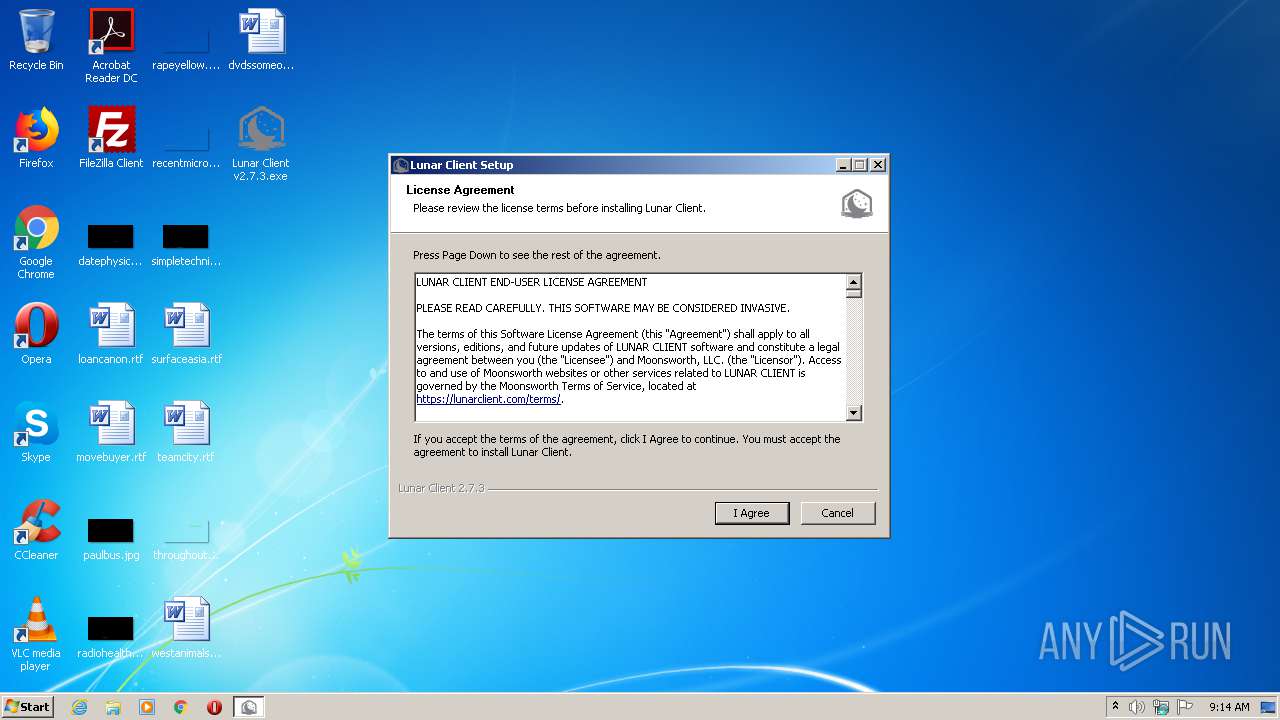
| File name: | Lunar Client v2.7.3.exe |
| Full analysis: | https://app.any.run/tasks/593aa1f3-1ca7-4b57-8c0e-d6dbeb1d4103 |
| Verdict: | Suspicious activity |
| Analysis date: | June 03, 2021, 08:14:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 8D661E81957B5BCC21C273088E34203E |
| SHA1: | BCC0F3912F53E517F0CB61C06B70661B4E4A202A |
| SHA256: | 2B802605ECE335F6FF05062BE544B40FC7E939C69391FBBAA4E930F5D621D064 |
| SSDEEP: | 12288:f8eeeeeeeeeeeeeeee7eeeeeeeeeeeeeezeeeeeeeeeeeeeeeeee7eeeeeeeeee3:f8ddMaDu173pG1szLSvJwxVh05 |
MALICIOUS
Loads dropped or rewritten executable
- Lunar Client v2.7.3.exe (PID: 1252)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2516)
Executable content was dropped or overwritten
- Lunar Client v2.7.3.exe (PID: 1252)
INFO
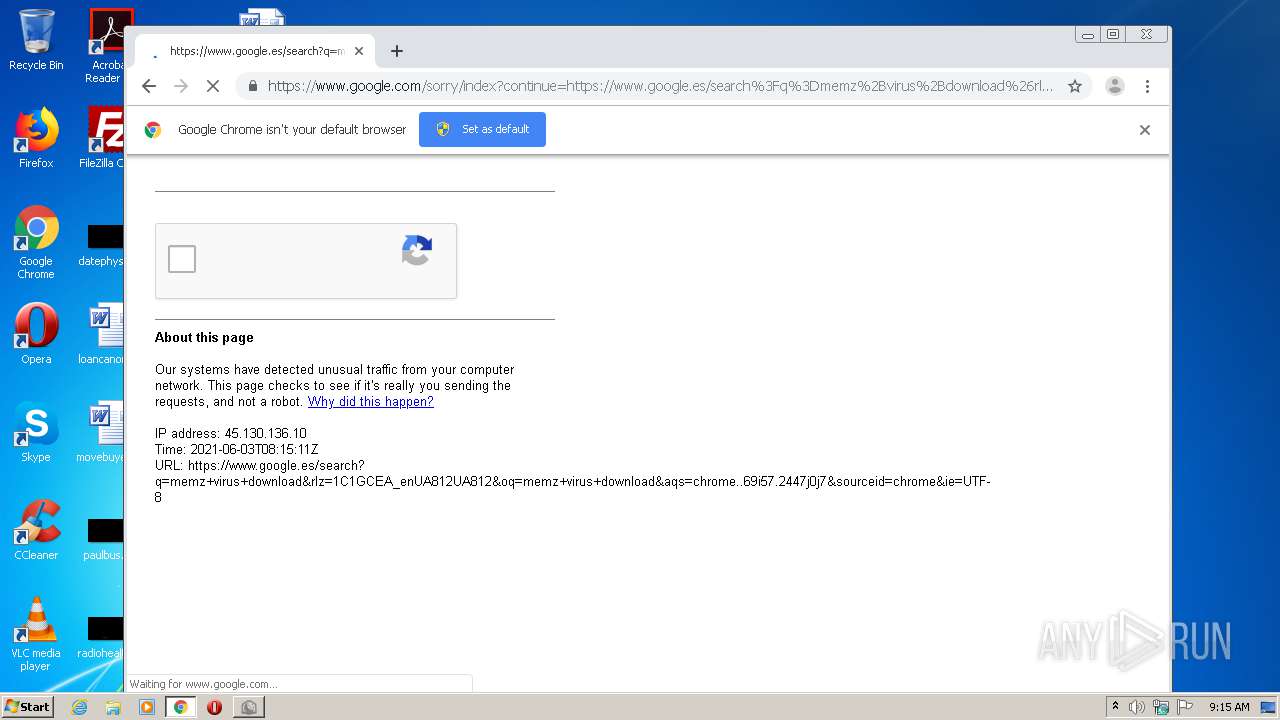
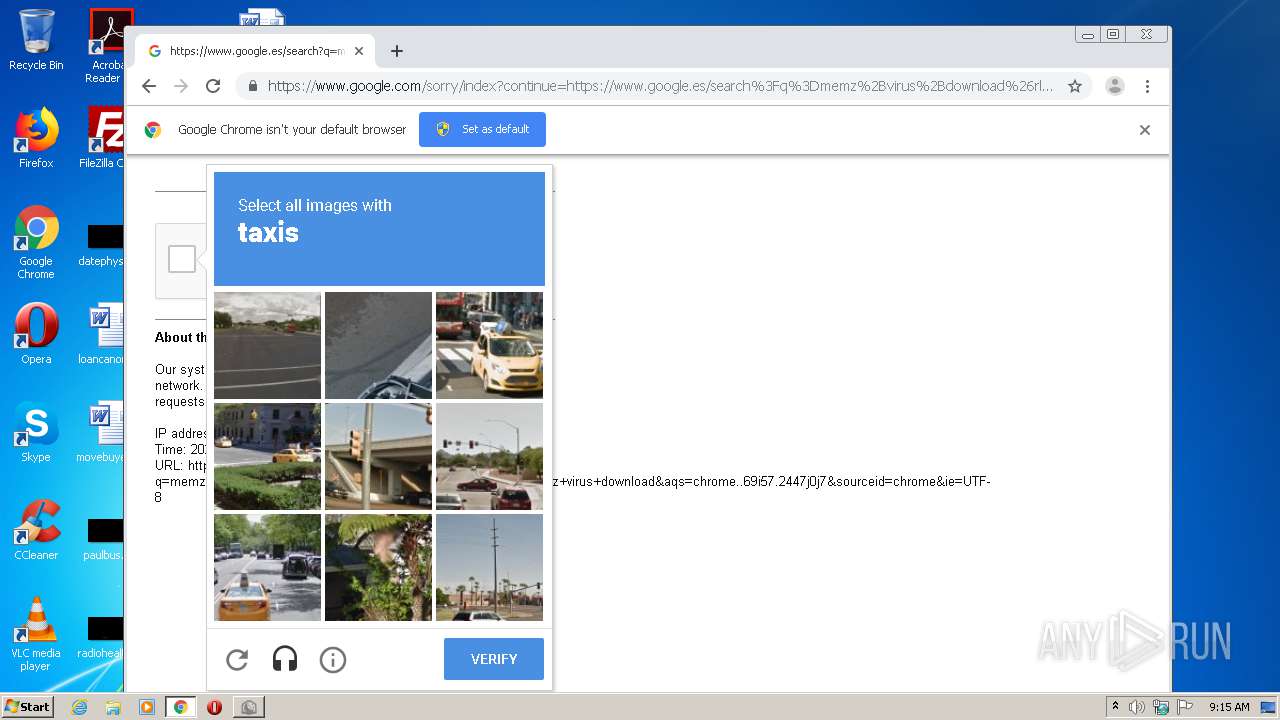
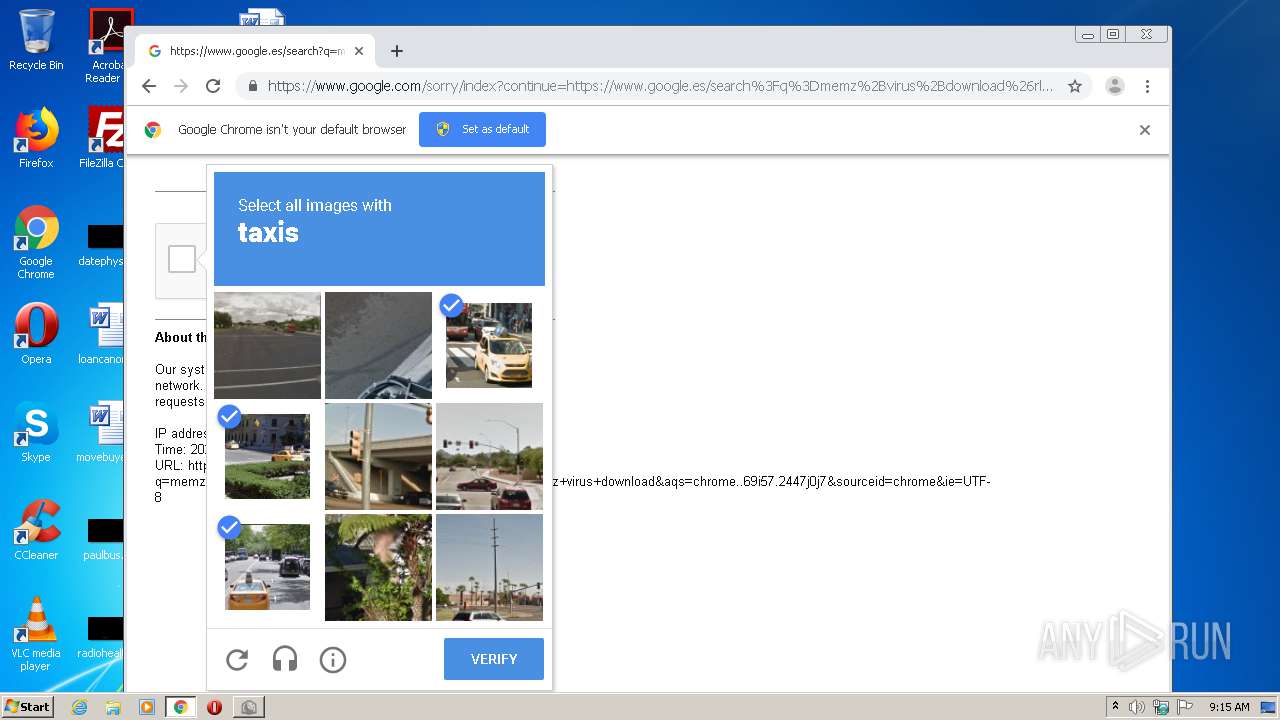
Reads the hosts file
- chrome.exe (PID: 2516)
- chrome.exe (PID: 1944)
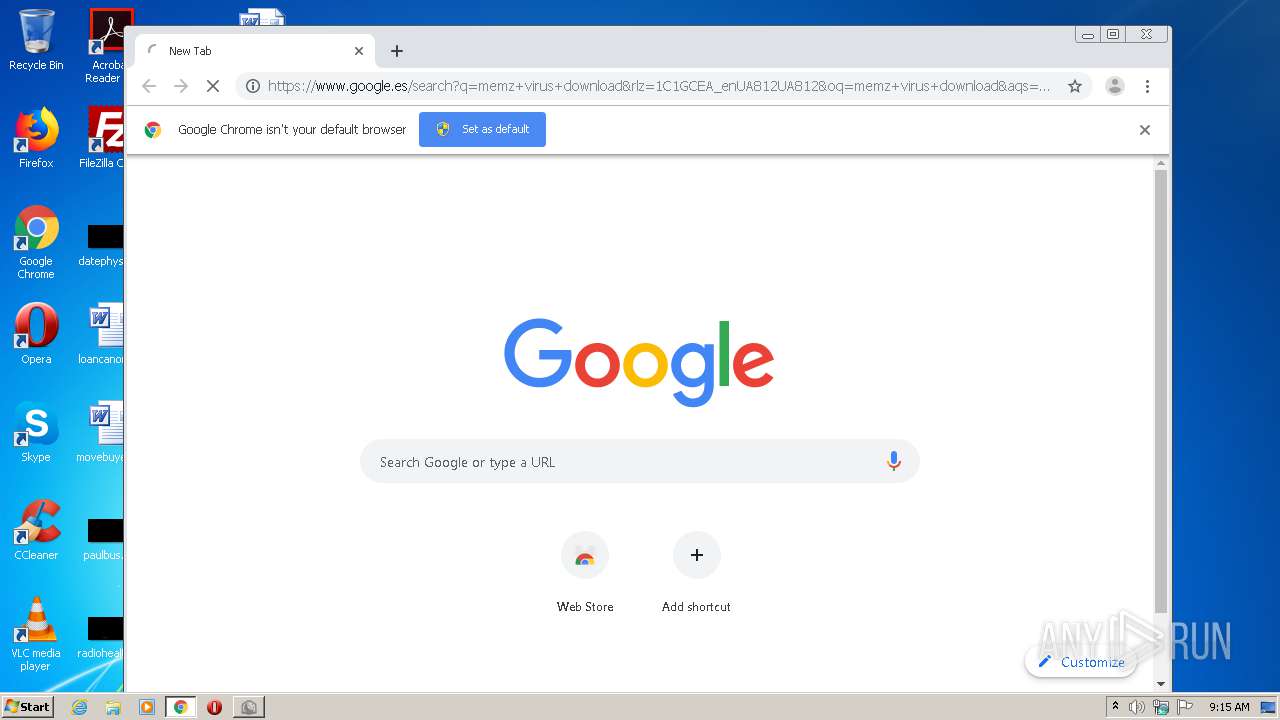
Manual execution by user
