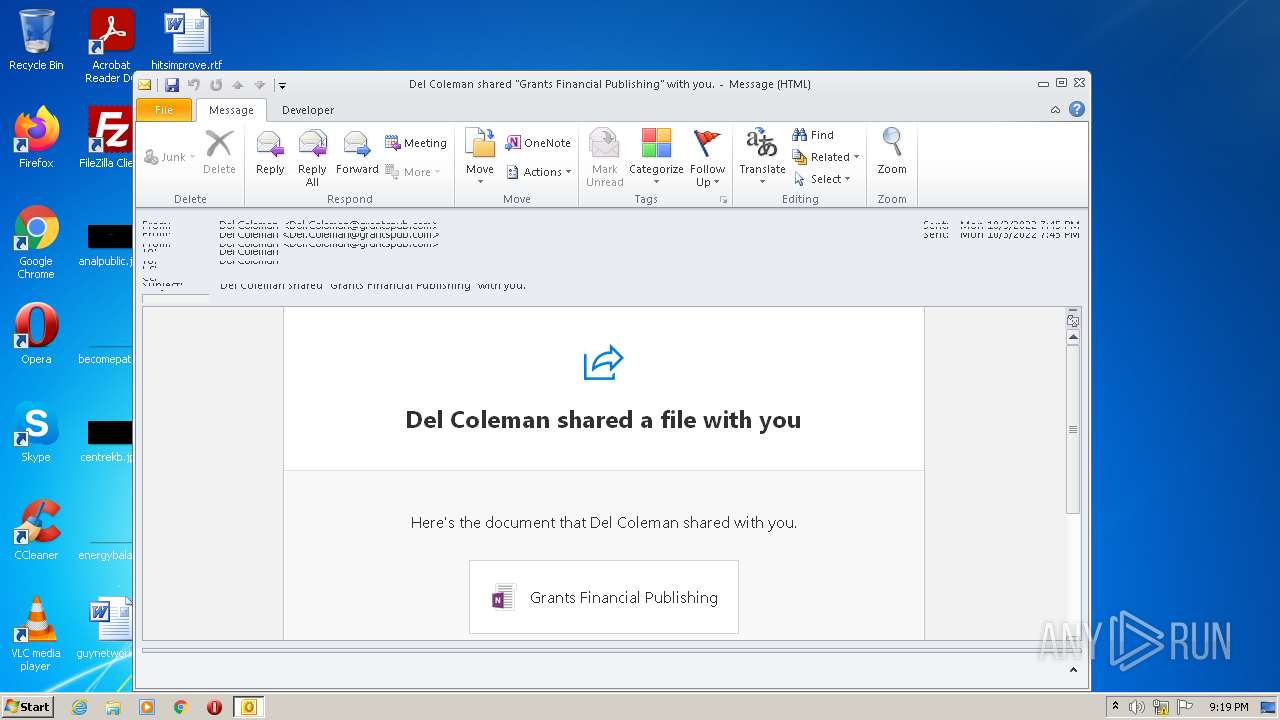
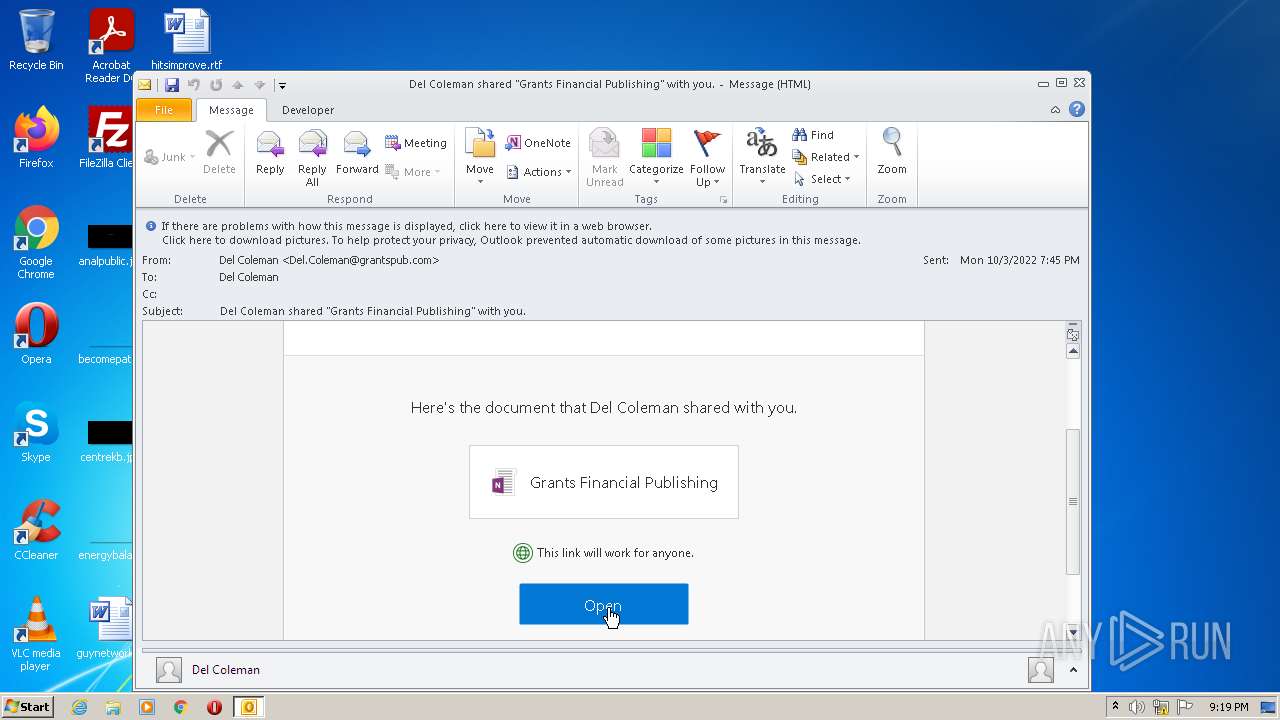
| File name: | Del Coleman shared Grants Financial Publishing with you.msg |
| Full analysis: | https://app.any.run/tasks/c80c75c3-c057-4feb-b80e-b134bd30177c |
| Verdict: | Malicious activity |
| Analysis date: | October 04, 2022, 20:18:57 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | E8C853147226C937967A467B7BABD259 |
| SHA1: | E85DD1AEEFE757D46B1BB68932A480A0485099DF |
| SHA256: | 2B502674D7DF2F4F19EFC1643AC21F2DFAA742552AB60EC1CFC6B19DB8F76318 |
| SSDEEP: | 1536:tcsUtzOxmhv6sWLWDM6GxNSiL+DRD0ii4TsUrq3DZpvjZsNM1:ZUtzYmhv3yGVdi4YUrqTZpvCNM1 |
MALICIOUS
Unusual execution from Microsoft Office
- OUTLOOK.EXE (PID: 3160)
SUSPICIOUS
Starts Internet Explorer
- OUTLOOK.EXE (PID: 3160)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3820)
INFO
Checks supported languages
- OUTLOOK.EXE (PID: 3160)
- iexplore.exe (PID: 3420)
- iexplore.exe (PID: 3820)
Searches for installed software
- OUTLOOK.EXE (PID: 3160)
Reads the computer name
- OUTLOOK.EXE (PID: 3160)
- iexplore.exe (PID: 3420)
- iexplore.exe (PID: 3820)
