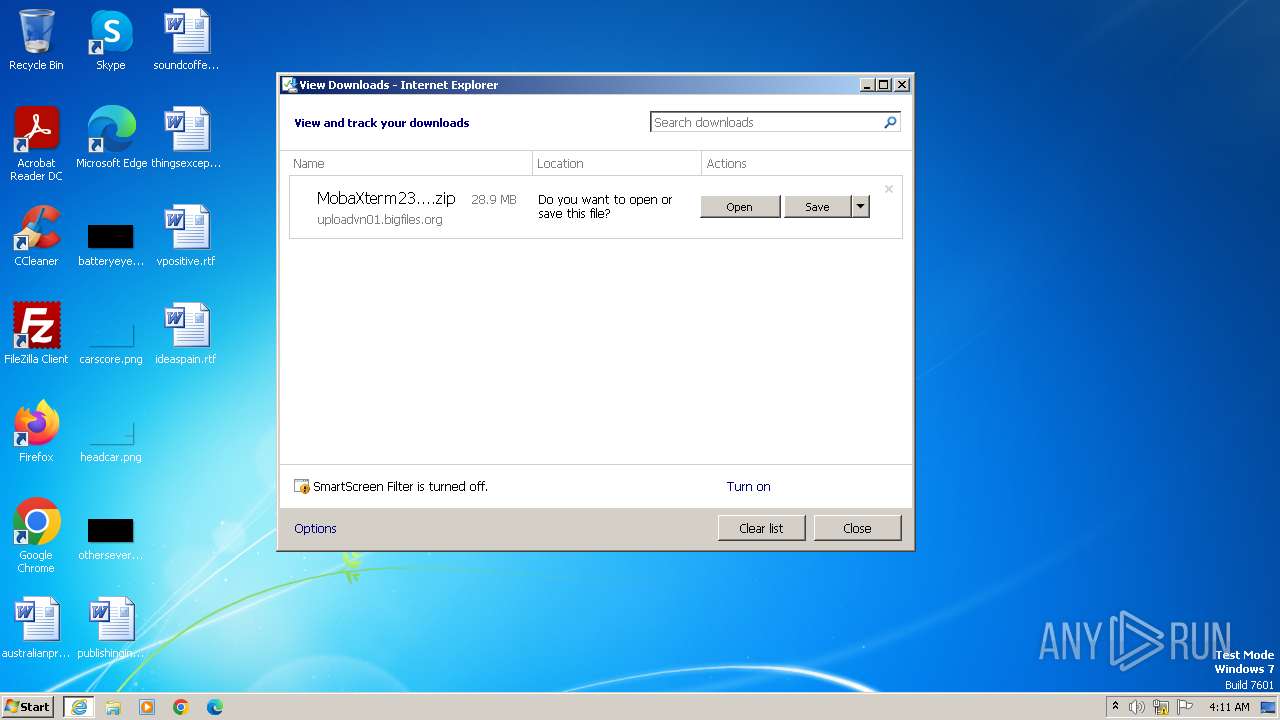
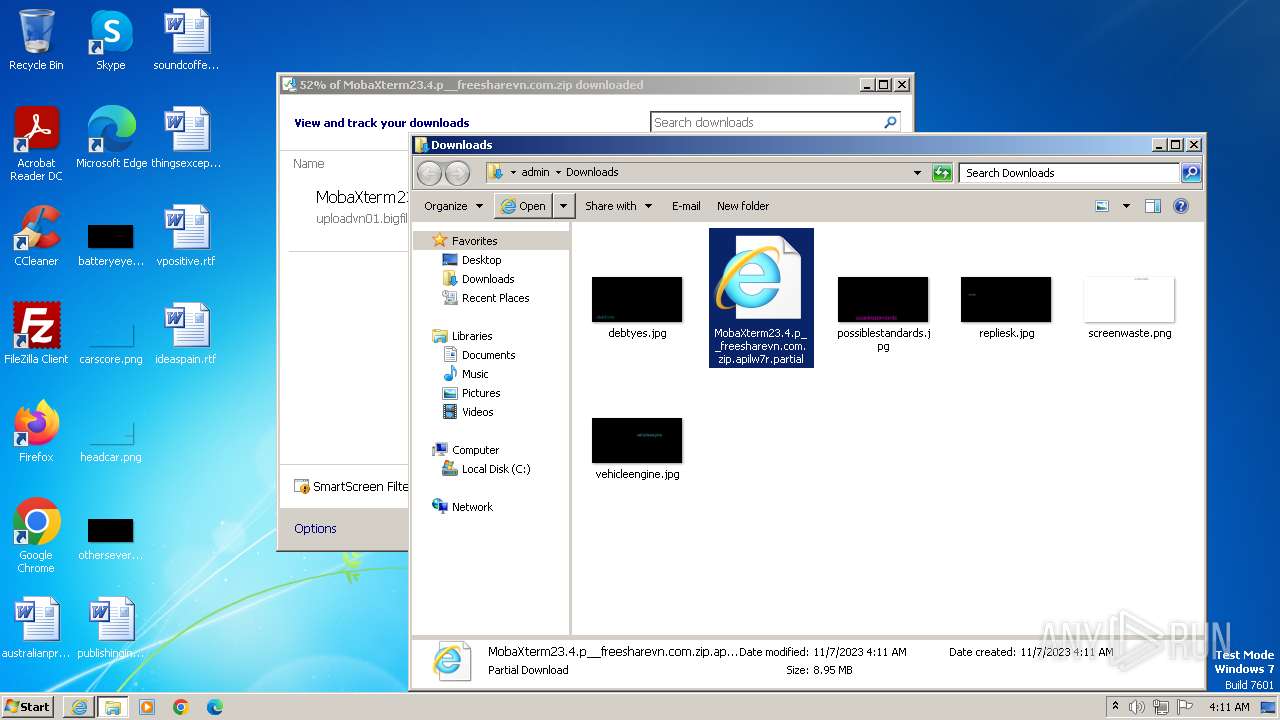
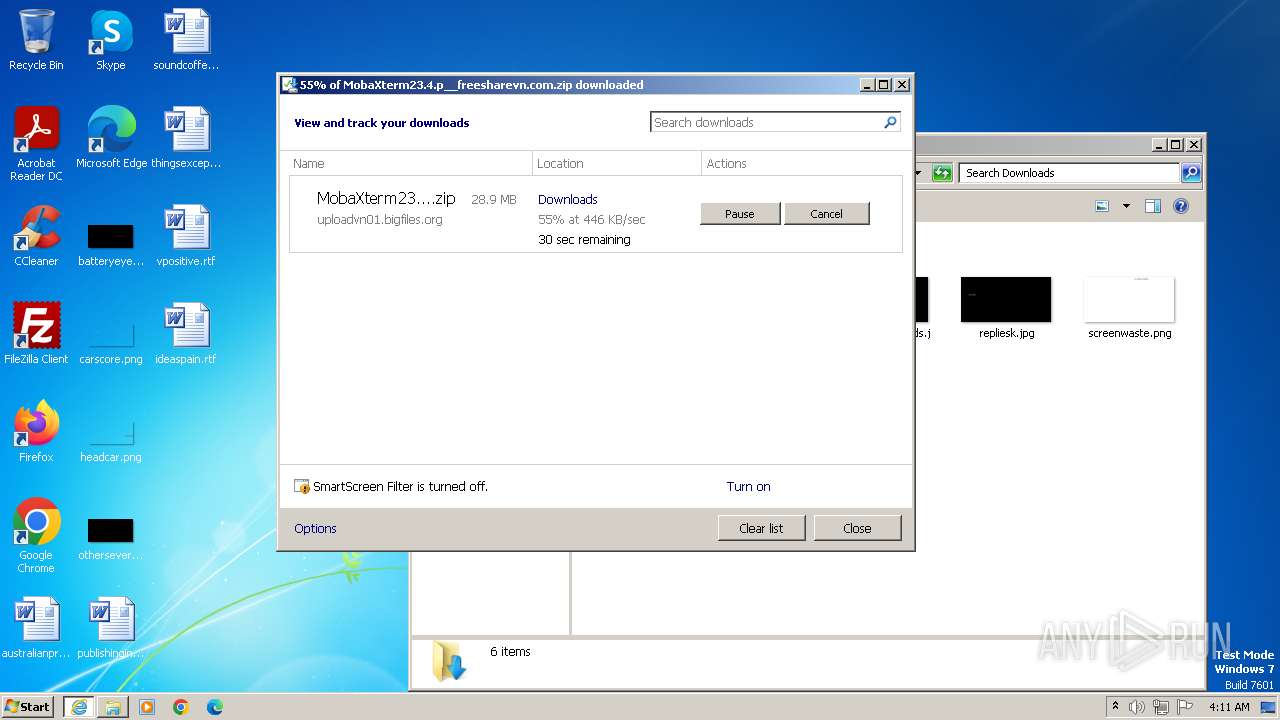
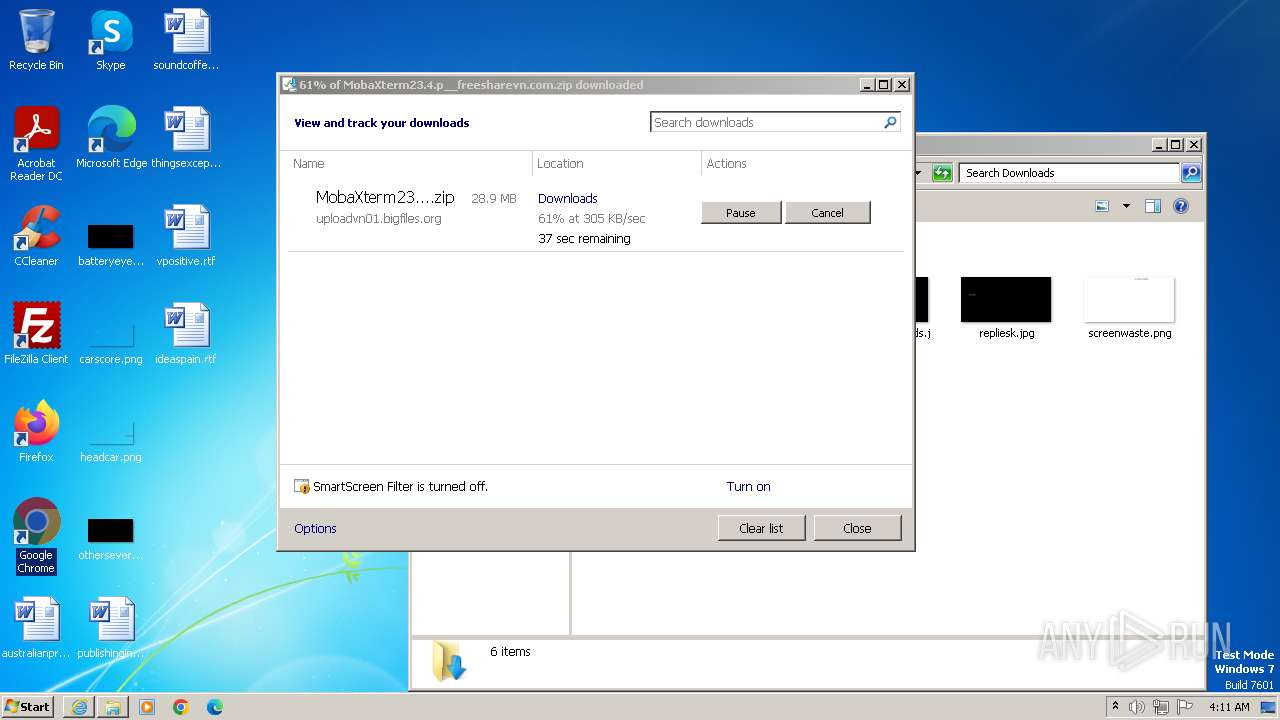
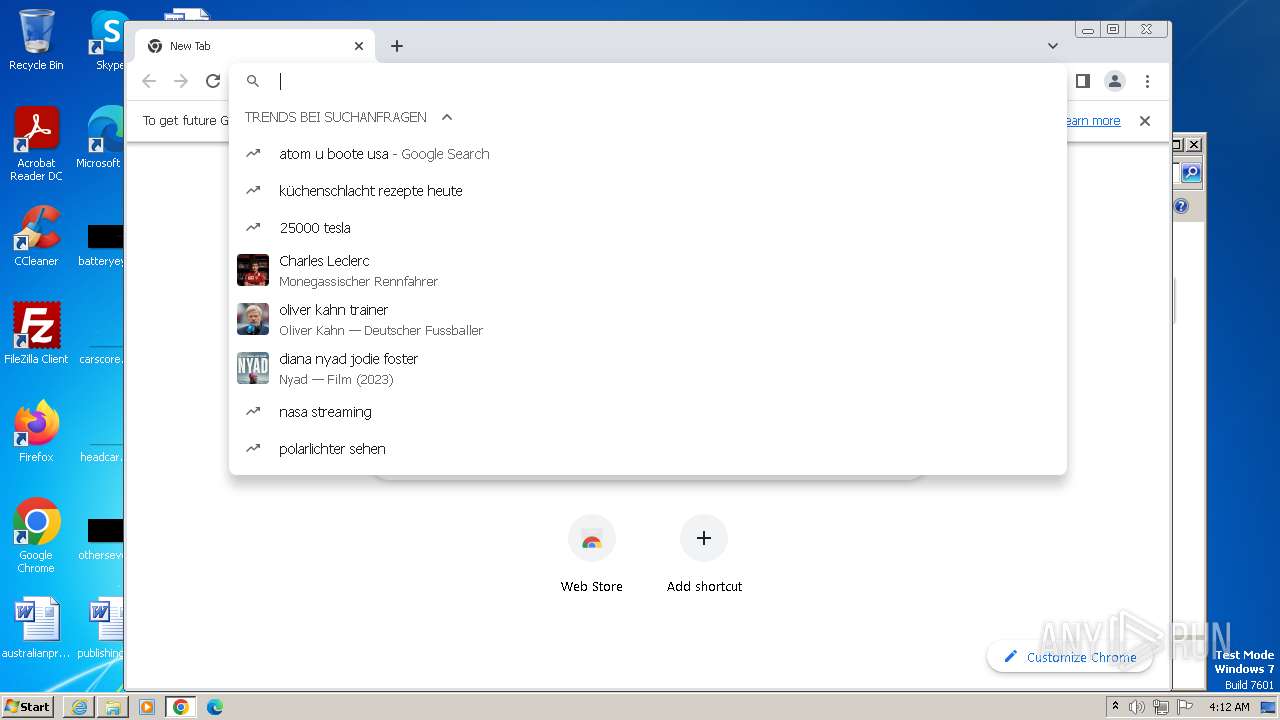
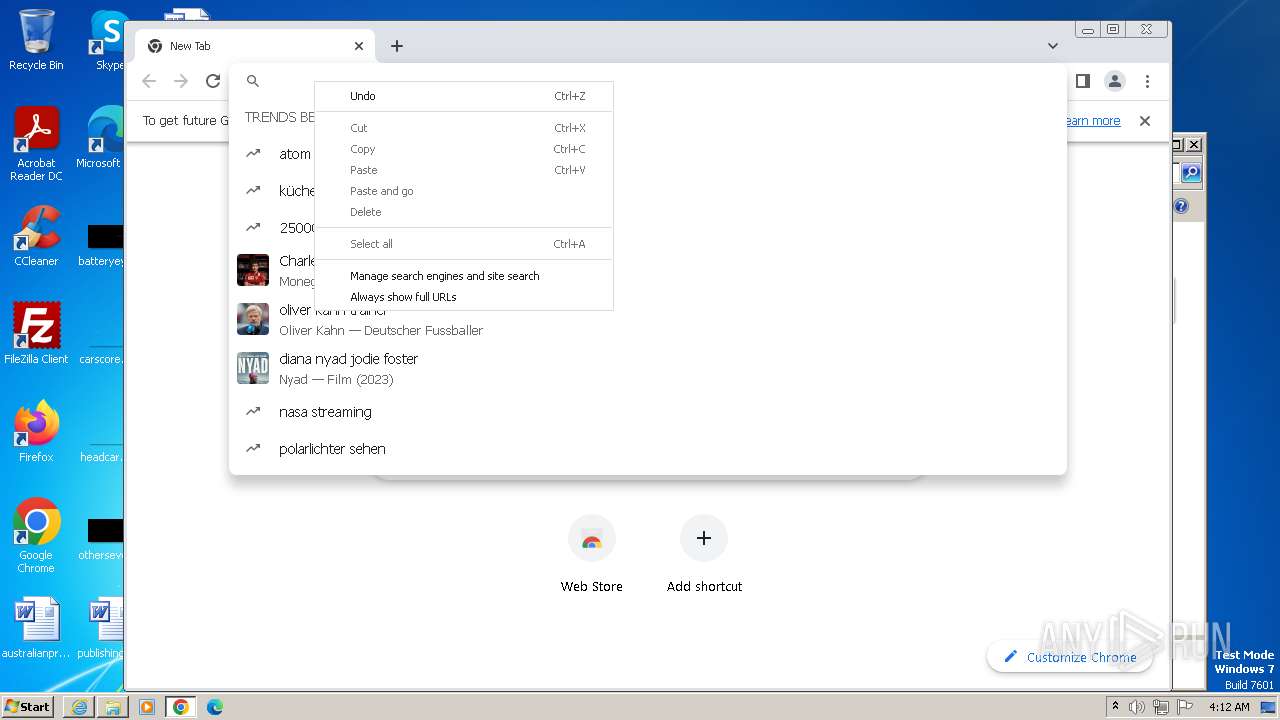
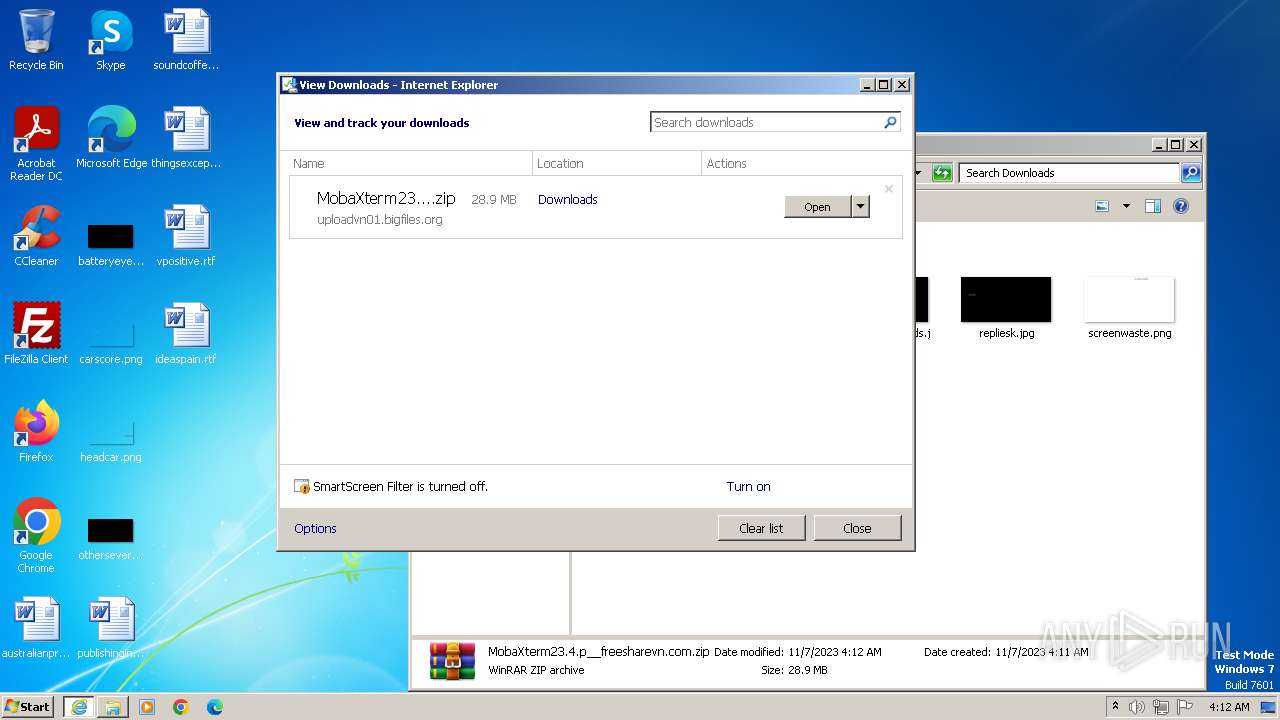
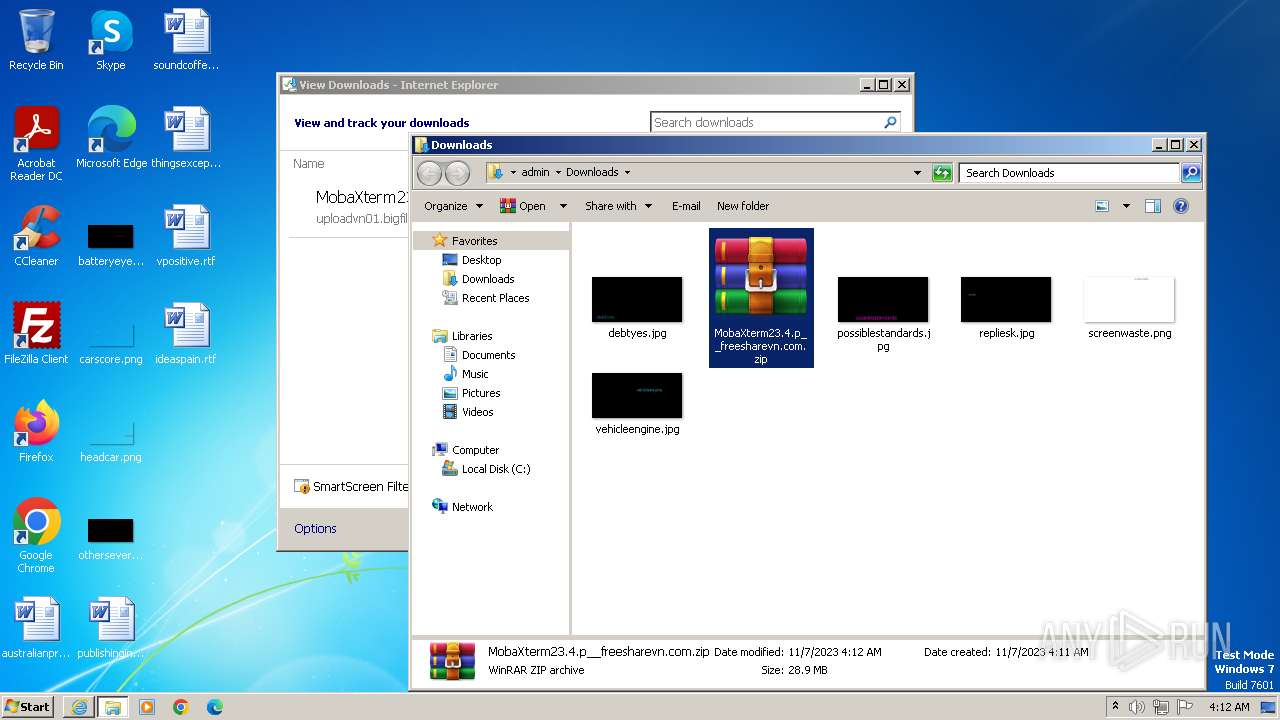
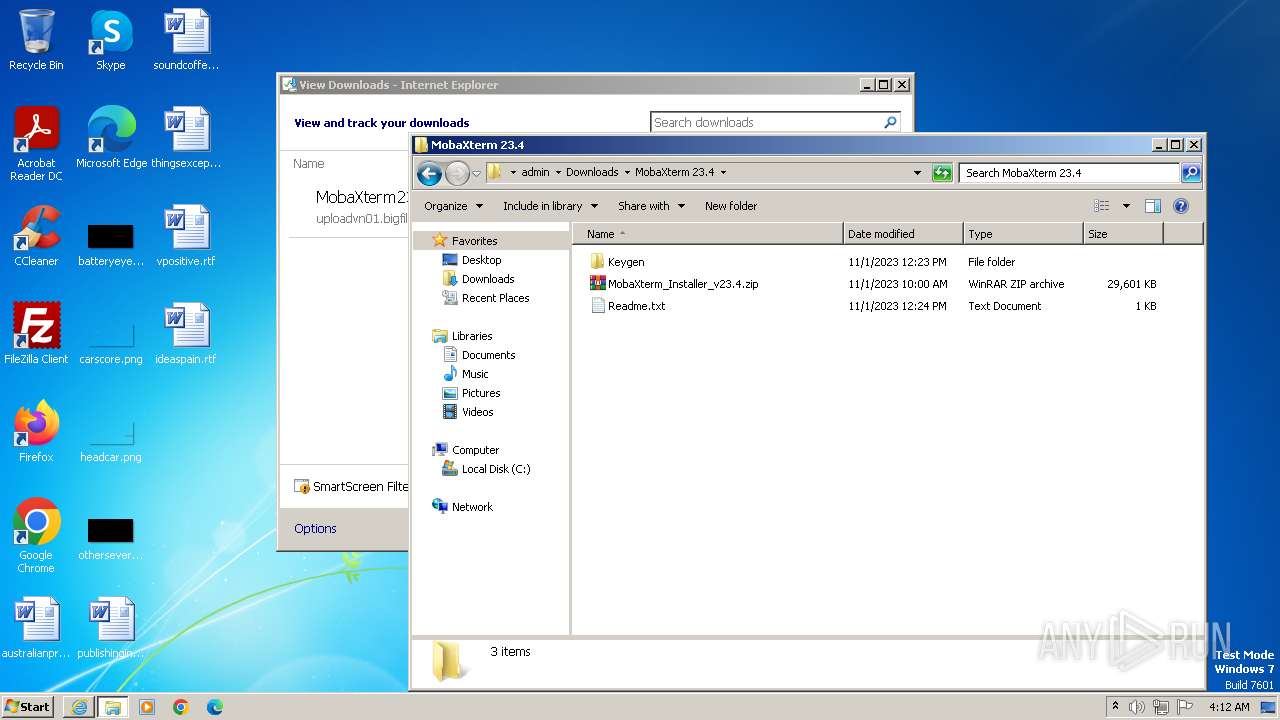
| URL: | https://uploadvn01.bigfiles.org:183/d/2xb2k3tuxryja65ufoh22f7bfyeldbyjbyotif7zzd5ktwdwisn4vgyg4zmjsgkf7c7yzvmw/MobaXterm23.4.p__freesharevn.com.zip |
| Full analysis: | https://app.any.run/tasks/3ddbc74c-aaaf-4b9d-9d7b-87b995c57c56 |
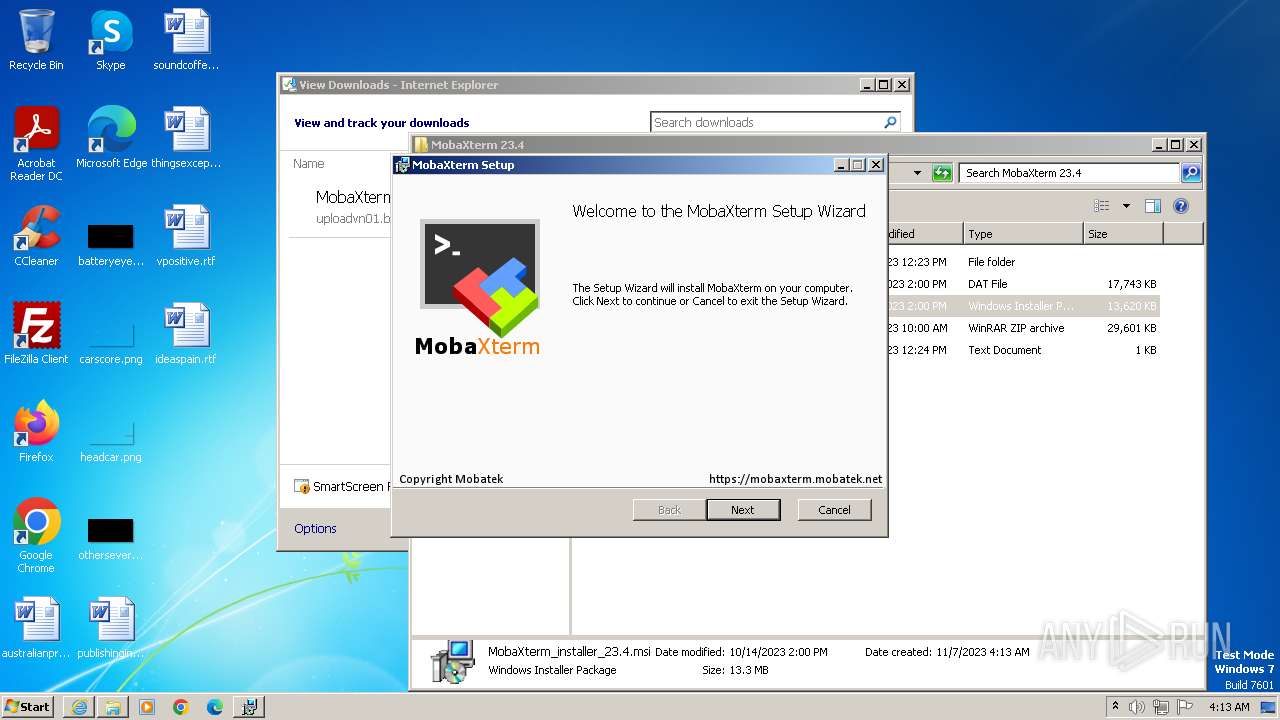
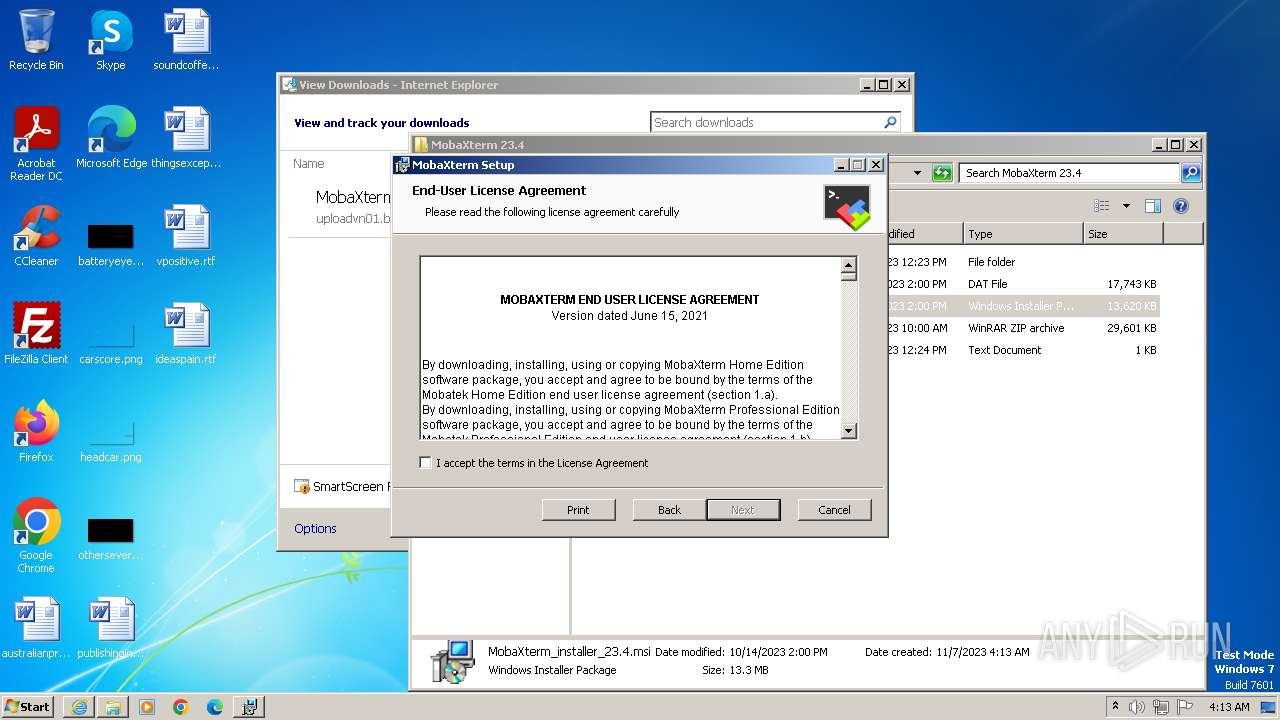
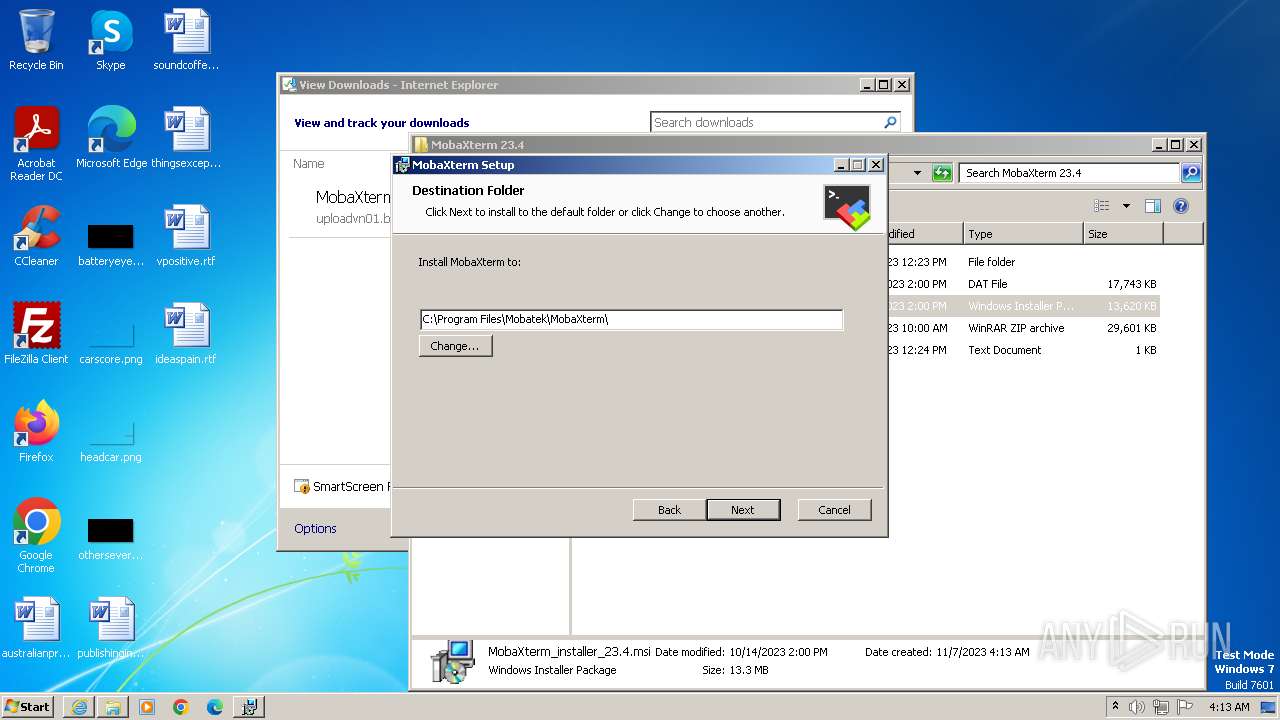
| Verdict: | Malicious activity |
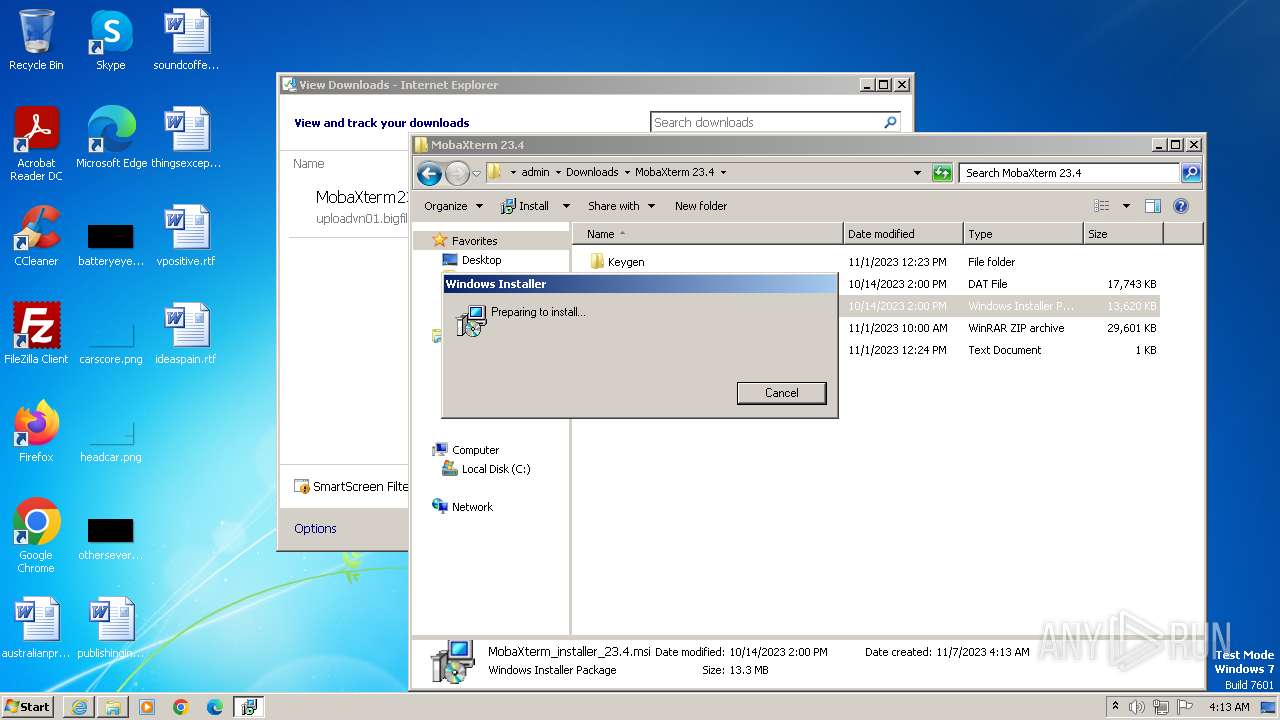
| Analysis date: | November 07, 2023, 04:10:53 |
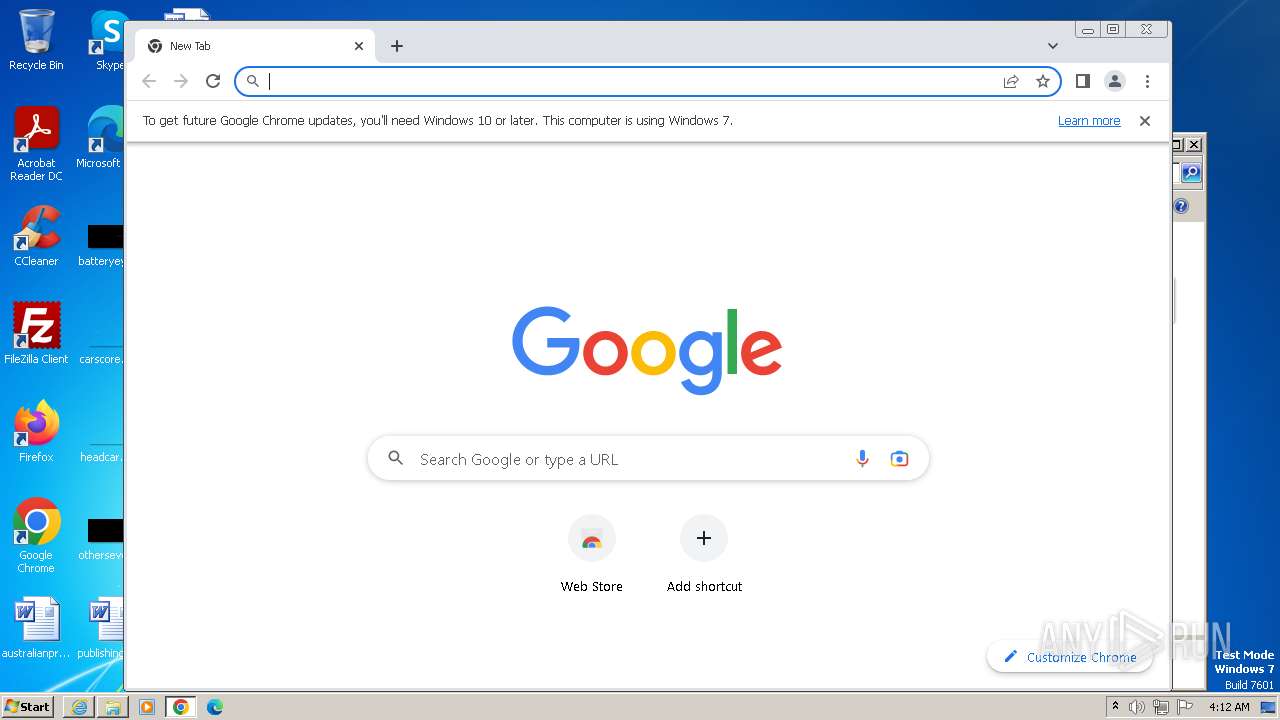
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| SHA1: | B0A4E0D590F57861CB4C391796941719CC14C611 |
| SHA256: | 2B9CA09EB44CB7B33A96EAC1E021499DC838CD8E5CCCC95BC5D9C321FD0C461B |
| SSDEEP: | 3:N8ZEGsCQJA7NBMtOXdXAQESHAAWH6+6W0QpcfESzW6WWl+sLFn:2ZEGRTRAQb+Tp5SzW9/W |
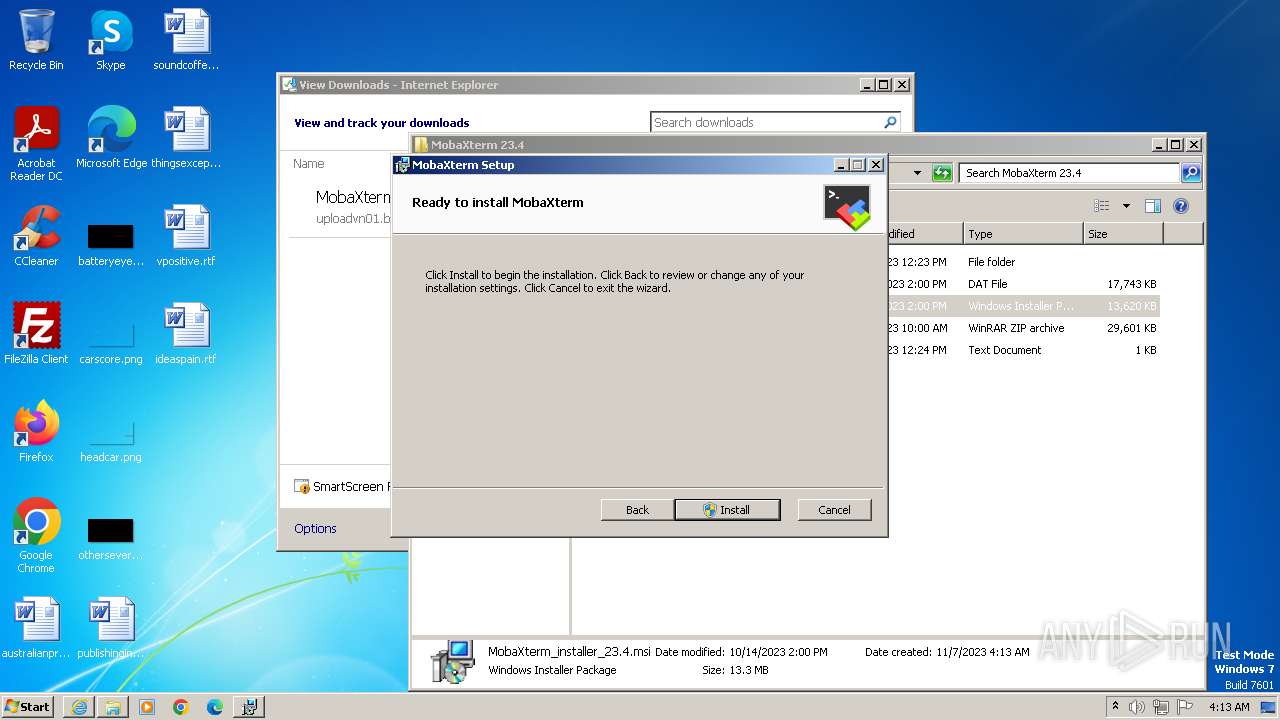
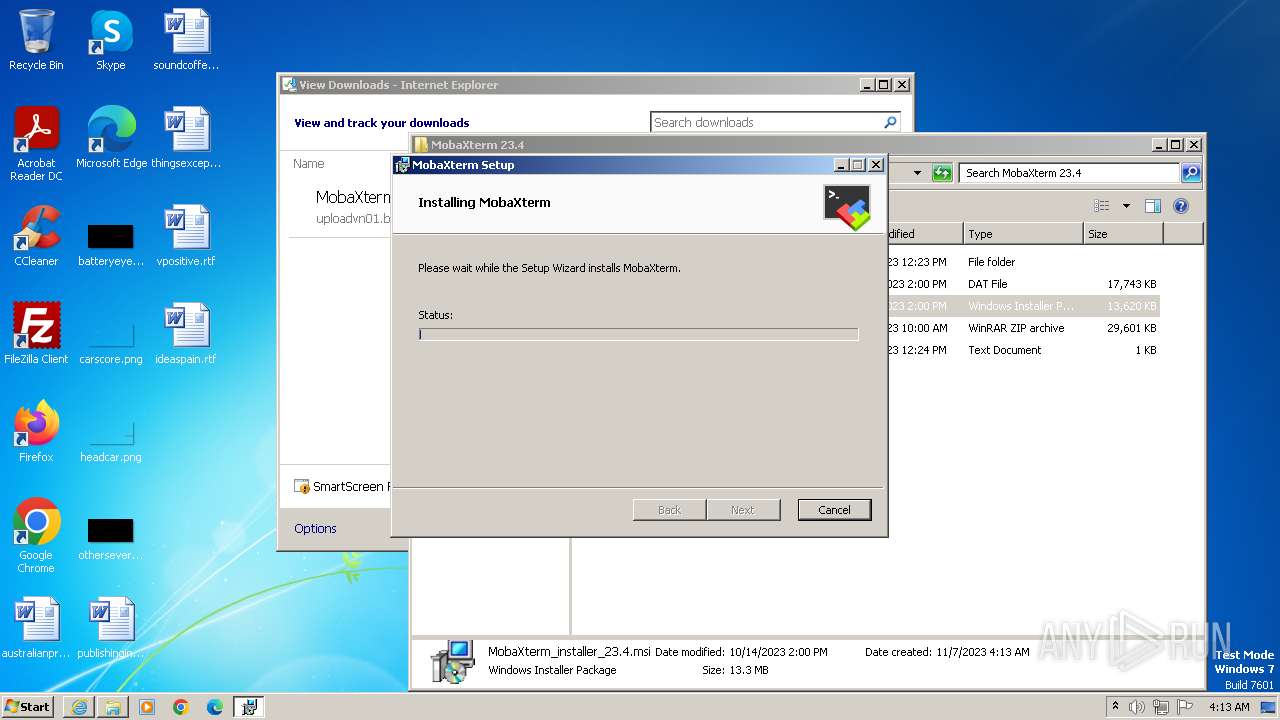
MALICIOUS
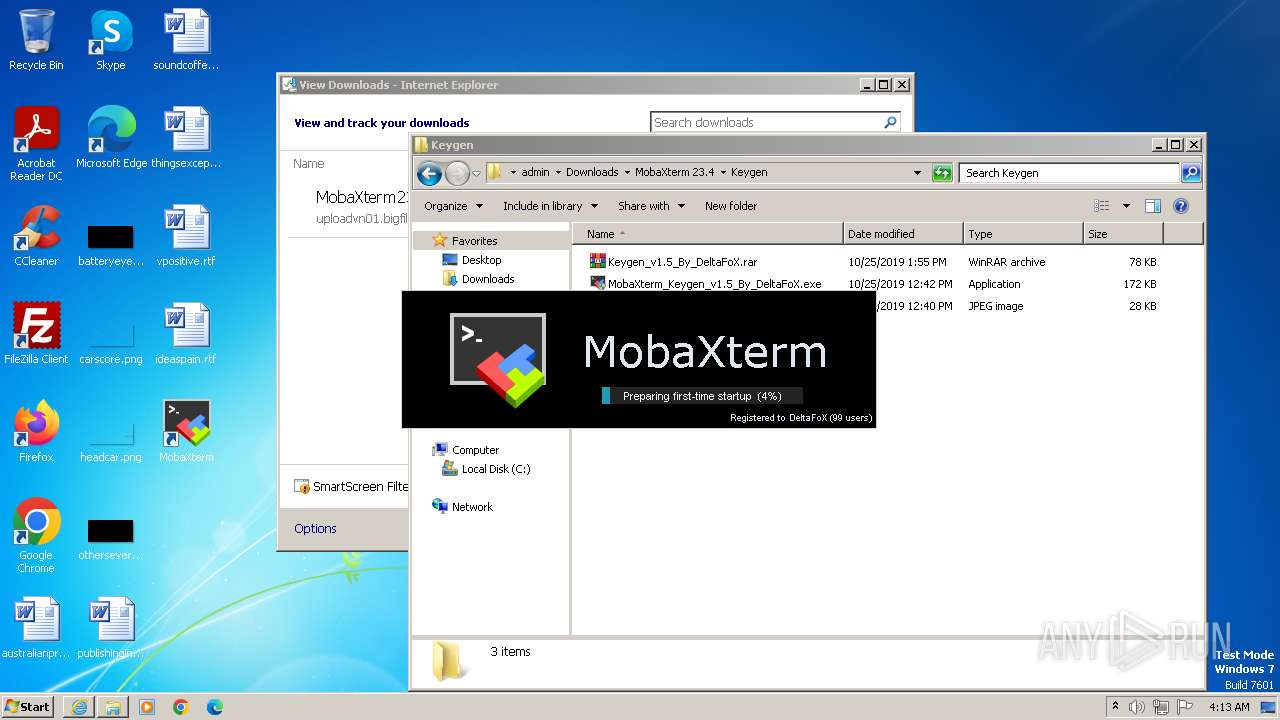
Drops the executable file immediately after the start
