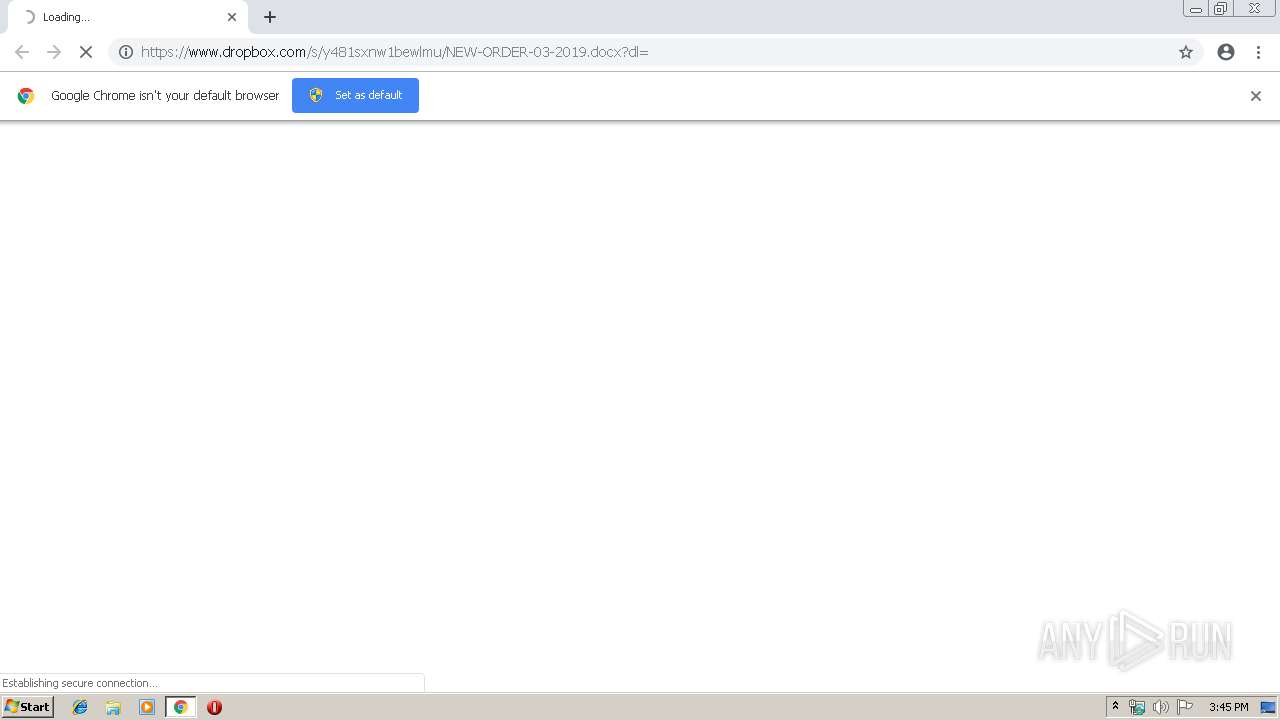
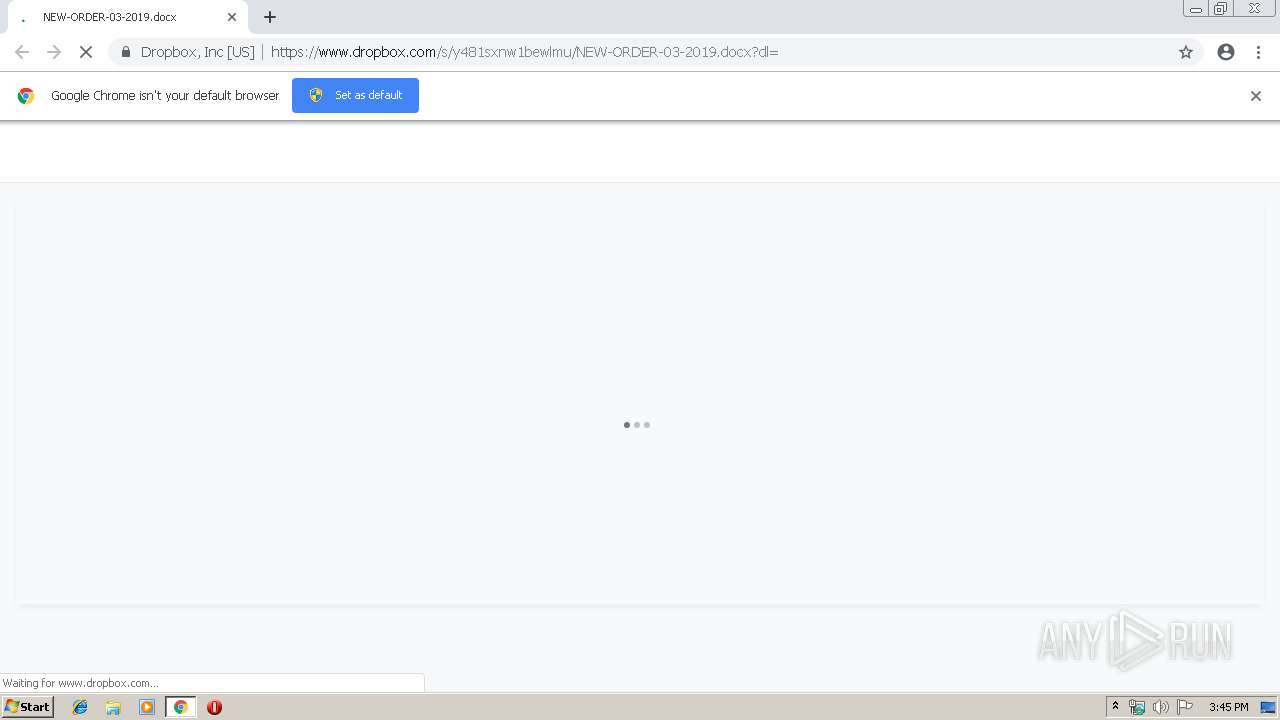
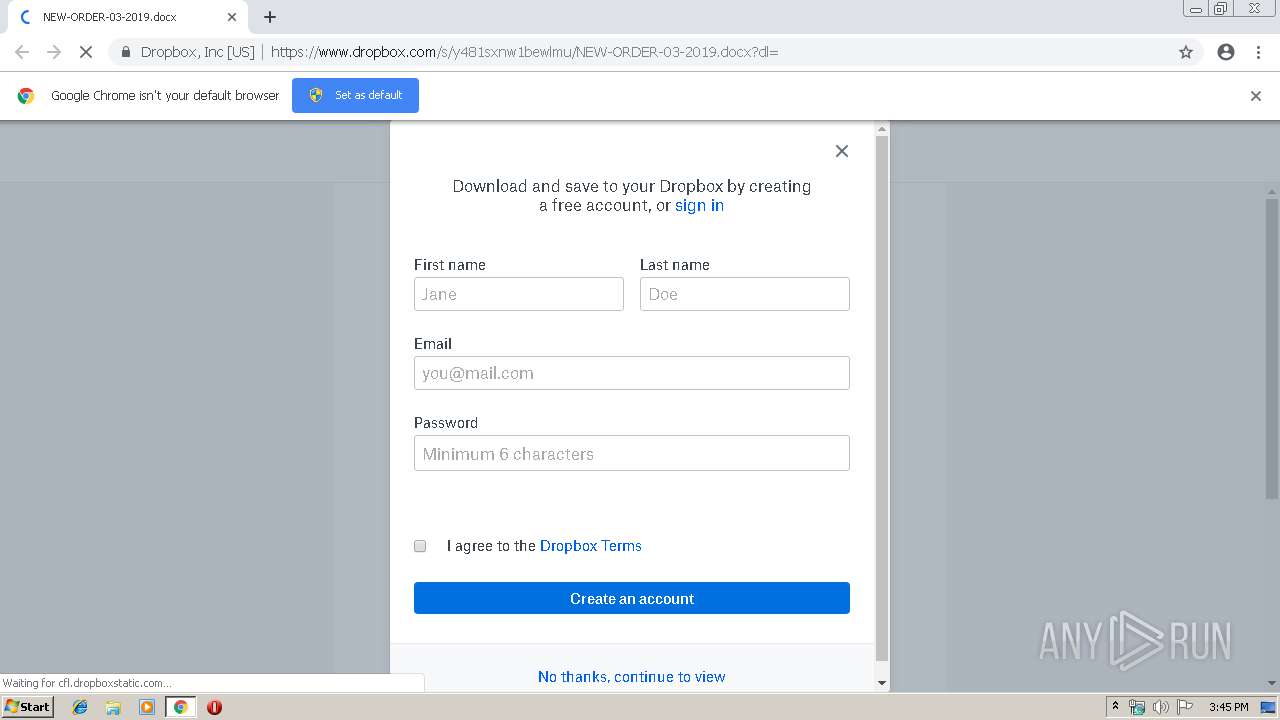
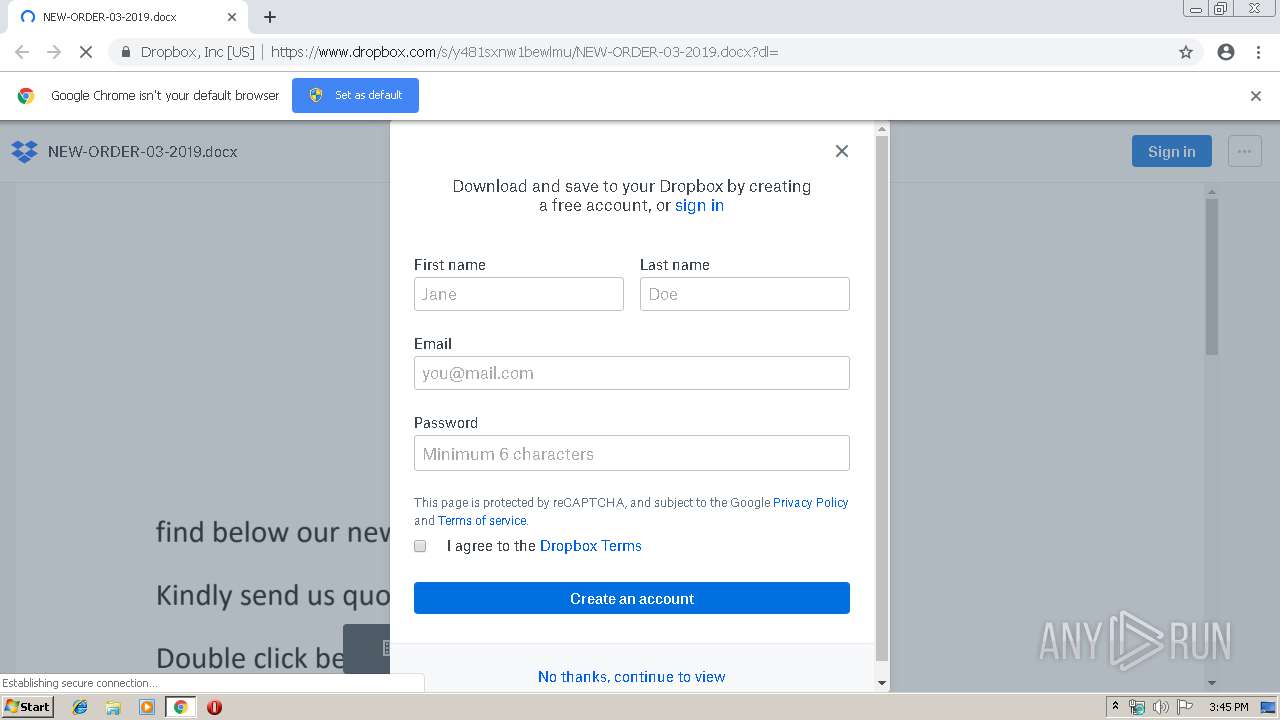
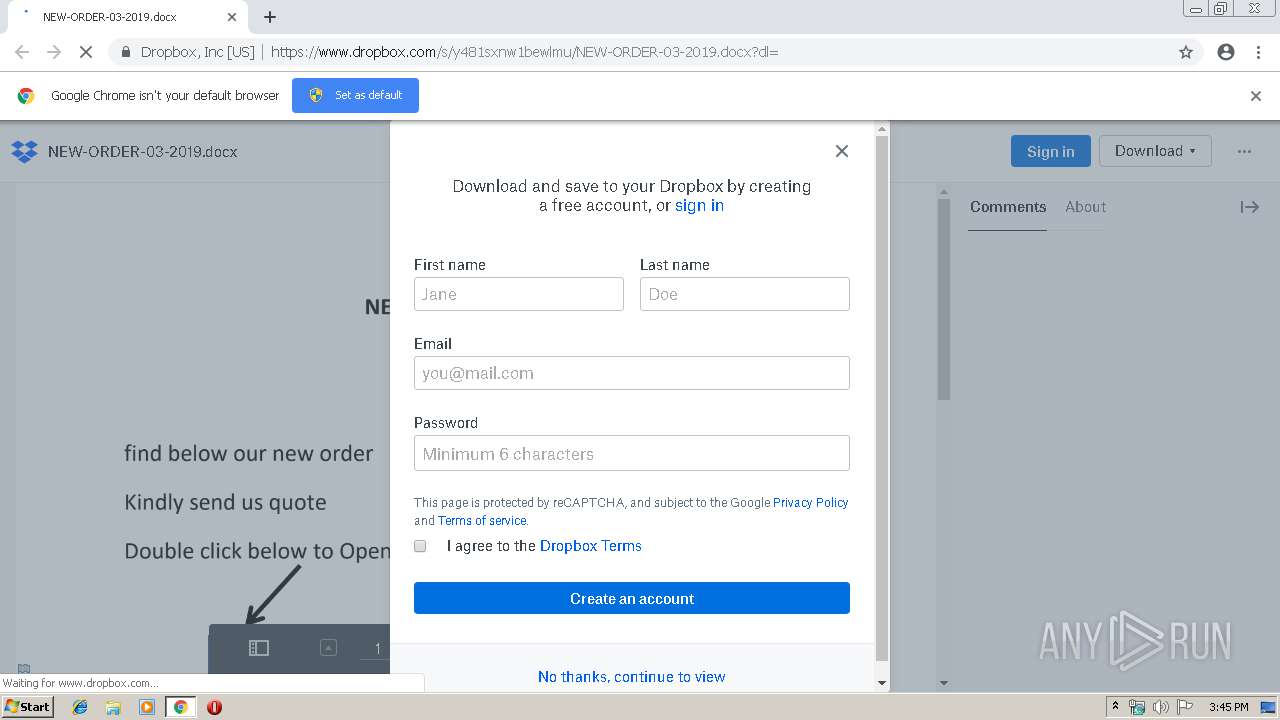
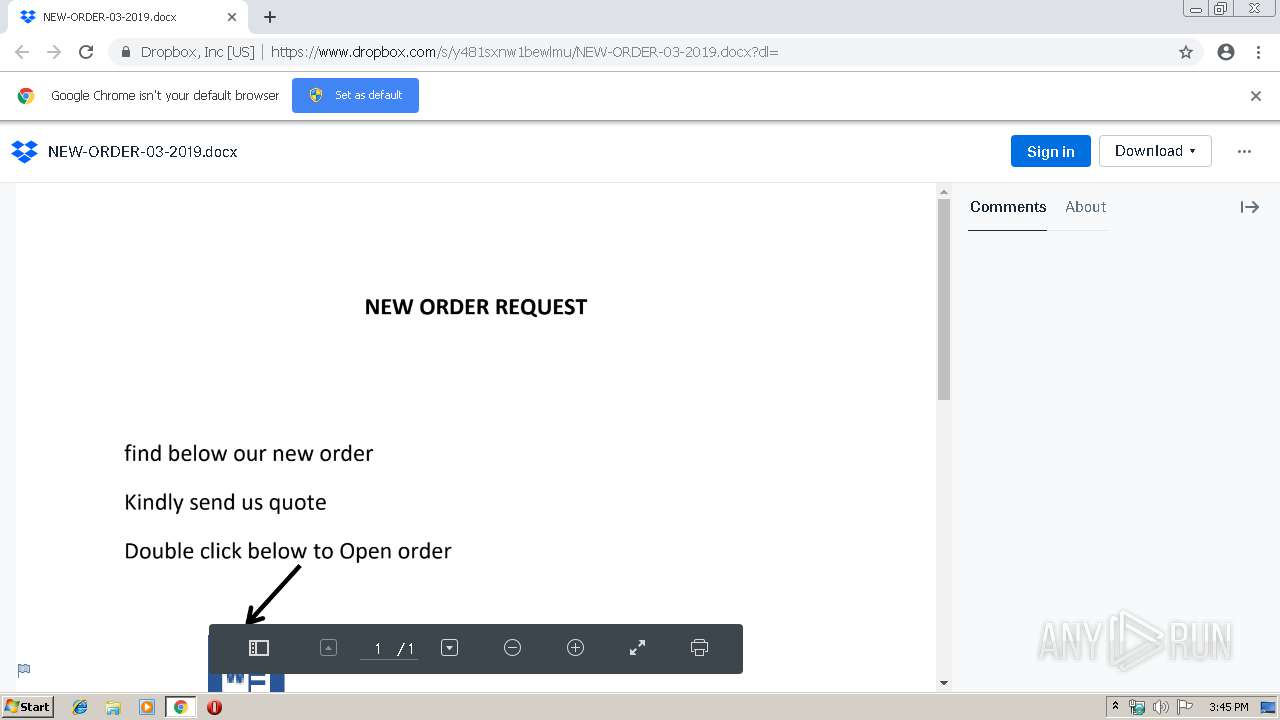
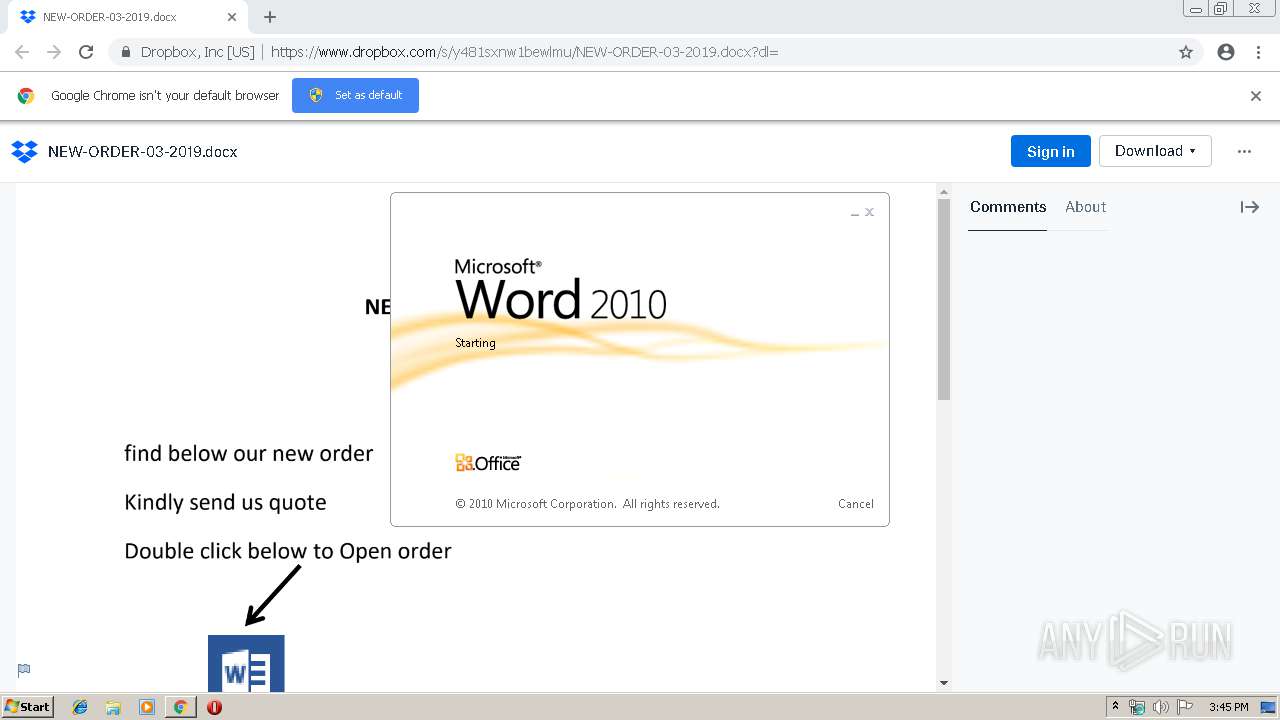
| URL: | https://www.dropbox.com/s/y481sxnw1bewlmu/NEW-ORDER-03-2019.docx?dl= |
| Full analysis: | https://app.any.run/tasks/268b561f-3e17-4ed0-b238-e5bd735d78ee |
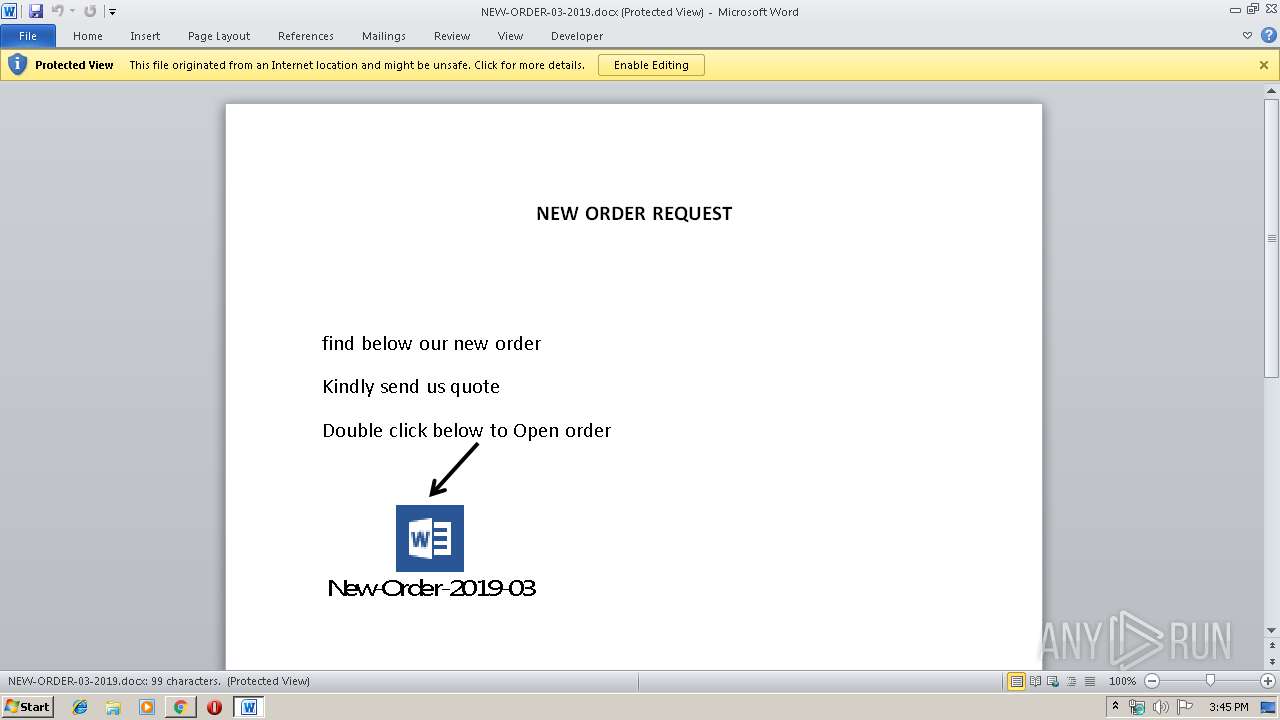
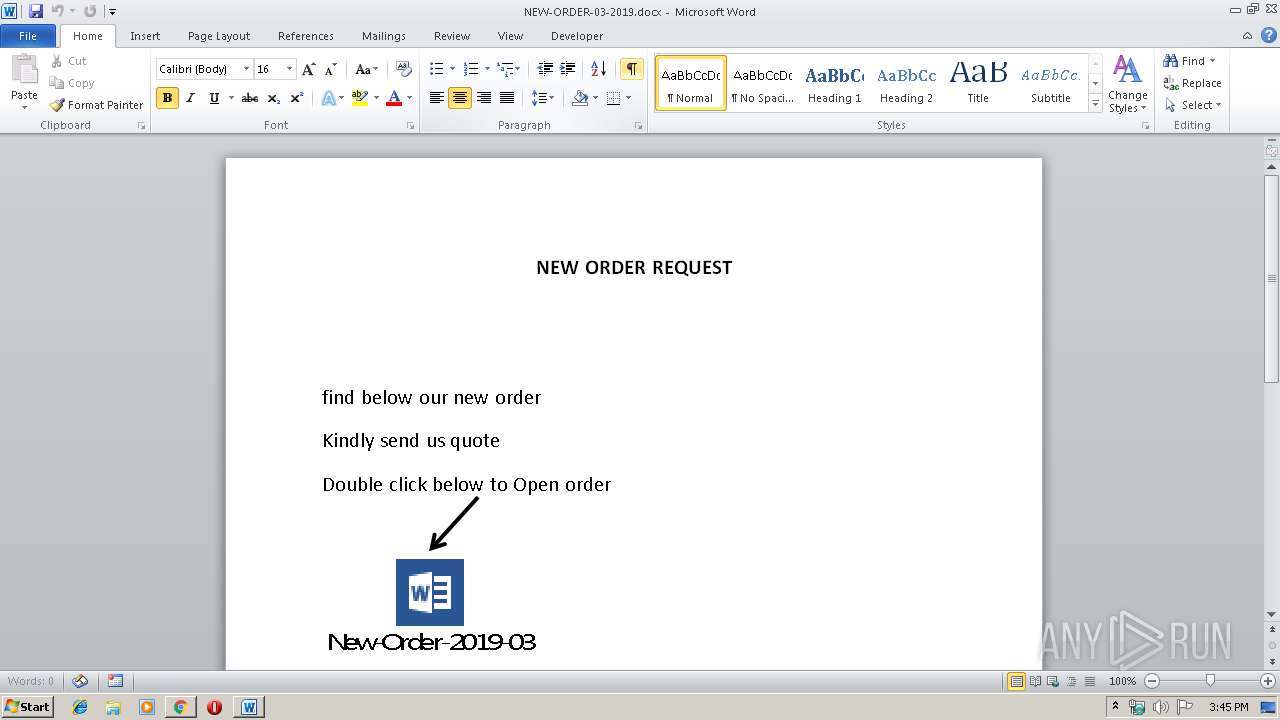
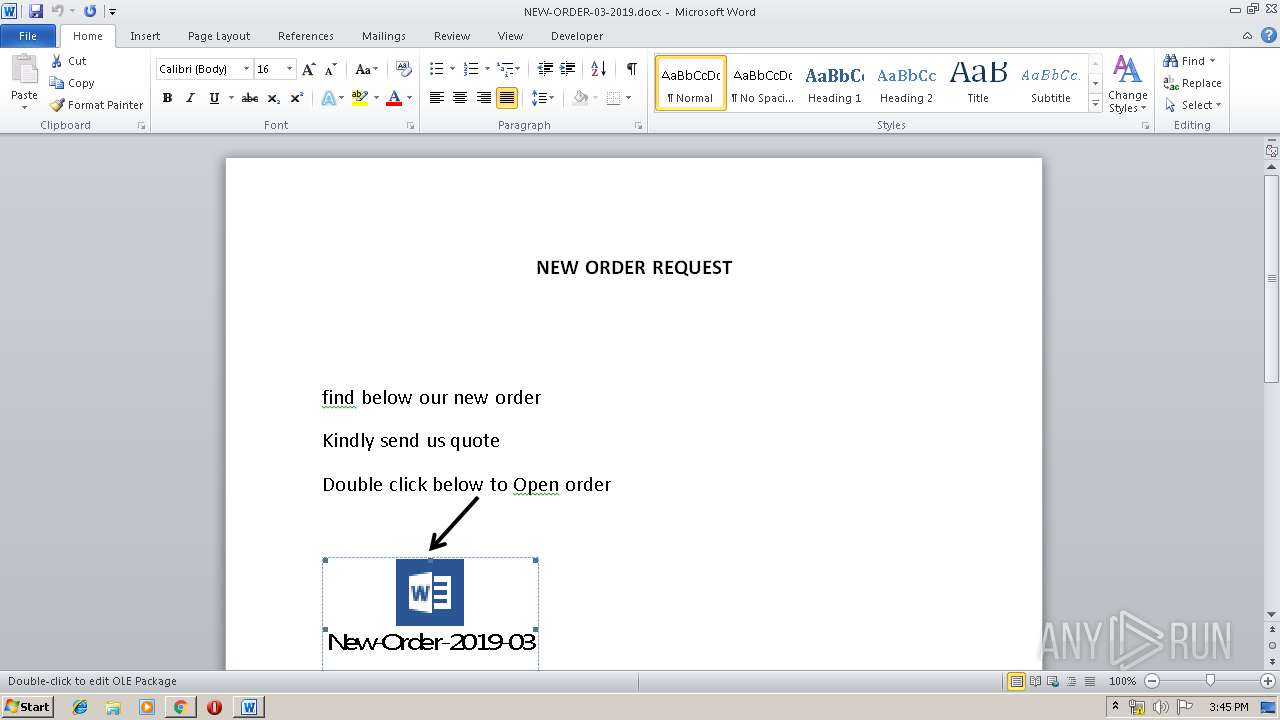
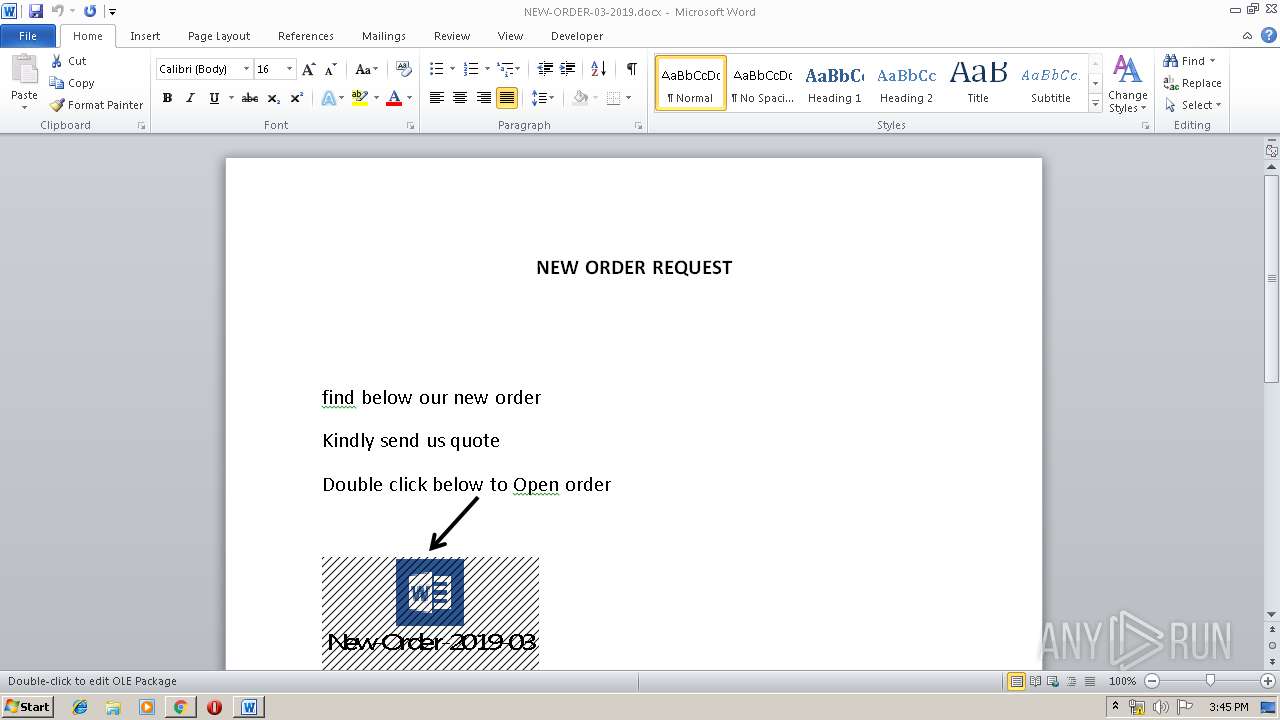
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2019, 15:44:34 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 7D85D8FD6958D849C11B7B9BCE11092E |
| SHA1: | 5ACA90D70A0157816CBB86DC57EE321FB048ECFD |
| SHA256: | 2B50A7EEEA9D4B695BC6D4D92081CDCE7DCE3DA82EC706A4295A88DCC93F6C60 |
| SSDEEP: | 3:N8DSLcVHGkhLSe5XhY/BKGdKJY:2OLHkdzqdoY |
MALICIOUS
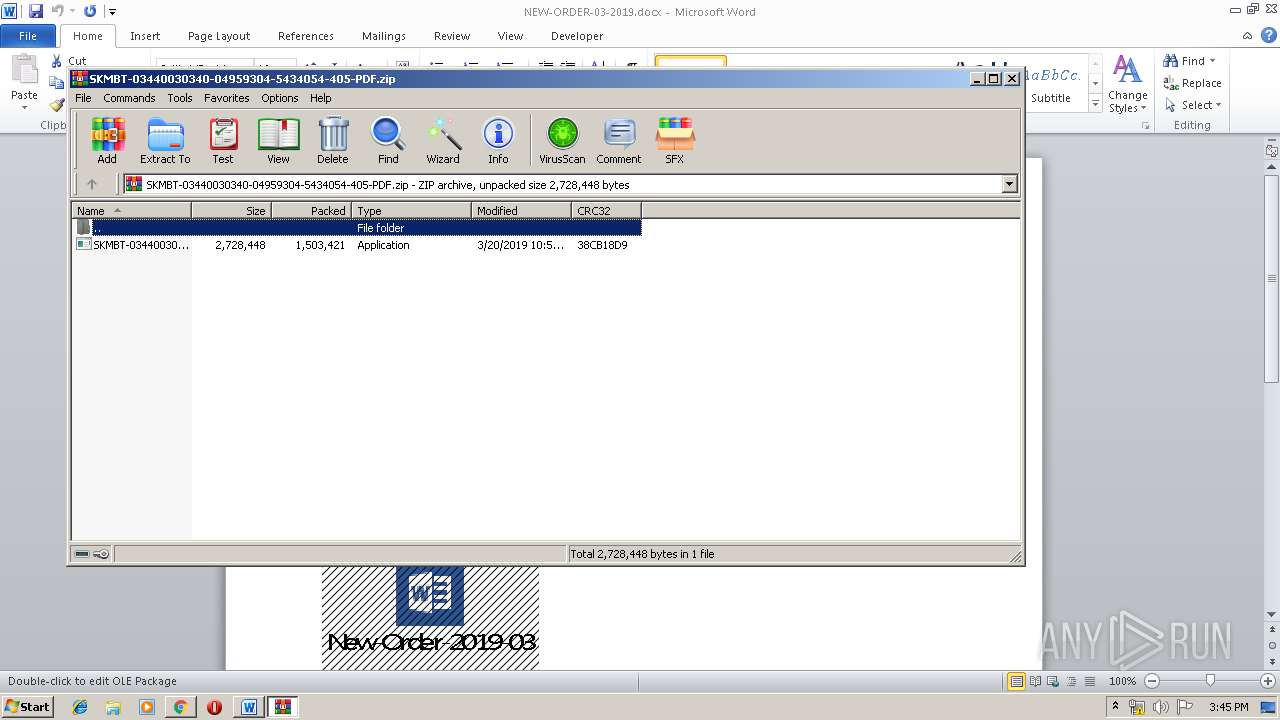
