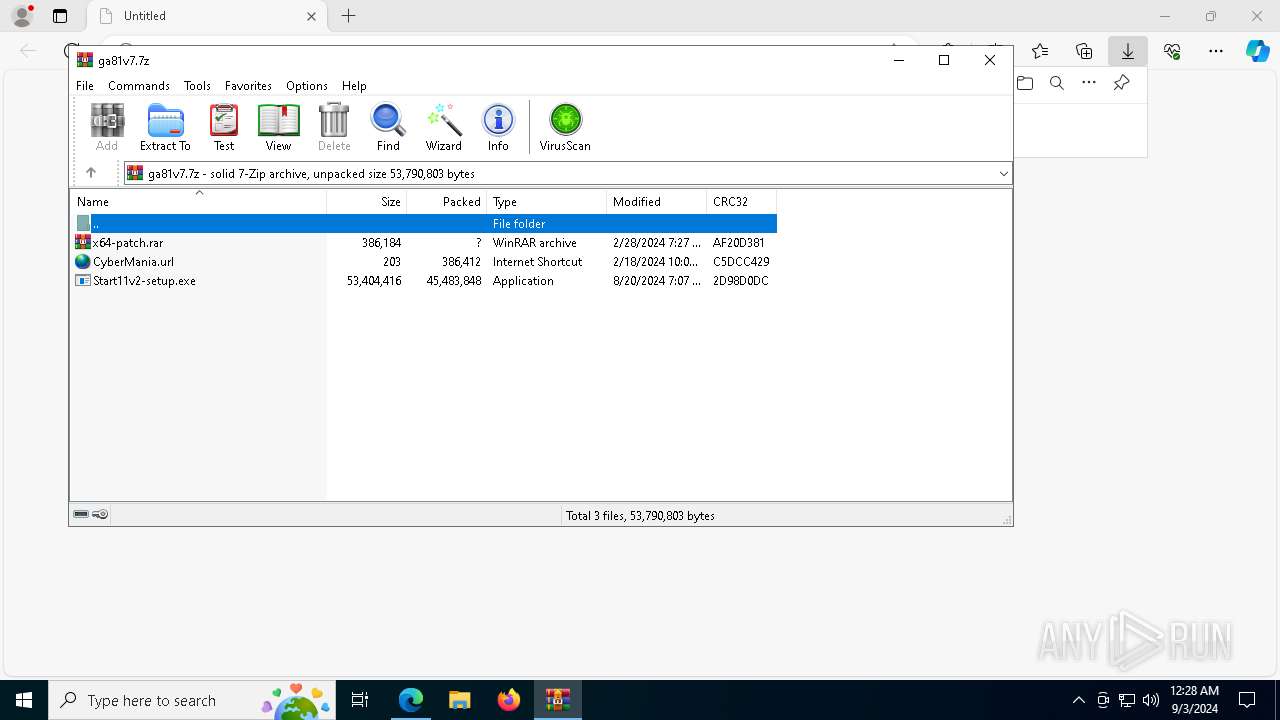
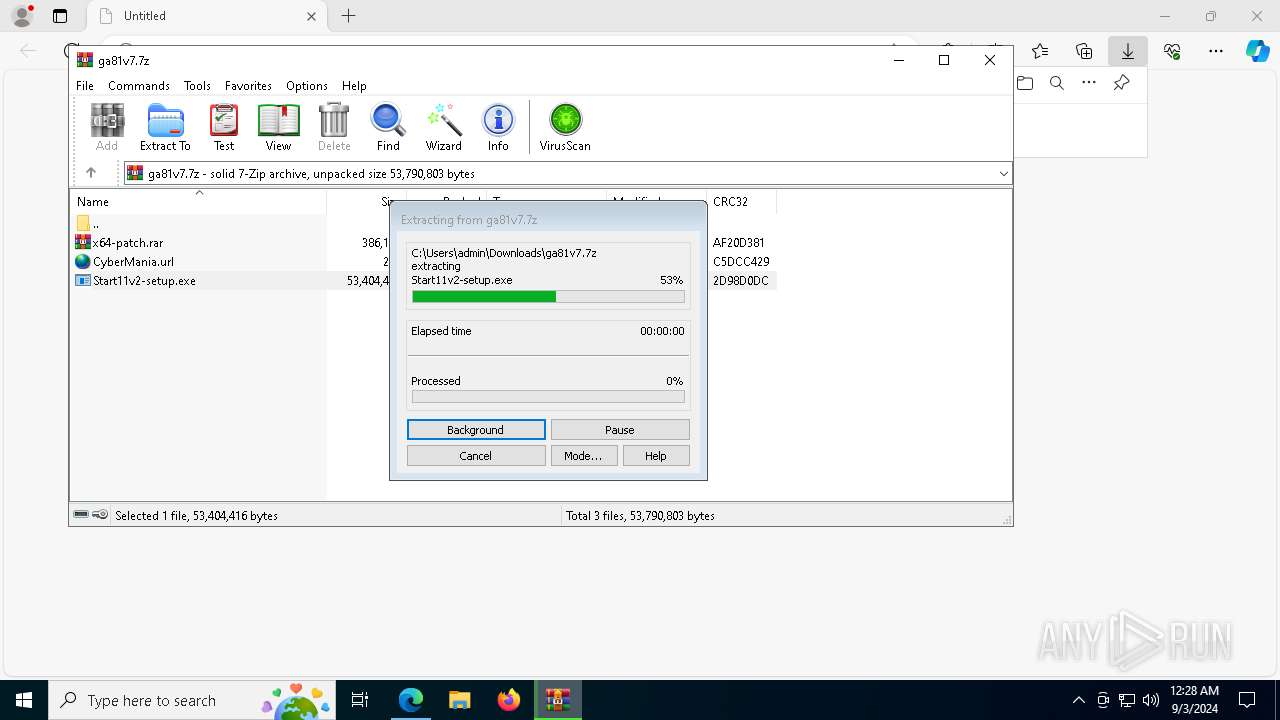
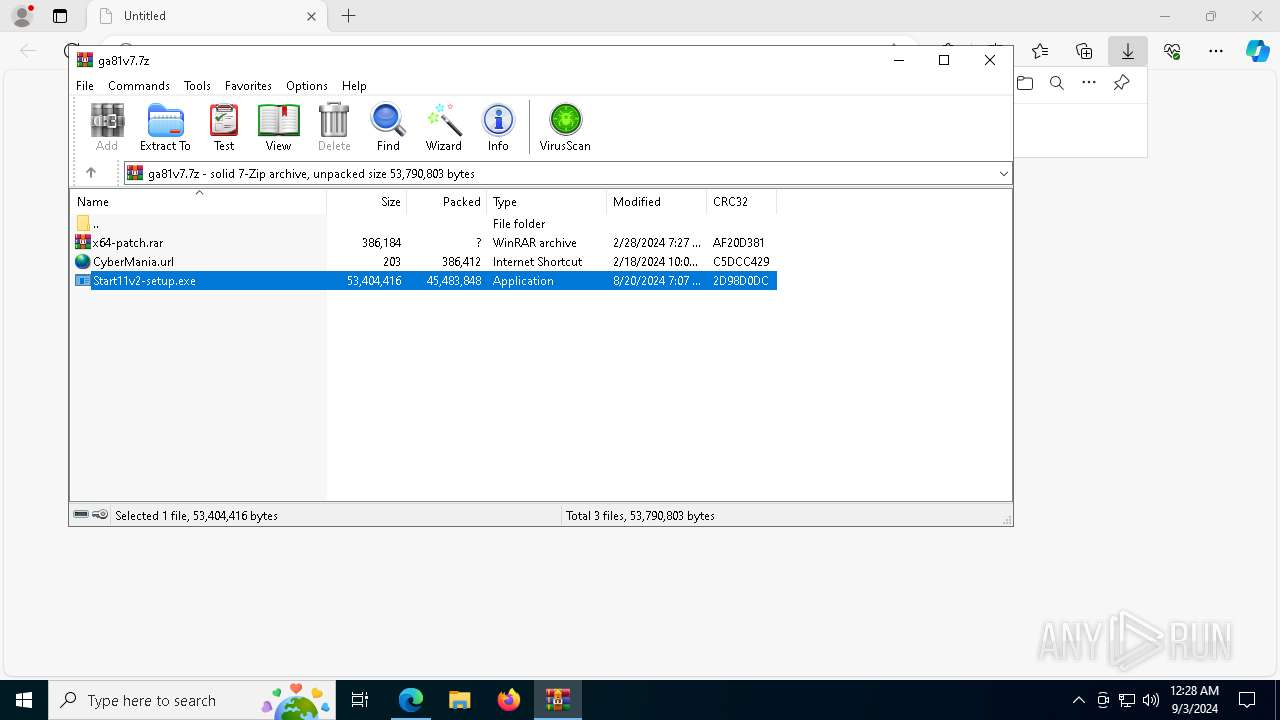
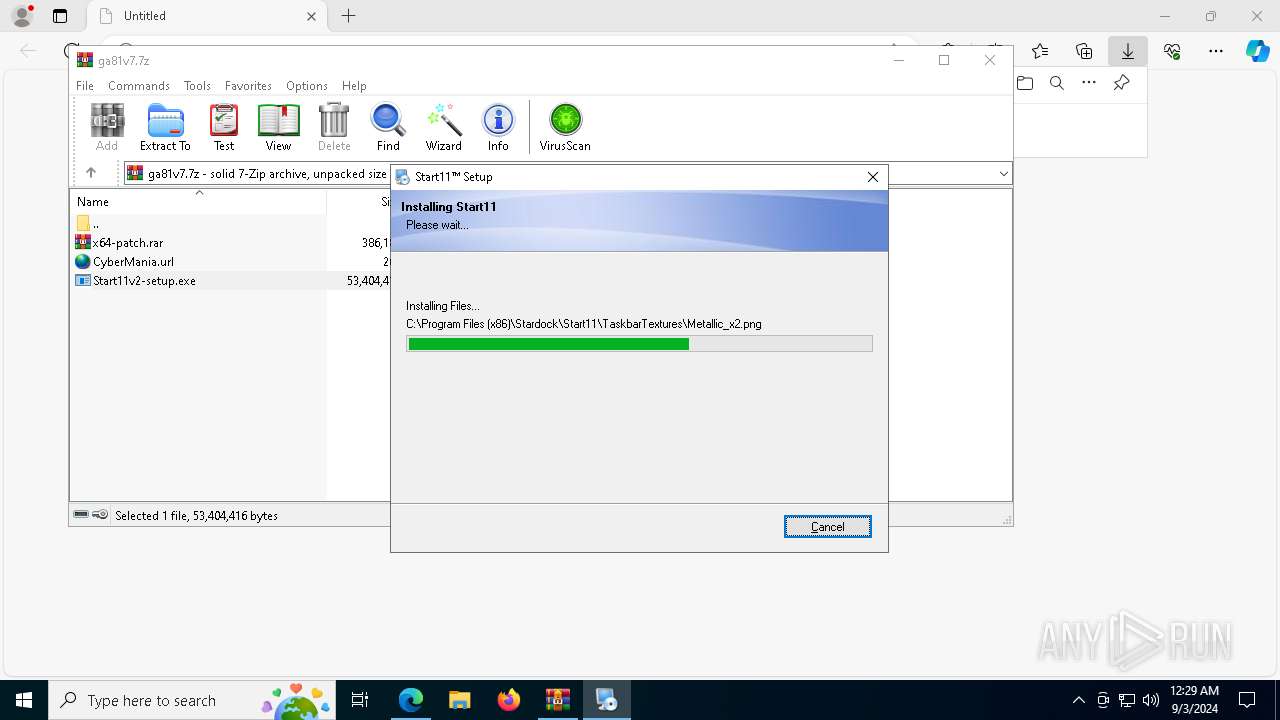
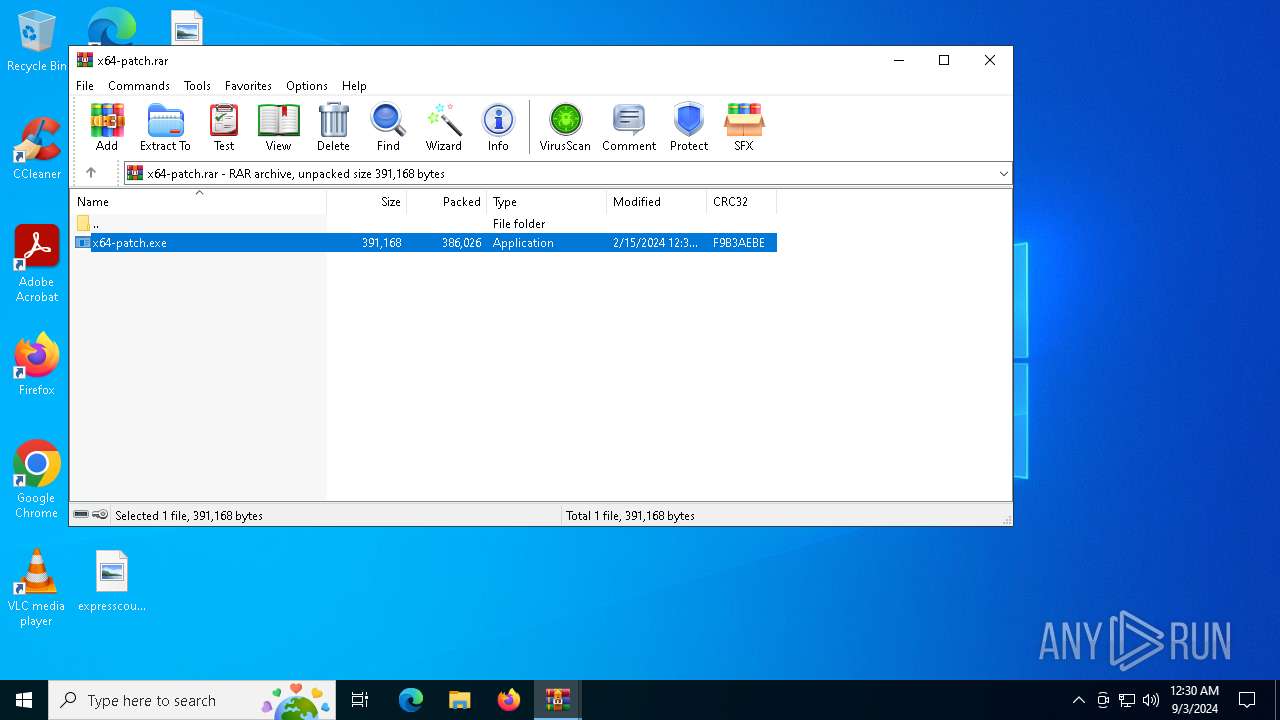
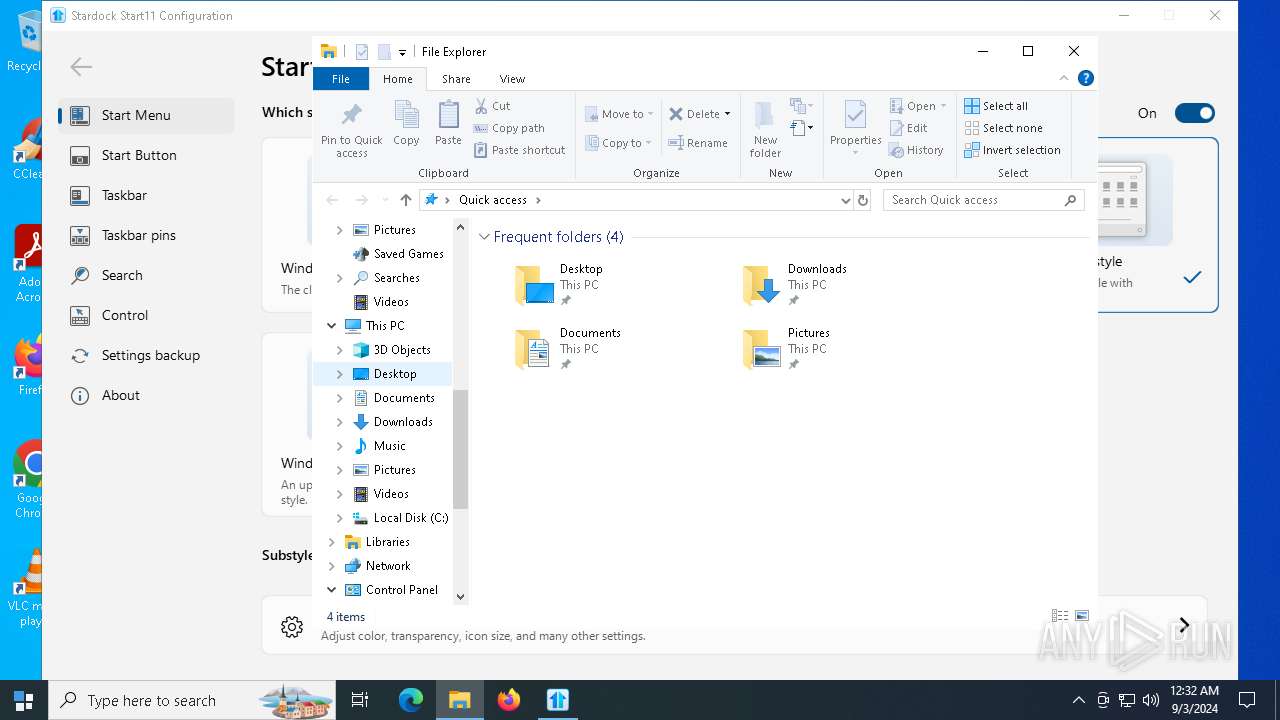
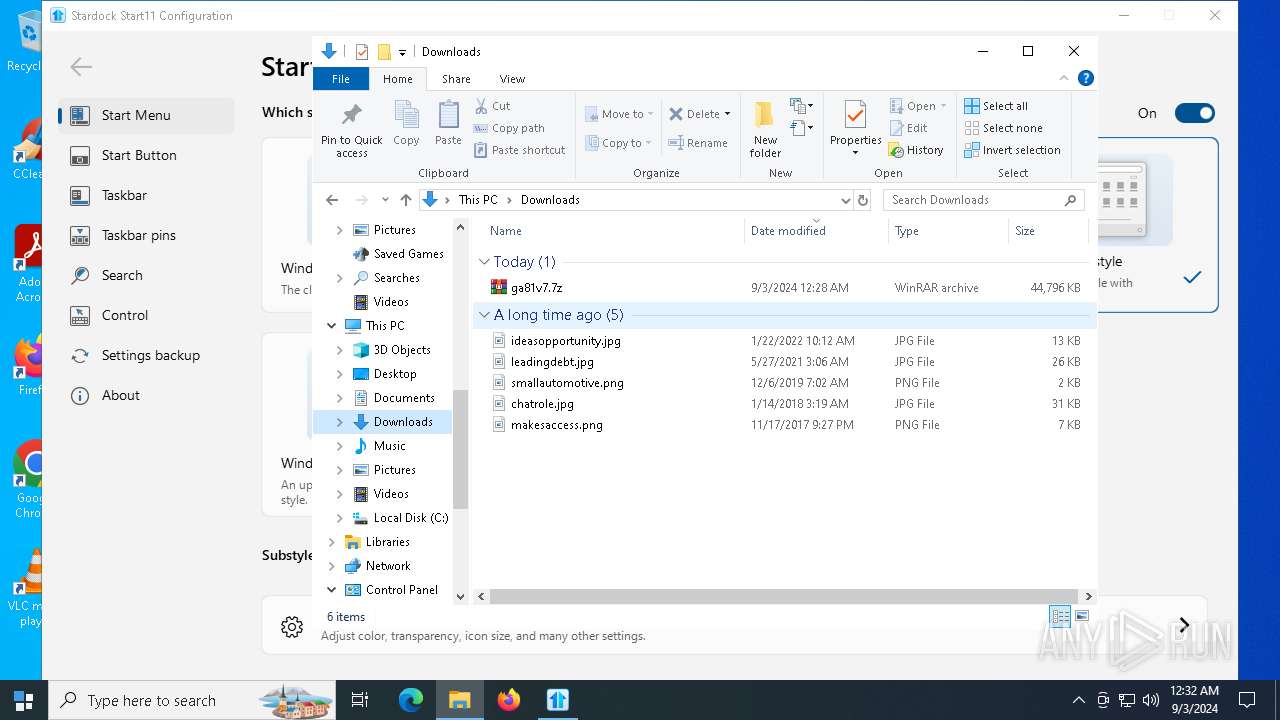
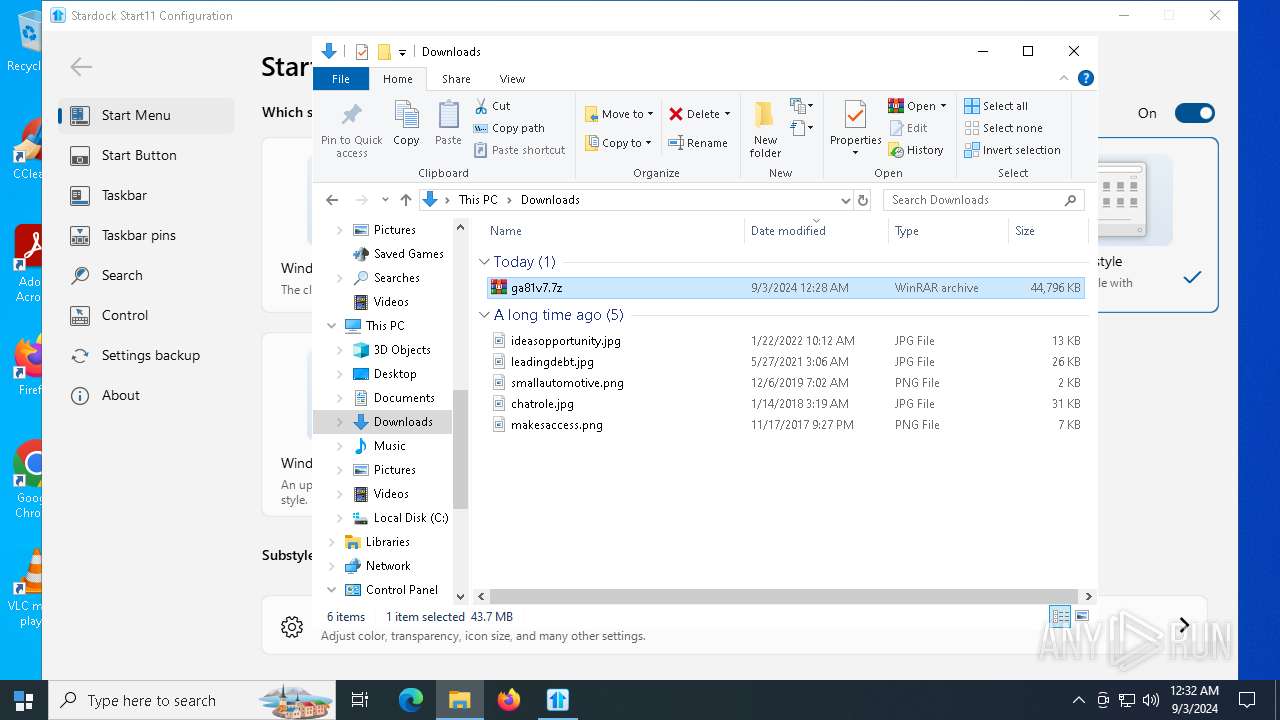
| URL: | https://files.catbox.moe/ga81v7.7z |
| Full analysis: | https://app.any.run/tasks/9273f252-9585-43c0-88fc-00ecf63ddf50 |
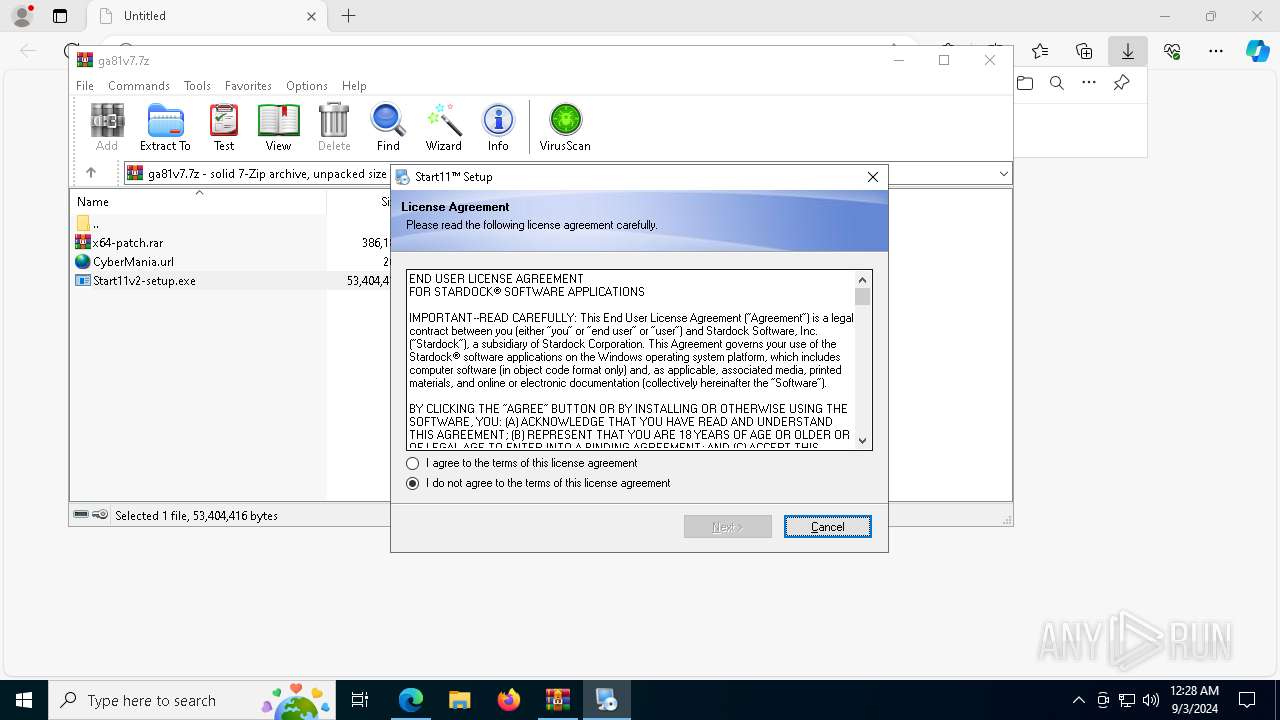
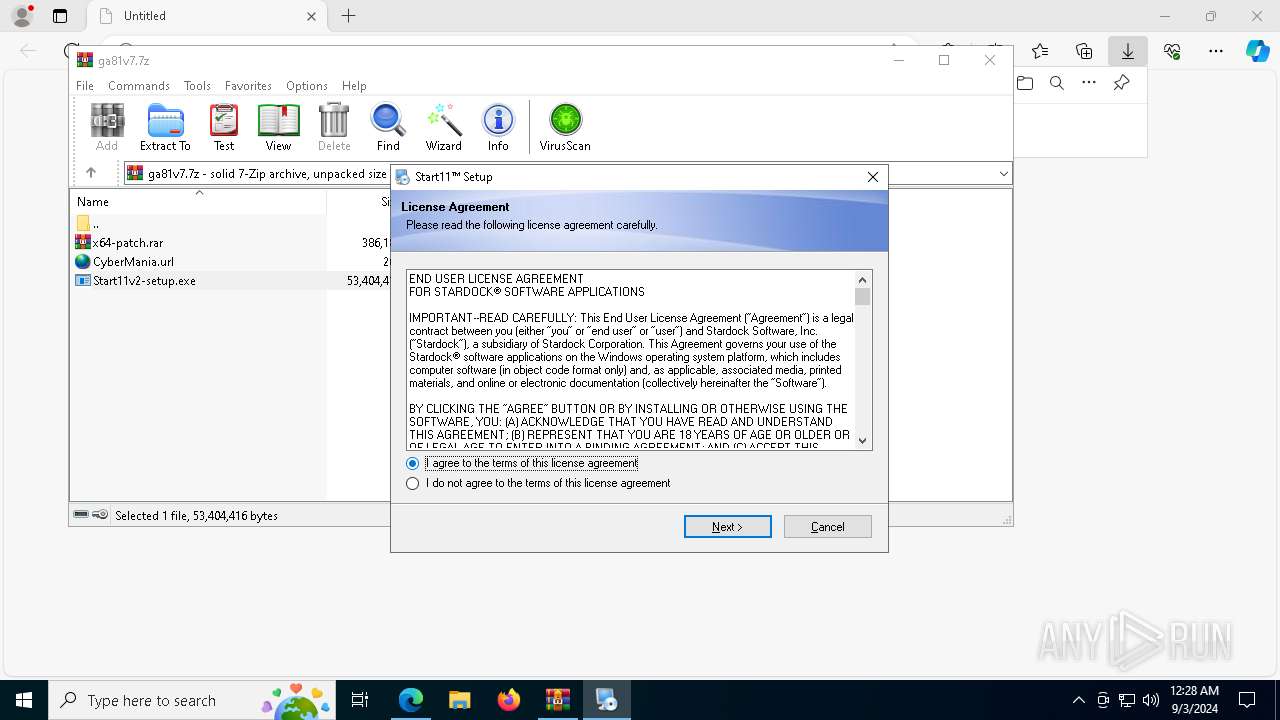
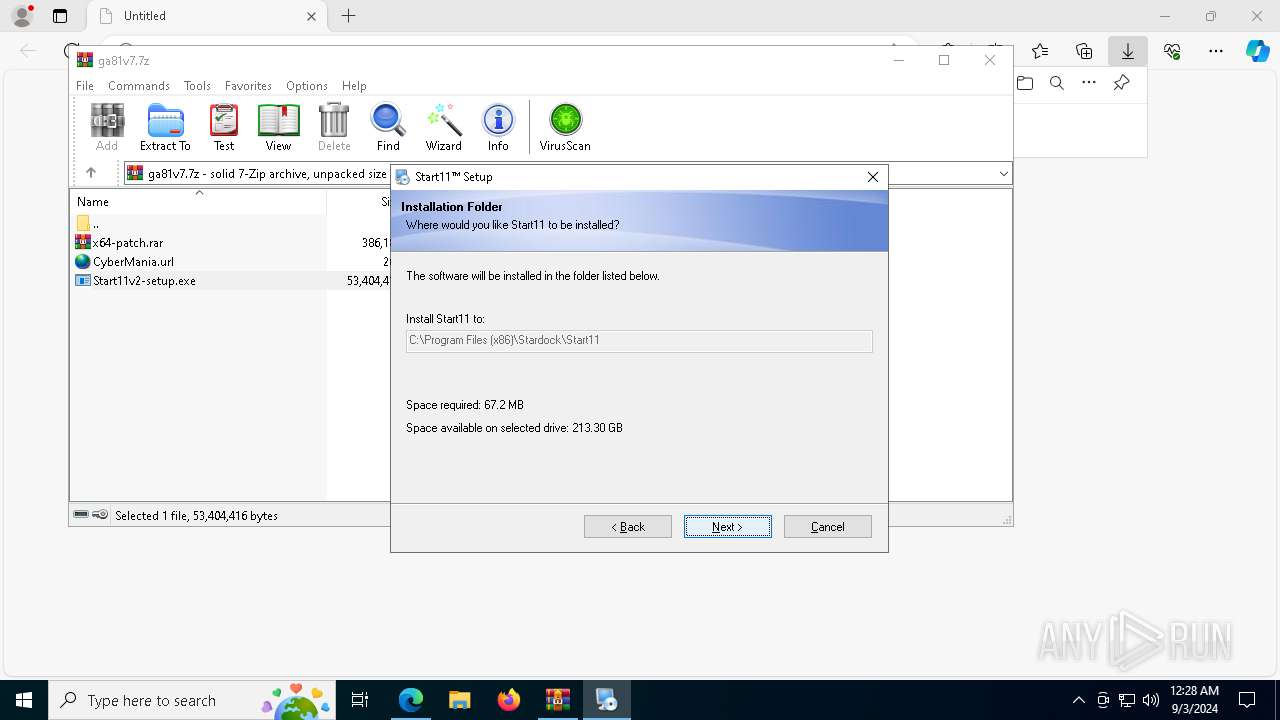
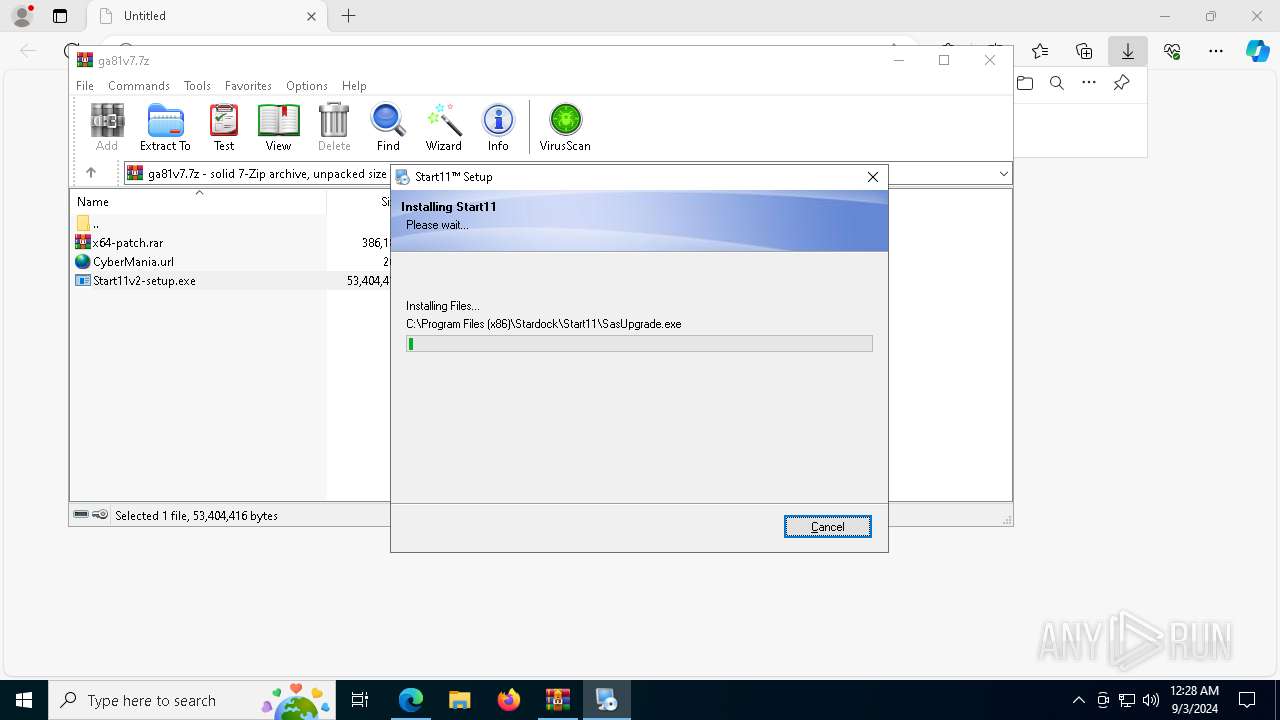
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2024, 00:28:01 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 1E5F5EF404E5E1E0A458720E96F87435 |
| SHA1: | DACD93D6F9741A86903C47454BCBA06E6C9D70AF |
| SHA256: | 2B984E565AB977437E1B0017ECDE19398EA0546C536148FC01DC21123DE30410 |
| SSDEEP: | 3:N8MW3lofn:2MW1ofn |
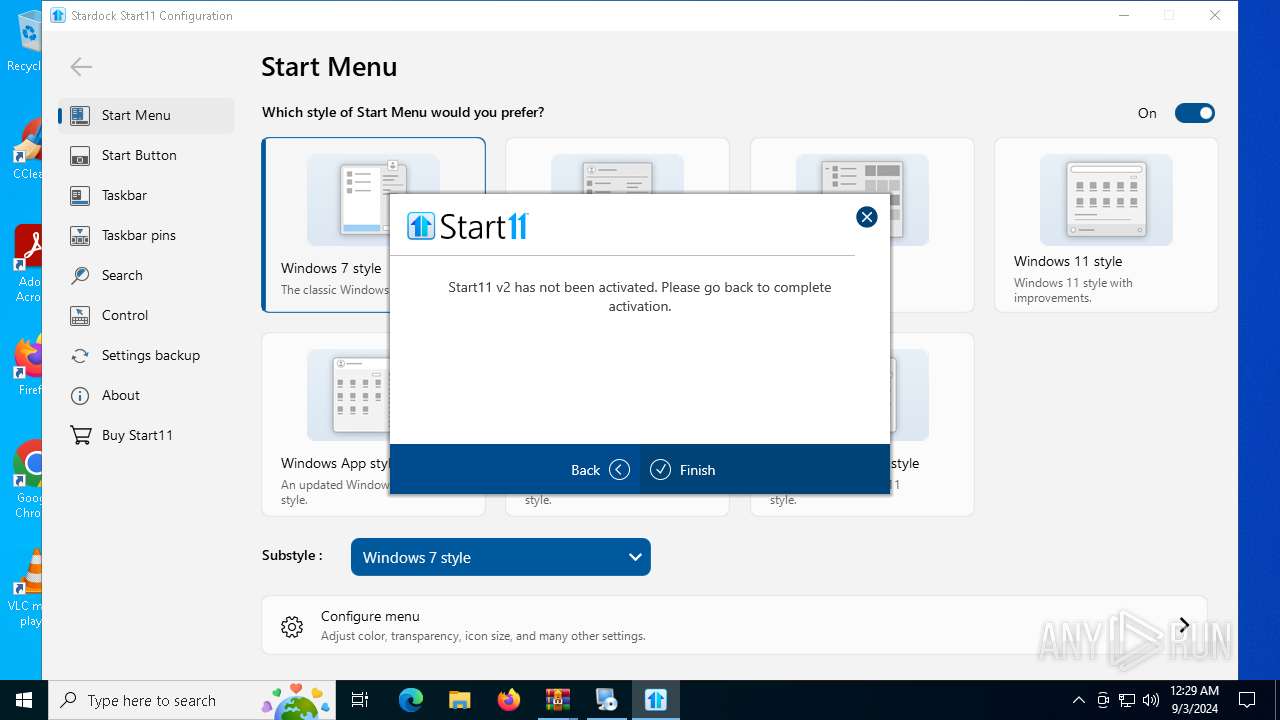
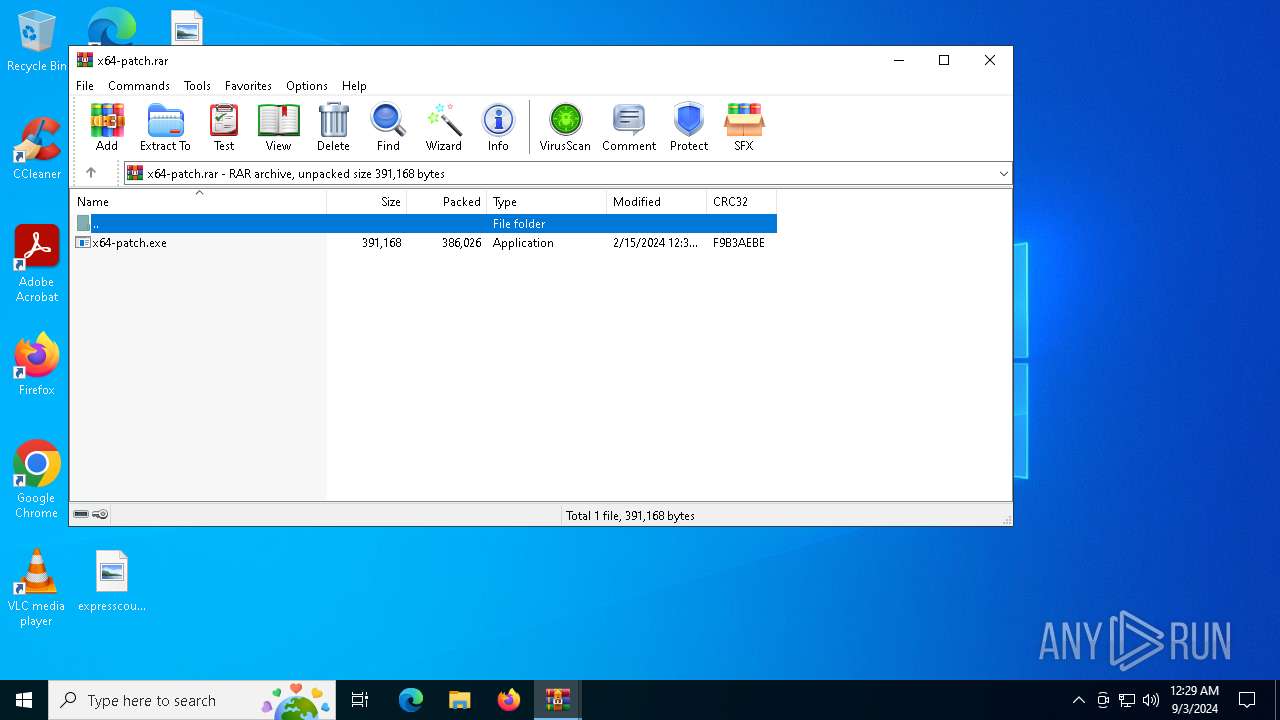
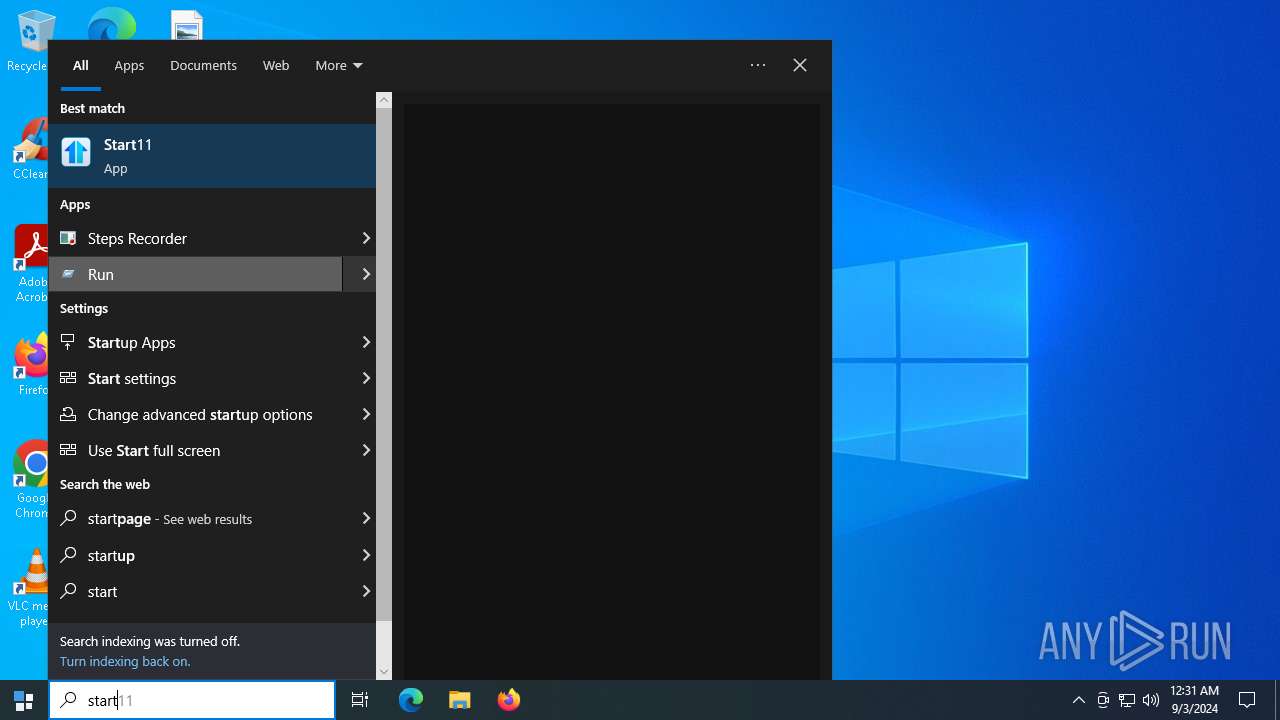
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- irsetup.exe (PID: 2028)
SUSPICIOUS
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 7776)
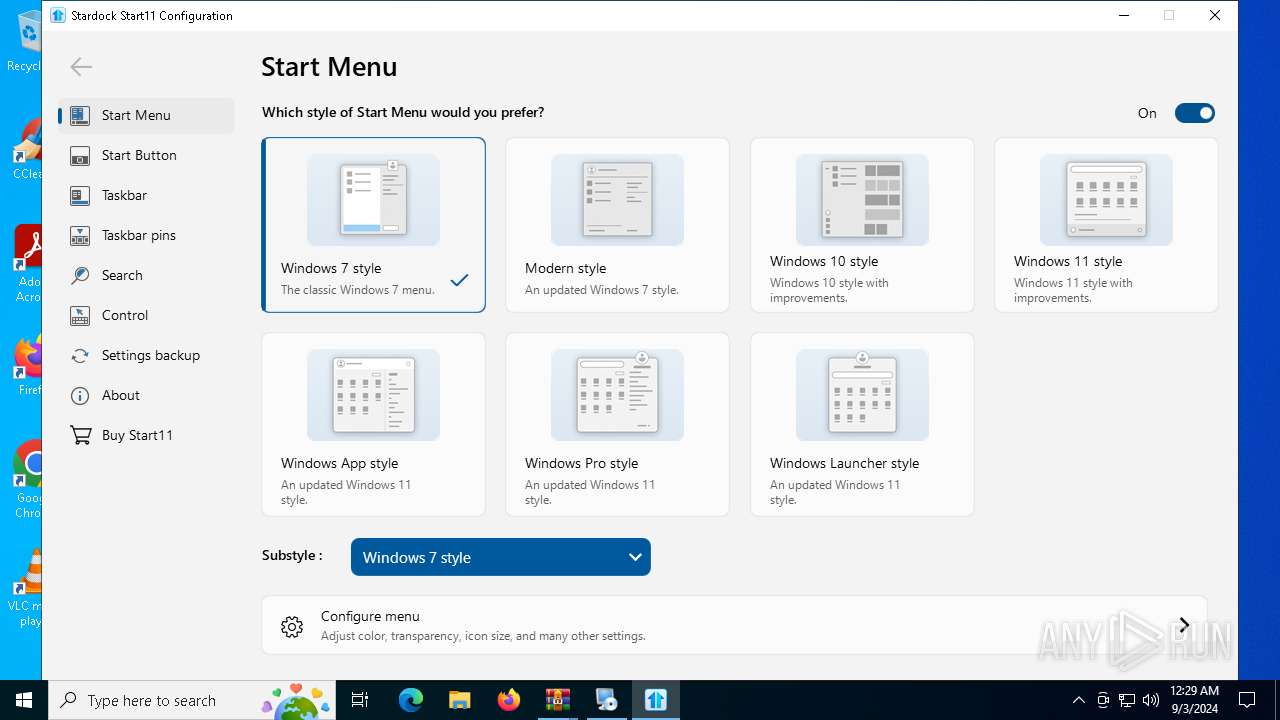
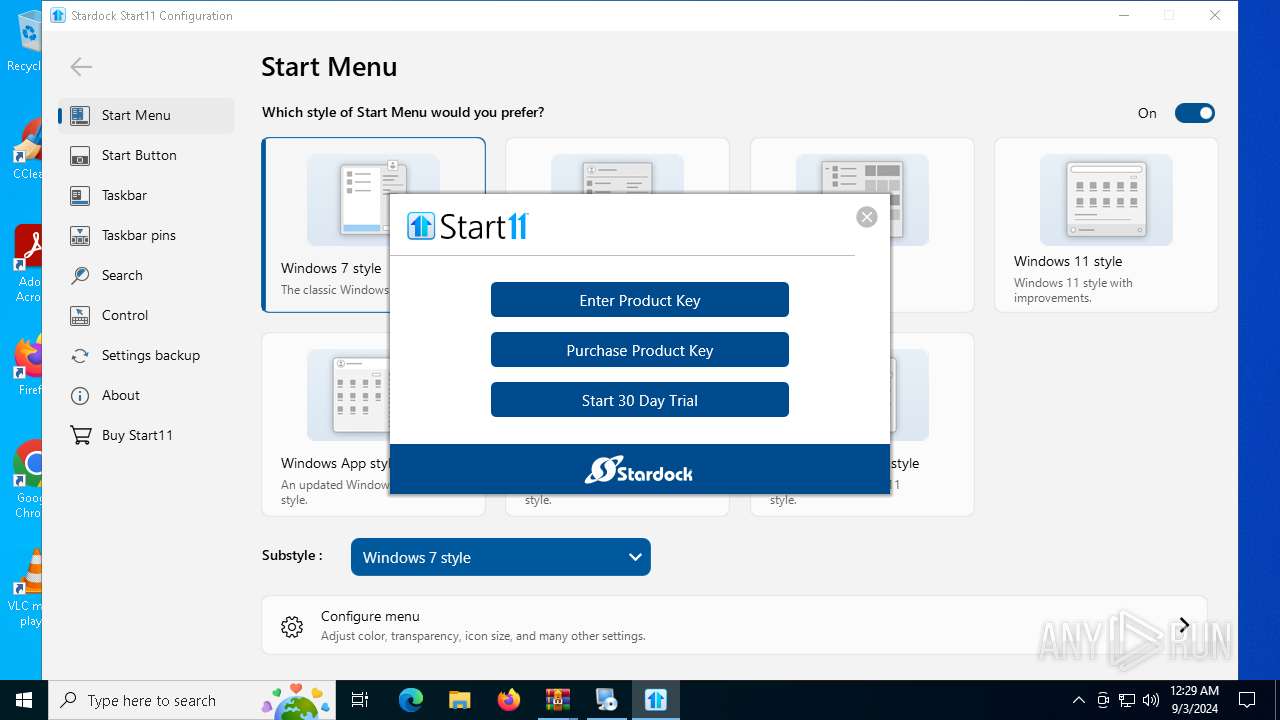
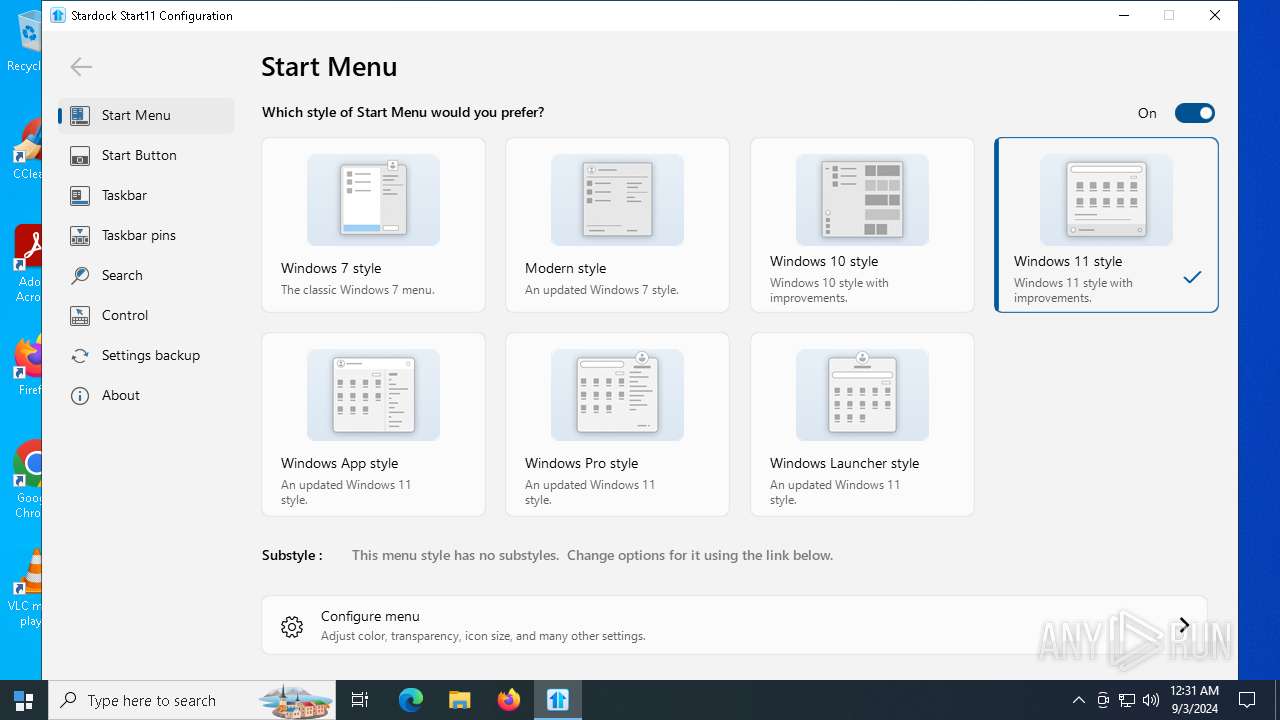
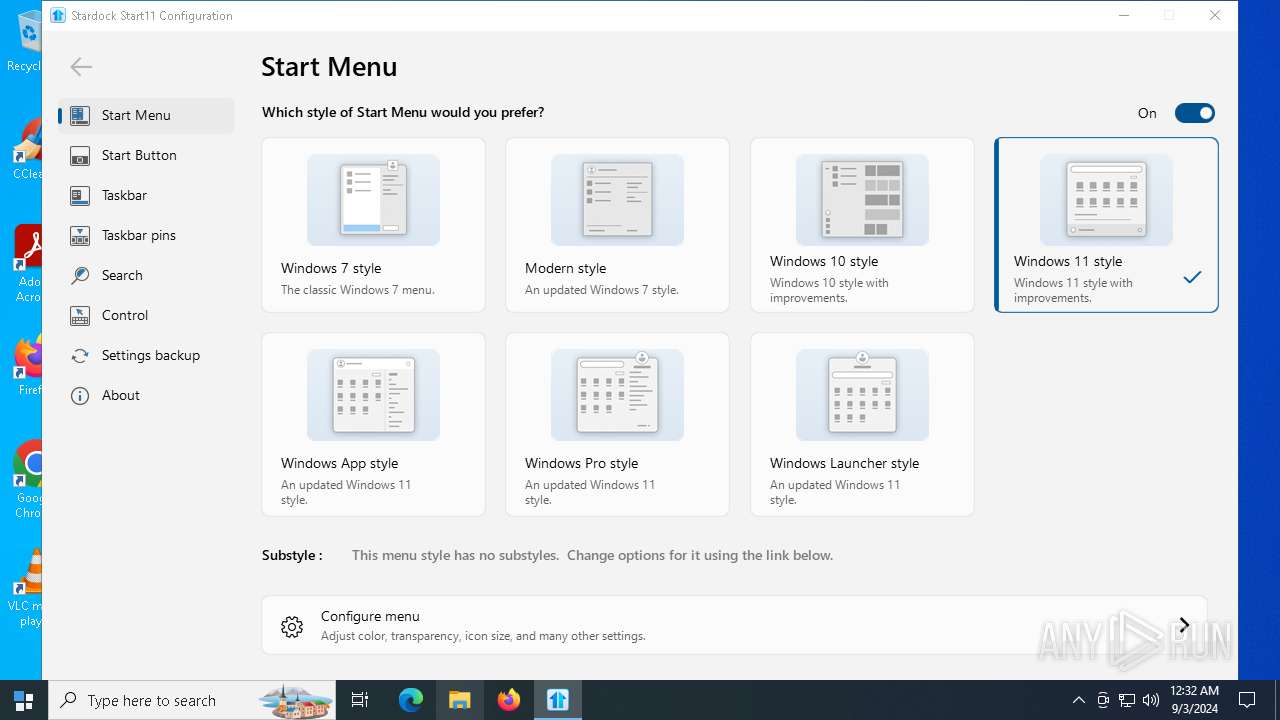
- Start11v2-setup.exe (PID: 3708)
- irsetup.exe (PID: 2028)
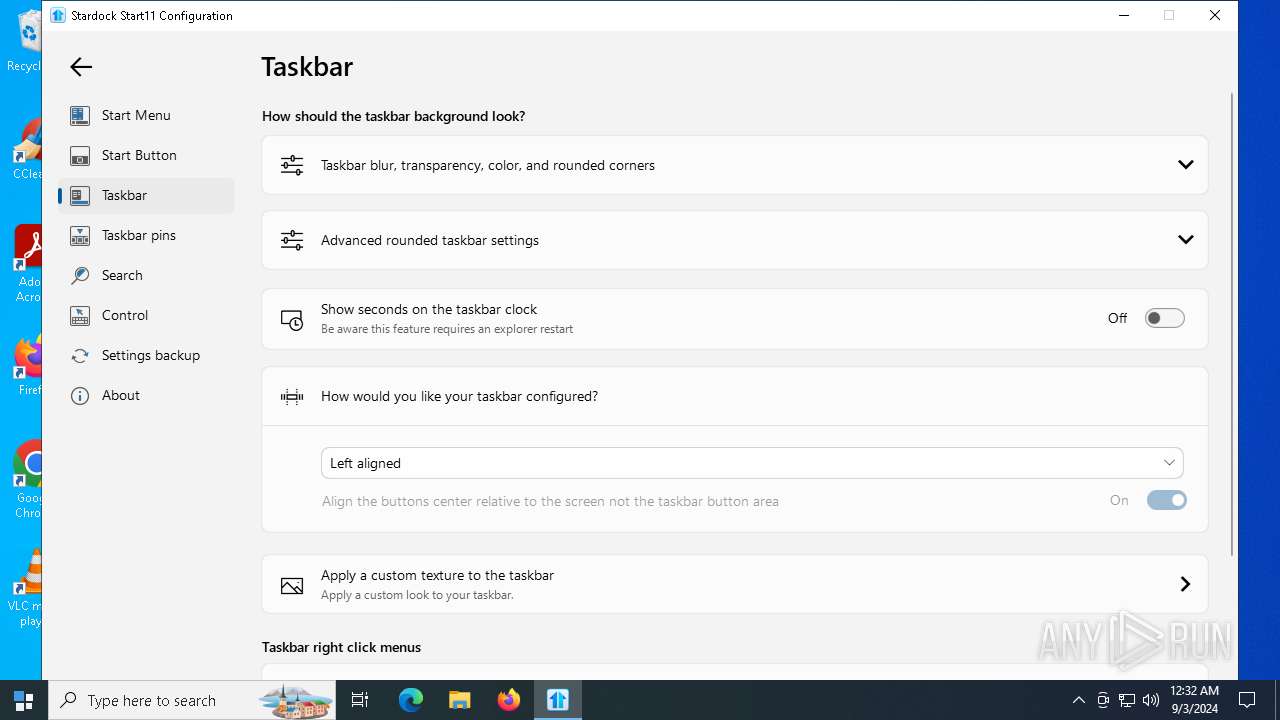
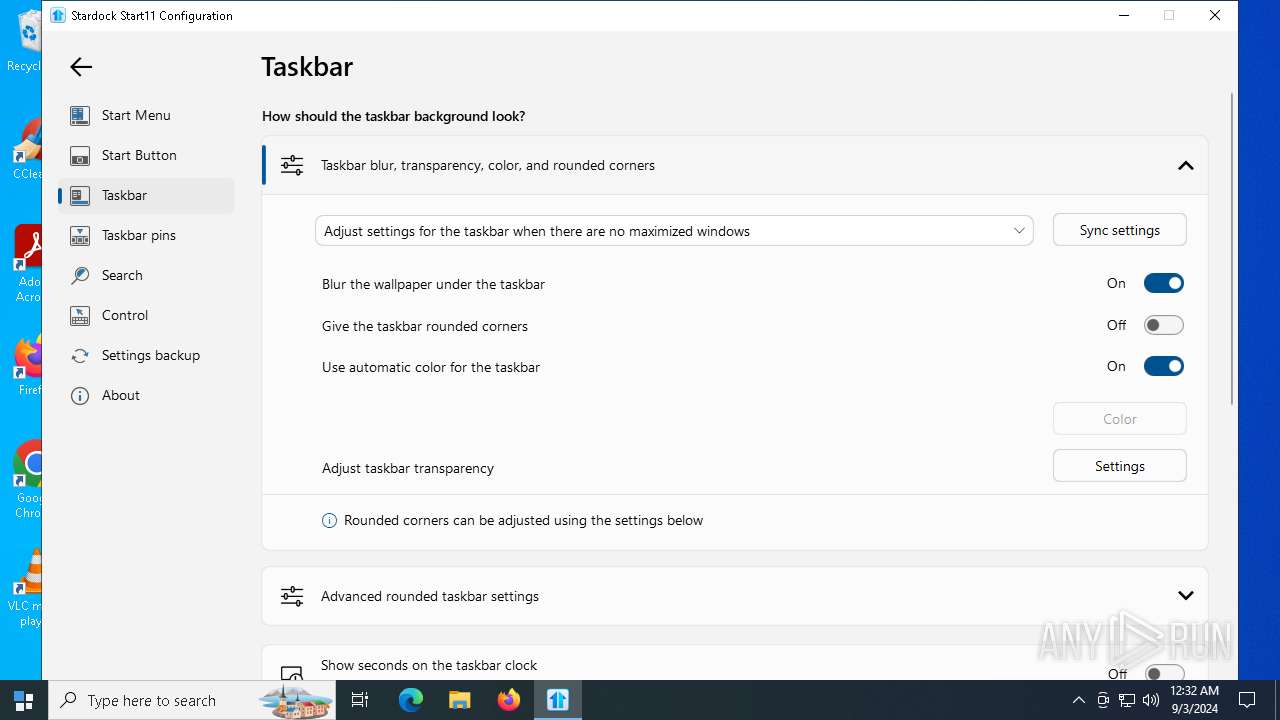
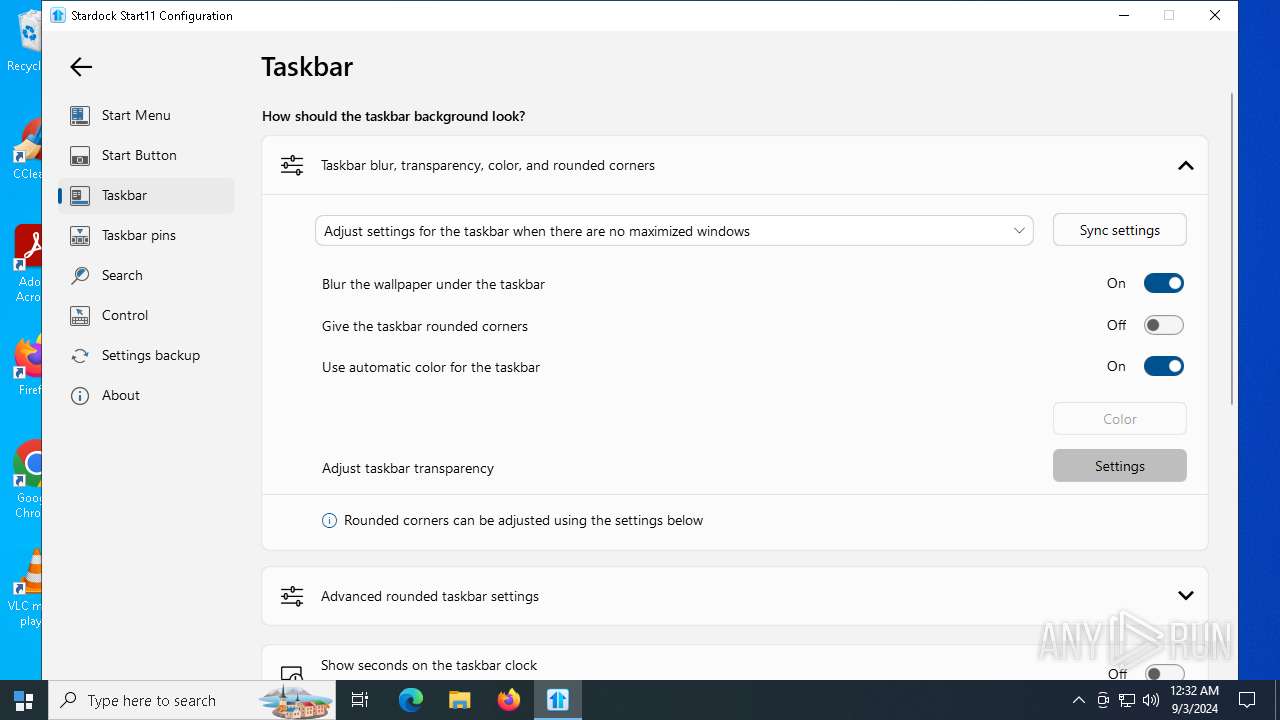
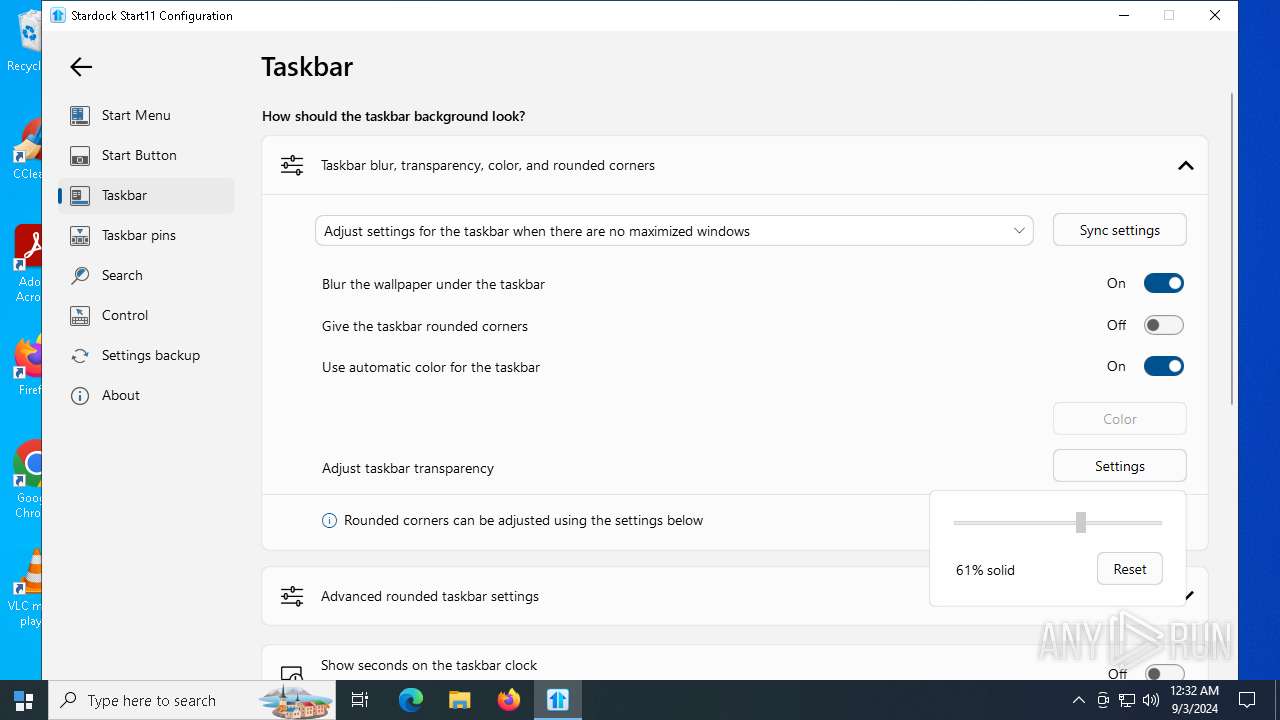
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7288)
- Start11Config.exe (PID: 8060)
- SdDisplay.exe (PID: 7956)
- WinRAR.exe (PID: 3352)
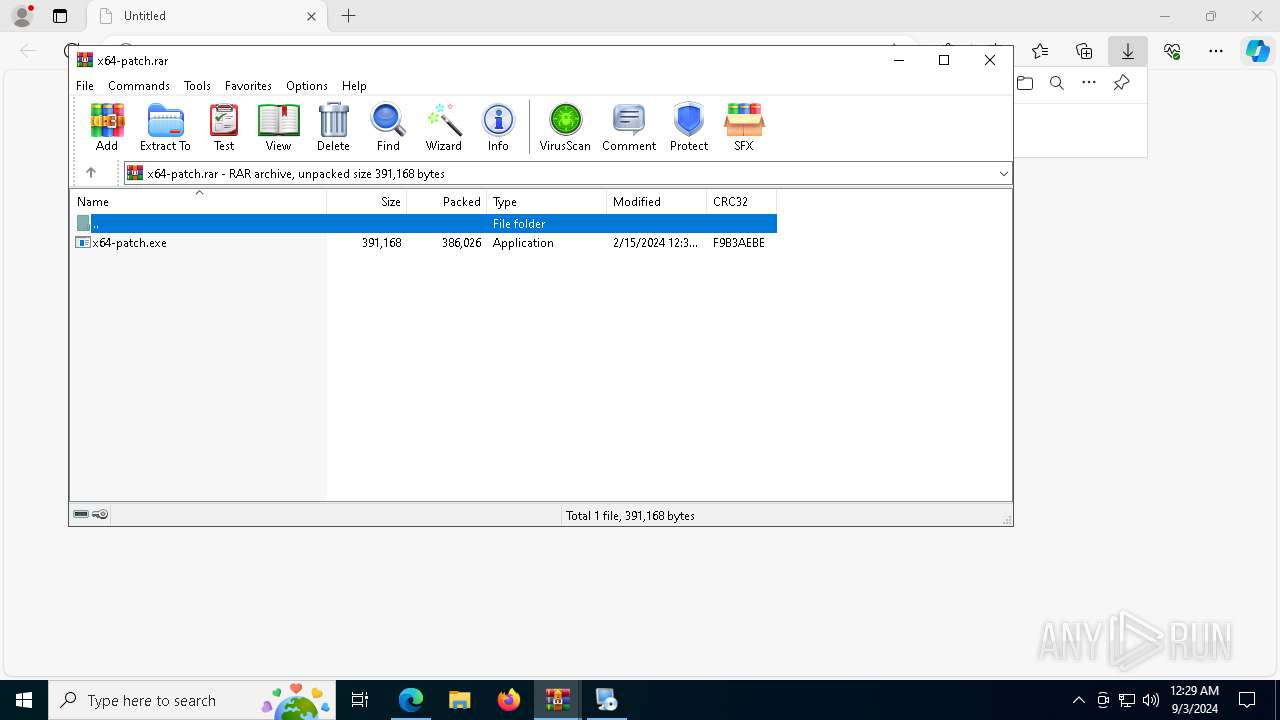