- msiexec.exe (PID: 3352)
- MobaXterm.exe (PID: 2176)
- MobaXterm.exe (PID: 3036)
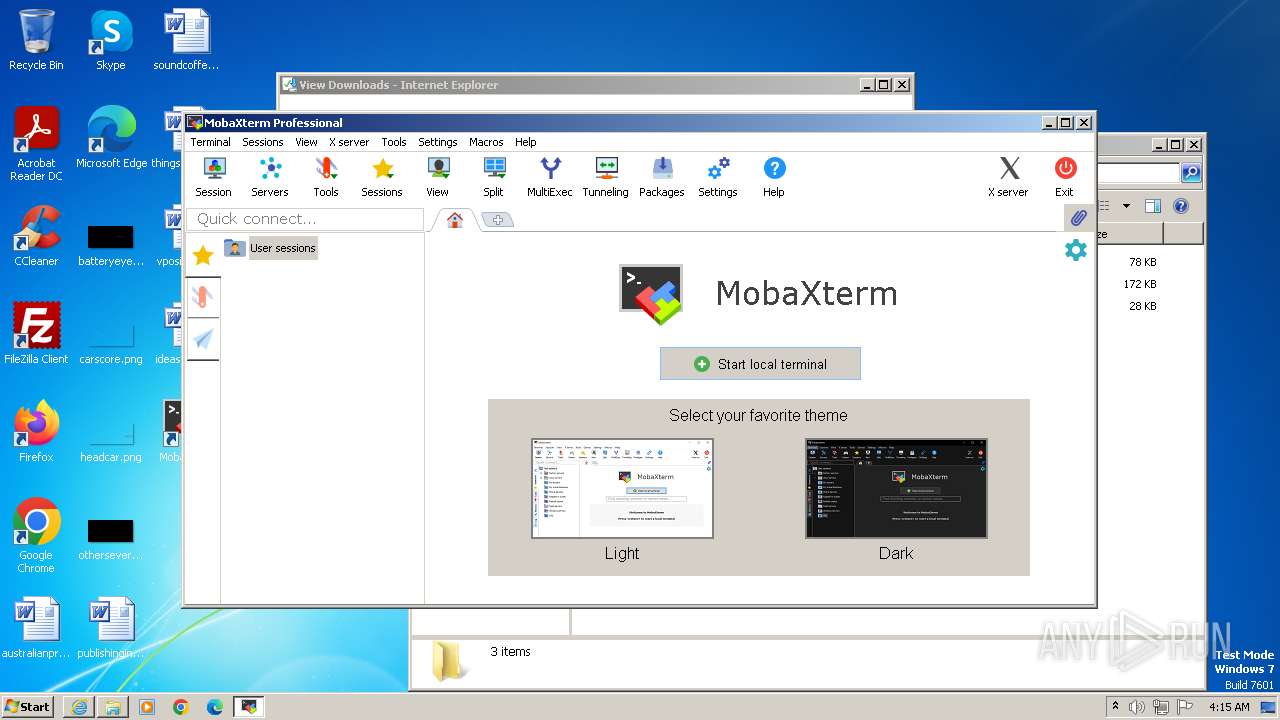
Detects Cygwin installation
- MobaXterm.exe (PID: 3036)
SUSPICIOUS
Process drops legitimate windows executable
- msiexec.exe (PID: 3556)
- msiexec.exe (PID: 3352)
Executes as Windows Service
- VSSVC.exe (PID: 2668)
Checks Windows Trust Settings
- msiexec.exe (PID: 3352)
The process creates files with name similar to system file names
- MobaXterm.exe (PID: 3036)
Reads the Internet Settings
- MobaXterm.exe (PID: 3036)
INFO
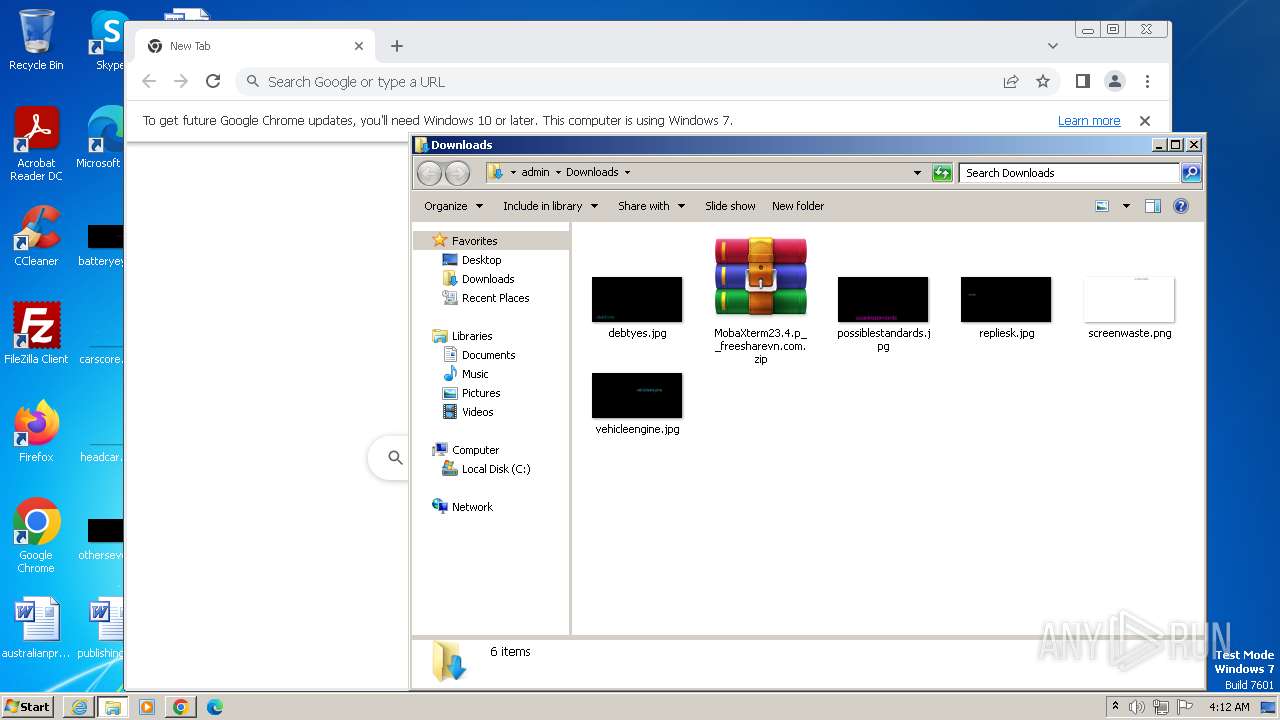
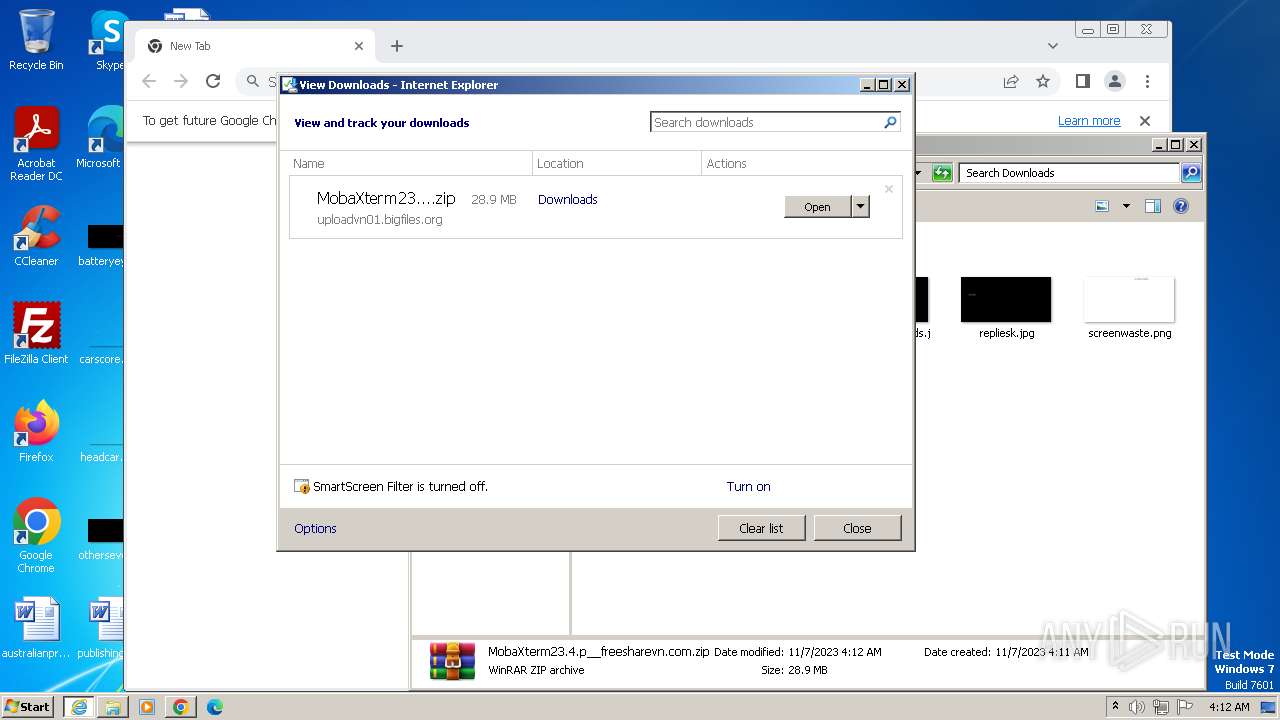
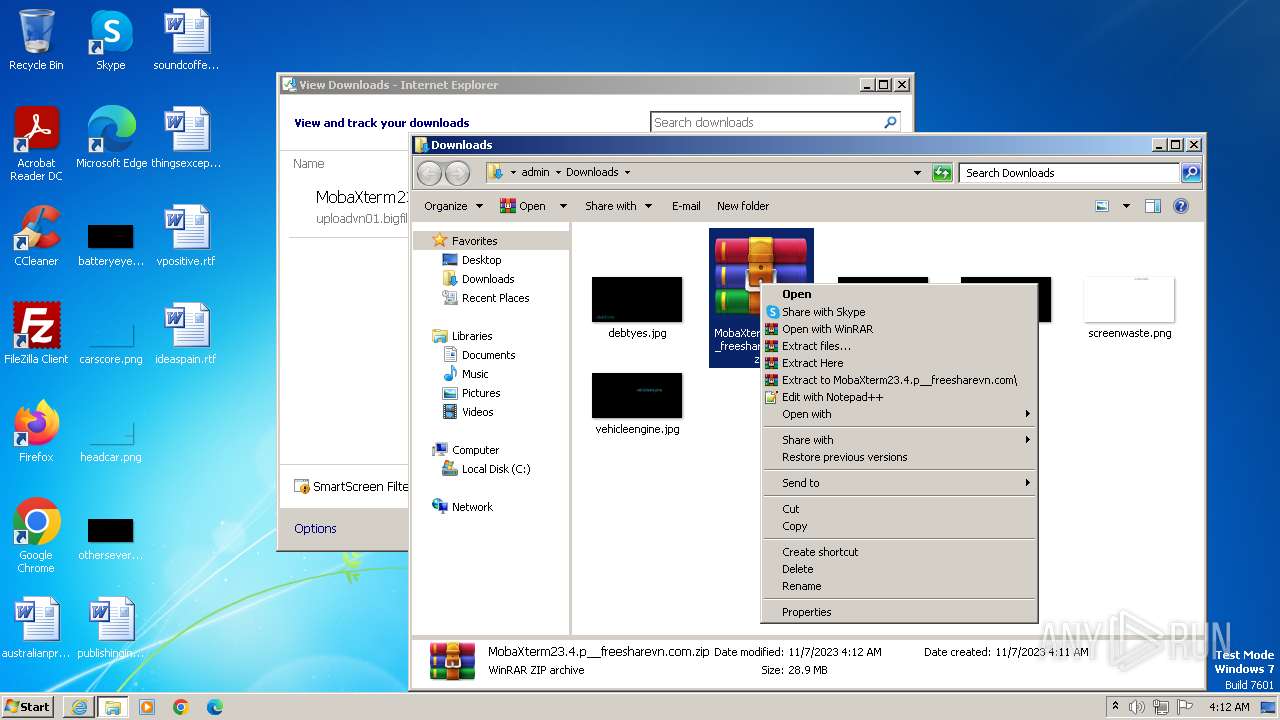
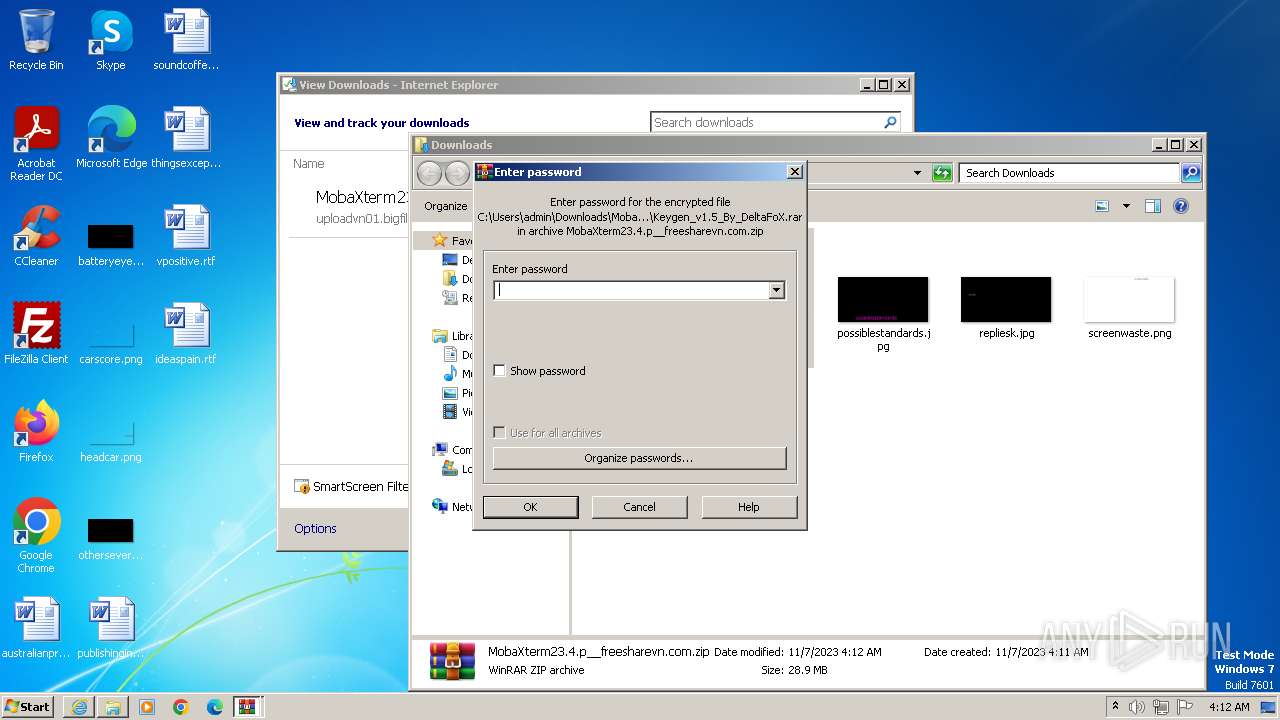
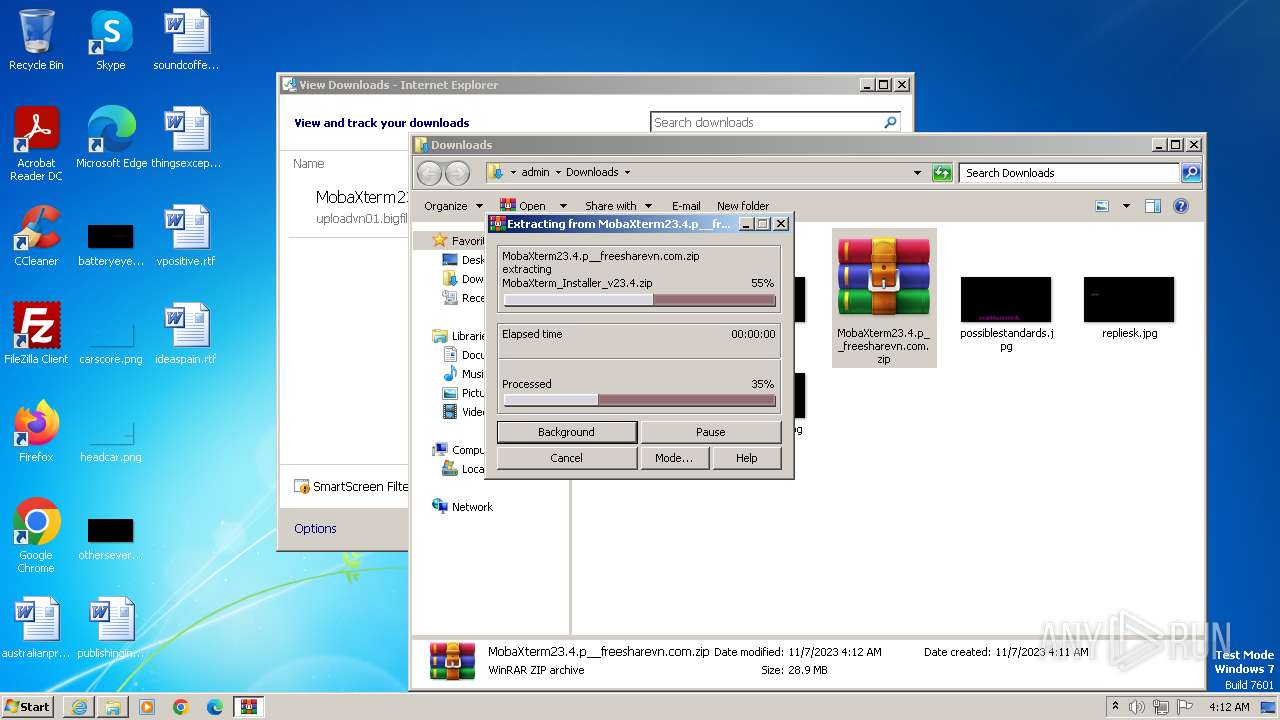
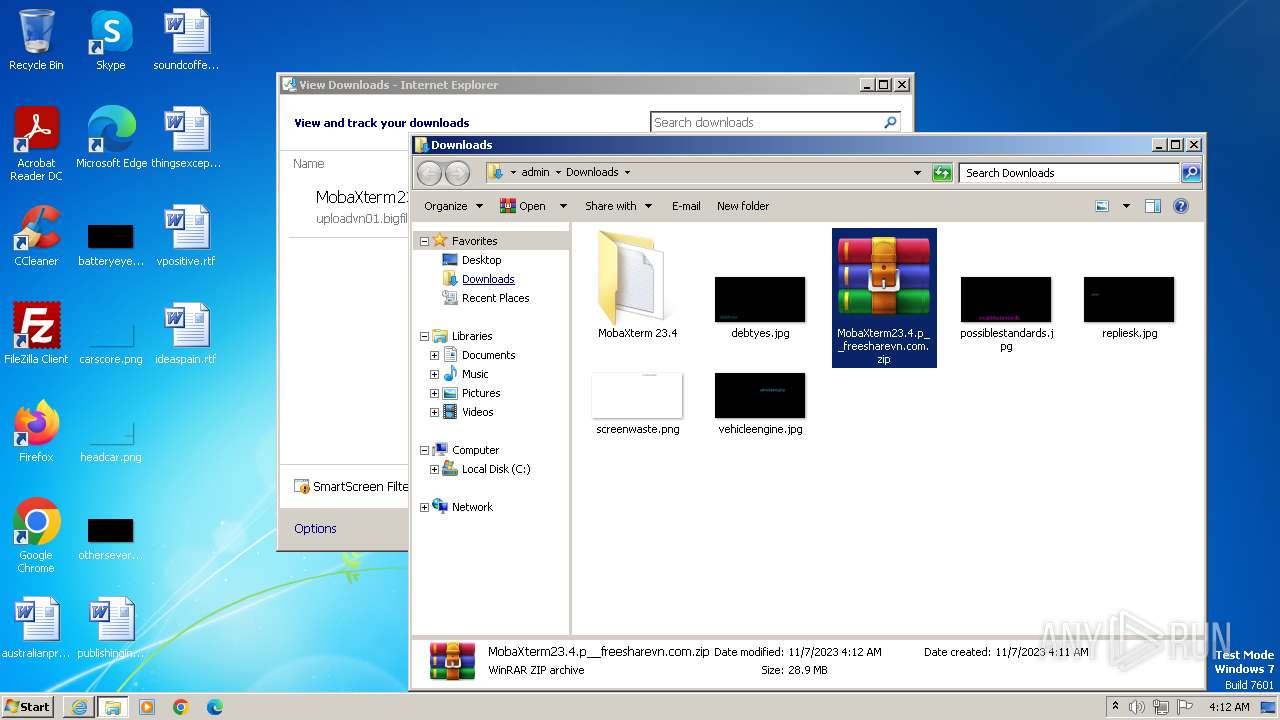
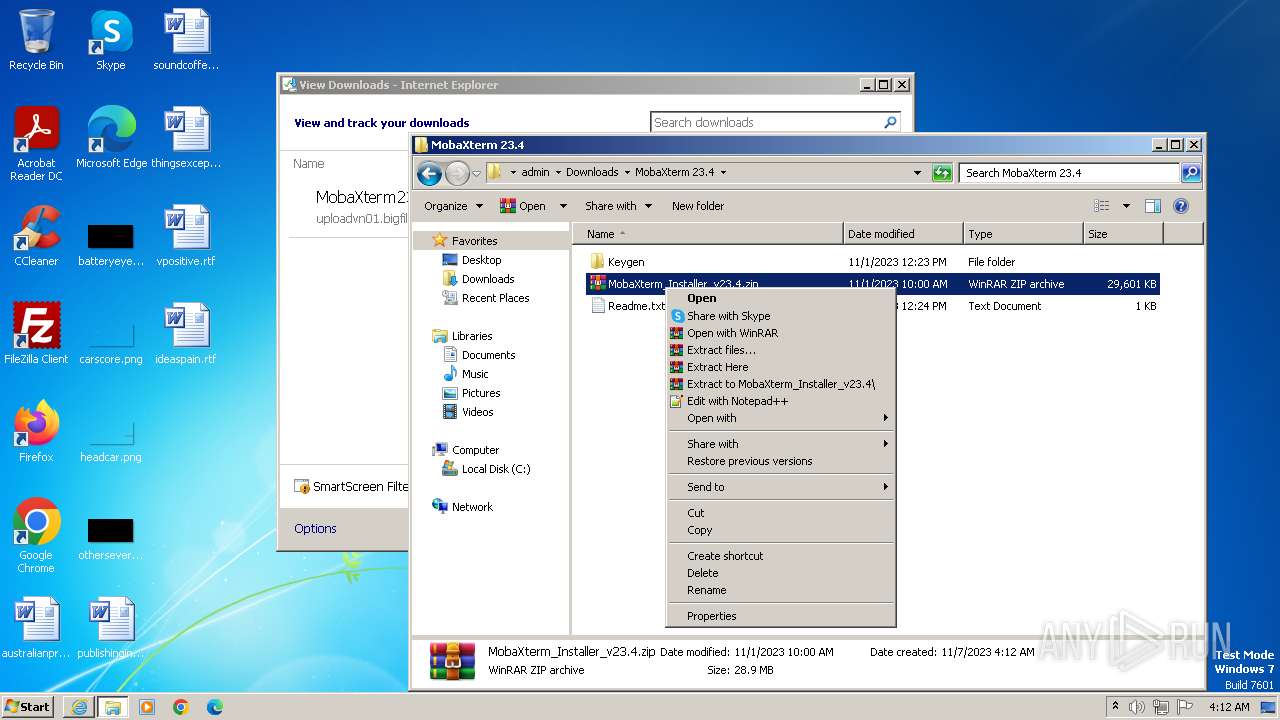
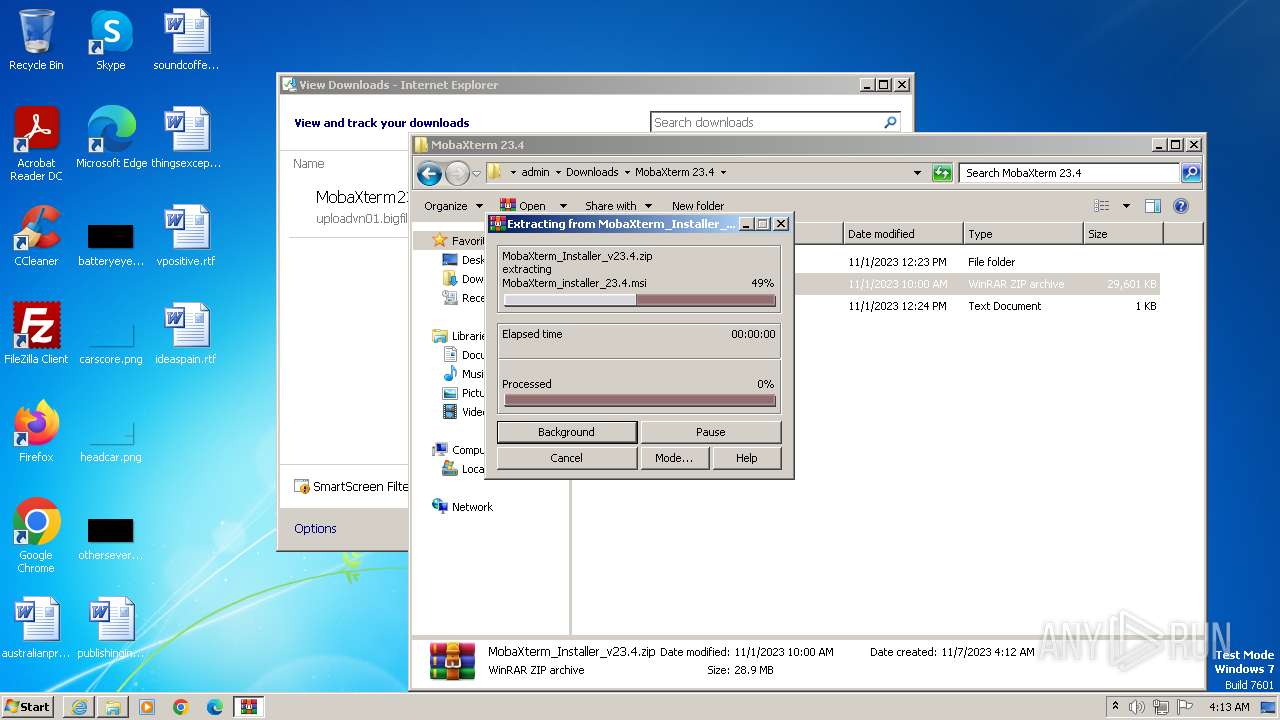
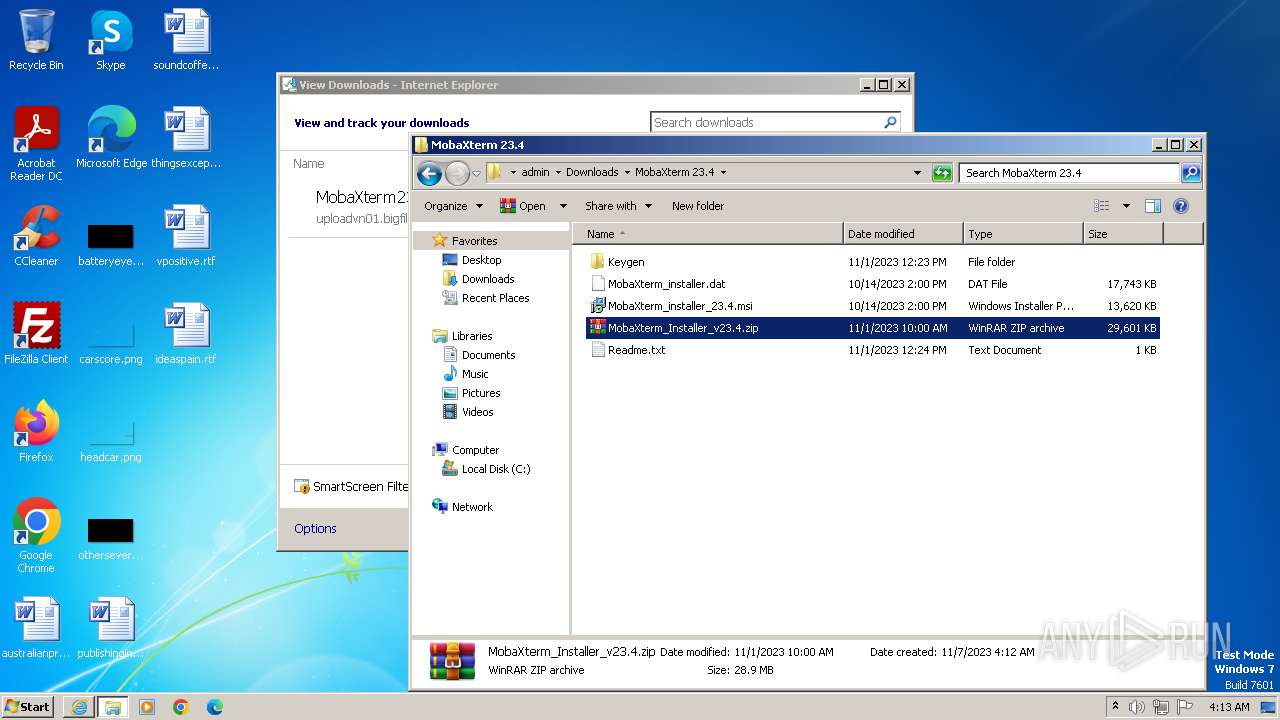
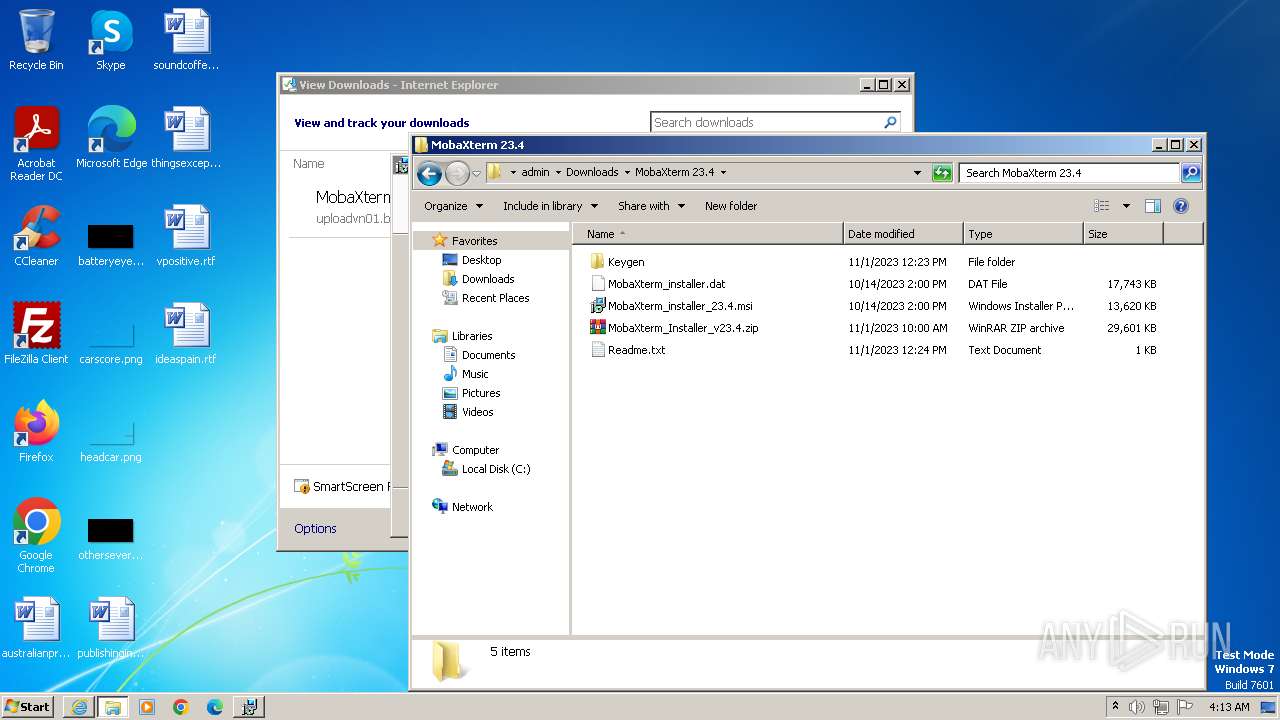
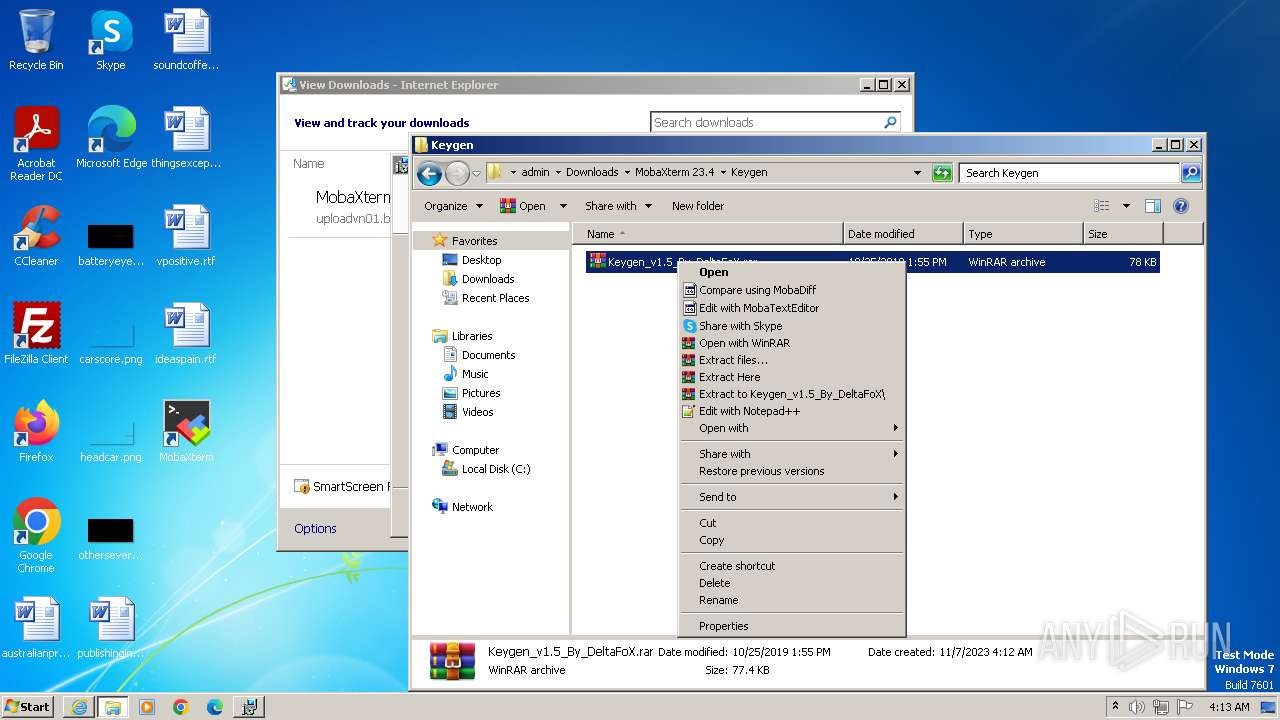
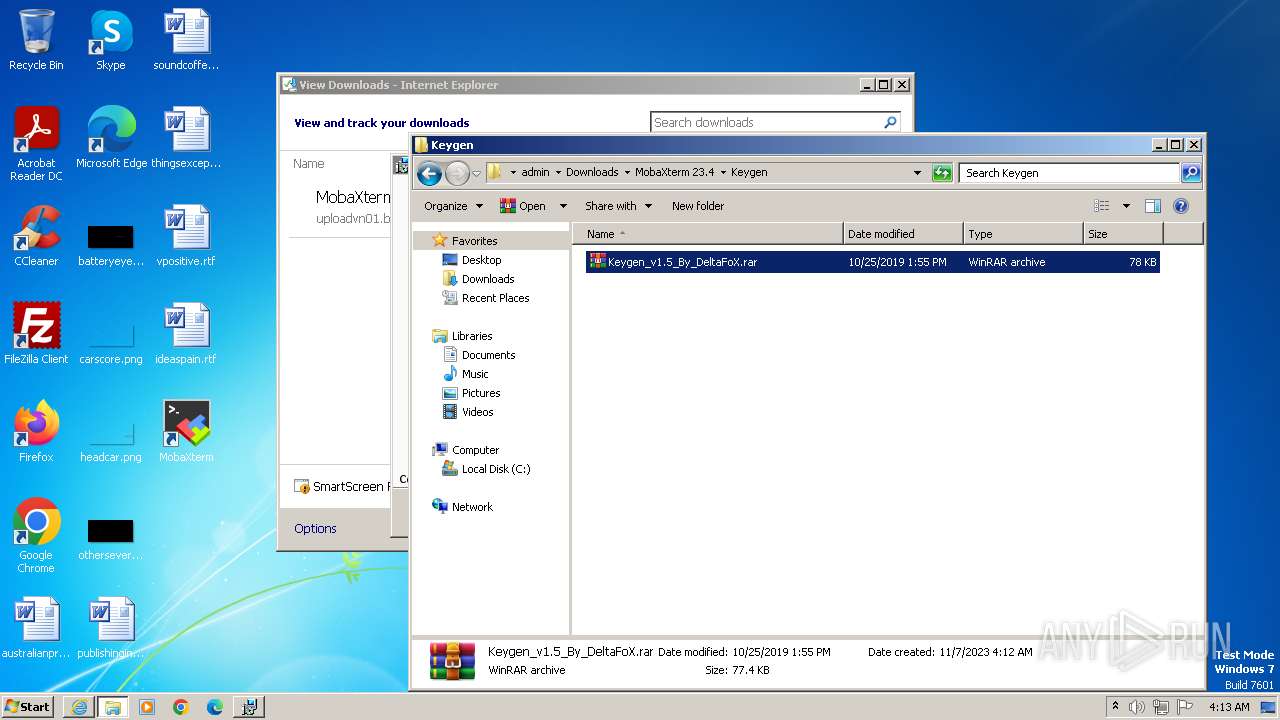
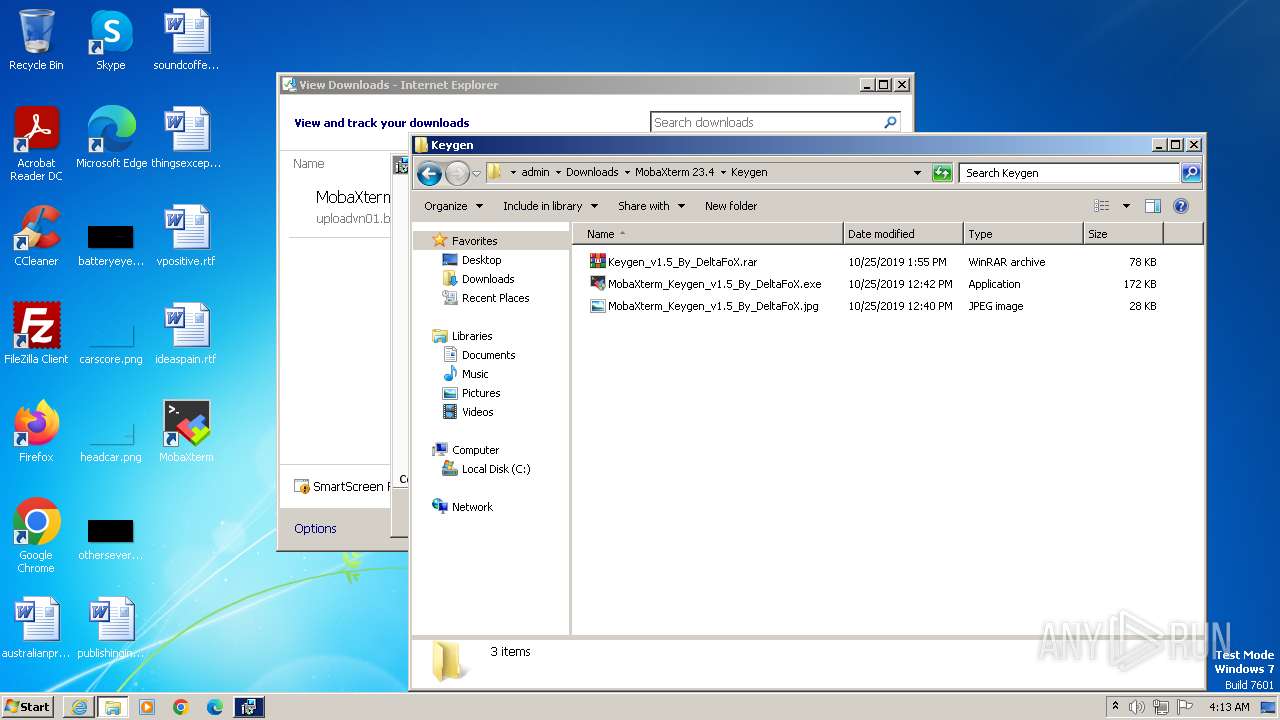
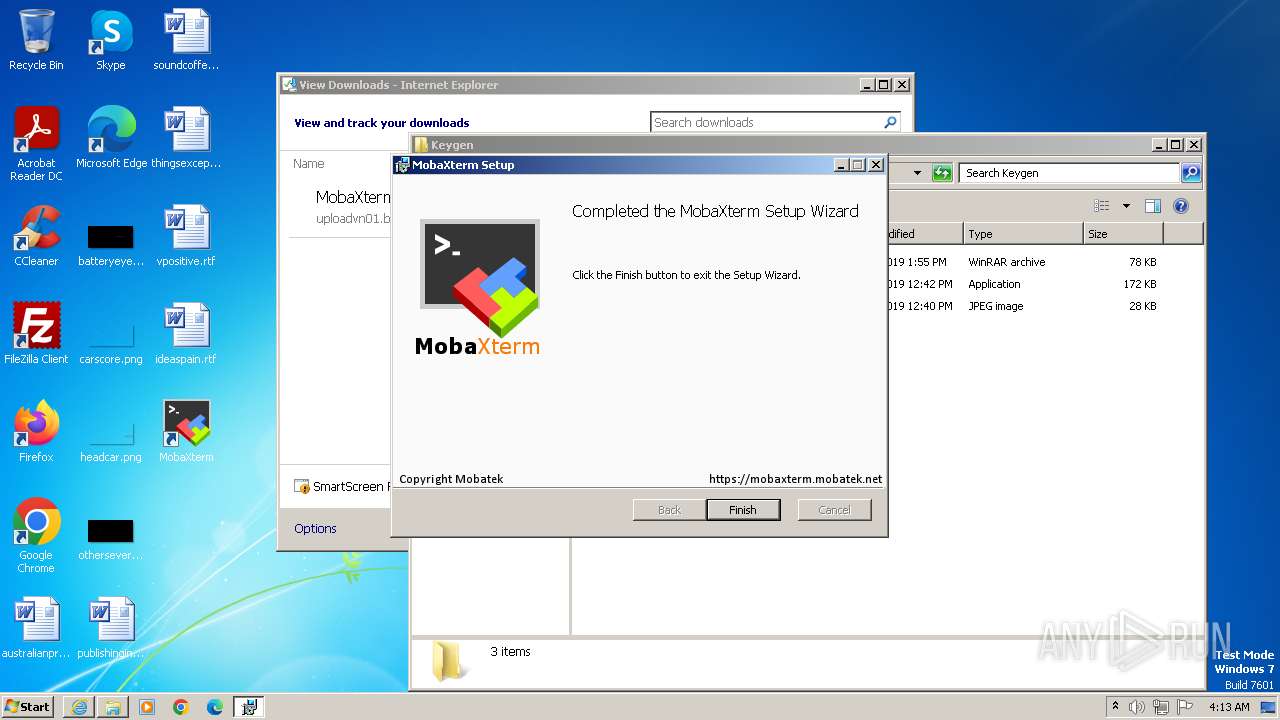
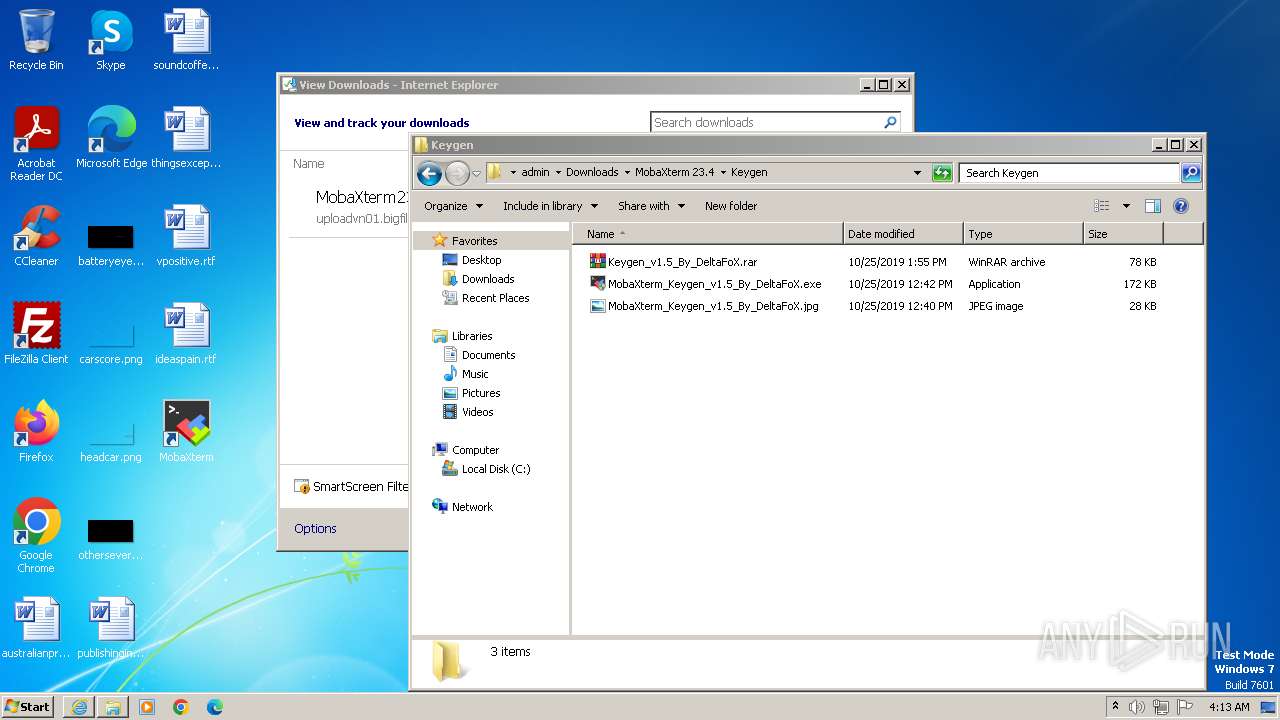
Manual execution by a user
- wmpnscfg.exe (PID: 3444)
- WinRAR.exe (PID: 2988)
- msiexec.exe (PID: 3556)
- WinRAR.exe (PID: 3516)
- chrome.exe (PID: 3908)
- WinRAR.exe (PID: 1992)