- chrome.exe (PID: 2516)
Application launched itself
- chrome.exe (PID: 2516)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| ProductVersion: | 2.7.3 |
|---|---|
| ProductName: | Lunar Client |
| LegalCopyright: | Copyright © 2021 Moonsworth, LLC |
| FileVersion: | 2.7.3 |
| FileDescription: | Lunar Client |
| CompanyName: | Moonsworth, LLC |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x0000 |
| ProductVersionNumber: | 2.7.3.0 |
| FileVersionNumber: | 2.7.3.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | 6 |
| OSVersion: | 4 |
| EntryPoint: | 0x338f |
| UninitializedDataSize: | 16384 |
| InitializedDataSize: | 473088 |
| CodeSize: | 26624 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2018:12:15 23:26:14+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Dec-2018 22:26:14 |
| Detected languages: |
|
| CompanyName: | Moonsworth, LLC |
| FileDescription: | Lunar Client |
| FileVersion: | 2.7.3 |
| LegalCopyright: | Copyright © 2021 Moonsworth, LLC |
| ProductName: | Lunar Client |
| ProductVersion: | 2.7.3 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 15-Dec-2018 22:26:14 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45028 |
.rdata | 0x00008000 | 0x000014A2 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02518 |
.data | 0x0000A000 | 0x00070FF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03712 |
.ndata | 0x0007B000 | 0x0013C000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x001B7000 | 0x00019EF0 | 0x0001A000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.1628 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.29611 | 1059 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.40993 | 16936 | UNKNOWN | English - United States | RT_ICON |
3 | 7.85547 | 5952 | UNKNOWN | English - United States | RT_ICON |
4 | 2.7701 | 4264 | UNKNOWN | English - United States | RT_ICON |
5 | 3.15002 | 1128 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 2.64216 | 76 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.89887 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
78
Monitored processes
43
