| File name: | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59 |
| Full analysis: | https://app.any.run/tasks/4767ec4d-ac4a-4e90-8375-fb268cae2e20 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2025, 20:28:52 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | A624151637F5C948A734E75A07B1C764 |
| SHA1: | 09AB154C60C57502D34227E0278B52BC5D9E482F |
| SHA256: | 2B939E56AE1082F47A9CA214AA2F59CD688DA7047FDD89208EAF6D0C1B226E59 |
| SSDEEP: | 49152:BKFBRduX/LsgdyOOE3XSN9SQhWupZzg0Sh66I668JRWNilSaHDzYt/uF10rC8gx1:YRuXTsEPOEHkWGzgB4ARosNH3YhuF106 |
MALICIOUS
Connects to the CnC server
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
XORed URL has been found (YARA)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
SUSPICIOUS
Application launched itself
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
Reads security settings of Internet Explorer
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
Connects to unusual port
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
Contacting a server suspected of hosting an CnC
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
Potential Corporate Privacy Violation
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
There is functionality for taking screenshot (YARA)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
There is functionality for communication over UDP network (YARA)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
INFO
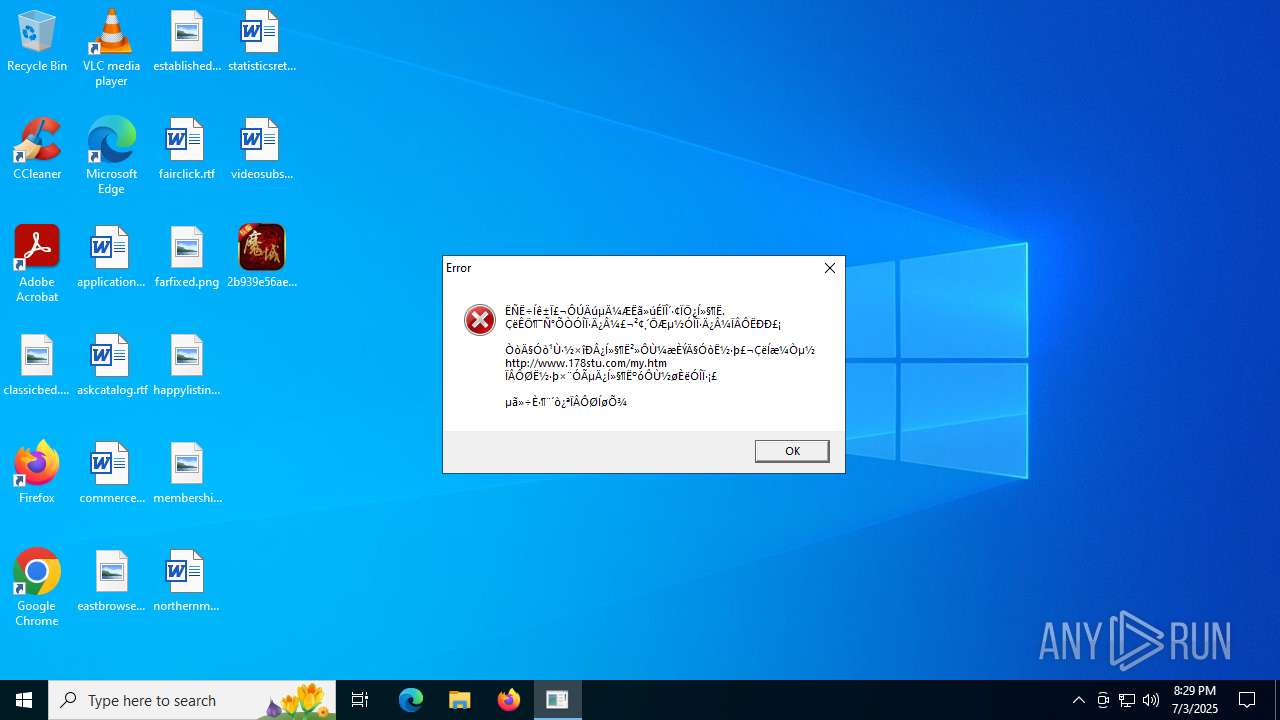
The sample compiled with chinese language support
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
Checks supported languages
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
- identity_helper.exe (PID: 2980)
Process checks computer location settings
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
Reads the computer name
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 4984)
- identity_helper.exe (PID: 2980)
Checks proxy server information
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
- slui.exe (PID: 7564)
Application launched itself
- msedge.exe (PID: 1332)
- msedge.exe (PID: 1636)
- msedge.exe (PID: 5560)
Reads Environment values
- identity_helper.exe (PID: 2980)
Reads the software policy settings
- slui.exe (PID: 7564)
Aspack has been detected
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
Compiled with Borland Delphi (YARA)
- 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe (PID: 2228)
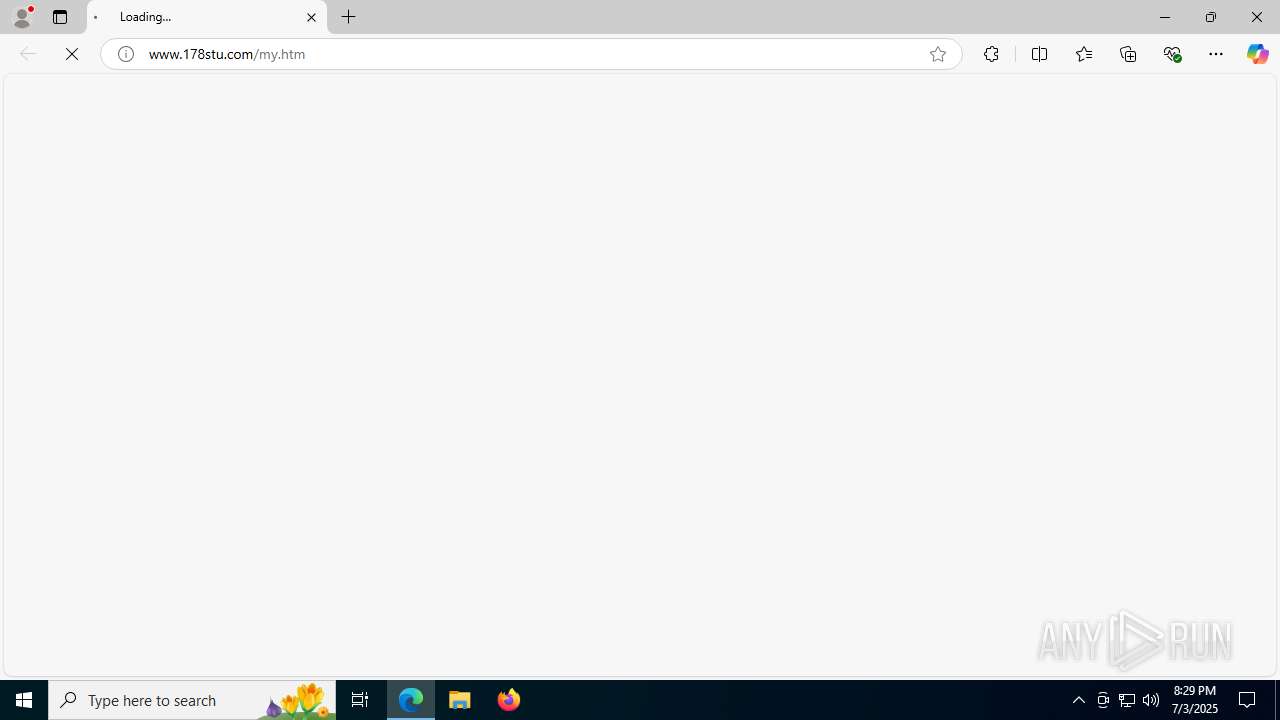
Manual execution by a user
- msedge.exe (PID: 1636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
xor-url
(PID) Process(2228) 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe
Decrypted-URLs (2)http://info.178stu.com/hst2_new.txt
http://www.178stu.com/hst2_new.txt
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:12:11 12:45:48+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 546816 |
| InitializedDataSize: | 1371648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x86c70 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Windows, Chinese (Simplified) |
