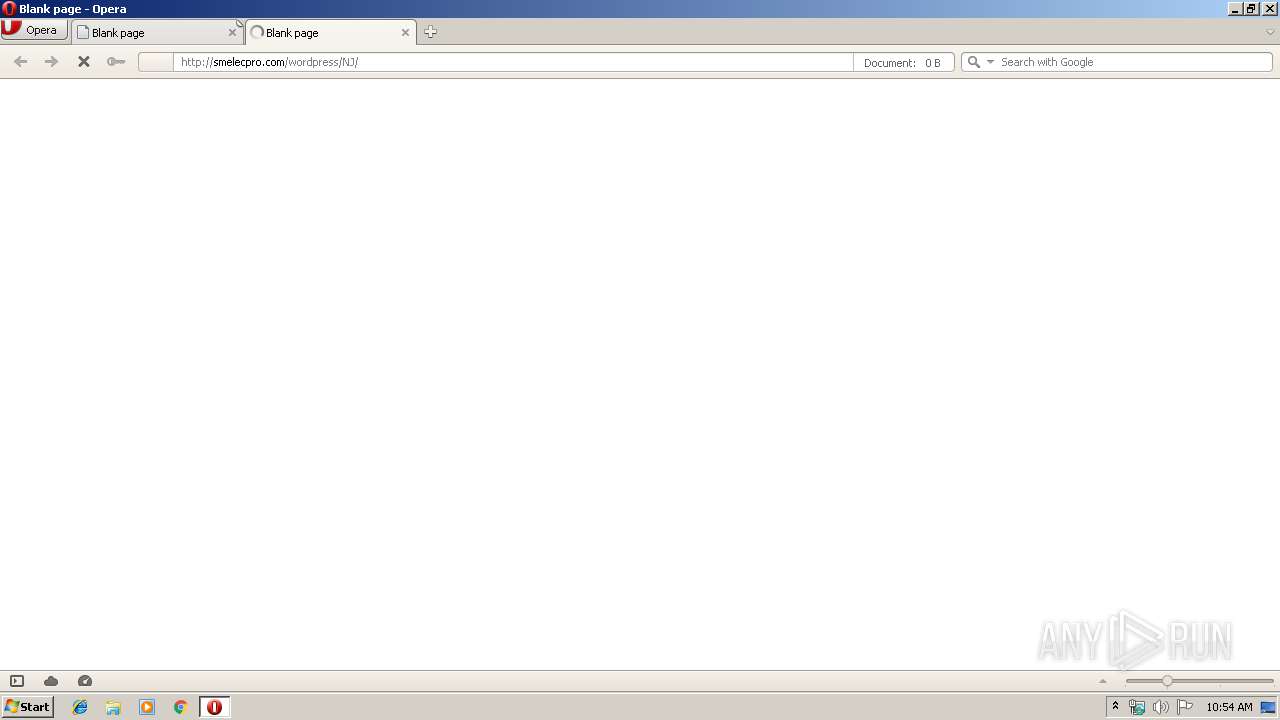
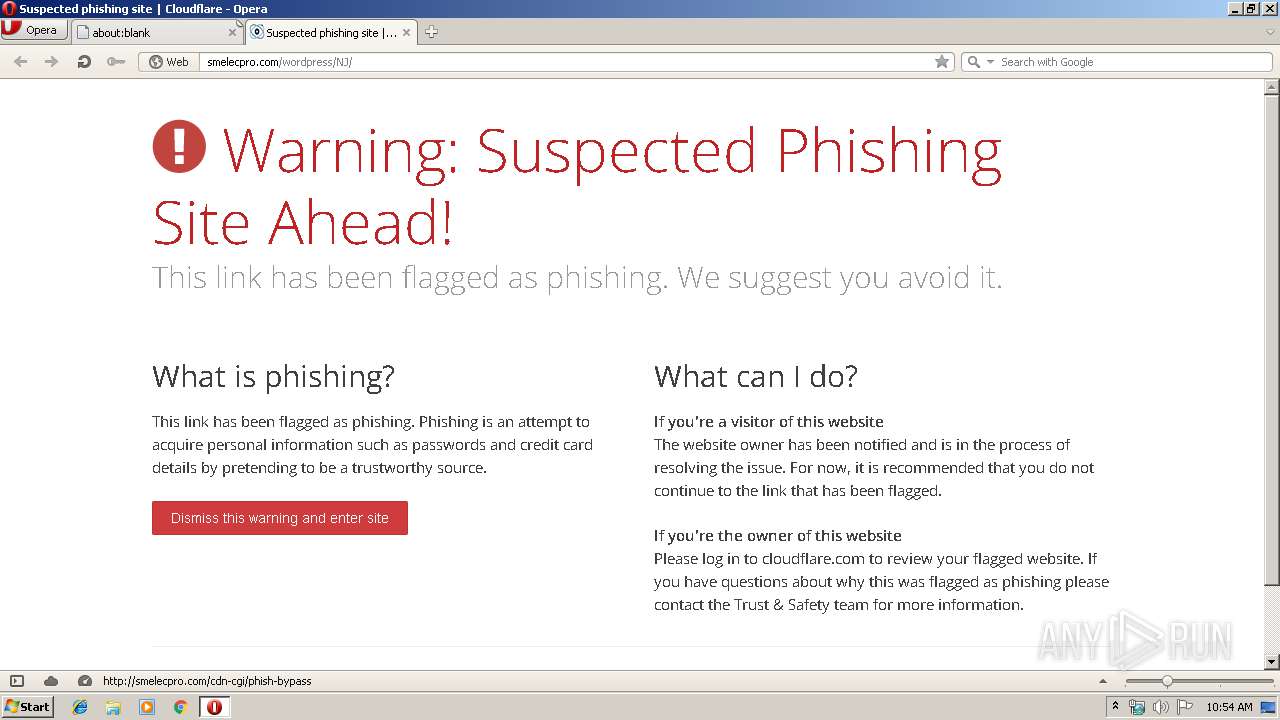
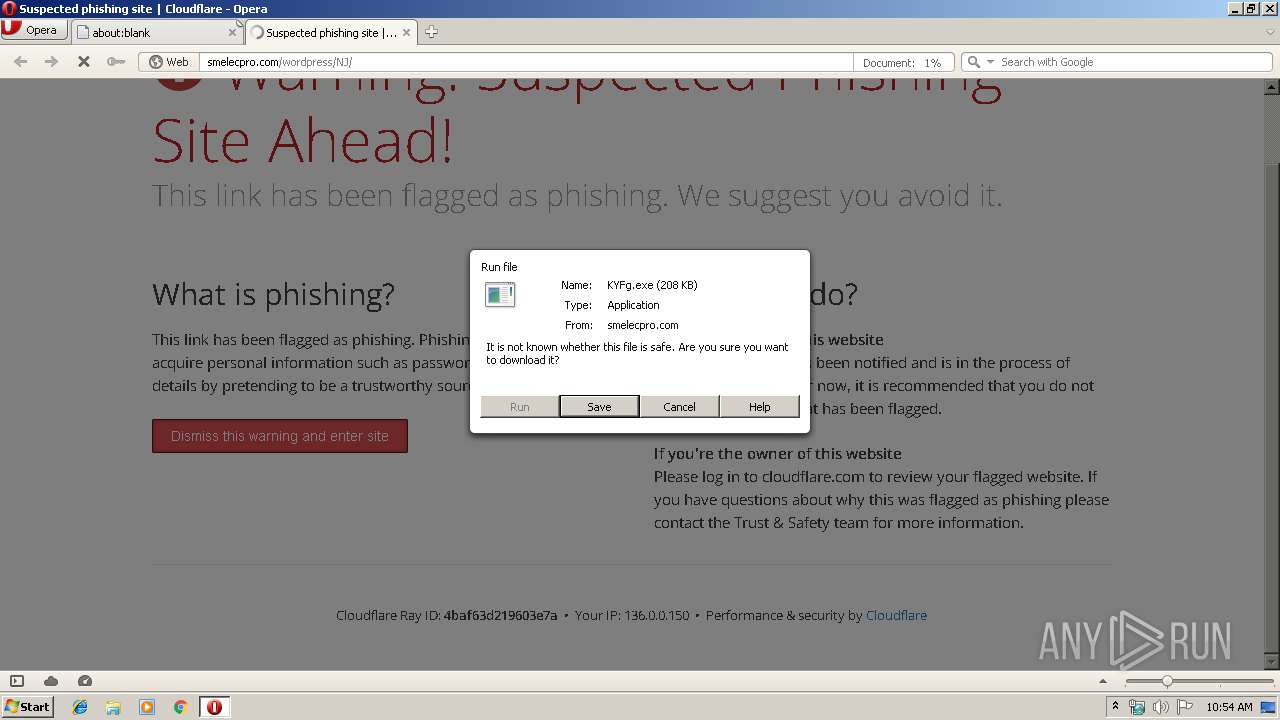
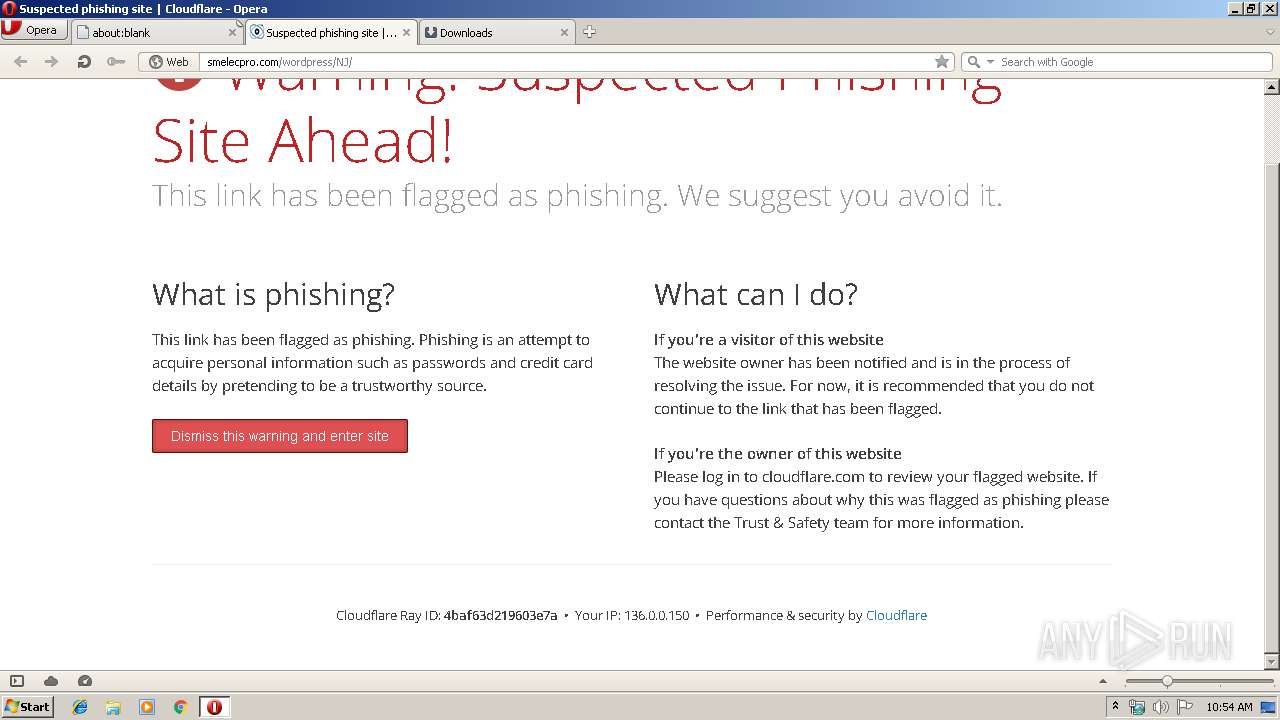
| URL: | http://smelecpro.com/wordpress/NJ/ |
| Full analysis: | https://app.any.run/tasks/d8220887-e850-4043-a361-91b7d1e277ba |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 21, 2019, 10:54:30 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 20BB73FD486669C3ED63350ACF5C4893 |
| SHA1: | E242879E6FD7BEE686C563153B474FCC466289C2 |
| SHA256: | 2B8D7376FA4E02D97954B90364FF46490A70772776010F7C0281E12E335A79B7 |
| SSDEEP: | 3:N1KNIAOCXQGwRVDxK:CaAOQ |
MALICIOUS
Downloads executable files from the Internet
- opera.exe (PID: 1476)
Application was dropped or rewritten from another process
- wabmetagen.exe (PID: 2388)
- KYFg.exe (PID: 1308)
- KYFg.exe (PID: 2692)
- wabmetagen.exe (PID: 2876)
Emotet process was detected
- wabmetagen.exe (PID: 2388)
SUSPICIOUS
Executable content was dropped or overwritten
- opera.exe (PID: 1476)
- KYFg.exe (PID: 2692)
Starts itself from another location
- KYFg.exe (PID: 2692)
Application launched itself
- KYFg.exe (PID: 1308)
- wabmetagen.exe (PID: 2388)
Connects to server without host name
- wabmetagen.exe (PID: 2876)
INFO
Creates files in the user directory
- opera.exe (PID: 1476)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
34
Monitored processes
5