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3496)
Uses Task Scheduler to run other applications
- SKMBT-03440030340-04959304-5434054-405-PDF.exe (PID: 1456)
- DPTopologyApp.exe (PID: 2872)
- DPTopologyApp.exe (PID: 4008)
- DPTopologyApp.exe (PID: 3060)
- DPTopologyApp.exe (PID: 2596)
- DPTopologyApp.exe (PID: 2172)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2972)
- schtasks.exe (PID: 3748)
- schtasks.exe (PID: 1096)
- schtasks.exe (PID: 1436)
- schtasks.exe (PID: 2508)
- schtasks.exe (PID: 2524)
Application was dropped or rewritten from another process
- DPTopologyApp.exe (PID: 3060)
- DPTopologyApp.exe (PID: 4008)
- DPTopologyApp.exe (PID: 2172)
- DPTopologyApp.exe (PID: 2596)
- SKMBT-03440030340-04959304-5434054-405-PDF.exe (PID: 1456)
- DPTopologyApp.exe (PID: 2872)
SUSPICIOUS
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3496)
- chrome.exe (PID: 332)
Application launched itself
- WINWORD.EXE (PID: 3496)
Executable content was dropped or overwritten
- SKMBT-03440030340-04959304-5434054-405-PDF.exe (PID: 1456)
- WinRAR.exe (PID: 2708)
Modifies files in Chrome extension folder
- chrome.exe (PID: 332)
Uses RUNDLL32.EXE to load library
- RegAsm.exe (PID: 2080)
Creates files in the user directory
- RegAsm.exe (PID: 2080)
- rundll32.exe (PID: 3052)
Connects to unusual port
- RegAsm.exe (PID: 2080)
Reads Internet Cache Settings
- rundll32.exe (PID: 3052)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 2356)
Application launched itself
- chrome.exe (PID: 332)
Creates files in the user directory
- WINWORD.EXE (PID: 3496)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3496)
- WINWORD.EXE (PID: 2824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
80
Monitored processes
44
Malicious processes
2
Suspicious processes
8
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 240 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11855969432822756612 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11855969432822756612 