| File name: | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin |
| Full analysis: | https://app.any.run/tasks/8f48051d-c038-4699-b190-8fe4a28afd37 |
| Verdict: | Malicious activity |
| Analysis date: | April 26, 2025, 11:10:41 |
| OS: | Windows 11 Professional (build: 22000, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 9 sections |
| MD5: | 9DB890EC3C47AD684CE08C90B0090DA7 |
| SHA1: | D5B9C6F09C77567A5F127B38BFAC5F9935750057 |
| SHA256: | 2B7BDF42FF60D3D2970D79903AF02CD1F4D5BC2338177A64DCB8EE527D349B20 |
| SSDEEP: | 98304:1B+yUo4FOM10at+yfTkBJDojH2Zbbrmhxxz+yc/7CsxDyGutQDXvflg6XKqSIhVK:rip5hVOHMaVQof3uibkZQUx9 |
MALICIOUS
Executing a file with an untrusted certificate
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 5740)
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
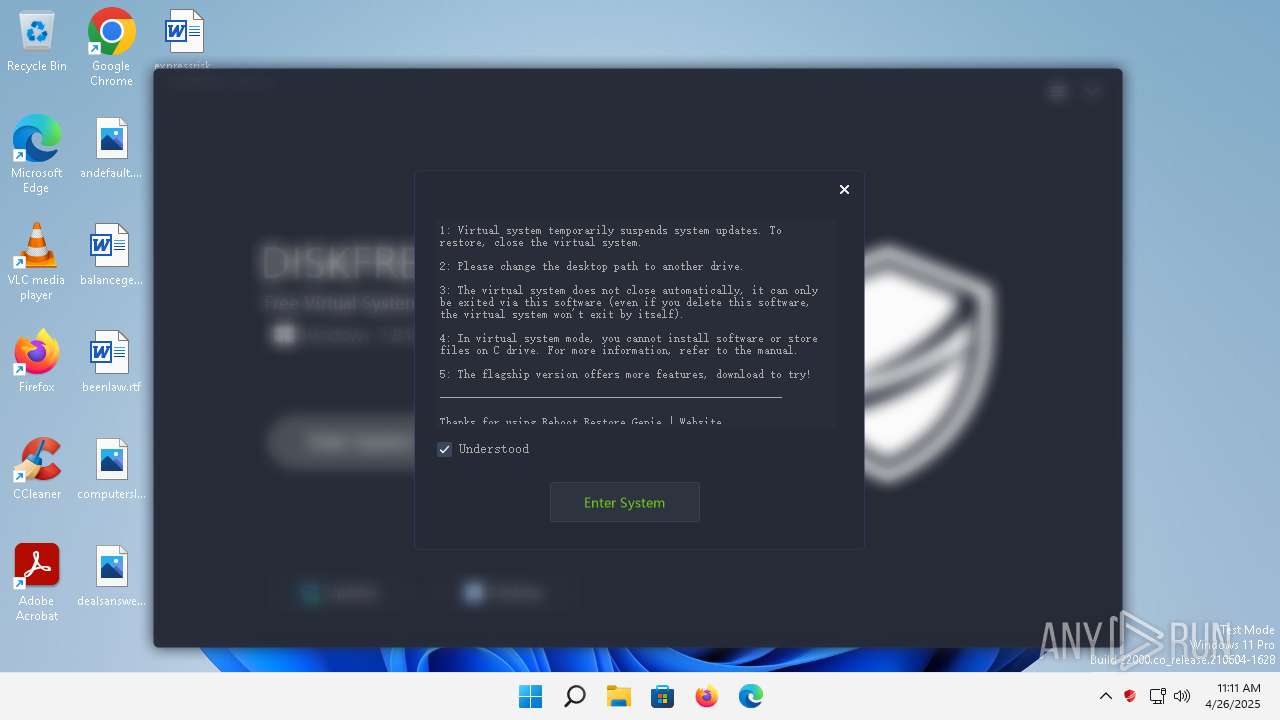
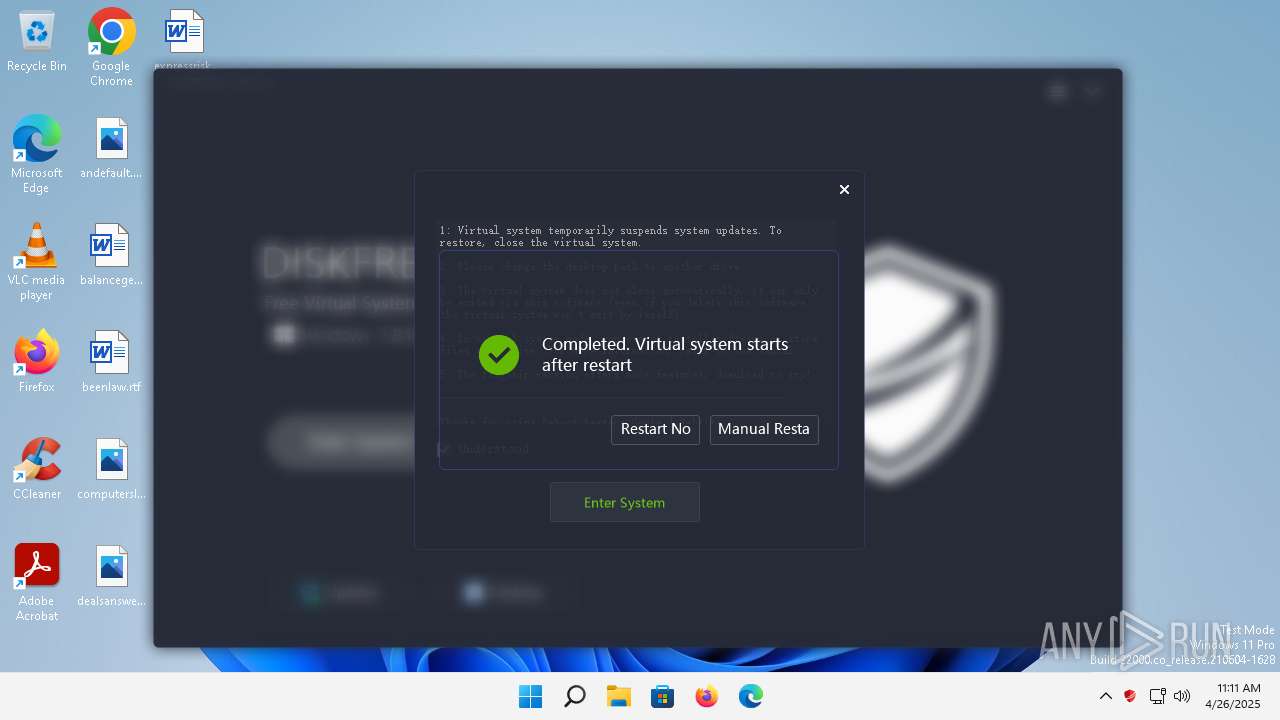
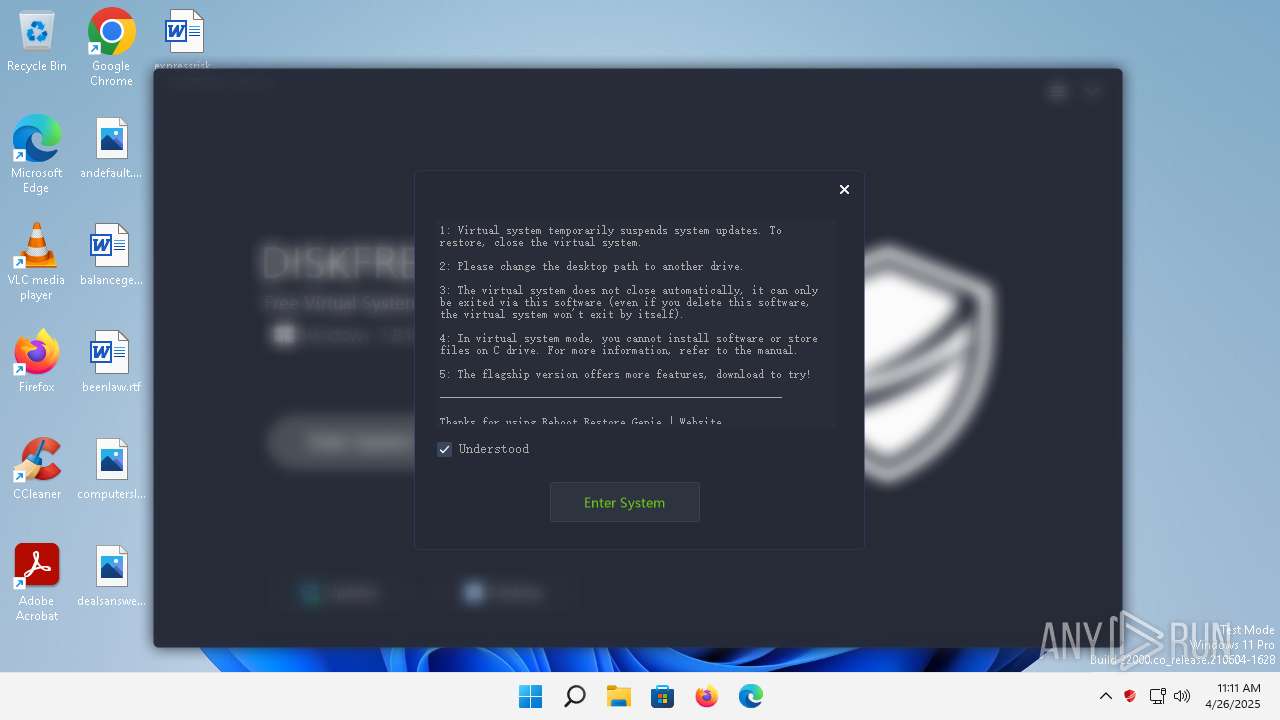
Changes the Windows auto-update feature
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
UAC/LUA settings modification
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
SUSPICIOUS
Starts CMD.EXE for commands execution
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Starts application with an unusual extension
- cmd.exe (PID: 3040)
Creates files in the driver directory
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Drops a system driver (possible attempt to evade defenses)
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Executable content was dropped or overwritten
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Reads security settings of Internet Explorer
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Reads the Internet Settings
