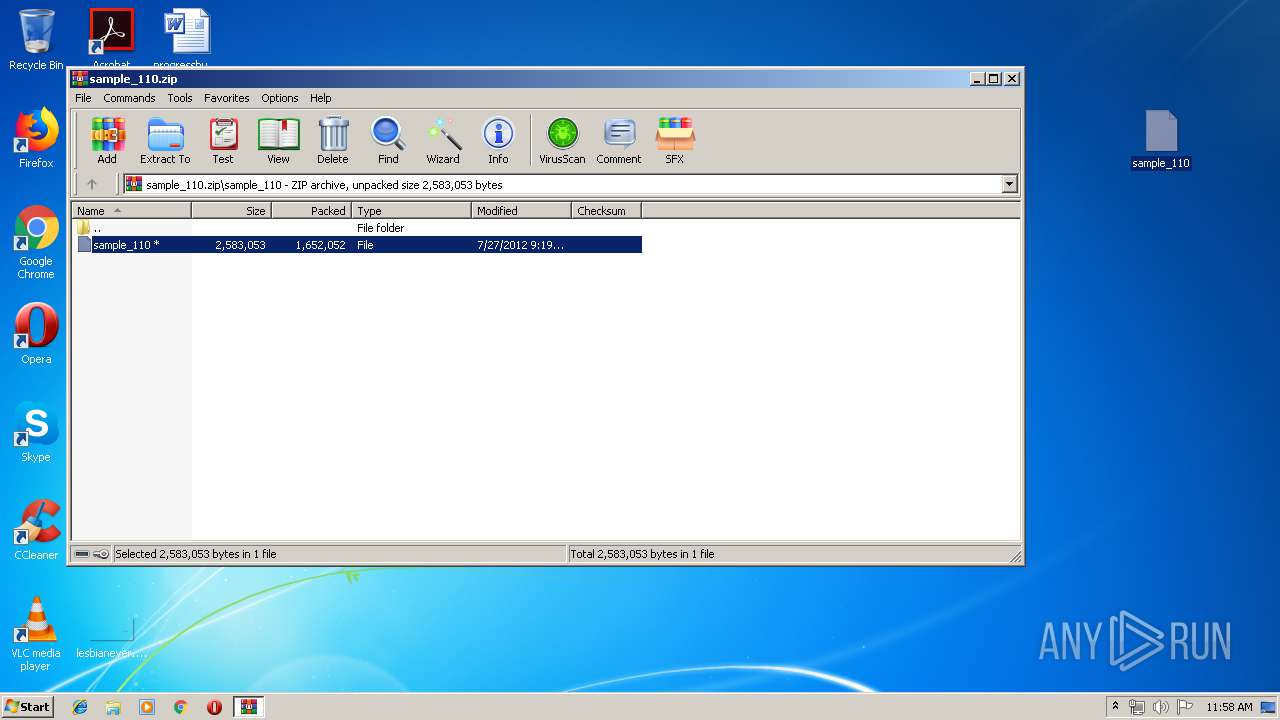
| File name: | sample_110.zip |
| Full analysis: | https://app.any.run/tasks/fb6b679f-8ef6-44e6-a7cd-1cc26135a20c |
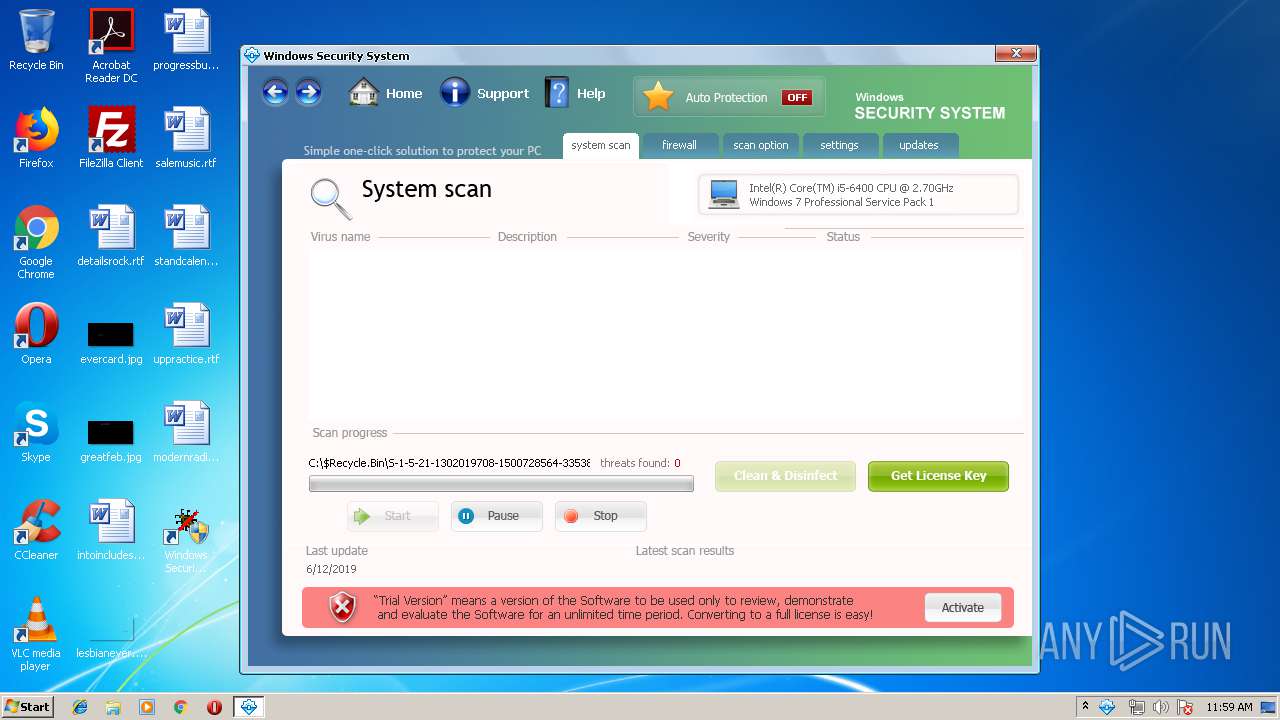
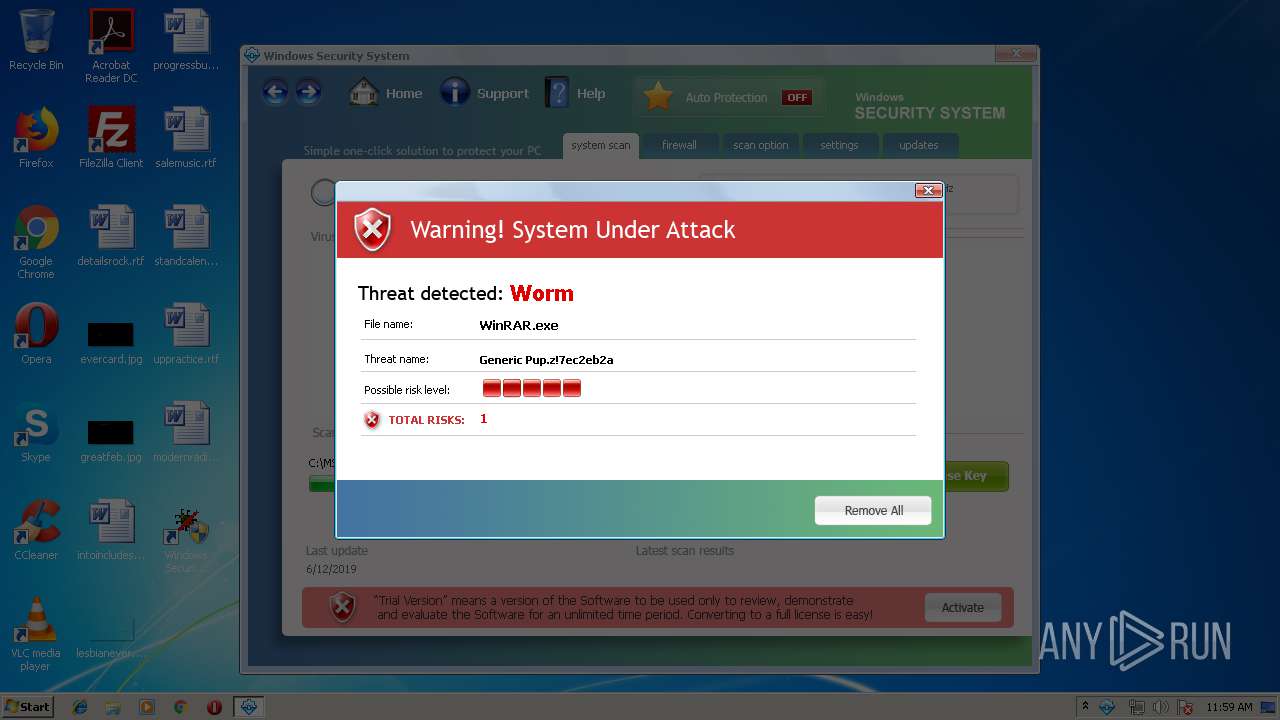
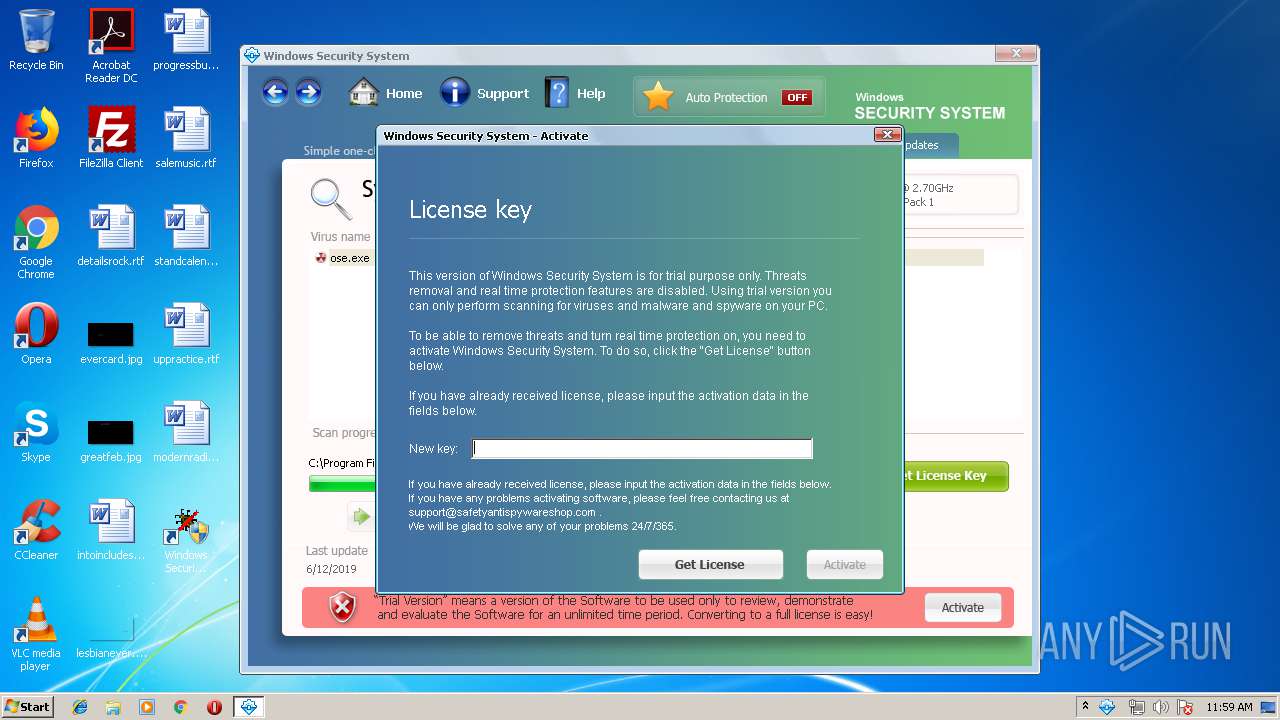
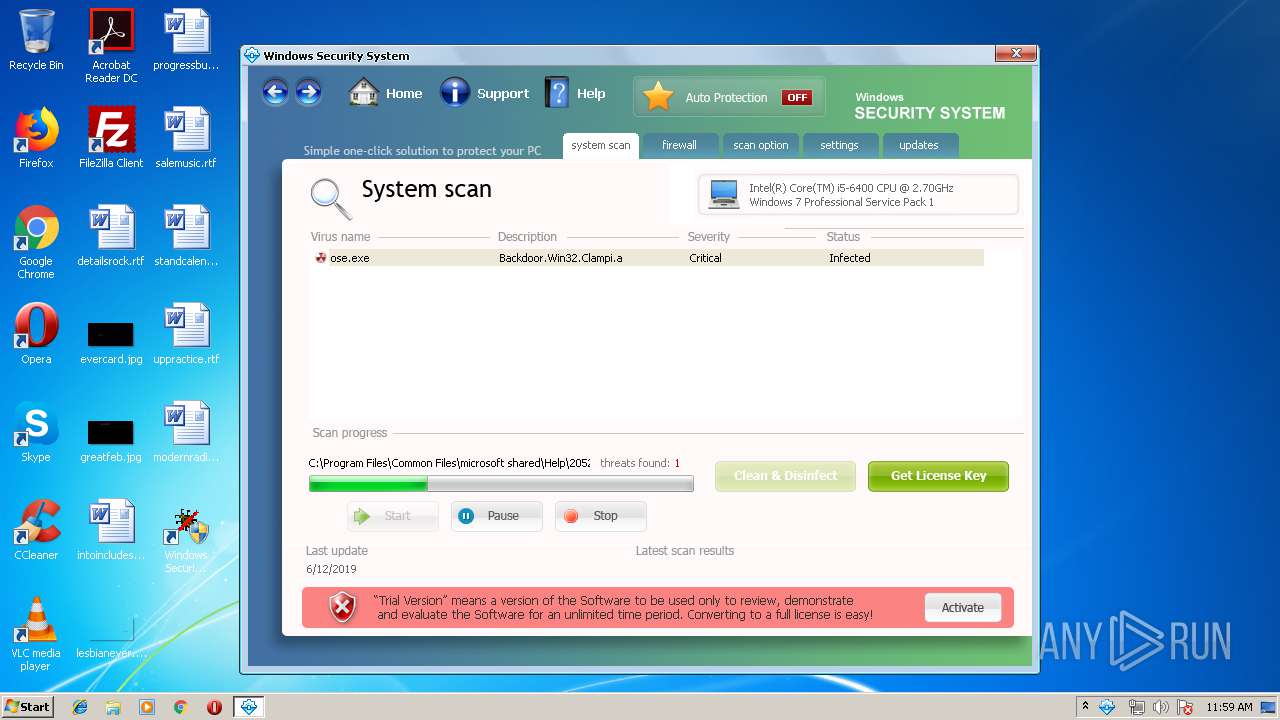
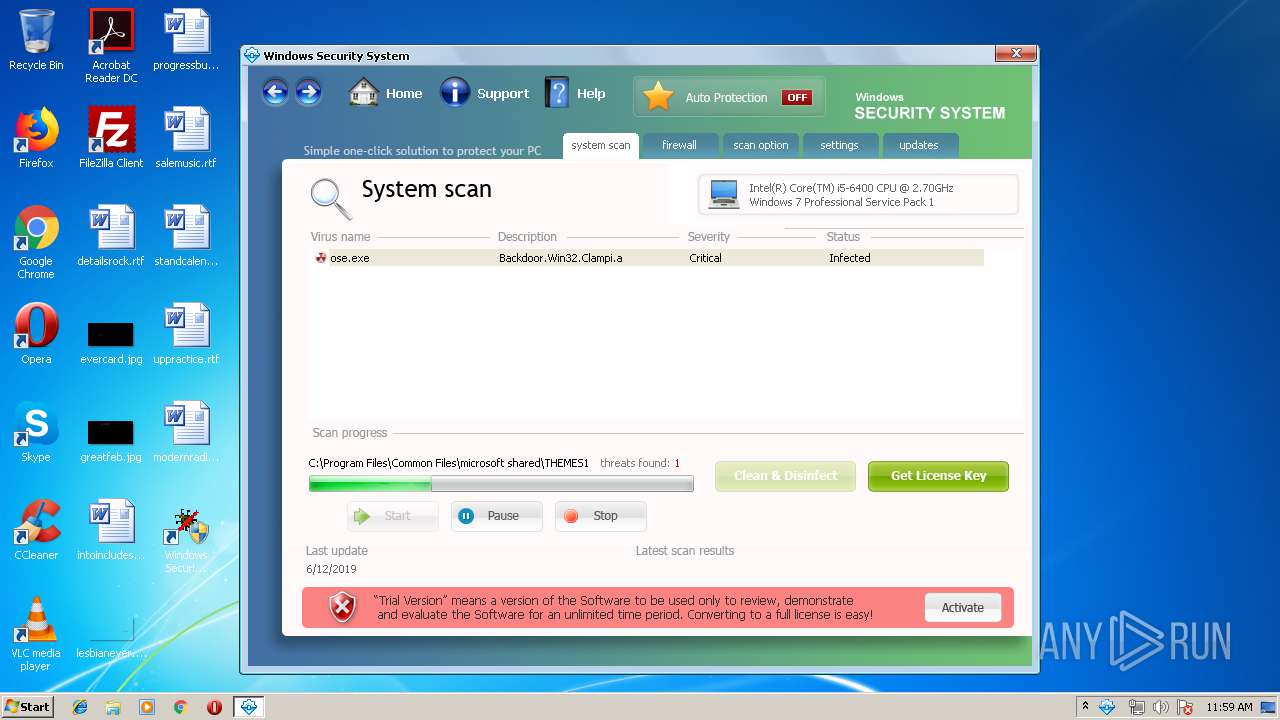
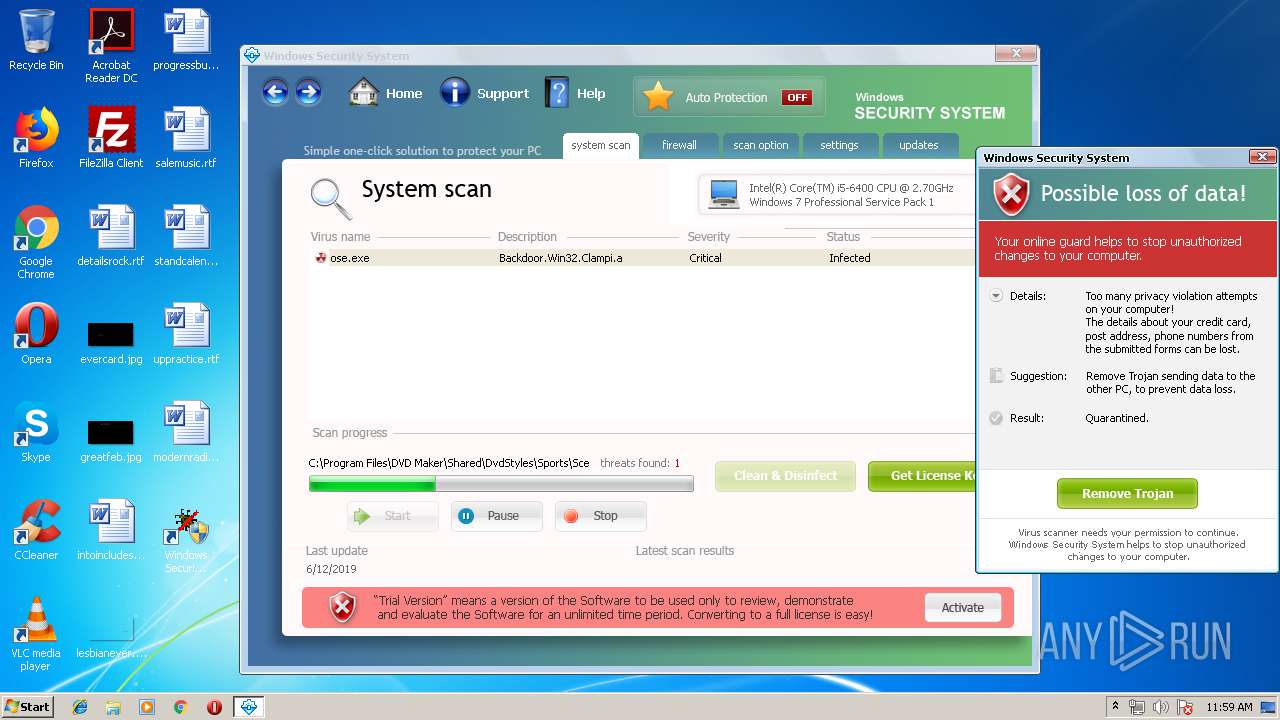
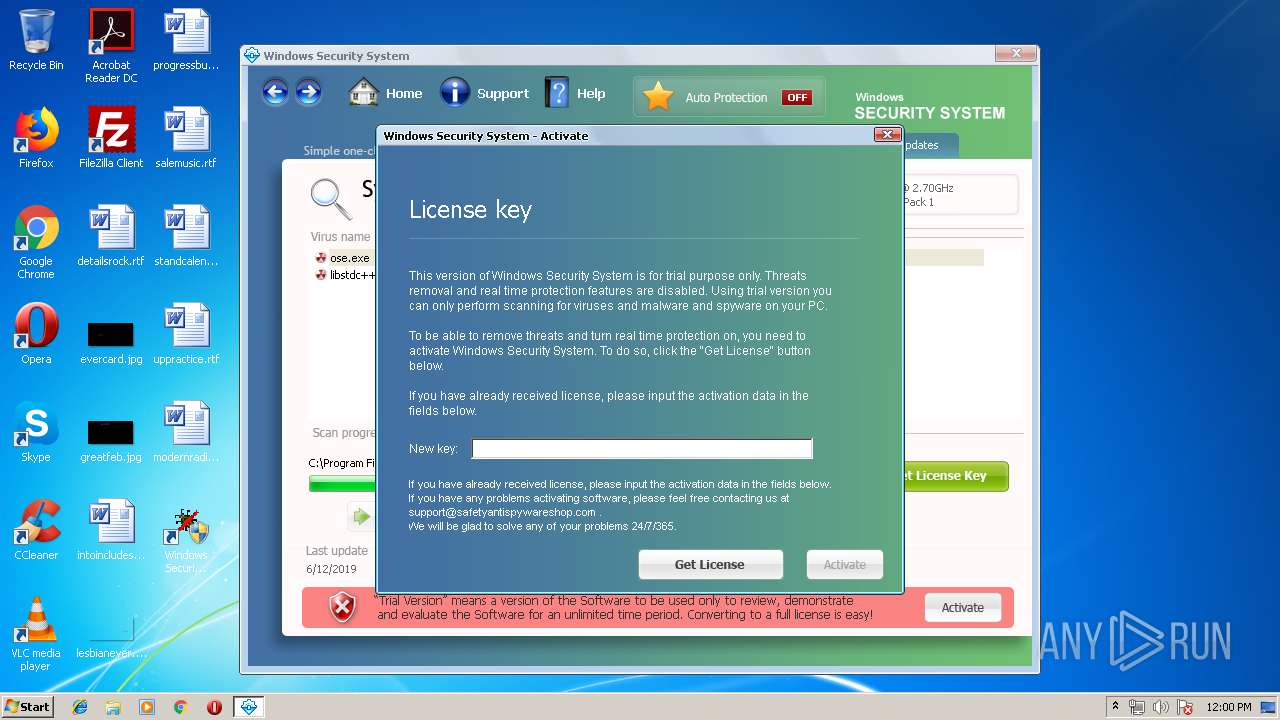
