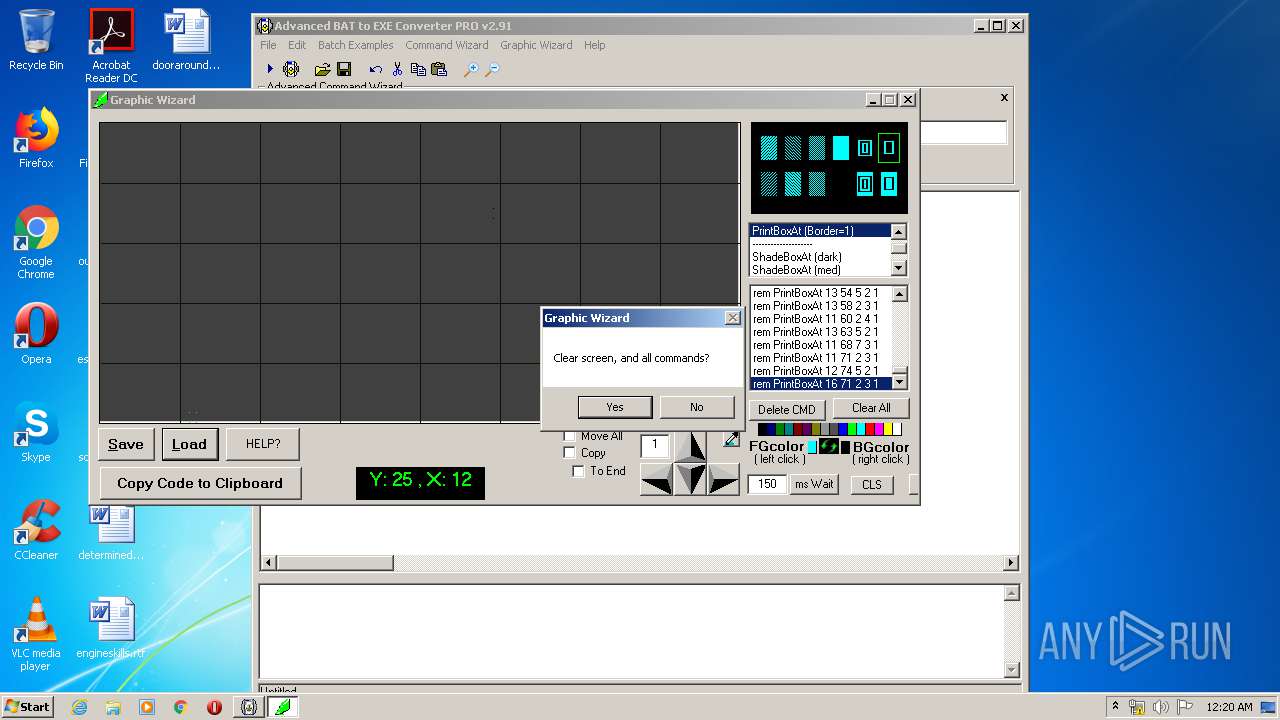
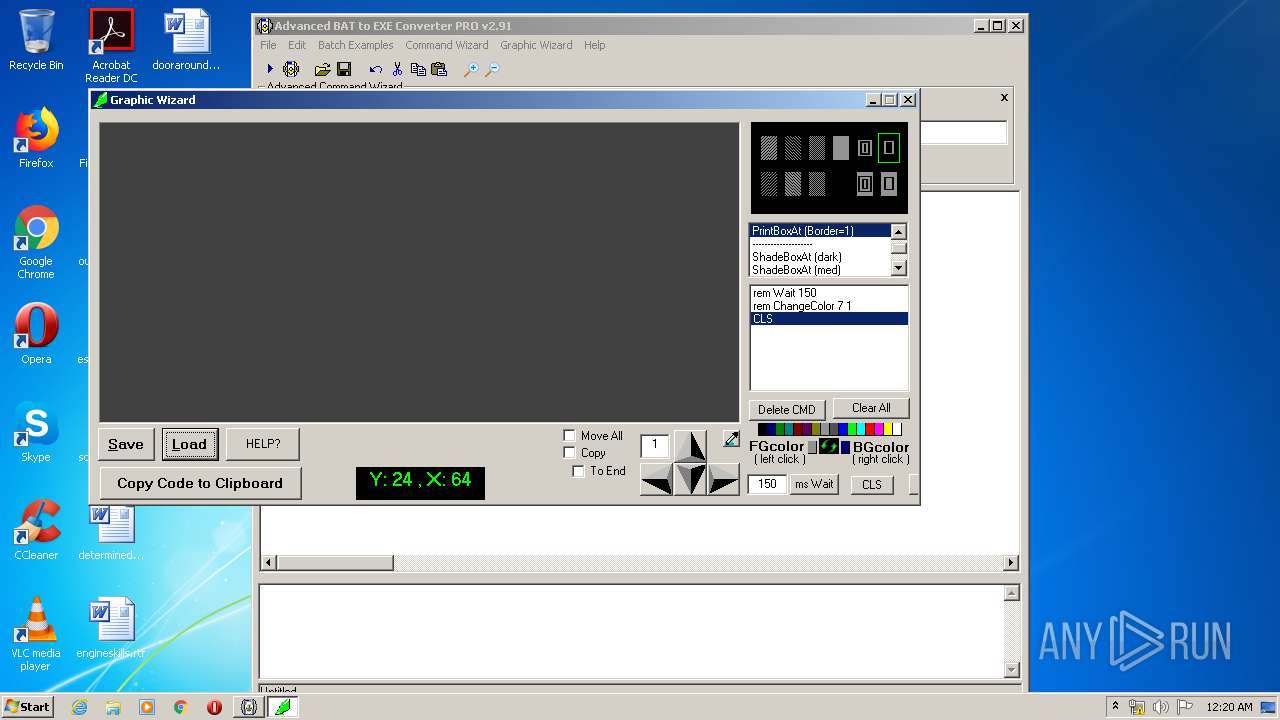
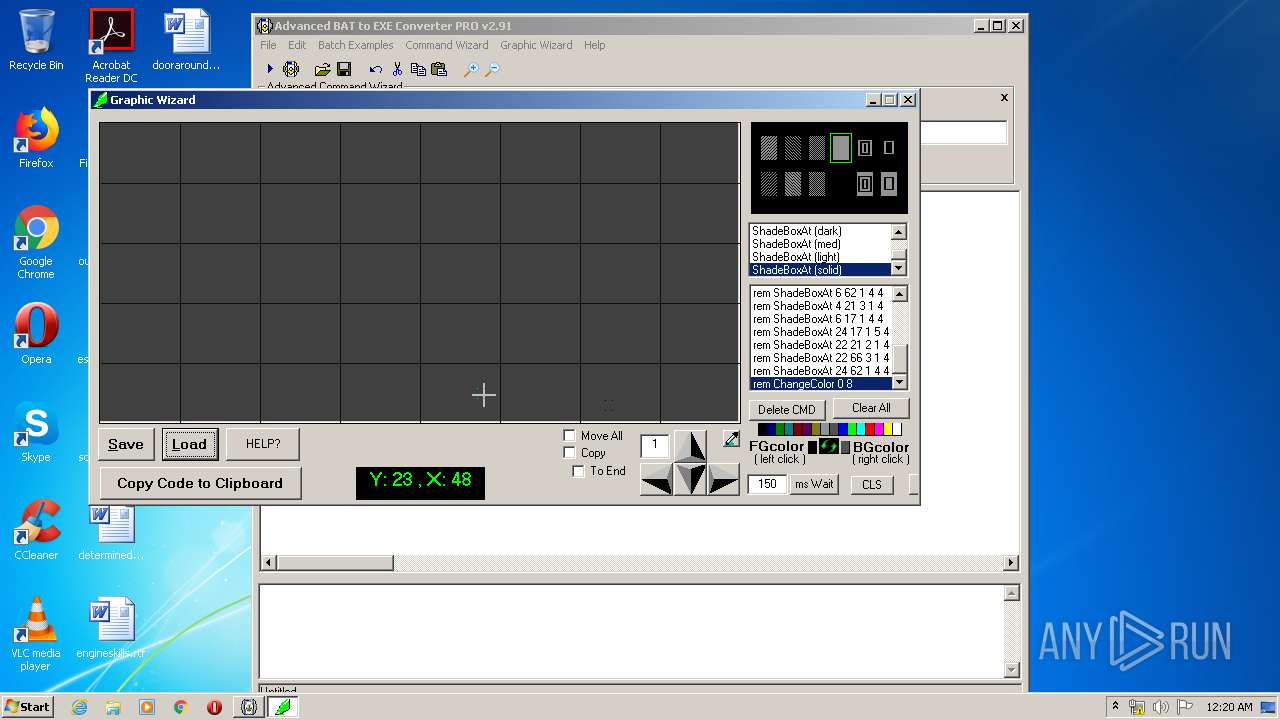
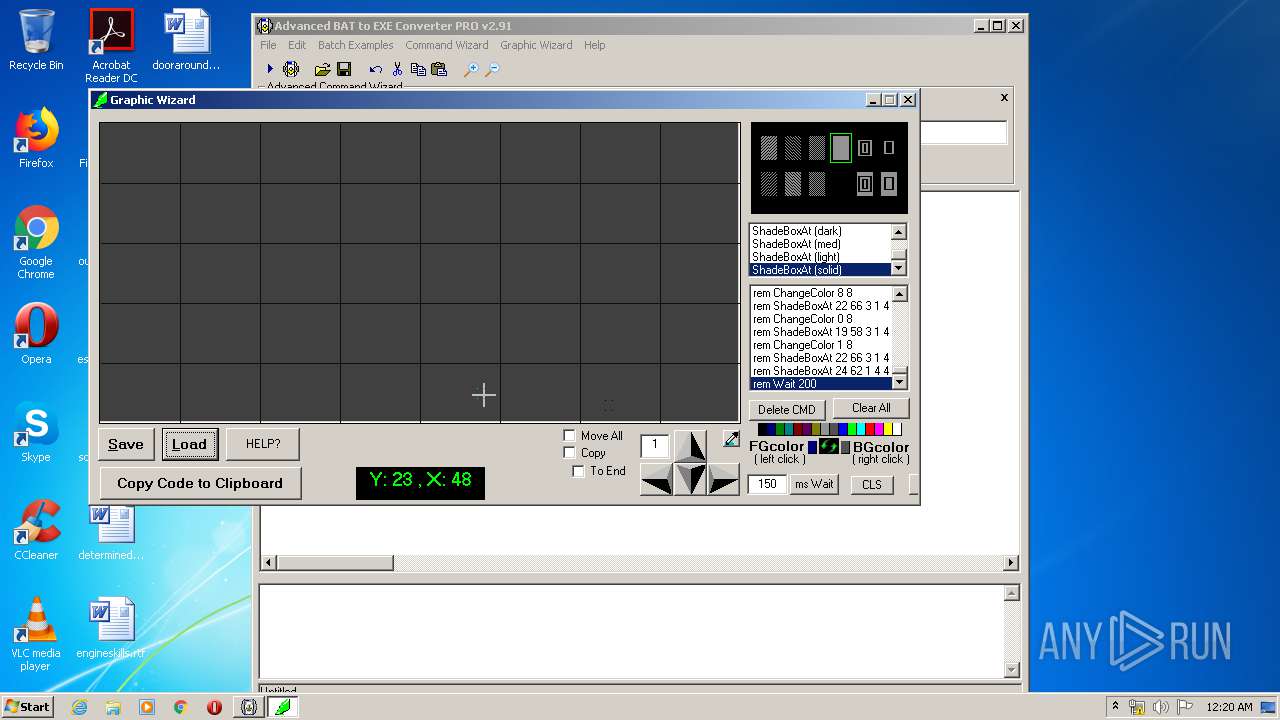
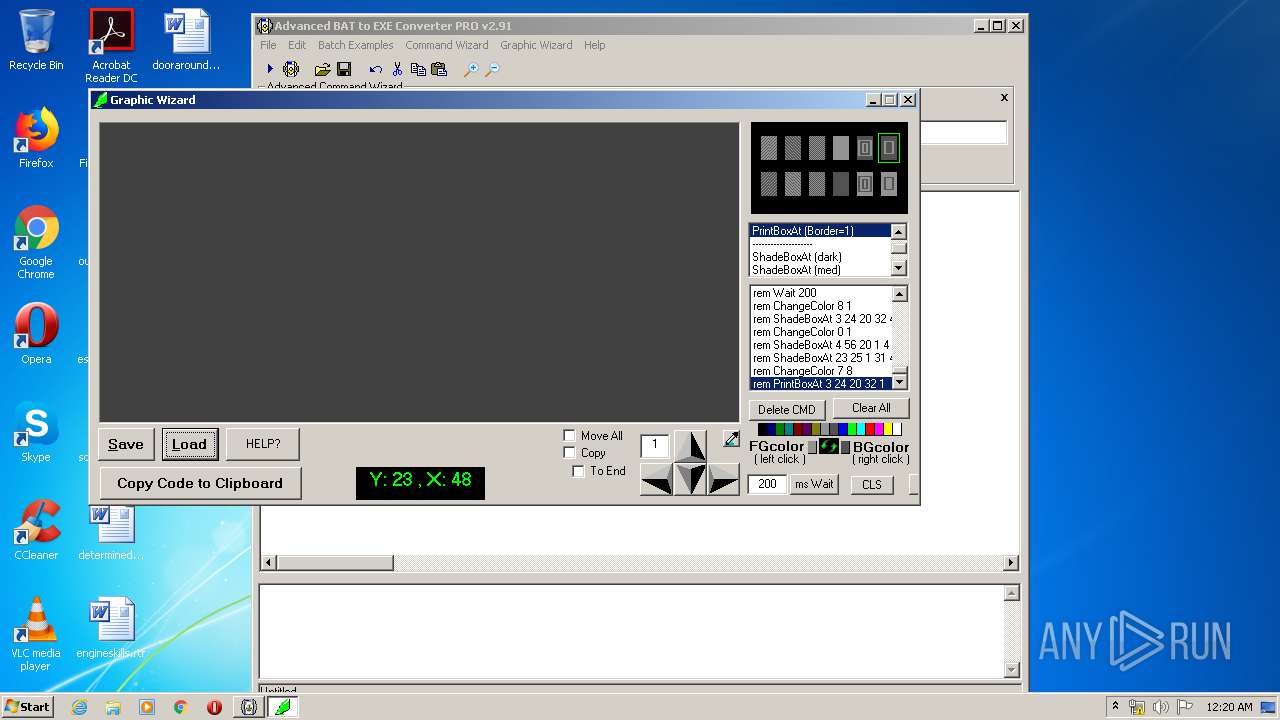
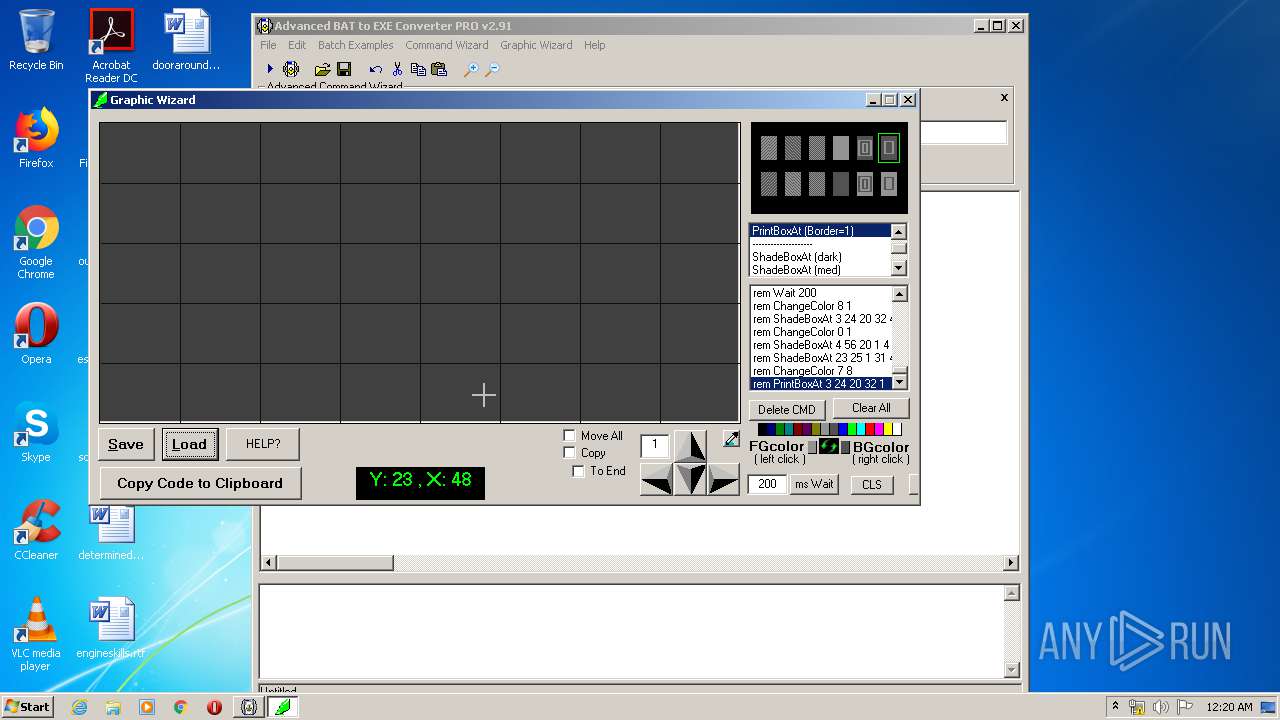
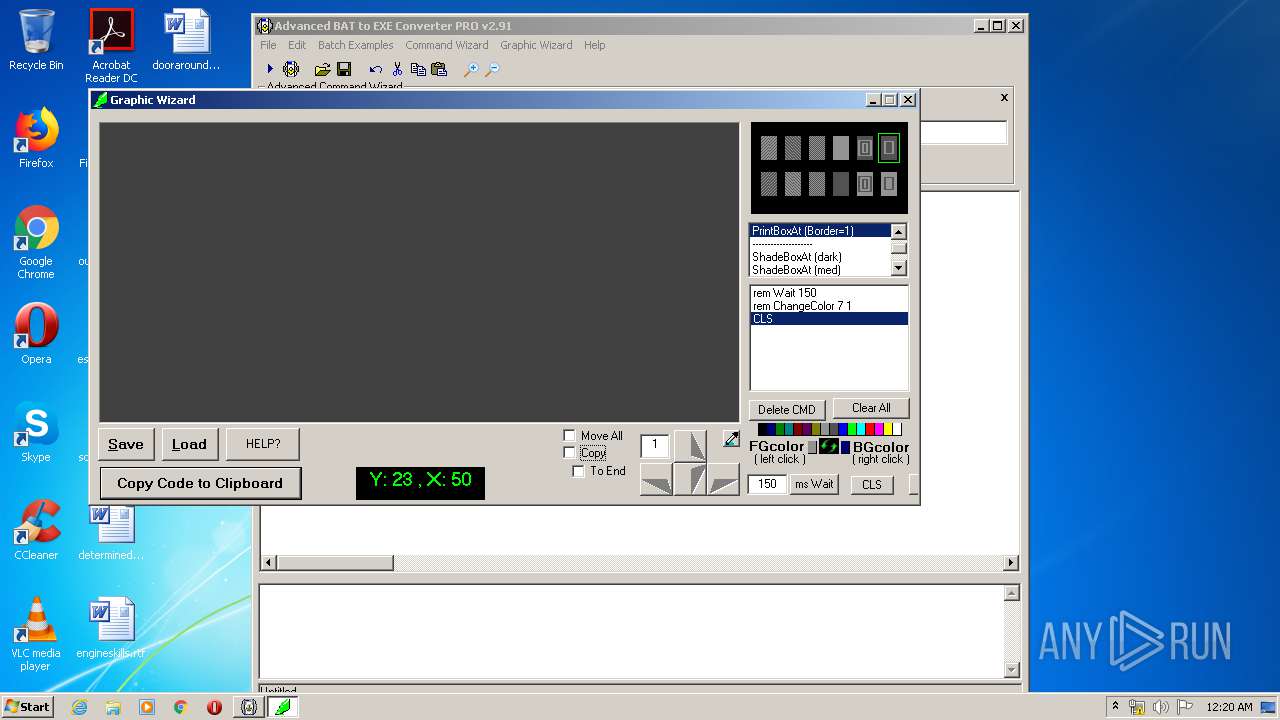
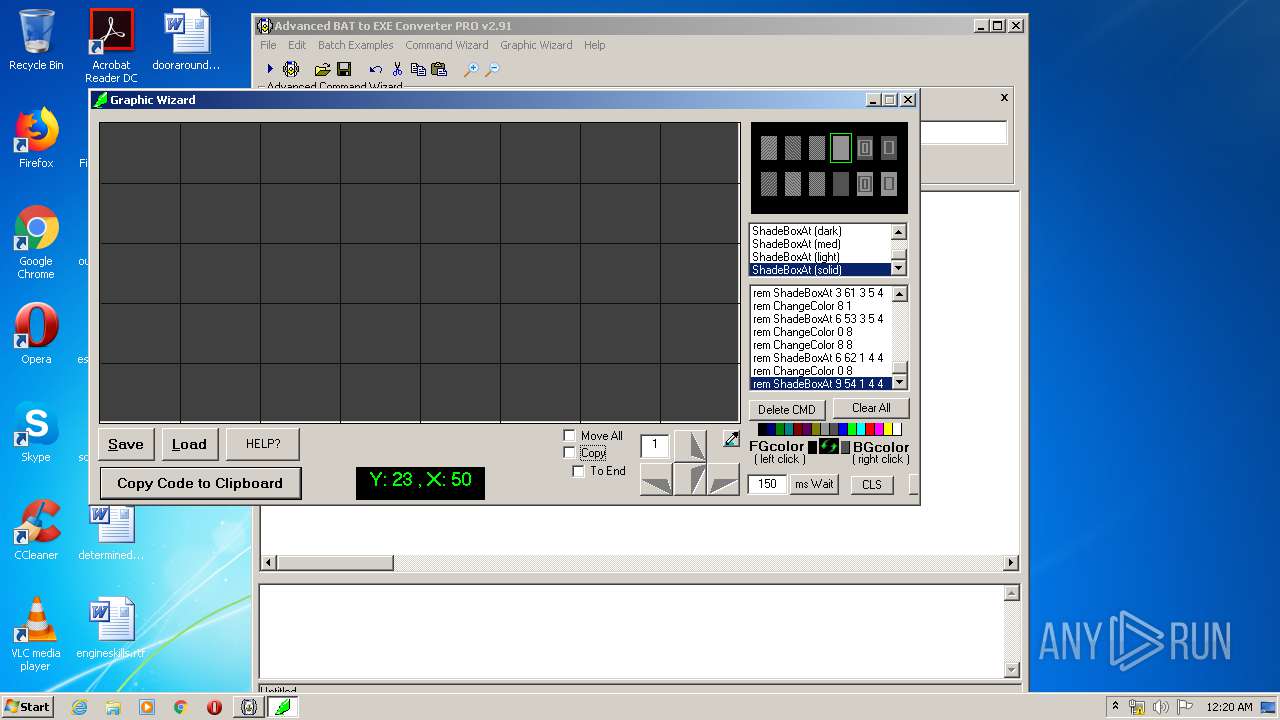
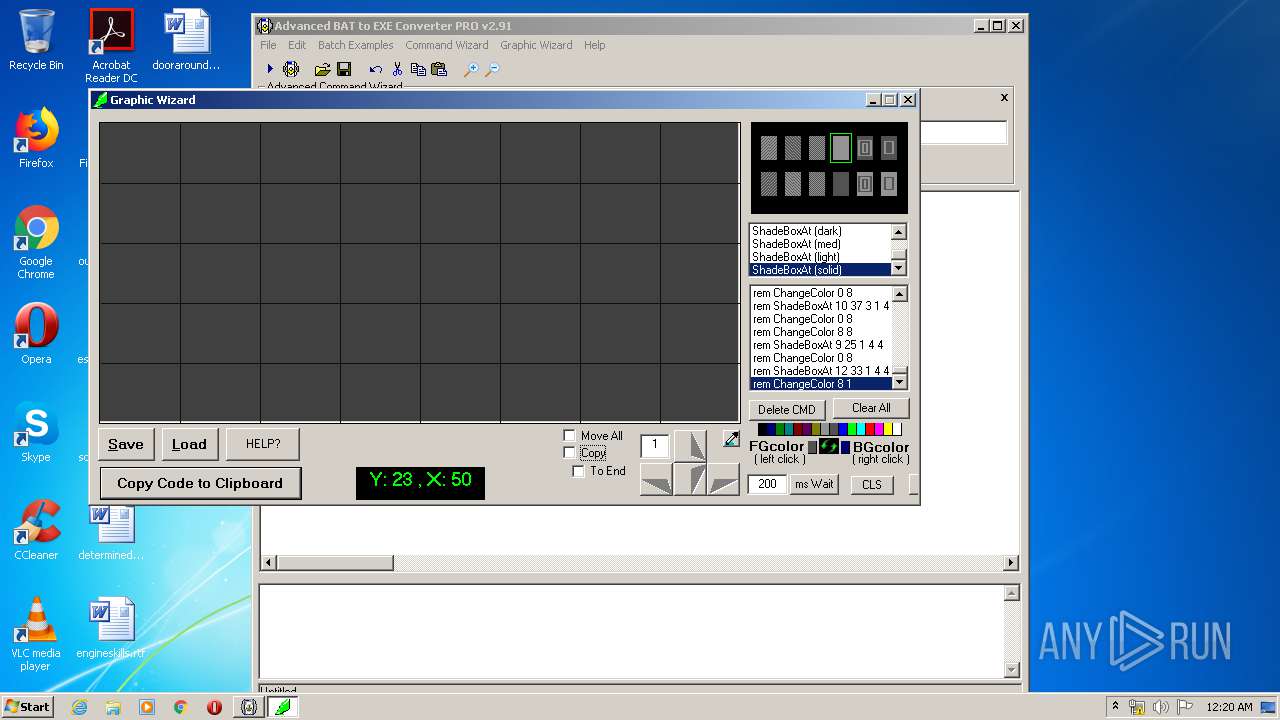
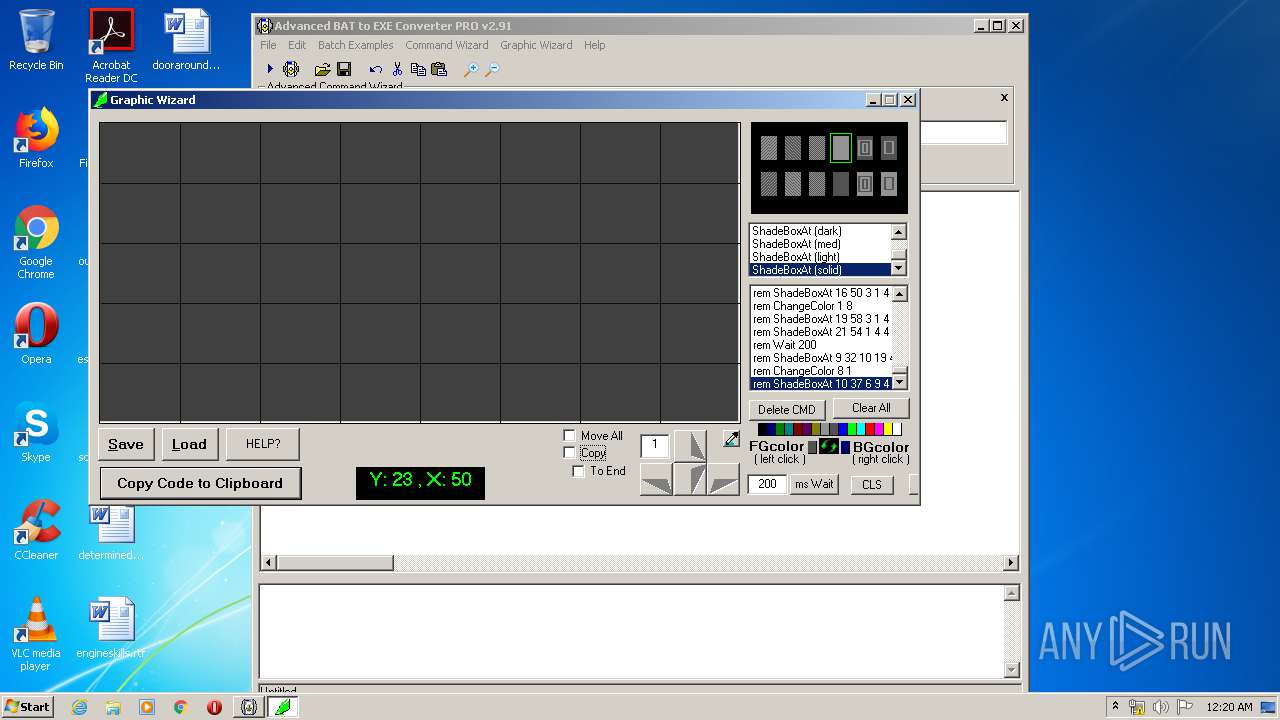
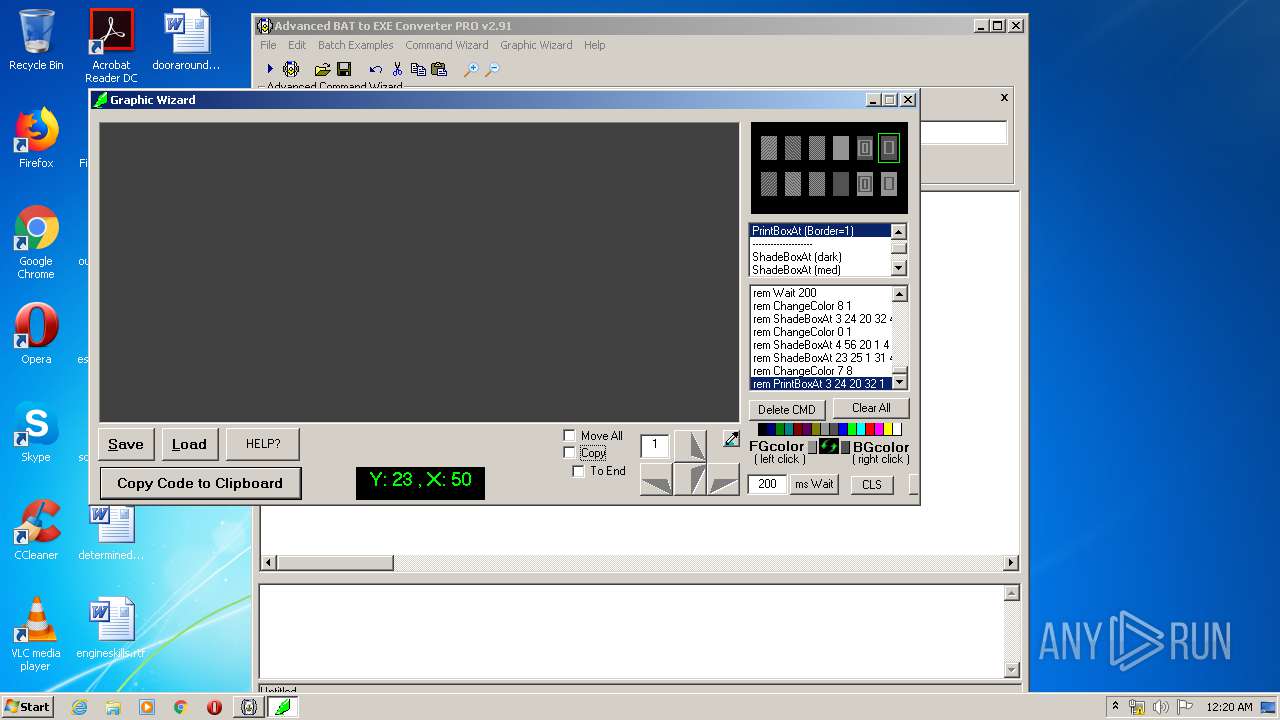
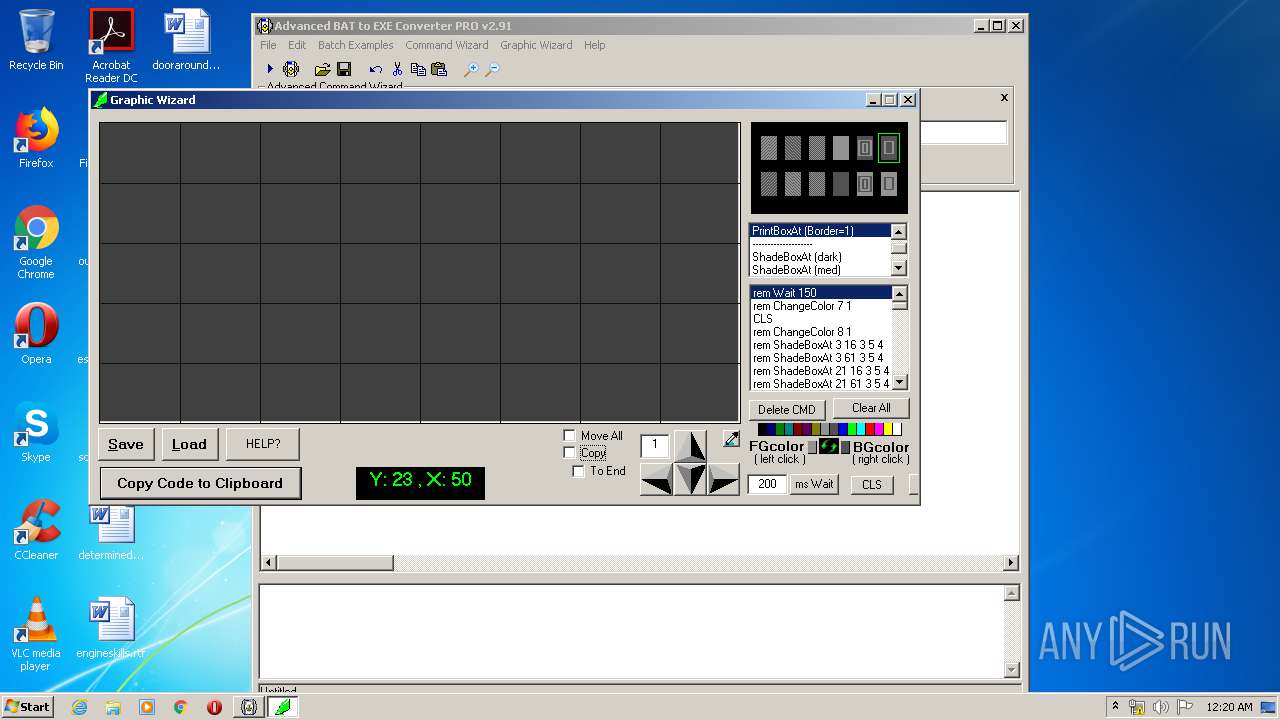
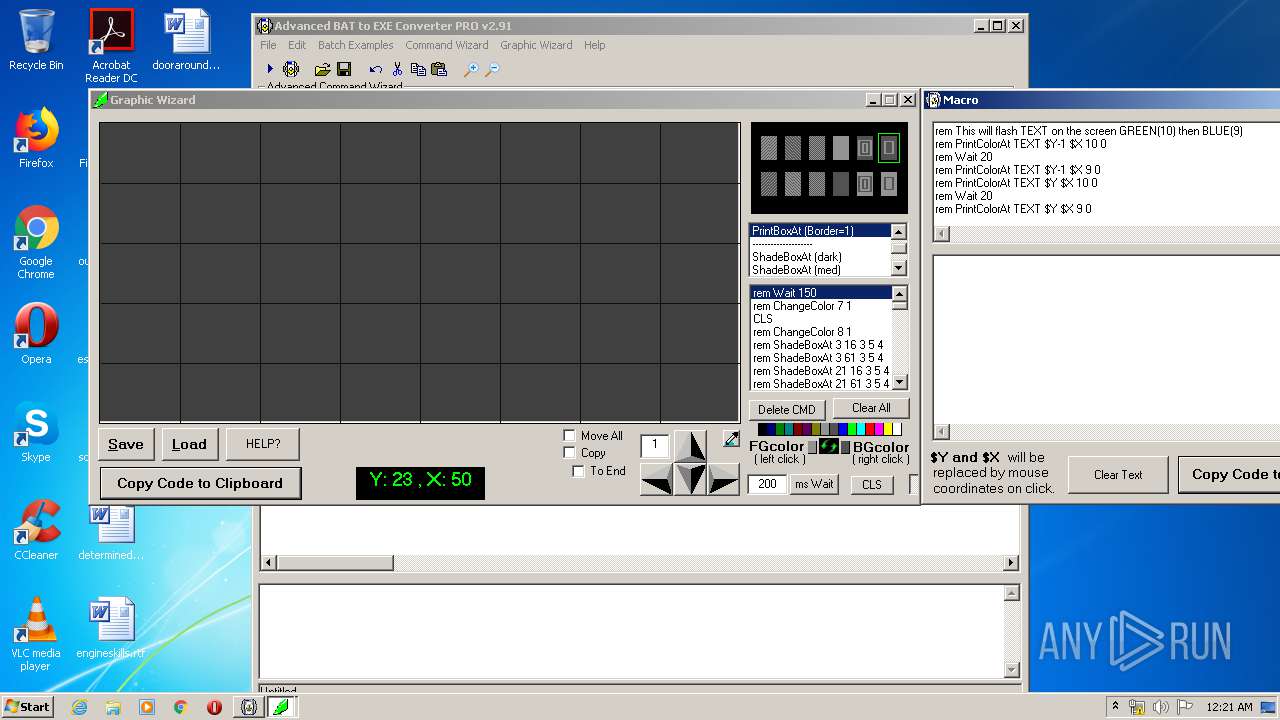
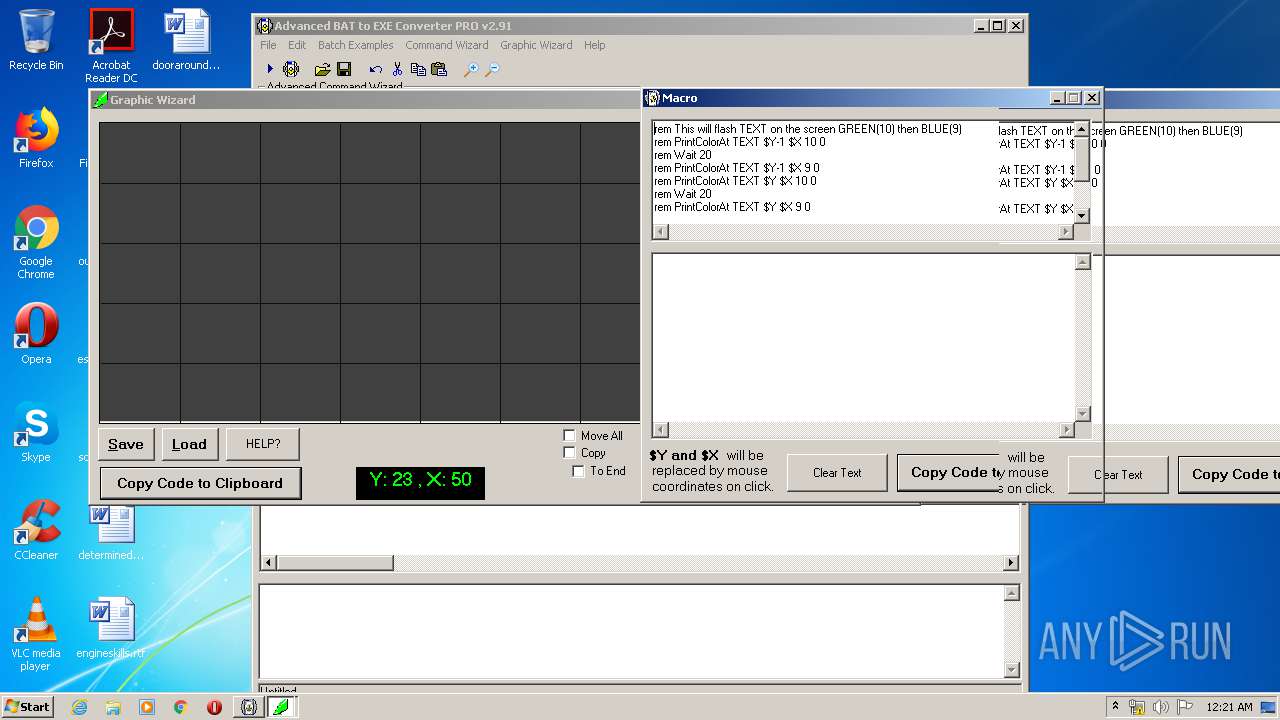
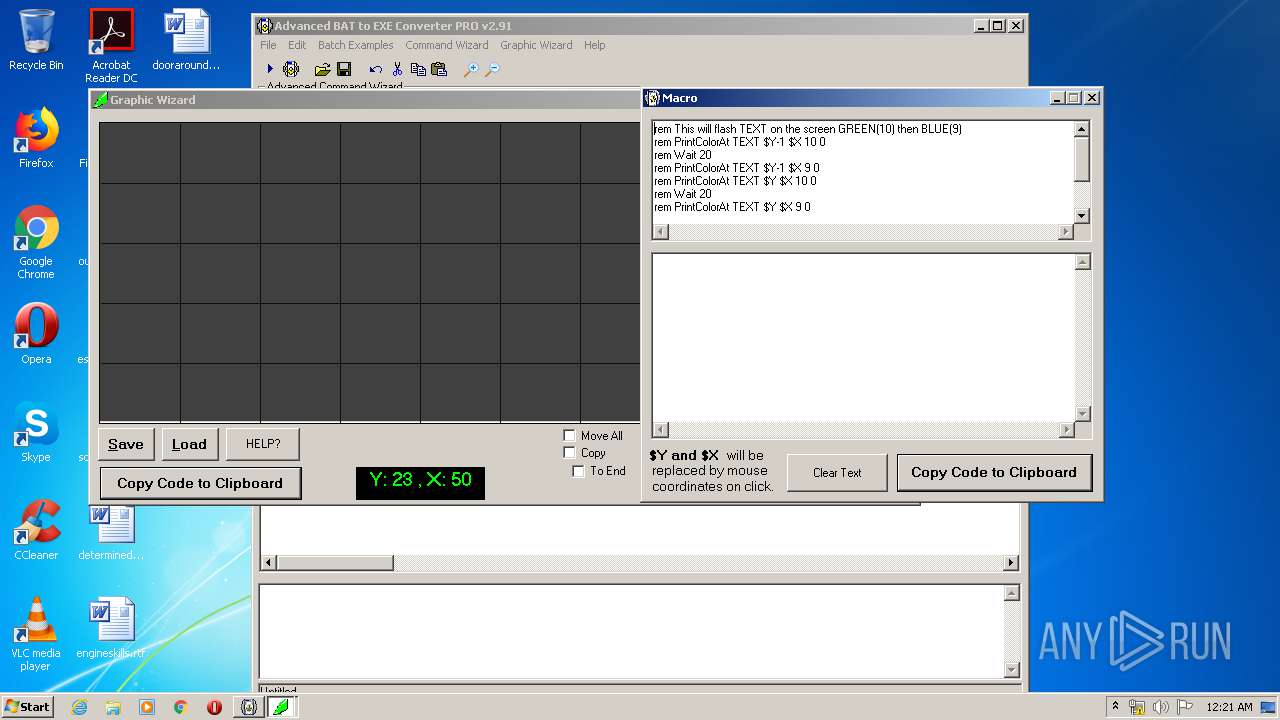
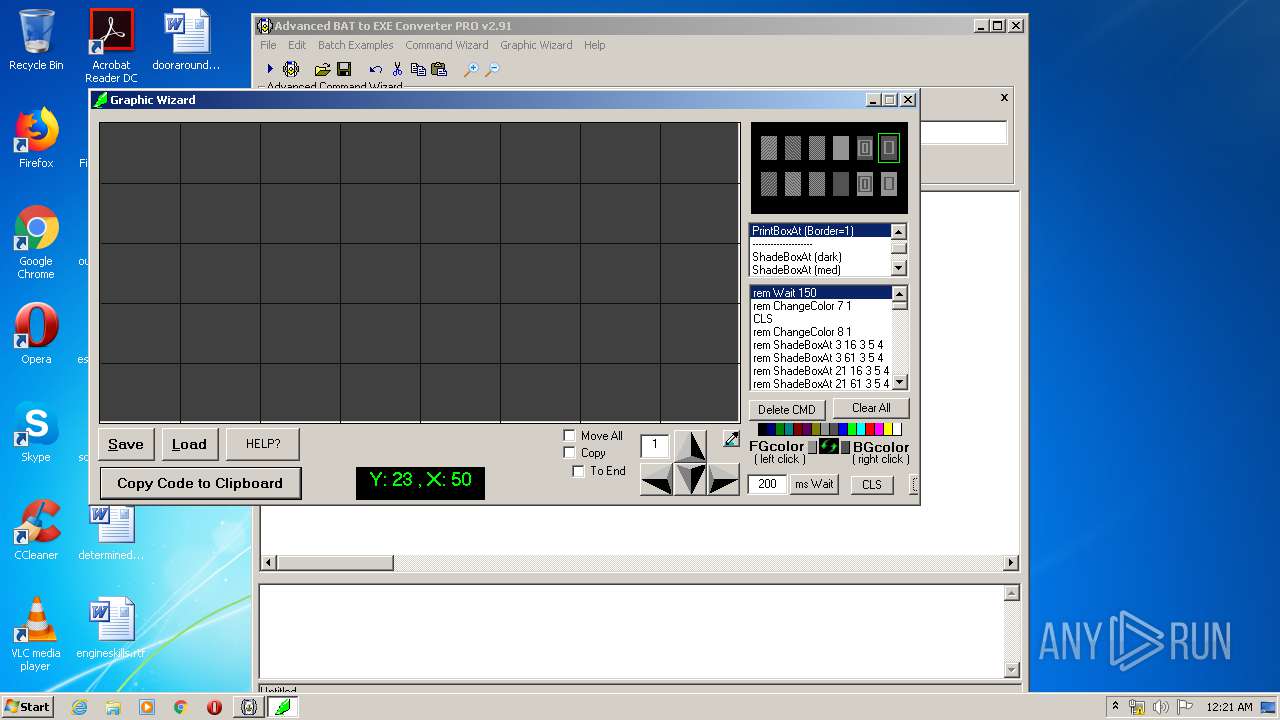
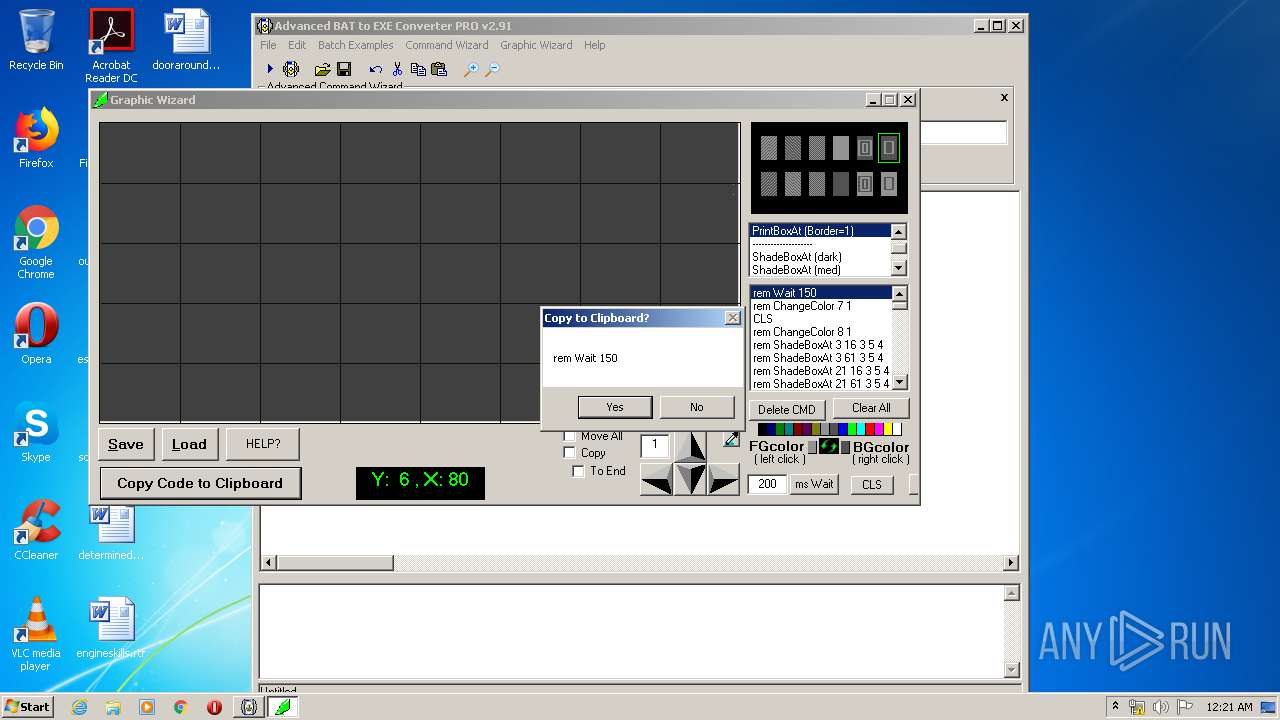