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1308 | "C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\KYFg.exe" | C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\KYFg.exe | — | opera.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 1476 | "C:\Program Files\Opera\opera.exe" http://smelecpro.com/wordpress/NJ/ | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 2388 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | KYFg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 2692 | --d003b24c | C:\Users\admin\AppData\Local\Opera\Opera\temporary_downloads\KYFg.exe | KYFg.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
| 2876 | --9bc43e78 | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Timeline Wizard command line exe Exit code: 0 Version: 12.0.4518.1014 Modules
| |||||||||||||||
Total events
540
Read events
462
Write events
78
Delete events
0
Modification events
| (PID) Process: | (1476) opera.exe | Key: | HKEY_CURRENT_USER\Software\Opera Software |
| Operation: | write | Name: | Last CommandLine v2 |
Value: C:\Program Files\Opera\opera.exe http://smelecpro.com/wordpress/NJ/ | |||
| (PID) Process: | (1476) opera.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1476) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1476) opera.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2876) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2876) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2876) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2876) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2876) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2876) wabmetagen.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\wabmetagen_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
Executable files
4
Suspicious files
38
Text files
11
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\sessions\opr8E3D.tmp | — | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr8E3E.tmp | — | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opr8E7D.tmp | — | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\sesn\opr00001.tmp | — | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\operaprefs.ini | text | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opssl6.dat | binary | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\tasks.xml | xml | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\X3XFWJWRDEABT36UFE8G.temp | — | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Local\Opera\Opera\cache\assoc002\g_0000\opr00003.000 | ttf | |
MD5:— | SHA256:— | |||
| 1476 | opera.exe | C:\Users\admin\AppData\Roaming\Opera\Opera\opcacrt6.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
15
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1476 | opera.exe | GET | — | 185.26.182.111:80 | http://sitecheck2.opera.com/?host=smelecpro.com&hdn=v5bsu0lOzHkiADNtKbty4g== | unknown | — | — | whitelisted |
1476 | opera.exe | GET | — | 104.27.187.223:80 | http://smelecpro.com/cdn-cgi/styles/fonts/opensans-400.woff | US | — | — | malicious |
1476 | opera.exe | GET | 200 | 66.225.197.197:80 | http://crl4.digicert.com/DigiCertHighAssuranceEVRootCA.crl | US | der | 543 b | whitelisted |
1476 | opera.exe | GET | 200 | 104.27.186.223:80 | http://smelecpro.com/wordpress/NJ/ | US | html | 1.50 Kb | malicious |
1476 | opera.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEAOXQPQlVpLtFek%2BmcpabOk%3D | US | der | 471 b | whitelisted |