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4308 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" https://www.dropbox.com/s/y481sxnw1bewlmu/NEW-ORDER-03-2019.docx?dl= | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 764 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | — | DPTopologyApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=964,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=6913385958461086250 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=6913385958461086250 --renderer-client-id=8 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3340 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1096 | "C:\Windows\System32\schtasks.exe" /create /tn printfilterpipelinesvc /tr "C:\Users\admin\AppData\Local\Temp\dwm\DPTopologyApp.exe" /sc minute /mo 1 /F | C:\Windows\System32\schtasks.exe | — | DPTopologyApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=964,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1881527828553289062 --mojo-platform-channel-handle=3952 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1436 | "C:\Windows\System32\schtasks.exe" /create /tn printfilterpipelinesvc /tr "C:\Users\admin\AppData\Local\Temp\dwm\DPTopologyApp.exe" /sc minute /mo 1 /F | C:\Windows\System32\schtasks.exe | — | DPTopologyApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Manages scheduled tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1456 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.15245\SKMBT-03440030340-04959304-5434054-405-PDF.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2708.15245\SKMBT-03440030340-04959304-5434054-405-PDF.exe | WinRAR.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1464 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\RegAsm.exe | — | DPTopologyApp.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Assembly Registration Utility Exit code: 0 Version: 2.0.50727.5420 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1500 