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 10:58:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | A089F75C43A874EEAD67DC041CDE9B07 |
| SHA1: | 291A2C1FBB58A8C93AF19300B9AE075F07216AF4 |
| SHA256: | 2B4E3E146059FC9BC347E41EEE60472985F6FB6B064B2AB1DA5DF637CD60E725 |
| SSDEEP: | 24576:b8FpErVT10BGkWinp9g7brLLieW+pzAo+OnAfafsUset06fDg5to1aaf6bKhvzQT:bYp810Aklp6bLvObOWkfN0W1LisIr |
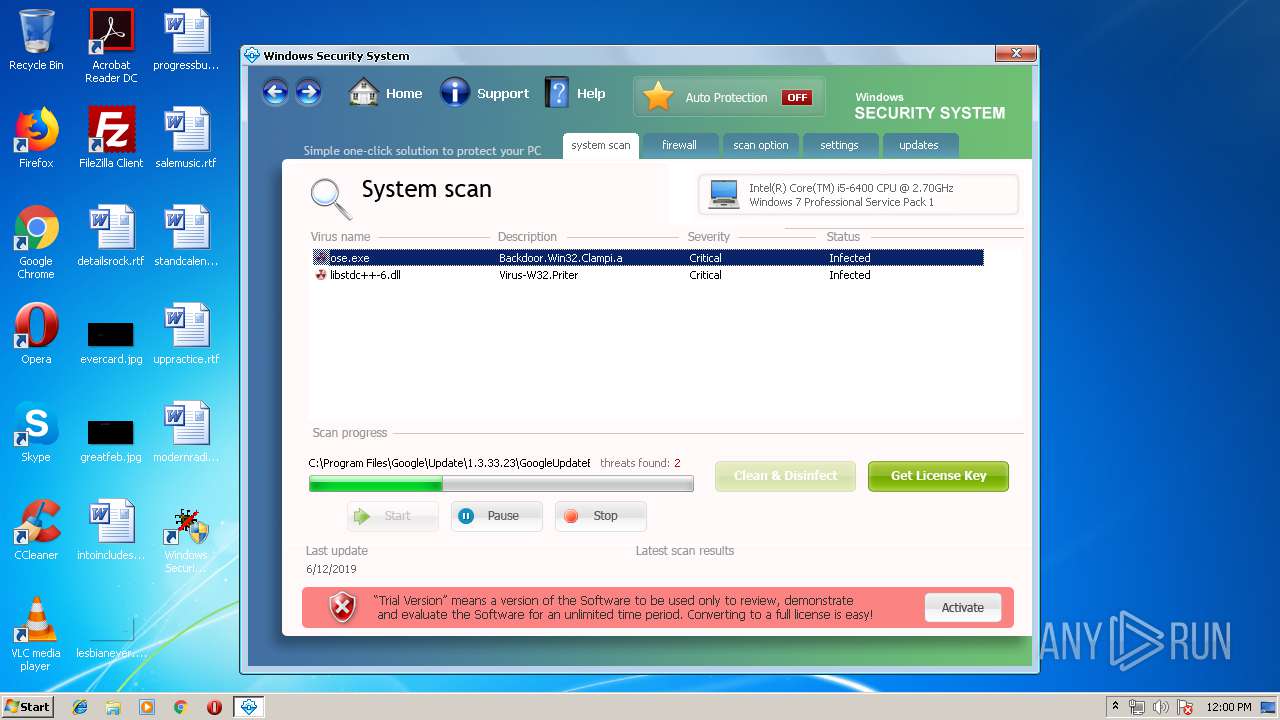
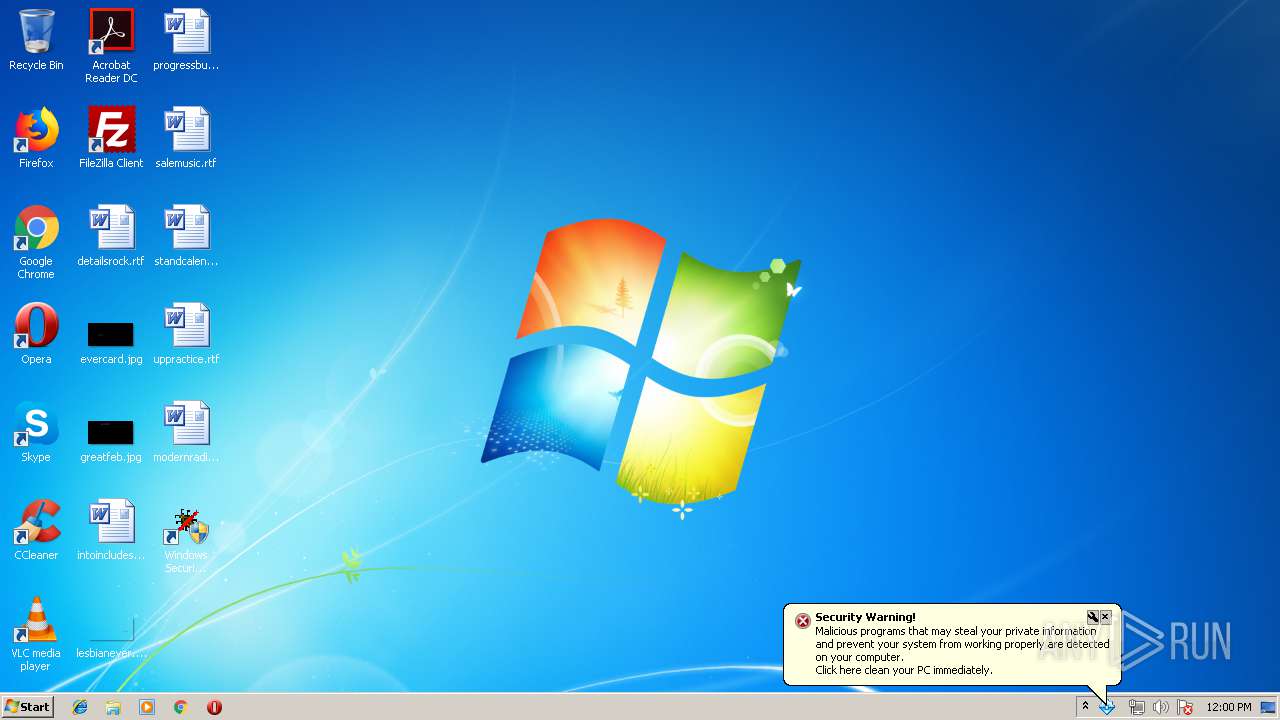
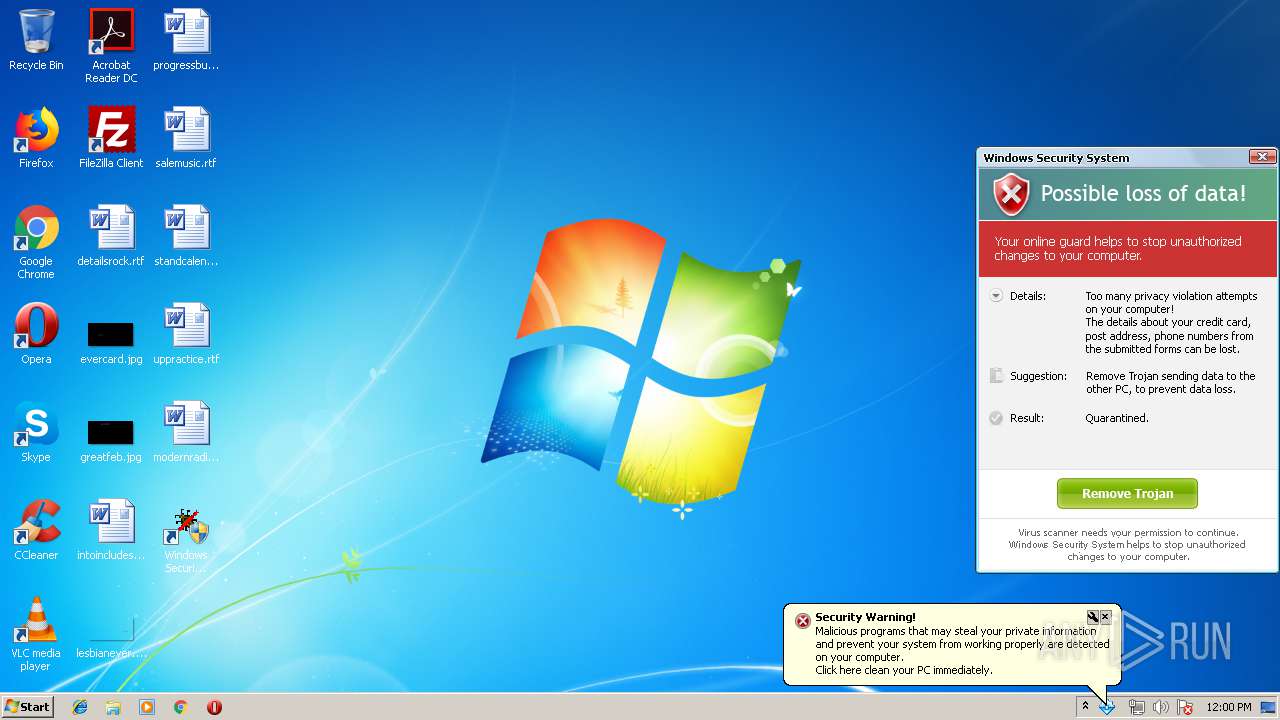
MALICIOUS
