| File name: | Profit (1).exe |
| Full analysis: | https://app.any.run/tasks/c54a24db-df56-4615-9474-03df6898cdbc |
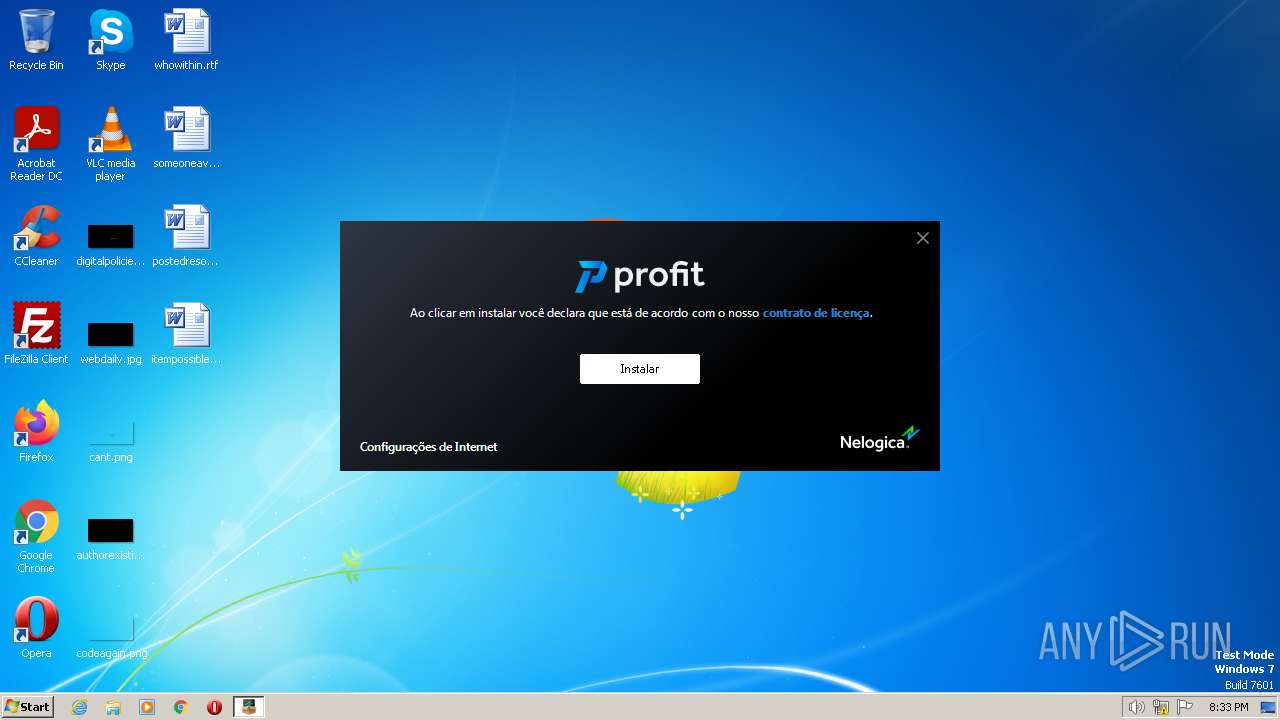
| Verdict: | Malicious activity |
| Analysis date: | June 19, 2023, 19:32:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | D2A0217A7943A47359F4CECE59D8AF51 |
| SHA1: | 731ADE581272046708CE67D333CBDD904072EAED |
| SHA256: | 2B78E2412F30FEC12BEC24EB8B84F05FA208D4407F362F5011E47897A07CE54E |
| SSDEEP: | 98304:hIBnRhiTIMzVPFpFyDisIddjmbj3PFbTRyBhWkql6M2xN1YIetcmQV7yuSzqve:URhiv3sJ3PiBhtql6M4N2IetrJzqve |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process checks if it is being run in the virtual environment
- Profit (1).exe (PID: 2768)
Executable content was dropped or overwritten
- Profit (1).exe (PID: 2768)
Reads the Internet Settings
- Profit (1).exe (PID: 2768)
Reads the Windows owner or organization settings
- Profit (1).exe (PID: 2768)
INFO
Reads the computer name
- Profit (1).exe (PID: 2768)
Checks supported languages
- Profit (1).exe (PID: 2768)
Create files in a temporary directory
- Profit (1).exe (PID: 2768)
The process checks LSA protection
- Profit (1).exe (PID: 2768)
Reads the machine GUID from the registry
- Profit (1).exe (PID: 2768)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (67.7) |
|---|---|---|
| .exe | | | Win32 EXE PECompact compressed (generic) (25.6) |
| .exe | | | Win32 Executable (generic) (2.7) |
| .exe | | | Win16/32 Executable Delphi generic (1.2) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| FileVersion: | 1.40.0.0 |
|---|---|
| FileDescription: | v1.40.0.0 |
| ProductVersion: | 1.0.0.0 |
| CompanyName: | Nelogica |
| CharacterSet: | Windows, Latin1 |
| LanguageCode: | Portuguese (Brazilian) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 1.0.0.0 |
| FileVersionNumber: | 1.40.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 5 |
| ImageVersion: | - |
| OSVersion: | 5 |
| EntryPoint: | 0x4fa47c |
| UninitializedDataSize: | - |
| InitializedDataSize: | 2888192 |
| CodeSize: | 5215744 |
| LinkerVersion: | 2.25 |
| PEType: | PE32 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| TimeStamp: | 2023:06:15 18:05:08+00:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 15-Jun-2023 18:05:08 |
| Detected languages: |
|
| CompanyName: | Nelogica |
| ProductVersion: | 1.0.0.0 |
| FileDescription: | v1.40.0.0 |
| FileVersion: | 1.40.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 11 |
| Time date stamp: | 15-Jun-2023 18:05:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x004F5B44 | 0x004F5C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44731 |
.itext | 0x004F7000 | 0x000038DC | 0x00003A00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.31048 |
.data | 0x004FB000 | 0x00028014 | 0x00028200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.66782 |
.bss | 0x00524000 | 0x000BC7B8 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x005E1000 | 0x00003EF0 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.18194 |
.didata | 0x005E5000 | 0x0000613E | 0x00006200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.0102 |
.edata | 0x005EC000 | 0x0000009B | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.8995 |
.tls | 0x005ED000 | 0x00000070 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x005EE000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.37688 |
.reloc | 0x005EF000 | 0x0006F850 | 0x0006FA00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.70435 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.25898 | 1495 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.79834 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 6.2982 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 5.71992 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 7.94692 | 21584 | UNKNOWN | English - United States | RT_ICON |
6 | 5.5575 | 9640 | UNKNOWN | English - United States | RT_ICON |