| 1504 | "C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\gewiz.exe" | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\gewiz.exe | ab2econv.exe | ||||||||||||
User: admin Company: Brandon Dargo Integrity Level: HIGH Description: Graphic Wizard Exit code: 0 Version: 1.05 Modules
| |||||||||||||||
| 1844 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | fastcmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2112 | cmd /c ""C:\Users\admin\AppData\Local\Temp\bfcwrk\do.bat" " | C:\Windows\system32\cmd.exe | — | gewiz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2192 | "C:\Users\admin\AppData\Local\Temp\bfcwrk\fastcmd.exe" "C:\Users\admin\AppData\Local\Temp\bfcwrk\gew10.fst" | C:\Users\admin\AppData\Local\Temp\bfcwrk\fastcmd.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\gewizold.exe" | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\gewizold.exe | — | ab2econv.exe | |||||||||||
User: admin Company: Brandon Dargo Integrity Level: HIGH Description: Graphical Enhancement Wizard Exit code: 0 Version: 1.02.0001 Modules
| |||||||||||||||
| 2432 | C:\Windows\system32\cmd.exe /c cls | C:\Windows\system32\cmd.exe | — | fastcmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Local\Temp\bfcwrk\fastcmd.exe" "C:\Users\admin\AppData\Local\Temp\bfcwrk\gew10.fst" | C:\Users\admin\AppData\Local\Temp\bfcwrk\fastcmd.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2704 | cmd /c ""C:\Users\admin\AppData\Local\Temp\bfcwrk\do.bat" " | C:\Windows\system32\cmd.exe | — | gewiz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2764 | "C:\Users\admin\AppData\Local\Temp\bfcwrk\fastcmd.exe" "C:\Users\admin\AppData\Local\Temp\bfcwrk\gew10.fst" | C:\Users\admin\AppData\Local\Temp\bfcwrk\fastcmd.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
837
Read events
756
Write events
77
Delete events
4
Modification events
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter PRO v2.91 |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\uninstall.exe | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter PRO v2.91 |
| Operation: | write | Name: | DisplayName |
Value: Advanced BAT to EXE Converter PRO v2.91 | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Advanced BAT to EXE Converter PRO v2.91 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\uninstall.exe | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402} |
| Operation: | write | Name: | |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402}\InprocServer32 |
| Operation: | write | Name: | |
Value: C:\Windows\system32\richtx32.ocx | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\CLSID\{3B7C8860-D78F-101B-B9B5-04021C009402}\InprocServer32 |
| Operation: | write | Name: | ThreadingModel |
Value: Apartment | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl |
| Operation: | write | Name: | |
Value: Microsoft Rich Textbox Control 6.0 (SP6) | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl\CLSID |
| Operation: | write | Name: | |
Value: {3B7C8860-D78F-101B-B9B5-04021C009402} | |||
| (PID) Process: | (3284) advbattoexepro.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\RICHTEXT.RichtextCtrl\CurVer |
| Operation: | write | Name: | |
Value: RICHTEXT.RichtextCtrl.1 | |||
Executable files
22
Suspicious files
1
Text files
44
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex15.bat | text | |
MD5:35799D0D8A5FBB856A91EF6C00674DC5 | SHA256:2142548213CFC2696260B0DF630DE2F49BDC4D4D1C18D47635B1B07EB5D761A3 | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex4.bat | text | |
MD5:61FB1B1E92413CF5FBCC9745F05B371E | SHA256:F430757EE91792681C832AB05A5F79AD32E7A9389ACDA7226BD41C8CF5A1AFF3 | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex2.bat | text | |
