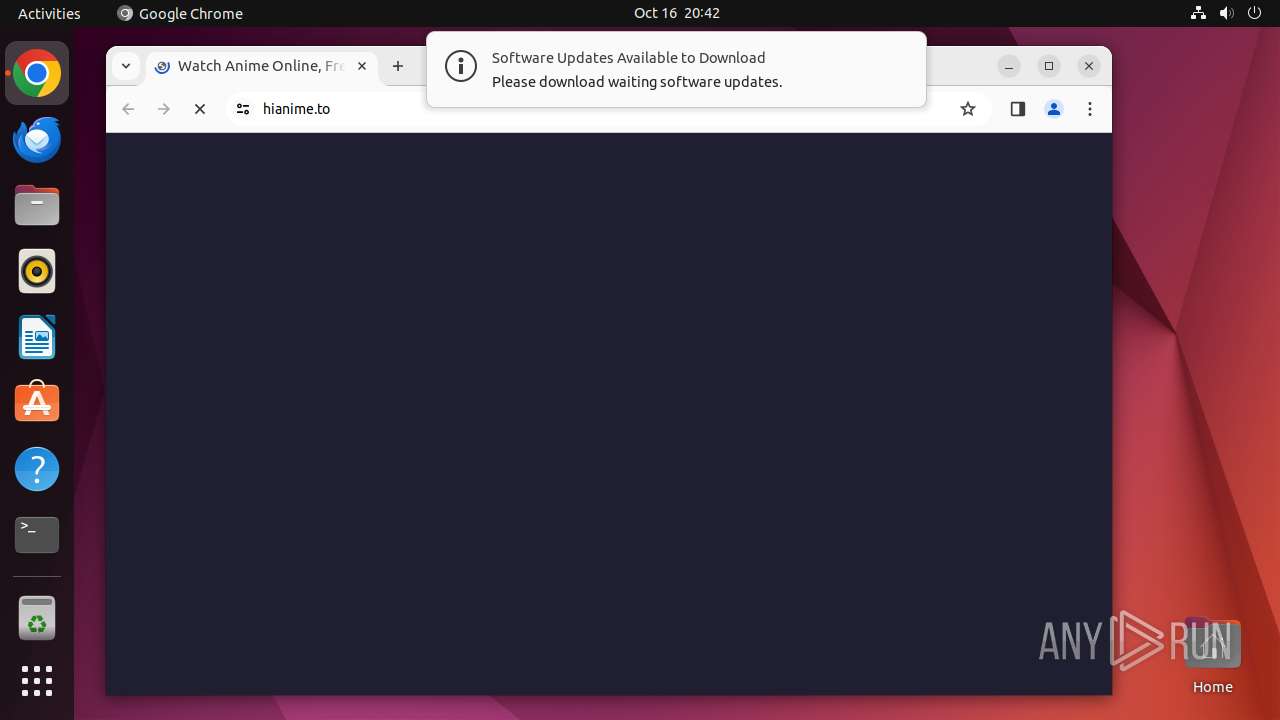
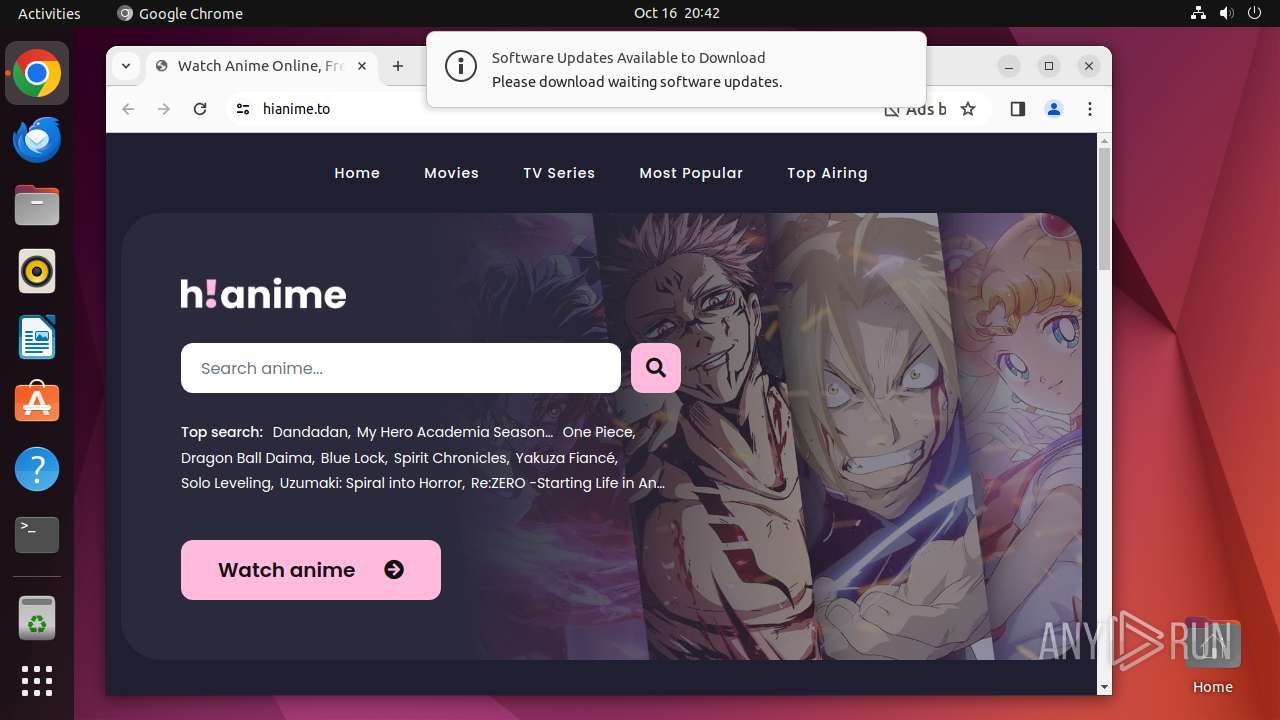
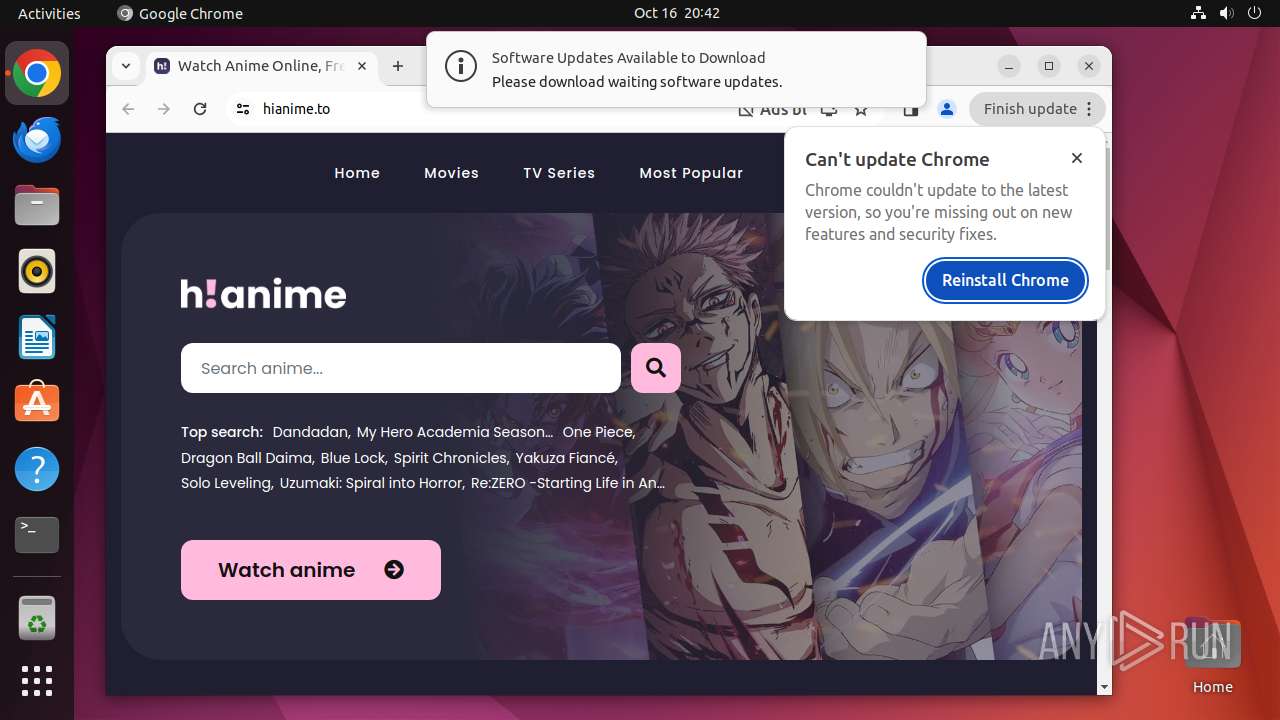
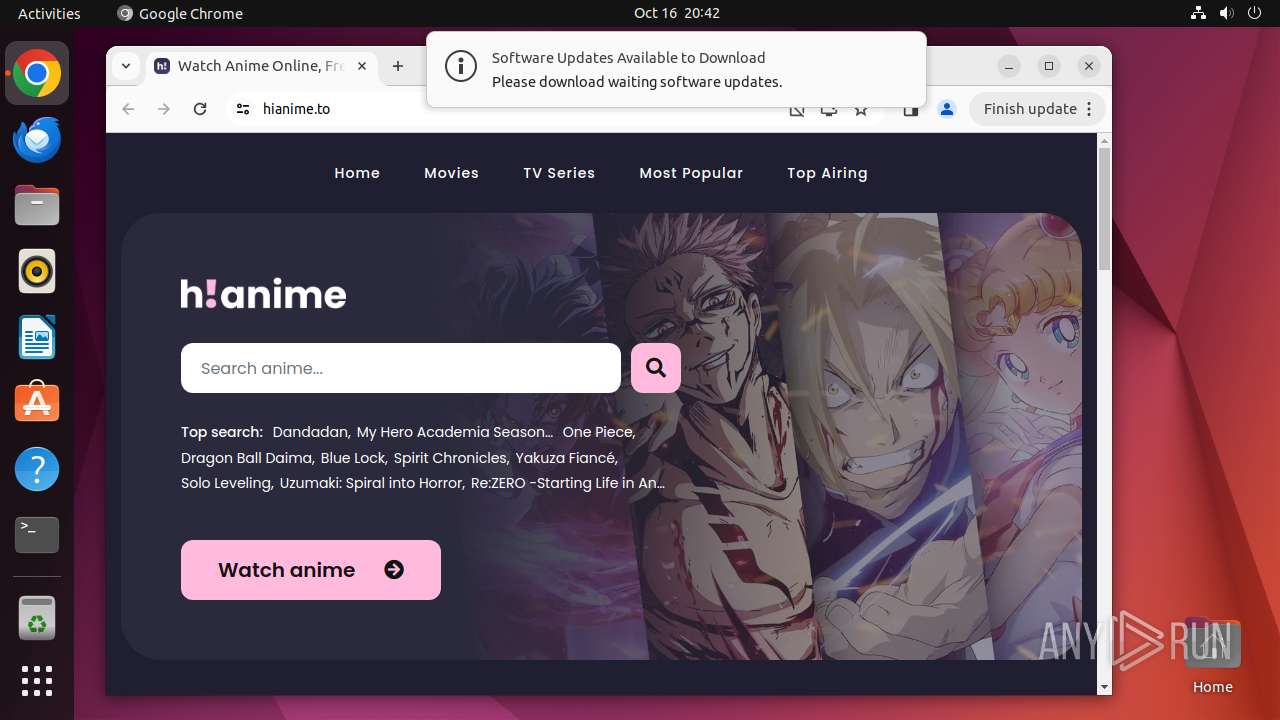
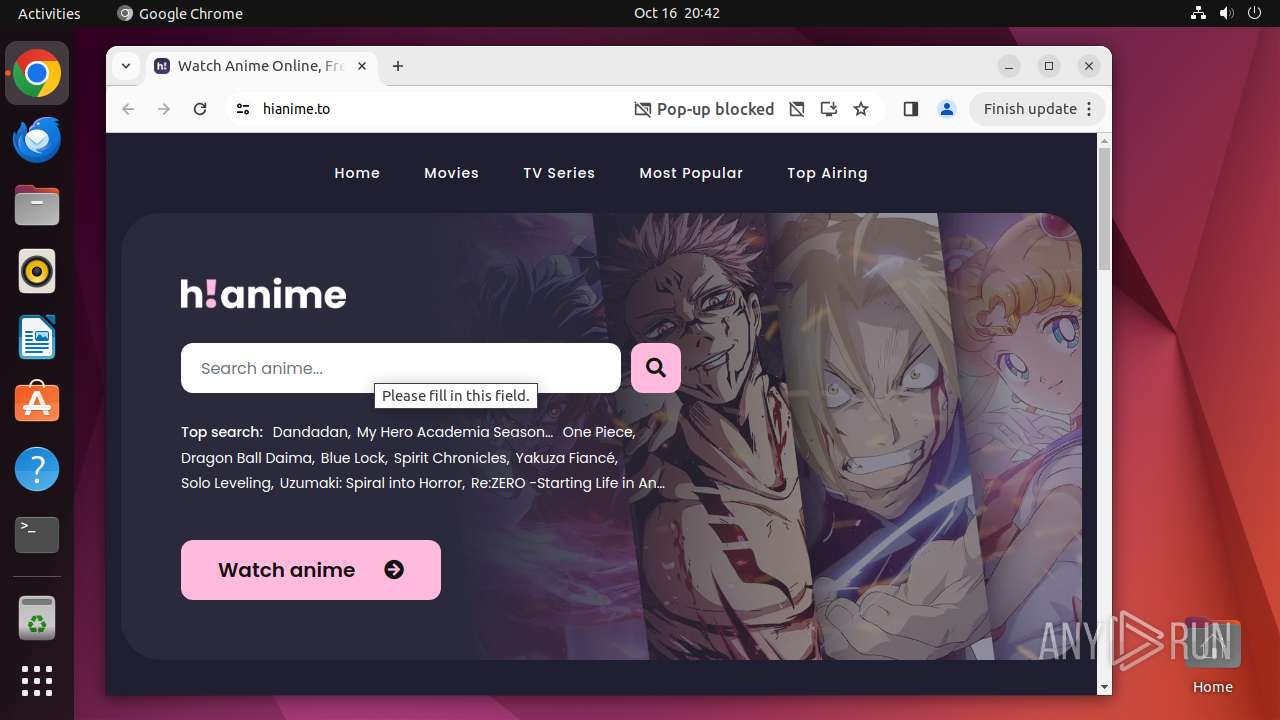
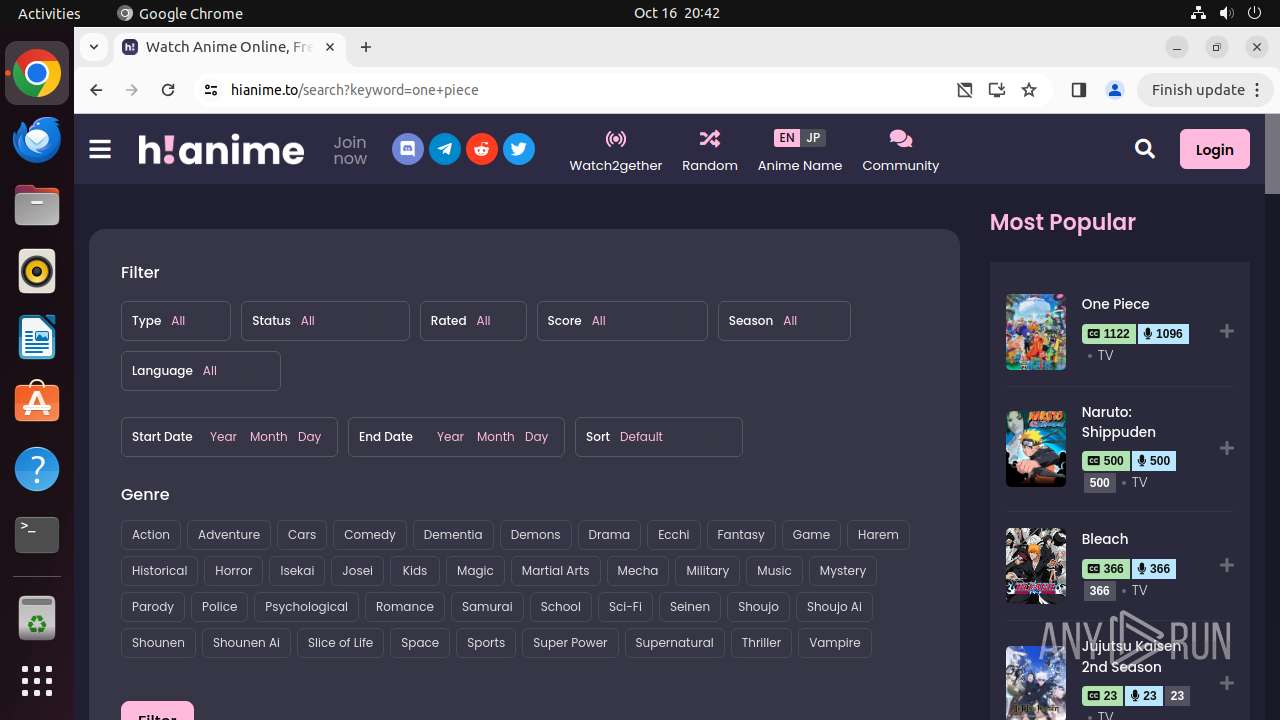
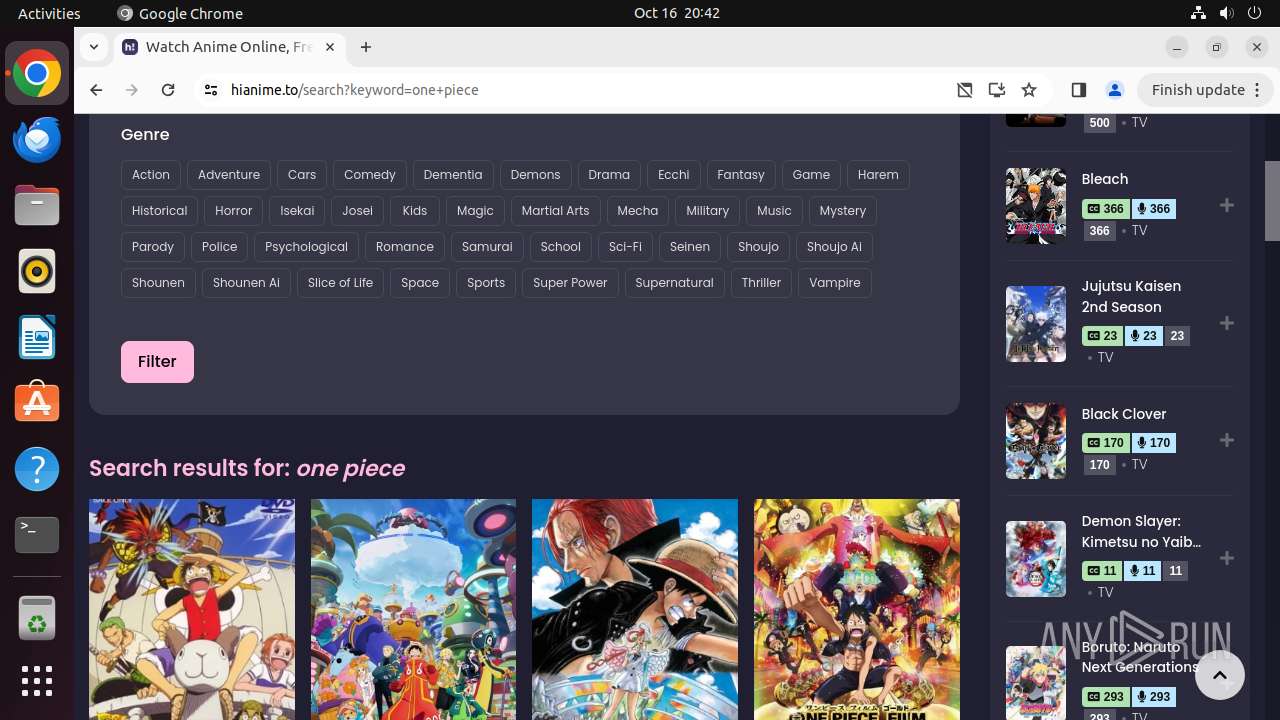
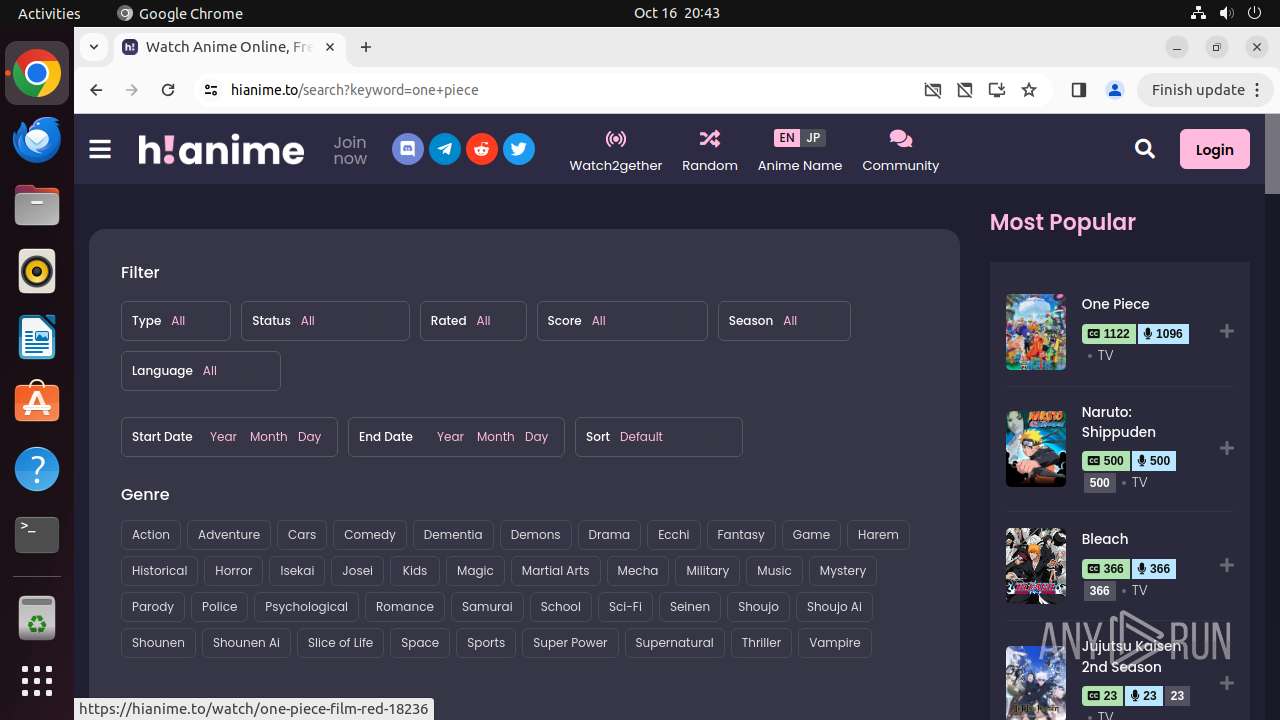
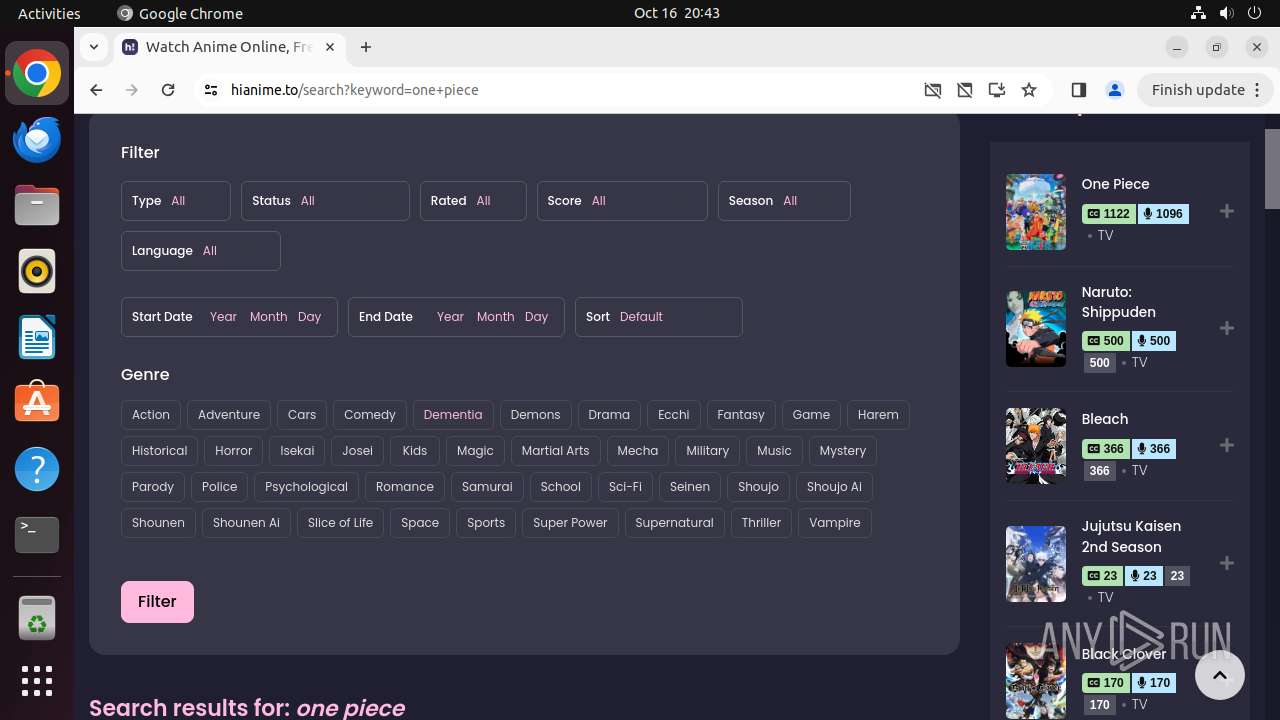
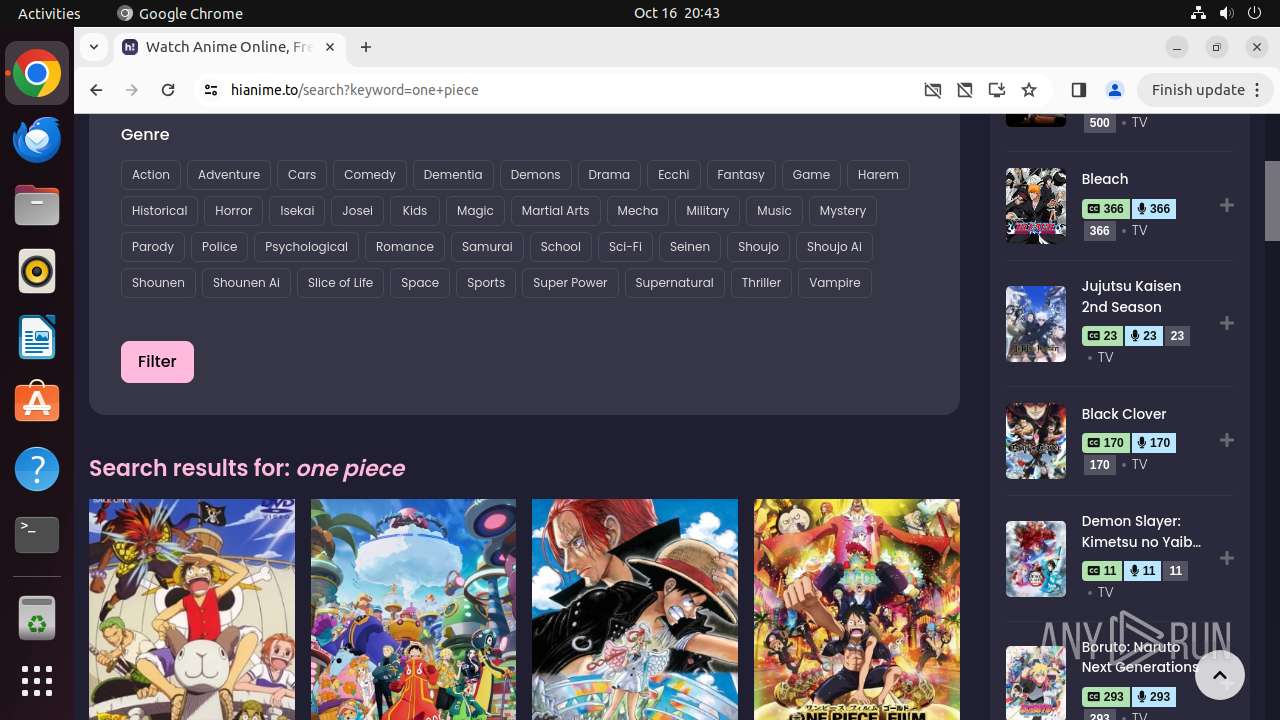
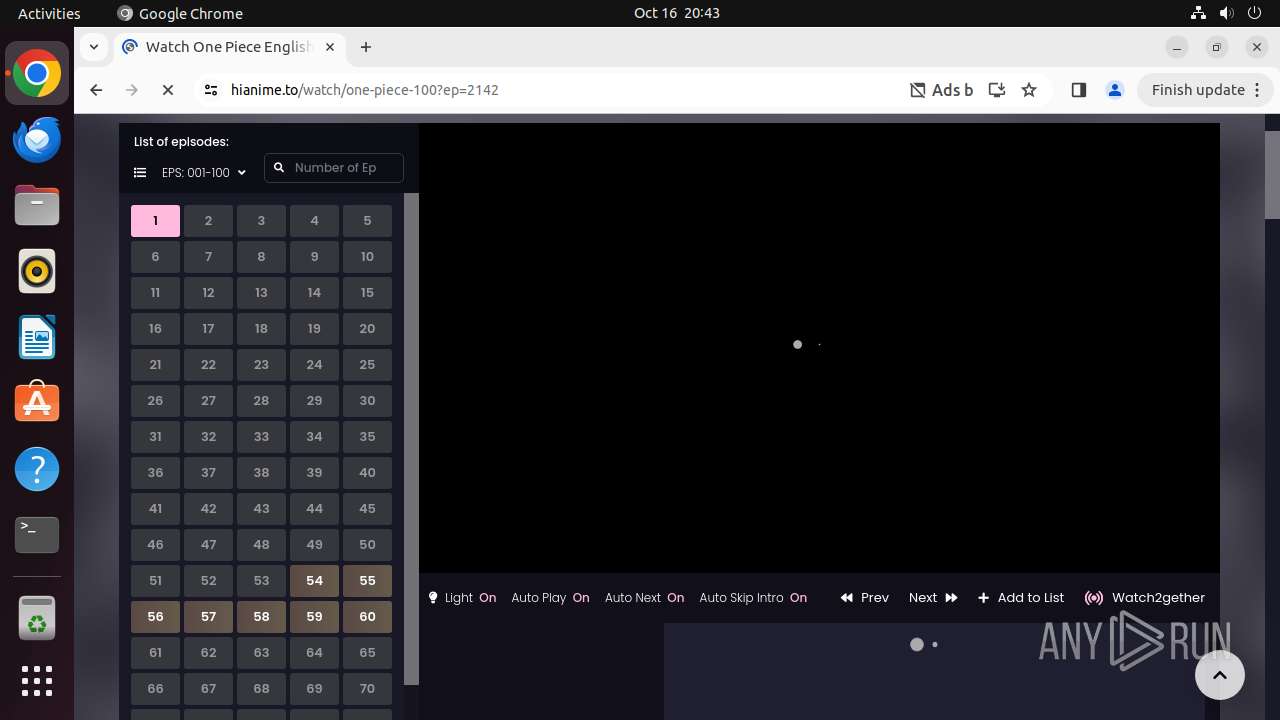
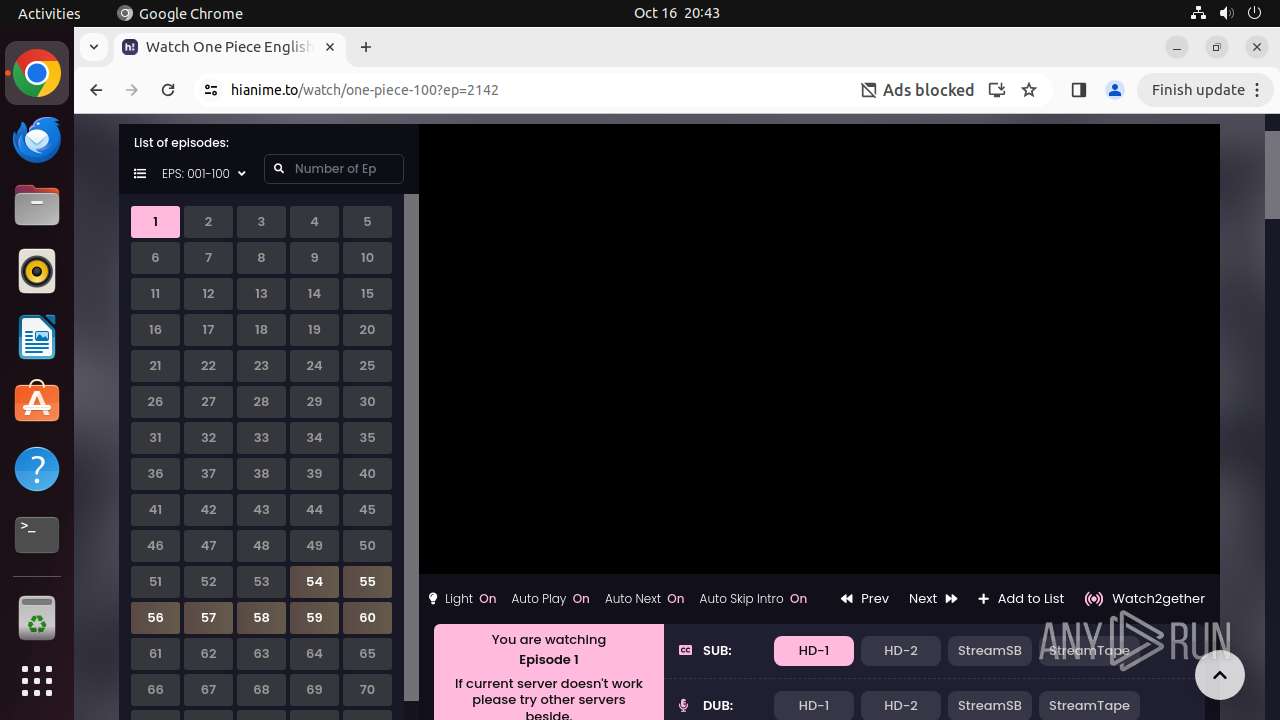
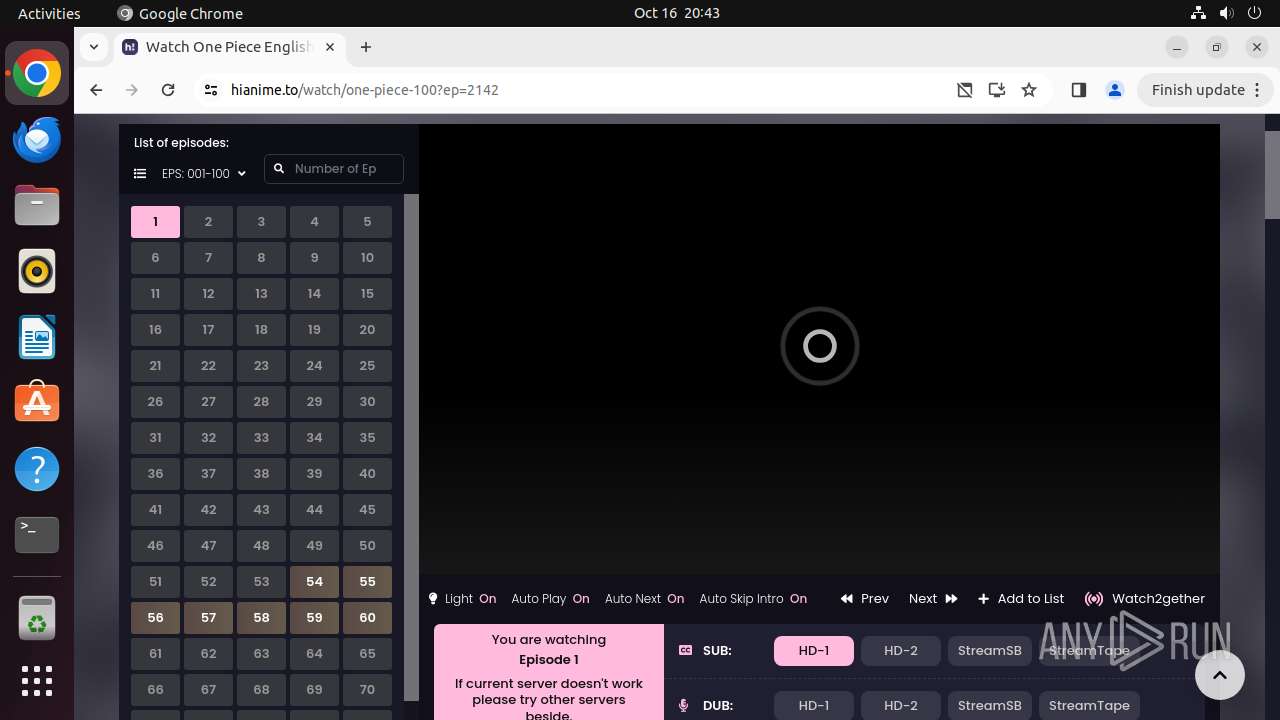
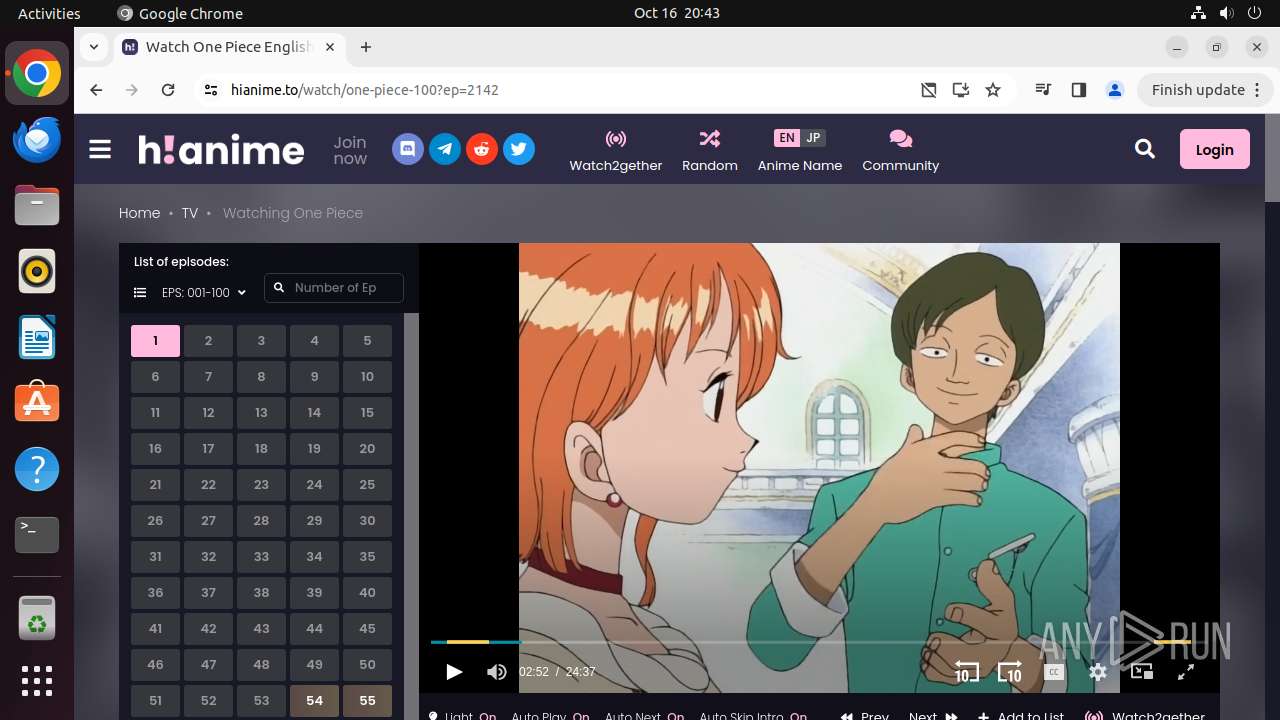
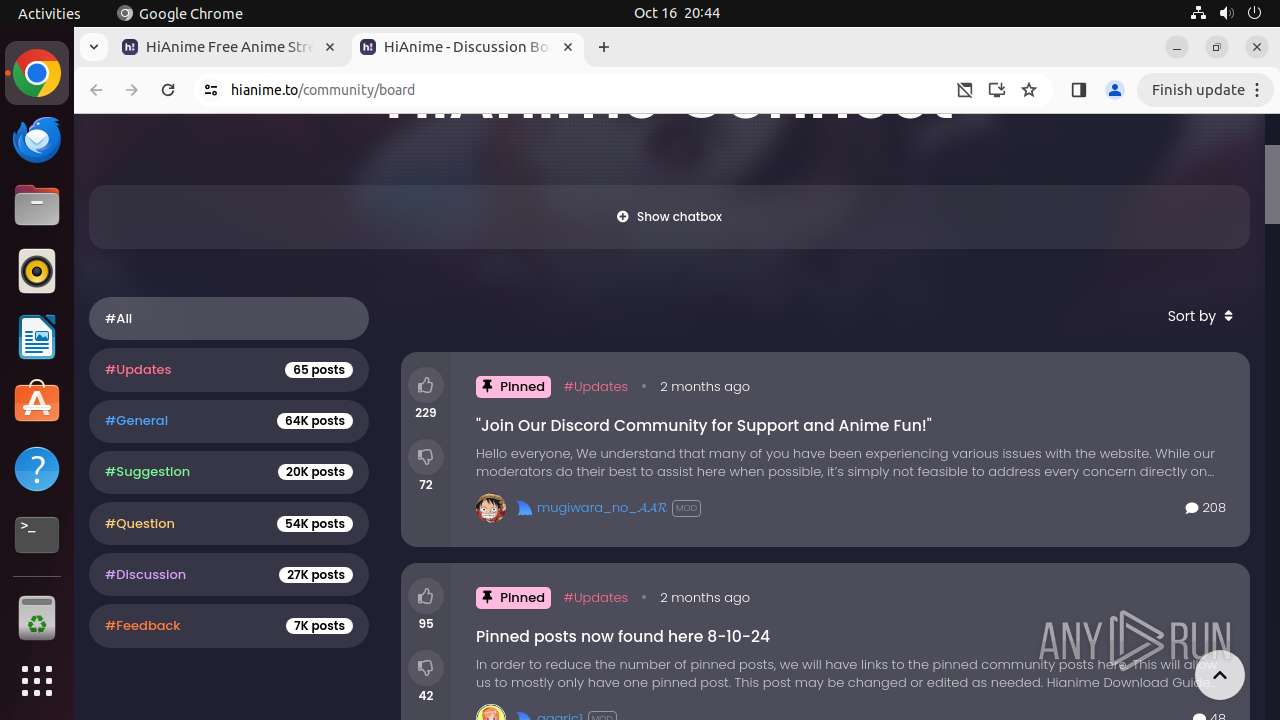
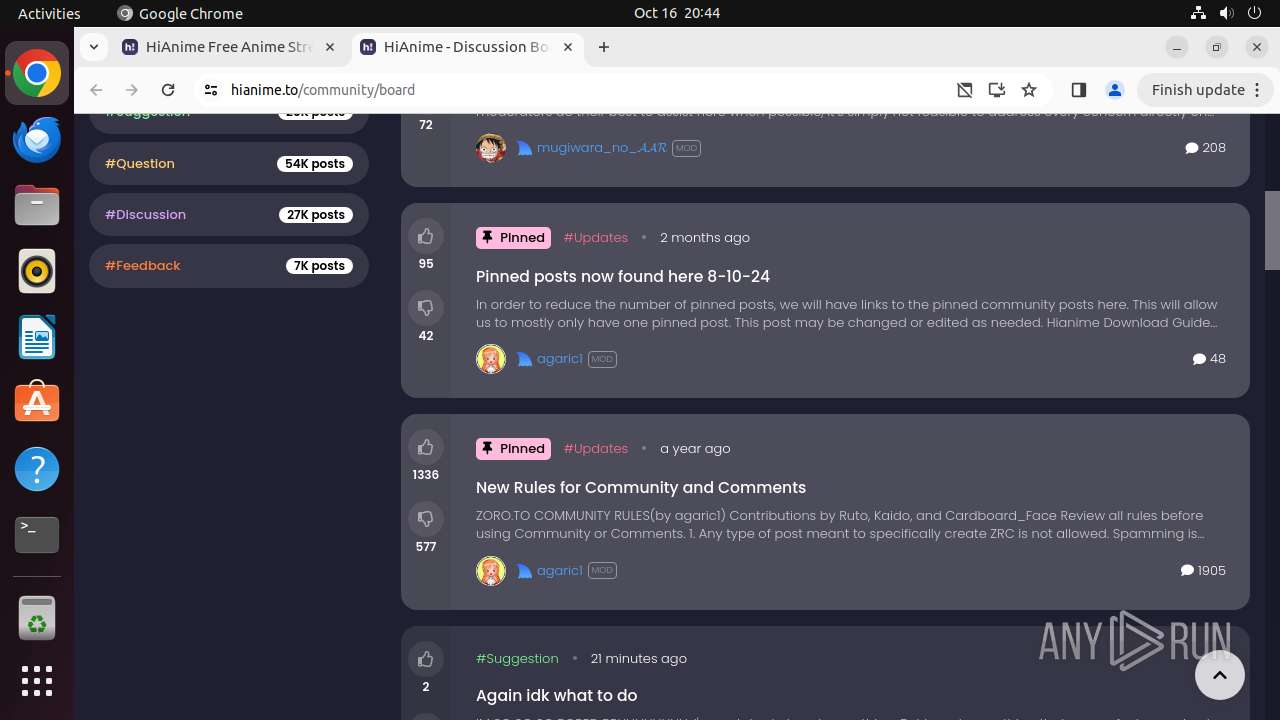
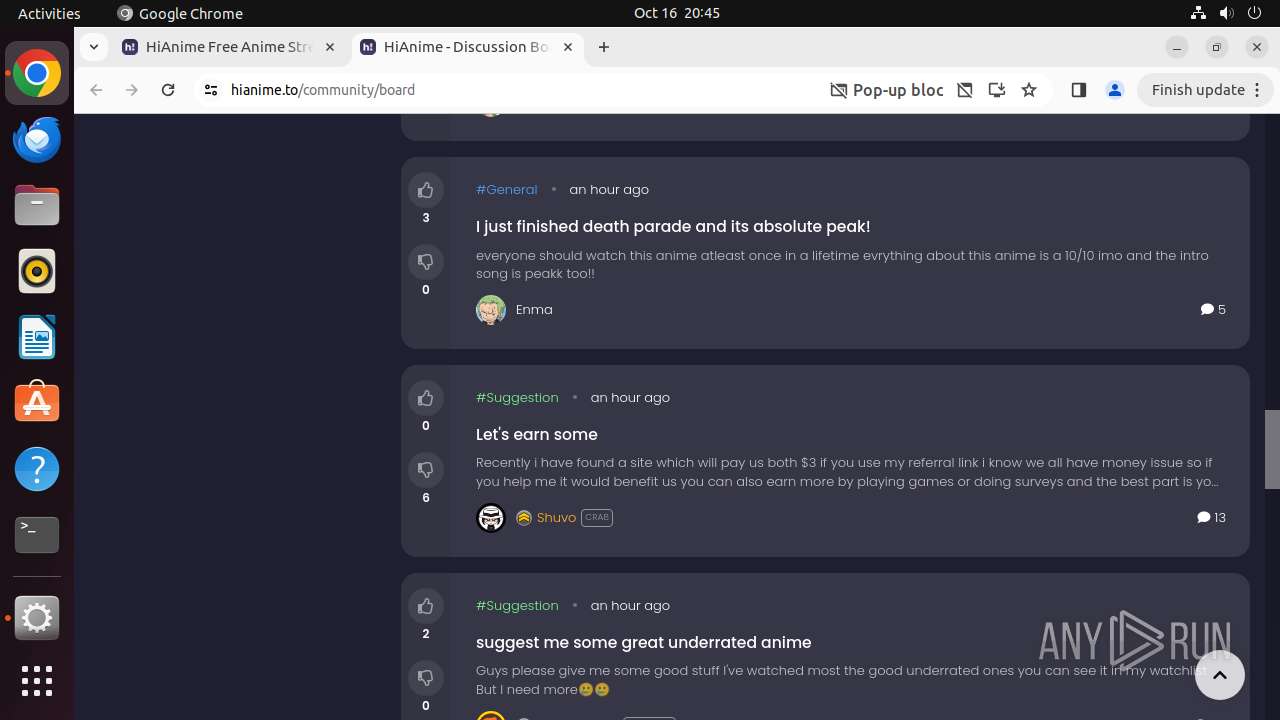
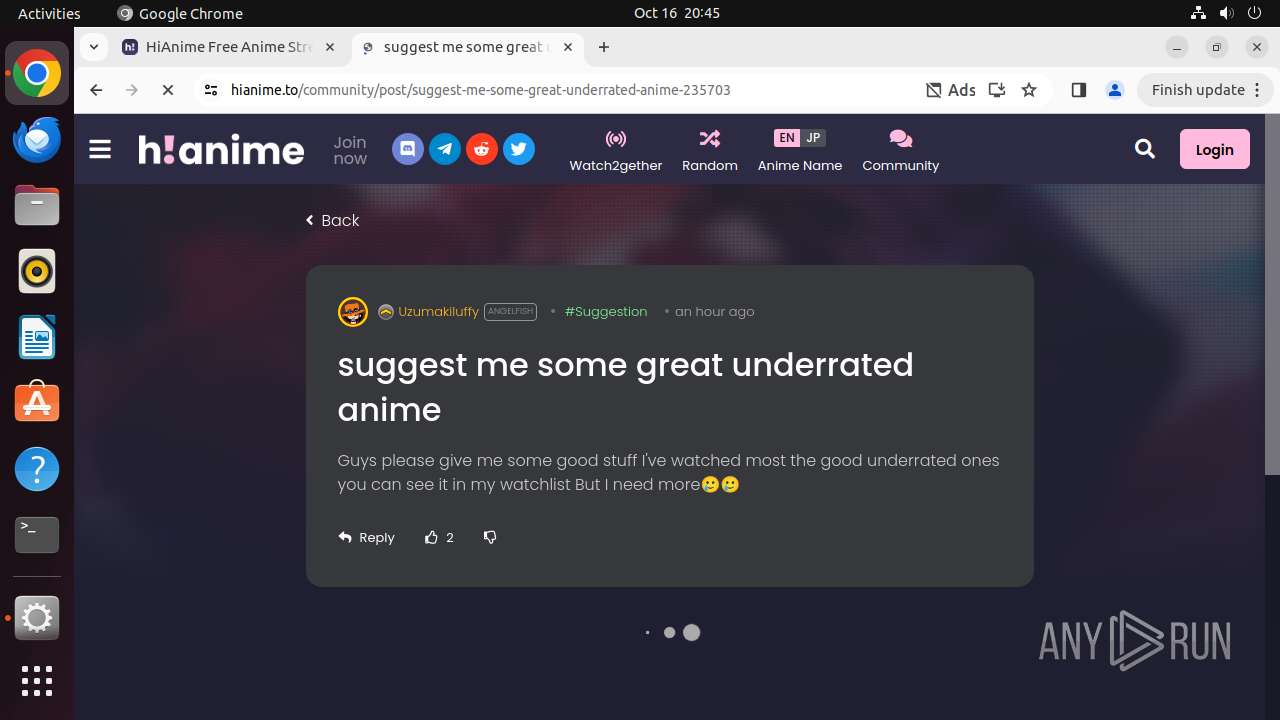
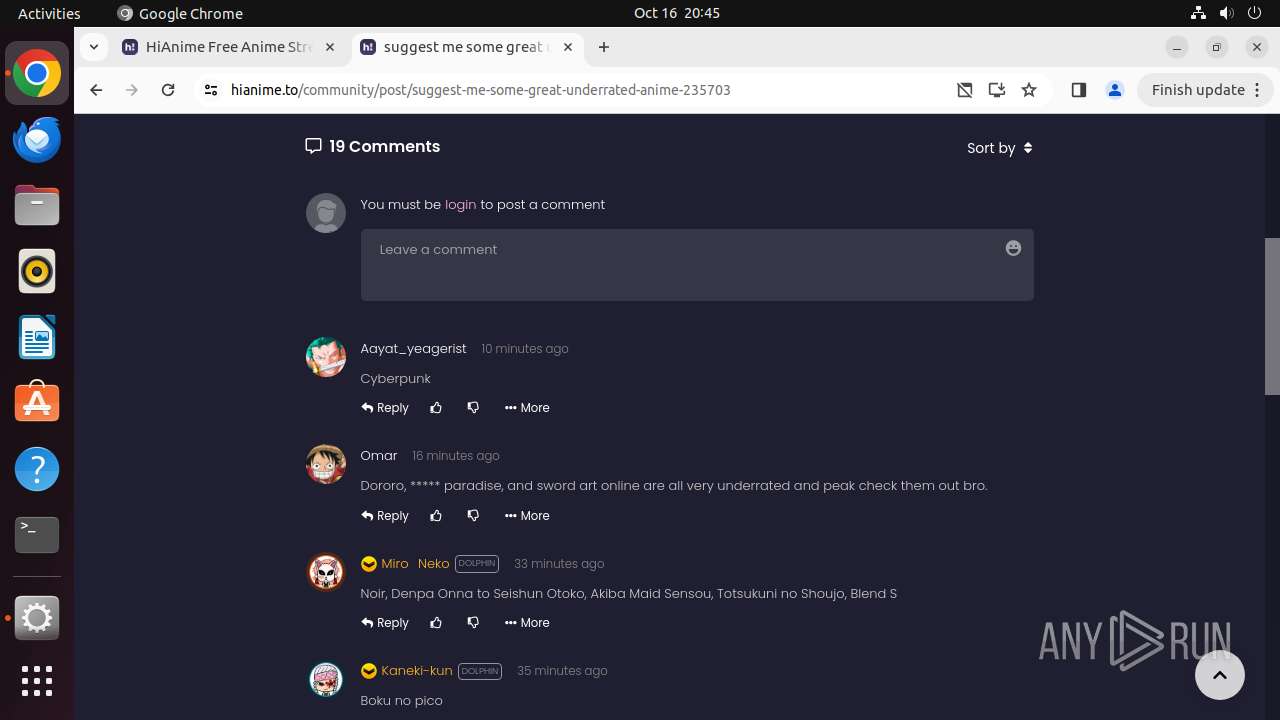
| URL: | hianime.to |
