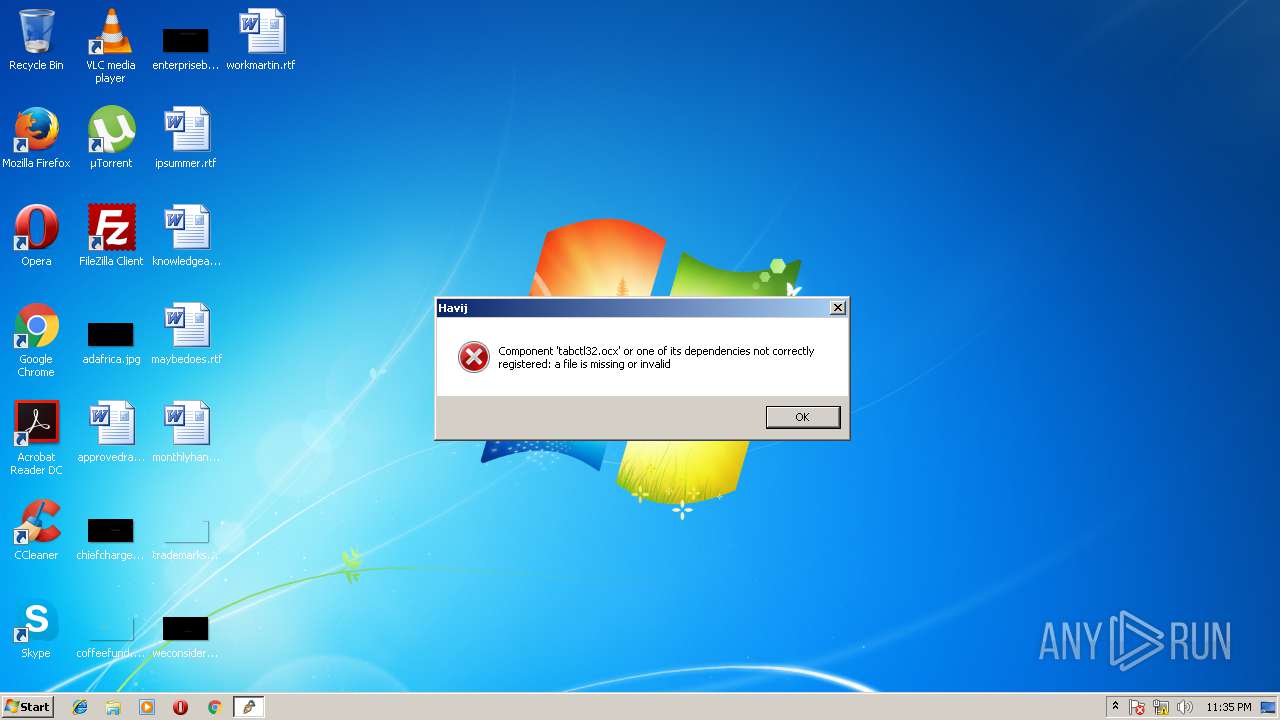
| File name: | Havij 2.00 Pro.exe |
| Full analysis: | https://app.any.run/tasks/16642e39-da72-438c-8575-f90b4a165730 |
| Verdict: | Malicious activity |
| Analysis date: | June 09, 2018, 22:34:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | D3B75FFEC79BBD63E794AFE037696B75 |
| SHA1: | 780D681C9C67913367052F4F06F2BE90D9171C2D |
| SHA256: | 2B8E82926C69E313855720F156FFAE01C1142EC607F905ED6C1C5A89E508305A |
| SSDEEP: | 49152:jwHvV4P6ATSdMzLOE7PjdaNwZ93J4AyibqIZcBCbWcAhu:8HvV4P6hARPj0wZ93FZbqIdS |
MALICIOUS
Changes the autorun value in the registry
- Havij 2.00 Pro.exe (PID: 3896)
Application was dropped or rewritten from another process
- svchost.exe (PID: 3440)
- svchost.exe (PID: 572)
- Havij.exe (PID: 4076)
SUSPICIOUS
Creates files in the user directory
- Havij 2.00 Pro.exe (PID: 3896)
- svchost.exe (PID: 3440)
Creates executable files which already exist in Windows
- Havij 2.00 Pro.exe (PID: 3896)
- svchost.exe (PID: 3440)
Executable content was dropped or overwritten
- Havij 2.00 Pro.exe (PID: 3896)
- svchost.exe (PID: 3440)
INFO
Dropped object may contain URL's
- Havij 2.00 Pro.exe (PID: 3896)
- svchost.exe (PID: 3440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Microsoft Visual Basic 6 (28.5) |
|---|---|---|
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (25.4) |
| .exe | | | InstallShield setup (14.9) |
| .exe | | | Win32 Executable MS Visual C++ (generic) (10.8) |
| .exe | | | Win64 Executable (generic) (9.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:03:06 10:25:21+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 2144768 |
| InitializedDataSize: | 30720 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20d88e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.15.0.0 |
| ProductVersionNumber: | 1.15.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| Comments: | http://hack-crack9.blogspot.com |
| CompanyName: | ITSecTeam |
| FileDescription: | Advanced SQL Injection Tool |
| LegalCopyright: | Copyright © 2009-2018 |
| LegalTrademarks: | ITSecTeam |
| ProductName: | Havij |
| FileVersion: | 2 |
| ProductVersion: | 2 |
| InternalName: | Havij |
| OriginalFileName: | Havij.exe |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Mar-2018 09:25:21 |
| Detected languages: |
|
| Debug artifacts: |
|
| Comments: | http://hack-crack9.blogspot.com |
| CompanyName: | ITSecTeam |
| FileDescription: | Advanced SQL Injection Tool |
| LegalCopyright: | Copyright © 2009-2018 |
| LegalTrademarks: | ITSecTeam |
| ProductName: | Havij |
| FileVersion: | 2.00 |
| ProductVersion: | 2.00 |
| InternalName: | Havij |
| OriginalFilename: | Havij.exe |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 06-Mar-2018 09:25:21 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0020B894 | 0x0020BA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.22781 |
.sdata | 0x0020E000 | 0x00000138 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.75639 |
.rsrc | 0x00210000 | 0x00007382 | 0x00007400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.11784 |
.reloc | 0x00218000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.04224 | 2850 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 3.03821 | 1640 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 3.23396 | 744 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 3.0616 | 296 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.32601 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.05831 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 3.00443 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.05546 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 3.42281 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 4.44847 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
mscoree.dll |
