| File name: | services.exe |
| Full analysis: | https://app.any.run/tasks/fb074907-79e1-4364-a004-c2e2f62cb889 |
| Verdict: | Malicious activity |
| Threats: | DCrat, also known as Dark Crystal RAT, is a remote access trojan (RAT), which was first introduced in 2018. It is a modular malware that can be customized to perform different tasks. For instance, it can steal passwords, crypto wallet information, hijack Telegram and Steam accounts, and more. Attackers may use a variety of methods to distribute DCrat, but phishing email campaigns are the most common. |
| Analysis date: | December 11, 2024, 09:53:41 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | FDB968D542CF5D4E7CFF70589955A364 |
| SHA1: | B2FCF014582BADE83C856D33D3426611A609E912 |
| SHA256: | 2B75CC0DBEBAF3384EBEA43F8AD75A811FA6BB419788C4AE0CBCF3B04BF76FDD |
| SSDEEP: | 98304:yyi35GwMMZt73IGYKgefQpkxiNdOjdPI1dbAewB8whLGemtfOzKZ+bbxZA9Mdf8P:RCQdXEeovG |
MALICIOUS
Uses sleep, probably for evasion detection (SCRIPT)
- wscript.exe (PID: 6492)
DARKCRYSTAL has been detected (SURICATA)
- RuntimeBroker.exe (PID: 6264)
Connects to the CnC server
- RuntimeBroker.exe (PID: 6264)
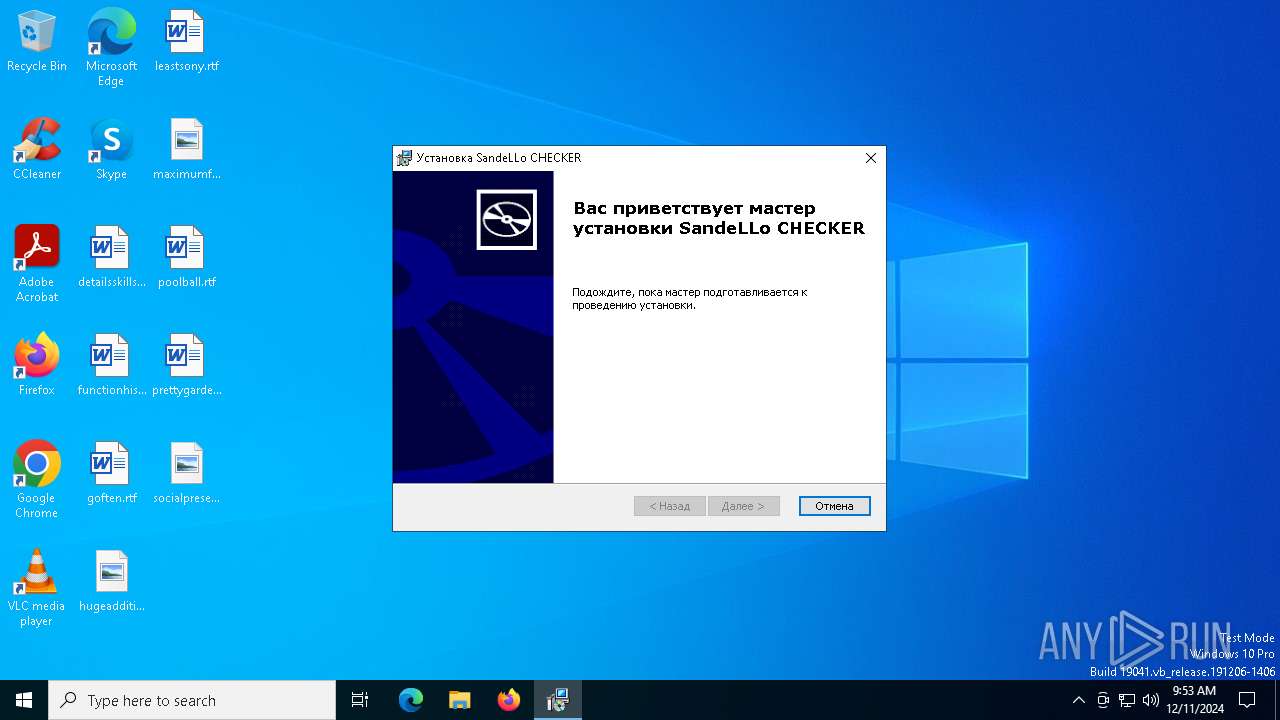
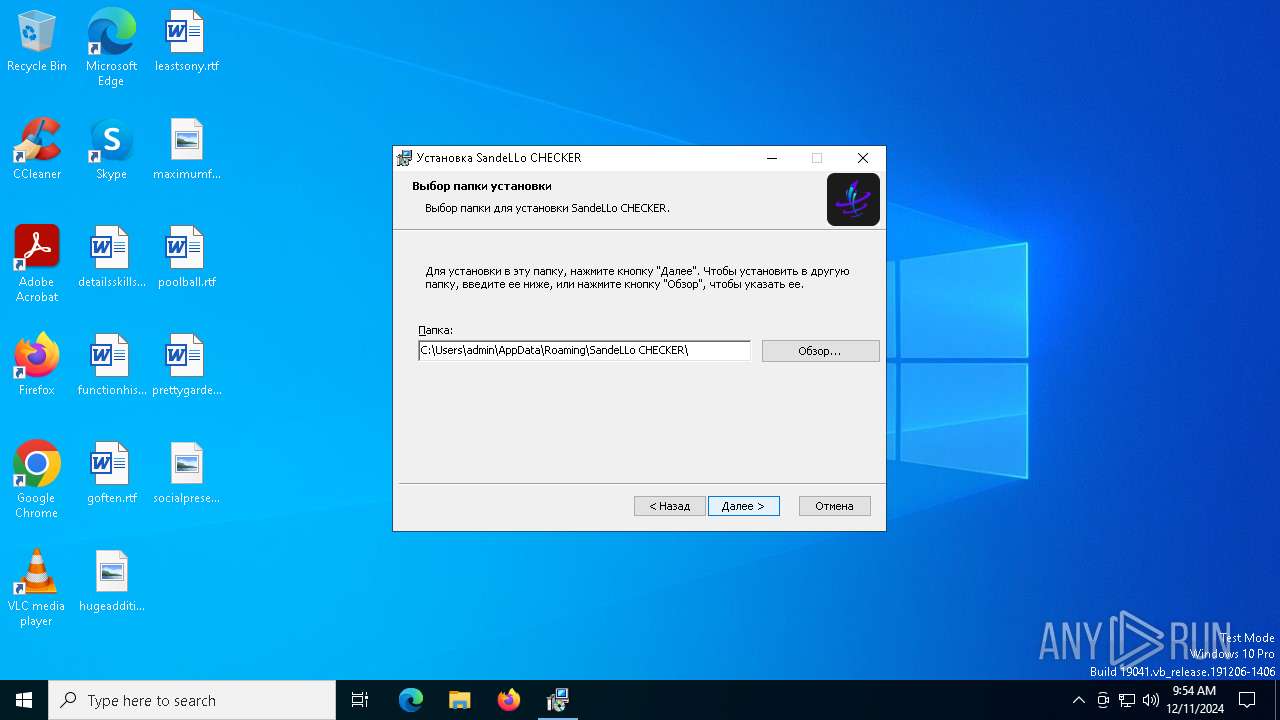
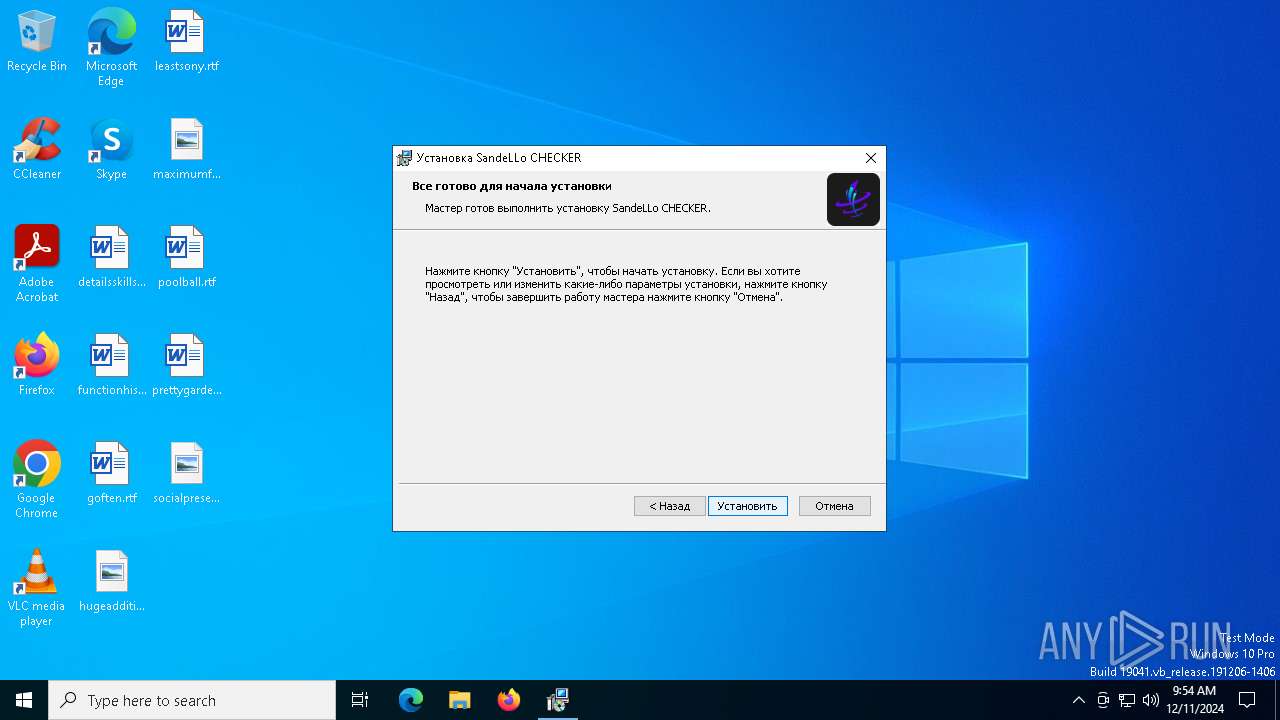
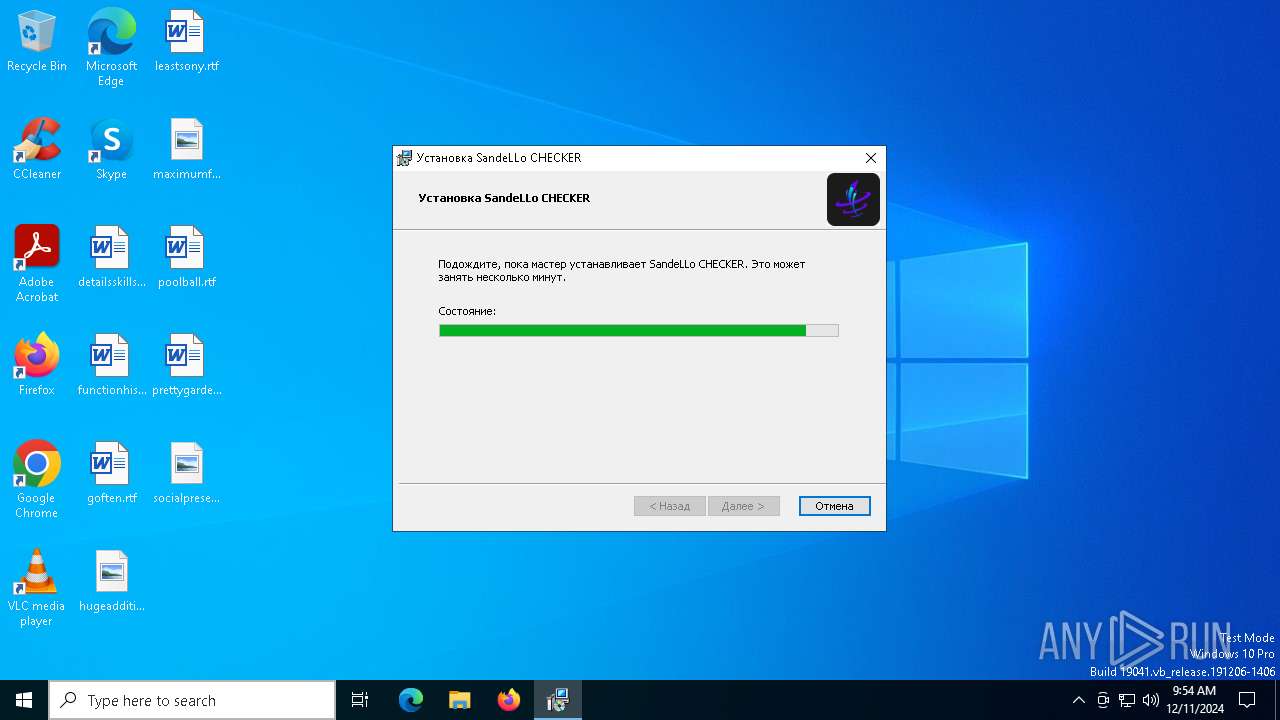
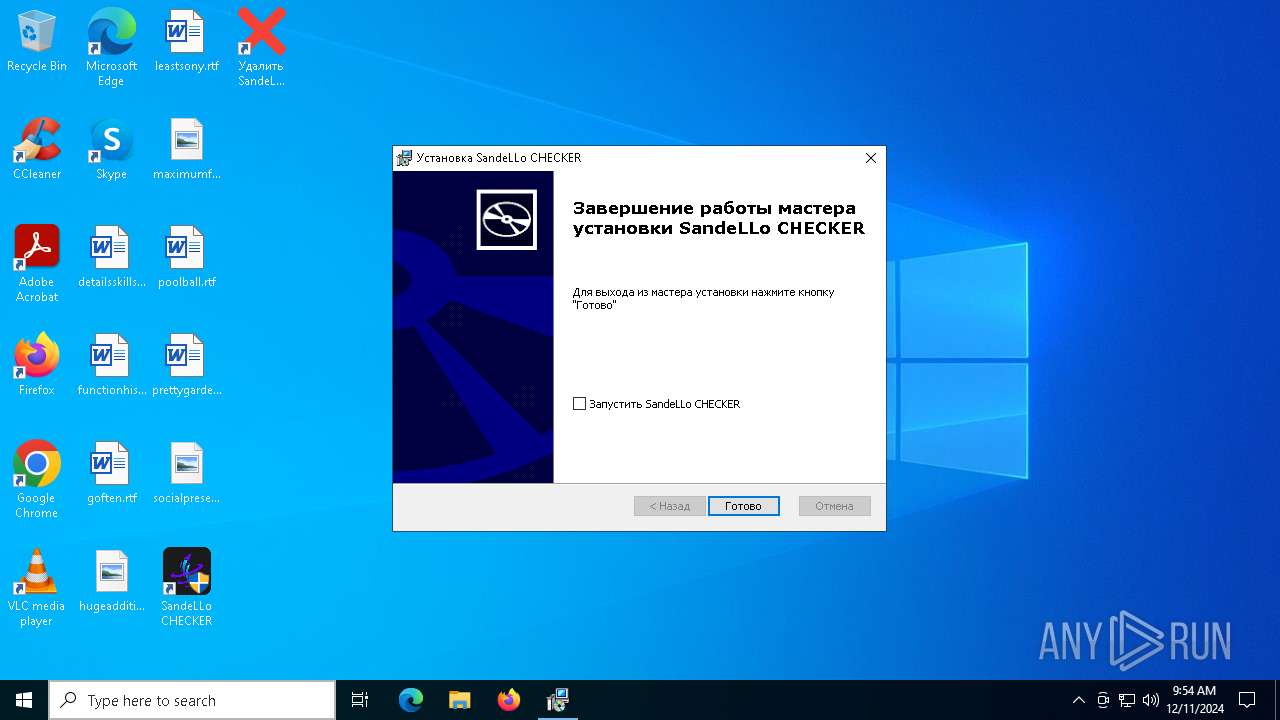
Executing a file with an untrusted certificate
- SandeLLo CHECKER.exe (PID: 1328)
SUSPICIOUS
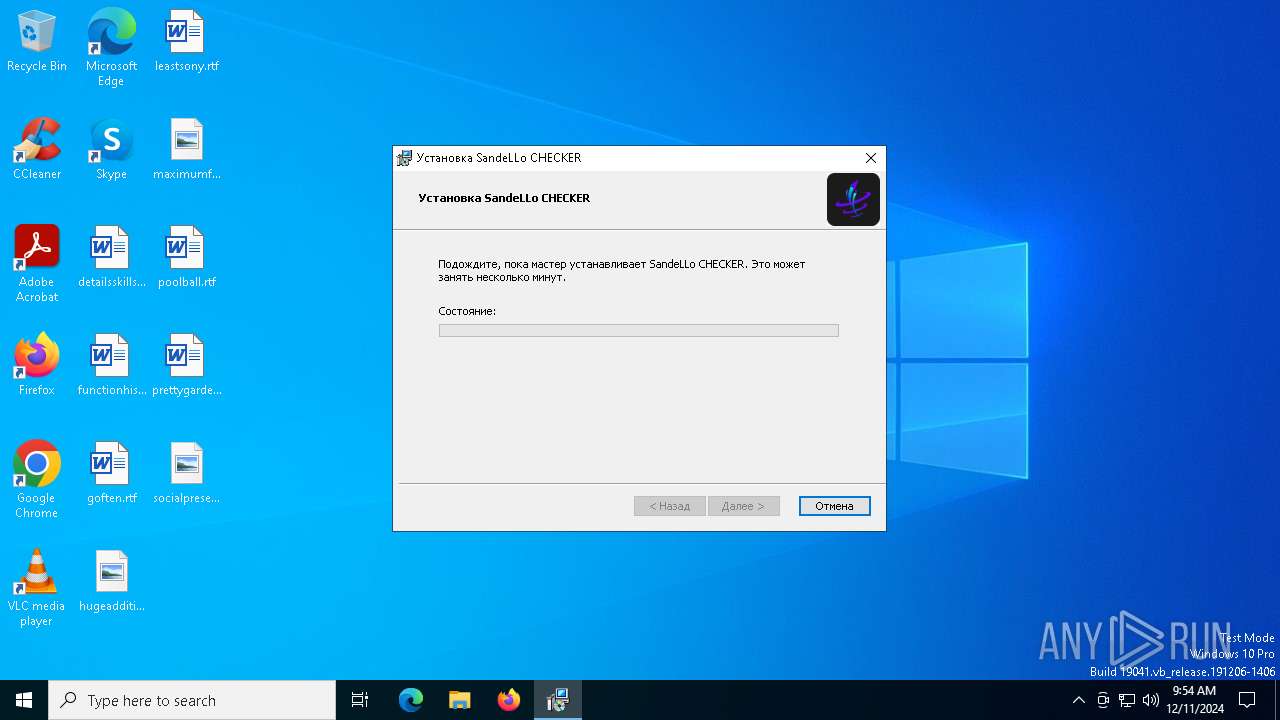
Executable content was dropped or overwritten
- services.exe (PID: 6204)
- 1313.exe (PID: 6260)
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- providerBrowser.exe (PID: 6464)
- RuntimeBroker.exe (PID: 6264)