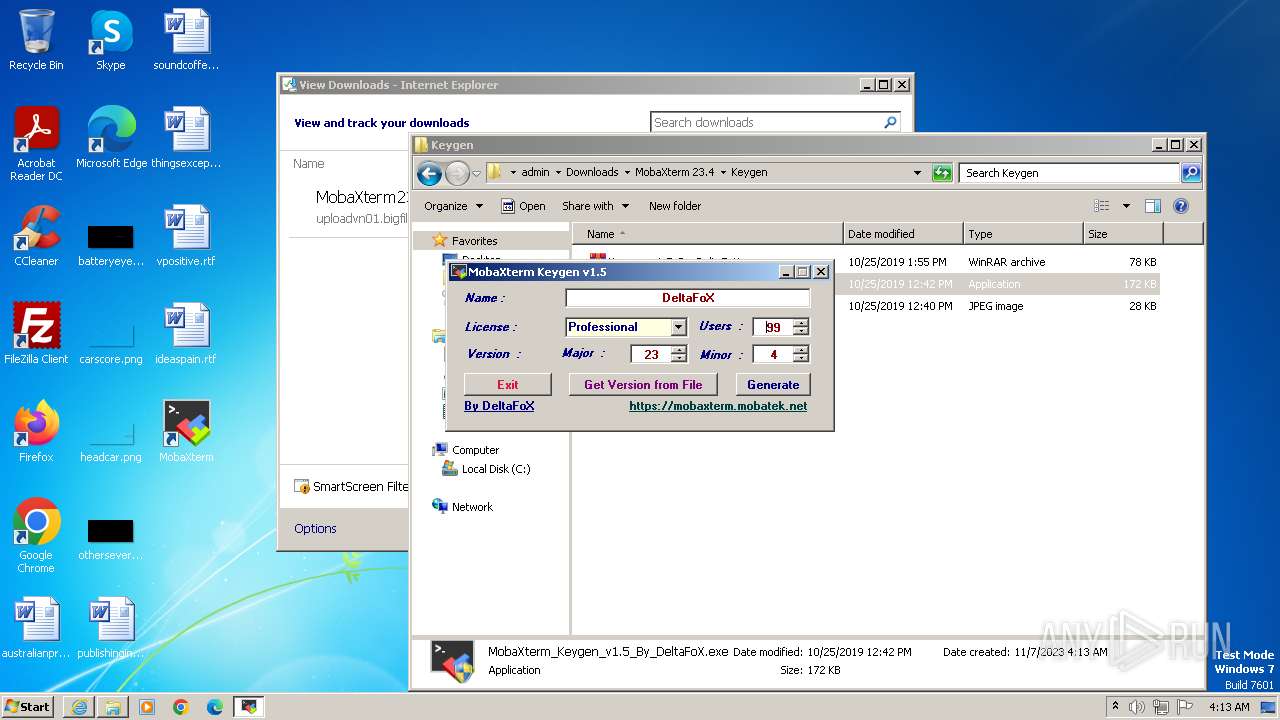
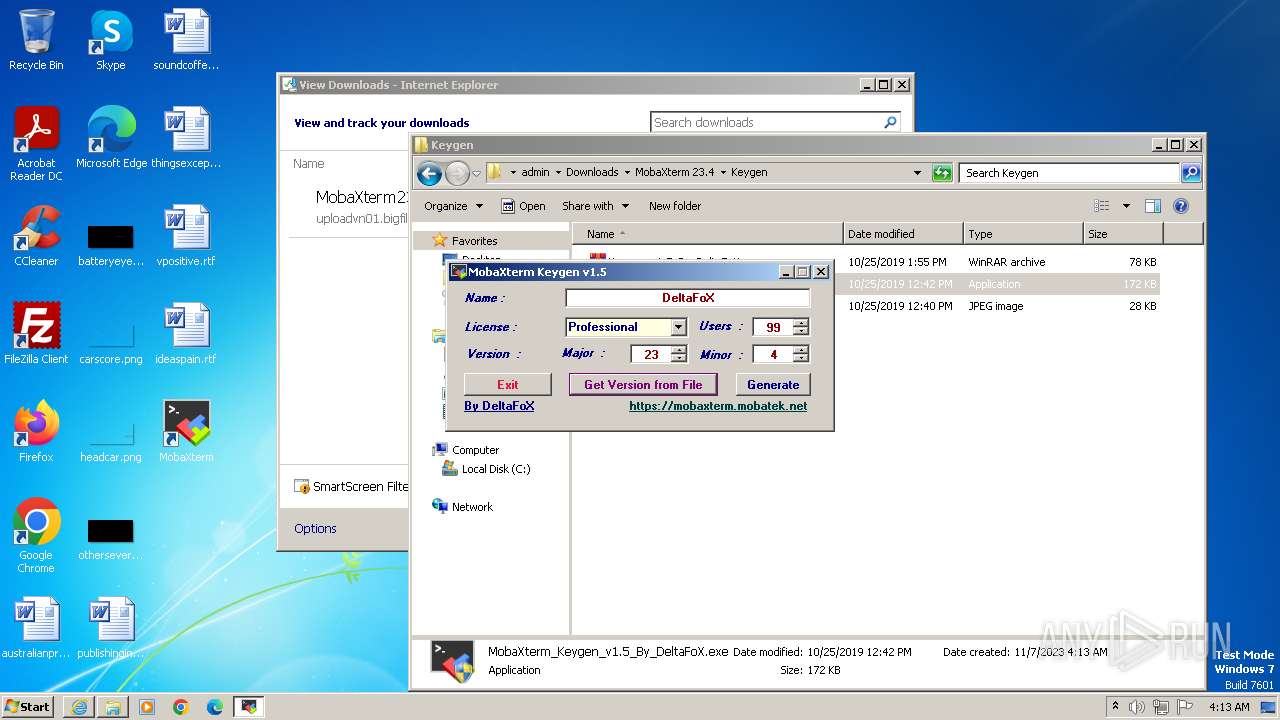
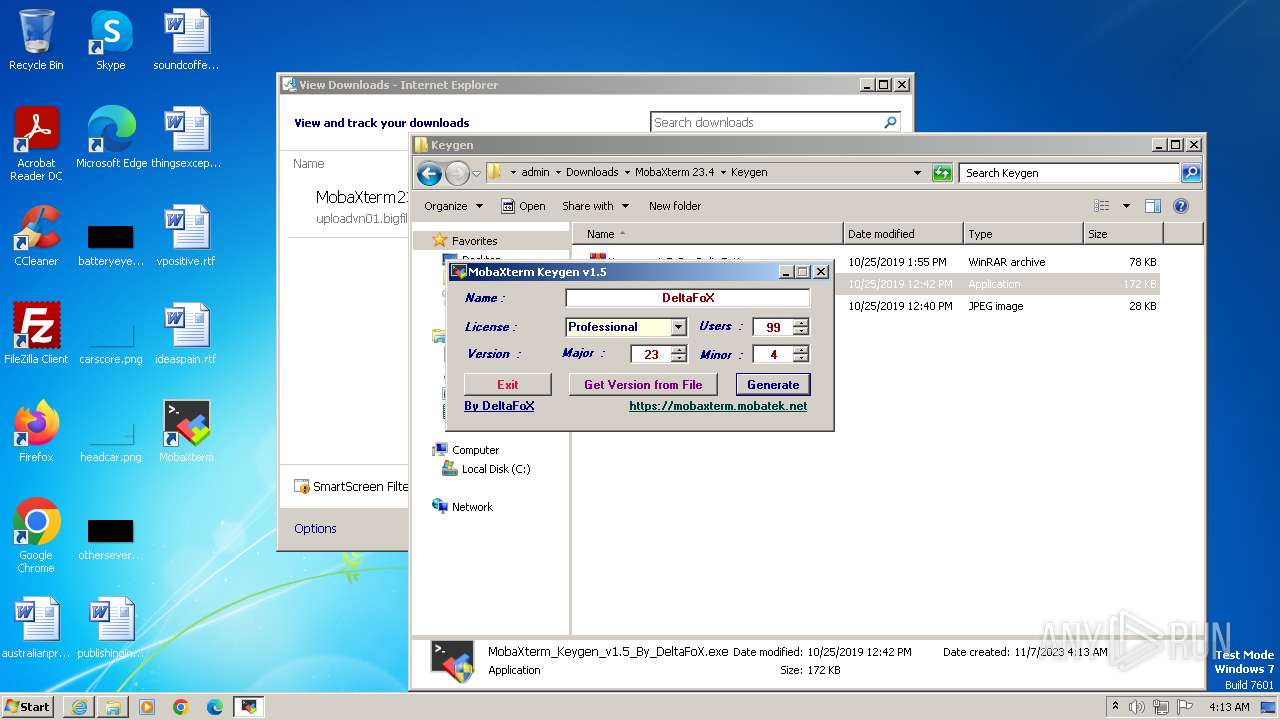
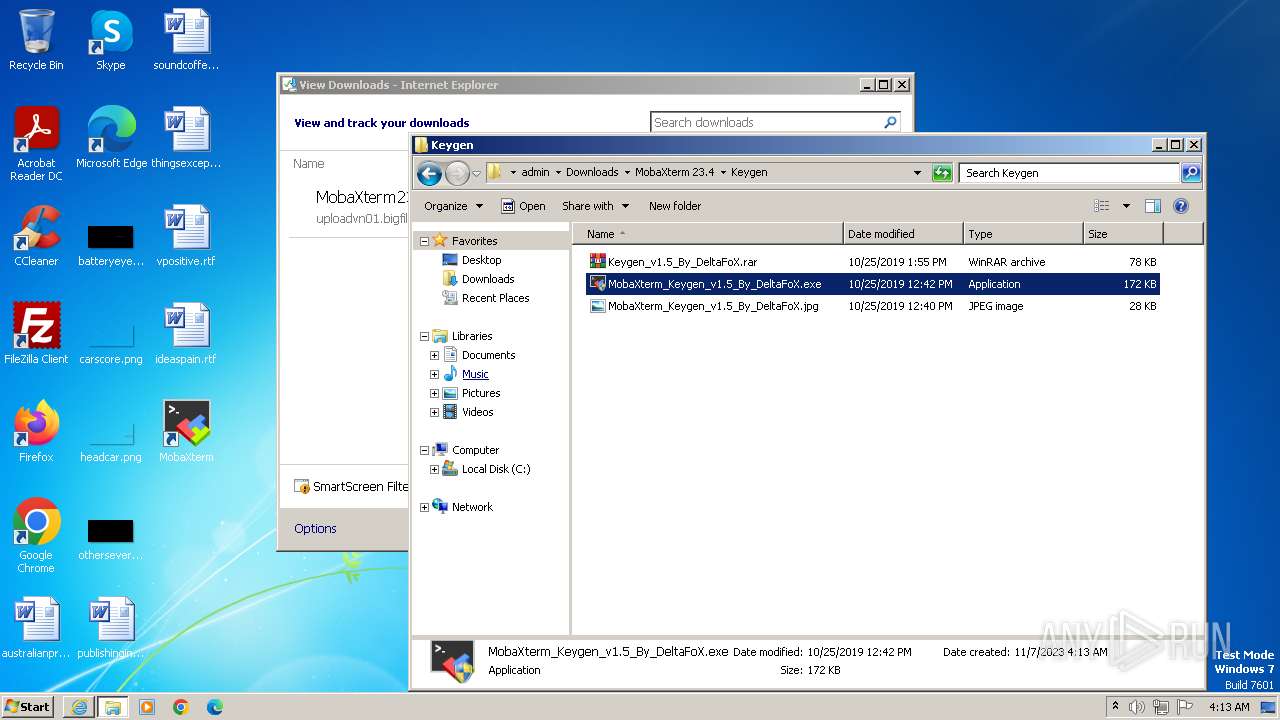
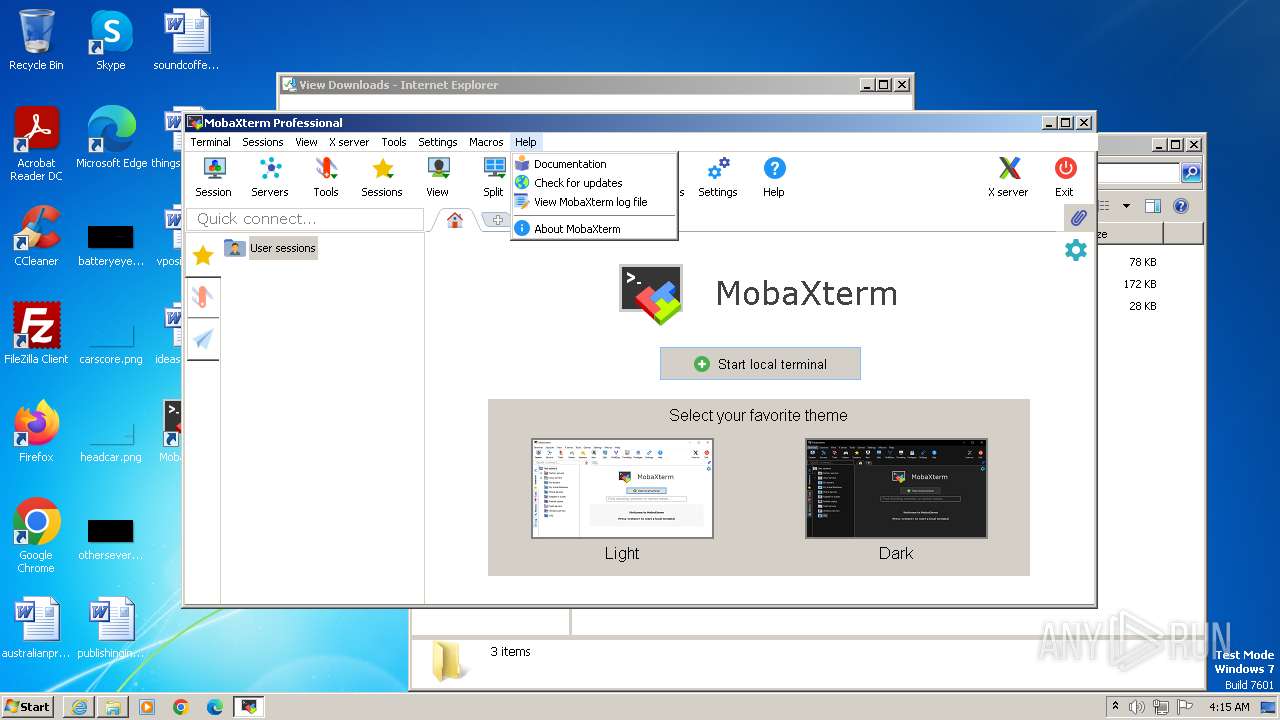
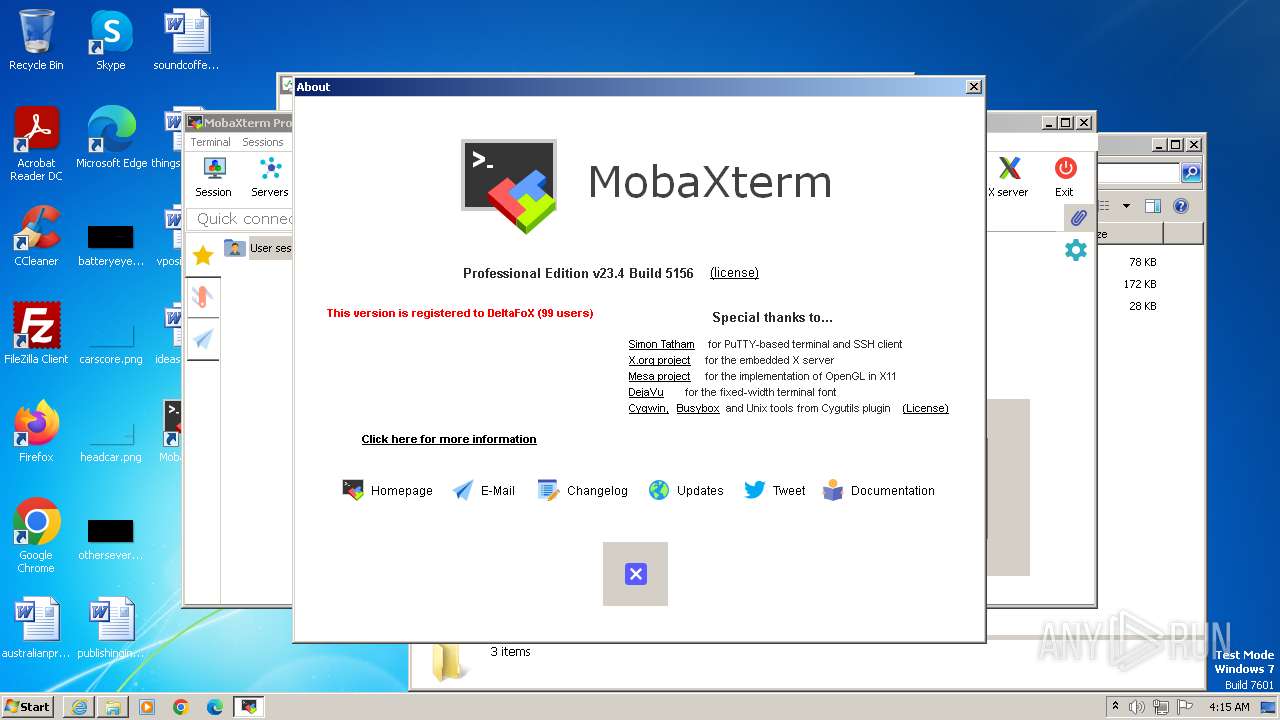
- MobaXterm_Keygen_v1.5_By_DeltaFoX.exe (PID: 2368)
- MobaXterm.exe (PID: 3036)
- MobaXterm_Keygen_v1.5_By_DeltaFoX.exe (PID: 1836)
Application launched itself
- iexplore.exe (PID: 3240)
- chrome.exe (PID: 3908)
- msiexec.exe (PID: 3352)
The process uses the downloaded file
- chrome.exe (PID: 2760)
- chrome.exe (PID: 1644)
- iexplore.exe (PID: 3240)
- chrome.exe (PID: 1088)
- WinRAR.exe (PID: 2988)
Reads the computer name
- wmpnscfg.exe (PID: 3444)
- msiexec.exe (PID: 3352)
- msiexec.exe (PID: 3832)
- msiexec.exe (PID: 1828)
- MobaXterm.exe (PID: 2176)
- msiexec.exe (PID: 2336)
- MobaXterm_Keygen_v1.5_By_DeltaFoX.exe (PID: 1836)
- MobaXterm.exe (PID: 3036)
- XWin_MobaX.exe (PID: 1152)
Checks supported languages
- wmpnscfg.exe (PID: 3444)
- msiexec.exe (PID: 3352)
- msiexec.exe (PID: 3832)
- msiexec.exe (PID: 1828)
- MobaXterm.exe (PID: 2176)
- msiexec.exe (PID: 2336)
- MobaXterm.exe (PID: 3036)
- MobaXterm_Keygen_v1.5_By_DeltaFoX.exe (PID: 1836)
- XWin_MobaX.exe (PID: 1152)
- xkbcomp_w32.exe (PID: 4004)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 3556)
Reads the machine GUID from the registry