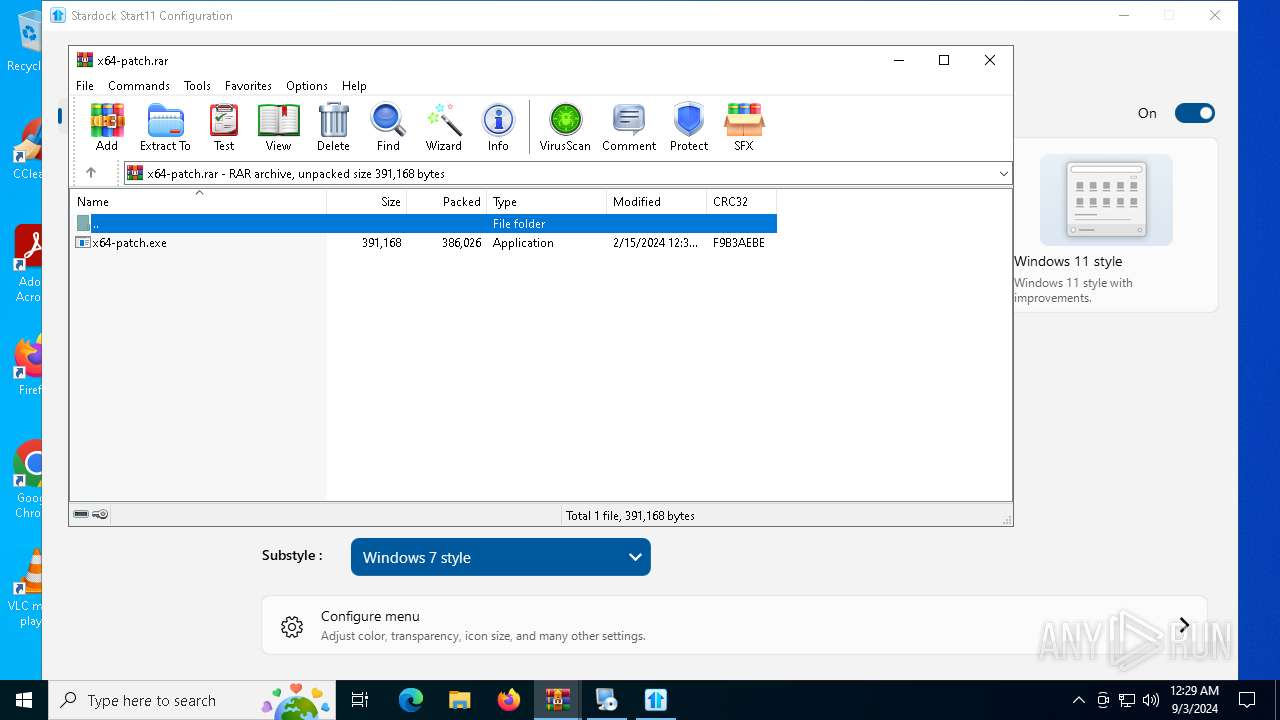
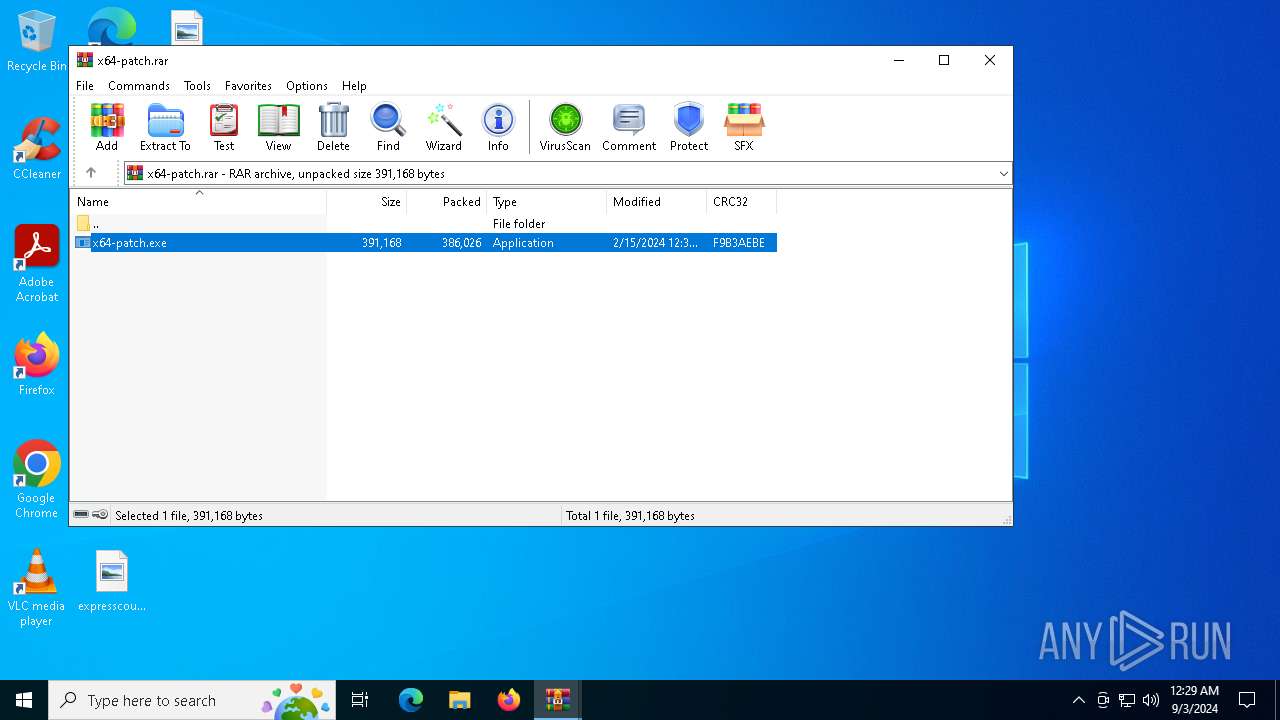
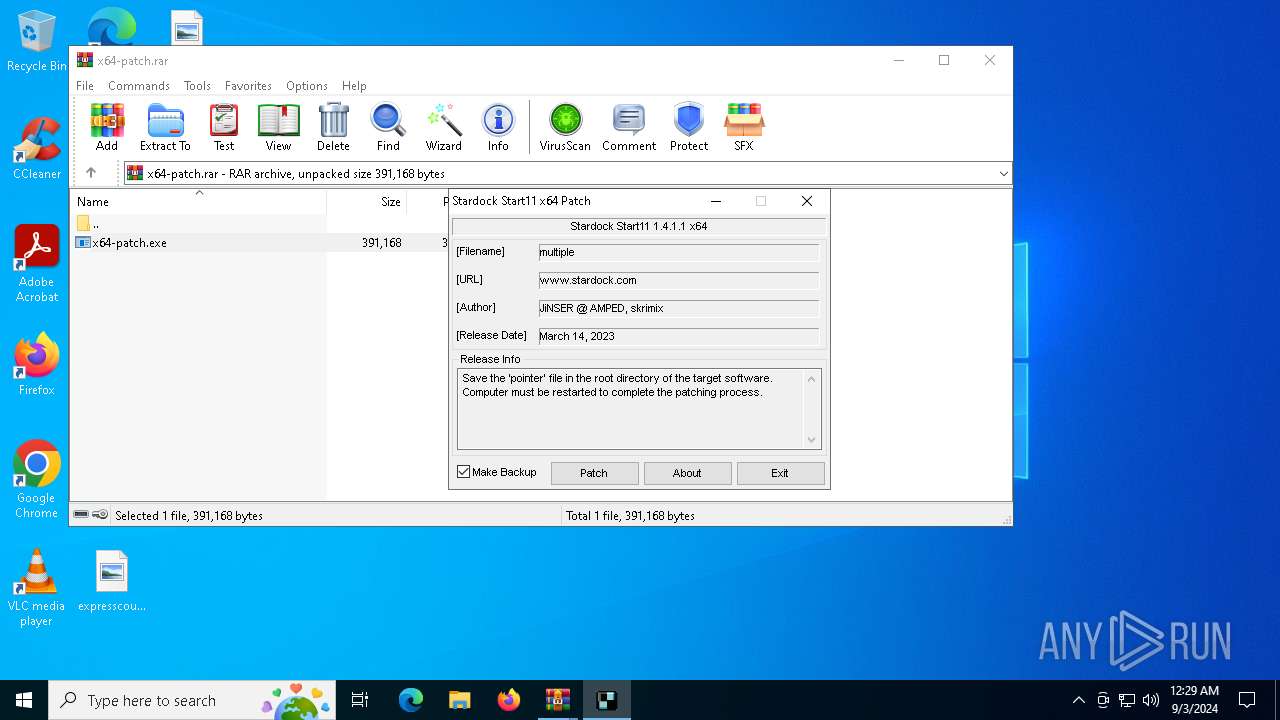
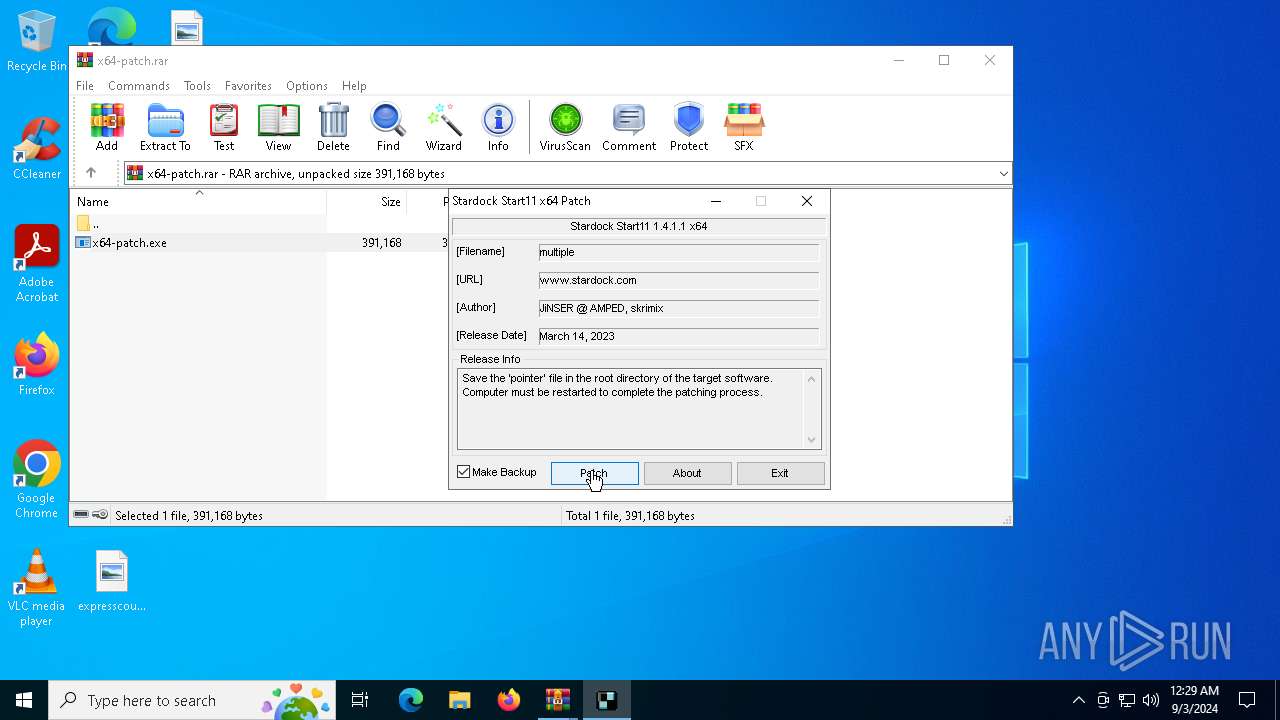
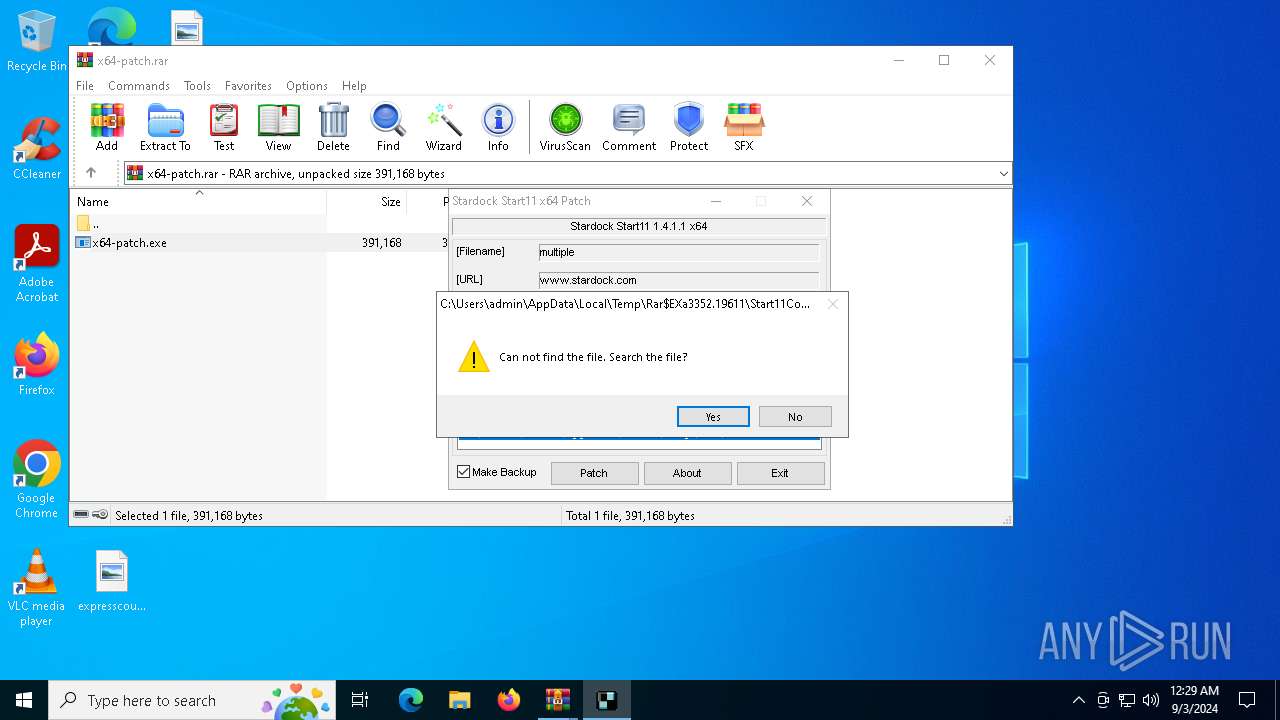
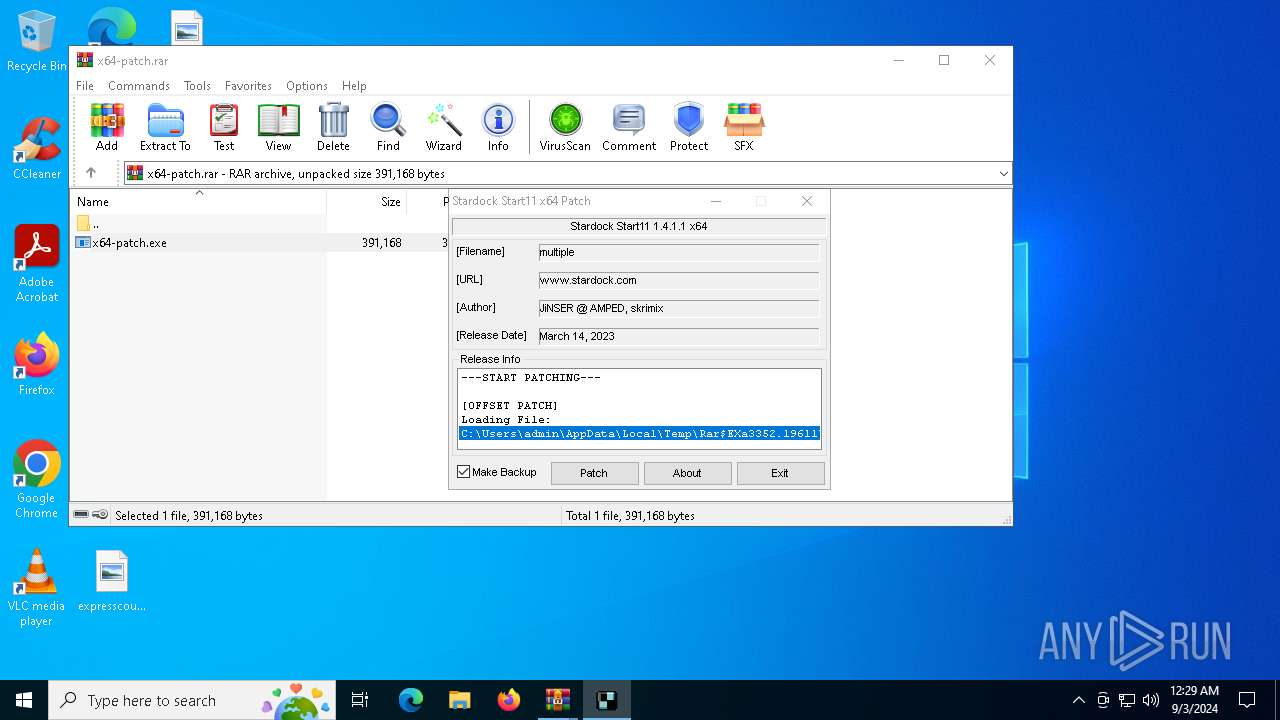
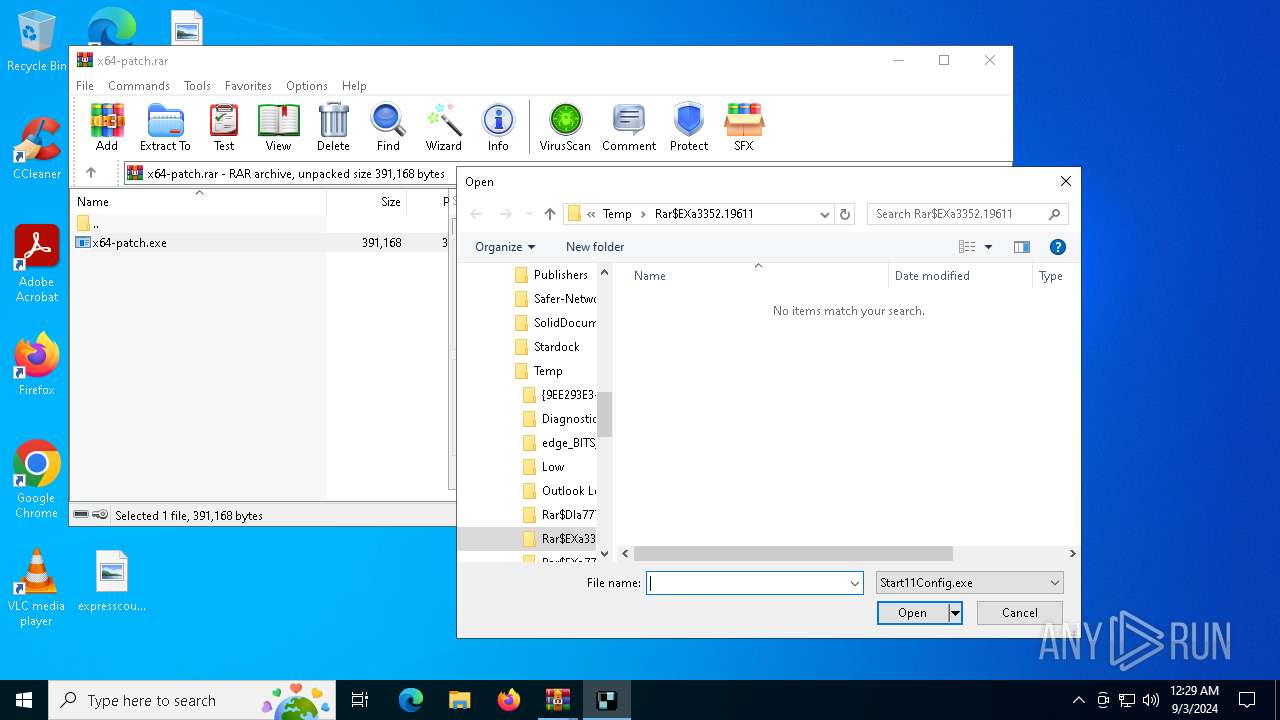
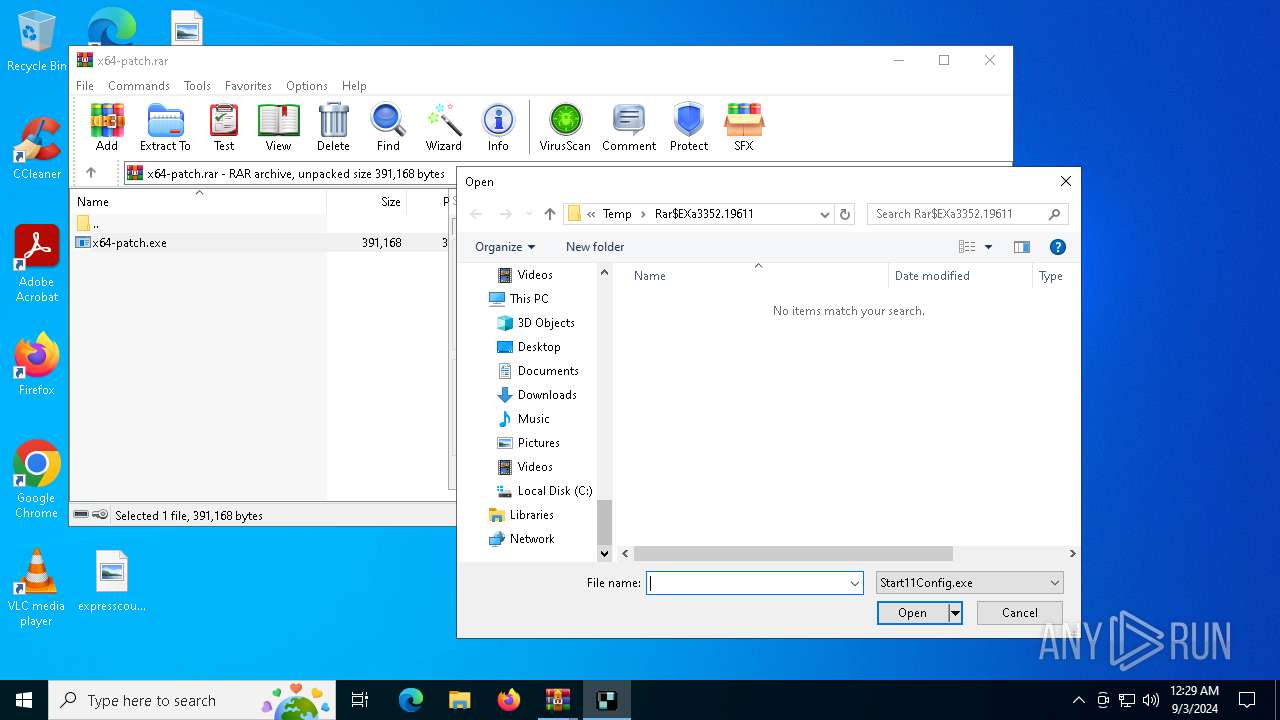
- x64-patch.exe (PID: 5468)
- Start11Config.exe (PID: 3540)
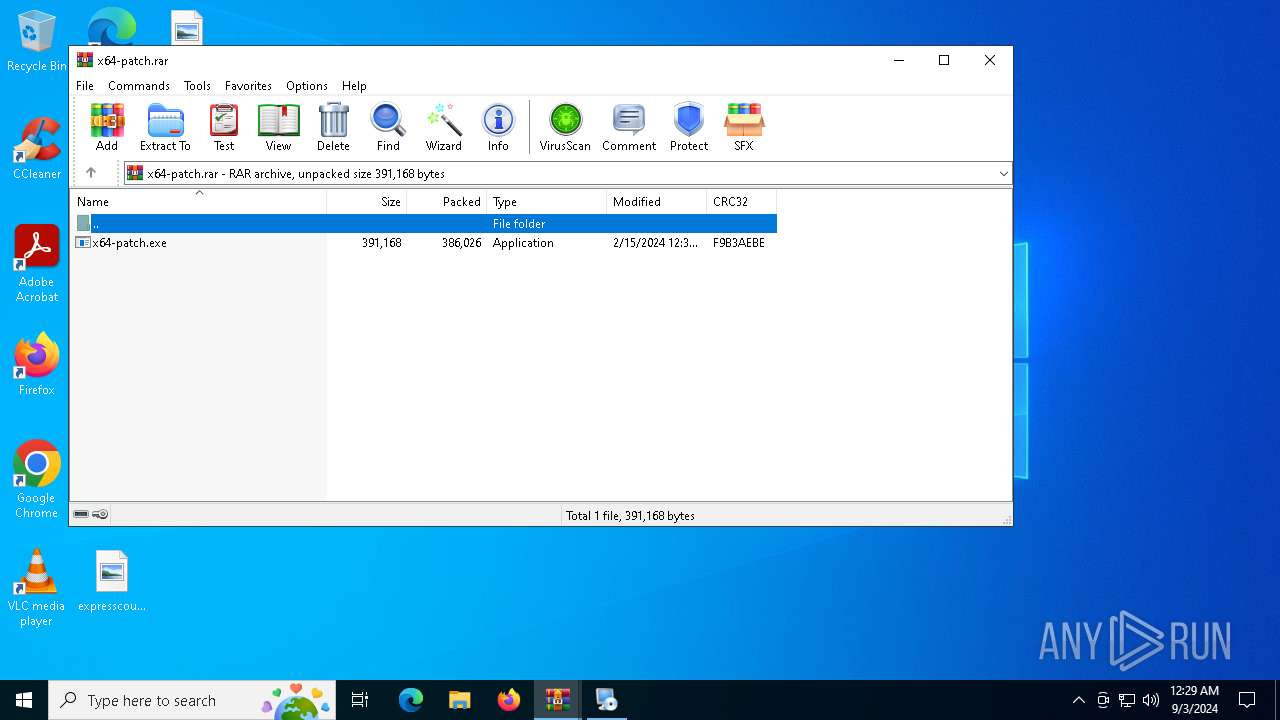
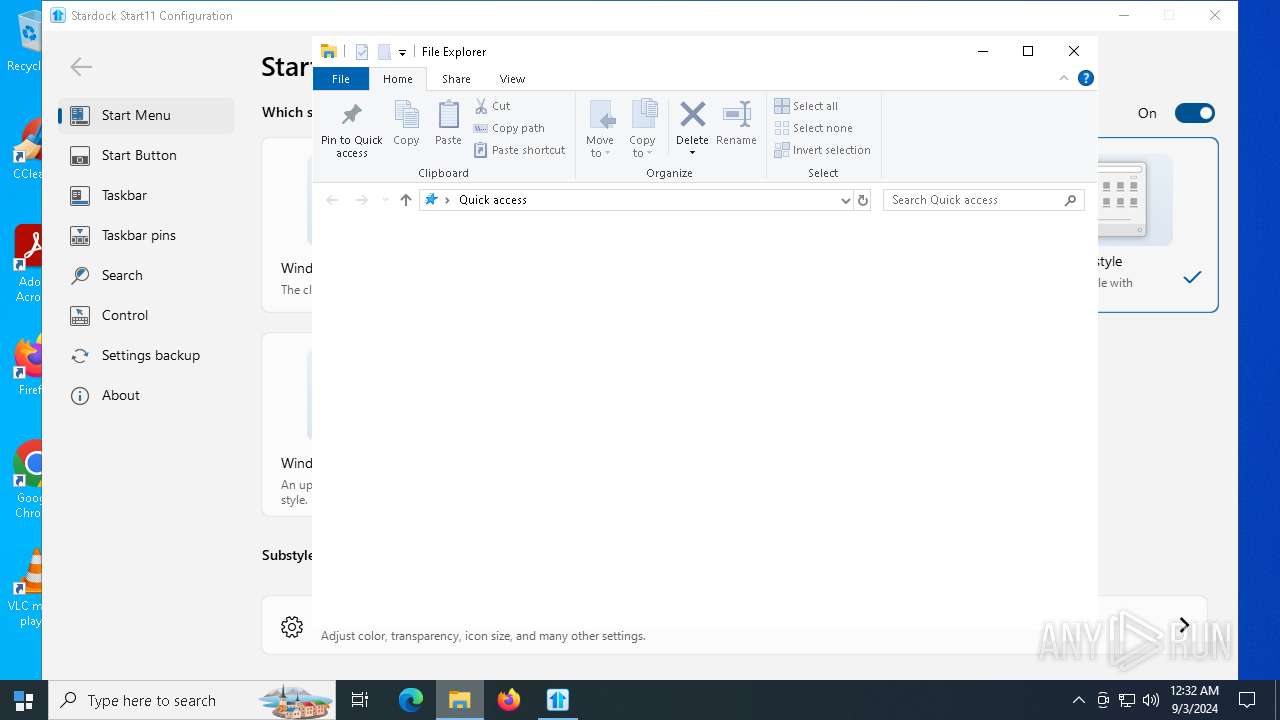
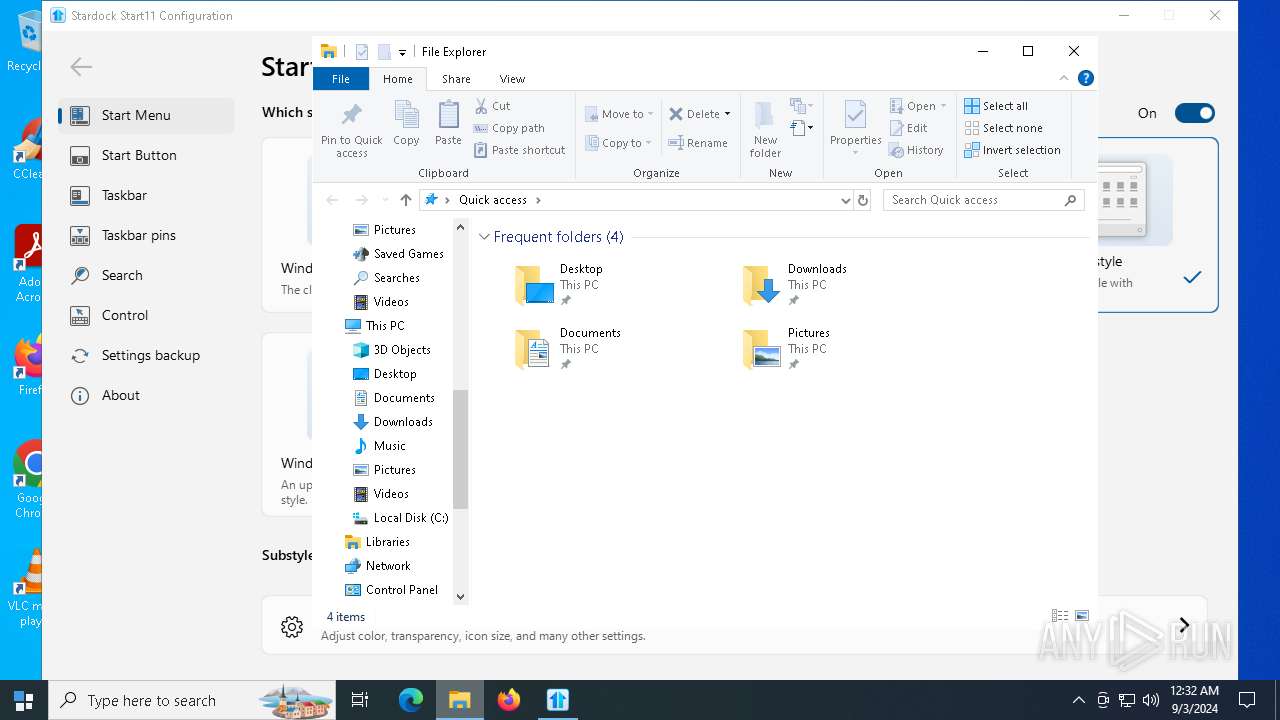
Creates file in the systems drive root
- WinRAR.exe (PID: 7776)
- x64-patch.exe (PID: 5468)
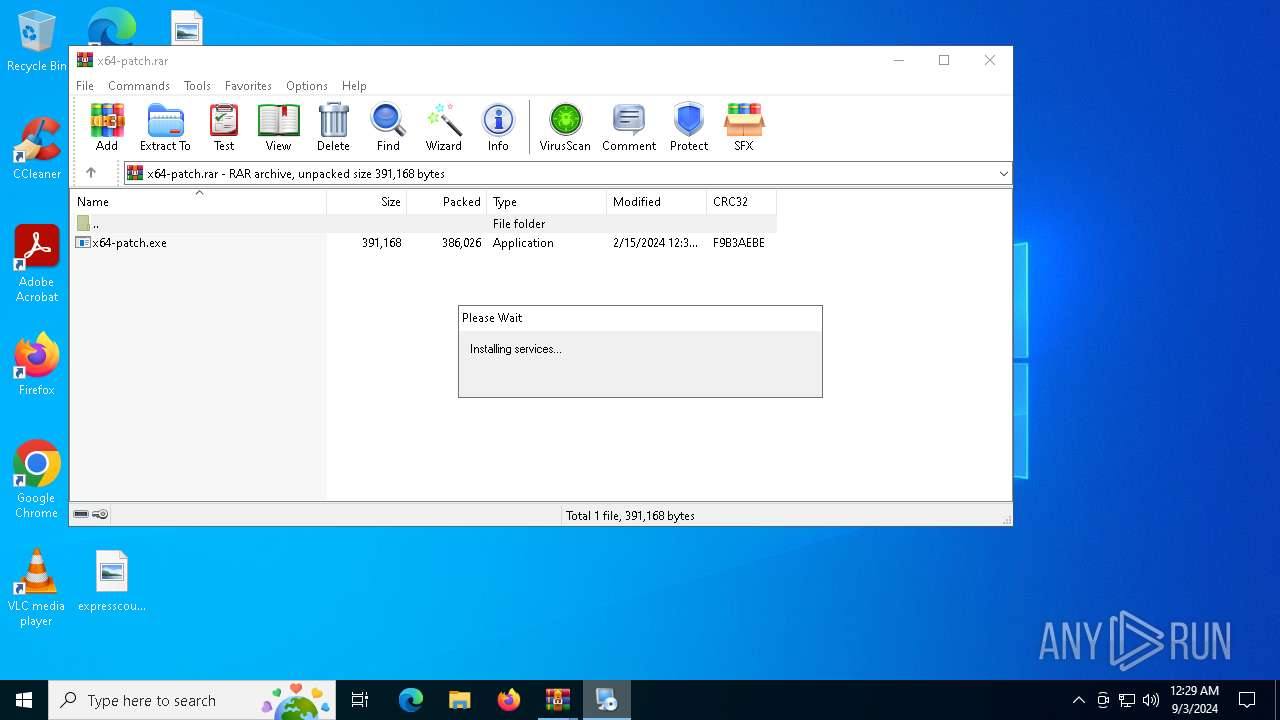
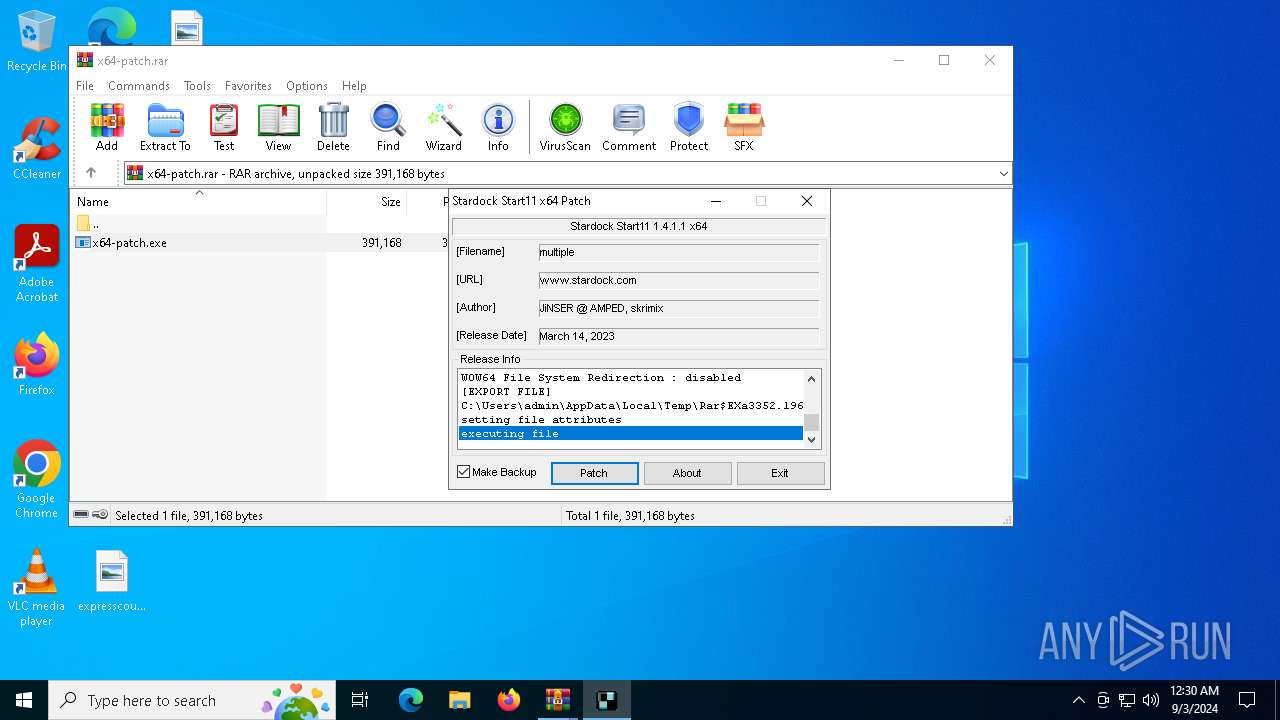
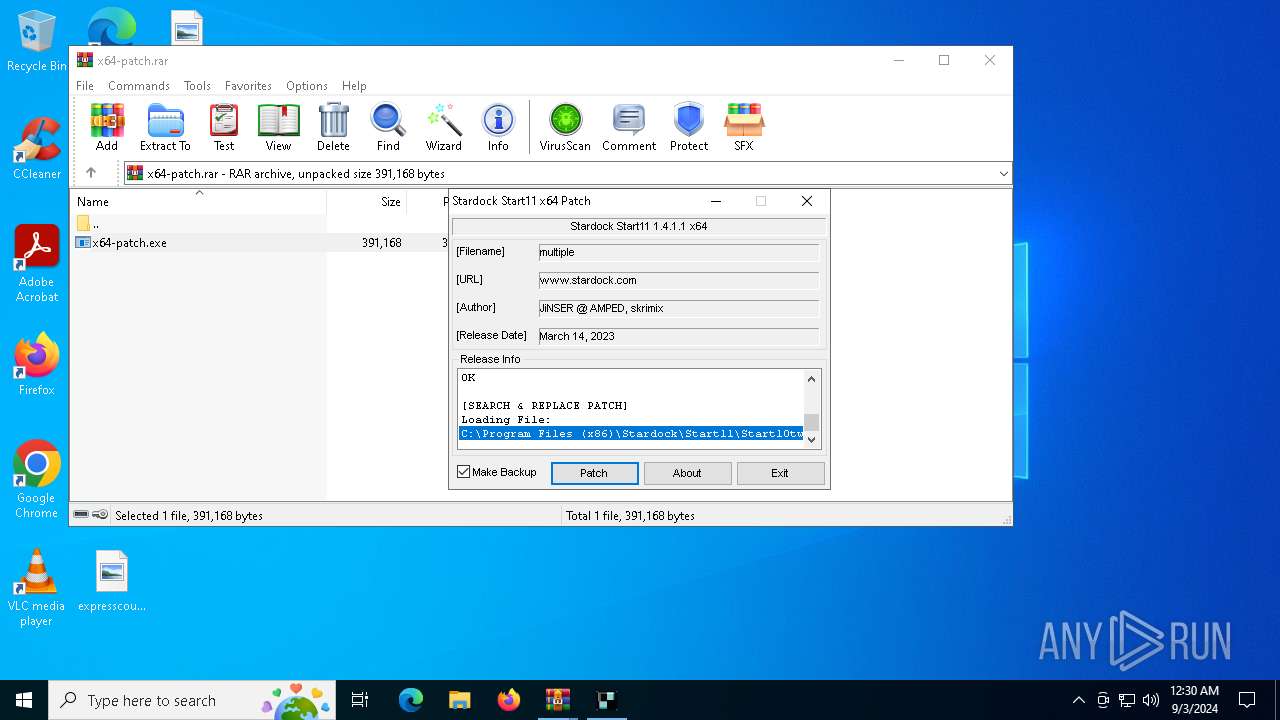
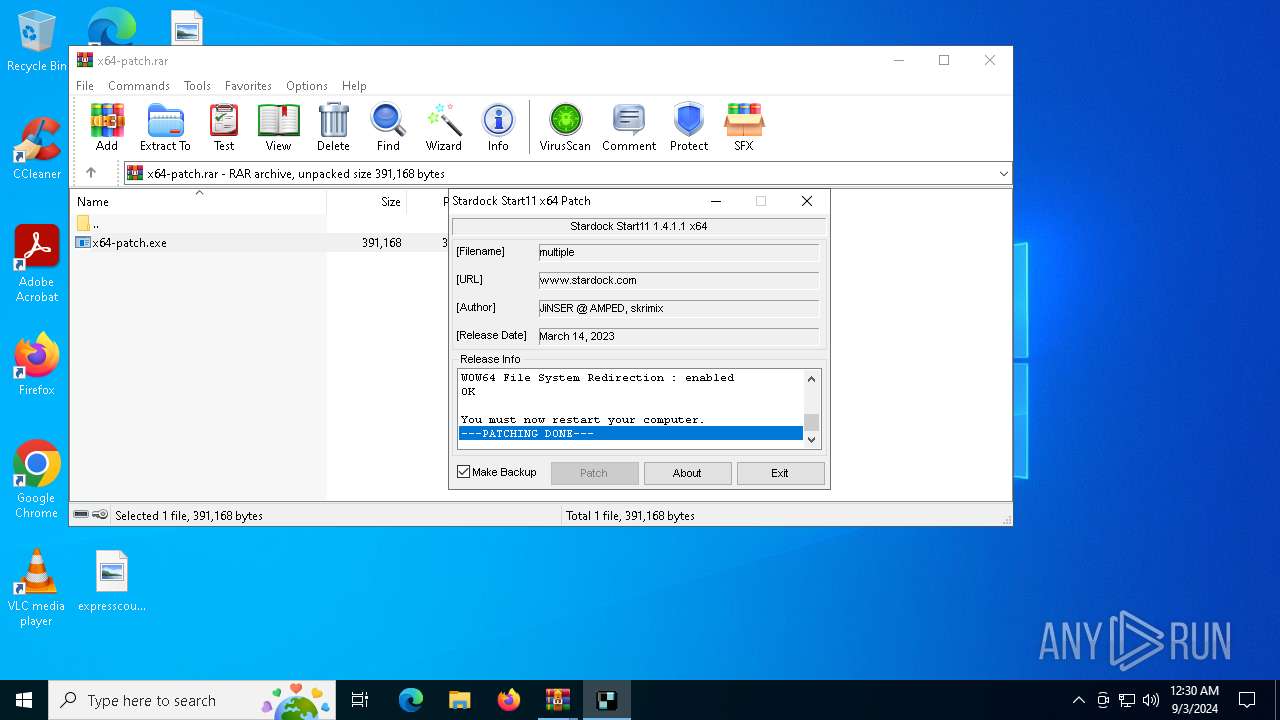
Executable content was dropped or overwritten
- Start11v2-setup.exe (PID: 3708)
- irsetup.exe (PID: 2028)
- x64-patch.exe (PID: 5468)
- cmd.exe (PID: 5160)
Reads the Windows owner or organization settings
- irsetup.exe (PID: 2028)
The process exported the data from the registry
- irsetup.exe (PID: 2028)
Reads the date of Windows installation
- irsetup.exe (PID: 2028)
- Start11v2-setup.exe (PID: 3708)
Checks Windows Trust Settings
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7288)
- Start11Config.exe (PID: 8060)
- Start11Config.exe (PID: 3540)
Reads Internet Explorer settings
- irsetup.exe (PID: 2028)
- SdDisplay.exe (PID: 7956)
Process drops legitimate windows executable
- irsetup.exe (PID: 2028)
Starts CMD.EXE for commands execution
- irsetup.exe (PID: 2028)
- x64-patch.exe (PID: 5468)
The process creates files with name similar to system file names
- irsetup.exe (PID: 2028)
- cmd.exe (PID: 5160)
- x64-patch.exe (PID: 5468)
Executes as Windows Service
- Start11Srv.exe (PID: 7464)