| CompanyName: | 潇湘网络 |
| FileDescription: | 商业程序 |
| InternalName: | LoginTools.exe |
| LegalCopyright: | 版权所有 (C) 2022 |
| OriginalFileName: | LoginTools.exe |
| ProductName: | 商业程序 |
| ProductVersion: | 1, 0, 0, 0 |
| FileVersion: | 1,0,0,0 |
Total processes
179
Monitored processes
44
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 424 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x29c,0x2a0,0x2a4,0x290,0x294,0x7ffc4515f208,0x7ffc4515f214,0x7ffc4515f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 536 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=8 --always-read-main-dll --field-trial-handle=4416,i,7670701012108179895,14652571821105292301,262144 --variations-seed-version --mojo-platform-channel-handle=4428 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 700 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2168,i,7670701012108179895,14652571821105292301,262144 --variations-seed-version --mojo-platform-channel-handle=2552 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 756 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2372,i,5800227638721988913,3694815978440882585,262144 --variations-seed-version --mojo-platform-channel-handle=2368 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1180 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=2740,i,7670701012108179895,14652571821105292301,262144 --variations-seed-version --mojo-platform-channel-handle=2756 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --always-read-main-dll --field-trial-handle=5364,i,7670701012108179895,14652571821105292301,262144 --variations-seed-version --mojo-platform-channel-handle=5272 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1332 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --edge-skip-compat-layer-relaunch --single-argument http://www.178stu.com/my.htm | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 1 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1636 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --flag-switches-begin --disable-quic --flag-switches-end --do-not-de-elevate --single-argument http://www.178stu.com/my.htm | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2076 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6492,i,7670701012108179895,14652571821105292301,262144 --variations-seed-version --mojo-platform-channel-handle=6932 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2140 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x284,0x288,0x28c,0x27c,0x294,0x7ffc4515f208,0x7ffc4515f214,0x7ffc4515f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
10 691
Read events
10 664
Write events
27
Delete events
0
Modification events
| (PID) Process: | (2228) 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2228) 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2228) 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (5560) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 1 | |||