- msiexec.exe (PID: 3352)
- wmpnscfg.exe (PID: 3444)
- msiexec.exe (PID: 3832)
- msiexec.exe (PID: 1828)
- msiexec.exe (PID: 2336)
- MobaXterm_Keygen_v1.5_By_DeltaFoX.exe (PID: 1836)
- MobaXterm.exe (PID: 3036)
Drops the executable file immediately after the start
- msiexec.exe (PID: 3556)
- WinRAR.exe (PID: 1992)
Create files in a temporary directory
- msiexec.exe (PID: 3352)
Creates files in the program directory
- MobaXterm_Keygen_v1.5_By_DeltaFoX.exe (PID: 1836)
Reads product name
- MobaXterm.exe (PID: 3036)
Reads Environment values
- MobaXterm.exe (PID: 3036)
Reads mouse settings
- MobaXterm.exe (PID: 3036)
Creates files or folders in the user directory
- MobaXterm.exe (PID: 3036)
- xkbcomp_w32.exe (PID: 4004)
- XWin_MobaX.exe (PID: 1152)
Dropped object may contain TOR URL's
- MobaXterm.exe (PID: 3036)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
85
Monitored processes
35
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 284 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3632 --field-trial-handle=1188,i,12949275497550514063,4841893976565689482,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4116 --field-trial-handle=1188,i,12949275497550514063,4841893976565689482,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=4024 --field-trial-handle=1188,i,12949275497550514063,4841893976565689482,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1152 | "C:\Users\admin\AppData\Roaming\MobaXterm\slash\bin\XWin_MobaX.exe" -silent-dup-error -notrayicon -nolisten inet6 -hostintitle +bs -clipboard -nowgl -multiwindow -noreset :0 | C:\Users\admin\AppData\Roaming\MobaXterm\slash\bin\XWin_MobaX.exe | — | MobaXterm.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --mojo-platform-channel-handle=1328 --field-trial-handle=1188,i,12949275497550514063,4841893976565689482,131072 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --gpu-preferences=UAAAAAAAAADgAAAYAAAAAAAAAAAAAAAAAABgAAAAAAAwAAAAAAAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAEgAAAAAAAAASAAAAAAAAAAYAAAAAgAAABAAAAAAAAAAGAAAAAAAAAAQAAAAAAAAAAAAAAAOAAAAEAAAAAAAAAABAAAADgAAAAgAAAAAAAAACAAAAAAAAAA= --use-gl=angle --use-angle=swiftshader-webgl --mojo-platform-channel-handle=1556 --field-trial-handle=1188,i,12949275497550514063,4841893976565689482,131072 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1644 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3968 --field-trial-handle=1188,i,12949275497550514063,4841893976565689482,131072 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1828 | C:\Windows\system32\MsiExec.exe -Embedding 71B251C0FC4EDC6EBBDB96E9DC13381E | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
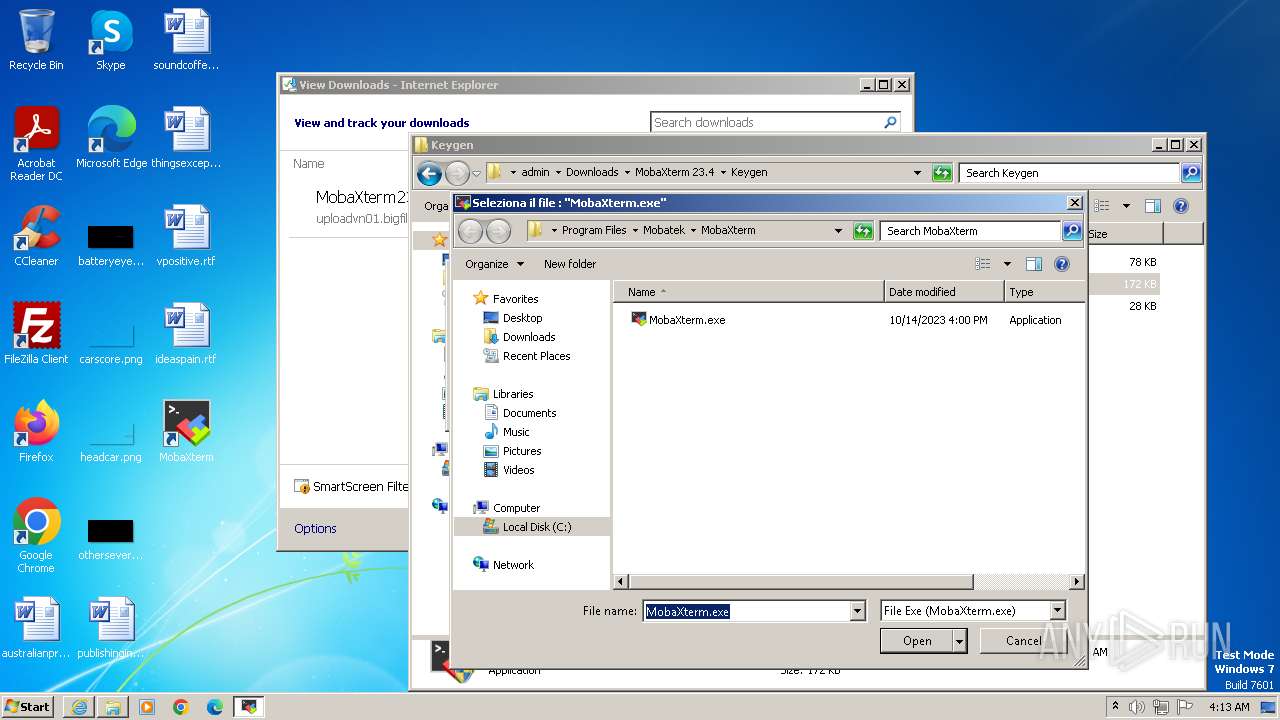