Application launched itself
- iexplore.exe (PID: 3420)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3160)
- iexplore.exe (PID: 3820)
Changes internet zones settings
- iexplore.exe (PID: 3420)
Reads settings of System Certificates
- iexplore.exe (PID: 3820)
- iexplore.exe (PID: 3420)
Checks Windows Trust Settings
- iexplore.exe (PID: 3420)
- iexplore.exe (PID: 3820)
Reads internet explorer settings
- iexplore.exe (PID: 3820)
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3160)
Reads the date of Windows installation
- iexplore.exe (PID: 3420)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (58.9) |
|---|---|---|
| .oft | | | Outlook Form Template (34.4) |
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
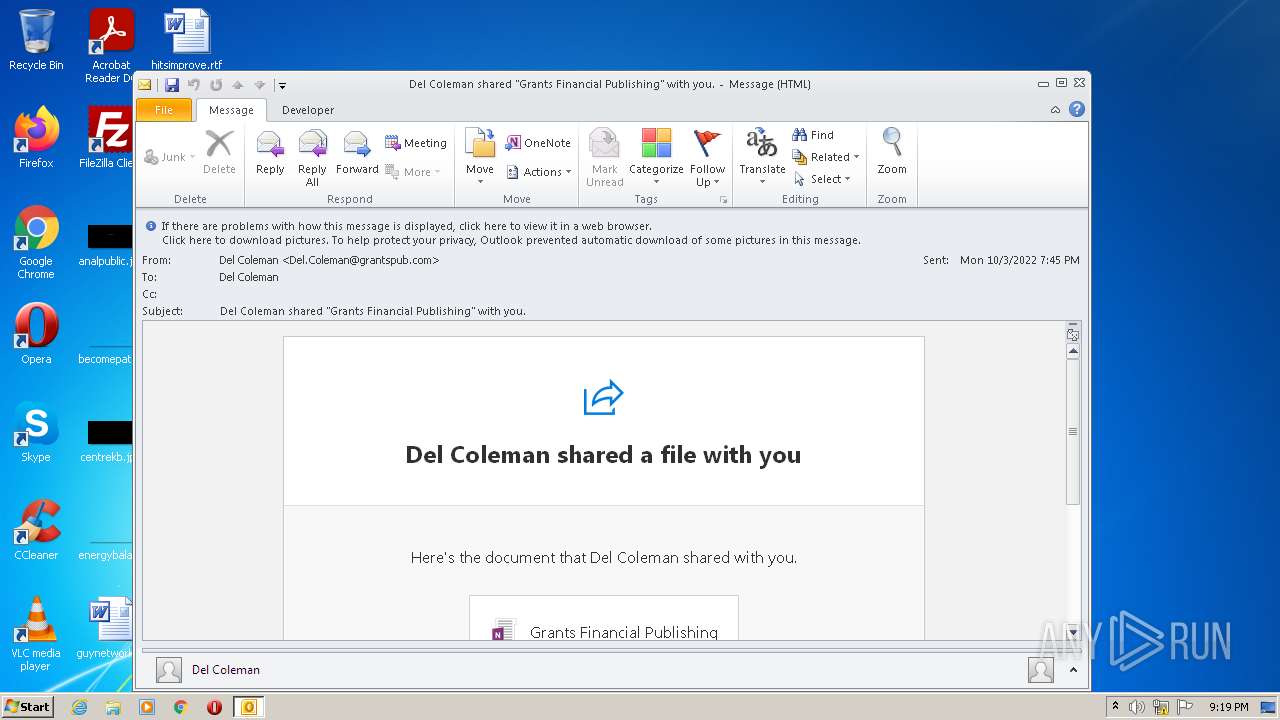
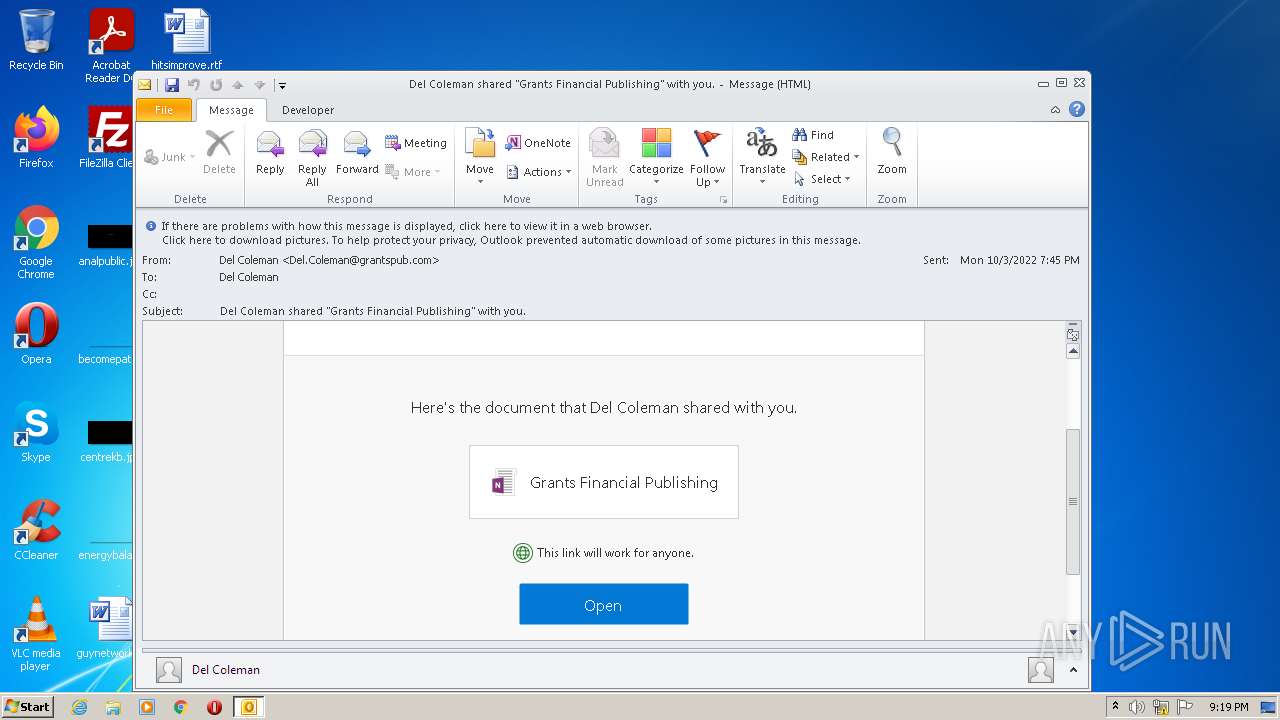
| 3160 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Del Coleman shared Grants Financial Publishing with you.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
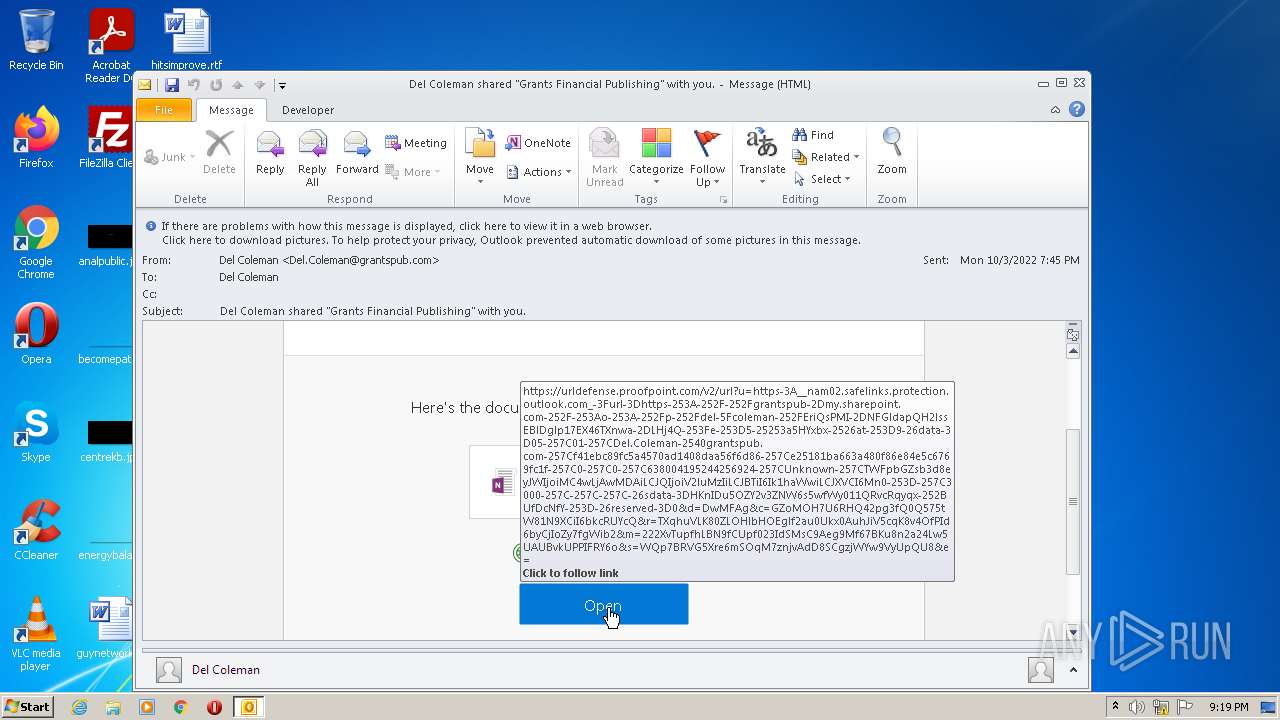
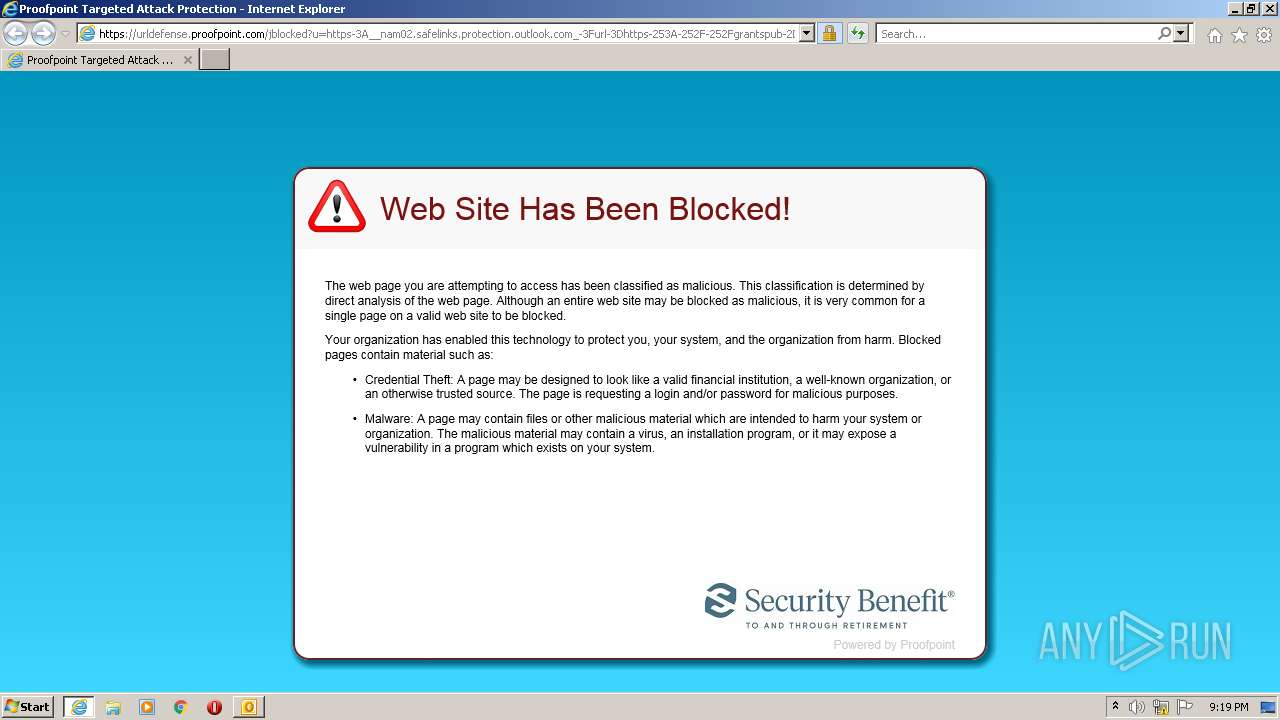