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=964,10472020817386206667,17024858077240079286,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=11981614293396522363 --mojo-platform-channel-handle=2692 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
3 776
Read events
3 237
Write events
523
Delete events
16
Modification events
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2016) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 332-13197656713479625 |
Value: 259 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (332) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
2
Suspicious files
391
Text files
165
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\41cd6eff-7bbd-4f1a-b78a-e883069d075d.tmp | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
84
DNS requests
54
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2356 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEAx5qUSwjBGVIJJhX%2BJrHYM%3D | US | der | 471 b | whitelisted |
2356 | chrome.exe | GET | 302 | 172.217.23.142:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 502 b | whitelisted |
2356 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRJ9L2KGL92BpjF3kAtaDtxauTmhgQUPdNQpdagre7zSmAKZdMh1Pj41g8CEAU5fm3dSuY9dJCdoTinHgw%3D | US | der | 471 b | whitelisted |
2356 | chrome.exe | GET | 200 | 217.146.165.205:80 | http://r2---sn-oun-1gie.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=136.0.0.150&mm=28&mn=sn-oun-1gie&ms=nvh&mt=1553182862&mv=u&pl=20&shardbypass=yes | CH | crx | 842 Kb | whitelisted |
2356 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2356 | chrome.exe | 172.217.22.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 162.125.66.5:443 | uca51c85d73535f0bd362f633e79.previews.dropboxusercontent.com | Dropbox, Inc. | DE | shared |
2356 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 172.217.22.67:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2356 | chrome.exe | 162.125.66.1:443 | www.dropbox.com | Dropbox, Inc. | DE | shared |
2356 | chrome.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2356 | chrome.exe | 104.16.99.29:443 | cfl.dropboxstatic.com | Cloudflare Inc | US | shared |
2356 | chrome.exe | 162.125.248.1:443 | dropbox.com | Dropbox, Inc. | US | shared |
2356 | chrome.exe | 13.32.223.253:443 | marketing.dropbox.com | Amazon.com, Inc. | US | suspicious |
2356 | chrome.exe | 172.217.20.104:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.dropbox.com |
| shared |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.digicert.com |
| whitelisted |
uca51c85d73535f0bd362f633e79.previews.dropboxusercontent.com |
| unknown |
cfl.dropboxstatic.com |
| shared |
safebrowsing.googleapis.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
dropbox.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2356 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
2356 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY Dropbox.com Offsite File Backup in Use |
1072 | svchost.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup Domain (ipapi .co in DNS lookup) |