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 580 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16282801167333670917 --mojo-platform-channel-handle=4604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 632 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5818495852026741480 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2244 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16998835090157153434 --mojo-platform-channel-handle=3756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 704 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4366476540676052995 --mojo-platform-channel-handle=3400 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8363875608383336545 --renderer-client-id=33 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3356 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7825807747635319175 --renderer-client-id=31 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4720 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9689208669556260764 --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10538914807198131658 --mojo-platform-channel-handle=4408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1044,12969050532267600168,16994915579634744464,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4822269475278169805 --mojo-platform-channel-handle=4304 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1252 | "C:\Users\admin\Desktop\Lunar Client v2.7.3.exe" | C:\Users\admin\Desktop\Lunar Client v2.7.3.exe | explorer.exe | ||||||||||||
User: admin Company: Moonsworth, LLC Integrity Level: MEDIUM Description: Lunar Client Exit code: 0 Version: 2.7.3 Modules
| |||||||||||||||
Total events
1 405
Read events
1 299
Write events
101
Delete events
5
Modification events
| (PID) Process: | (1392) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2516-13267181704070750 |
Value: 259 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2516) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2516-13267181704070750 |
Value: 259 | |||
Executable files
2
Suspicious files
62
Text files
230
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-60B88F88-9D4.pma | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\6d5f92fc-c412-4a0c-a25e-96512f3e2442.tmp | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF185cf0.TMP | text | |