Reads security settings of Internet Explorer
- services.exe (PID: 6204)
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- providerBrowser.exe (PID: 6464)
Checks Windows Trust Settings
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- msiexec.exe (PID: 6628)
Process drops legitimate windows executable
- SandeLLoCHECKER_Installer.exe (PID: 6440)
Reads the Windows owner or organization settings
- SandeLLoCHECKER_Installer.exe (PID: 6440)
Starts CMD.EXE for commands execution
- wscript.exe (PID: 6492)
- providerBrowser.exe (PID: 6464)
Executes as Windows Service
- VSSVC.exe (PID: 6012)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6492)
Executing commands from a ".bat" file
- wscript.exe (PID: 6492)
- providerBrowser.exe (PID: 6464)
Executed via WMI
- schtasks.exe (PID: 6912)
- schtasks.exe (PID: 6800)
- schtasks.exe (PID: 6840)
- schtasks.exe (PID: 6612)
- schtasks.exe (PID: 2088)
- schtasks.exe (PID: 6188)
- schtasks.exe (PID: 6856)
- schtasks.exe (PID: 2136)
- schtasks.exe (PID: 3532)
- schtasks.exe (PID: 4056)
- schtasks.exe (PID: 2996)
- schtasks.exe (PID: 4876)
- schtasks.exe (PID: 3796)
- schtasks.exe (PID: 3808)
- schtasks.exe (PID: 3576)
Starts application with an unusual extension
- cmd.exe (PID: 6256)
Probably delay the execution using 'w32tm.exe'
- cmd.exe (PID: 6256)
Connects to the server without a host name
- RuntimeBroker.exe (PID: 6264)
INFO
Checks supported languages
- 1313.exe (PID: 6260)
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- services.exe (PID: 6204)
- msiexec.exe (PID: 6628)
- msiexec.exe (PID: 6820)
- msiexec.exe (PID: 5028)
- providerBrowser.exe (PID: 6464)
- RuntimeBroker.exe (PID: 6264)
- msiexec.exe (PID: 1448)
Create files in a temporary directory
