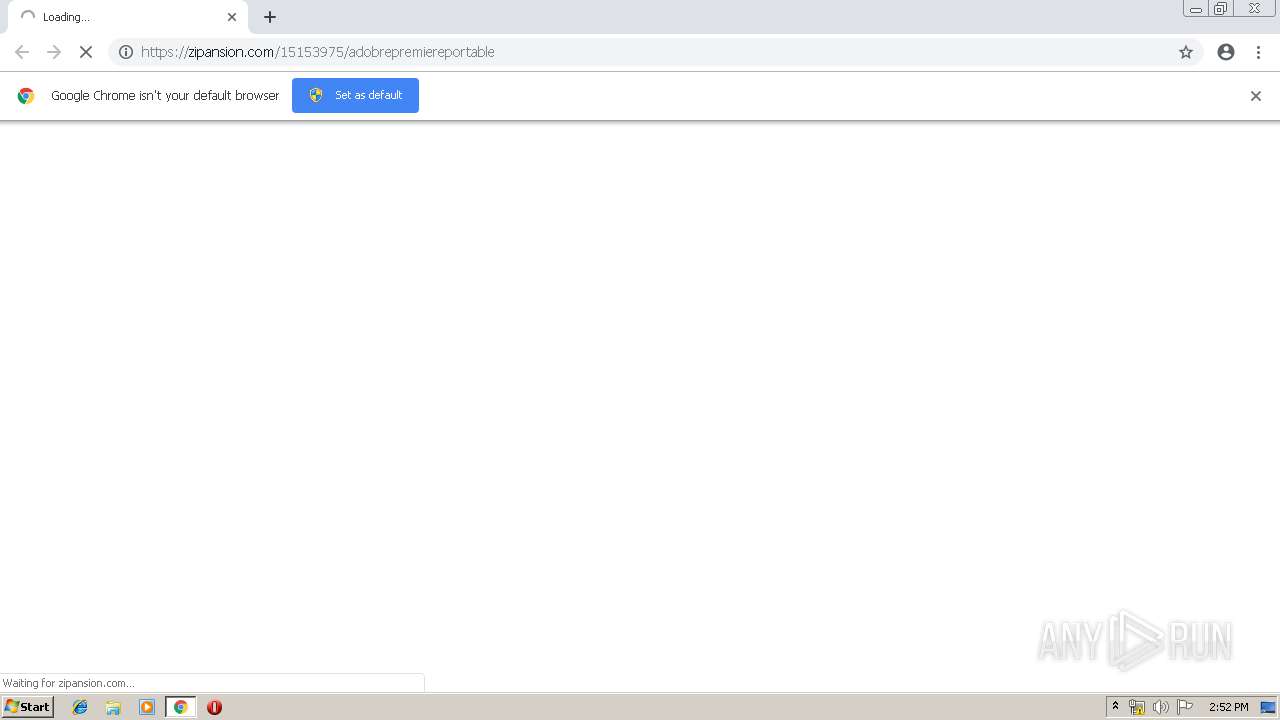
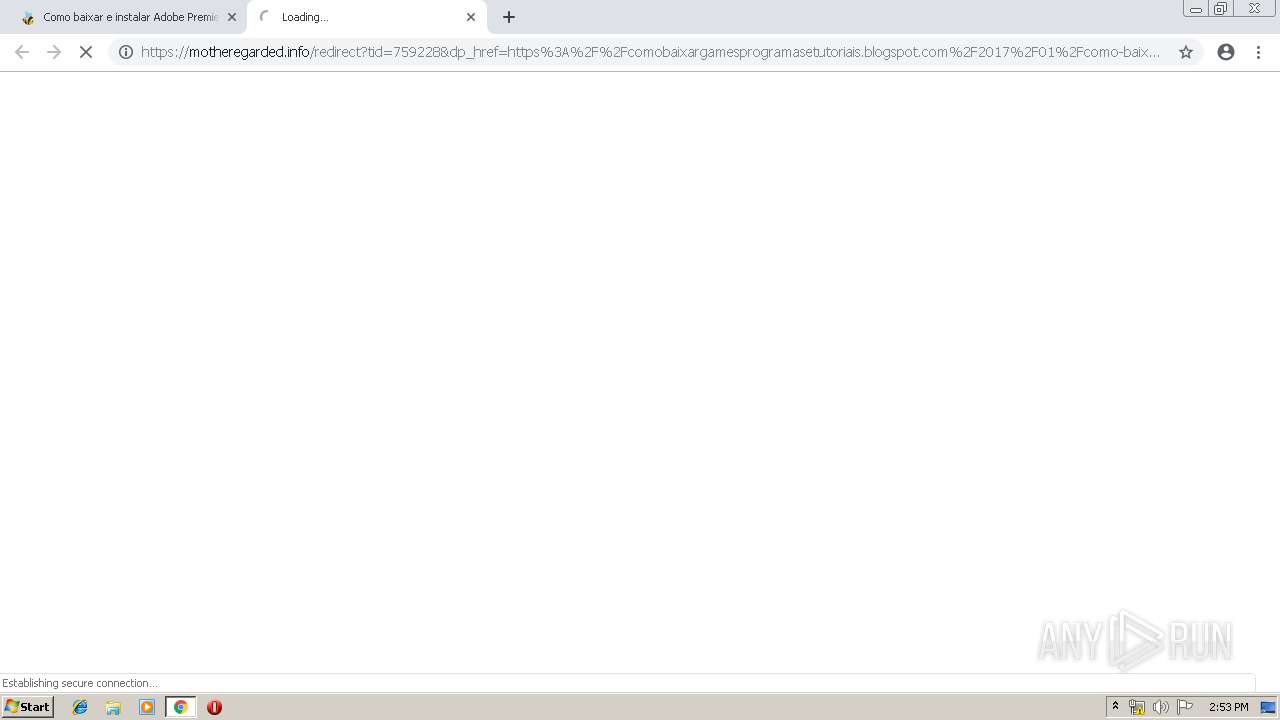
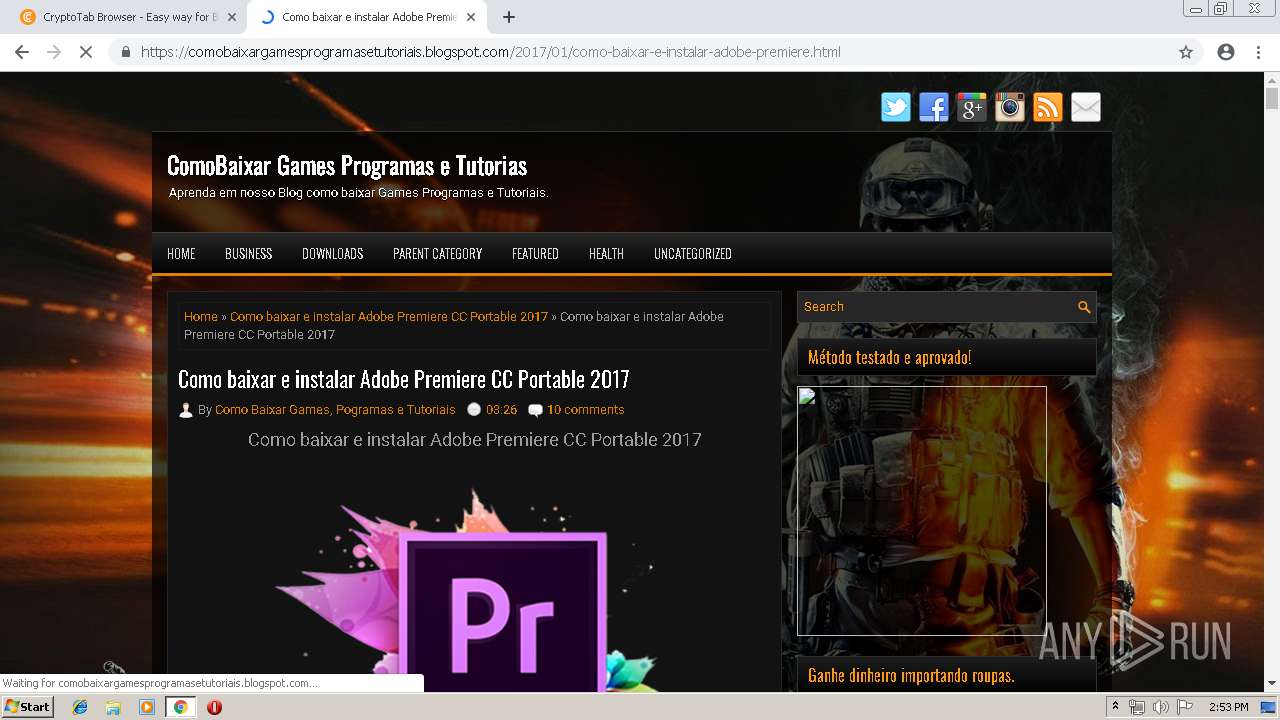
| URL: | https://zipansion.com/15153975/adobrepremiereportable |
| Full analysis: | https://app.any.run/tasks/bc198cd6-d7bc-4e3a-ad42-c9669635a3a3 |
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2019, 13:52:17 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A00BD595305A1CB46BB1CC0771BED111 |
| SHA1: | 00590A37A3D1EAB27481DE15F53506C3CABDB2FF |
| SHA256: | 2B53EE8603CC5DBAD9475BD156B0EC1821503F25373AB895393DCB09F694FDBB |
| SSDEEP: | 3:N8fW/yToUQ2QKocc5Eu:2fW/yTWc9u |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 2204)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 3828)
Modifies the open verb of a shell class
- chrome.exe (PID: 2204)
Dropped object may contain TOR URL's
- chrome.exe (PID: 2204)
Application launched itself
- chrome.exe (PID: 2204)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