MD5:— | SHA256:— | |||
| 1252 | Lunar Client v2.7.3.exe | C:\Users\admin\AppData\Local\Temp\nsy3CA7.tmp\StdUtils.dll | executable | |
MD5:C6A6E03F77C313B267498515488C5740 | SHA256:B72E9013A6204E9F01076DC38DABBF30870D44DFC66962ADBF73619D4331601E | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RF185d6d.TMP | text | |
MD5:— | SHA256:— | |||
| 2516 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Last Tabs | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
61
DNS requests
47
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
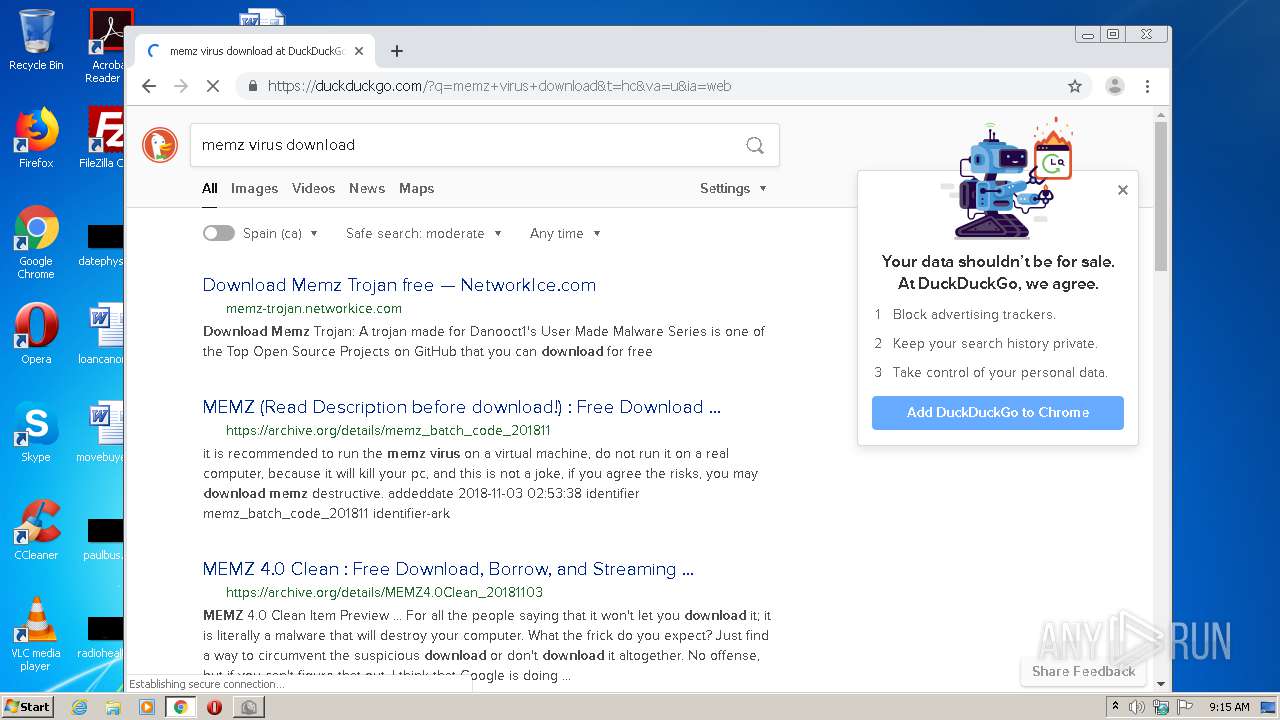
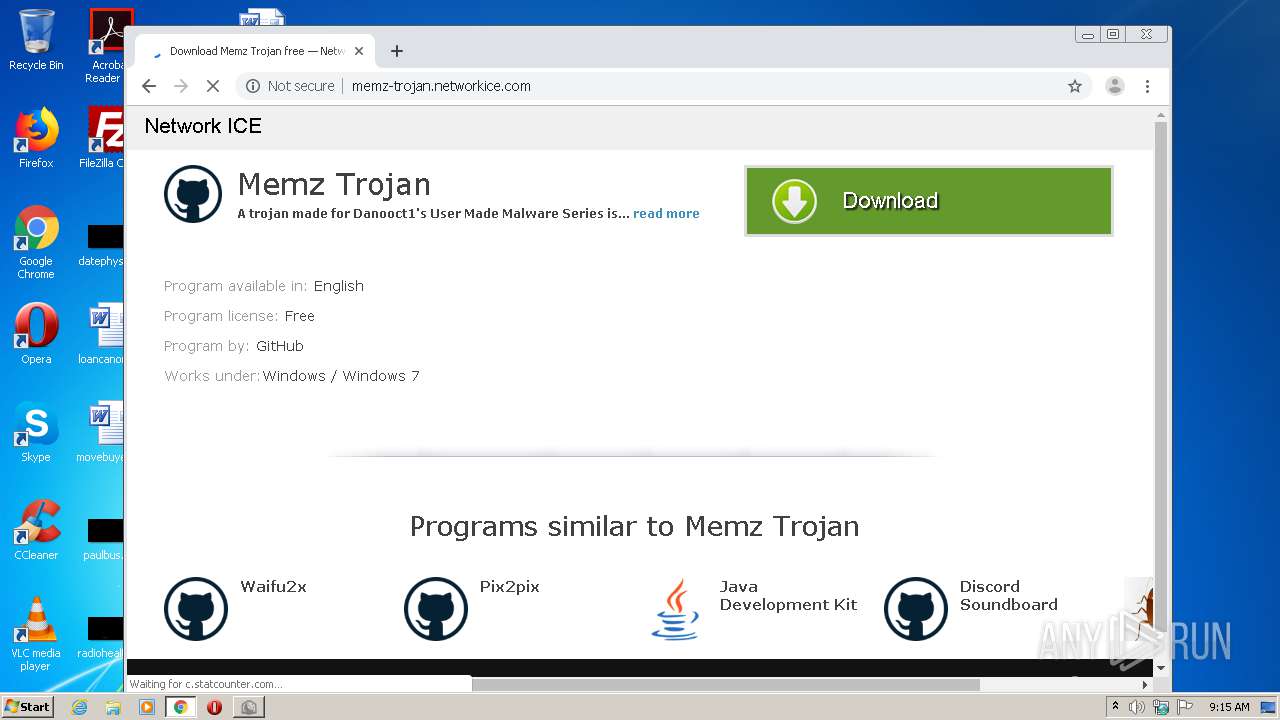
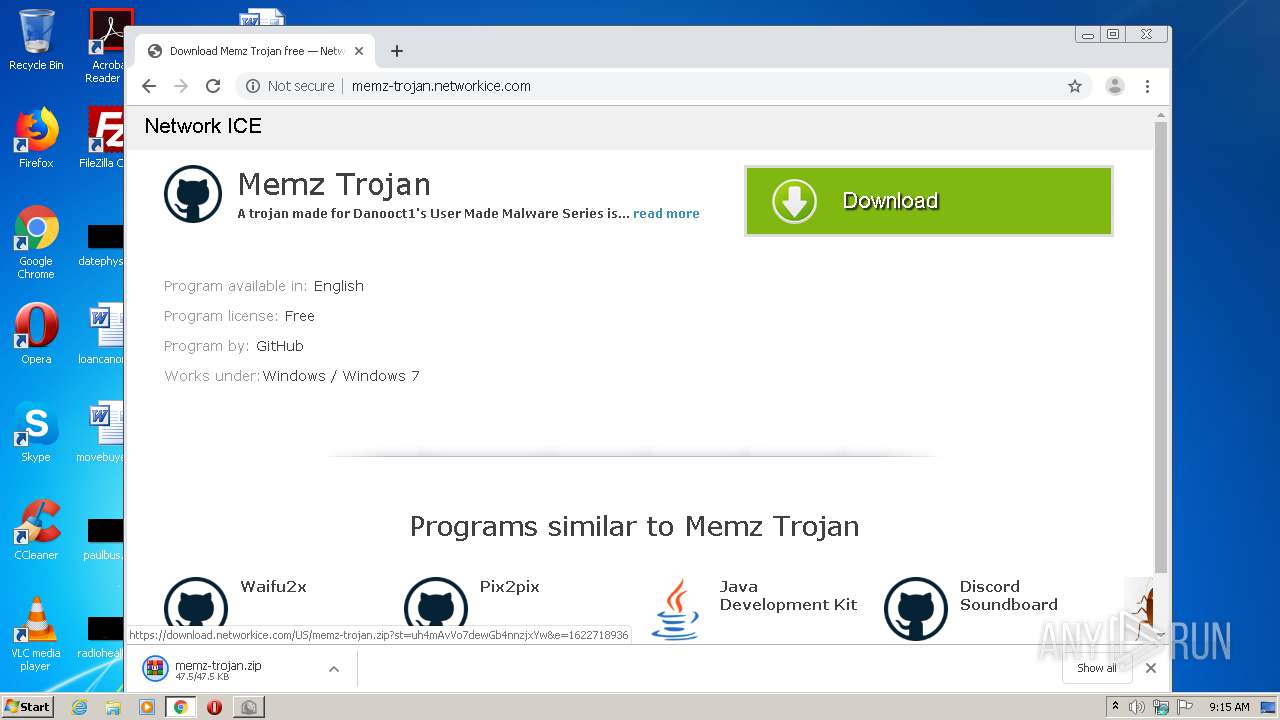
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/css/gr4/style.css?v=1616412208007 | US | text | 4.33 Kb | unknown |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/css/gr4/jquery.bxslider.css | US | text | 704 b | unknown |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/images/gr4/inner2-shadow-1.png | US | image | 2.67 Kb | unknown |
