| File name: | Listary.exe |
| Full analysis: | https://app.any.run/tasks/60bc50e0-1dca-4dfd-95f5-6db46c0e90c1 |
| Verdict: | Malicious activity |
| Analysis date: | November 11, 2018, 03:24:12 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | F0151470CB0ED6780C450AFB7442AFA1 |
| SHA1: | F5F7B9615DF6A3DAB9AA6178A6483BD05AB83FCF |
| SHA256: | 2B8C353207469046496F8F65A50A321A4F06DEB6CFF91A8FBF6BA074E0062FD1 |
| SSDEEP: | 98304:CW8ADj4Gf8MzI2CmfPpL8xMJ/PR5In/7mmWZhJVWX0B05zcNls:b8EBfNzI2CeLSyJ5In/imWZhJVWXe05J |
MALICIOUS
Changes the autorun value in the registry
- Listary.tmp (PID: 840)
Loads dropped or rewritten executable
- ListaryService.exe (PID: 2432)
- Listary.exe (PID: 3052)
- Listary.exe (PID: 3540)
- CrashSender1403.exe (PID: 1352)
- explorer.exe (PID: 1604)
- CrashSender1403.exe (PID: 2292)
- ListaryHookHelper32.exe (PID: 3292)
Application was dropped or rewritten from another process
- ListaryService.exe (PID: 2432)
- Listary.exe (PID: 3540)
- Listary.exe (PID: 3052)
- CrashSender1403.exe (PID: 2292)
- CrashSender1403.exe (PID: 1352)
- ListaryHookHelper32.exe (PID: 3292)
SUSPICIOUS
Executable content was dropped or overwritten
- Listary.exe (PID: 1972)
- Listary.tmp (PID: 840)
Starts SC.EXE for service management
- Listary.tmp (PID: 840)
Creates files in the user directory
- Listary.tmp (PID: 840)
- Listary.exe (PID: 3540)
- Listary.exe (PID: 3052)
Creates files in the program directory
- ListaryService.exe (PID: 2432)
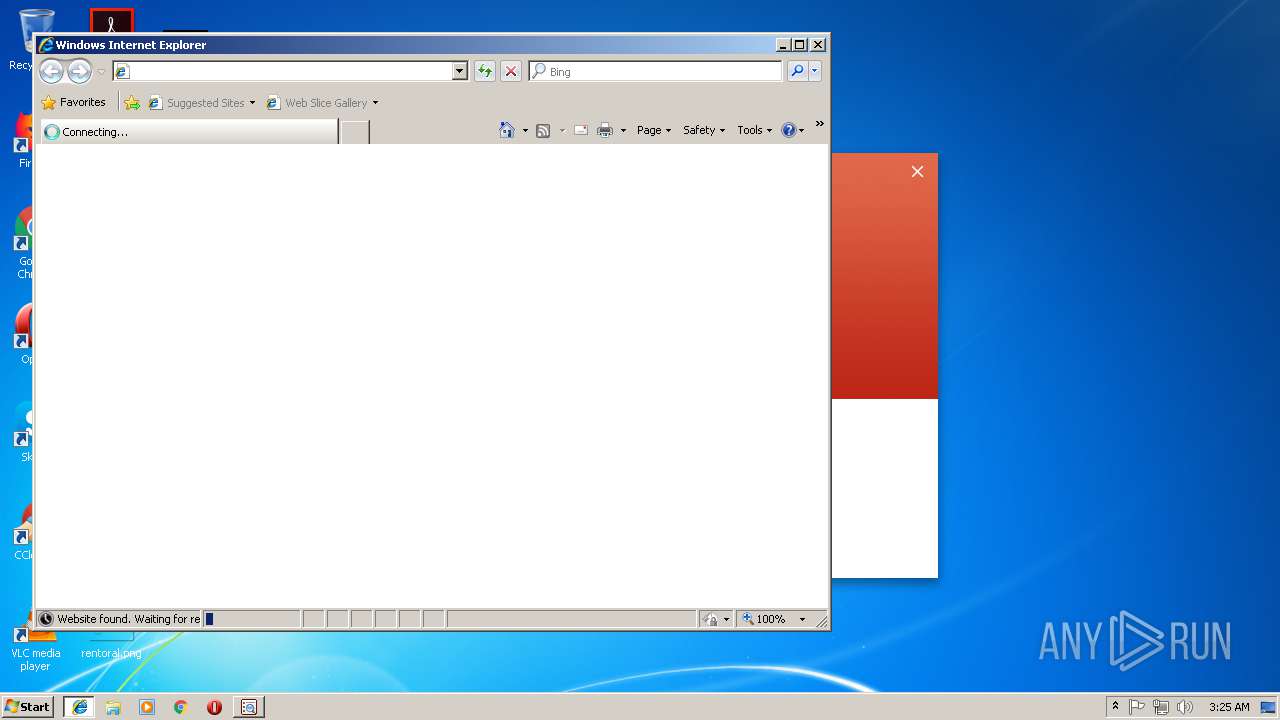
Starts Internet Explorer
- Listary.tmp (PID: 840)
INFO
Application was dropped or rewritten from another process
- Listary.tmp (PID: 840)
Loads dropped or rewritten executable
- Listary.tmp (PID: 840)
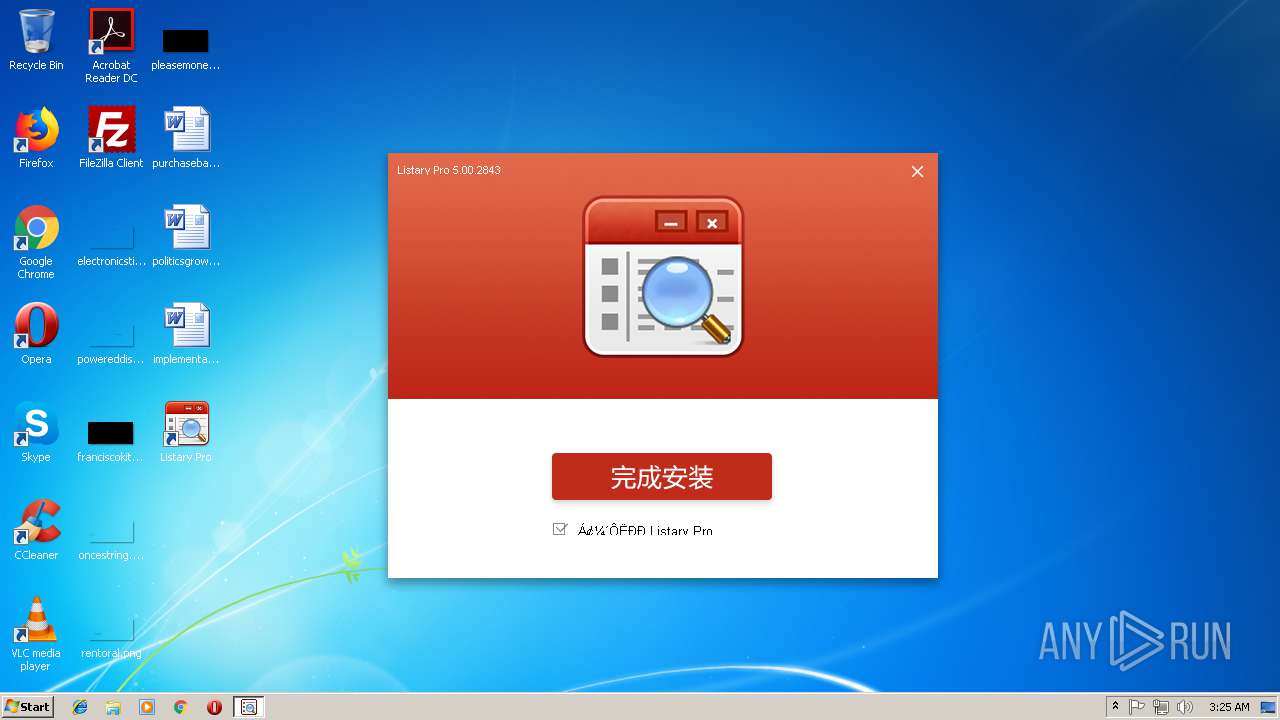
Creates a software uninstall entry
- Listary.tmp (PID: 840)
Application launched itself
- iexplore.exe (PID: 3268)
Changes internet zones settings
- iexplore.exe (PID: 3268)
Creates files in the program directory
- Listary.tmp (PID: 840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:20 00:22:17+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 37888 |