66
Monitored processes
34
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17278698613379920990 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17278698613379920990 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4012 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --service-pipe-token=149936345498030390 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=149936345498030390 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=17921414881149996482 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17921414881149996482 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2924 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=15627383397094404485 --mojo-platform-channel-handle=4228 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 904 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8784503781744073338 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8784503781744073338 --renderer-client-id=32 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --service-pipe-token=15986217461281026634 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15986217461281026634 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15675072076810376395 --mojo-platform-channel-handle=2624 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --service-pipe-token=2312394881892865390 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2312394881892865390 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2360 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1720 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10589409726560908096 --mojo-platform-channel-handle=4008 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=968,2617367137757668551,8917391212861724207,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=10004508946579182932 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10004508946579182932 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
629
Read events
498
Write events
126
Delete events
5
Modification events
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1892) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2204-13199982755583875 |
Value: 259 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2204) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
237
Text files
191
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c8d8aced-3d04-4f47-a912-ed8e37eba705.tmp | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2204 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
50
TCP/UDP connections
129
DNS requests
81
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
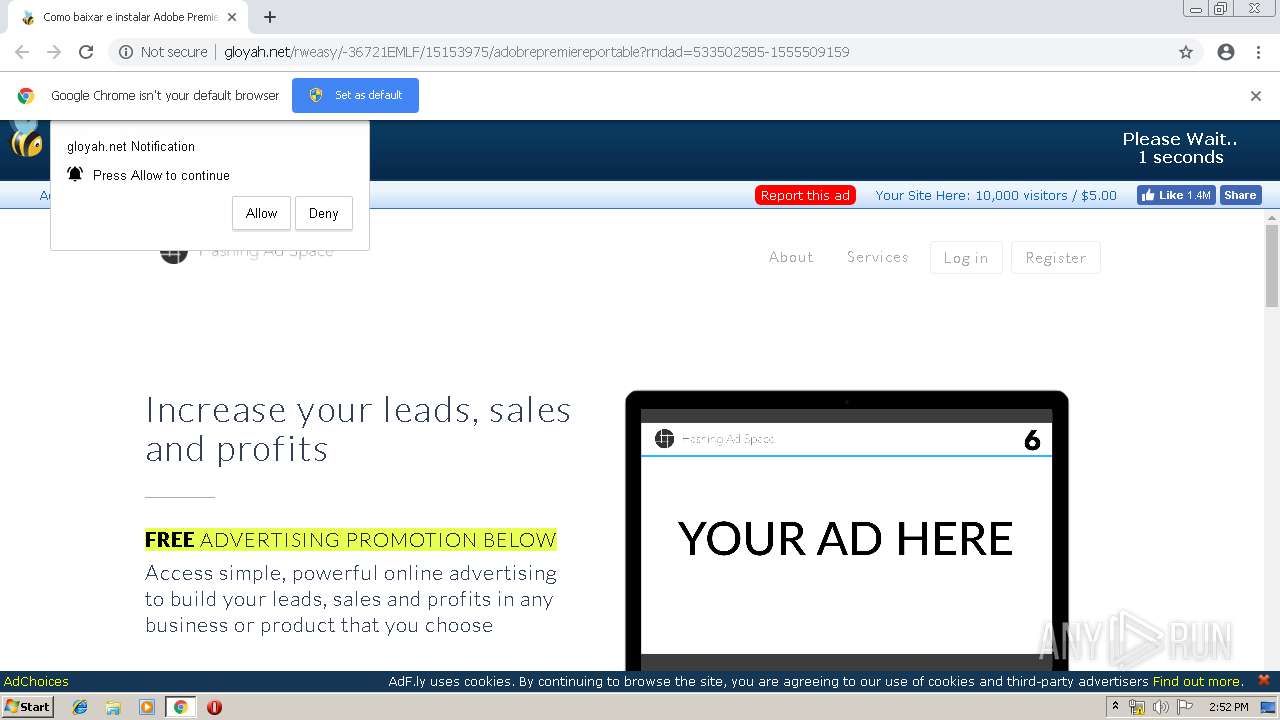
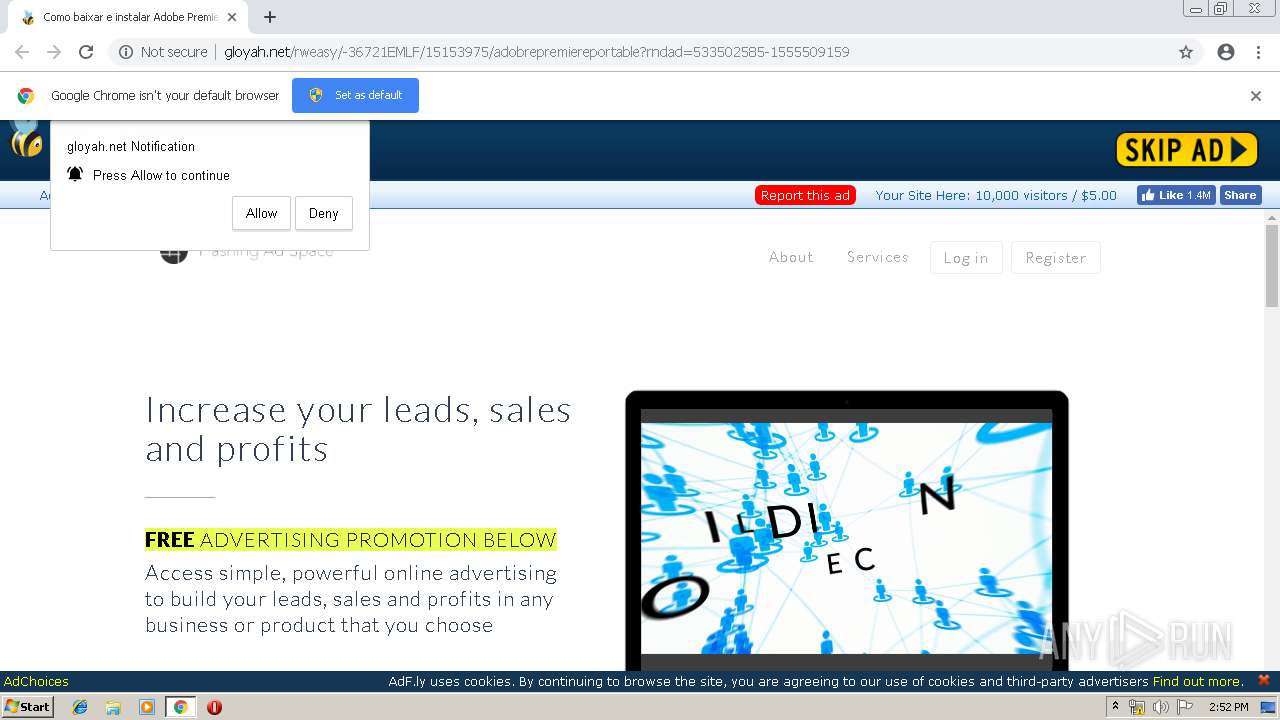
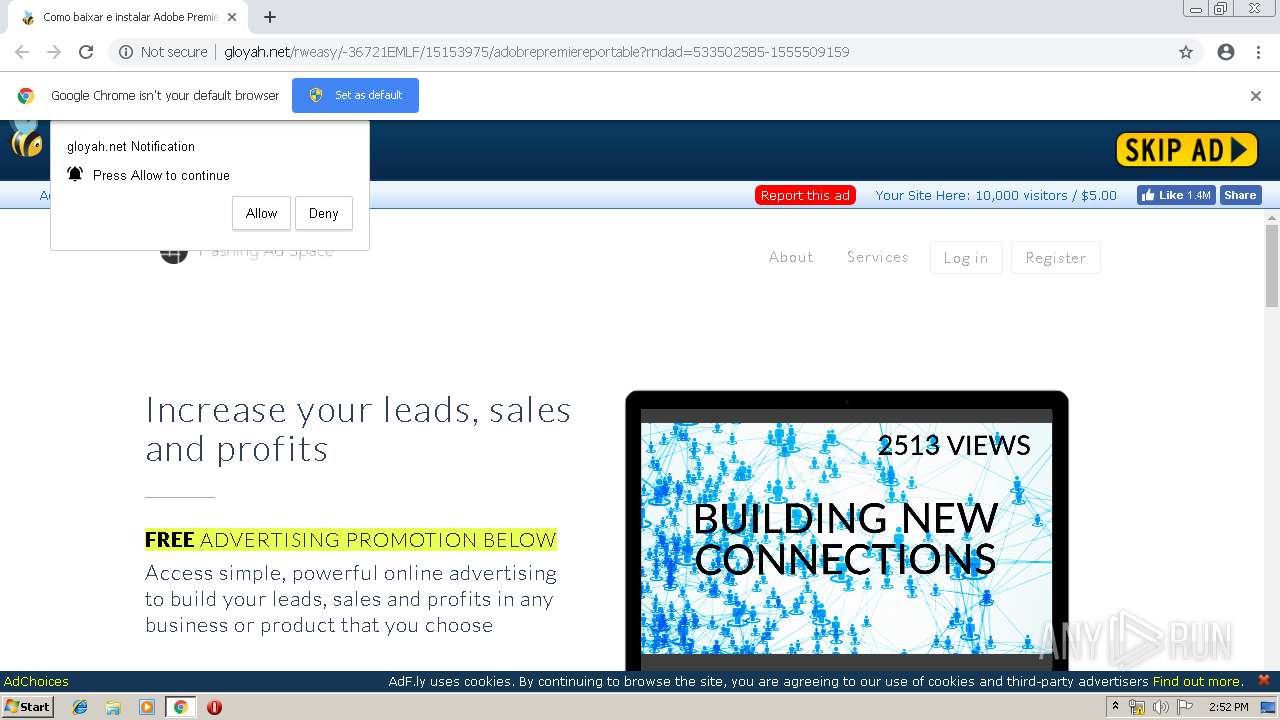
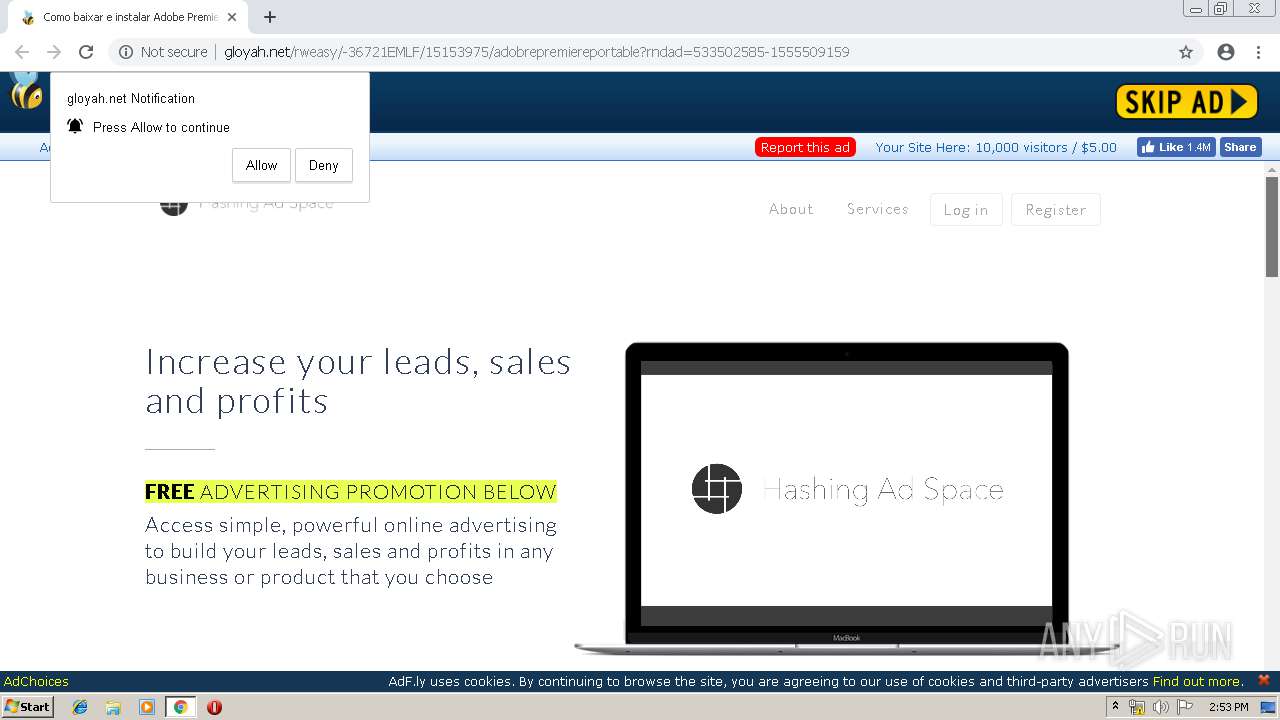
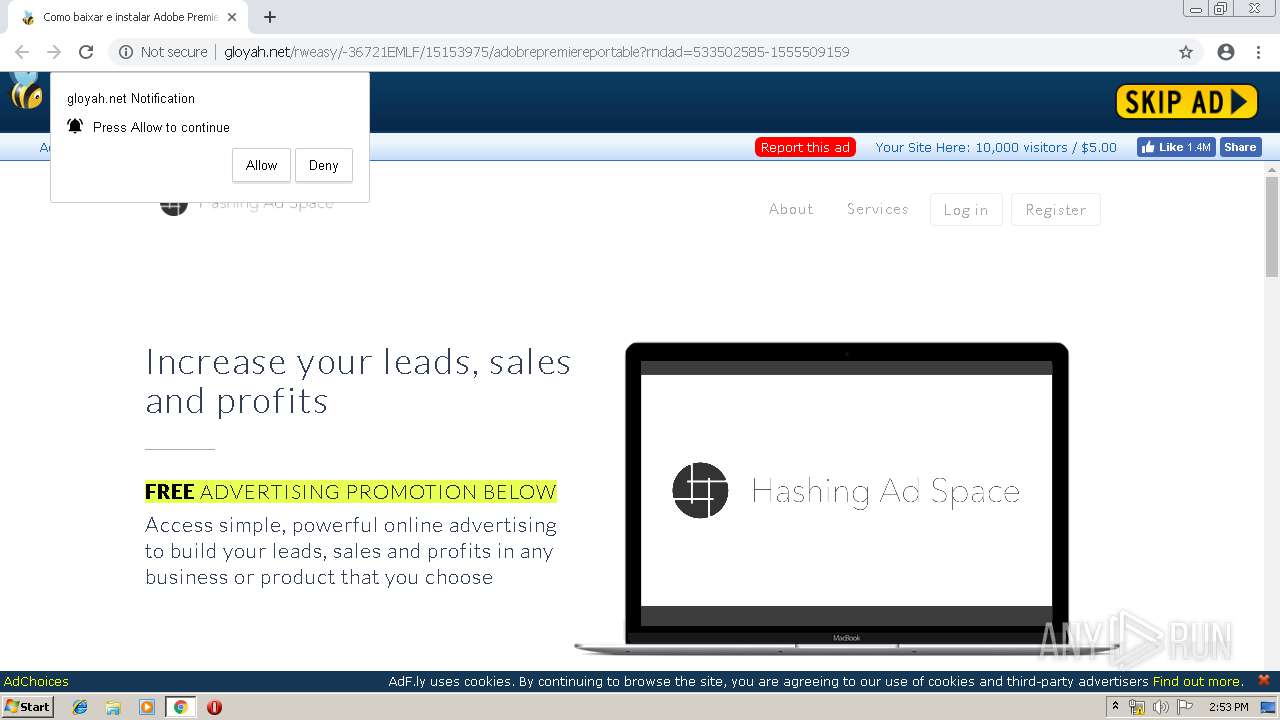
