| File name: | uv-installer.ps1 |
| Full analysis: | https://app.any.run/tasks/6da7f18a-c1da-41eb-aa57-35f7a7560fcc |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2025, 11:33:11 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (367) |
| MD5: | 0E2AF489D1ECBEB4F860D218FC47CAAA |
| SHA1: | 329CC4747AF9AC0834C96158F669994BCE064DCF |
| SHA256: | 2BBC7651618AD8F157C5E5D1DD32E1B3E2BF8AF1859C244596A635DB963BD9C0 |
| SSDEEP: | 384:07sanH74vczieoWPJdTRBfMdP4h/b9GiQY:07syH7icloGHVBfMdP4h/b9GiQY |
MALICIOUS
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 4516)
Bypass execution policy to execute commands
- powershell.exe (PID: 4516)
Script downloads file (POWERSHELL)
- powershell.exe (PID: 4516)
SUSPICIOUS
Gets file extension (POWERSHELL)
- powershell.exe (PID: 4516)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 4516)
Executable content was dropped or overwritten
- powershell.exe (PID: 4516)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 4516)
INFO
Disables trace logs
- powershell.exe (PID: 4516)
Checks proxy server information
- powershell.exe (PID: 4516)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 4516)
Uses string replace method (POWERSHELL)
- powershell.exe (PID: 4516)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4516)
Manual execution by a user
- uvx.exe (PID: 2008)
Checks supported languages
- uvx.exe (PID: 2008)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
123
Monitored processes
4
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2008 | "C:\Users\admin\Desktop\uvx.exe" | C:\Users\admin\Desktop\uvx.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 2 Modules
| |||||||||||||||
| 2996 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | uvx.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4516 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -ep bypass C:\Users\admin\Desktop\uv-installer.ps1 | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 804
Read events
5 801
Write events
2
Delete events
1
Modification events
| (PID) Process: | (4516) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | Path |
Value: C:\Users\admin\.local\bin;%USERPROFILE%\AppData\Local\Microsoft\WindowsApps | |||
| (PID) Process: | (4516) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | write | Name: | cargo-dist-95614123-5ef0-4298-81c5-27169a106e04 |
Value: cargo-dist-dummy | |||
| (PID) Process: | (4516) powershell.exe | Key: | HKEY_CURRENT_USER\Environment |
| Operation: | delete value | Name: | cargo-dist-95614123-5ef0-4298-81c5-27169a106e04 |
Value: cargo-dist-dummy | |||
Executable files
2
Suspicious files
7
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
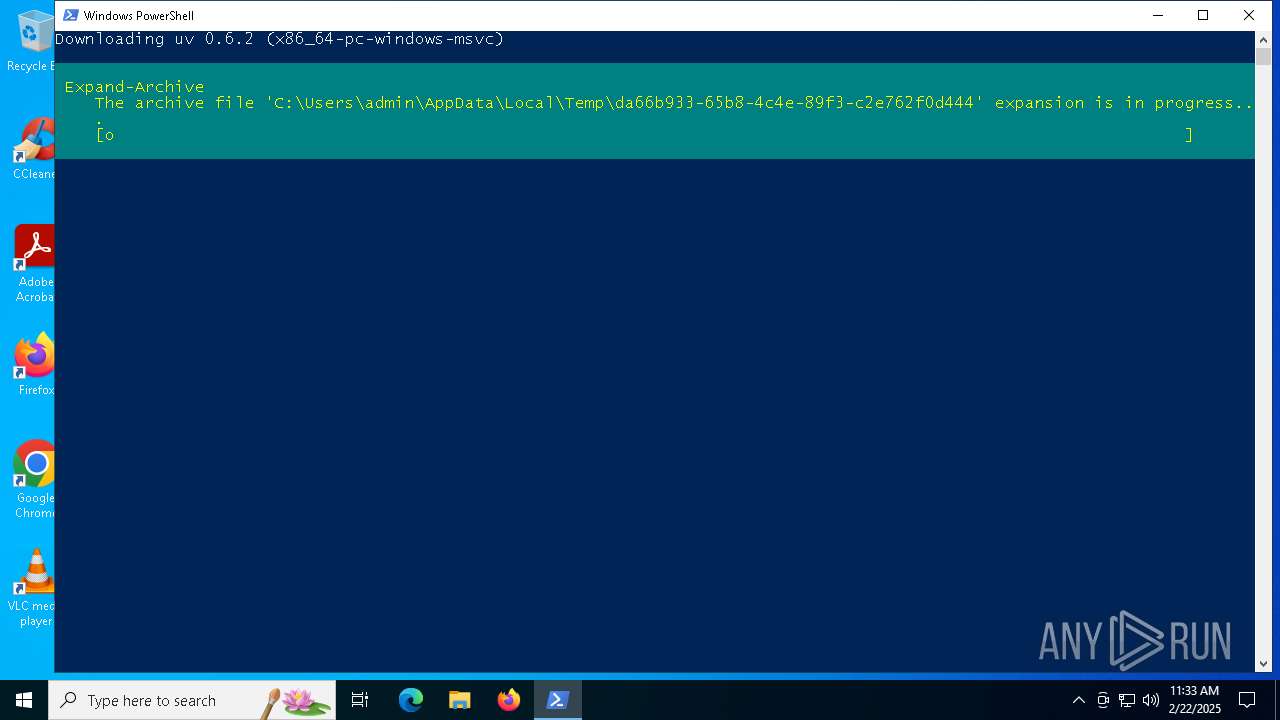
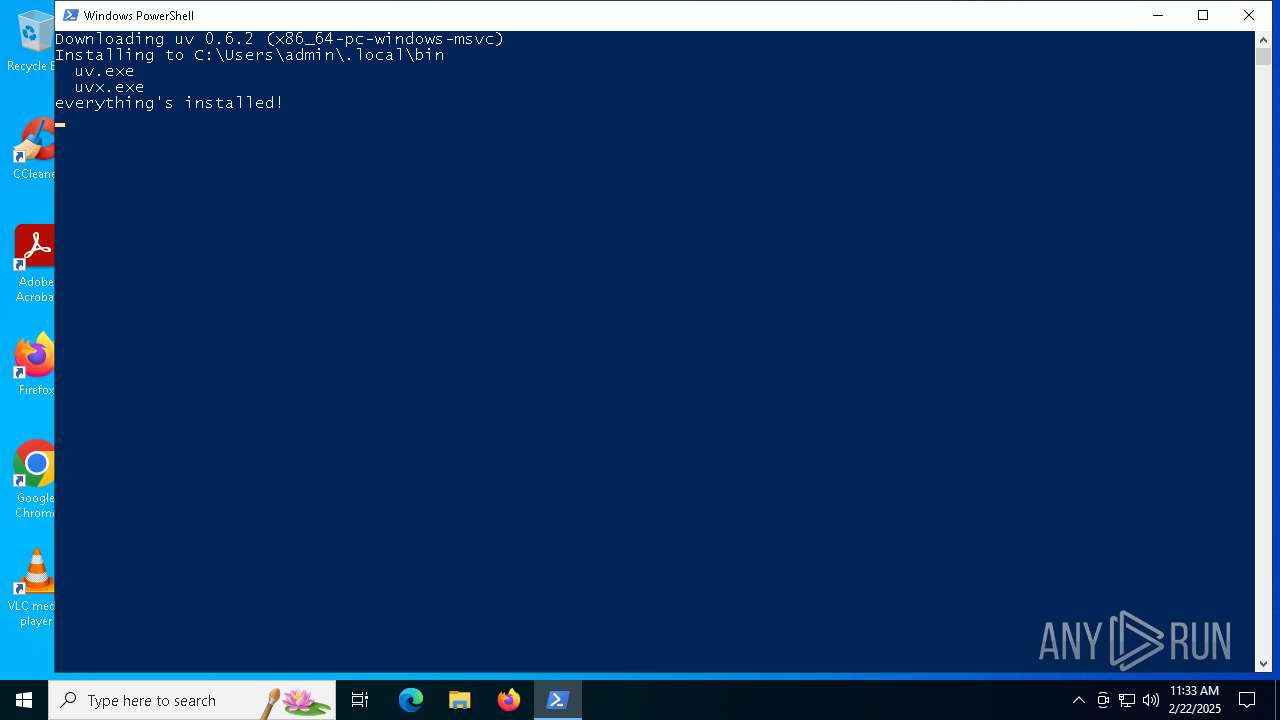
