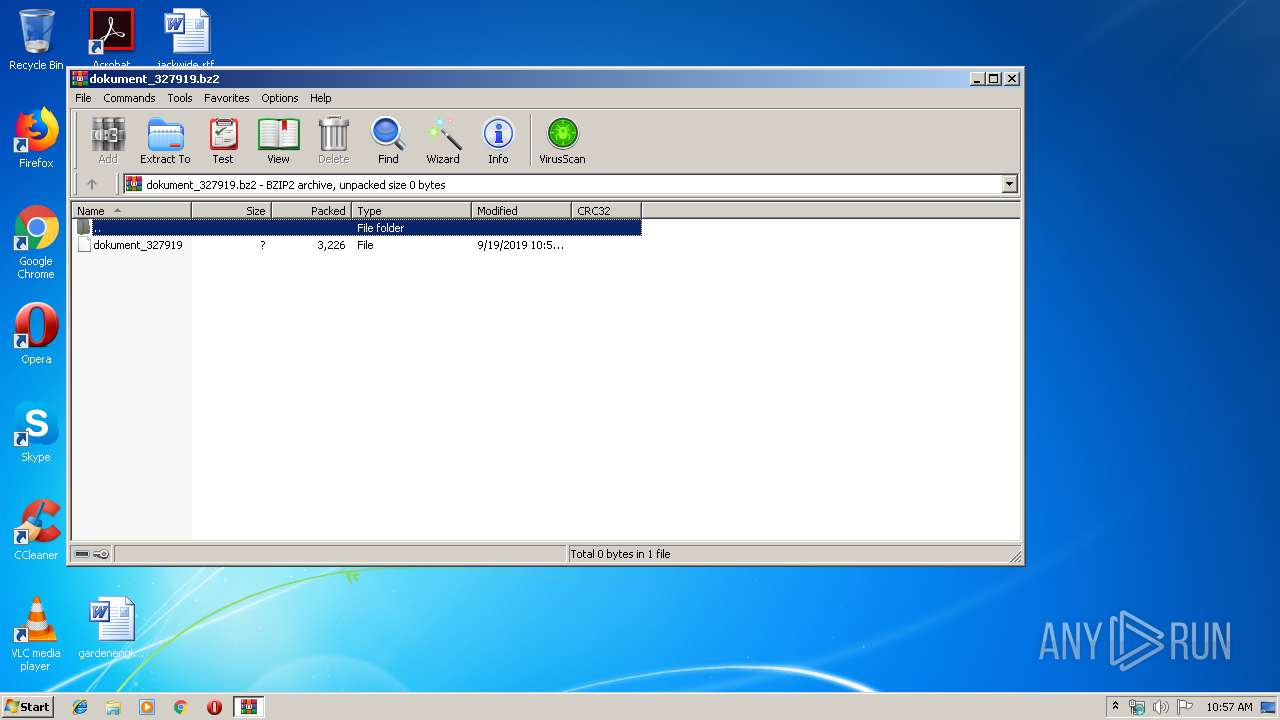
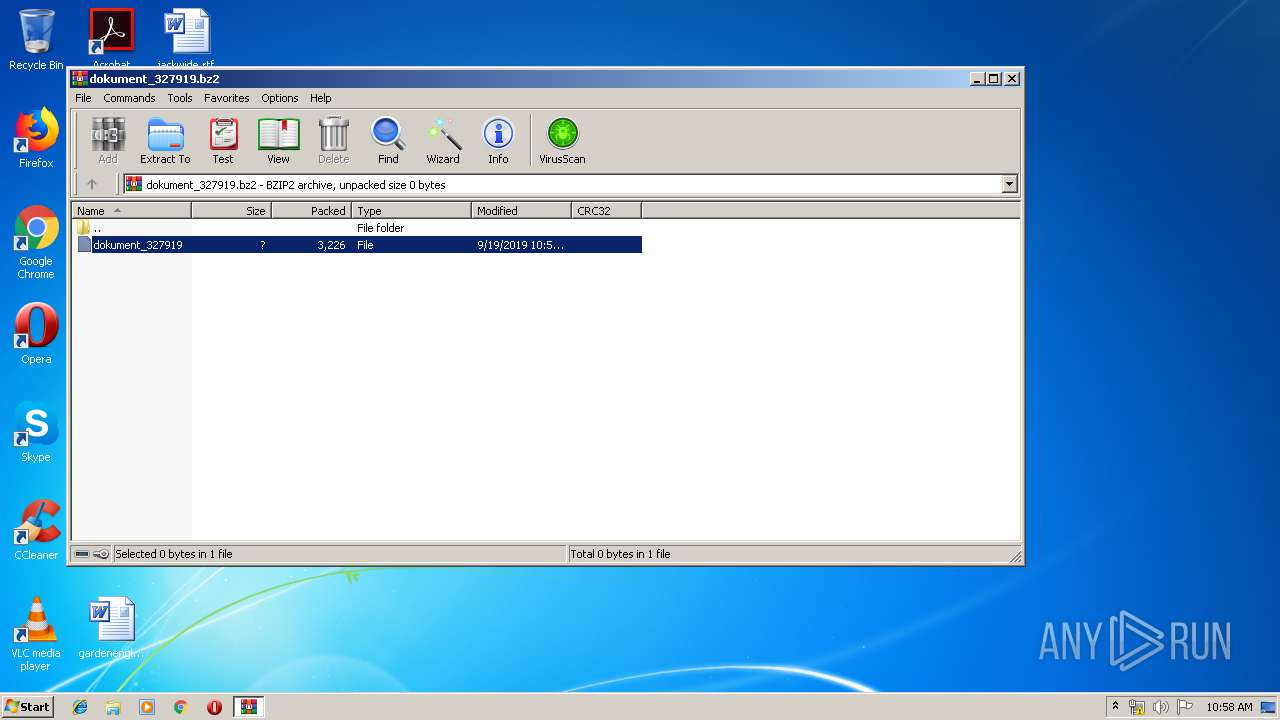
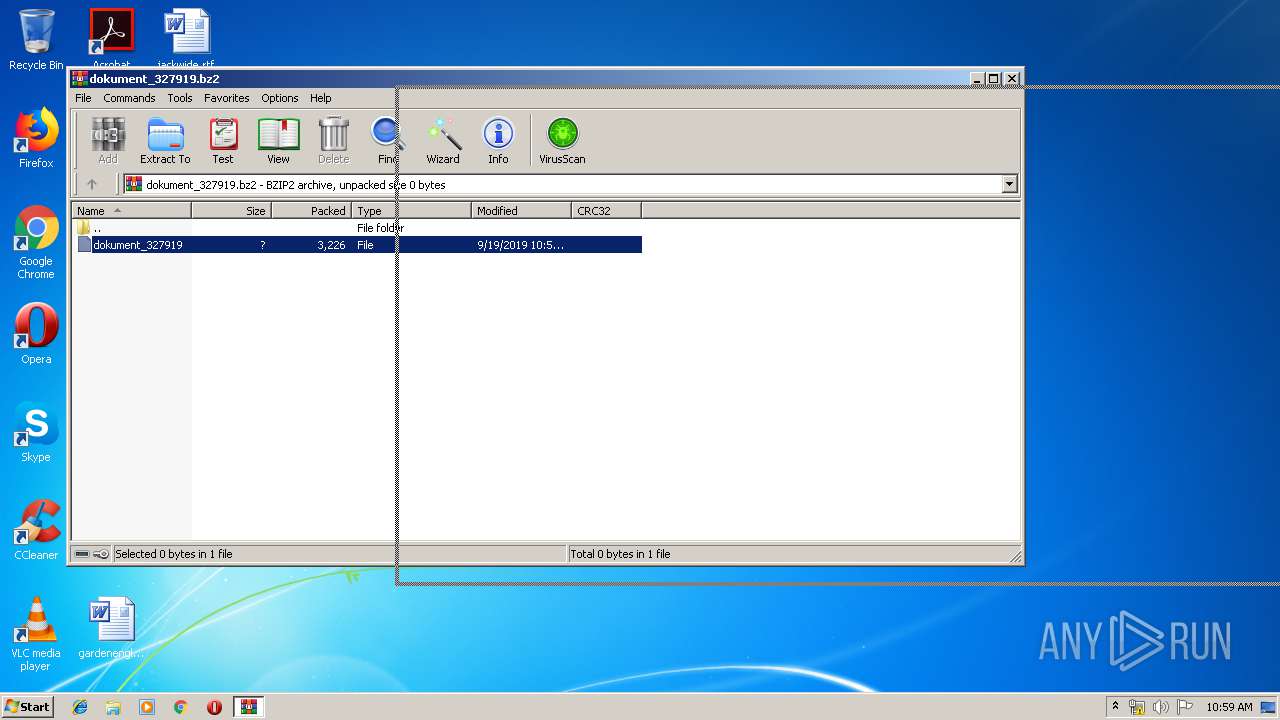
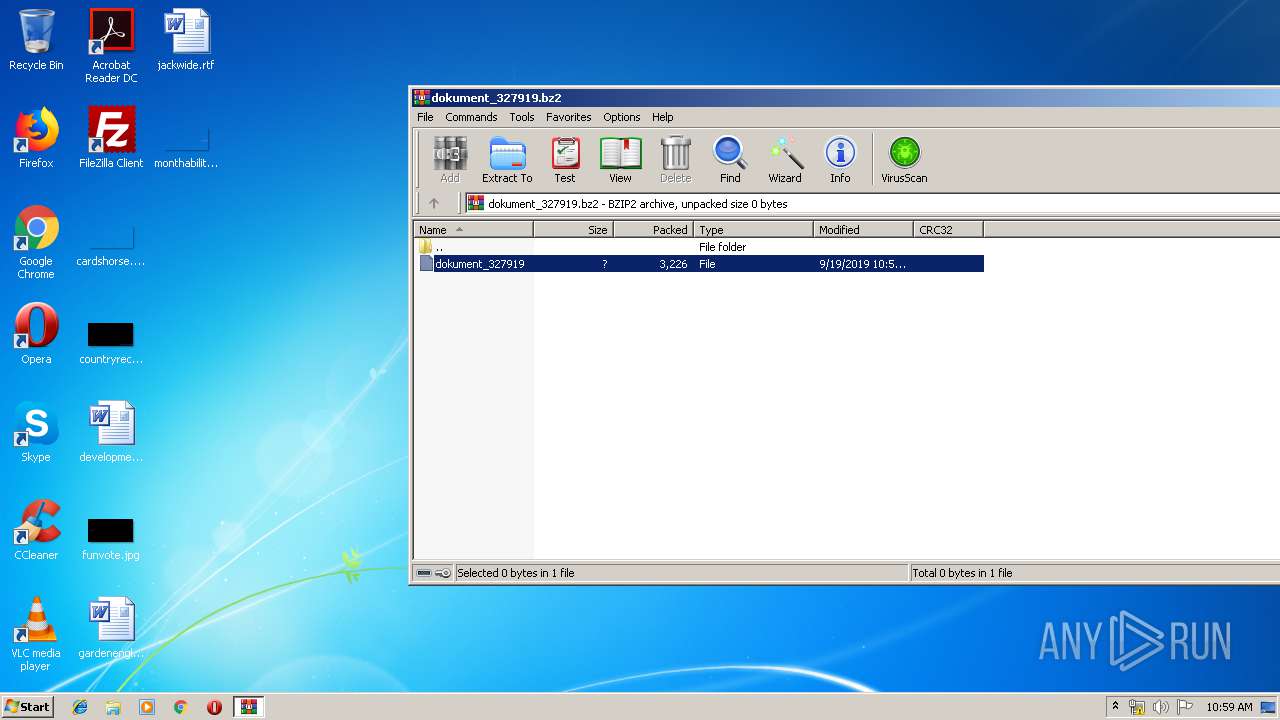
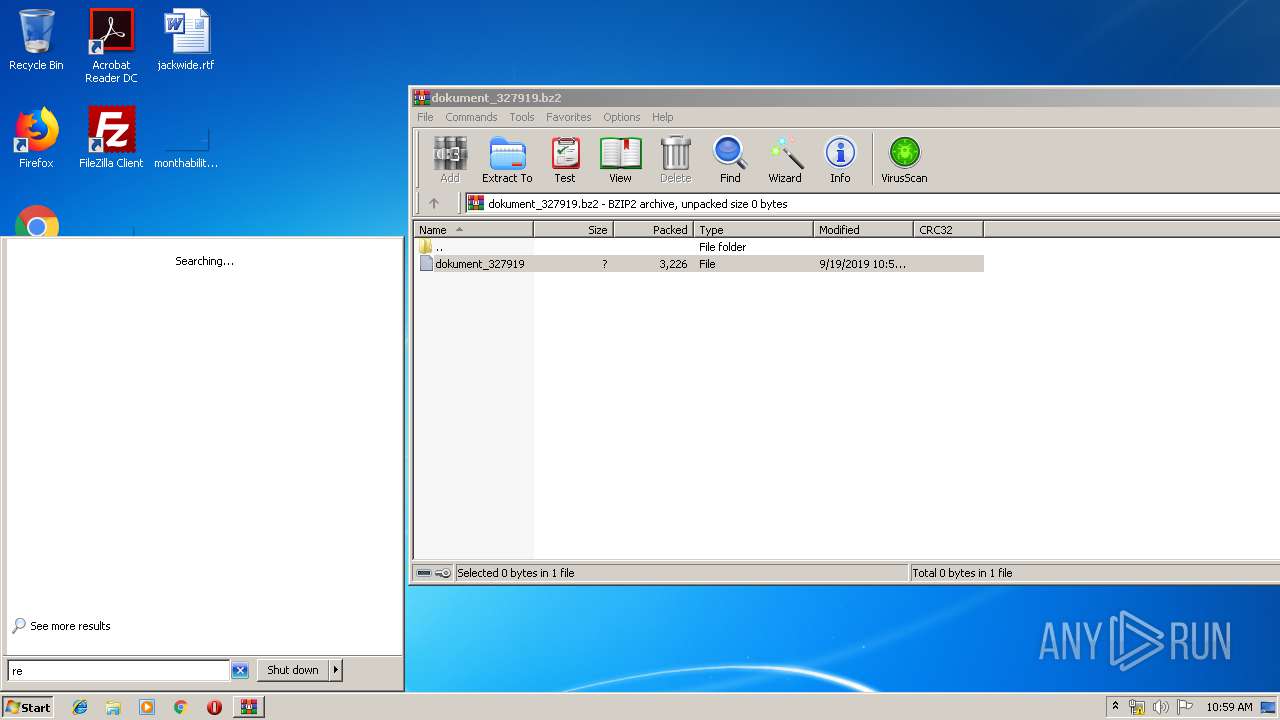
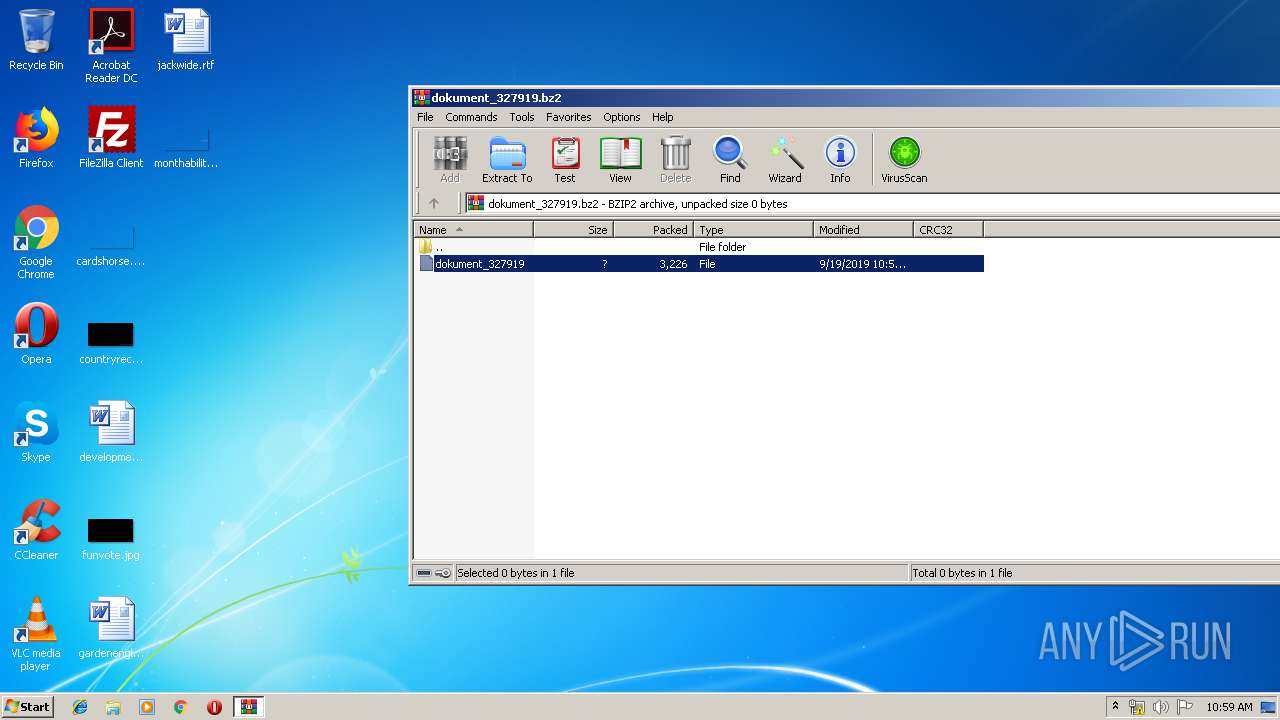
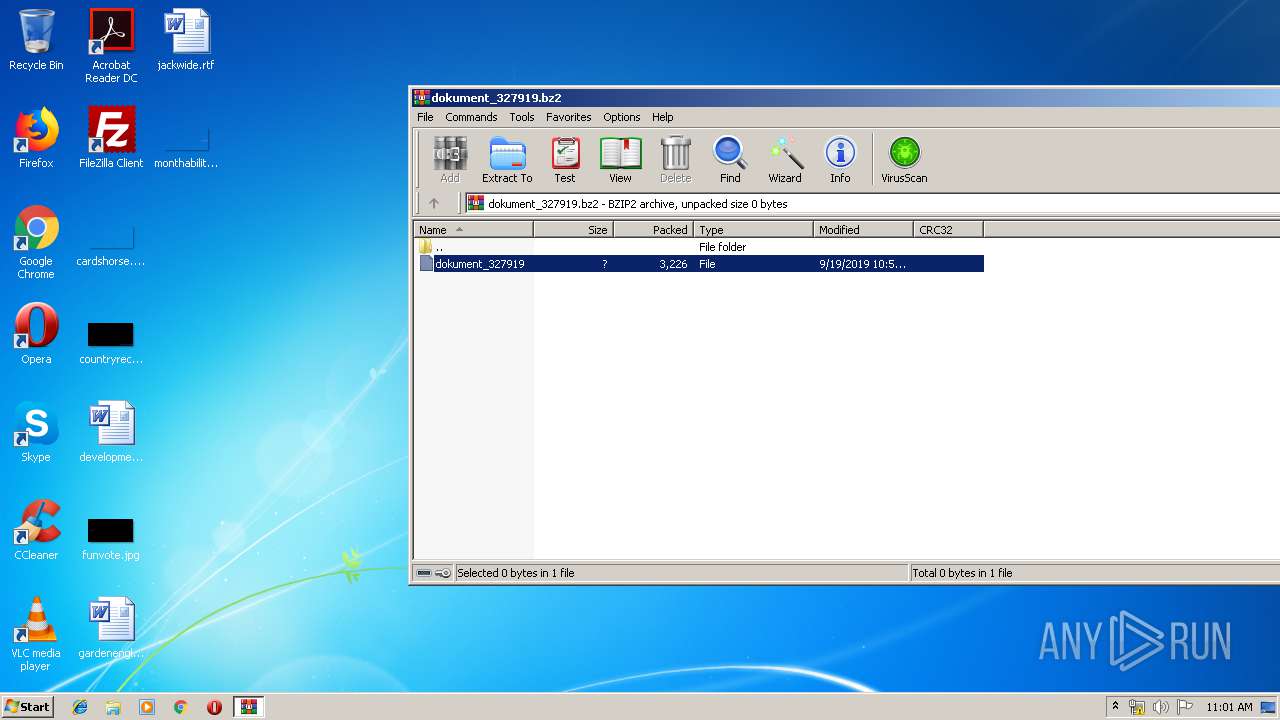
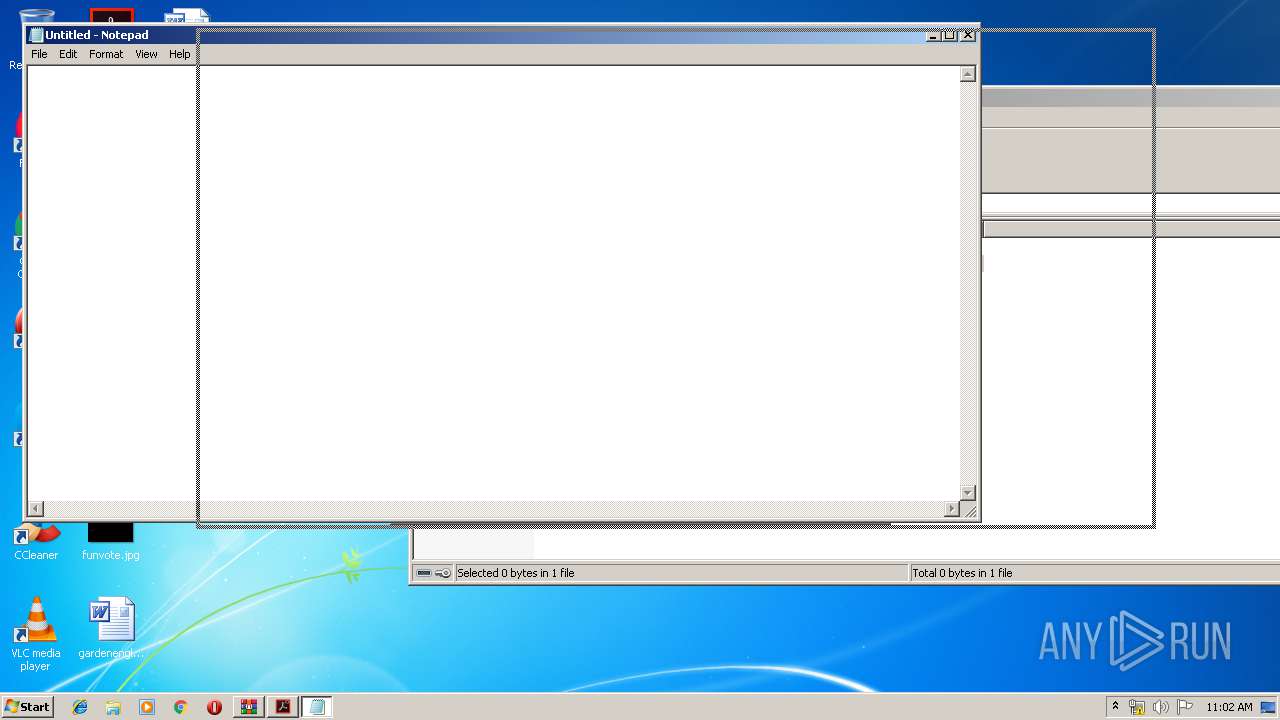
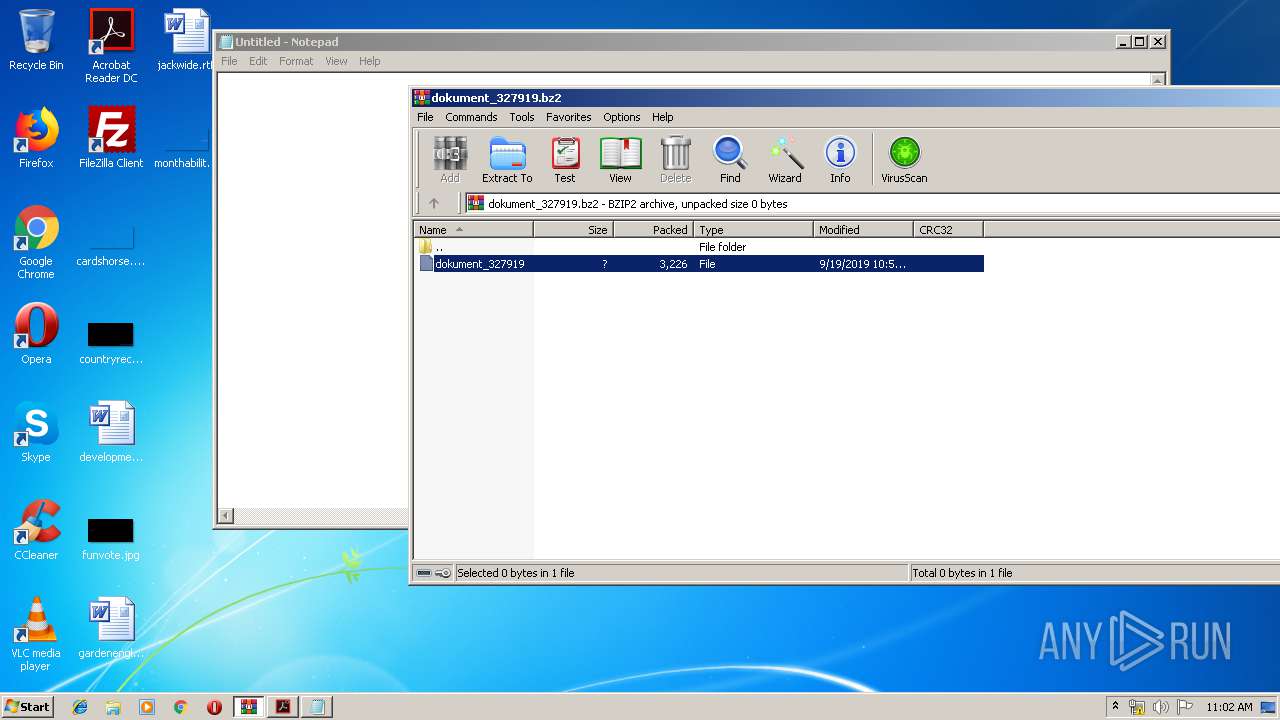
| File name: | dokument_327919.bz2 |
| Full analysis: | https://app.any.run/tasks/60c5a0be-0e28-44d6-bd3a-2a1354d4edac |
| Verdict: | Malicious activity |
| Analysis date: | September 19, 2019, 09:57:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-bzip2 |
| File info: | bzip2 compressed data, block size = 900k |
| MD5: | F344D66C52D851A0E0FDC1B7F8771AB3 |
| SHA1: | 659DCB9BE308EA477E9FB08C961DFAC2E1148D5A |
| SHA256: | 2B6D56AC1546487B64862A6A704016D32C4DBB210B11678366D028D824ECE7D2 |