- services.exe (PID: 6204)
- SandeLLoCHECKER_Installer.exe (PID: 6440)
Process checks computer location settings
- services.exe (PID: 6204)
Reads the computer name
- services.exe (PID: 6204)
- 1313.exe (PID: 6260)
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- msiexec.exe (PID: 6628)
- msiexec.exe (PID: 6820)
- msiexec.exe (PID: 5028)
- providerBrowser.exe (PID: 6464)
- msiexec.exe (PID: 1448)
- SandeLLo CHECKER.exe (PID: 1328)
Checks proxy server information
- SandeLLoCHECKER_Installer.exe (PID: 6440)
Drops encrypted VBS script (Microsoft Script Encoder)
- 1313.exe (PID: 6260)
Reads the machine GUID from the registry
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- RuntimeBroker.exe (PID: 6264)
- msiexec.exe (PID: 6628)
- SandeLLo CHECKER.exe (PID: 1328)
Reads the software policy settings
- SandeLLoCHECKER_Installer.exe (PID: 6440)
The sample compiled with english language support
- SandeLLoCHECKER_Installer.exe (PID: 6440)
- msiexec.exe (PID: 7100)
- msiexec.exe (PID: 6628)
Reads Environment values
- msiexec.exe (PID: 6820)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 7100)
Executable content was dropped or overwritten
- msiexec.exe (PID: 7100)
- msiexec.exe (PID: 6628)
Changes the display of characters in the console
- cmd.exe (PID: 6256)
Manages system restore points
- SrTasks.exe (PID: 3812)
Sends debugging messages
- msiexec.exe (PID: 1448)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (53.2) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (17.5) |
| .scr | | | Windows screen saver (16.1) |
| .exe | | | Win32 Executable (generic) (5.5) |
| .exe | | | Win16/32 Executable Delphi generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 5120 |