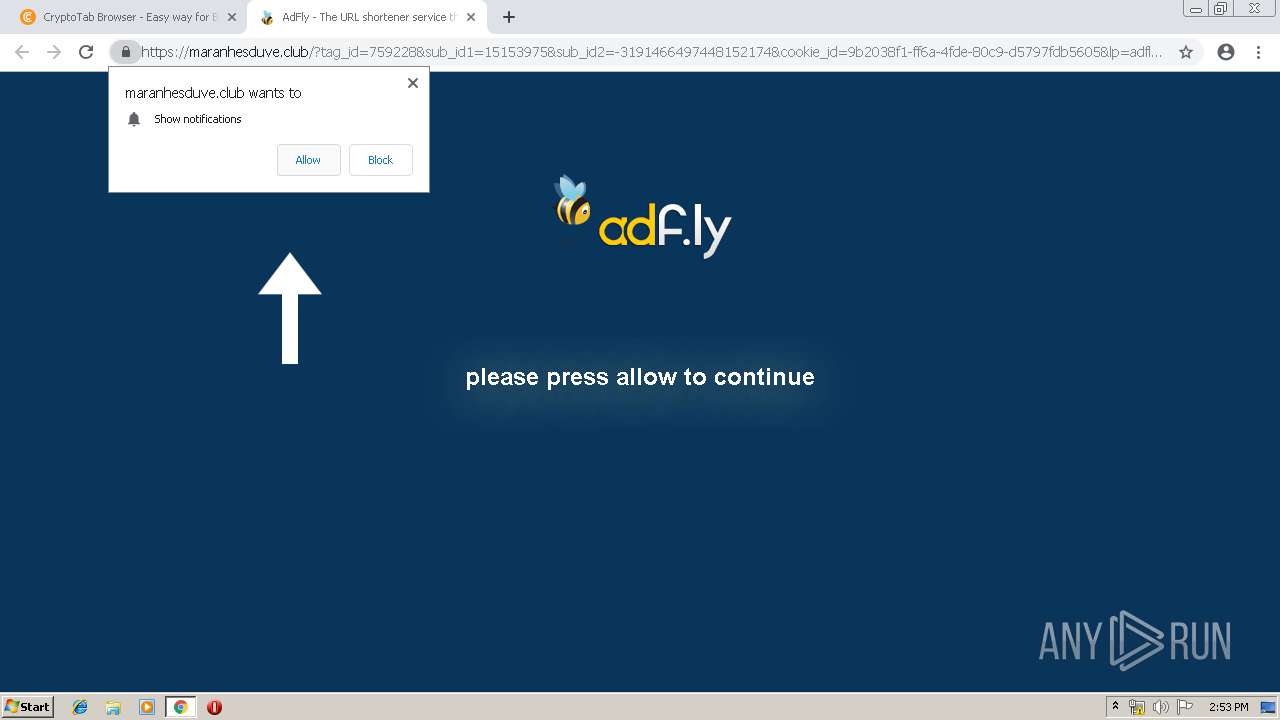
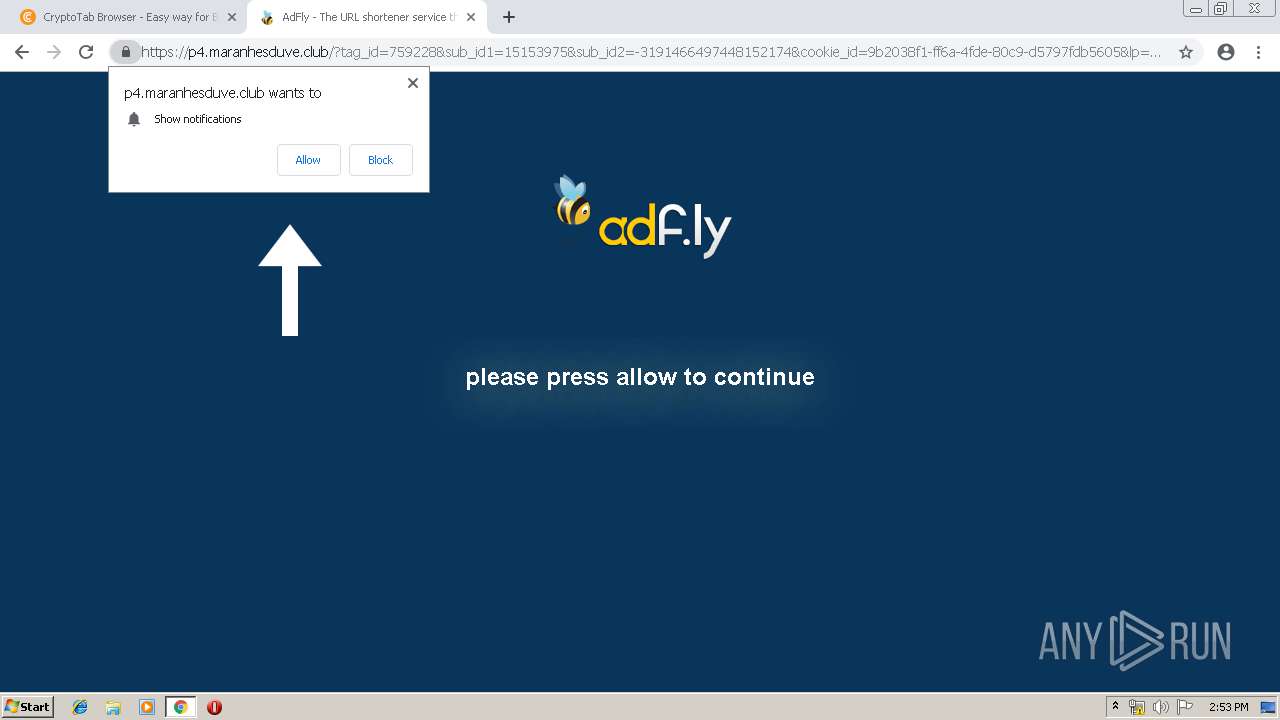
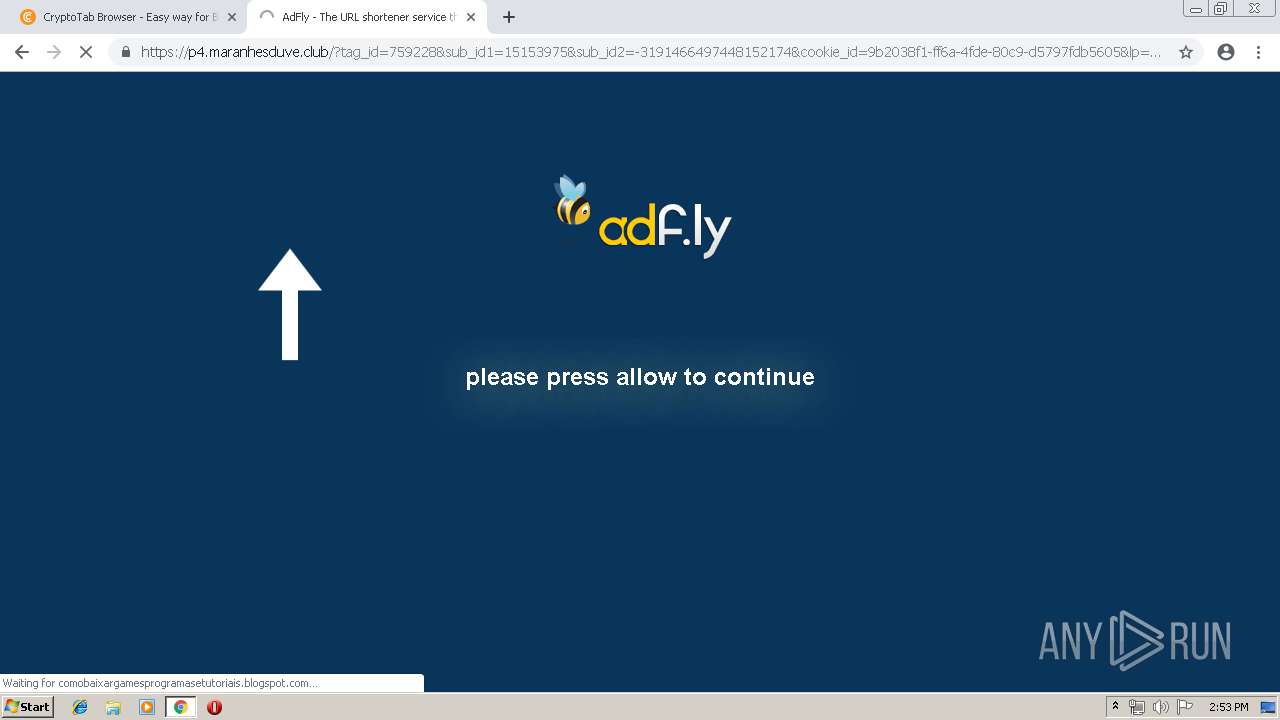
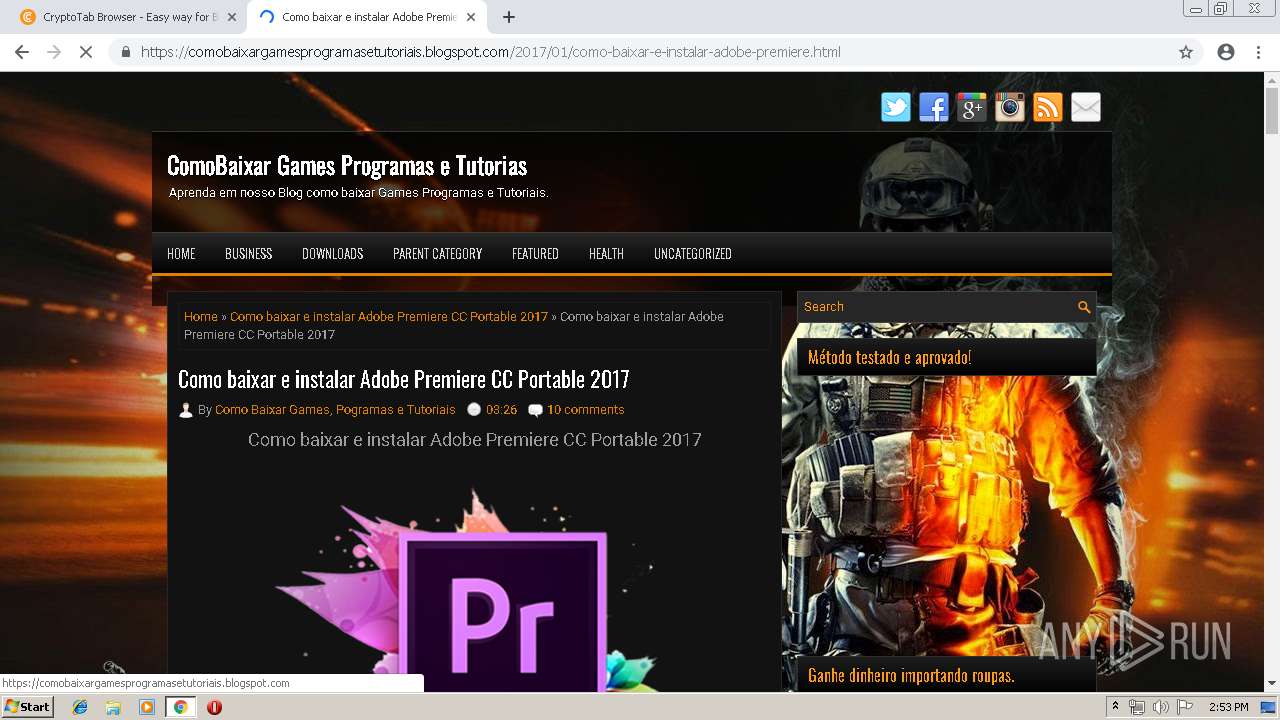
3828 | chrome.exe | GET | 301 | 104.27.155.99:80 | http://zipansion.com/15153975/adobrepremiereportable | US | — | — | malicious |
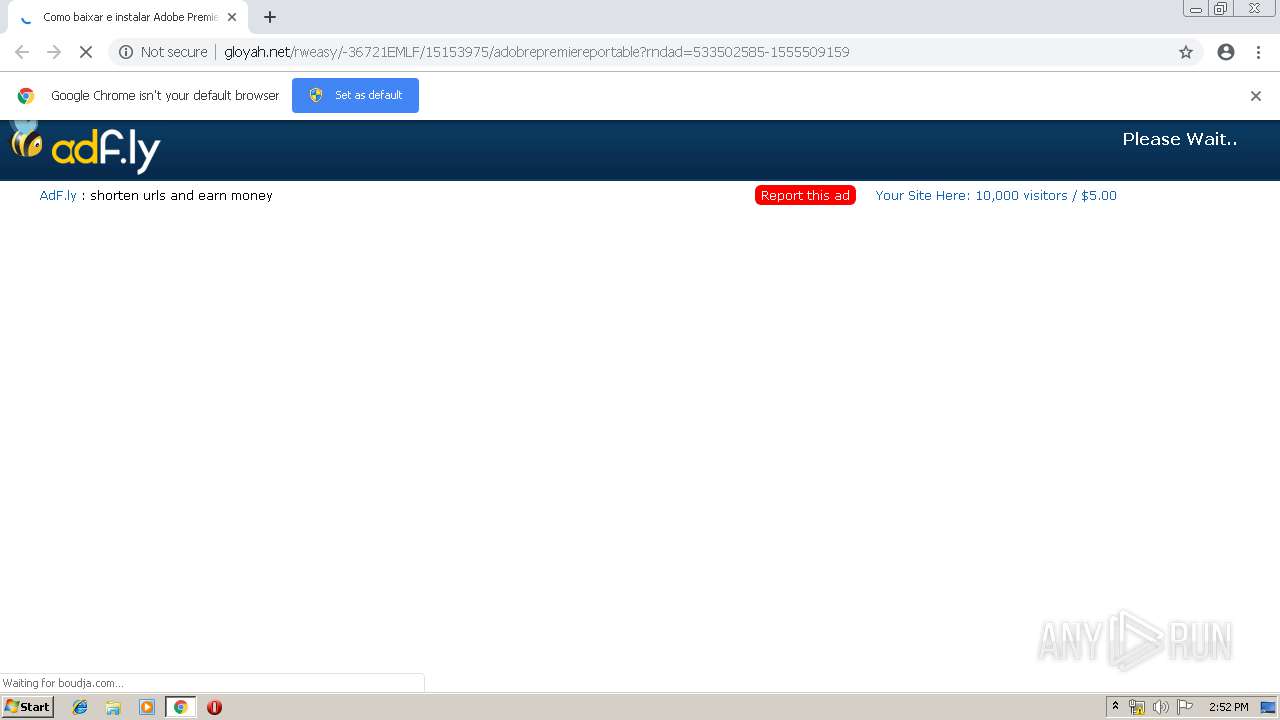
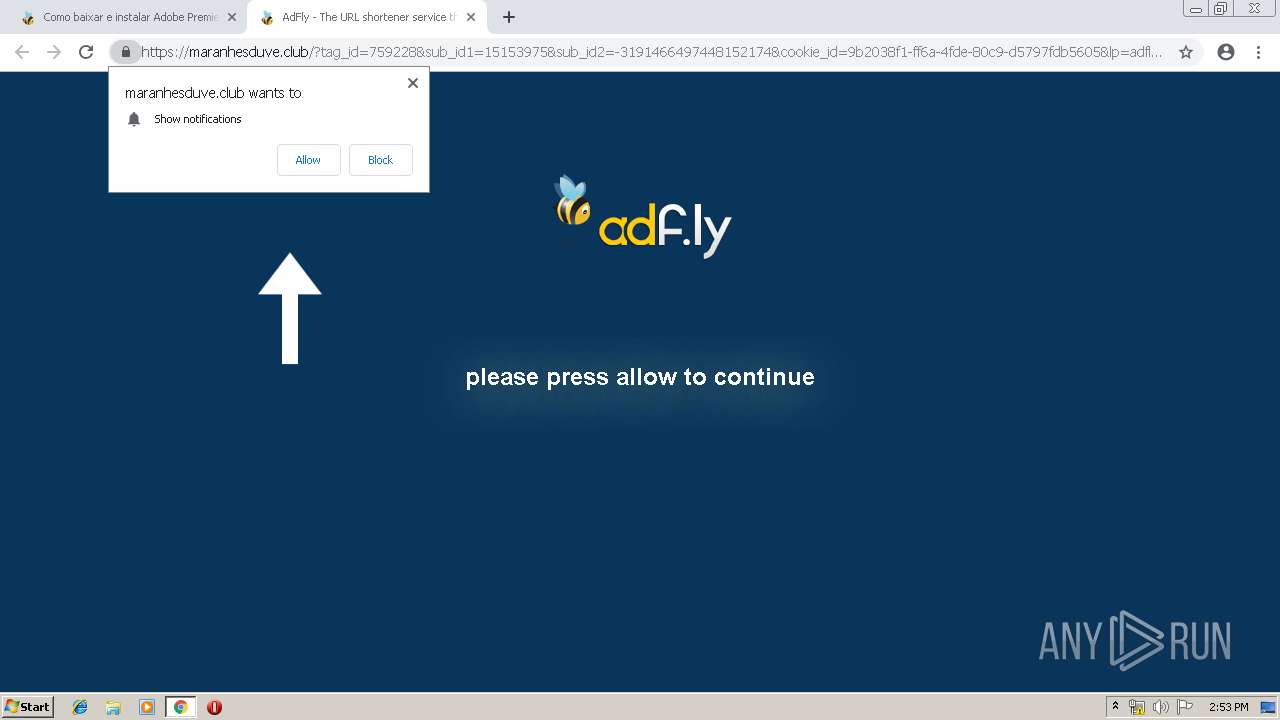
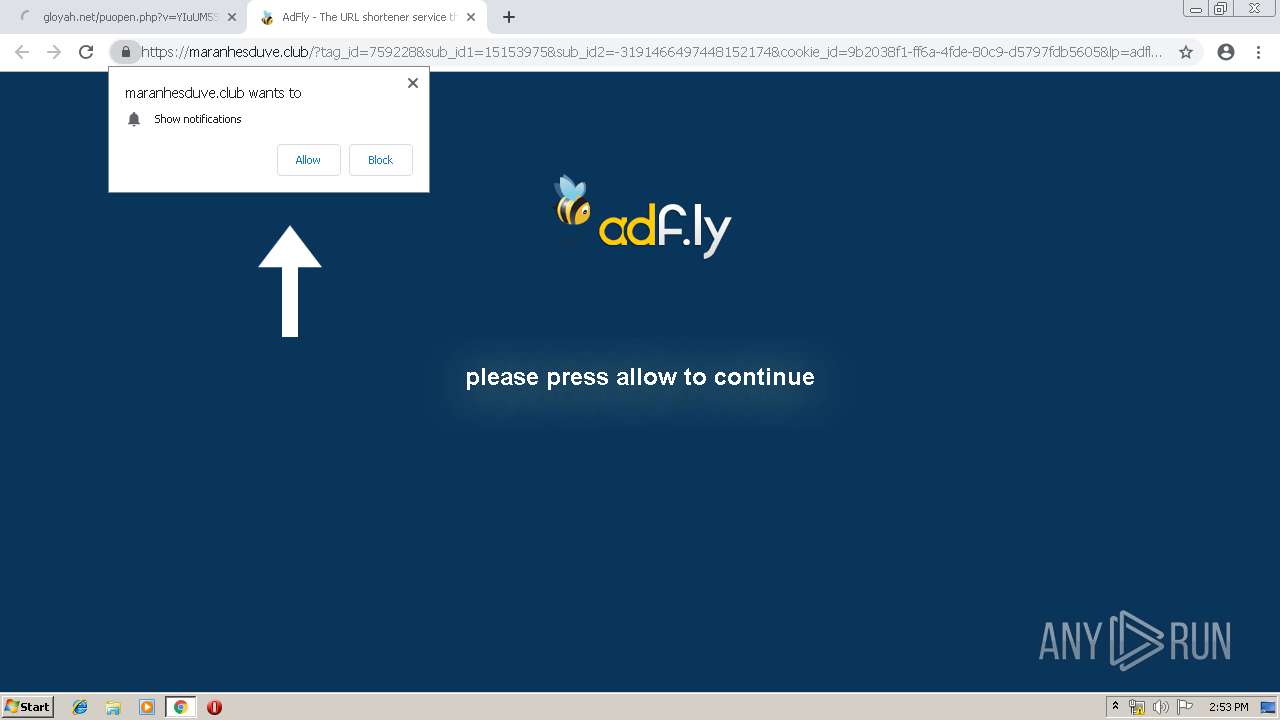
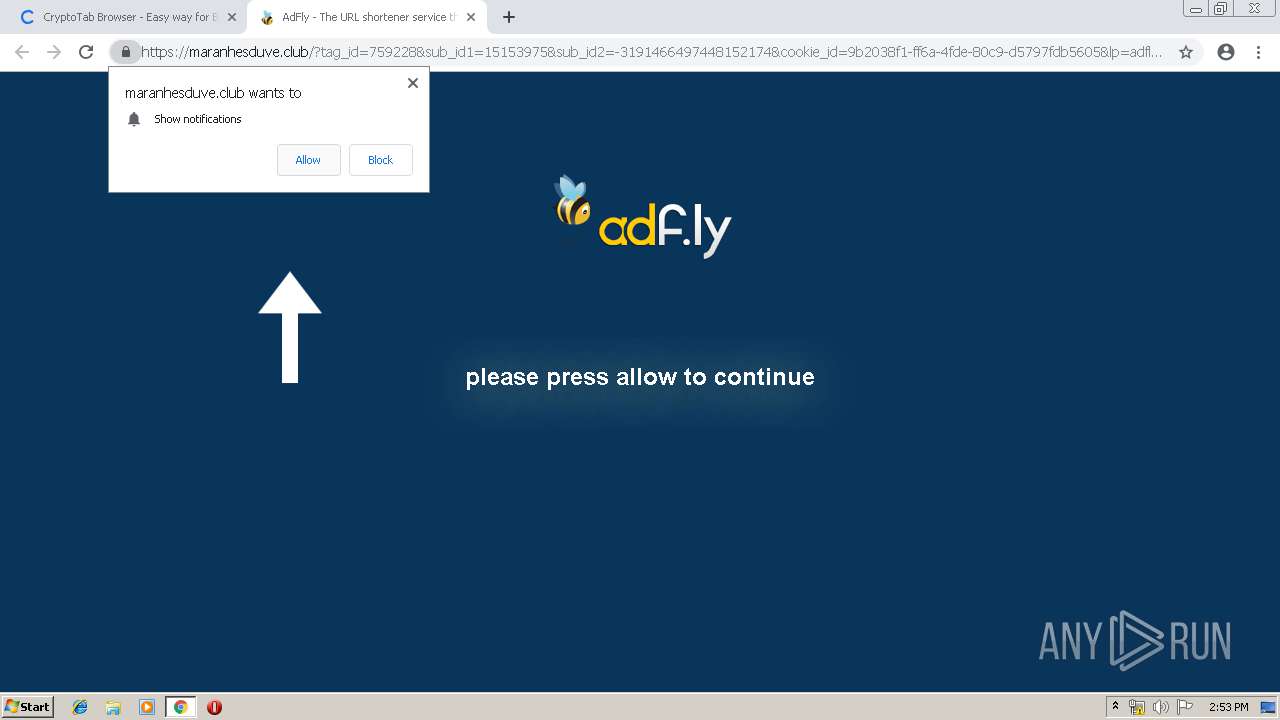
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://cdn.gloyah.net/static/js/b64.js | US | text | 1.08 Kb | suspicious |
3828 | chrome.exe | GET | 200 | 13.32.222.7:80 | http://d1nmxiiewlx627.cloudfront.net/?ixmnd=709056 | US | text | 38.8 Kb | whitelisted |
3828 | chrome.exe | GET | 204 | 34.225.238.53:80 | http://agreensdistra.info/NW1UbW4aUjceU2ApEVg6Bj88Ly93WAUqDXApLR44ezsVIiJwPzNLGlwJaVteAV5iWUhFBDBQXxMeIAwaQB5pXEhcAzICUxMbaVxABll6VUAESyAdD1JQZUseQRk4UF8AWGFYXgxcYVRYDVs | US | — | — | unknown |