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
- PickerHost.exe (PID: 856)
Creates file in the systems drive root
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Creates or modifies Windows services
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Uses powercfg.exe to modify the power settings
- cmd.exe (PID: 4460)
Executing commands from a ".bat" file
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 708)
- cmd.exe (PID: 1852)
The system shut down or reboot
- cmd.exe (PID: 3920)
Modifies existing scheduled task
- schtasks.exe (PID: 4288)
INFO
Checks supported languages
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
- chcp.com (PID: 4480)
Reads the computer name
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Changes file name
- cmd.exe (PID: 3996)
- cmd.exe (PID: 4816)
- cmd.exe (PID: 1684)
- cmd.exe (PID: 3920)
Create files in a temporary directory
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
The sample compiled with chinese language support
- 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe (PID: 4632)
Changes the display of characters in the console
- cmd.exe (PID: 3040)
Reads security settings of Internet Explorer
- PickerHost.exe (PID: 856)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2025:04:21 03:27:18+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 977920 |
| InitializedDataSize: | 9403392 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x13f9329 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
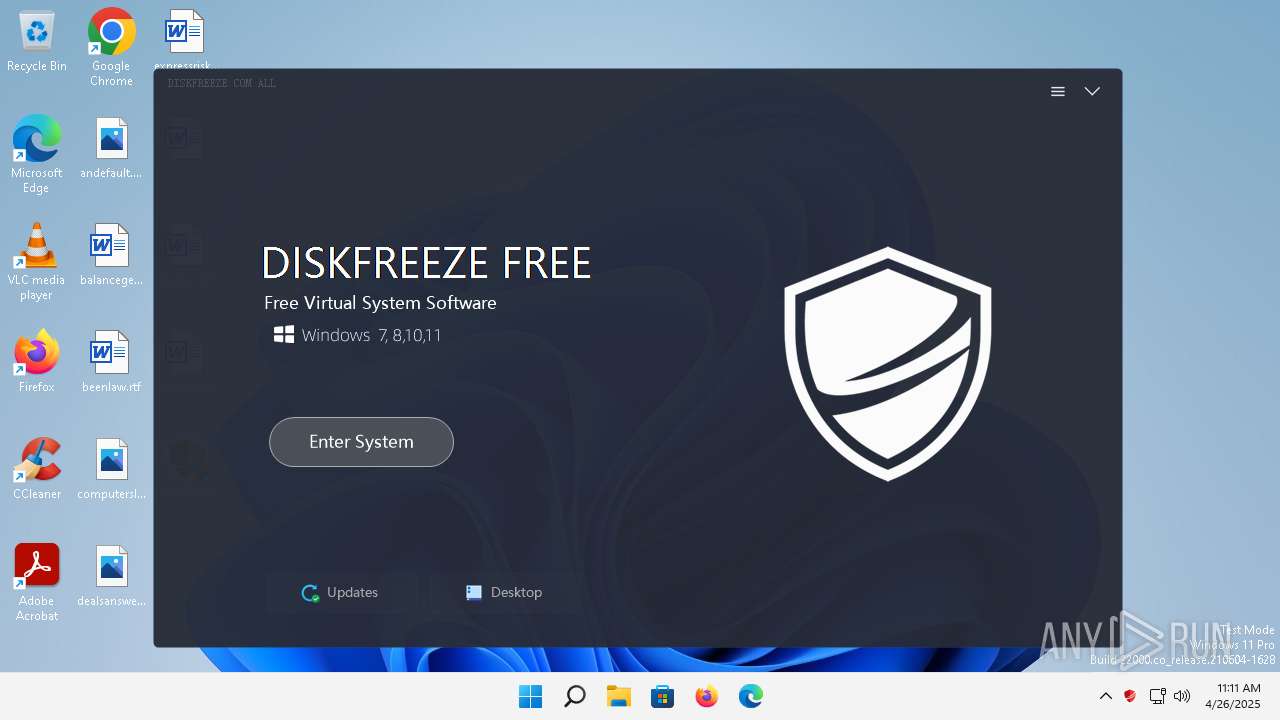
| FileVersionNumber: | 2.6.0.0 |
| ProductVersionNumber: | 2.6.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 2.6.0.0 |