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\da66b933-65b8-4c4e-89f3-c2e762f0d444\uv.exe | — | |
MD5:— | SHA256:— | |||
| 4516 | powershell.exe | C:\Users\admin\.local\bin\uv.exe | — | |
MD5:— | SHA256:— | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\uv\uv-receipt.json | binary | |
MD5:080C54A4CCE85142E9DA5E228CFA5577 | SHA256:9A1106062062B88343F8BE2B9DCB5DDC28D947B0E0D5693BAEE206E3A417E201 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms~RF1360b1.TMP | binary | |
MD5:D040F64E9E7A2BB91ABCA5613424598E | SHA256:D04E0A6940609BD6F3B561B0F6027F5CA4E8C5CF0FB0D0874B380A0374A8D670 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0TSPMBS7Y5GUWBQ802VH.temp | binary | |
MD5:9EC906BEA4BF5D19FC4DCE264E9730F4 | SHA256:D8FBB89169D6F8892900CAF2AD239A1670379948F565C0AB7F39702691E2A171 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\da66b933-65b8-4c4e-89f3-c2e762f0d444\uv.zip | compressed | |
MD5:25CCD1707AB60B14E27FFE6F7FFECFA8 | SHA256:5F33C3CC5C183775CC51B3E661A0D2CE31142D32A50406A67C7AD0321FC841D9 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_04aljzap.vkv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:9EC906BEA4BF5D19FC4DCE264E9730F4 | SHA256:D8FBB89169D6F8892900CAF2AD239A1670379948F565C0AB7F39702691E2A171 | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\ModuleAnalysisCache | binary | |
MD5:C904B83F3EB6B36C24B175843EAE2F18 | SHA256:AE9C3B418FC314078AEA3B8FE77670BDBD72E127D1DAE886D031A73C2074B64F | |||
| 4516 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_32plx030.nyj.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
24
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2632 | svchost.exe | GET | 200 | 23.53.40.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1576 | RUXIMICS.exe | GET | 200 | 23.53.40.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.53.40.170:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1576 | RUXIMICS.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2632 | svchost.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 302 | 140.82.121.3:443 | https://github.com/astral-sh/uv/releases/download/0.6.2/uv-x86_64-pc-windows-msvc.zip | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2632 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1576 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.110.131:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1576 | RUXIMICS.exe | 23.53.40.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2632 | svchost.exe | 23.53.40.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.53.40.170:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1576 | RUXIMICS.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET HUNTING Terse Request for Zip File (GET) |