Total processes
35
Monitored processes
4
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\8.1.7601.17587\svchost.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\8.1.7601.17587\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Intel Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 8.1.1.7900 Modules
| |||||||||||||||
| 3440 | "C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\2.00\svchost.exe" | C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\2.00\svchost.exe | Havij 2.00 Pro.exe | ||||||||||||
User: admin Company: Microsoft Integrity Level: MEDIUM Description: Windows 8.1.7601.17587 Installation Exit code: 0 Version: 8.1.7601.17587 Modules
| |||||||||||||||
| 3896 | "C:\Users\admin\Downloads\Havij 2.00 Pro.exe" | C:\Users\admin\Downloads\Havij 2.00 Pro.exe | explorer.exe | ||||||||||||
User: admin Company: ITSecTeam Integrity Level: MEDIUM Description: Advanced SQL Injection Tool Exit code: 0 Version: 2.00 Modules
| |||||||||||||||
| 4076 | "C:\Users\admin\Downloads\Havij.exe" | C:\Users\admin\Downloads\Havij.exe | — | Havij 2.00 Pro.exe | |||||||||||
User: admin Company: ITSecTeam Integrity Level: MEDIUM Description: Advanced SQL Injection Tool Exit code: 0 Version: 1.15 Modules
| |||||||||||||||
Total events
1 323
Read events
1 244
Write events
79
Delete events
0
Modification events
| (PID) Process: | (3896) Havij 2.00 Pro.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3896) Havij 2.00 Pro.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3896) Havij 2.00 Pro.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Intel(R) Common Networking System |
Value: C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\2.00\svchost.exe | |||
| (PID) Process: | (4076) Havij.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductNonBootFiles |
Value: 1288241153 | |||
| (PID) Process: | (3440) svchost.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\93\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3440) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3440) svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (4076) Havij.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductNonBootFiles |
Value: 1288241154 | |||
| (PID) Process: | (572) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (572) svchost.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\svchost_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
3
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3896 | Havij 2.00 Pro.exe | C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\2.00\server.zip | — | |
MD5:— | SHA256:— | |||
| 3440 | svchost.exe | C:\Users\admin\AppData\Local\Temp\$inst\temp_0.tmp | — | |
MD5:— | SHA256:— | |||
| 4076 | Havij.exe | C:\Users\admin\AppData\Local\Temp\~DFD2BE23BF24C850AA.TMP | — | |
MD5:— | SHA256:— | |||
| 3896 | Havij 2.00 Pro.exe | C:\Users\admin\AppData\Roaming\Intel Corporation\Intel(R) Common User Interface\2.00\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 3896 | Havij 2.00 Pro.exe | C:\Users\admin\Downloads\Havij.exe | executable | |
MD5:— | SHA256:— | |||
| 3440 | svchost.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\8.1.7601.17587\svchost.exe | executable | |
MD5:— | SHA256:— | |||
| 3440 | svchost.exe | C:\Users\admin\AppData\Local\Temp\$inst\2.tmp | compressed | |
MD5:8708699D2C73BED30A0A08D80F96D6D7 | SHA256:A32E0A83001D2C5D41649063217923DAC167809CAB50EC5784078E41C9EC0F0F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
572 | svchost.exe | GET | — | 103.243.173.221:80 | http://chanchandomain.club/1/explorer.txt | SG | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
572 | svchost.exe | 103.243.173.221:80 | chanchandomain.club | PhoenixNAP | SG | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
chanchandomain.club |
| malicious |