| SSDEEP: | 48:srLiNg9k9Zjc0LocXQJ8RJ8u5FtwtIIzgL79lxKTvSnbPH0qOLs3se3gtoXCkIaI:yG740McXM838u5b6Itbcu7ceL3gtoSk8 |
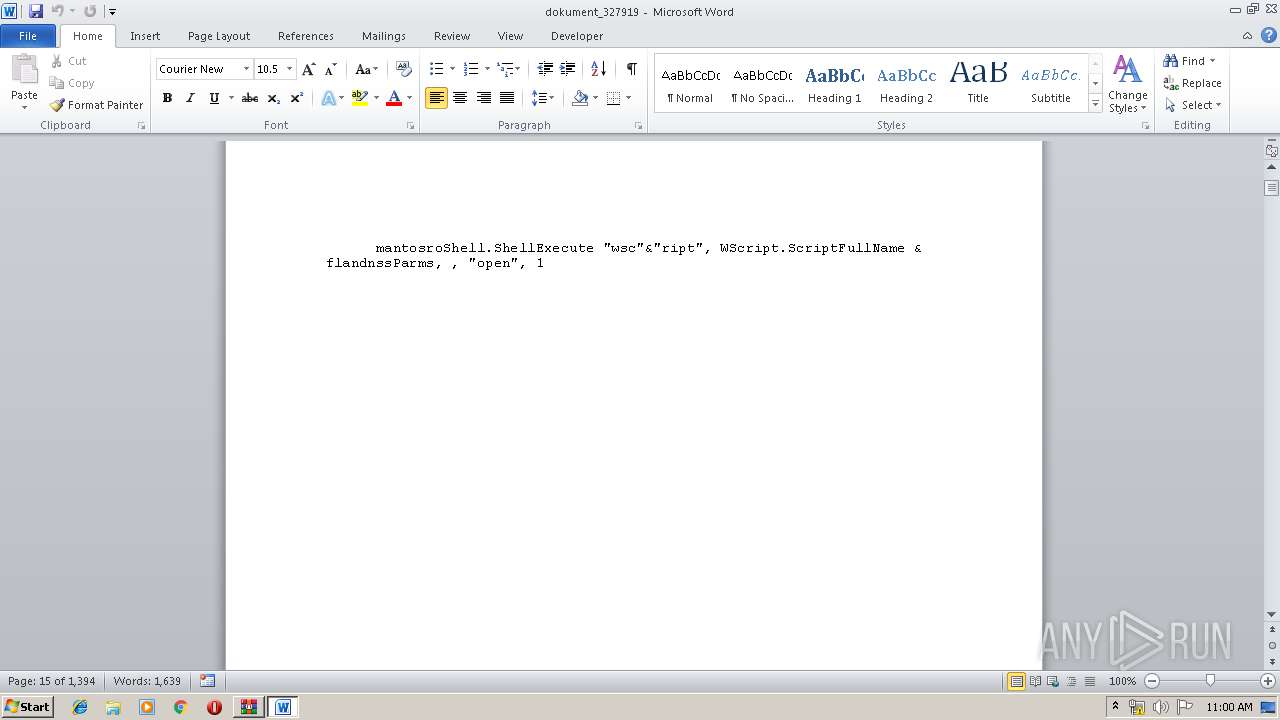
MALICIOUS
Loads the Task Scheduler COM API
- MsiExec.exe (PID: 3092)
- MsiExec.exe (PID: 3236)
- MsiExec.exe (PID: 3824)
- MsiExec.exe (PID: 2984)
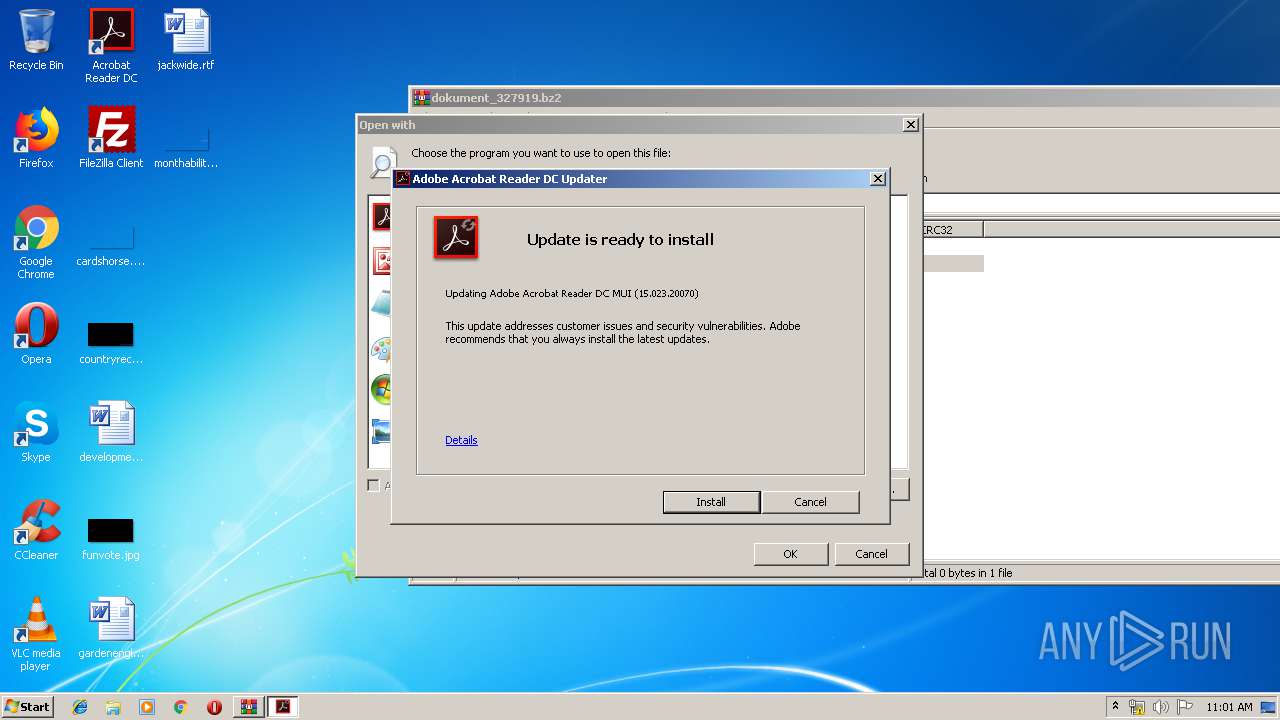
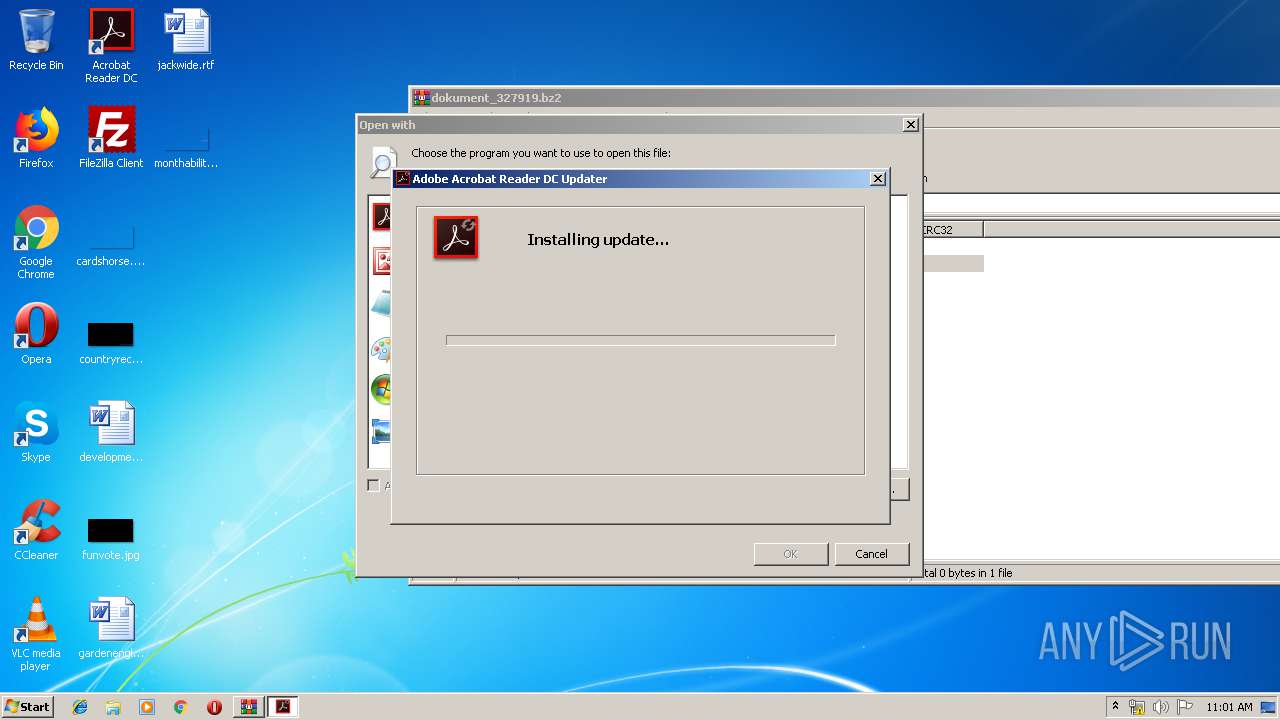
Application was dropped or rewritten from another process
- AdobeARMHelper.exe (PID: 2696)
- AdobeARMHelper.exe (PID: 3420)
- AdobeARM.exe (PID: 2496)
- AdobeARM.exe (PID: 2652)
SUSPICIOUS
Creates files in the program directory
- AdobeARM.exe (PID: 2496)
- AdobeARMHelper.exe (PID: 3420)
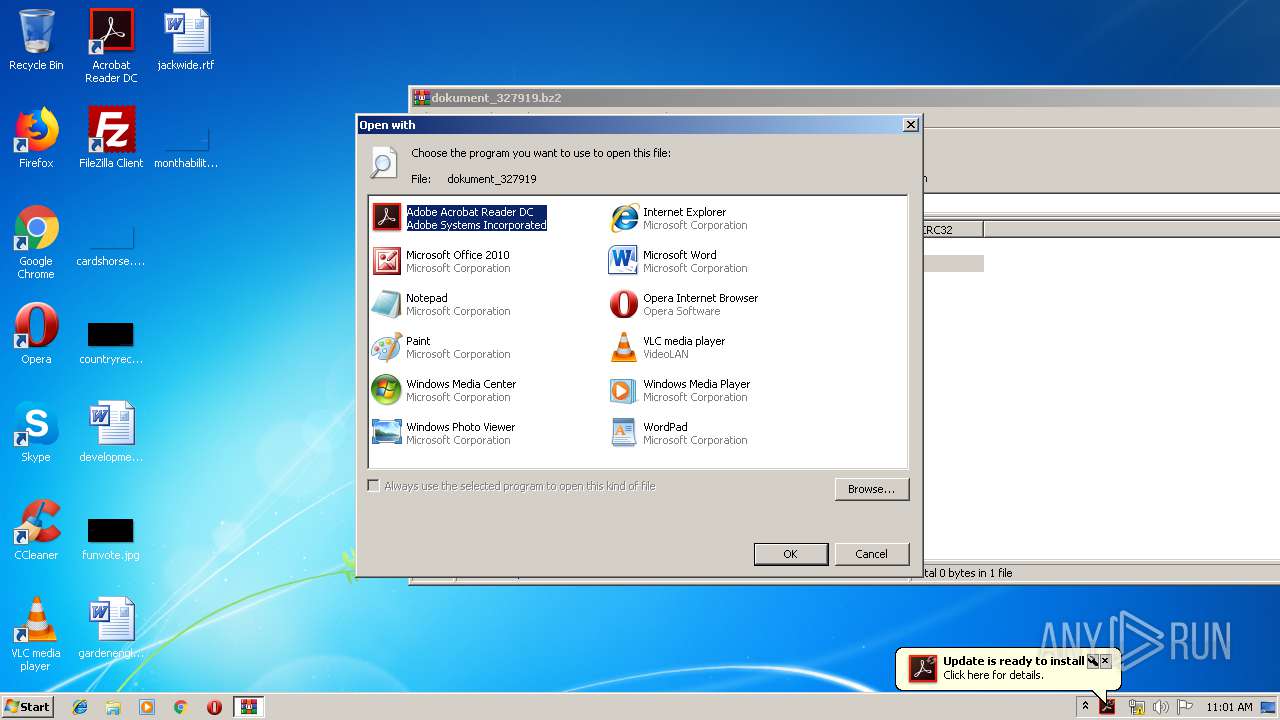
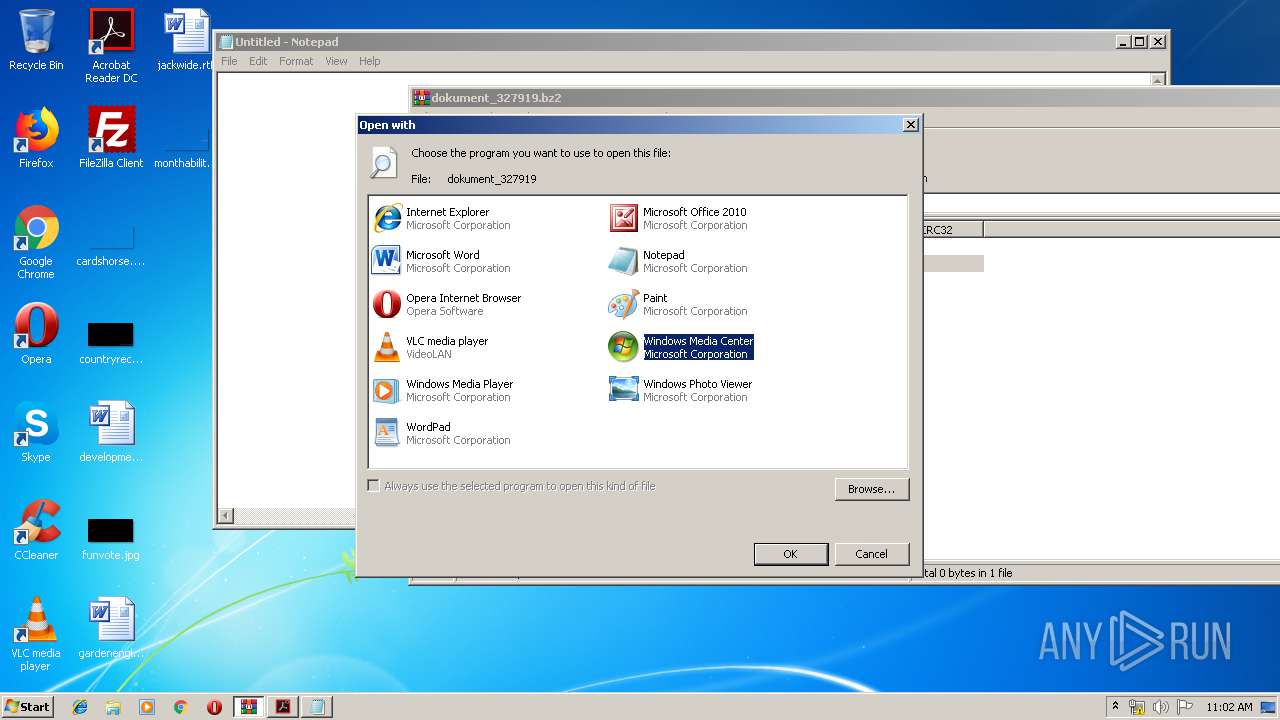
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 2888)