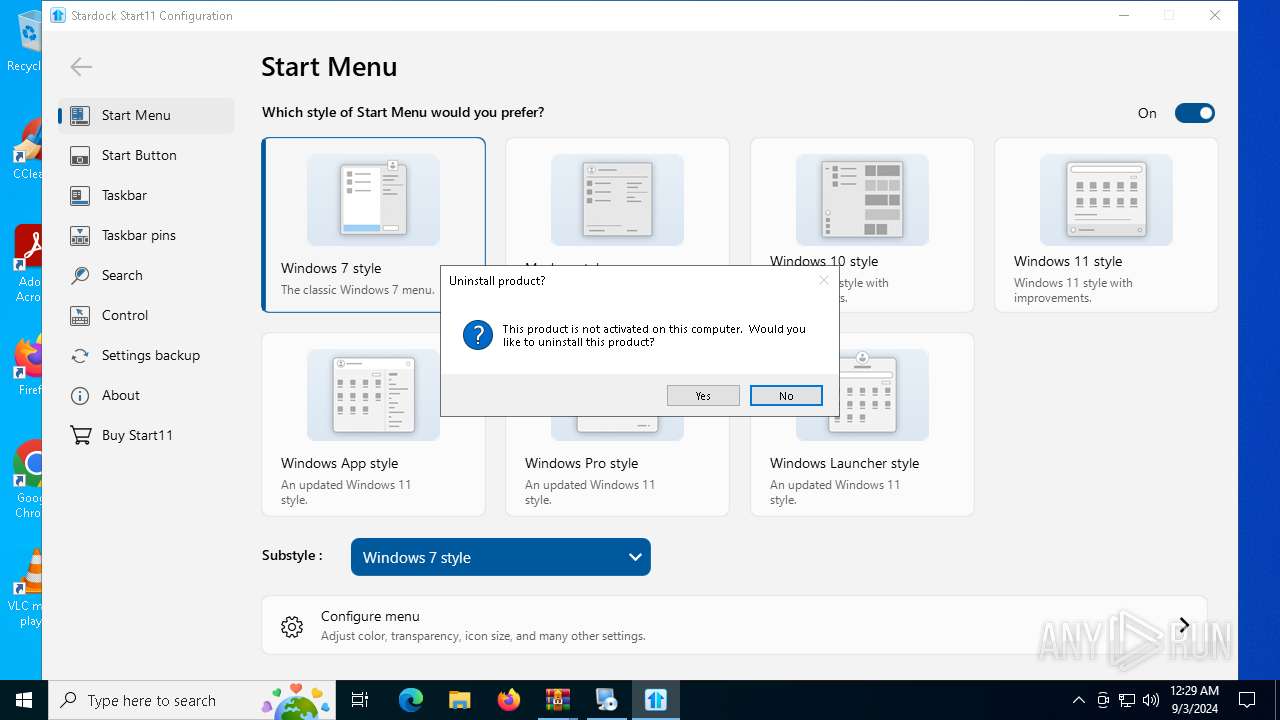
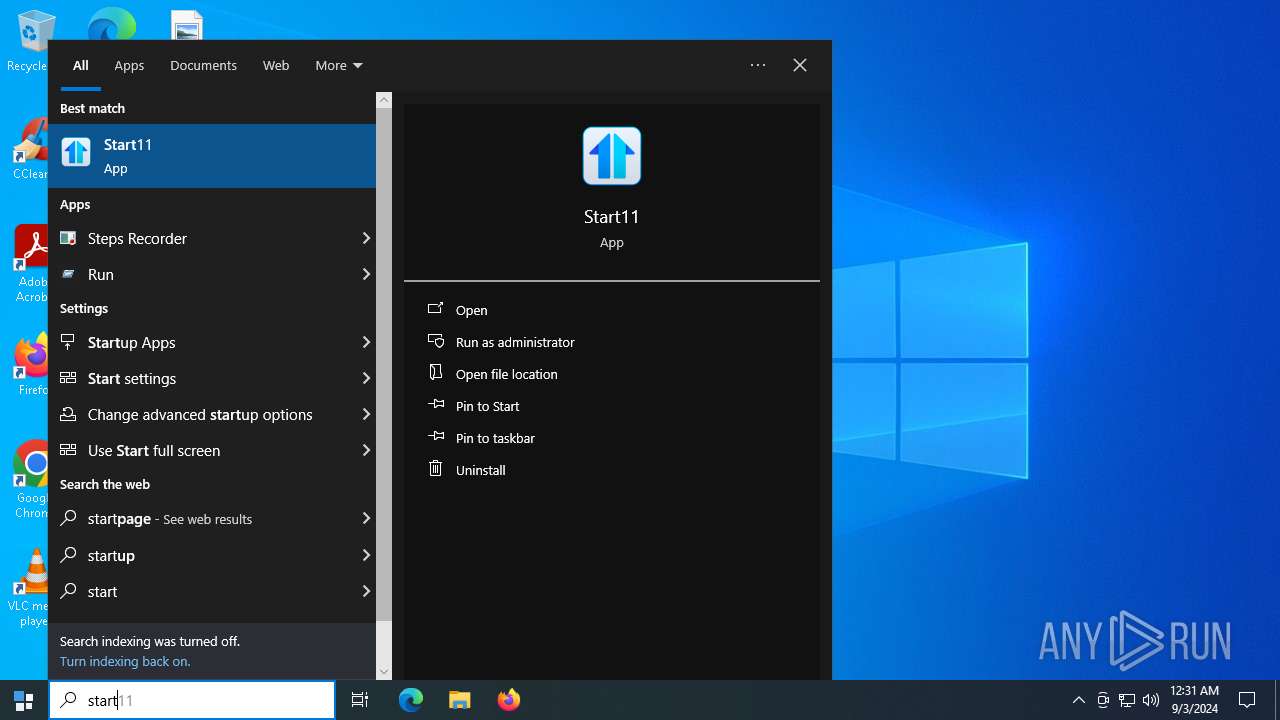
Application launched itself
- WinRAR.exe (PID: 7776)
Creates a software uninstall entry
- irsetup.exe (PID: 2028)
Reads Microsoft Outlook installation path
- irsetup.exe (PID: 2028)
- SdDisplay.exe (PID: 7956)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 5244)
Changes Internet Explorer settings (feature browser emulation)
- SdDisplay.exe (PID: 7956)
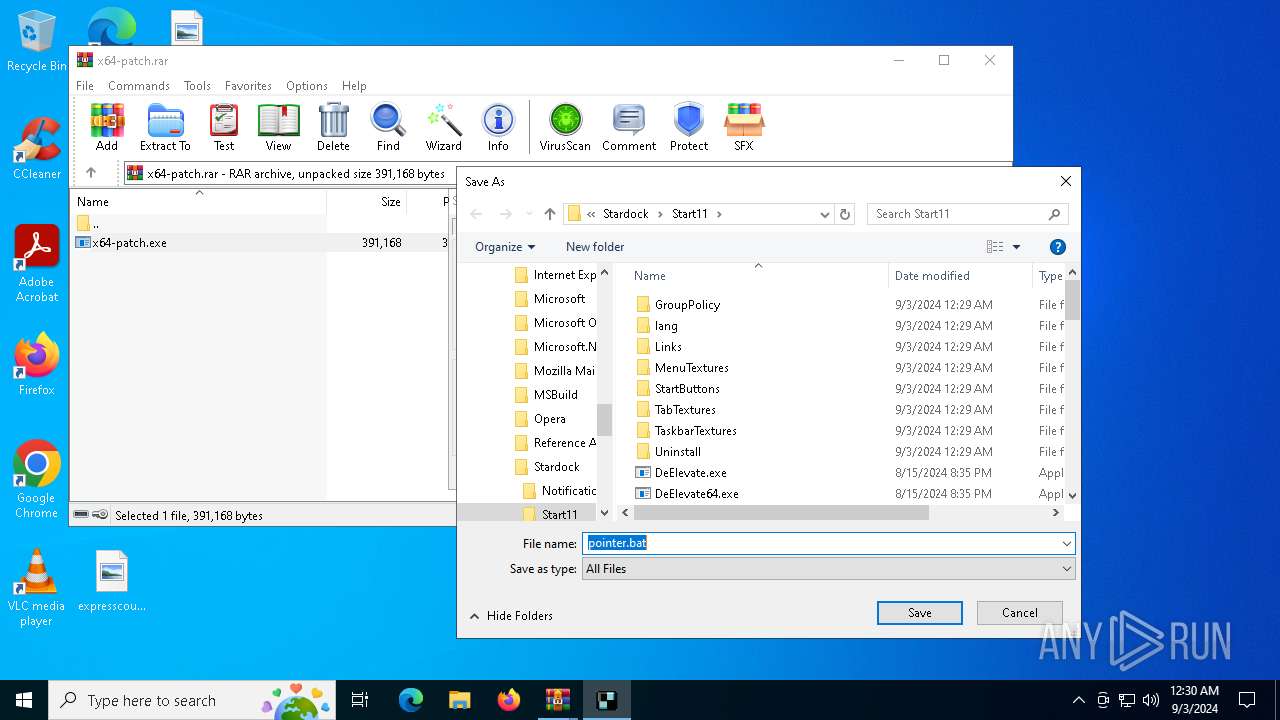
Executing commands from a ".bat" file
- x64-patch.exe (PID: 5468)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 1172)
Detected use of alternative data streams (AltDS)
- powershell.exe (PID: 4760)
Starts POWERSHELL.EXE for commands execution
- explorer.exe (PID: 4168)
INFO
Reads Environment values
- identity_helper.exe (PID: 7568)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 7288)
- Start11Config.exe (PID: 8060)
- identity_helper.exe (PID: 2136)
- Start11Config.exe (PID: 3540)
Reads Microsoft Office registry keys
- msedge.exe (PID: 1568)
- msedge.exe (PID: 7976)
- Start11Config.exe (PID: 7288)
- explorer.exe (PID: 4168)
Application launched itself
- msedge.exe (PID: 1568)
- msedge.exe (PID: 7976)
Attempting to use file storage service
- msedge.exe (PID: 1480)
Checks supported languages
- identity_helper.exe (PID: 7568)
- Start11v2-setup.exe (PID: 3708)
- GetMachineSID.exe (PID: 2768)
- Start11Srv.exe (PID: 6744)
- Start11Srv.exe (PID: 7464)
- Start11_64.exe (PID: 1344)
- Start11_64.exe (PID: 6740)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7288)
- Start11Config.exe (PID: 8060)
- SdDisplay.exe (PID: 7956)
- irsetup.exe (PID: 2028)
- identity_helper.exe (PID: 2136)
- x64-patch.exe (PID: 5468)
- movefile.exe (PID: 7412)
- movefile.exe (PID: 7580)
- movefile.exe (PID: 6636)