| 3420 | "C:\Program Files\Internet Explorer\iexplore.exe" https://urldefense.proofpoint.com/v2/url?u=https-3A__nam02.safelinks.protection.outlook.com_-3Furl-3Dhttps-253A-252F-252Fgrantspub-2Dmy.sharepoint.com-252F-253Ao-253A-252Fp-252Fdel-5Fcoleman-252FEriQsPMI-2DNFGldapQH2lssEBlDglp17EX46TXnwa-2DLHj4Q-253Fe-253D5-25253a5HYxbx-2526at-253D9-26data-3D05-257C01-257CDel.Coleman-2540grantspub.com-257Cf41ebc89fc5a4570ad1408daa56f6d86-257Ce25181ba663a480f86e84e5c6769fc1f-257C0-257C0-257C638004195244256924-257CUnknown-257CTWFpbGZsb3d8eyJWIjoiMC4wLjAwMDAiLCJQIjoiV2luMzIiLCJBTiI6Ik1haWwiLCJXVCI6Mn0-253D-257C3000-257C-257C-257C-26sdata-3DHKnIDu5OZY2v3ZNW6s5wfWy011QRvcRqyqx-252BUfDcNfY-253D-26reserved-3D0&d=DwMFAg&c=GZoMOH7U6RHQ42pg3fQ0Q575tW81N9XCiI6bkcRUYcQ&r=TXqhuVLK80ZLOHlbHOEglf2au0Ukx0AuhJiV5cqK8v4OfPId6byCjIoZy7fgWib2&m=222XvTupfhLBN9fCUpf023IdSMsC9Aeg9Mf67BKu8n2a24Lw5UAUBvkUPPIFRY6o&s=WQp7BRVG5Xre6mSOqM7znjvAdD8SCgzjWYw9VyUpQU8&e= | C:\Program Files\Internet Explorer\iexplore.exe | OUTLOOK.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3820 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3420 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