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://gloyah.net/funcript1555509159885.php?pub=15153975&v=aDHBJSvKbvWtU2vYNlzdMEuIMlCt4WzaNsjBgCzLLMj1cE1VIIFtNEhKZgmYFzyMauSc8z1MM1z8cCudMpztYkiYLlCdJV1ZZsCBIH6cMBTBUSxKNxT4Mi5NNgzQUlsTIgnMY3idOvjRImsbIpmdNFrKIgjApj0Lc1n8VSlYLsCxJWwaY6X9QWiTOijoQjyIL0C5JWiZanWF5mkcRlWNxXldbiWwViuIdzCdI36bIkn5NWraaXXJBifOYinMU3ybdfHBR3vbb0itI2scIlmRhmhIcs2IgyibOOiJJiiOYimME31bYfjVcGzbZpGJR2lbMtzJZCiLMwzokjyIOlTxZWkaYij9gWybOiTwUC2MY6TIYC4aZzmFZGkbNmCJJy9e | US | text | 59.0 Kb | suspicious |
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://cdn.gloyah.net/static/css/adfly_7.css | US | text | 869 b | suspicious |
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://cdn.gloyah.net/static/js/amvn.js | US | text | 87.6 Kb | suspicious |
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://cdn.gloyah.net/static/js/main.js | US | text | 673 b | suspicious |