- movefile.exe (PID: 6156)
- movefile.exe (PID: 7480)
- movefile.exe (PID: 2032)
- movefile.exe (PID: 7372)
- movefile.exe (PID: 6716)
- movefile.exe (PID: 7664)
- movefile.exe (PID: 7772)
- movefile.exe (PID: 7024)
- movefile.exe (PID: 4088)
- movefile.exe (PID: 7568)
- movefile.exe (PID: 5388)
- PLUGScheduler.exe (PID: 1172)
- Start11Config.exe (PID: 3540)
- Start11_64.exe (PID: 4032)
Reads the computer name
- identity_helper.exe (PID: 7568)
- irsetup.exe (PID: 2028)
- GetMachineSID.exe (PID: 2768)
- Start11Srv.exe (PID: 6744)
- Start11Config.exe (PID: 7472)
- Start11Srv.exe (PID: 7464)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7288)
- Start11v2-setup.exe (PID: 3708)
- SdDisplay.exe (PID: 7956)
- Start11Config.exe (PID: 8060)
- identity_helper.exe (PID: 2136)
- x64-patch.exe (PID: 5468)
- PLUGScheduler.exe (PID: 1172)
- Start11Config.exe (PID: 3540)
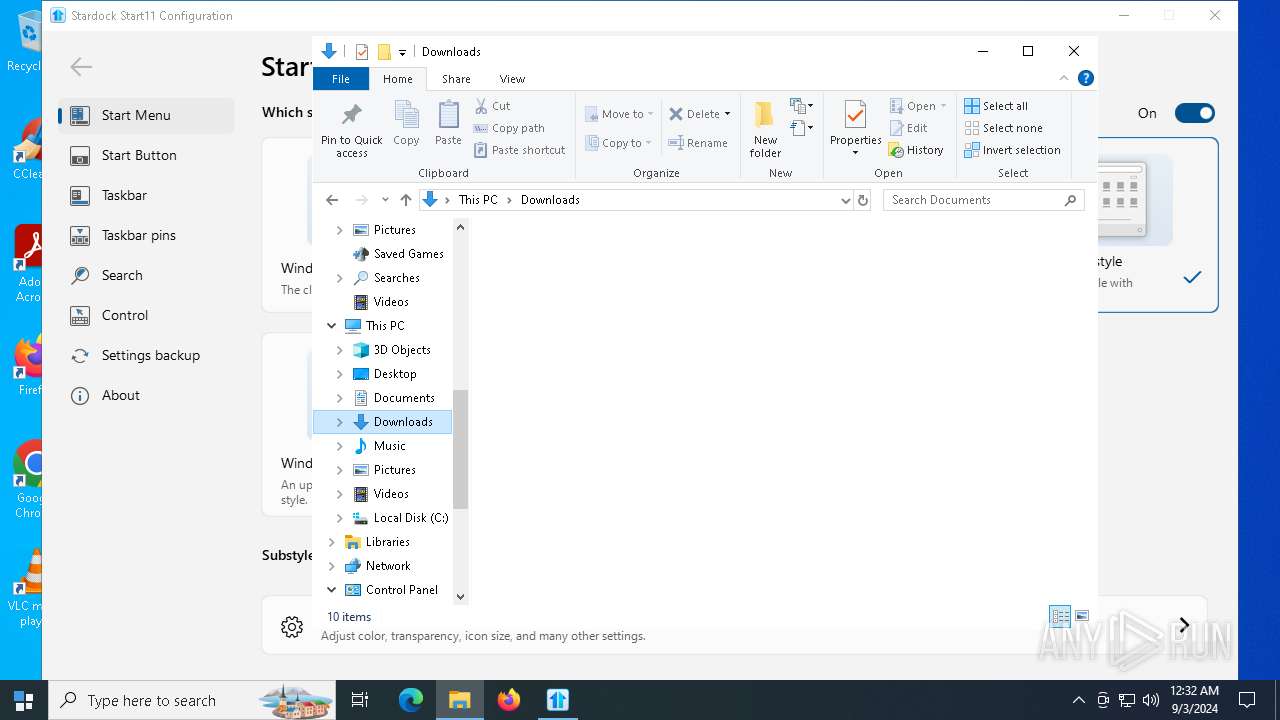
The process uses the downloaded file
- msedge.exe (PID: 1568)
- msedge.exe (PID: 7768)
- WinRAR.exe (PID: 7776)
- irsetup.exe (PID: 2028)
- Start11v2-setup.exe (PID: 3708)
- WinRAR.exe (PID: 3352)
- explorer.exe (PID: 4168)
Create files in a temporary directory
- Start11v2-setup.exe (PID: 3708)
- irsetup.exe (PID: 2028)
- GetMachineSID.exe (PID: 2768)
- reg.exe (PID: 7584)
- x64-patch.exe (PID: 5468)
- explorer.exe (PID: 4168)
Process checks computer location settings
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7288)
- Start11Config.exe (PID: 8060)
- Start11v2-setup.exe (PID: 3708)
- Start11Config.exe (PID: 3540)
Checks proxy server information
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- SdDisplay.exe (PID: 7956)
- explorer.exe (PID: 4168)
Reads the software policy settings
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 7288)