| InitializedDataSize: | 62976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x9c14 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 5.0.2843.0 |
| ProductVersionNumber: | 5.0.2843.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | 大眼仔~旭感情无限公司(Anan)国际 |
| CompanyName: | 大眼仔~旭感情无限公司 |
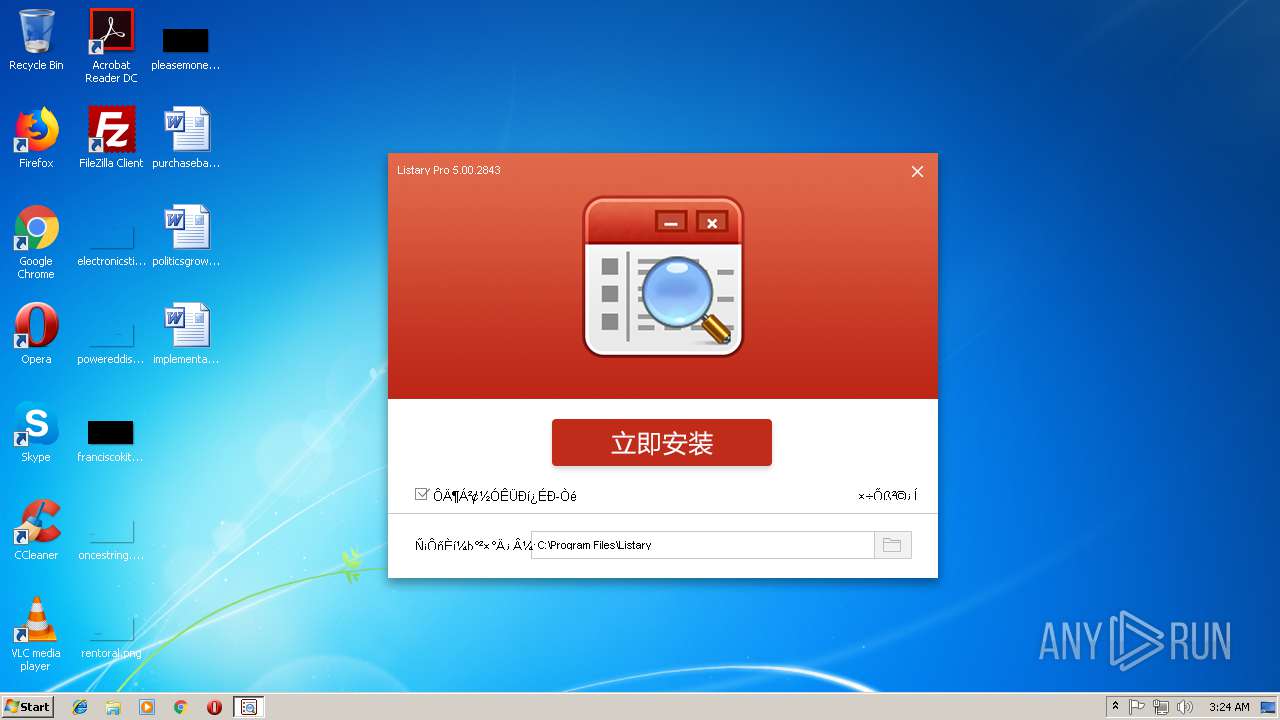
| FileDescription: | Listary 中文版 |
| FileVersion: | 5.00.2843 |
| LegalCopyright: | Copyright © 2017 大眼仔~旭感情无限公司 |
| ProductName: | Listary Pro 5.00 Build 2843 |
| ProductVersion: | 5.00 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 19-Jun-1992 22:22:17 |
| Detected languages: |
|
| Comments: | 大眼仔~旭感情无限公司(Anan)国际 |
| 拑䠘ࠀ귘t: | 긨t |
| CompanyName: | 大眼仔~旭感情无限公司 |
| FileDescription: | Listary 中文版 |
| FileVersion: | 5.00.2843 |
| LegalCopyright: | Copyright © 2017 大眼仔~旭感情无限公司 |
| ProductName: | Listary Pro 5.00 Build 2843 |
| ProductVersion: | 5.00 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 19-Jun-1992 22:22:17 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
CODE | 0x00001000 | 0x00009338 | 0x00009400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.55605 |
DATA | 0x0000B000 | 0x0000024C | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.73918 |
BSS | 0x0000C000 | 0x00000E8C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0000D000 | 0x00000950 | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.43073 |
.tls | 0x0000E000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0000F000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0.204488 |
.reloc | 0x00010000 | 0x000008B0 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 0 |
.rsrc | 0x00011000 | 0x0000E524 | 0x0000E600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED | 7.25806 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.06505 | 1376 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 5.10224 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.66899 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 