1476 | opera.exe | GET | 200 | 104.27.186.223:80 | http://smelecpro.com/cdn-cgi/styles/cf.errors.css | US | text | 4.77 Kb | malicious |
1476 | opera.exe | GET | 200 | 104.27.187.223:80 | http://smelecpro.com/cdn-cgi/scripts/cf.common.js | US | text | 1.94 Kb | malicious |
1476 | opera.exe | GET | 200 | 104.27.187.223:80 | http://smelecpro.com/cdn-cgi/scripts/zepto.min.js | US | text | 9.12 Kb | malicious |
1476 | opera.exe | GET | — | 104.27.186.223:80 | http://smelecpro.com/cdn-cgi/styles/fonts/opensans-300.woff | US | — | — | malicious |
1476 | opera.exe | GET | — | 104.27.187.223:80 | http://smelecpro.com/cdn-cgi/images/icon-exclamation.png?1376755637 | US | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1476 | opera.exe | 66.225.197.197:80 | crl4.digicert.com | CacheNetworks, Inc. | US | whitelisted |
1476 | opera.exe | 82.145.215.40:443 | certs.opera.com | Opera Software AS | — | whitelisted |
1476 | opera.exe | 104.27.186.223:80 | smelecpro.com | Cloudflare Inc | US | shared |
1476 | opera.exe | 185.26.182.111:80 | sitecheck2.opera.com | Opera Software AS | — | whitelisted |
1476 | opera.exe | 104.27.187.223:80 | smelecpro.com | Cloudflare Inc | US | shared |
2876 | wabmetagen.exe | 89.211.201.179:80 | — | Ooredoo Q.S.C. | QA | malicious |
1476 | opera.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
smelecpro.com |
| malicious |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1476 | opera.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1476 | opera.exe | Misc activity | ET INFO EXE - Served Attached HTTP |