- Start11Config.exe (PID: 8060)
- explorer.exe (PID: 4168)
Reads the machine GUID from the registry
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 6884)
- Start11Config.exe (PID: 8060)
- Start11Config.exe (PID: 7288)
- SdDisplay.exe (PID: 7956)
- Start11Config.exe (PID: 3540)
Process checks Internet Explorer phishing filters
- irsetup.exe (PID: 2028)
- SdDisplay.exe (PID: 7956)
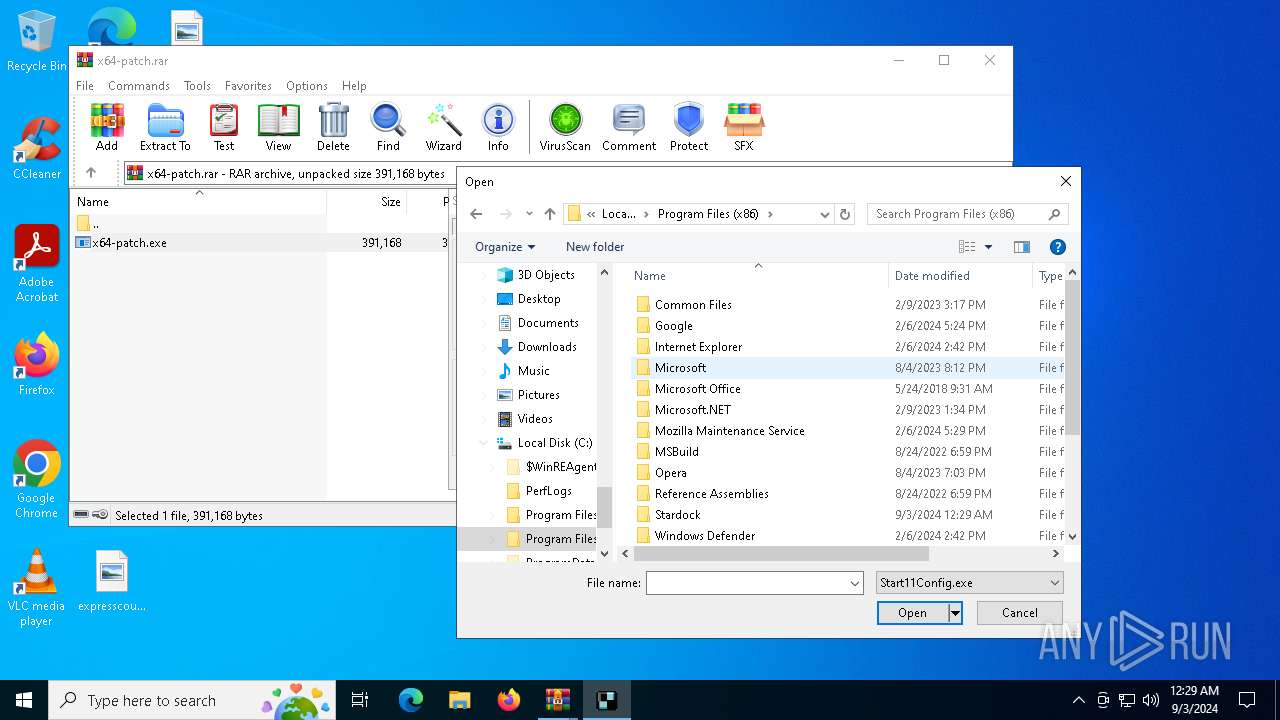
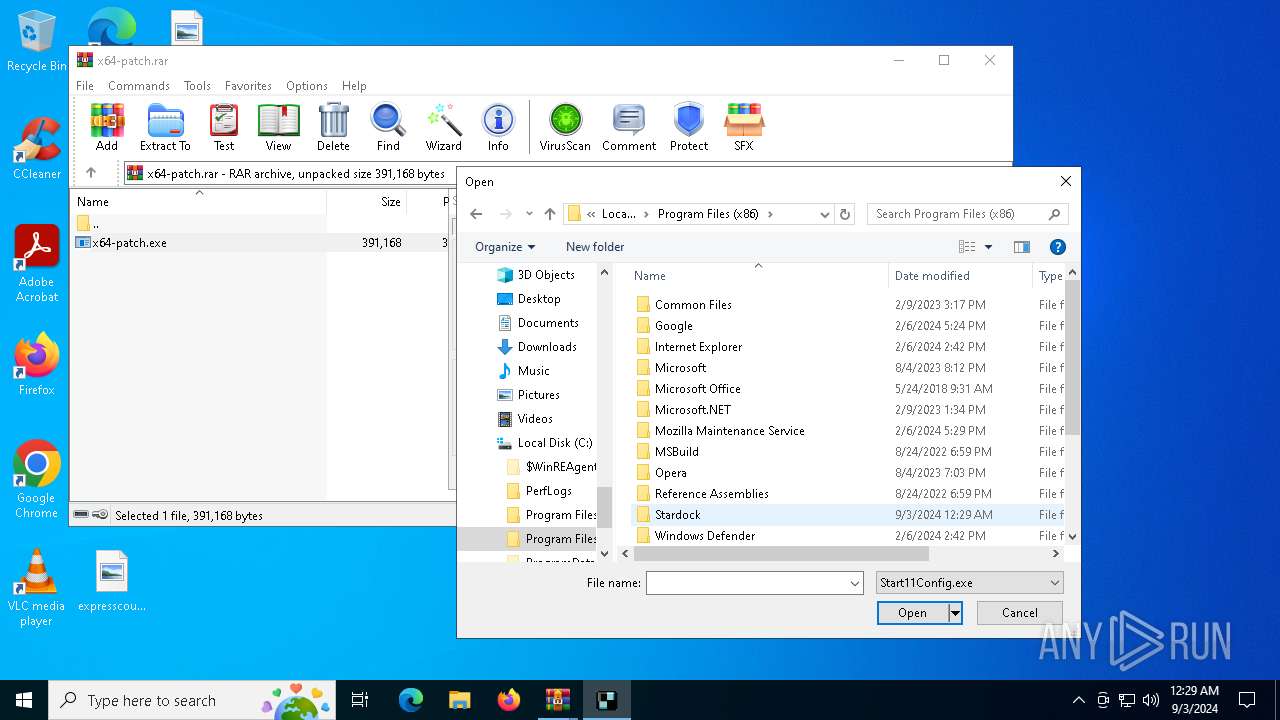
Creates files in the program directory
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- x64-patch.exe (PID: 5468)
- cmd.exe (PID: 5160)
- PLUGScheduler.exe (PID: 1172)
- explorer.exe (PID: 4168)
Creates files or folders in the user directory
- irsetup.exe (PID: 2028)
- Start11Config.exe (PID: 7472)
- Start11Config.exe (PID: 7288)
- explorer.exe (PID: 4168)
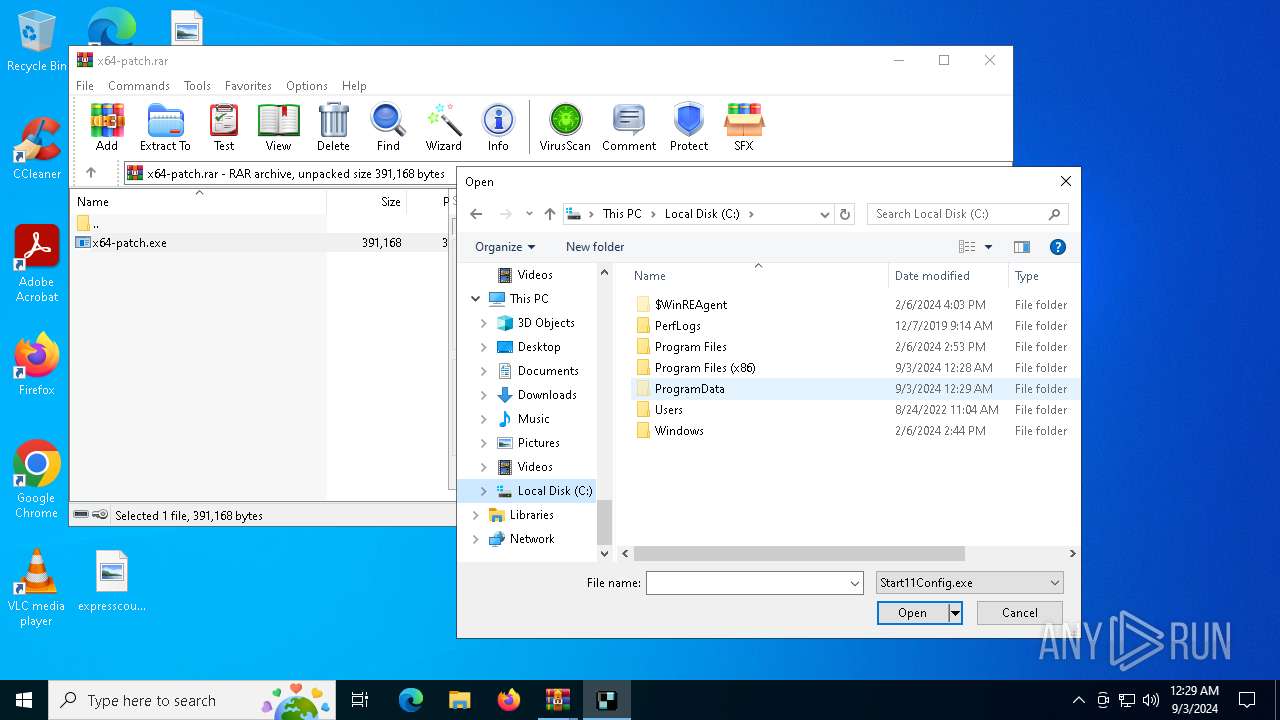
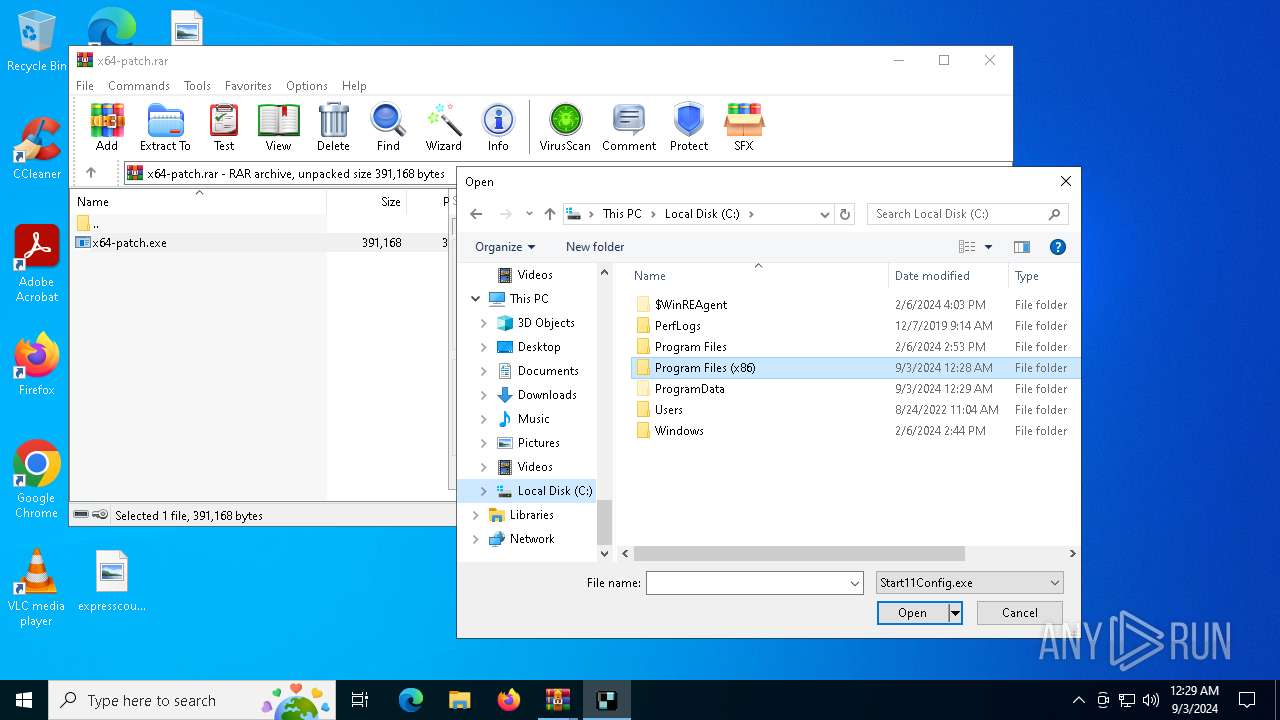
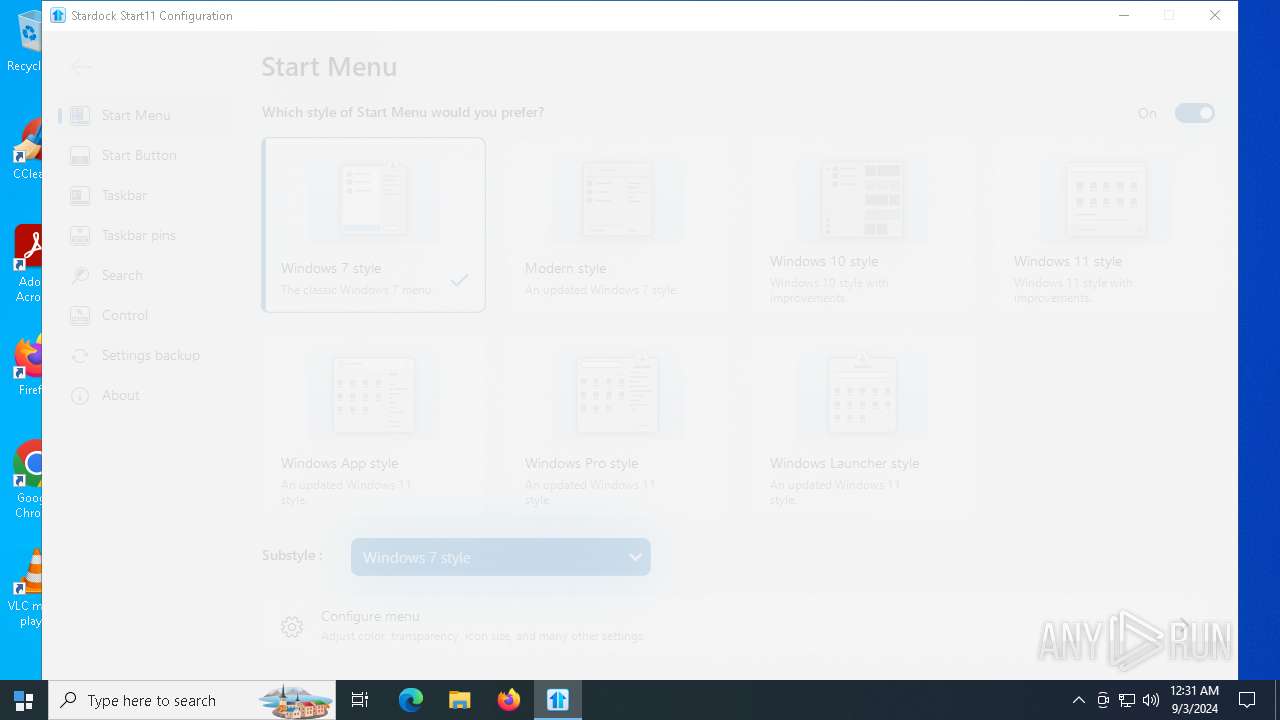
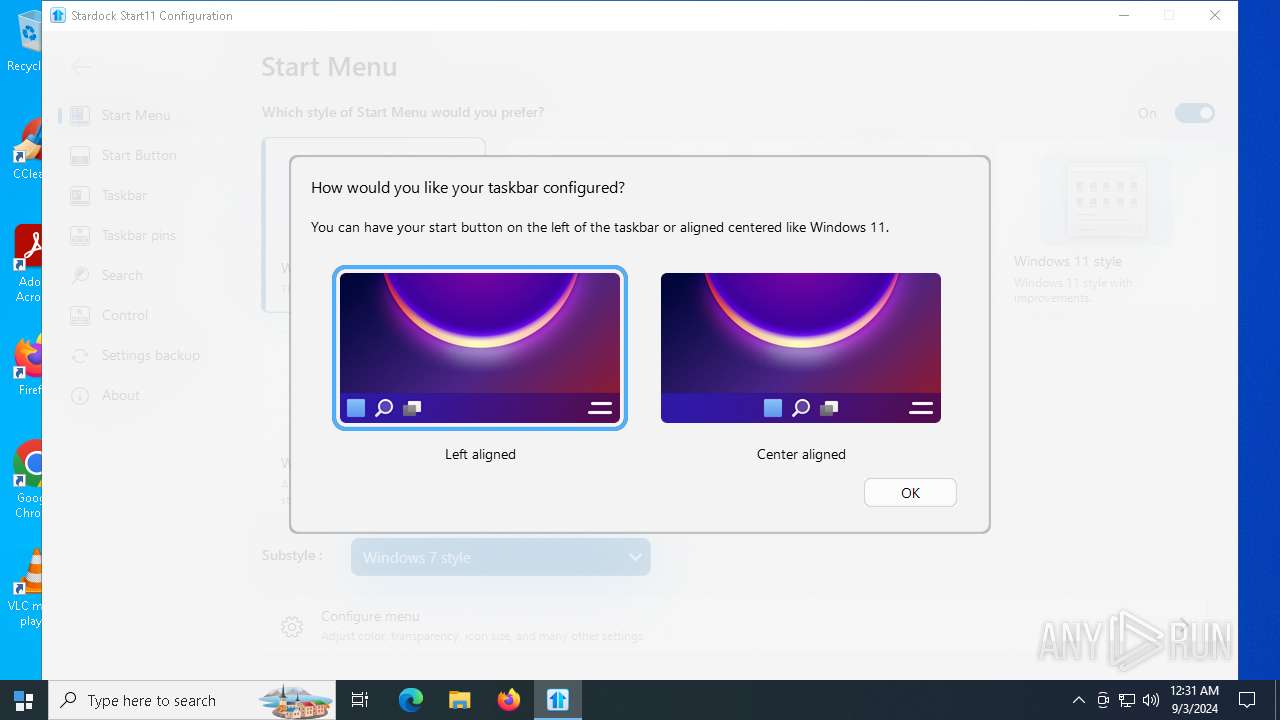
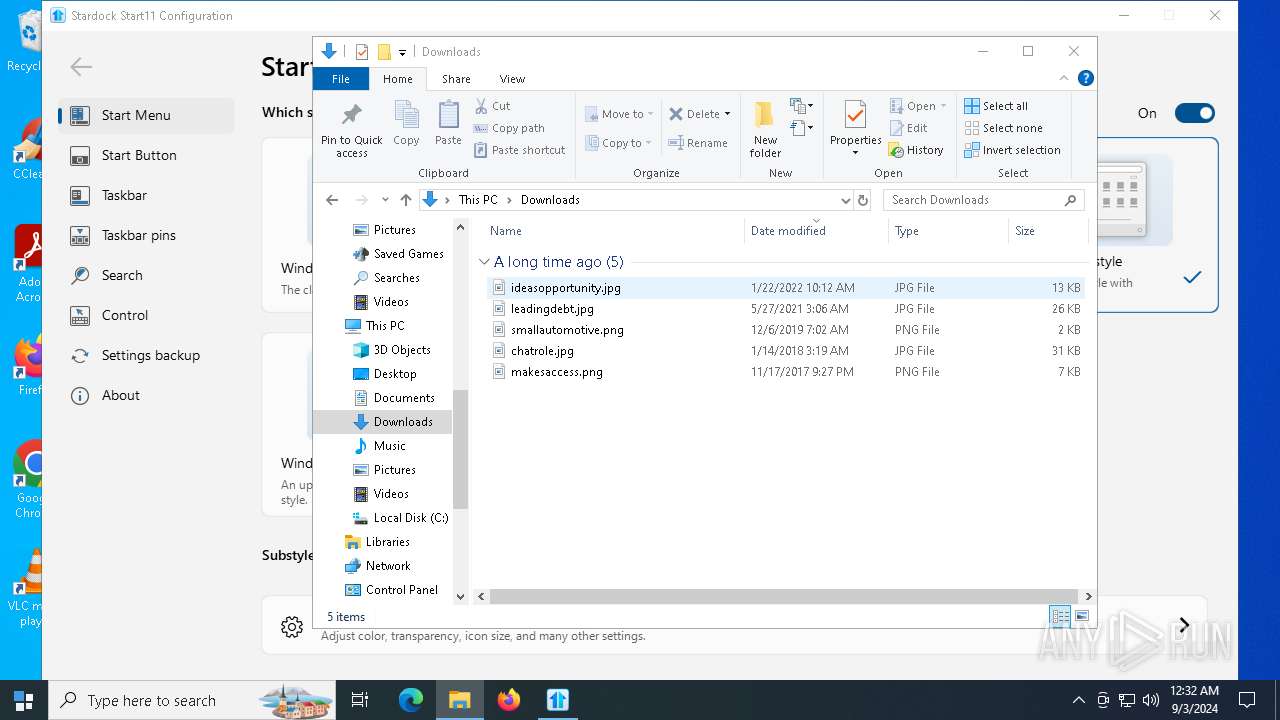
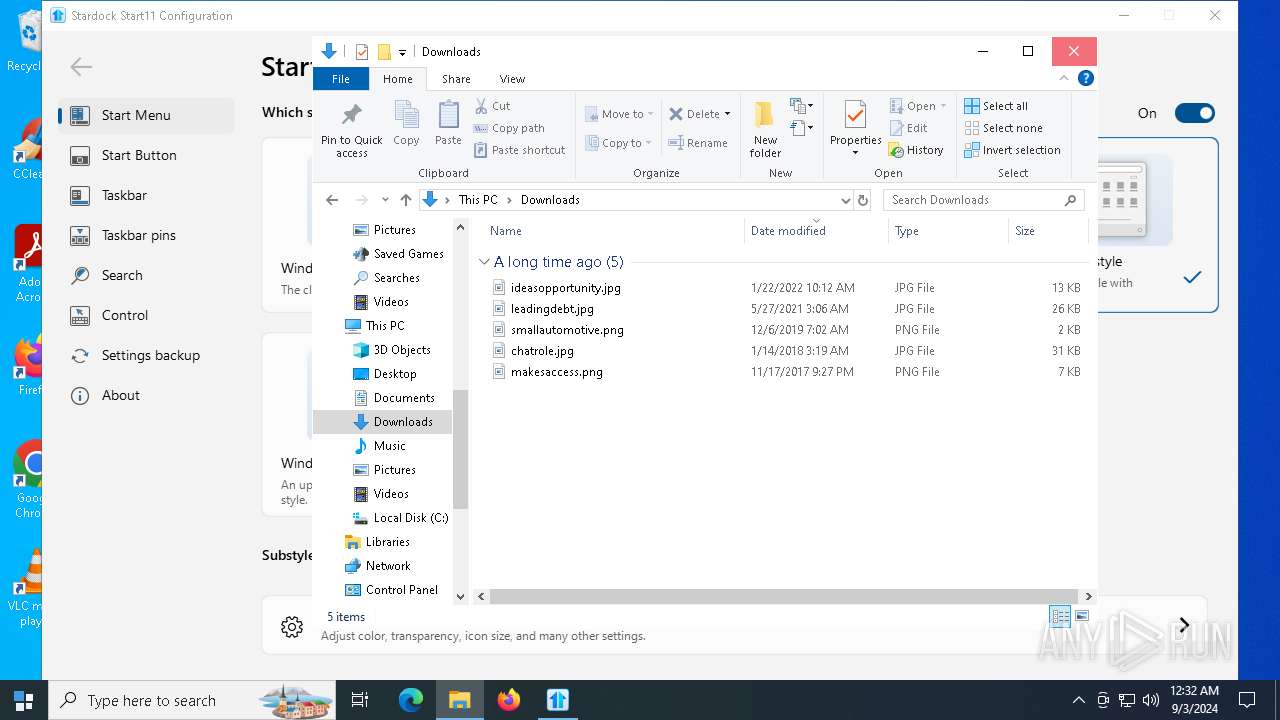
Manual execution by a user
- Start11Config.exe (PID: 8060)
- powershell.exe (PID: 4760)
- powershell.exe (PID: 4768)
- Start11Config.exe (PID: 3540)
UPX packer has been detected
- irsetup.exe (PID: 2028)
The process uses Lua
- irsetup.exe (PID: 2028)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3352)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
388
Monitored processes
108
Malicious processes
5
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=3440 --field-trial-handle=2364,i,12436251388469164812,625673893796361419,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 236 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa3352.19611\x64-patch.