| InitializedDataSize: | 8866816 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x20cc |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
166
Monitored processes
37
Malicious processes
6
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\Users\admin\AppData\Roaming\SandeLLo CHECKER\SandeLLo CHECKER.exe" | C:\Users\admin\AppData\Roaming\SandeLLo CHECKER\SandeLLo CHECKER.exe | msiexec.exe | ||||||||||||
User: admin Company: SandeLLo Integrity Level: HIGH Description: SandeLLo CHECKER Version: 1.7.2.8 Modules
| |||||||||||||||
| 1448 | C:\Windows\syswow64\MsiExec.exe -Embedding 26BA425FBD706755DAD9C67FFB99B6D7 | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | schtasks.exe /create /tn "dllhostd" /sc MINUTE /mo 8 /tr "'C:\ChaincontainerFontReviewMonitor\dllhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2136 | schtasks.exe /create /tn "conhostc" /sc MINUTE /mo 6 /tr "'C:\ChaincontainerFontReviewMonitor\conhost.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2996 | schtasks.exe /create /tn "RuntimeBrokerR" /sc MINUTE /mo 13 /tr "'C:\ChaincontainerFontReviewMonitor\RuntimeBroker.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3060 | chcp 65001 | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3532 | schtasks.exe /create /tn "conhost" /sc ONLOGON /tr "'C:\ChaincontainerFontReviewMonitor\conhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3576 | schtasks.exe /create /tn "RuntimeBrokerR" /sc MINUTE /mo 14 /tr "'C:\ChaincontainerFontReviewMonitor\RuntimeBroker.