Application was dropped or rewritten from another process
- sample_110.exe (PID: 3012)
- sample_110.exe (PID: 3084)
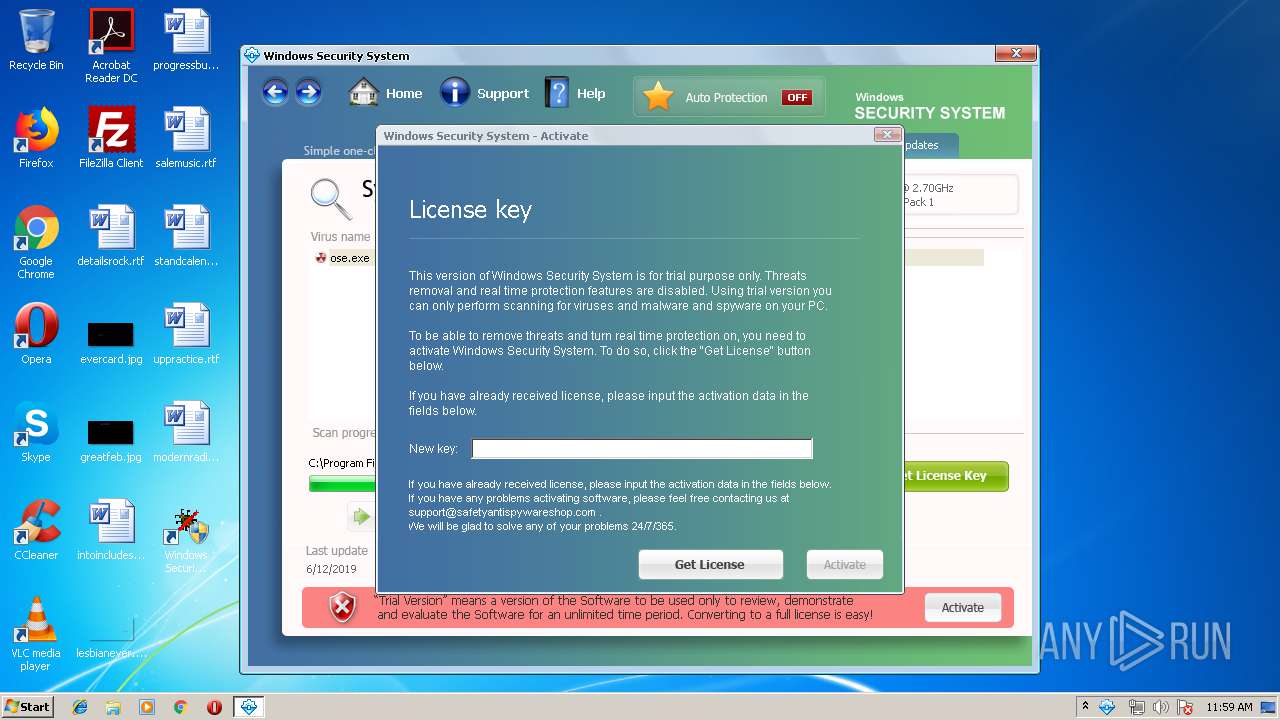
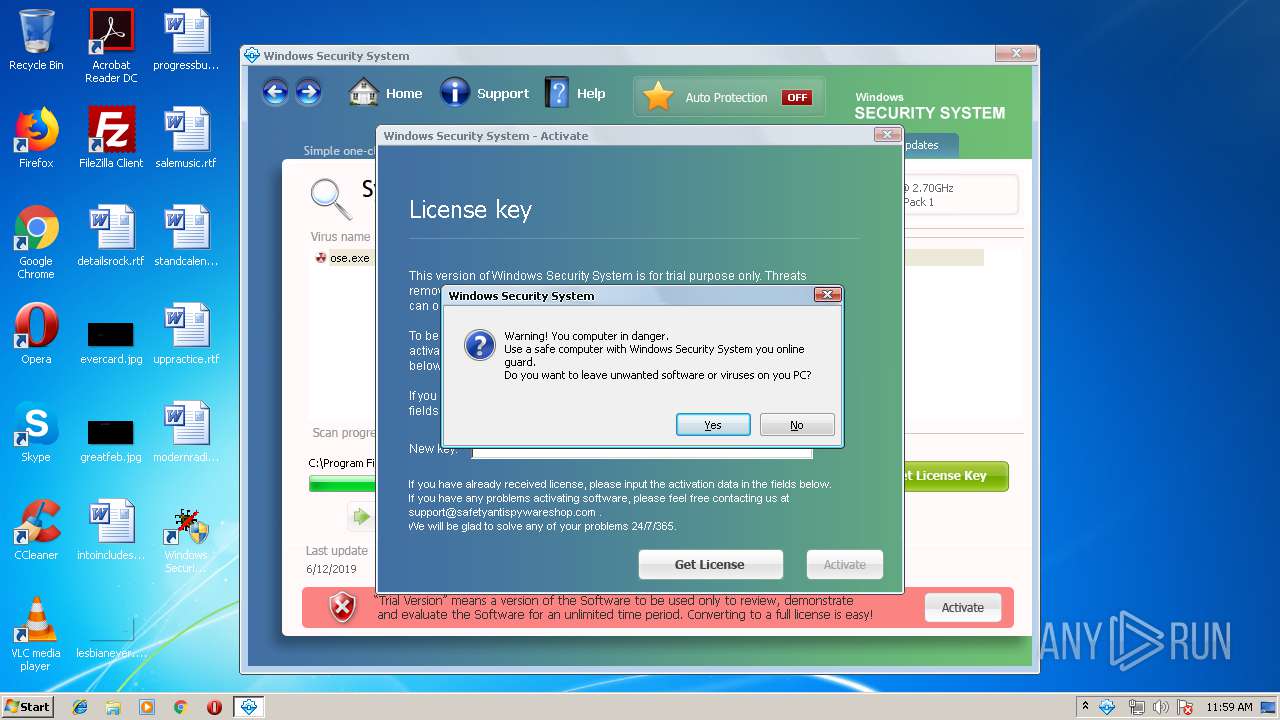
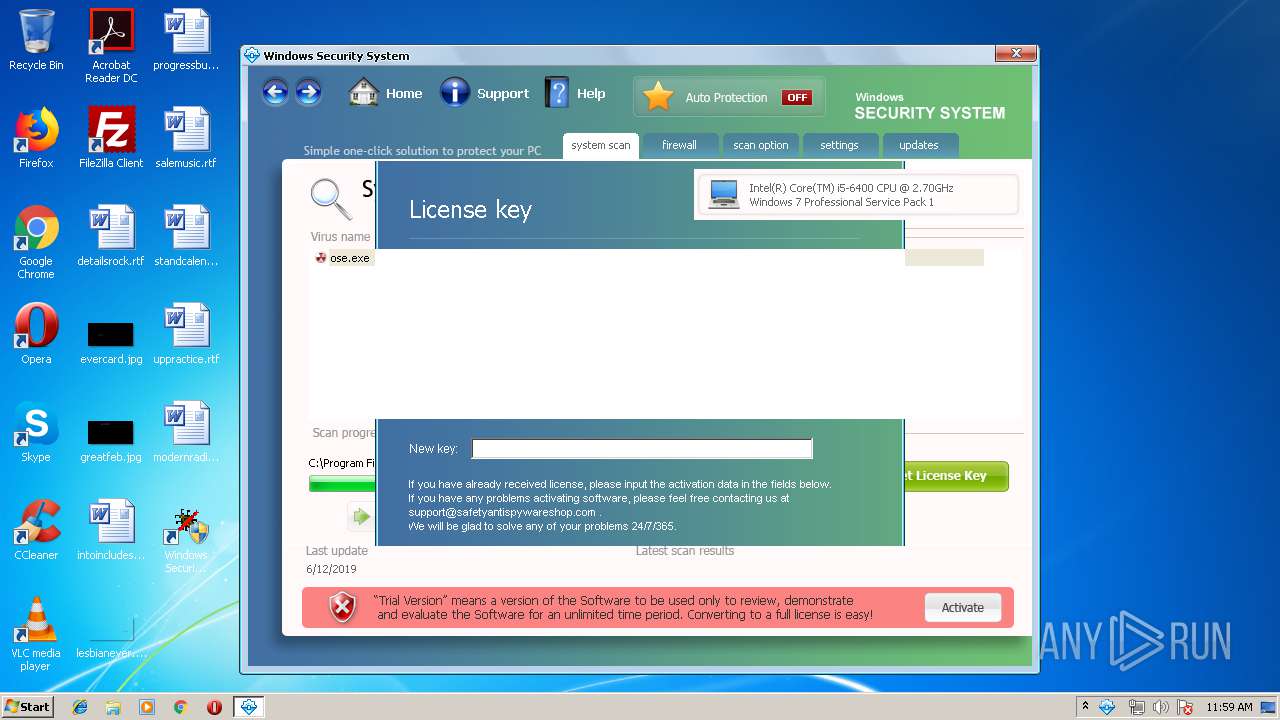
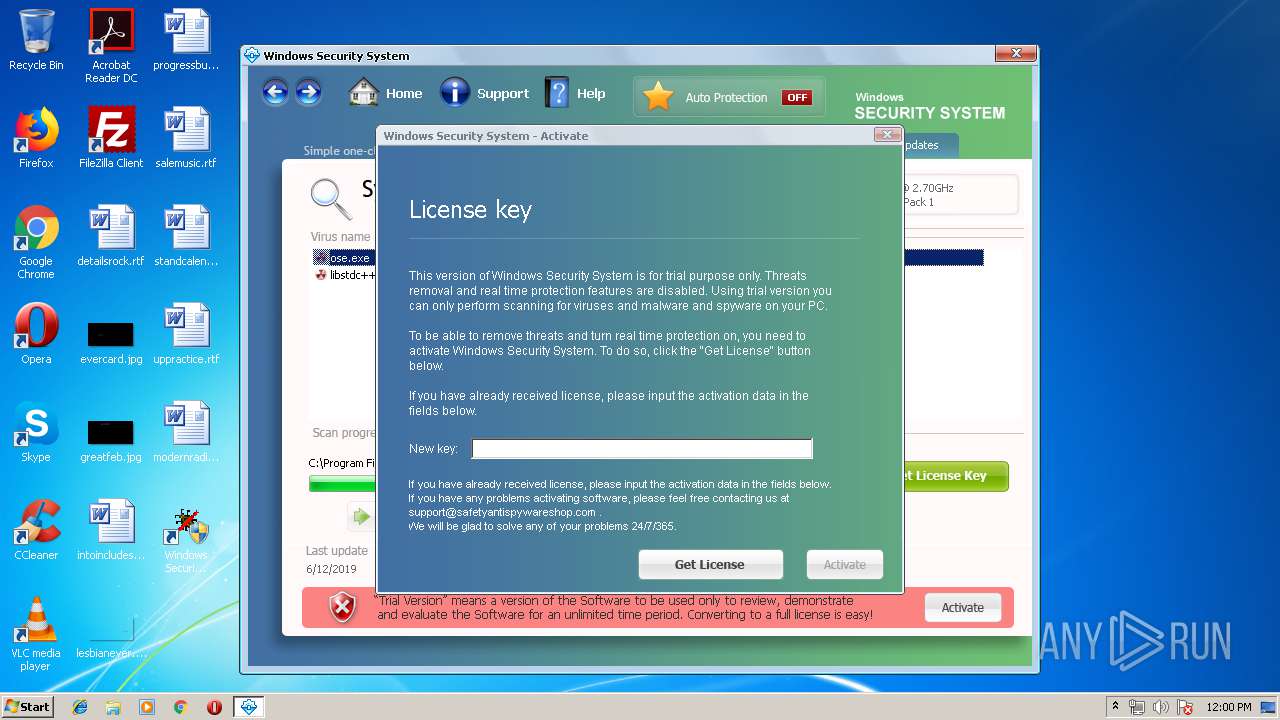
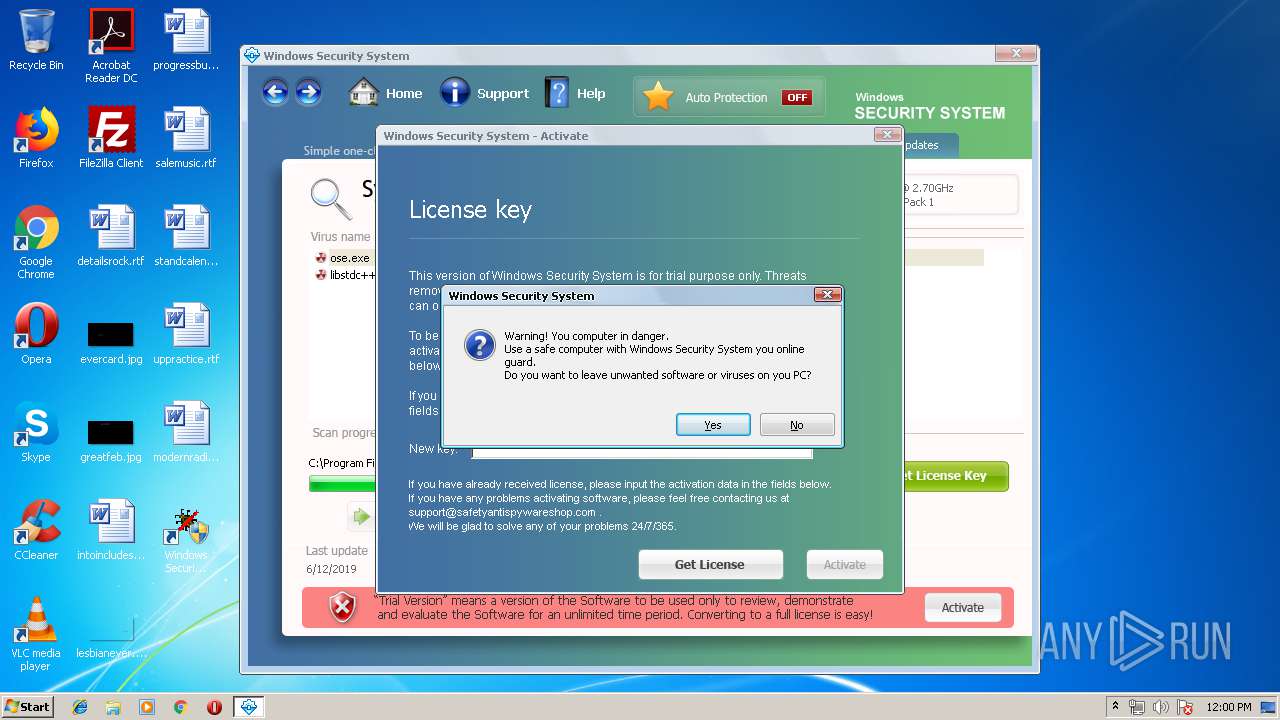
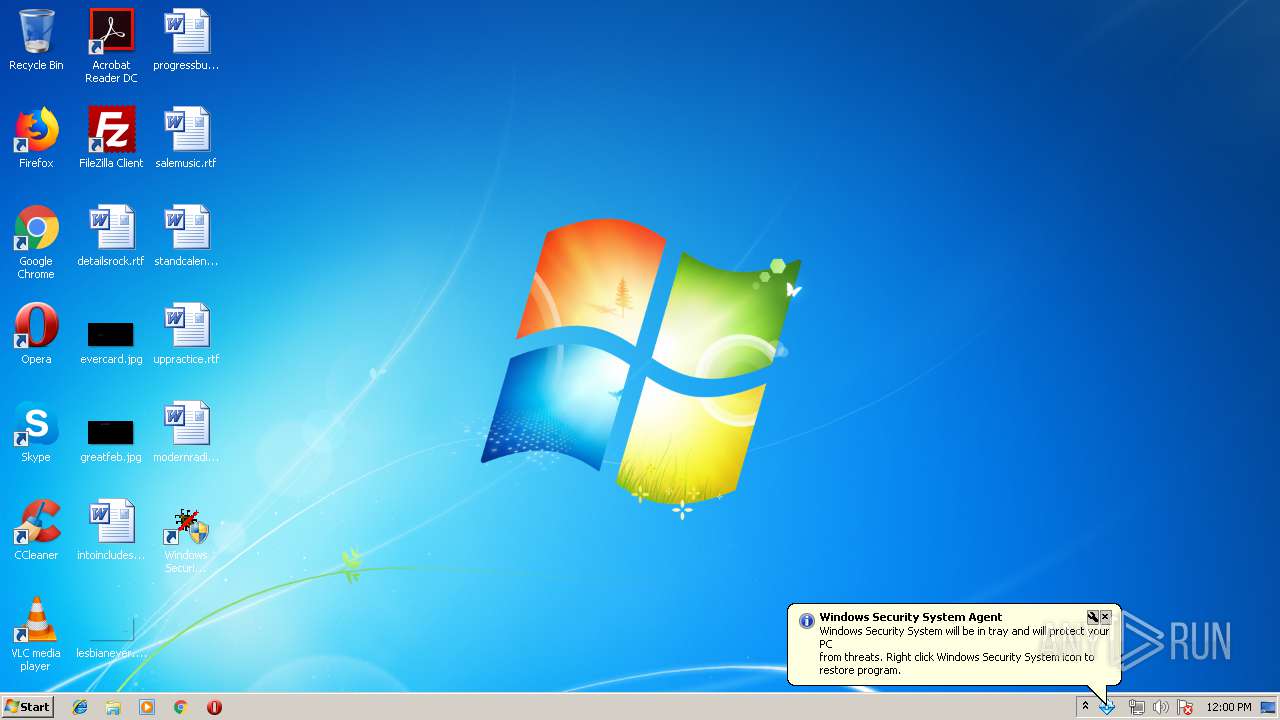
- Windows Security System.exe (PID: 3264)
Changes the autorun value in the registry
- Windows Security System.exe (PID: 3264)
SUSPICIOUS
Executable content was dropped or overwritten