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa3352.19611\x64-patch.exe | — | WinRAR.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --no-appcompat-clear --gpu-preferences=WAAAAAAAAADgAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=2228 --field-trial-handle=2232,i,7525519569905191851,16470020328888310427,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 872 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1172 | "C:\Program Files\RUXIM\PLUGscheduler.exe" | C:\Program Files\RUXIM\PLUGScheduler.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Update LifeCycle Component Scheduler Exit code: 0 Version: 10.0.19041.3623 (WinBuild.160101.0800) Modules
| |||||||||||||||
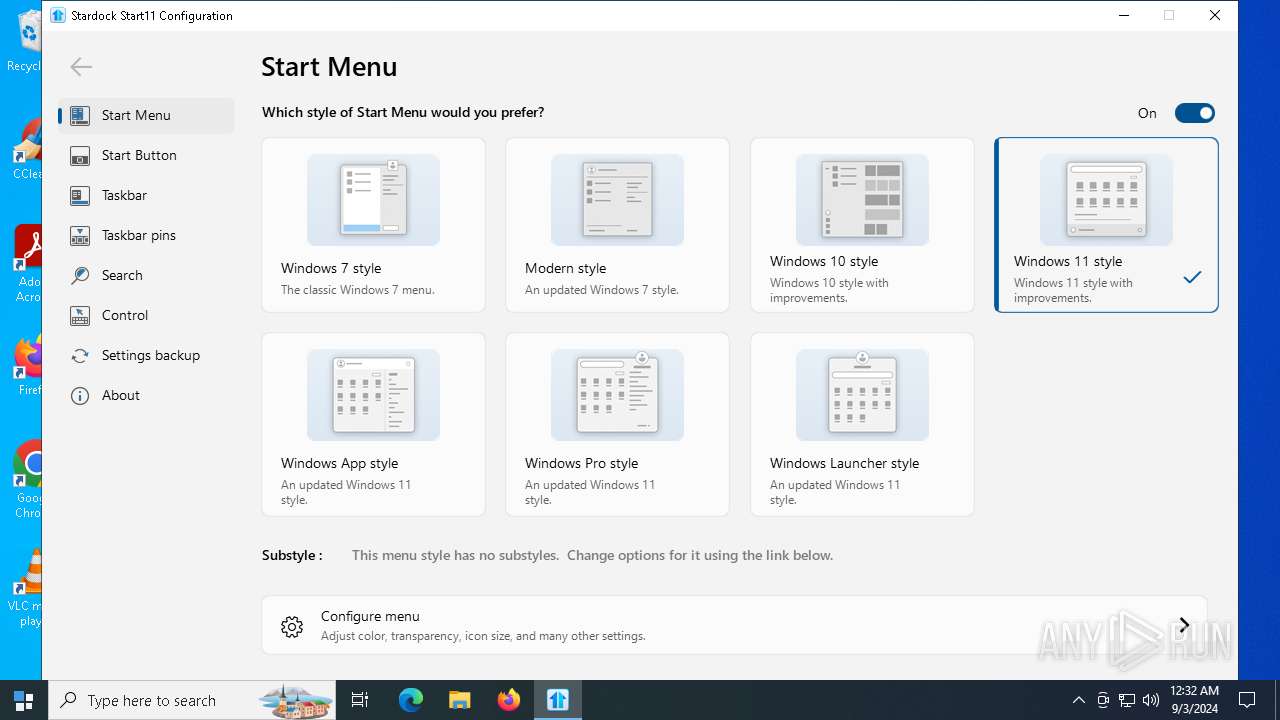
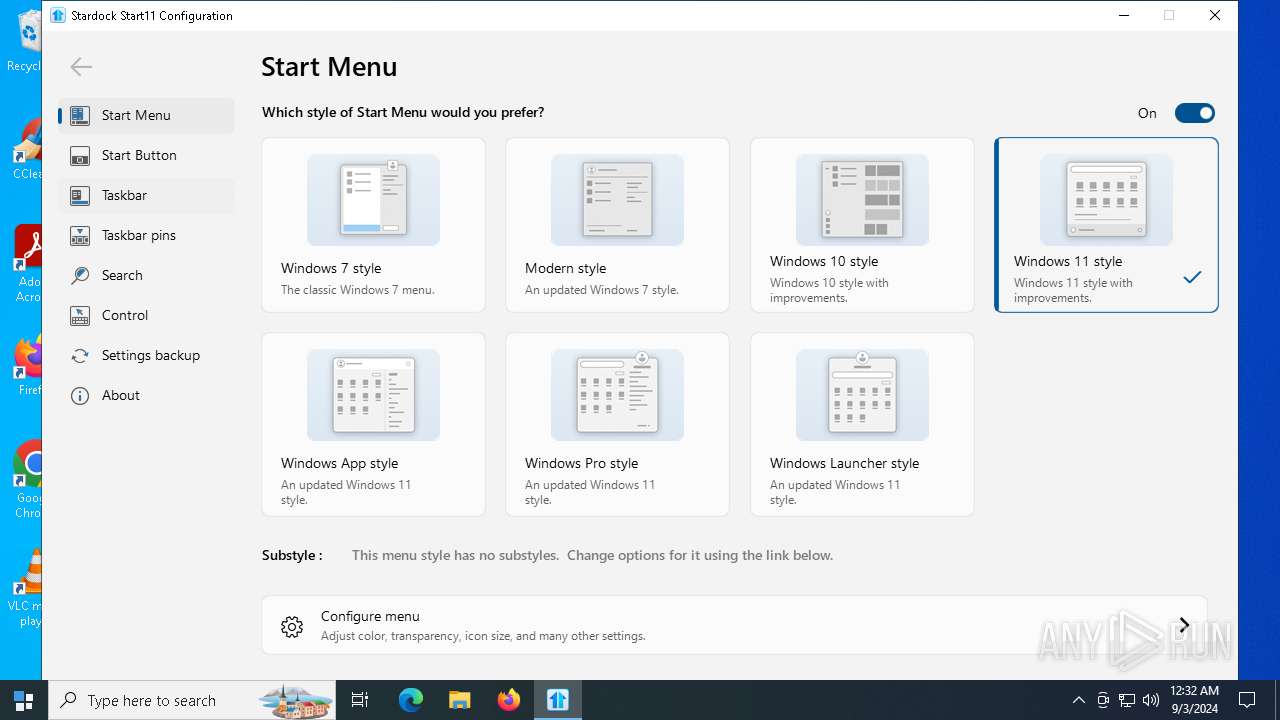
| 1344 | "C:\Program Files (x86)\Stardock\Start11\Start11_64.exe" START | C:\Program Files (x86)\Stardock\Start11\Start11_64.exe | — | Start11Srv.exe | |||||||||||
User: admin Company: Stardock Software, Inc Integrity Level: MEDIUM Description: Start11 Exit code: 0 Version: 2.0.0.0 Modules
| |||||||||||||||
| 1480 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --no-appcompat-clear --mojo-platform-channel-handle=2496 --field-trial-handle=2232,i,7525519569905191851,16470020328888310427,262144 --variations-seed-version /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "https://files.catbox.moe/ga81v7.7z" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2028 | "C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe" __IRAOFF:1936418 "__IRAFN:C:\Users\admin\AppData\Local\Temp\Rar$EXa7776.13600\Start11v2-setup.exe" "__IRCT:3" "__IRTSS:0" "__IRSID:S-1-5-21-1693682860-607145093-2874071422-1001" | C:\Users\admin\AppData\Local\Temp\_ir_sf_temp_0\irsetup.exe | Start11v2-setup.exe | ||||||||||||