7.97658 | 33312 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.36049 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.4438 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 4.74554 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4089 | 3.21823 | 754 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4090 | 3.31515 | 780 | Latin 1 / Western European | UNKNOWN | RT_STRING |
4091 | 3.25024 | 718 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
48
Monitored processes
14
Malicious processes
9
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | "C:\Users\admin\AppData\Local\Temp\is-A2EC5.tmp\Listary.tmp" /SL5="$C053C,4981944,101888,C:\Users\admin\AppData\Local\Temp\Listary.exe" | C:\Users\admin\AppData\Local\Temp\is-A2EC5.tmp\Listary.tmp | Listary.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Listary\CrashSender1403.exe" "b5d875e6-563d-4b8d-8c06-bf1978b0a1ad-tmp" | C:\Program Files\Listary\CrashSender1403.exe | — | Listary.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Crash Report Delivery Module Exit code: 0 Version: 1.4.0.3 Modules
| |||||||||||||||
| 1604 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1960 | "C:\Windows\system32\sc.exe" start ListaryService | C:\Windows\system32\sc.exe | — | Listary.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1972 | "C:\Users\admin\AppData\Local\Temp\Listary.exe" | C:\Users\admin\AppData\Local\Temp\Listary.exe | explorer.exe | ||||||||||||
User: admin Company: 大眼仔~旭感情无限公司 Integrity Level: HIGH Description: Listary 中文版 Exit code: 0 Version: 5.00.2843 Modules
| |||||||||||||||
| 2264 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3268 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Listary\CrashSender1403.exe" "f4398a93-726b-4022-b4b6-98aa8be613ec-tmp" | C:\Program Files\Listary\CrashSender1403.exe | — | Listary.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Crash Report Delivery Module Exit code: 0 Version: 1.4.0.3 Modules
| |||||||||||||||