MD5:F1B2105133C39884567D416D8B30D3B6 | SHA256:F3A44D7C5D903D5915CDC99980AEEDF7F44C5158B5F220B4EA76ABF9088721E1 | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex16.bat | text | |
MD5:0A432204880D3B2F962A31E1038452A0 | SHA256:01ADC122AF82DA3402AAA26924B7EDA5BC7D69916987427128B960CC45E7C51F | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex13.bat | text | |
MD5:08B4A153B6BE6F70A9F0B798099EDF8A | SHA256:10E136DB8BD05B97074ADA54C425E7EC2C7698EE1971CCFB42716B9D550F4CA4 | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex11.bat | text | |
MD5:DE52187D28EB0AC874B13FBA1768BCD3 | SHA256:5EE2AF2C1AF1A2CE719FB13B9C172367E3FF652BCDBEB0E53B9FD3018FAAF9FB | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex5.bat | text | |
MD5:563B6793AE8BDD9AD9F345C5E4BF8AA0 | SHA256:A909CB43BB48EBE363B25B070116A351438267CB014325DC505BAD2E332A24FC | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex3.bat | text | |
MD5:A4615F826E2D1621F2EEE3F2B8BC2B32 | SHA256:D4A0B446785C3E07ECAAEFB6B437E4B9FC762A43EDE531441D8E12A85F75CDBE | |||
| 3284 | advbattoexepro.exe | C:\Users\admin\AppData\Local\Temp\gentee00\setup_temp.gea | bs | |
MD5:D46A77ED65AAD700AA12EE41078065CA | SHA256:DD42618C53181ED9B09C66B8D4297C14AC4F645BF66226EB934809BE17288088 | |||
| 3284 | advbattoexepro.exe | C:\Program Files\Advanced BAT to EXE Converter PRO v2.91\ab2econv291pro\advex7.bat | text | |
MD5:1A36090F88917D755C2F41070D309F46 | SHA256:61F5B7062340C85A2A66E3FFCB50C466AF415B5452DD5EB2B495A619A41FBA00 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report