16 360
Read events
15 671
Write events
669
Delete events
20
Modification events
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3160) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
0
Suspicious files
9
Text files
21
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRE135.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3420 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\mapisvc.inf | text | |
MD5:F3B25701FE362EC84616A93A45CE9998 | SHA256:B3D510EF04275CA8E698E5B3CBB0ECE3949EF9252F0CDC839E9EE347409A2209 | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\6DE5008B.dat | image | |
MD5:778A1154ABC8197D7400570AFC1DE067 | SHA256:872B38DE556D3505248BA0D19A9F23DB7B359A8151DD460F30ECAFC1AAAF088B | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_AvailabilityOptions_2_3228B2779E112E45860BCCBC40D076AB.dat | xml | |
MD5:EEAA832C12F20DE6AAAA9C7B77626E72 | SHA256:C4C9A90F2C961D9EE79CF08FBEE647ED7DE0202288E876C7BAAD00F4CA29CA16 | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_Calendar_2_77F5FF9B31F37746A6DD9483C18CB2D6.dat | xml | |
MD5:B21ED3BD946332FF6EBC41A87776C6BB | SHA256:B1AAC4E817CD10670B785EF8E5523C4A883F44138E50486987DC73054A46F6F4 | |||
| 3420 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_1DC6D7385EA816C957BA2B715AC5C442 | der | |
MD5:— | SHA256:— | |||
| 3160 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Outlook\RoamCache\Stream_WorkHours_1_7F6EA80502549840AC0B30996F4ECCBF.dat | xml | |
MD5:807EF0FC900FEB3DA82927990083D6E7 | SHA256:4411E7DC978011222764943081500FFF0E43CBF7CCD44264BD1AB6306CA68913 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
11
DNS requests
10
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3160 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3420 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
3820 | iexplore.exe | GET | 200 | 104.18.32.68:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | US | der | 1.42 Kb | whitelisted |
3820 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQh80WaEMqmyEvaHjlisSfVM4p8SAQUF9nWJSdn%2BTHCSUPZMDZEjGypT%2BsCEByrgD5piqUjHxqAhX8eRyo%3D | US | der | 471 b | whitelisted |
3420 | iexplore.exe | GET | 200 | 8.253.95.121:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?87bd767e3a157c33 | US | compressed | 4.70 Kb | whitelisted |
3820 | iexplore.exe | GET | 200 | 172.64.155.188:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEBN9U5yqfDGppDNwGWiEeo0%3D | US | der | 2.18 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3160 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3420 | iexplore.exe | 131.253.33.200:443 | www.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3820 | iexplore.exe | 67.231.146.66:443 | urldefense.proofpoint.com | PROOFPOINT-ASN-US-WEST | US | suspicious |
3420 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | EDGECAST | GB | whitelisted |
3820 | iexplore.exe | 104.18.32.68:80 | ocsp.comodoca.com | CLOUDFLARENET | — | suspicious |
3420 | iexplore.exe | 8.253.95.121:80 | ctldl.windowsupdate.com | LEVEL3 | US | suspicious |
3820 | iexplore.exe | 172.64.155.188:80 | ocsp.comodoca.com | CLOUDFLARENET | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
urldefense.proofpoint.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ocsp.comodoca.com |
| whitelisted |
ocsp.usertrust.com |
| whitelisted |
ocsp.sectigo.com |
| whitelisted |