7 | 5.75785 | 4264 | UNKNOWN | English - United States | RT_ICON |
8 | 6.02985 | 1128 | UNKNOWN | English - United States | RT_ICON |
4034 | 3.21381 | 292 | UNKNOWN | UNKNOWN | RT_STRING |
4035 | 3.31589 | 576 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
gdi32.dll |
iphlpapi.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
msvcrt.dll |
netapi32.dll |
ole32.dll |
oleaut32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x00527640 |
__dbk_fcall_wrapper | 2 | 0x00012224 |
TMethodImplementationIntercept | 3 | 0x000E3954 |
Total processes
37
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2768 | "C:\Users\admin\AppData\Local\Temp\Profit (1).exe" | C:\Users\admin\AppData\Local\Temp\Profit (1).exe | explorer.exe | ||||||||||||
User: admin Company: Nelogica Integrity Level: MEDIUM Description: v1.40.0.0 Exit code: 0 Version: 1.40.0.0 Modules
| |||||||||||||||
Total events
506
Read events
506
Write events
0
Delete events
0
Modification events
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2768 | Profit (1).exe | C:\Users\admin\AppData\Local\Temp\Nelogica_2023-06-19_20-33-27\ssleay32.dll | executable | |
MD5:F9D53B2BC8209173699202F96C9FAF4C | SHA256:92EB5F3FE065CBB7A16F5B6868C9E4200BD925F21A6F6B0D2ACD2701CA0DE16C | |||
| 2768 | Profit (1).exe | C:\Users\admin\AppData\Local\Temp\Nelogica_2023-06-19_20-33-27\libeay32.dll | executable | |
MD5:851B354A6DB35473D012813DAE0C90EB | SHA256:7C02621BAF38250B9B817B88447FF793C6FA5D5D277A37E9221727555B5B8DD9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
9
DNS requests
3
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2768 | Profit (1).exe | GET | — | 108.138.36.20:80 | http://versionsdownloadserver-cdn.nelogica.com.br/files/6fb01ea7ad404b031c2187cfe9b1e177 | US | — | — | whitelisted |
2768 | Profit (1).exe | GET | — | 108.138.36.20:80 | http://versionsdownloadserver-cdn.nelogica.com.br/files/4d1377aa6715e6975ae4367da4e375c7 | US | — | — | whitelisted |
2768 | Profit (1).exe | GET | 200 | 99.84.88.20:80 | http://downloadserver-cdn.nelogica.com.br/produtos/bin/newprofit/version.txt | US | text | 4 b | malicious |
2768 | Profit (1).exe | GET | 200 | 108.138.36.20:80 | http://versionsdownloadserver-cdn.nelogica.com.br/version/pro/alpha/to/stable/pt-br | US | text | 33.7 Kb | whitelisted |
2768 | Profit (1).exe | GET | — | 108.138.36.20:80 | http://versionsdownloadserver-cdn.nelogica.com.br/files/4ae1febcf2f0bbda1d6169010a48d4df | US | — | — | whitelisted |
2768 | Profit (1).exe | GET | — | 108.138.36.20:80 | http://versionsdownloadserver-cdn.nelogica.com.br/files/00debbda9032e77d3b8b83cf59f0e6f5 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2768 | Profit (1).exe | 99.84.88.20:80 | downloadserver-cdn.nelogica.com.br | AMAZON-02 | US | suspicious |
2768 | Profit (1).exe | 108.138.36.20:80 | versionsdownloadserver-cdn.nelogica.com.br | AMAZON-02 | US | suspicious |
2768 | Profit (1).exe | 99.84.88.14:80 | downloadserver-cdn.nelogica.com.br | AMAZON-02 | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2768 | Profit (1).exe | 99.84.88.7:80 | downloadserver-cdn.nelogica.com.br | AMAZON-02 | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloadserver-cdn.nelogica.com.br |
| malicious |
dns.msftncsi.com |
| shared |
versionsdownloadserver-cdn.nelogica.com.br |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2768 | Profit (1).exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
2768 | Profit (1).exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
2768 | Profit (1).exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
2768 | Profit (1).exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
2768 | Profit (1).exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
2768 | Profit (1).exe | Potentially Bad Traffic | ET USER_AGENTS Suspicious User-Agent (Embarcadero URI Client/1.0) |
Process | Message |
|---|---|
Profit (1).exe | CreateMachineID:midDrives C:\ \Device\HarddiskVolume2 |