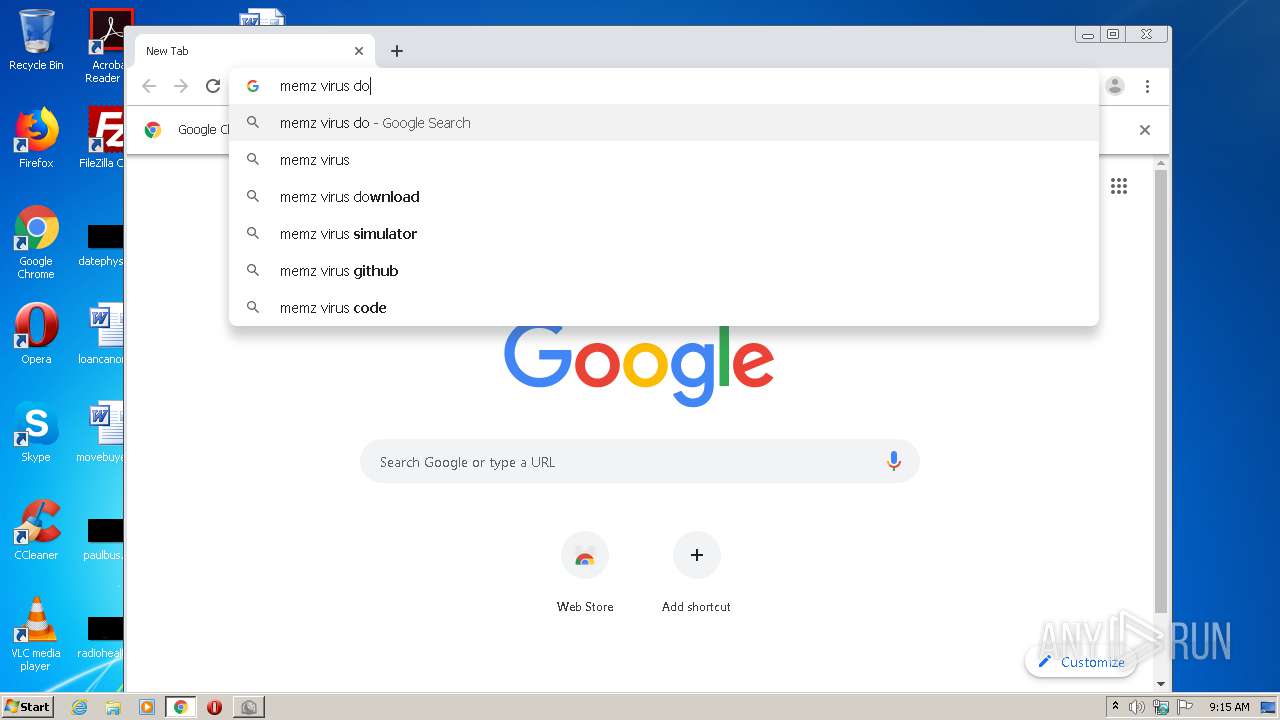
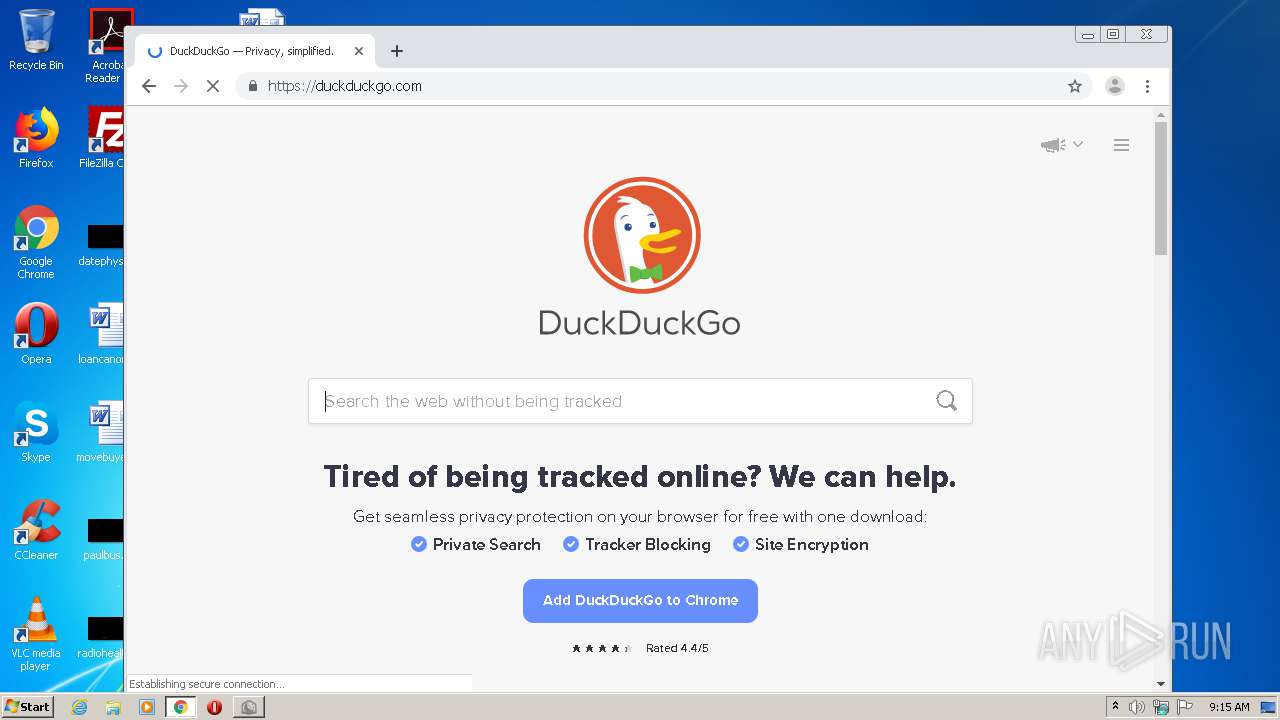
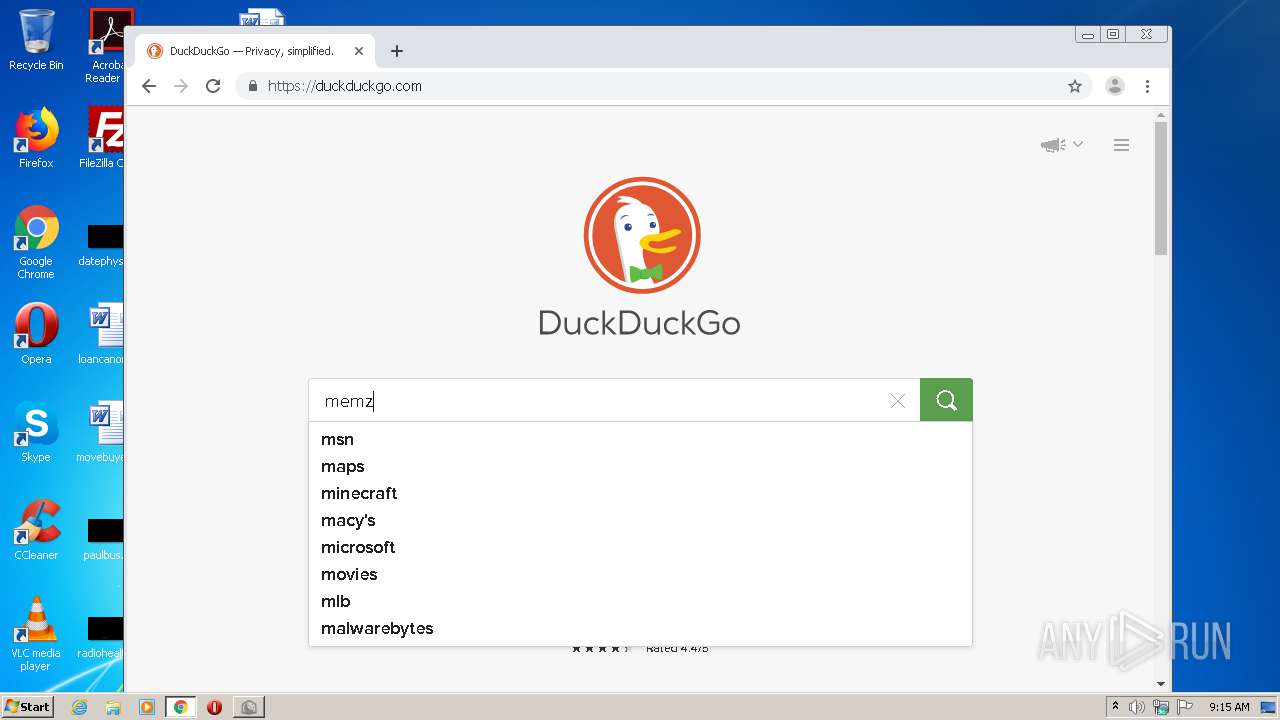
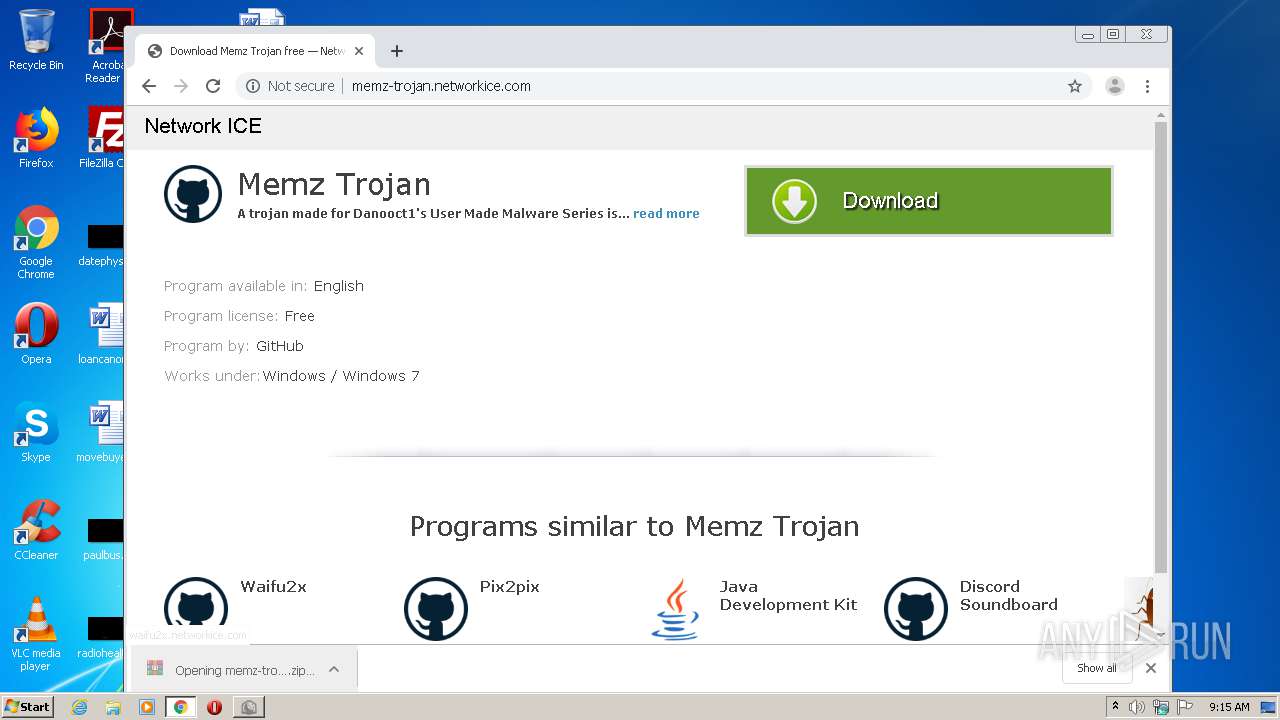
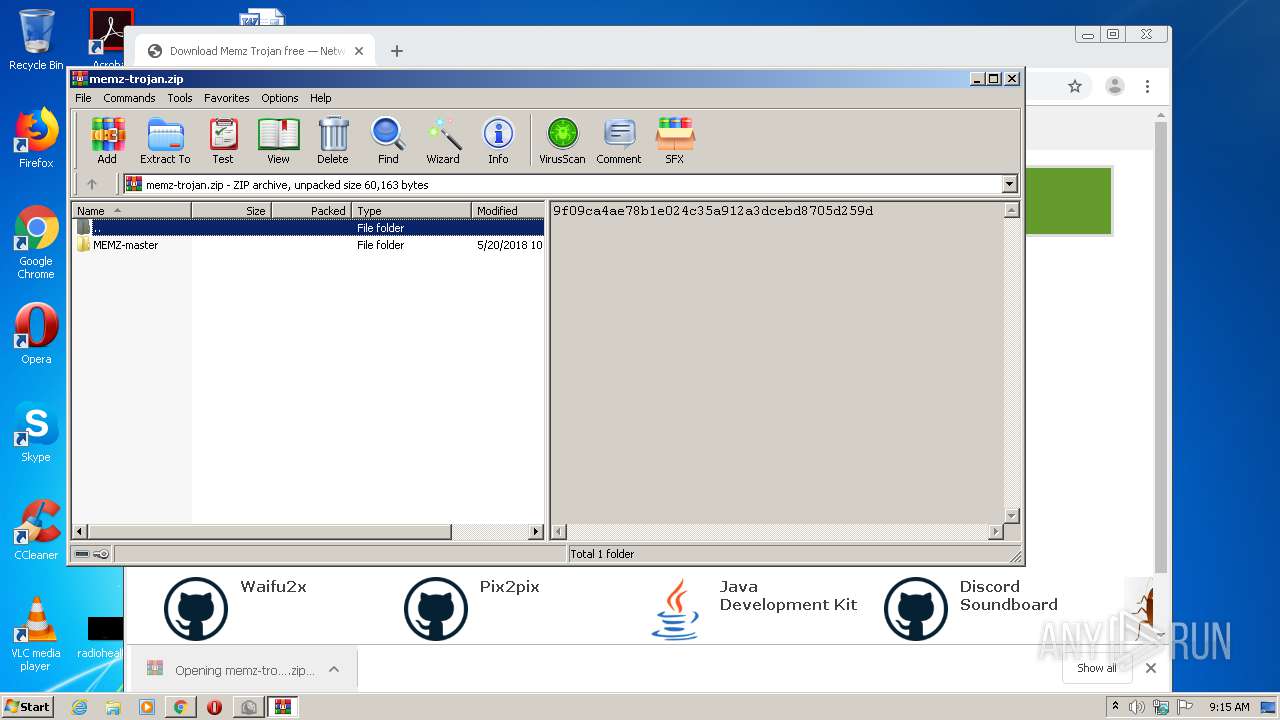
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://memz-trojan.networkice.com/ | US | html | 3.24 Kb | unknown |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/js/fresh_sw_4.js | US | text | 609 b | unknown |
1944 | chrome.exe | GET | 302 | 172.217.20.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 556 b | whitelisted |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/gen/memz-trojan-100x100.png | US | image | 6.73 Kb | unknown |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/gen/waifu2x-100x100.png | US | image | 6.73 Kb | unknown |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/gen/pix2pix-100x100.png | US | image | 6.73 Kb | unknown |