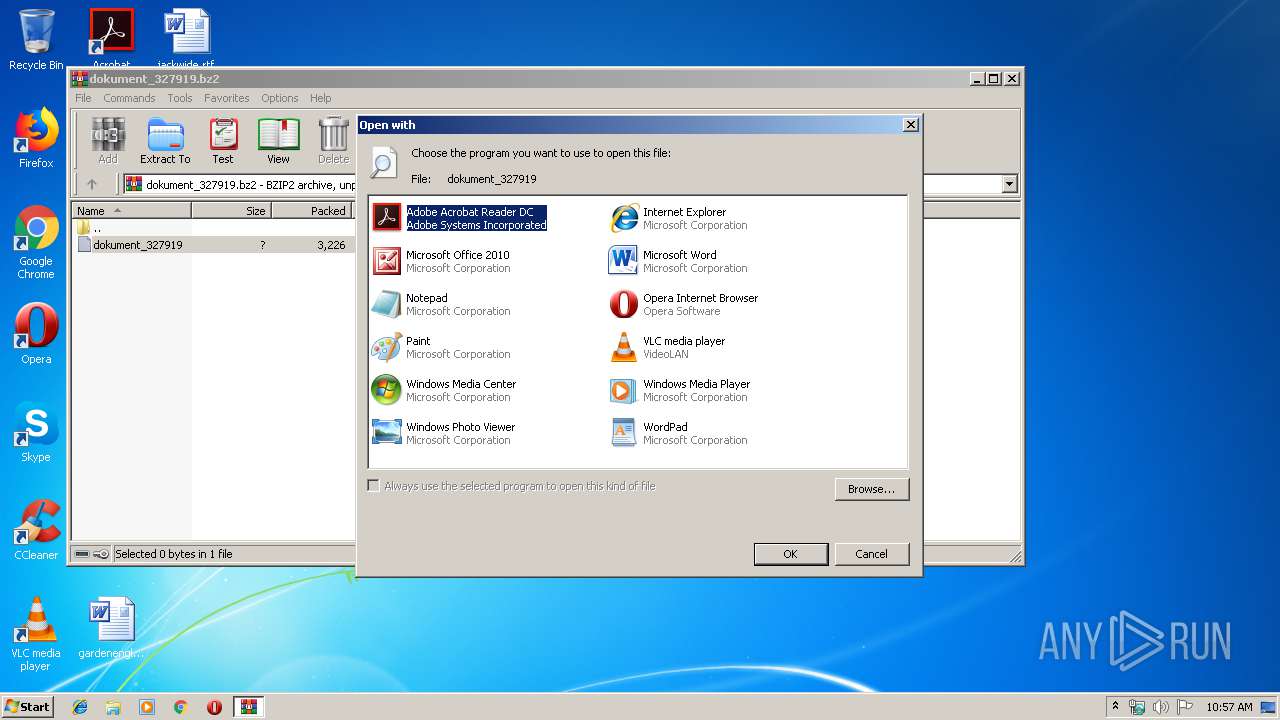
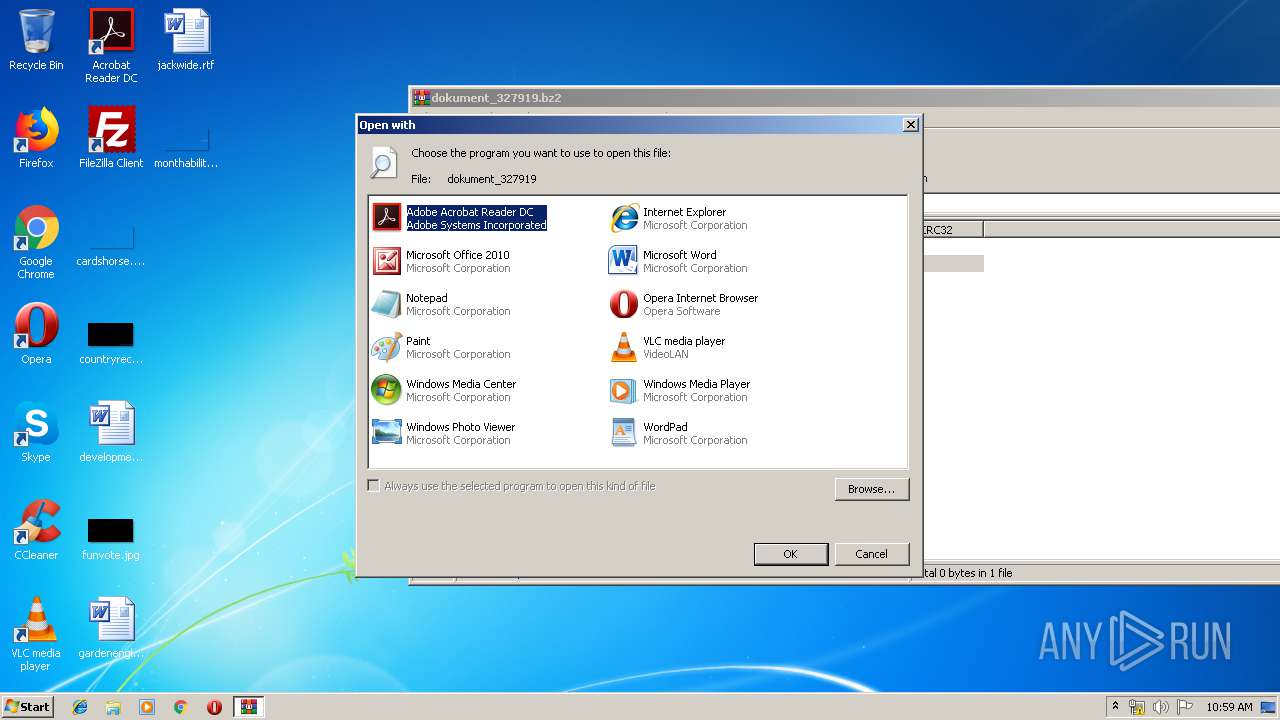
Starts Microsoft Office Application
- rundll32.exe (PID: 3020)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 2496)
- msiexec.exe (PID: 3312)
- AdobeARMHelper.exe (PID: 3420)
Removes files from Windows directory
- MsiExec.exe (PID: 3028)
Creates files in the Windows directory
- MsiExec.exe (PID: 3028)
INFO
Reads the hosts file
- RdrCEF.exe (PID: 3012)
Application launched itself
- RdrCEF.exe (PID: 3012)
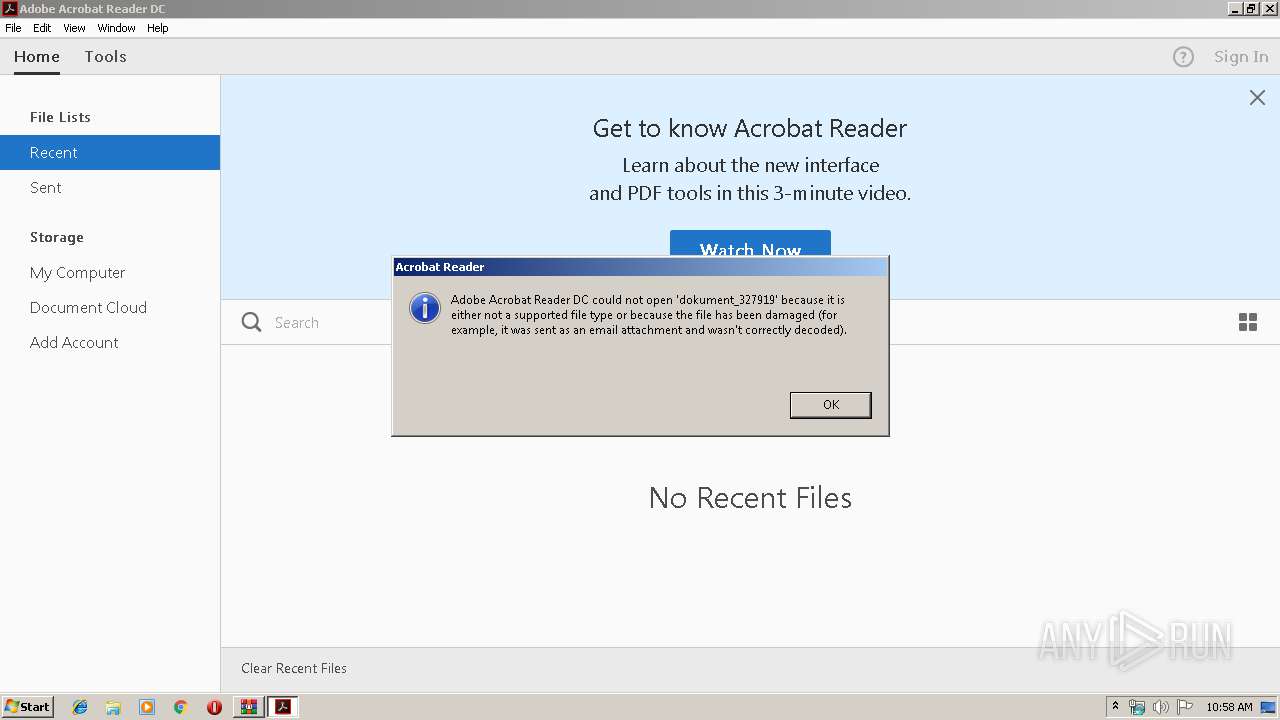
- AcroRd32.exe (PID: 3540)
- msiexec.exe (PID: 3312)
Creates files in the user directory
- WINWORD.EXE (PID: 2288)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2288)
Reads settings of System Certificates
- msiexec.exe (PID: 3312)
Creates files in the program directory