| 1836 | "C:\Users\admin\Downloads\MobaXterm 23.4\Keygen\MobaXterm_Keygen_v1.5_By_DeltaFoX.exe" | C:\Users\admin\Downloads\MobaXterm 23.4\Keygen\MobaXterm_Keygen_v1.5_By_DeltaFoX.exe | explorer.exe | ||||||||||||
User: admin Company: DeFconX Integrity Level: HIGH Description: MobaXterm_Keygen Exit code: 0 Version: 1.5.0.0 Modules
| |||||||||||||||
| 1992 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\MobaXterm 23.4\Keygen\Keygen_v1.5_By_DeltaFoX.rar" "C:\Users\admin\Downloads\MobaXterm 23.4\Keygen\" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
37 239
Read events
37 018
Write events
207
Delete events
14
Modification events
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3240) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
258
Suspicious files
766
Text files
1 092
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:4506AE01710CBB140C670288B87668B2 | SHA256:96A0A0F0775661CB4ED2A36A0C9CE30CA81E44C8C849CD6131E62882FDC45AD8 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab6EED.tmp | compressed | |
MD5:F3441B8572AAE8801C04F3060B550443 | SHA256:6720349E7D82EE0A8E73920D3C2B7CB2912D9FCF2EDB6FD98F2F12820158B0BF | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar6EEC.tmp | binary | |