User: admin Company: Indigo Rose Corporation Integrity Level: HIGH Description: Setup Application Exit code: 0 Version: 9.5.3.0 Modules
| |||||||||||||||
Total events
197 433
Read events
196 310
Write events
1 077
Delete events
46
Modification events
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (1568) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | urlstats |
Value: 0 | |||
Executable files
67
Suspicious files
1 027
Text files
369
Unknown types
208
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF129daf.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF129daf.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF129daf.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF129dbf.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF129dee.TMP | — | |
MD5:— | SHA256:— | |||
| 1568 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
28
TCP/UDP connections
110
DNS requests
84
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4708 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2660 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7472 | Start11Config.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEA6bGI750C3n79tQ4ghAGFo%3D | unknown | — | — | whitelisted |
7472 | Start11Config.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
2028 | irsetup.exe | GET | 200 | 195.138.255.18:80 | http://r10.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRpD%2BQVZ%2B1vf7U0RGQGBm8JZwdxcgQUdKR2KRcYVIUxN75n5gZYwLzFBXICEgM87dym5IuWcrhXeQ2ZBiaebw%3D%3D | unknown | — | — | whitelisted |
4708 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7472 | Start11Config.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEAKSYfpIaxYQcTpMuex%2BbEI%3D | unknown | — | — | whitelisted |