| Full analysis: | https://app.any.run/tasks/26d272ca-e5df-4f1c-820d-b11a4e9ff7f9 |
| Verdict: | Malicious activity |
| Analysis date: | October 16, 2024, 19:42:30 |
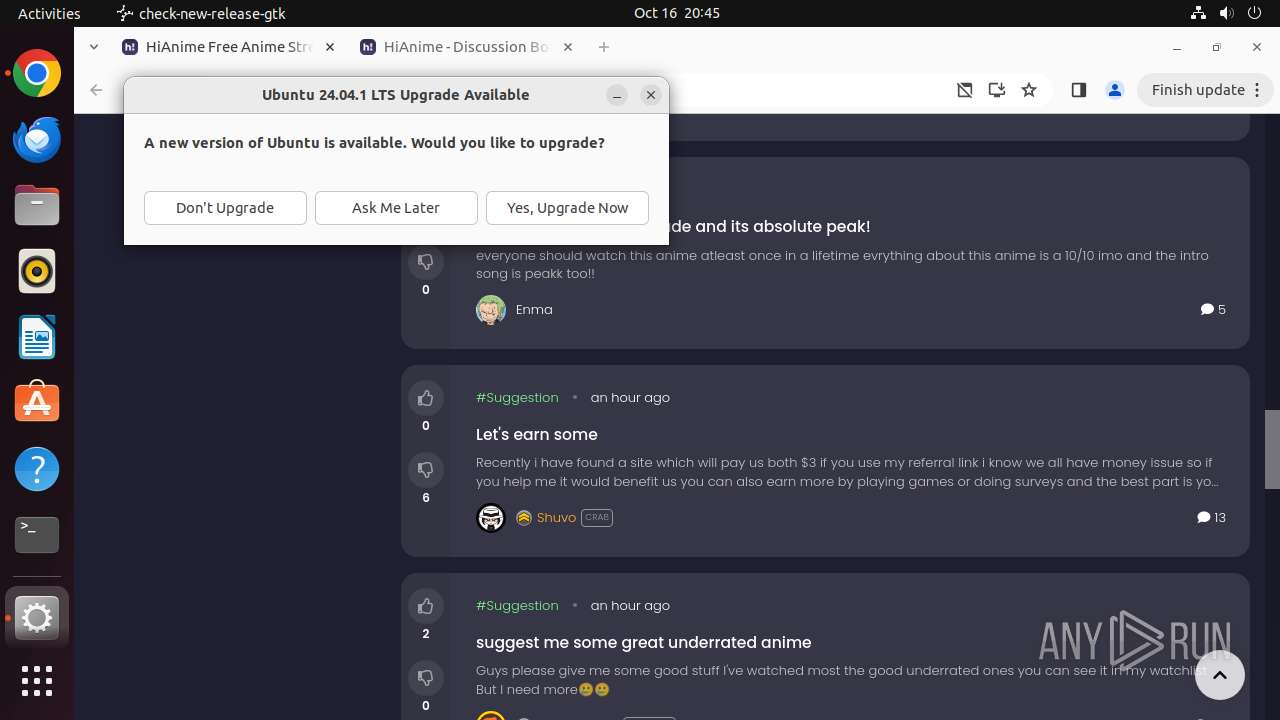
| OS: | Ubuntu 22.04.2 |
| Tags: | |
| Indicators: | |
| MD5: | 33DFC71708F50831A58069F5730CF4DD |
| SHA1: | FD3F97E7C3BE3F79EC9F54316D2F995DAD9B5D5B |
| SHA256: | 2B6999B813809F9D03C626187D12DBCB3BB2BCB473D6EE201A39347354C267B5 |
| SSDEEP: | 3:vJeKn:vJeKn |
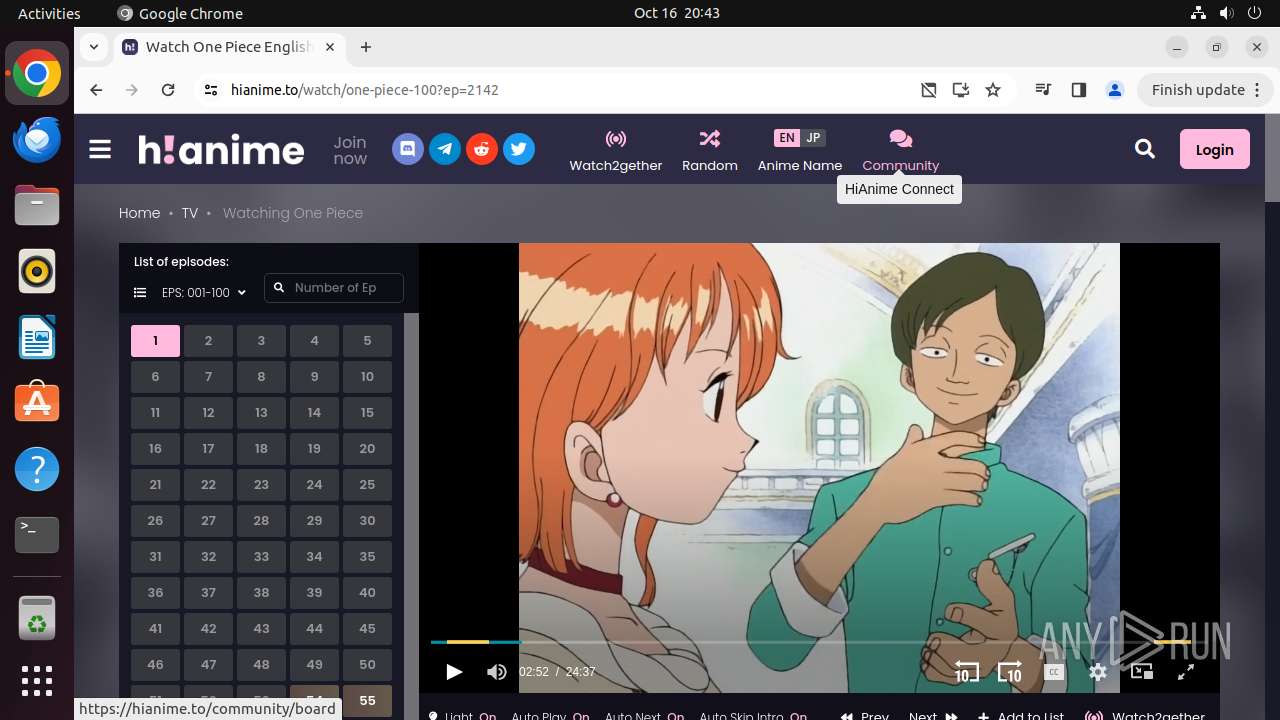
MALICIOUS
PHISHING has been detected (SURICATA)
- systemd-resolved (PID: 425)
SUSPICIOUS
Reads /proc/mounts (likely used to find writable filesystems)
- check-new-release-gtk (PID: 14382)
Executes commands using command-line interpreter
- update-notifier (PID: 14380)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
331