MD5:9441737383D21192400ECA82FDA910EC | SHA256:BC3A6E84E41FAEB57E7C21AA3B60C2A64777107009727C5B7C0ED8FE658909E5 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:60FE01DF86BE2E5331B0CDBE86165686 | SHA256:C08CCBC876CD5A7CDFA9670F9637DA57F6A1282198A9BC71FC7D7247A6E5B7A8 | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:98EC6D366AEE642E640795AB591F8C80 | SHA256:A3480FAECE3B538C6F1EB2FE41ACA6638969200CC3D8131D1BA1BD5780F070C8 | |||
| 3908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF174f58.TMP | — | |
MD5:— | SHA256:— | |||
| 3908 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3156 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\BC63673E946DC3D5C94300B2EE572DF8 | binary | |
MD5:63B3D86E28C75F50B32FC02A5269A566 | SHA256:542B9157296E7B2C4E373CD0EE745E82E3DC8C3A8650A6F4E0A4BDF6A8E9537A | |||
| 3240 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:2D5F710C1FB3BE7CFE90C201301B4F23 | SHA256:80600F10C4E33ACF7D494C5C962550D281CF5B51B6666A8D934D4639FA8498D7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
29
DNS requests
22
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3156 | iexplore.exe | GET | 200 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?2747dc4fd30729d5 | unknown | compressed | 4.66 Kb | unknown |
3156 | iexplore.exe | GET | 200 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?004031d42616ecc1 | unknown | compressed | 61.6 Kb | unknown |
3156 | iexplore.exe | GET | 200 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?3f99689a7126e91f | unknown | compressed | 61.6 Kb | unknown |
3156 | iexplore.exe | GET | 200 | 184.24.77.54:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgMXA9cc68JbLBjNTg2PNquUcQ%3D%3D | unknown | binary | 503 b | unknown |
3156 | iexplore.exe | GET | 200 | 23.212.210.158:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3240 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
3240 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
3240 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
3156 | iexplore.exe | GET | 200 | 23.53.40.83:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e94bb274b63b057c | unknown | compressed | 4.66 Kb | unknown |
3240 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3156 | iexplore.exe | 23.53.40.83:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2588 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
3156 | iexplore.exe | 23.212.210.158:80 | x1.c.lencr.org | AKAMAI-AS | AU | unknown |
3156 | iexplore.exe | 184.24.77.54:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3240 | iexplore.exe | 152.199.19.161:443 | iecvlist.microsoft.com | EDGECAST | US | whitelisted |
3240 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4052 | chrome.exe | 142.250.185.67:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com |
| whitelisted |
update.googleapis.com |
| whitelisted |