7884 | svchost.exe | HEAD | 200 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725594965&P2=404&P3=2&P4=RoP2w7d7B2Jg3gxS%2bvCKVfc%2b%2baa92Lpk%2bpcWDucDO4ZGbad3jID4eHLjYmxSGBnOhFWG94Z8W9t%2fxpQybQoBwQ%3d%3d | unknown | — | — | whitelisted |
7884 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725594965&P2=404&P3=2&P4=RoP2w7d7B2Jg3gxS%2bvCKVfc%2b%2baa92Lpk%2bpcWDucDO4ZGbad3jID4eHLjYmxSGBnOhFWG94Z8W9t%2fxpQybQoBwQ%3d%3d | unknown | — | — | whitelisted |
7884 | svchost.exe | GET | 206 | 23.48.23.7:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/7b9cac0d-9ca2-42ef-9c46-ce975d51335a?P1=1725594965&P2=404&P3=2&P4=RoP2w7d7B2Jg3gxS%2bvCKVfc%2b%2baa92Lpk%2bpcWDucDO4ZGbad3jID4eHLjYmxSGBnOhFWG94Z8W9t%2fxpQybQoBwQ%3d%3d | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
568 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4760 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2120 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1480 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1568 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
1480 | msedge.exe | 13.107.21.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1480 | msedge.exe | 108.181.20.37:443 | files.catbox.moe | TELUS Communications | CA | malicious |
1480 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
1480 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
files.catbox.moe |
| malicious |
edge.microsoft.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
bzib.nelreports.net |
| whitelisted |
update.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1480 | msedge.exe | Potentially Bad Traffic | ET INFO Observed File Sharing Service Download Domain (files .catbox .moe in TLS SNI) |
1480 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Downloading from a file sharing service is observed |
1 ETPRO signatures available at the full report