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3796 | schtasks.exe /create /tn "dllhost" /sc ONLOGON /tr "'C:\ChaincontainerFontReviewMonitor\dllhost.exe'" /rl HIGHEST /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3808 | schtasks.exe /create /tn "dllhostd" /sc MINUTE /mo 5 /tr "'C:\ChaincontainerFontReviewMonitor\dllhost.exe'" /f | C:\Windows\System32\schtasks.exe | — | WmiPrvSE.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 884
Read events
25 566
Write events
297
Delete events
21
Modification events
| (PID) Process: | (6204) services.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (6260) 1313.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbe\OpenWithProgids |
| Operation: | write | Name: | VBEFile |
Value: | |||
| (PID) Process: | (7100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Classes\Interface\{618736E0-3C3D-11CF-810C-00AA00389B71}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\WOW6432Node\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (7100) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Volatile\00\MACHINE\SOFTWARE\Classes\Interface\{03022430-ABC4-11D0-BDE2-00AA001A1953}\TypeLib |
| Operation: | write | Name: | Version |
Value: 1.1 | |||
| (PID) Process: | (6628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000EA9F2E9CB24BDB01E4190000E4150000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000EA9F2E9CB24BDB01E4190000E4150000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Leave) |
Value: 4800000000000000DA406A9CB24BDB01E4190000E4150000D20700000100000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6628) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppEnumGroups (Enter) |
Value: 4800000000000000DA406A9CB24BDB01E4190000E4150000D10700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
90
Suspicious files
24
Text files
46