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://cdn.gloyah.net/static/js/view105b.js | US | text | 26.5 Kb | suspicious |
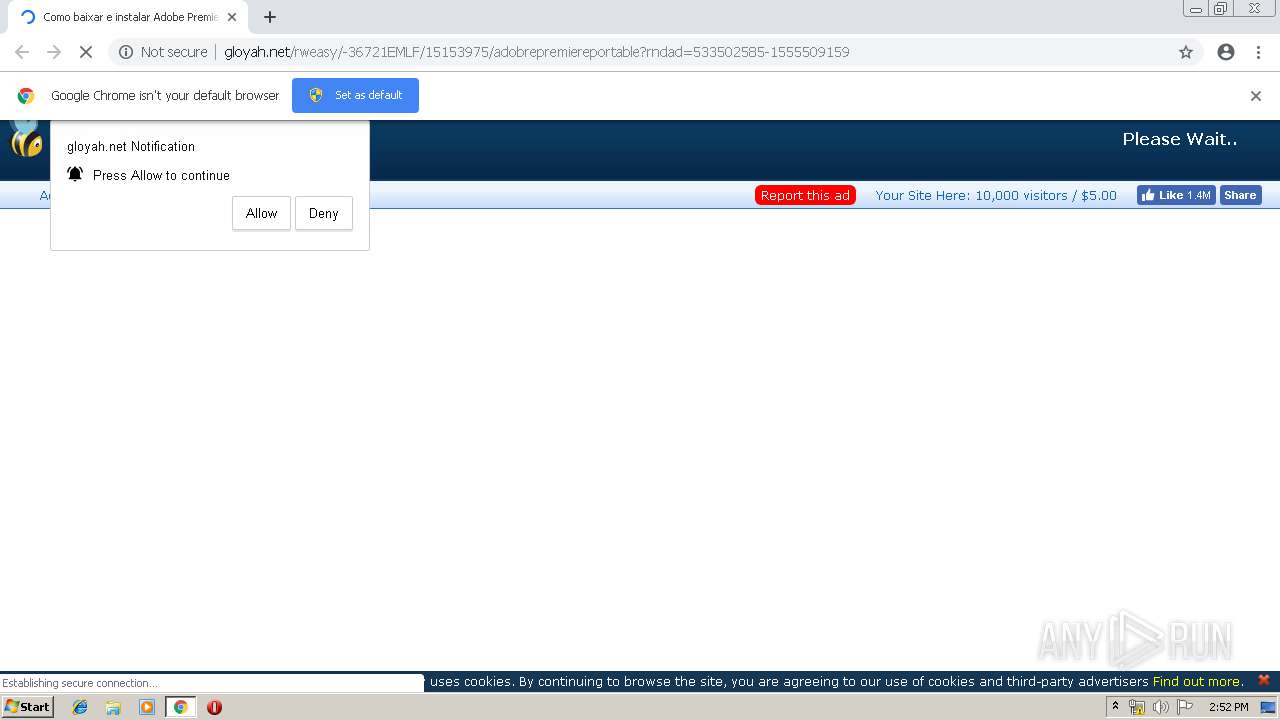
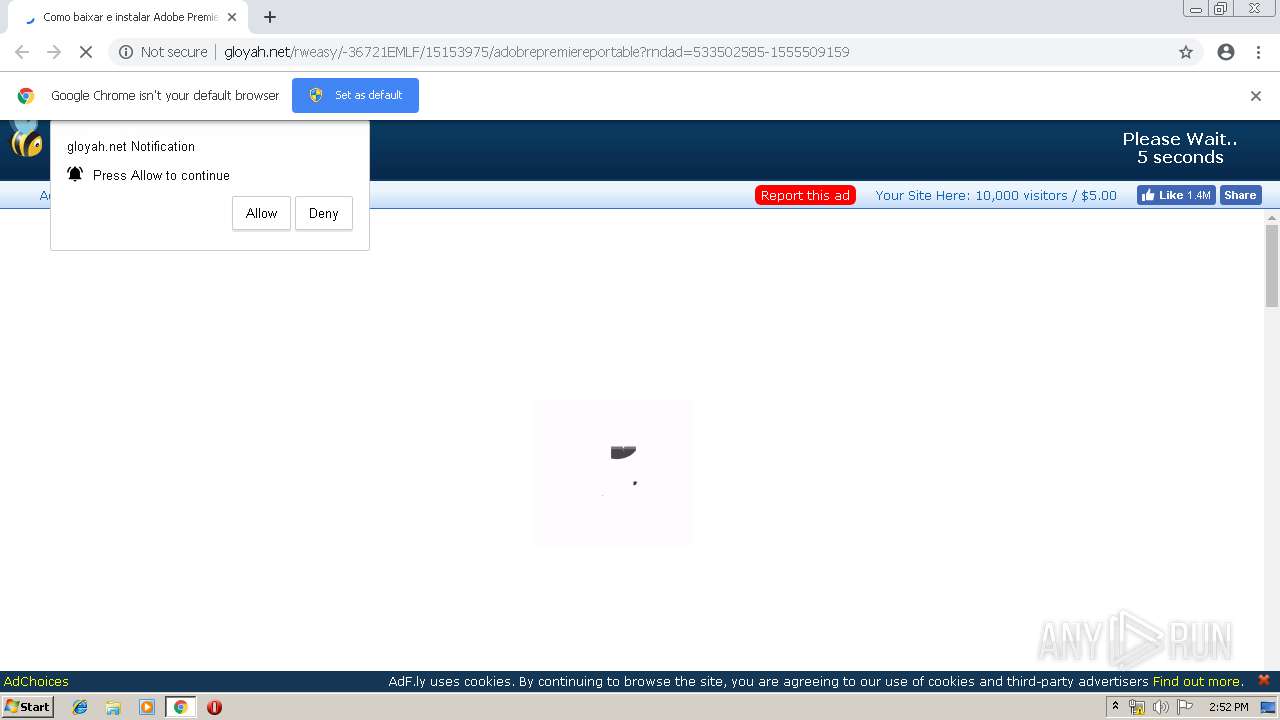
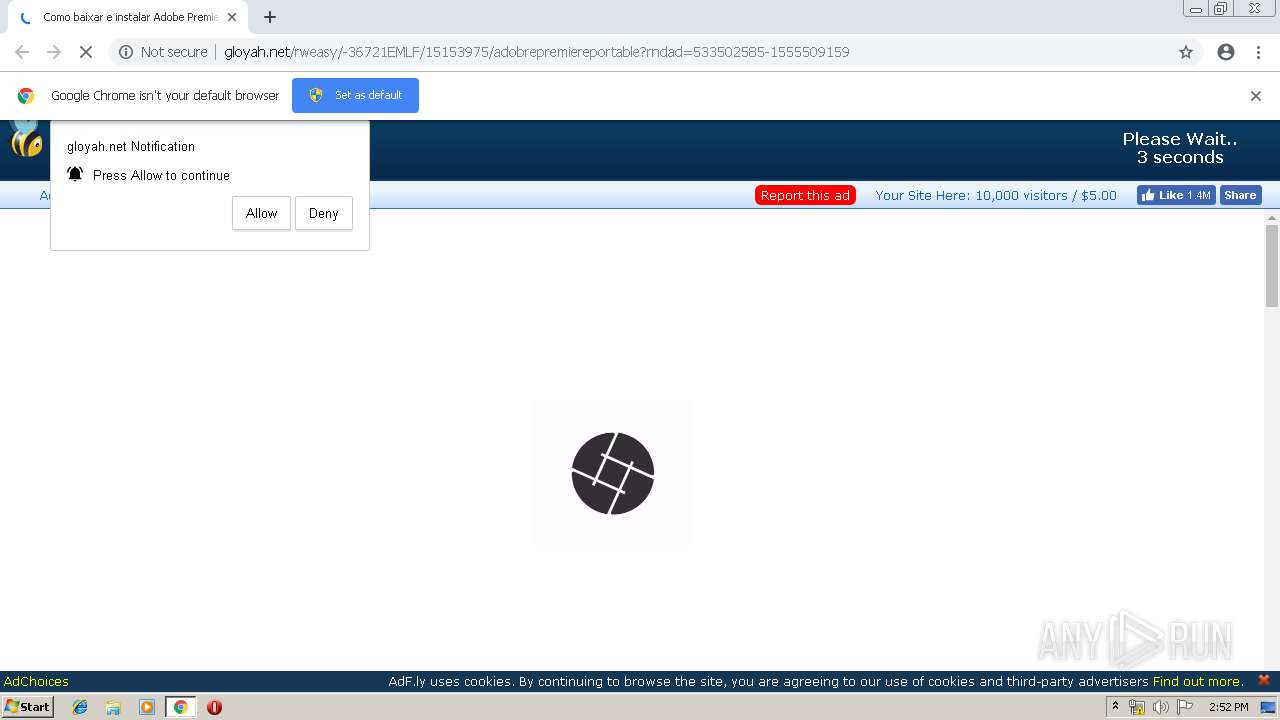
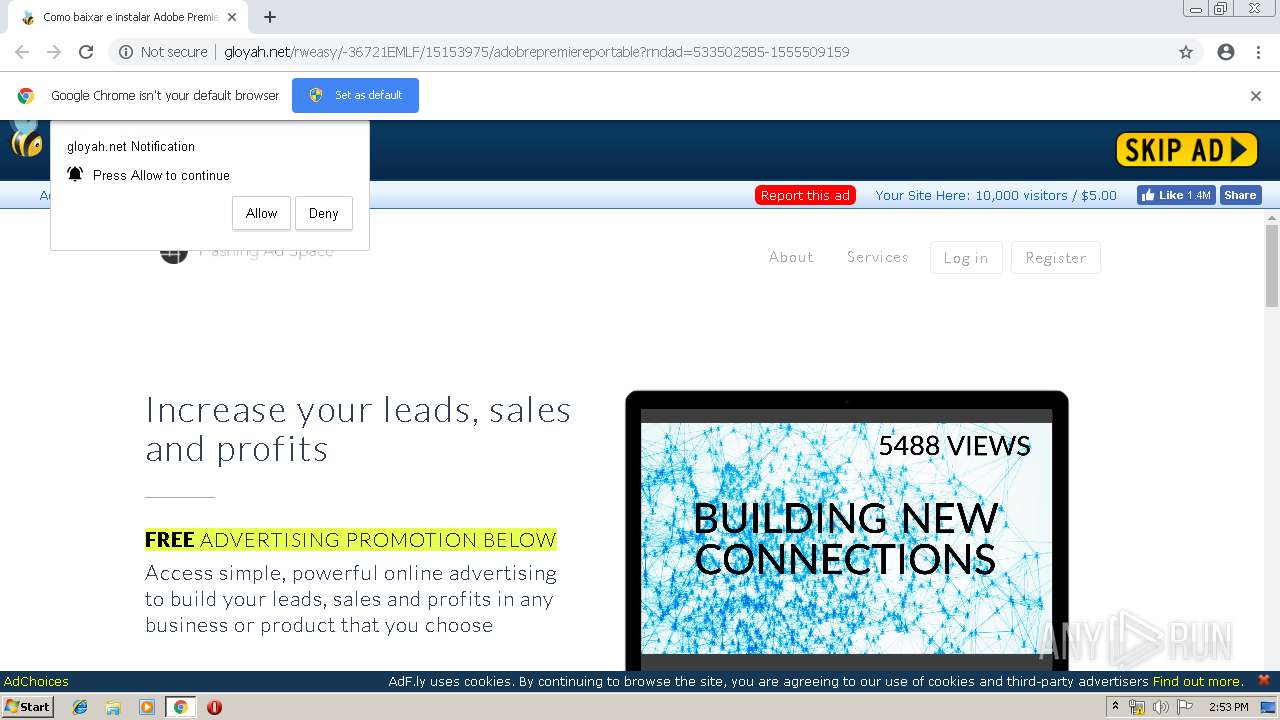
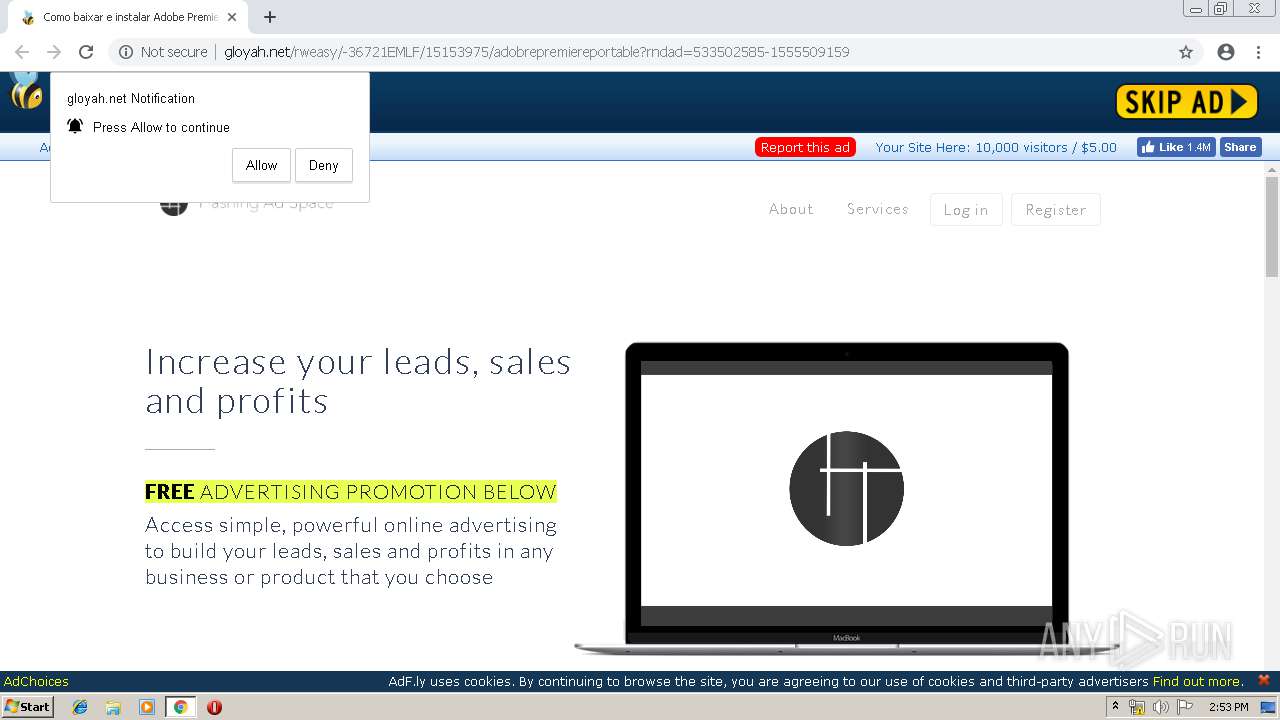
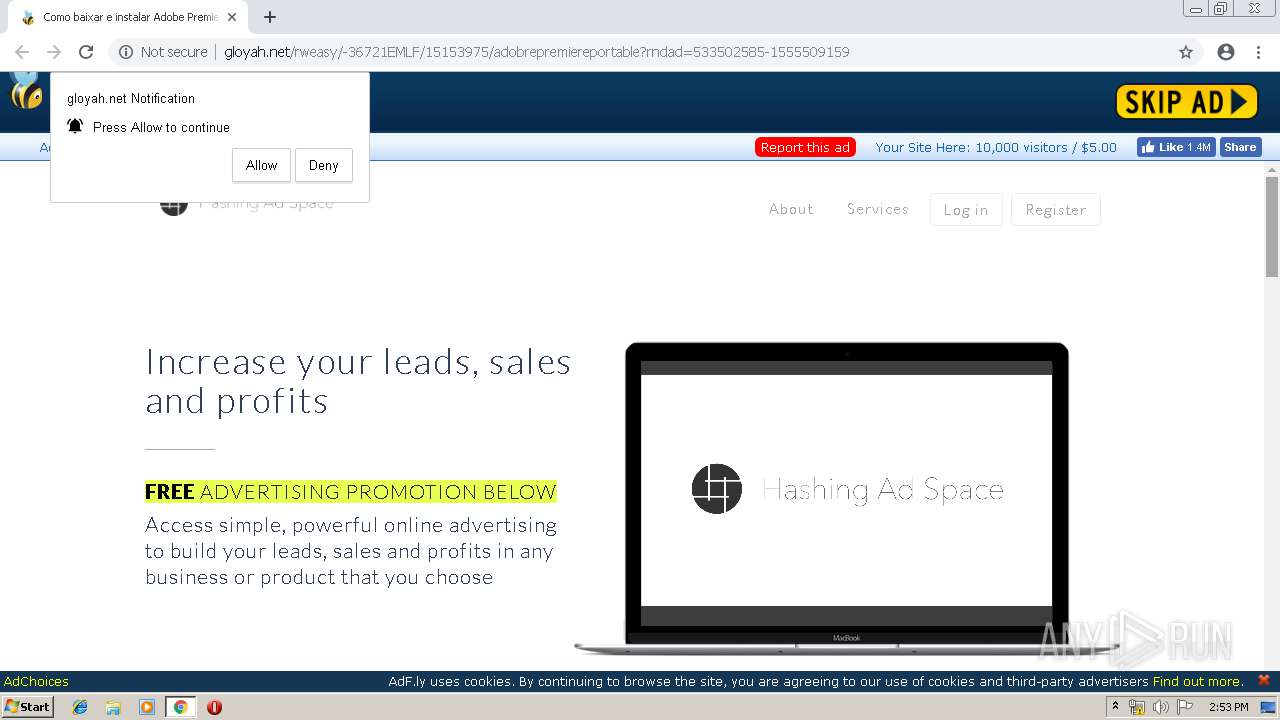
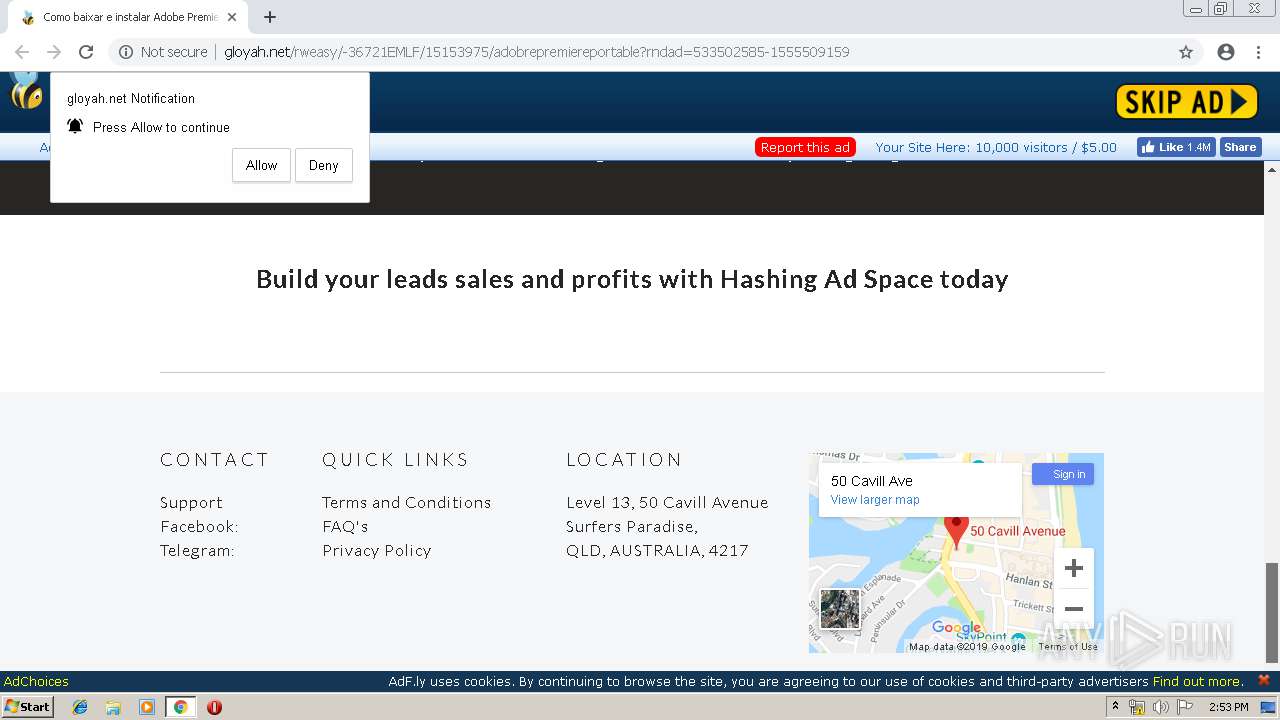
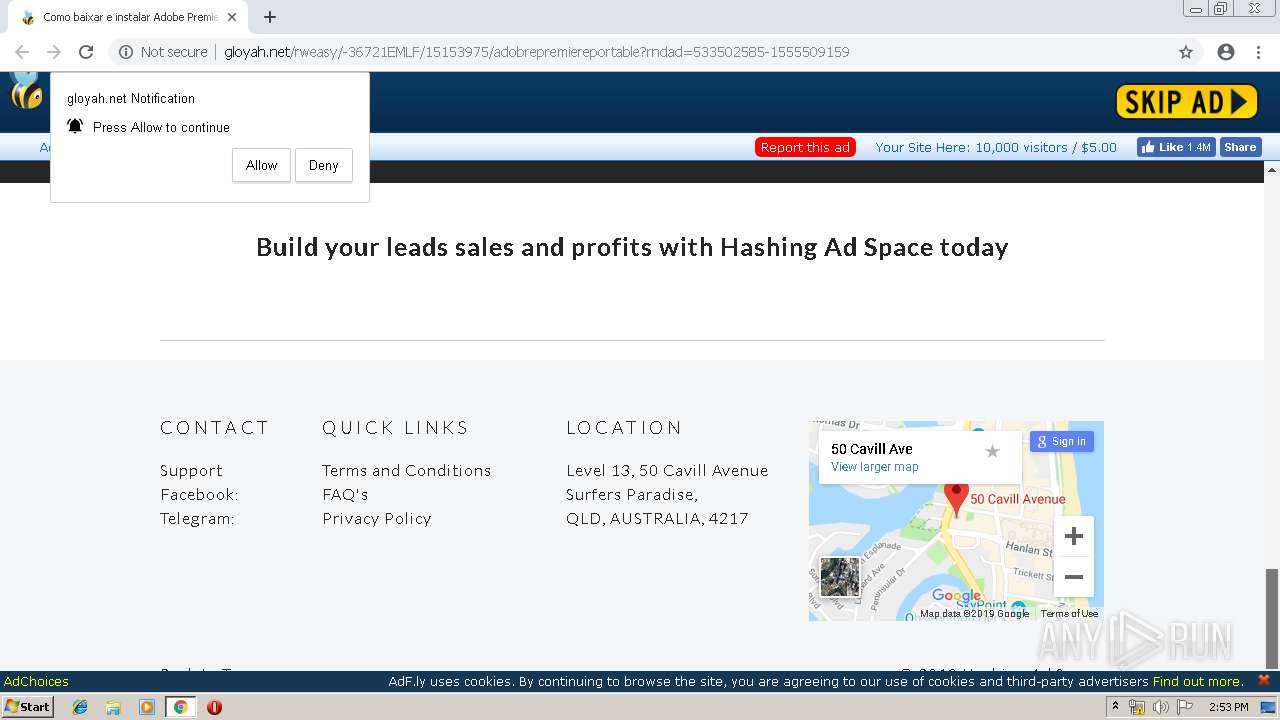
3828 | chrome.exe | GET | 200 | 172.64.170.14:80 | http://gloyah.net/rweasy/-36721EMLF/15153975/adobrepremiereportable?rndad=533502585-1555509159 | US | html | 5.88 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3828 | chrome.exe | 104.27.155.99:443 | zipansion.com | Cloudflare Inc | US | shared |
3828 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3828 | chrome.exe | 172.217.16.202:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 18.207.27.43:80 | enoughts.info | — | US | unknown |
3828 | chrome.exe | 13.32.222.7:80 | d1nmxiiewlx627.cloudfront.net | Amazon.com, Inc. | US | whitelisted |
3828 | chrome.exe | 13.32.219.97:80 | boudja.com | Amazon.com, Inc. | US | unknown |
3828 | chrome.exe | 34.225.238.53:80 | agreensdistra.info | Amazon.com, Inc. | US | unknown |
3828 | chrome.exe | 216.58.207.46:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
3828 | chrome.exe | 31.13.90.36:443 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
3828 | chrome.exe | 13.32.219.194:80 | leguinge.info | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
zipansion.com |
| malicious |
accounts.google.com |
| shared |
gloyah.net |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn.gloyah.net |
| suspicious |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
agreensdistra.info |
| unknown |
enoughts.info |
| unknown |
leguinge.info |
| whitelisted |