| 2432 | "C:\Program Files\Listary\ListaryService.exe" | C:\Program Files\Listary\ListaryService.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3052 | "C:\Program Files\Listary\Listary.exe" | C:\Program Files\Listary\Listary.exe | — | Listary.tmp | |||||||||||
User: admin Company: 大眼仔~旭 分享(Anan) Integrity Level: HIGH Description: Listary Exit code: 0 Version: 5.0.2843.0 Modules
| |||||||||||||||
| 3268 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | Listary.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 371
Read events
2 212
Write events
150
Delete events
9
Modification events
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 48030000D8EBB2166E79D401 | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 3631BC8C7EC77E36BCF5508B98AD7B9BC774FC9DE02E5F2C593CAE49C83B3430 | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Listary\api-ms-win-core-console-l1-1-0.dll | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 7772E5D54C92BEFB1FD65A6BB9A4D975825CF7188DFBF3F6DEC8ACF33314B1DE | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | Listary |
Value: "C:\Program Files\Listary\Listary.exe" -startup | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Listary Pro 5.00 Build 2843_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.1.ee2 (a) | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Listary Pro 5.00 Build 2843_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Listary | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Listary Pro 5.00 Build 2843_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Listary\ | |||
| (PID) Process: | (840) Listary.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Listary Pro 5.00 Build 2843_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: Listary | |||
Executable files
60
Suspicious files
0
Text files
85
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
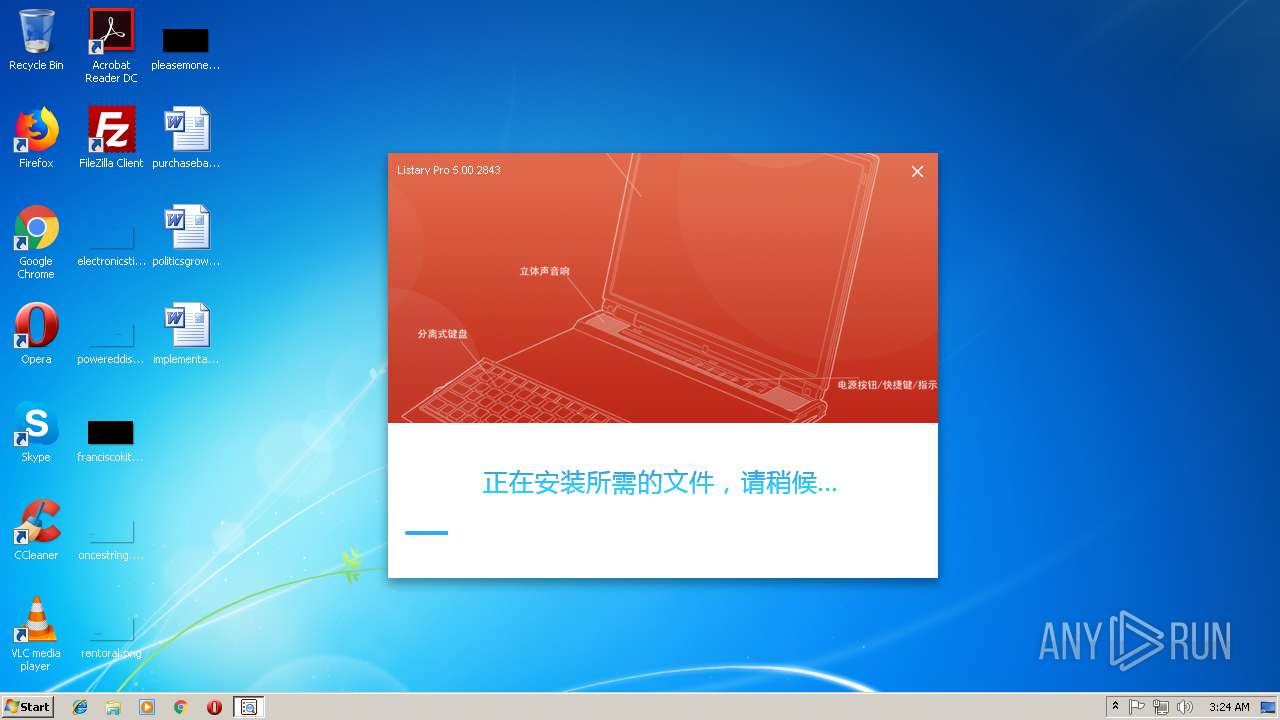
| 840 | Listary.tmp | C:\Users\admin\AppData\Local\Temp\is-LTEN5.tmp\Setup.png | image | |
MD5:DCF109F609165FFA58BD524AD98F643C | SHA256:0F0354E11C957FD17BDF1D84FFDF5ACC688B9B4EB94AF105FB751B0D0EA773CA | |||