- WinRAR.exe (PID: 908)
- sample_110.exe (PID: 3084)
Creates files in the program directory
- sample_110.exe (PID: 3084)
Starts itself from another location
- sample_110.exe (PID: 3084)
Starts CMD.EXE for commands execution
- sample_110.exe (PID: 3084)
Creates files in the user directory
- Windows Security System.exe (PID: 3264)
Reads internet explorer settings
- Windows Security System.exe (PID: 3264)
INFO
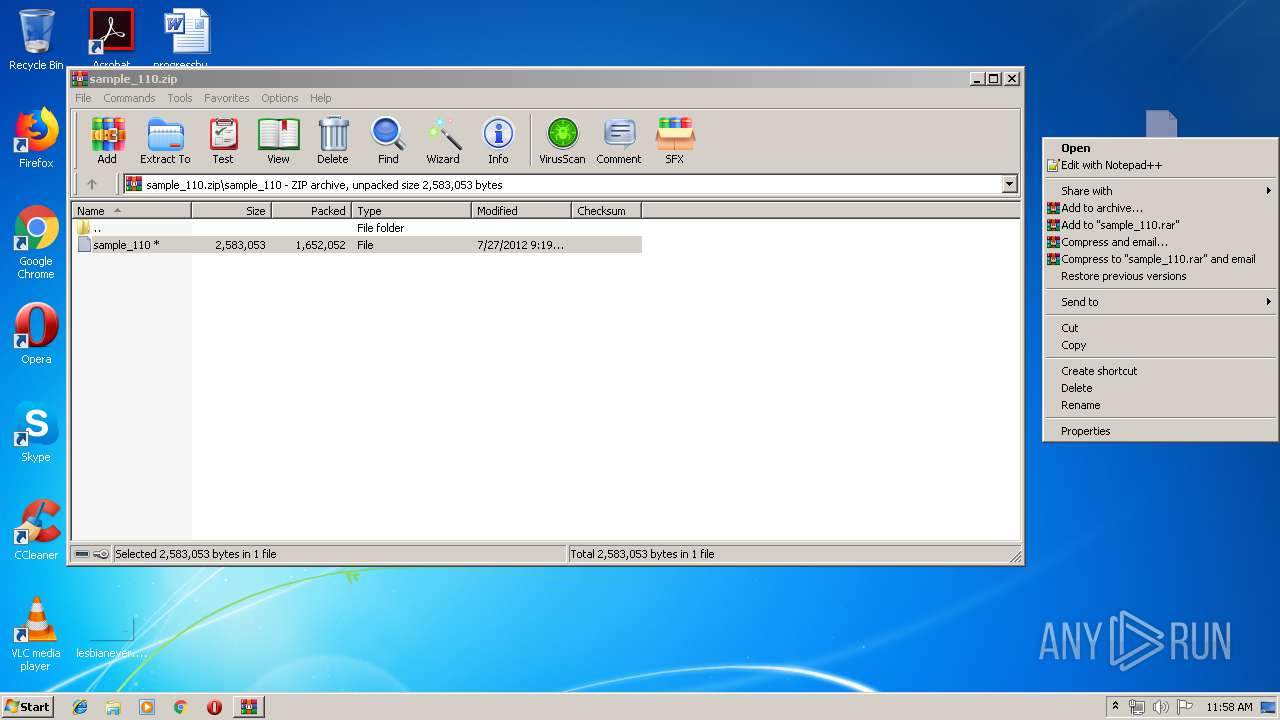
Manual execution by user