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6260 | 1313.exe | C:\ChaincontainerFontReviewMonitor\providerBrowser.exe | executable | |
MD5:3C711A0A74E8C5FC89548F05B1F67A6B | SHA256:A1978472C82135E7752C177D2FD1F88D8CD07E71C30F3E3A40502386D3DFF109 | |||
| 6204 | services.exe | C:\Users\admin\AppData\Local\Temp\1313.exe | executable | |
MD5:7210DAA62E82412DEC608EC34E5F6FD2 | SHA256:30FAB8A369BF3C795A748DB14009388D3445F4CA7E68003C6749C9C6E99EC738 | |||
| 6204 | services.exe | C:\Users\admin\AppData\Local\Temp\SandeLLoCHECKER_Installer.exe | executable | |
MD5:8A0591A6B534E32FA179F2D781B79026 | SHA256:4DF8350850592B587C4D2AAABDDC8454BC4652DF0082B85C3336139A9C6EA53E | |||
| 6260 | 1313.exe | C:\ChaincontainerFontReviewMonitor\9TzQXyTHgoob29sazyfZEid.vbe | vbe | |
MD5:13C89B1CBE245CAE54CF1DA56468DA91 | SHA256:B5072431A648B6E2CE4E3D5900D76B8A946CC0052E9FA1EDFB69B86B0EF09F17 | |||
| 6260 | 1313.exe | C:\ChaincontainerFontReviewMonitor\VrmByOJ3UjWOPW846PWQ6qNopwXBefMaIzkWH6LtaHB0UTKFfx.bat | text | |
MD5:9D6F31262212089459802E13984FAE06 | SHA256:39A4EB1C70F221D73487E591CE9FB41E0E80FCB9B9E2036CD3C732319E9D88E2 | |||
| 6440 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:67E486B2F148A3FCA863728242B6273E | SHA256:FACAF1C3A4BF232ABCE19A2D534E495B0D3ADC7DBE3797D336249AA6F70ADCFB | |||
| 6440 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\{F123046A-2CBF-4743-A59B-E3D2751B5780}\51B5780\SandeLLoCHECKER_Installer.msi | executable | |
MD5:E47C6582751CDC22D8C0EEAC60DE6D0B | SHA256:C645A247C399AE2E8CCF8F826415E7287B52080FCAE3DAC203E7E543FE792CCB | |||
| 6440 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:E4A0FE6859A0EBDFD8F15390484D54D2 | SHA256:6E75B8AA01733C02A7BDD69ABFD47BCB8581F46F2BABC83CFCF8AE719891BE6A | |||