- msiexec.exe (PID: 3312)
Creates a software uninstall entry
- msiexec.exe (PID: 3312)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 3236)
- MsiExec.exe (PID: 2088)
- MsiExec.exe (PID: 2984)
- MsiExec.exe (PID: 3028)
- MsiExec.exe (PID: 3092)
- MsiExec.exe (PID: 3824)
Starts application with an unusual extension
- msiexec.exe (PID: 3312)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .bz2/bzip2 | | | bzip2 compressed archive (100) |
|---|
Total processes
59
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1700 | C:\Windows\system32\MsiExec.exe -Embedding 9F54A8279EB6B253593D24F3C00104E9 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2088 | C:\Windows\system32\MsiExec.exe -Embedding 7FB215C2B751CC4852CDF6A14E9312BC M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
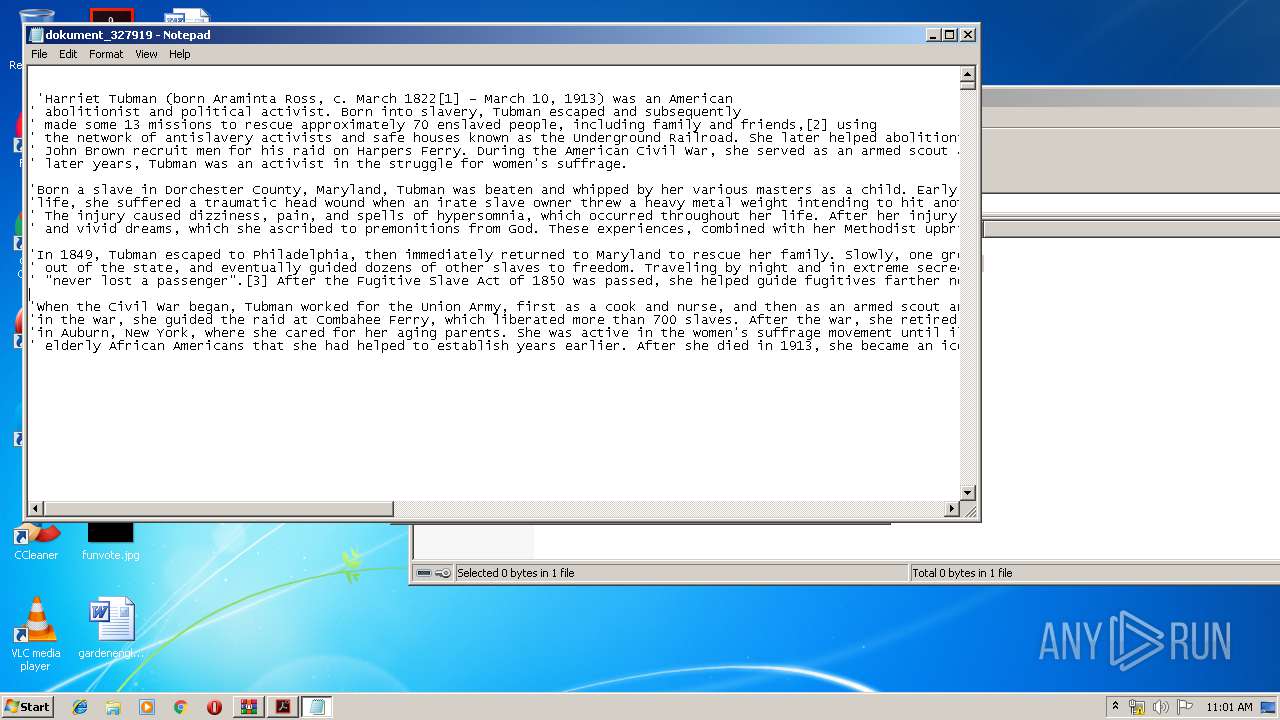
| 2288 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2888.18967\dokument_327919" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2496 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:15.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 2652 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /ArmUpdate /MSI FOLDER:"C:\ProgramData\Adobe\ARM\S\16133" /MODE:1 /PRODUCT:Reader /VERSION:15.0 /LANG:ENU | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | — | AdobeARMHelper.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: HIGH Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.31.1644 Modules
| |||||||||||||||
| 2696 | "C:\ProgramData\Adobe\ARM\S\16133\AdobeARMHelper.exe" /ArmUpdate /MSI FOLDER:"C:\ProgramData\Adobe\ARM\S\16133" /MODE:1 /PRODUCT:Reader /VERSION:15.0 /LANG:ENU | C:\ProgramData\Adobe\ARM\S\16133\AdobeARMHelper.exe | — | AdobeARM.