- sample_110.exe (PID: 3012)
- sample_110.exe (PID: 3084)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
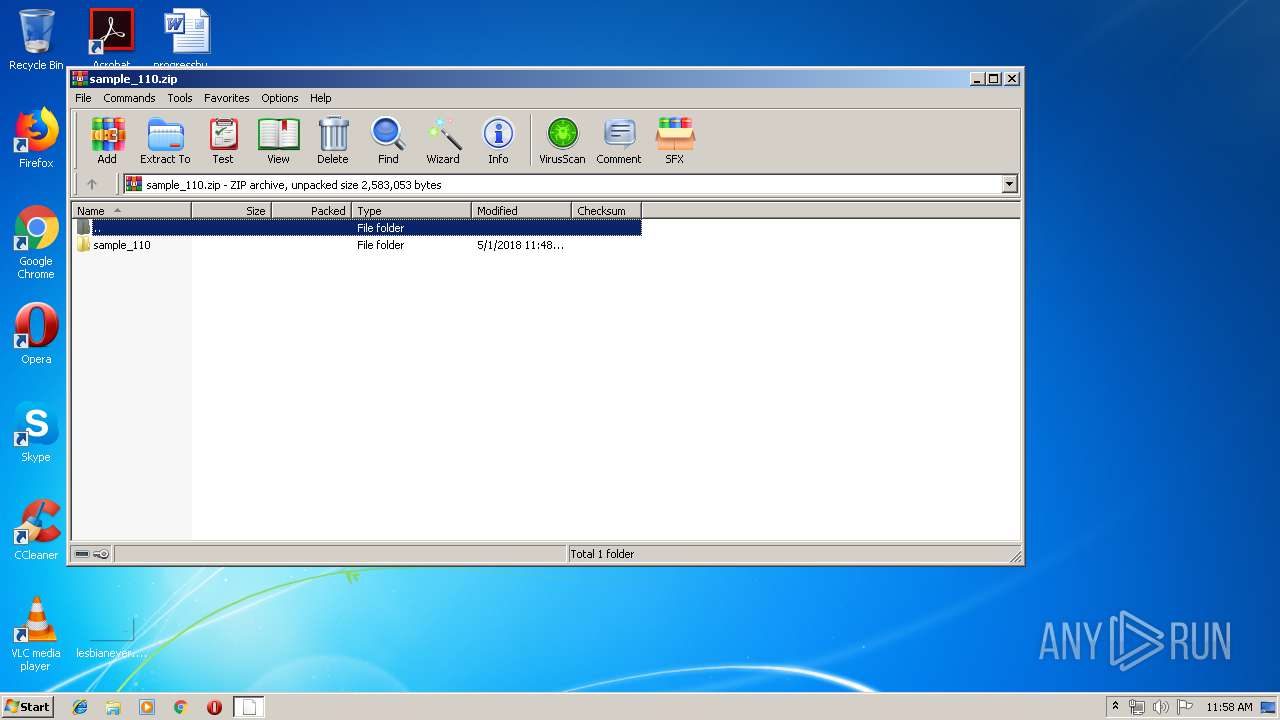
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:05:01 18:48:22 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_110/ |
Total processes
44
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
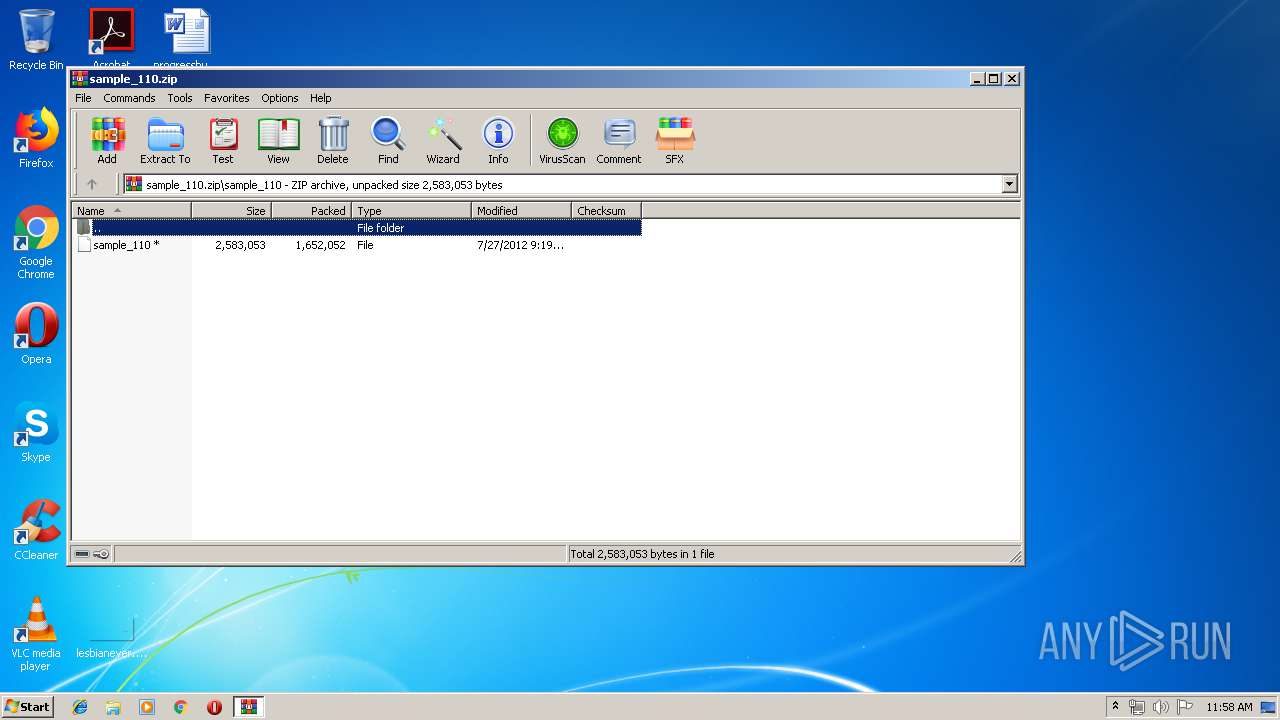
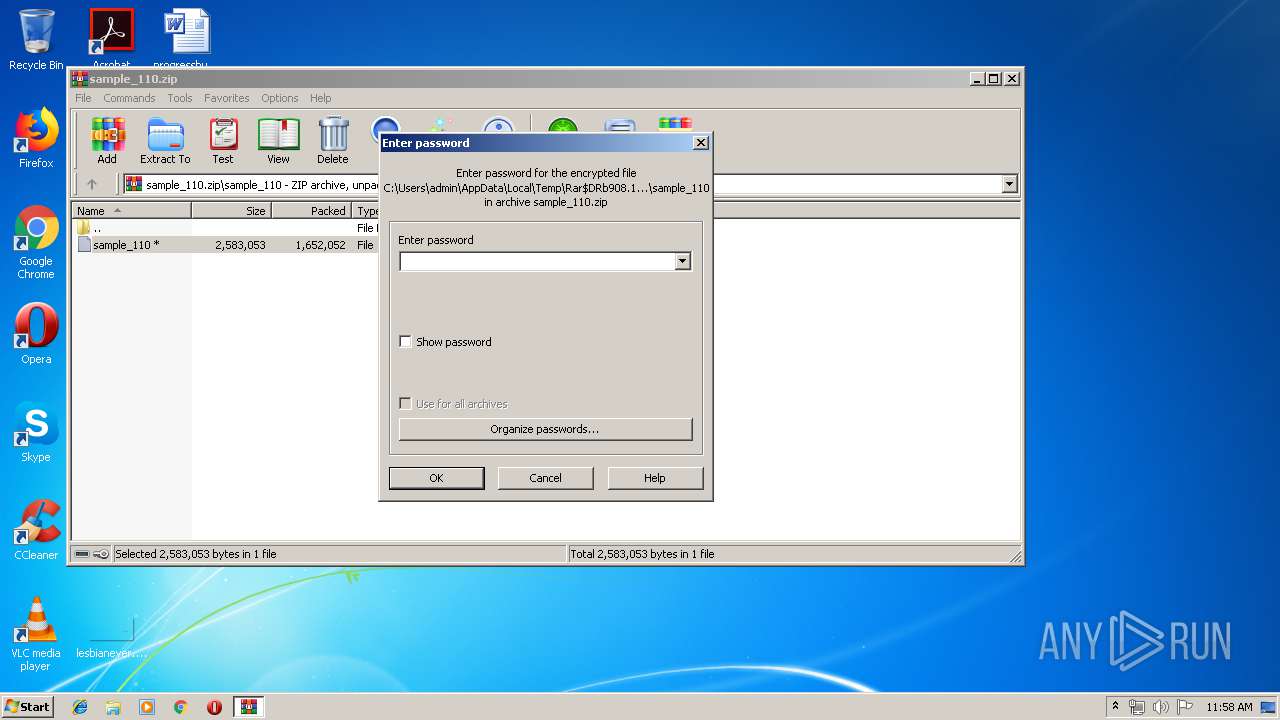