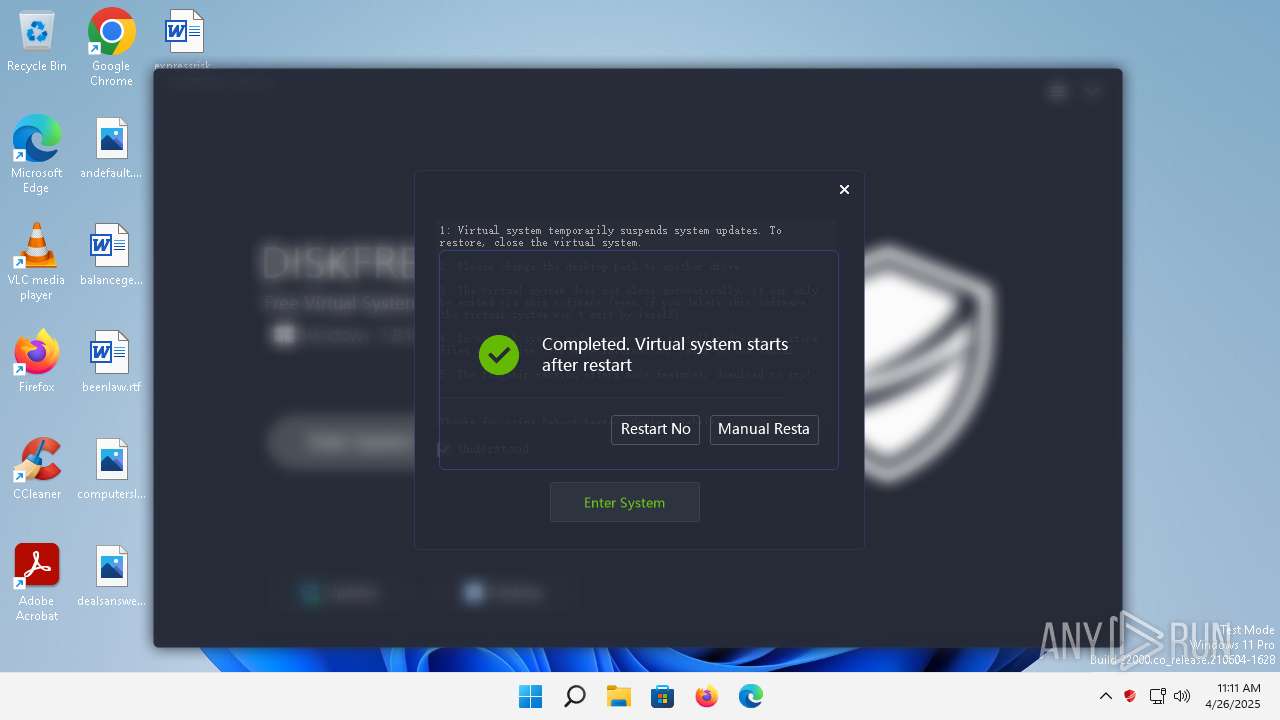
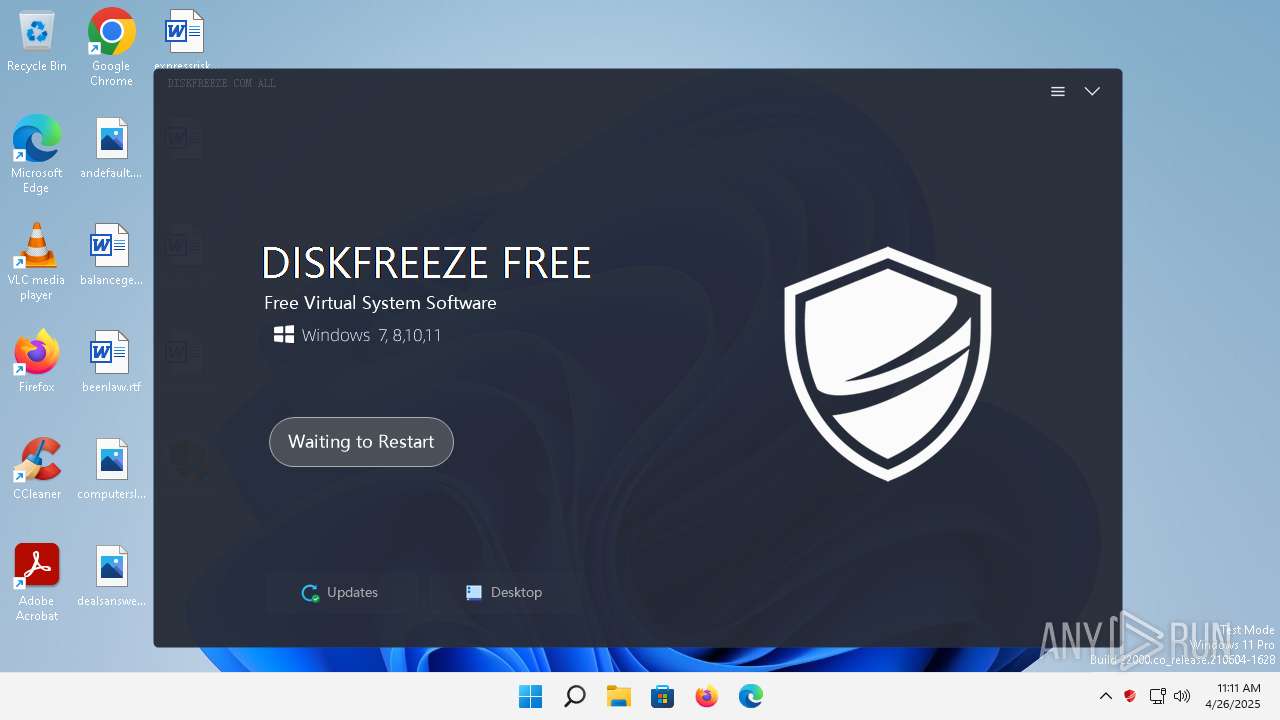
| FileDescription: | DiskFreeze Free |
| ProductName: | DiskFreeze Free |
| ProductVersion: | 2.6.0.0 |
| CompanyName: | DiskFreeze.com |
| LegalCopyright: | DiskFreeze All |
| Comments: | DiskFreeze Free |
Total processes
153
Monitored processes
50
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 136 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 708 | /c del /a/f/q "C:\Windows\System32\drivers\huanyuan.cn.sys" | C:\Windows\System32\cmd.exe | — | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 708 | cmd /c regedit /s C:\Users\admin\AppData\Local\Temp\updates.reg | C:\Windows\SysWOW64\cmd.exe | — | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | C:\Windows\System32\PickerHost.exe -Embedding | C:\Windows\System32\PickerHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: File Picker UI Host Exit code: 0 Version: 10.0.22000.653 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1056 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1072 | regedit /s C:\Users\admin\AppData\Local\Temp\updates.reg | C:\Windows\SysWOW64\regedit.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1428 | chkntfs /x c: | C:\Windows\System32\chkntfs.exe | — | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: NTFS Volume Maintenance Utility Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1684 | /c ren C:\Windows\System32\drivers\fadisk.sys fadisk_a.sys | C:\Windows\System32\cmd.exe | — | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 1 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1816 | \??\C:\Windows\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | C:\Windows\system32\cmd.exe /c C:\Users\admin\AppData\Local\Temp\updates.bat | C:\Windows\SysWOW64\cmd.exe | — | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.22000.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