| 6440 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:2EF993B11E37FF837F1D0C6719C451F9 | SHA256:024D529B6E60AE44288B77E7A83566B254ACA7BF41E3E25B41A3FD6D750EA873 | |||
| 6440 | SandeLLoCHECKER_Installer.exe | C:\Users\admin\AppData\Local\Temp\MSI6A86.tmp | executable | |
MD5:9E0AEF52F6C03B2FEA067342D9D4F22F | SHA256:42B8ADAFCB4E8496D9822A0C504F449E56456528A9251C153381D3F63D197E5B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
34
TCP/UDP connections
39
DNS requests
19
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5064 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6220 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6220 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3772 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
6264 | RuntimeBroker.exe | POST | 200 | 77.222.47.117:80 | http://77.222.47.117/packetrequestdownloads/0/defaultimage/_/universalProvider/0DownloadsWordpress/8ProtonBigloadlongpoll/privatePublicTrack/dump/Uploads/VideoPipeProcessorDefault.php | unknown | — | — | malicious |
6264 | RuntimeBroker.exe | POST | 200 | 77.222.47.117:80 | http://77.222.47.117/packetrequestdownloads/0/defaultimage/_/universalProvider/0DownloadsWordpress/8ProtonBigloadlongpoll/privatePublicTrack/dump/Uploads/VideoPipeProcessorDefault.php | unknown | — | — | malicious |
6264 | RuntimeBroker.exe | POST | 200 | 77.222.47.117:80 | http://77.222.47.117/packetrequestdownloads/0/defaultimage/_/universalProvider/0DownloadsWordpress/8ProtonBigloadlongpoll/privatePublicTrack/dump/Uploads/VideoPipeProcessorDefault.php | unknown | — | — | malicious |
6264 | RuntimeBroker.exe | POST | 200 | 77.222.47.117:80 | http://77.222.47.117/packetrequestdownloads/0/defaultimage/_/universalProvider/0DownloadsWordpress/8ProtonBigloadlongpoll/privatePublicTrack/dump/Uploads/VideoPipeProcessorDefault.php | unknown | — | — | malicious |