Monitored processes
115
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 425 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
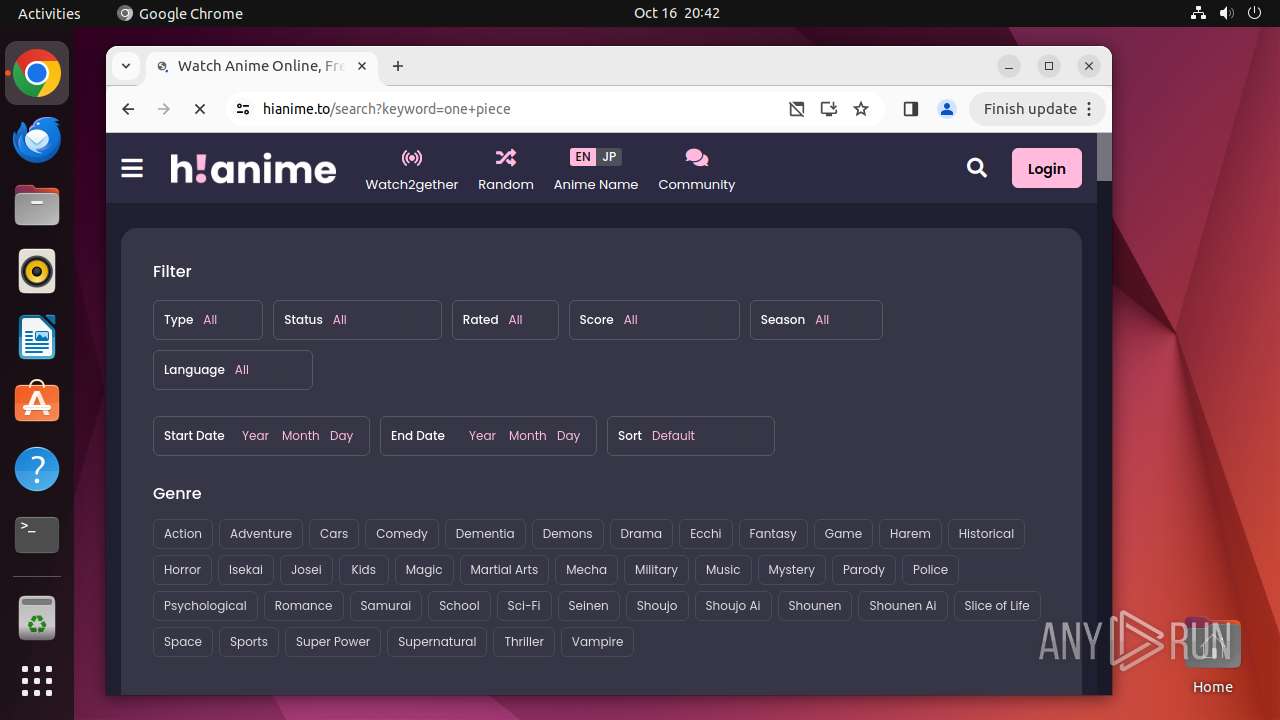
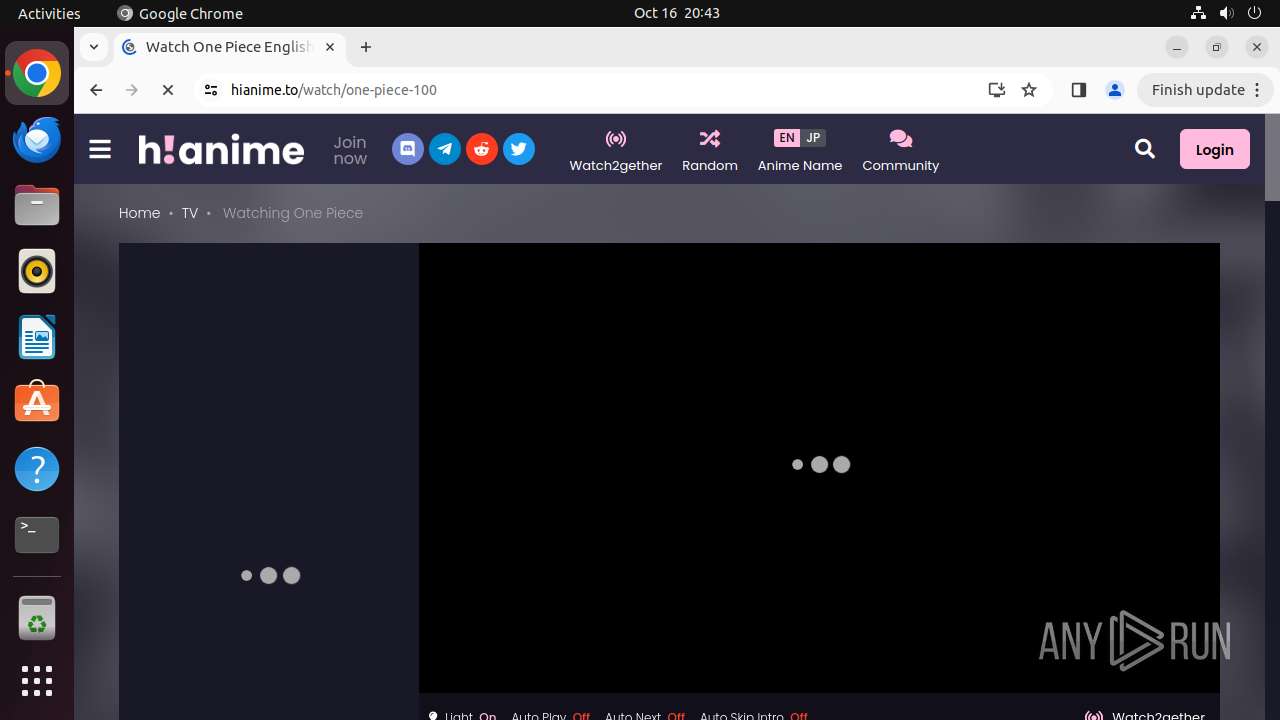
| 13907 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome hianime\.to " | /bin/sh | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 13908 | sudo -iu user google-chrome hianime.to | /usr/bin/sudo | — | sh |
User: root Integrity Level: UNKNOWN | ||||
| 13909 | /usr/bin/google-chrome hianime.to | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 13910 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13911 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13912 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13913 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 13914 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 13915 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