2 440
Read events
2 407
Write events
30
Delete events
3
Modification events
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Class\{4d36e967-e325-11ce-bfc1-08002be10318} |
| Operation: | write | Name: | UpperFilters |
Value: partmgr | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\www.huanyuan.cn\Parameters\Files |
| Operation: | write | Name: | File0 |
Value: C:\Protect.sys | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\www.huanyuan.cn\Parameters\Files |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\www.huanyuan.cn\Parameters\Files |
| Operation: | write | Name: | File1 |
Value: C:\Windows\system32\Drivers\www.huanyuan.cn.sys | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\www.huanyuan.cn\Parameters\Files |
| Operation: | write | Name: | Count |
Value: 2 | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\www.huanyuan.cn\Parameters\Files |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (4632) 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\www.huanyuan.cn\Parameters |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
2
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4632 | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | C:\Protect.sys | — | |
MD5:— | SHA256:— | |||
| 4632 | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | C:\FRKernel.sys | — | |
MD5:— | SHA256:— | |||
| 4632 | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | C:\Windows\System32\drivers\www.huanyuan.cn.sys | executable | |
MD5:0D9BACD06BBEDFC62F6C09A10D73CD6F | SHA256:959E4CB61B28C981558EF88EB0265E2E9E60F8DA14EDA62C2F26BE84E14FD2A3 | |||
| 4632 | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | C:\Windows\SysWOW64\drivers\www.huanyuan.cn.sys | executable | |
MD5:0D9BACD06BBEDFC62F6C09A10D73CD6F | SHA256:959E4CB61B28C981558EF88EB0265E2E9E60F8DA14EDA62C2F26BE84E14FD2A3 | |||
| 4632 | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | C:\Users\admin\AppData\Local\Temp\updates.bat | text | |
MD5:4337110C623F3CC02B15FE80634361B5 | SHA256:47BBA3E31337EA4024D95D7E3E6A5AC1EF733B29994887BEF0DF02242AEE0872 | |||
| 4632 | 2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | C:\Users\admin\AppData\Local\Temp\updates.reg | text | |
MD5:4337110C623F3CC02B15FE80634361B5 | SHA256:47BBA3E31337EA4024D95D7E3E6A5AC1EF733B29994887BEF0DF02242AEE0872 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
14
DNS requests
8
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2352 | smartscreen.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
3640 | svchost.exe | GET | 200 | 23.54.109.203:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1352 | svchost.exe | GET | 200 | 23.32.238.224:80 | http://www.msftconnecttest.com/connecttest.txt | unknown | — | — | whitelisted |
2352 | smartscreen.exe | GET | 200 | 199.232.214.172:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?dec2ea3b7fac569e | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1352 | svchost.exe | 23.32.238.169:80 | — | Akamai International B.V. | DE | unknown |
2352 | smartscreen.exe | 172.211.159.152:443 | checkappexec.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2352 | smartscreen.exe | 199.232.214.172:80 | ctldl.windowsupdate.com | FASTLY | US | whitelisted |
2352 | smartscreen.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
4576 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3640 | svchost.exe | 20.190.159.68:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
3640 | svchost.exe | 23.54.109.203:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2776 | svchost.exe | 20.189.173.7:443 | v10.events.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5236 | svchost.exe | 23.212.222.21:443 | fs.microsoft.com | AKAMAI-AS | AU | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
checkappexec.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
v10.events.data.microsoft.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1352 | svchost.exe | Misc activity | ET INFO Microsoft Connection Test |
Process | Message |
|---|---|
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [FRSDK] C:\Users\admin\Desktop\2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 1276, Source: |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 1249, Source: |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [FRSDK] C:\Users\admin\Desktop\2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [FRSDK] ProductID=5 |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 1249, Source: |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 2067, Source: |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 1918, Source: |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 1276, Source: |
2b7bdf42ff60d3d2970d79903af02cd1f4d5bc2338177a64dcb8ee527d349b20.bin.exe | [RestoreDll] ErrCode: 1, Line: 1249, Source: |