6264 | RuntimeBroker.exe | POST | 200 | 77.222.47.117:80 | http://77.222.47.117/packetrequestdownloads/0/defaultimage/_/universalProvider/0DownloadsWordpress/8ProtonBigloadlongpoll/privatePublicTrack/dump/Uploads/VideoPipeProcessorDefault.php | unknown | — | — | malicious |
6264 | RuntimeBroker.exe | POST | 200 | 77.222.47.117:80 | http://77.222.47.117/packetrequestdownloads/0/defaultimage/_/universalProvider/0DownloadsWordpress/8ProtonBigloadlongpoll/privatePublicTrack/dump/Uploads/VideoPipeProcessorDefault.php | unknown | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
2460 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
5064 | SearchApp.exe | 2.23.209.168:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
6440 | SandeLLoCHECKER_Installer.exe | 172.67.184.109:443 | cdn.semkrill.ru | CLOUDFLARENET | US | unknown |
6440 | SandeLLoCHECKER_Installer.exe | 142.250.185.195:80 | c.pki.goog | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
cdn.semkrill.ru |
| unknown |
c.pki.goog |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6264 | RuntimeBroker.exe | A Network Trojan was detected | ET MALWARE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
6264 | RuntimeBroker.exe | A Network Trojan was detected | REMOTE [ANY.RUN] DarkCrystal Rat Check-in (POST) |
2192 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
Process | Message |
|---|---|
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |
msiexec.exe | Logger::SetLogFile( C:\Users\admin\AppData\Roaming\Caphyon\Advanced Installer\AI_ResourceCleaner.log ) while OLD path is: |