0
Suspicious files
174
Text files
30
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 13909 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_3 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_2 | vxd | |
MD5:— | SHA256:— | |||
| 13909 | chrome | /home/user/.config/google-chrome/Default/DawnCache/data_0 | vxd | |
MD5:— | SHA256:— | |||
| 14047 | chrome | /home/user/.cache/mesa_shader_cache/index | koa | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
183
DNS requests
167
Threats
19
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/diffgen-puffin/khaoiebndkojlmppeemjhbpbandiljpe/1.05399c5840405f4af2454470ceccaa3d097f07e271705cf37c1e5559ce793eeb/1.1471c6c104c7e11f08fd446f83dcdb396b1fef335f4e3c744007c2272064f538/44367e7bc13464ae48fa3a83edb9a1fc3258aa32540abba470d2ff291e5eaf0e | US | binary | 2.11 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYjhkYWYwZDctOTExOS00MGQ5LTgyNjAtN2FlY2ZjMDg0NmNj/1.0.0.17_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 3.07 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aciueukdrxvb6khkx2mvifmvt57a_20240902.672363756.14/obedbbhbpmojnkanicioggnmelmoomoc_20240902.672363756.14_all_ENGB500000_pioxf2kb34f767sqbe3w4sspgi.crx3 | US | binary | 5.13 Mb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aci7xcbi5ygkczfyeplr35qrrv7q_9213/hfnkpimlhhgieaddgfemjhofmfblmnib_9213_all_gxhl2vderv5a3k7bi4otlgz4by.crx3 | US | binary | 25.4 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/cxxqn654fg7hzrcrrnqcniqqye_2024.10.11.1/kiabhabjdbkjdpjbpigfodbdjmbglcoo_2024.10.11.01_all_jzb2rltf4ebriiaz3nap6gmbai.crx3 | US | binary | 8.87 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adrga7eefaxjfdmmgfkiaxjg4yjq_2024.7.12.235938/eeigpngbgcognadeebkilcpcaedhellh_2024.07.12.235938_all_a6r64uyugl6fjh3lupjqo6w7ai.crx3 | US | binary | 136 Kb | whitelisted |
— | — | GET | 204 | 185.125.190.49:80 | http://connectivity-check.ubuntu.com/ | GB | — | — | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/nkdqyxgspetpxm6ece2vvcdz6i_2024.10.14.0/niikhdgajlphfehepabhhblakbdgeefj_2024.10.14.00_all_adpge7qng6bobqgsemkddjdinrna.crx3 | US | binary | 6.56 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acp3a5xpze3h54y65zrkwk4buq3q_1103/efniojlnjndmcbiieegkicadnoecjjef_1103_all_hw2k6cj4xwsjglhdhioidhyxc4.crx3 | US | binary | 150 Kb | whitelisted |
— | — | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/admugesd67uiivm5lappcmd2nwba_470/lmelglejhemejginpboagddgdfbepgmp_470_all_ZZ_dd3t5gikcafm54yzihxds6vsva.crx3 | US | binary | 54.0 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
470 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 185.125.190.98:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 91.189.91.48:80 | connectivity-check.ubuntu.com | Canonical Group Limited | US | whitelisted |
— | — | 212.102.56.179:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
— | — | 185.125.190.49:80 | connectivity-check.ubuntu.com | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
485 | snapd | 185.125.188.59:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
— | — | 142.250.186.35:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivity-check.ubuntu.com |
| whitelisted |
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
hianime.to |
| unknown |
safebrowsing.googleapis.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
425 | systemd-resolved | Potentially Bad Traffic | ET DNS Query for .to TLD |
425 | systemd-resolved | Potentially Bad Traffic | ET DNS Query for .to TLD |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Bidirectional and low-latency communication CDN (cdn .socket .io) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Bidirectional and low-latency communication CDN (cdn .socket .io) |
425 | systemd-resolved | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Domain chain identified as Phishing (socketzone) |
425 | systemd-resolved | Not Suspicious Traffic | INFO [ANY.RUN] Bidirectional and low-latency communication CDN (cdn .socket .io) |