| 840 | Listary.tmp | C:\Users\admin\AppData\Local\Temp\is-LTEN5.tmp\bg.png | image | |
MD5:4A09826133455CC08D578DF703F66812 | SHA256:9A3BEA174C636B7C1FAE818383163D0DA7B65AD87599C4EAF658AC4DA62B80CA | |||
| 1972 | Listary.exe | C:\Users\admin\AppData\Local\Temp\is-A2EC5.tmp\Listary.tmp | executable | |
MD5:AE91F5B5F959EEC980144630676AAC03 | SHA256:63608B493381240C1C413CBE401E805278B17A577A9BE2515093C5B4D7B467C0 | |||
| 840 | Listary.tmp | C:\Users\admin\AppData\Local\Temp\is-LTEN5.tmp\_isetup\_RegDLL.tmp | executable | |
MD5:0EE914C6F0BB93996C75941E1AD629C6 | SHA256:4DC09BAC0613590F1FAC8771D18AF5BE25A1E1CB8FDBF4031AA364F3057E74A2 | |||
| 840 | Listary.tmp | C:\Users\admin\AppData\Local\Temp\is-LTEN5.tmp\btn2.png | image | |
MD5:17B9B803894076EAEBB45FEF8EFD491B | SHA256:642A2DCB922F13F2E858CC5E824E58414D26DFC08579EC19509D615AD1D720AF | |||
| 840 | Listary.tmp | C:\Program Files\Listary\is-0I0IE.tmp | — | |
MD5:— | SHA256:— | |||
| 840 | Listary.tmp | C:\Users\admin\AppData\Local\Temp\is-LTEN5.tmp\botva2.dll | executable | |
MD5:0177746573EED407F8DCA8A9E441AA49 | SHA256:A4B61626A1626FDABEC794E4F323484AA0644BAA1C905A5DCF785DC34564F008 | |||
| 840 | Listary.tmp | C:\Program Files\Listary\is-4AHU2.tmp | — | |
MD5:— | SHA256:— | |||
| 840 | Listary.tmp | C:\Users\admin\AppData\Local\Temp\is-LTEN5.tmp\loading.png | image | |
MD5:7CB6CA4169B1271C27BEF3216535B069 | SHA256:73CEA4C9A4F350D158A699D29F37EA0789D8849F6844D64BE388513783A6CCEA | |||
| 840 | Listary.tmp | C:\Program Files\Listary\is-F998F.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2264 | iexplore.exe | GET | — | 211.149.181.205:80 | http://www.dayanzai.me/ | CN | — | — | unknown |
3268 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3268 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2264 | iexplore.exe | 211.149.181.205:80 | www.dayanzai.me | CHINANET SiChuan Telecom Internet Data Center | CN | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dayanzai.me |
| unknown |
www.bing.com |
| whitelisted |