| (PID) Process: | (1332) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1636) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1636) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1636) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
Executable files
0
Suspicious files
257
Text files
61
Unknown types
47
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF17ec63.TMP | — | |
MD5:— | SHA256:— | |||
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2228 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | C:\Windows\System32\drivers\etc\hosts | text | |
MD5:03450E8DDB20859F242195450C19B8F1 | SHA256:1BDD8F1DD7BD82B5B2313D8770DFE4F41CD3F45BBAEAB8B8A7F75FC5E2D3720B | |||
| 2228 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | C:\Users\admin\Desktop\hs.dat | text | |
MD5:03450E8DDB20859F242195450C19B8F1 | SHA256:1BDD8F1DD7BD82B5B2313D8770DFE4F41CD3F45BBAEAB8B8A7F75FC5E2D3720B | |||
| 1332 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:CDDDC745A8C954DC438C931889999BDB | SHA256:3DC9043838386F5363AC96A01477CF3163B5118B80191576A11B32CE9894314C | |||
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\bce883b2-a36f-405b-8143-e29eebdf9c91.tmp | binary | |
MD5:EDEBC8FE49F1EF2C7B521EA2CC9FCBA0 | SHA256:A104FD0EF1BA75E5EA5C0A23AB76818F7766CA2B538CB869F1F71368967E027C | |||
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF17ecb1.TMP | — | |
MD5:— | SHA256:— | |||
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF17ecb1.TMP | — | |
MD5:— | SHA256:— | |||
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1636 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
156
TCP/UDP connections
145
DNS requests
135
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2228 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | GET | — | 103.133.93.52:80 | http://info.178stu.com/hst2_new.txt | unknown | — | — | malicious |
2228 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | GET | — | 103.133.93.52:80 | http://www.178stu.com/hst2_new.txt | unknown | — | — | malicious |
— | — | POST | 200 | 20.190.160.64:443 | https://login.live.com/ppsecure/deviceaddcredential.srf | unknown | text | 16.7 Kb | whitelisted |
— | — | GET | 304 | 20.109.210.53:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5944 | MoUsoCoreWorker.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
— | — | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4984 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | 1.15.12.73:4567 | — | Shenzhen Tencent Computer Systems Company Limited | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
info.178stu.com |
| malicious |
www.178stu.com |
| malicious |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2228 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
2228 | 2b939e56ae1082f47a9ca214aa2f59cd688da7047fdd89208eaf6d0c1b226e59.exe | Potential Corporate Privacy Violation | ET INFO Unsupported/Fake Windows NT Version 5.0 |
— | — | Potentially Bad Traffic | ET INFO Possible Chrome Plugin install |
2 ETPRO signatures available at the full report