1944 | chrome.exe | GET | 200 | 162.210.197.143:80 | http://cdn.networkice.com/gen/java-development-kit-jdk-100x100.png | US | image | 9.00 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1944 | chrome.exe | 172.217.18.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 142.250.180.237:443 | accounts.google.com | Google Inc. | US | unknown |
1944 | chrome.exe | 216.58.214.238:443 | apis.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 142.250.180.238:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.19.99:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.18.68:443 | www.google.com | Google Inc. | US | whitelisted |
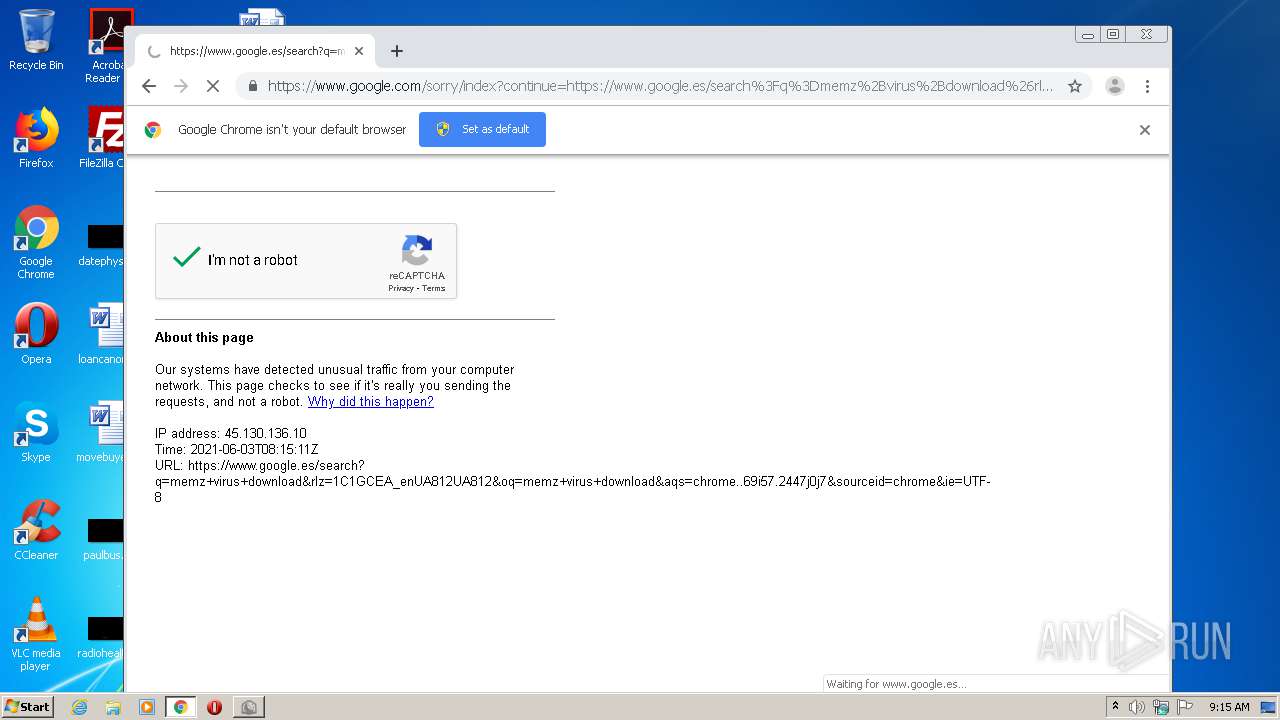
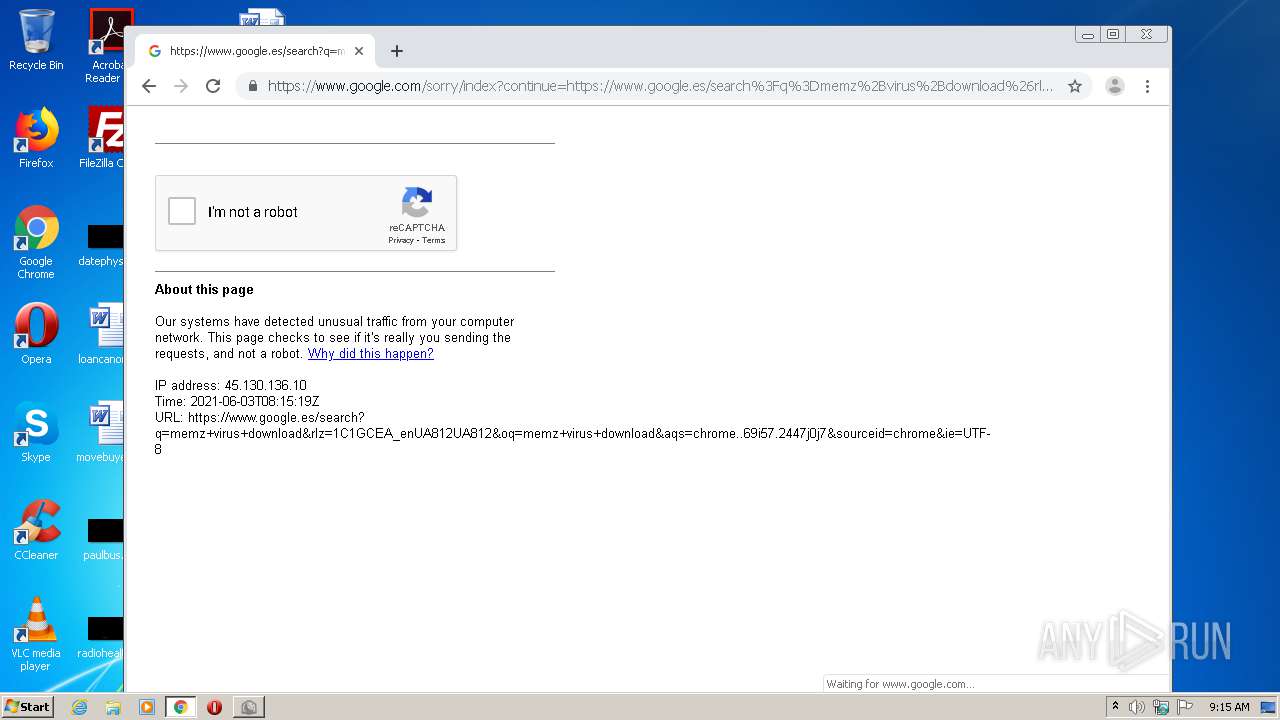
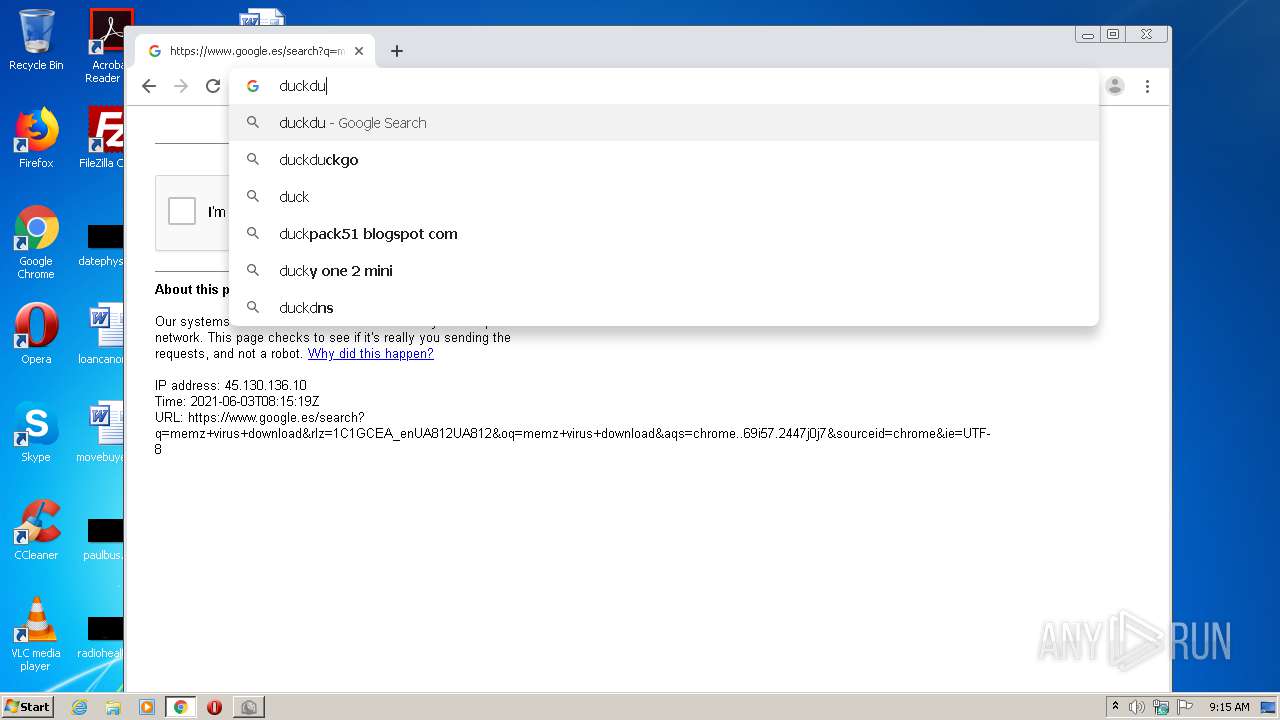
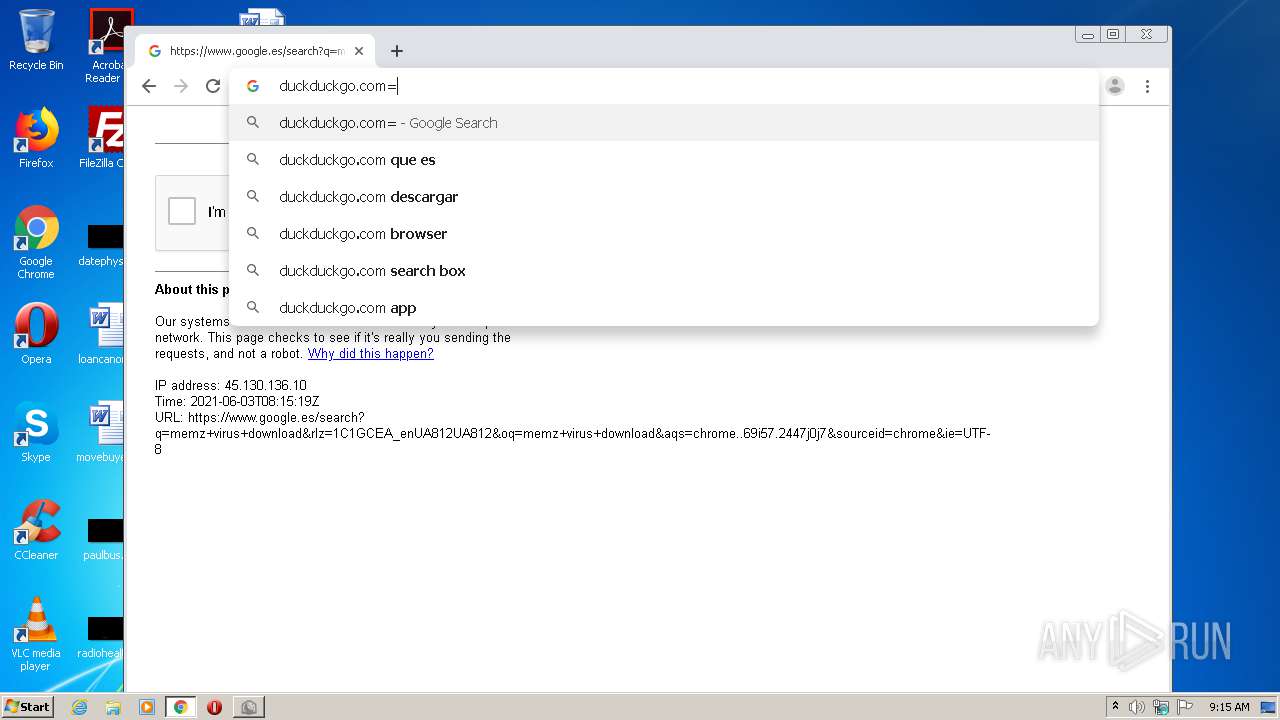
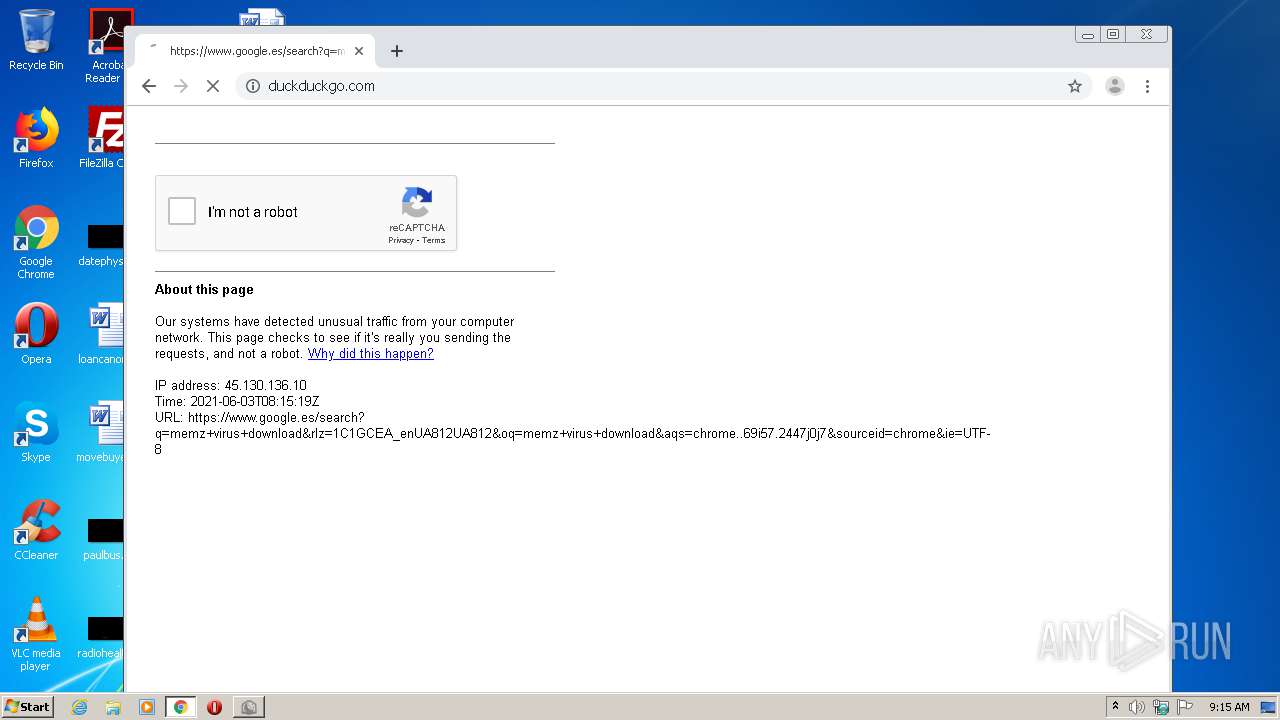
1944 | chrome.exe | 172.217.20.3:443 | www.google.es | Google Inc. | US | whitelisted |
1944 | chrome.exe | 172.217.19.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 142.250.201.193:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
1944 | chrome.exe | 142.250.184.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
www.google.com |
| malicious |
www.google.es |
| whitelisted |