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Helper Exit code: 3221226540 Version: 1.824.27.2646 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\dokument_327919.bz2" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2984 | C:\Windows\system32\MsiExec.exe -Embedding D9BBAD15D0D427E551F5002E25718E27 M Global\MSI0000 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3012 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 3020 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIa2888.18967\dokument_327919 | C:\Windows\system32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
9 220
Read events
6 932
Write events
2 119
Delete events
169
Modification events
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\dokument_327919.bz2 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2888) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
73
Suspicious files
15
Text files
40
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\LocalLow\Adobe\Acrobat\DC\ReaderMessages-journal | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\Cache\AdobeFnt16.lst.3172 | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Adobe\Acrobat\DC\AdobeFnt16.lst.3172 | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Reibimu_15es0t9_2g4.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R1gx2a81_15es0t8_2g4.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9R4bfian_15es0t7_2g4.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rmsfug2_15es0t6_2g4.tmp | — | |
MD5:— | SHA256:— | |||
| 3172 | AcroRd32.exe | C:\Users\admin\AppData\Local\Temp\acrord32_sbx\A9Rtgb9pk_15es0ta_2g4.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp76D6.tmp | — | |
MD5:— | SHA256:— | |||
| 2496 | AdobeARM.exe | C:\Users\admin\AppData\Local\Temp\Tmp76E6.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
6
DNS requests
9
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3540 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
3540 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
3540 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
3540 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
3540 | AcroRd32.exe | GET | 304 | 2.16.186.57:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3540 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
3540 | AcroRd32.exe | 2.16.186.57:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
ardownload2.adobe.com |
| whitelisted |