| 908 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\sample_110.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3012 | "C:\Users\admin\Desktop\sample_110.exe" | C:\Users\admin\Desktop\sample_110.exe | — | explorer.exe | |||||||||||
User: admin Company: SanDisk Integrity Level: MEDIUM Description: HaulConverter Exit code: 3221226540 Version: 3.3.0 Modules
| |||||||||||||||
| 3084 | "C:\Users\admin\Desktop\sample_110.exe" | C:\Users\admin\Desktop\sample_110.exe | explorer.exe | ||||||||||||
User: admin Company: SanDisk Integrity Level: HIGH Description: HaulConverter Exit code: 0 Version: 3.3.0 Modules
| |||||||||||||||
| 3104 | "C:\Windows\system32\cmd.exe" /c del C:\Users\admin\Desktop\SAMPLE~1.EXE > nul | C:\Windows\system32\cmd.exe | — | sample_110.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3264 | "C:\Program Files\wss\Windows Security System.exe" | C:\Program Files\wss\Windows Security System.exe | sample_110.exe | ||||||||||||
User: admin Company: SanDisk Integrity Level: HIGH Description: HaulConverter Exit code: 0 Version: 3.3.0 Modules
| |||||||||||||||
Total events
738
Read events
701
Write events
37
Delete events
0
Modification events
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_110.zip | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (908) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3084) sample_110.exe | Key: | HKEY_CURRENT_USER\Software\EBE507BD0A68FD941475A3D12A204B9E |
| Operation: | write | Name: | ”³³ |
Value: æã | |||
Executable files
2
Suspicious files
0
Text files
16
Unknown types
3
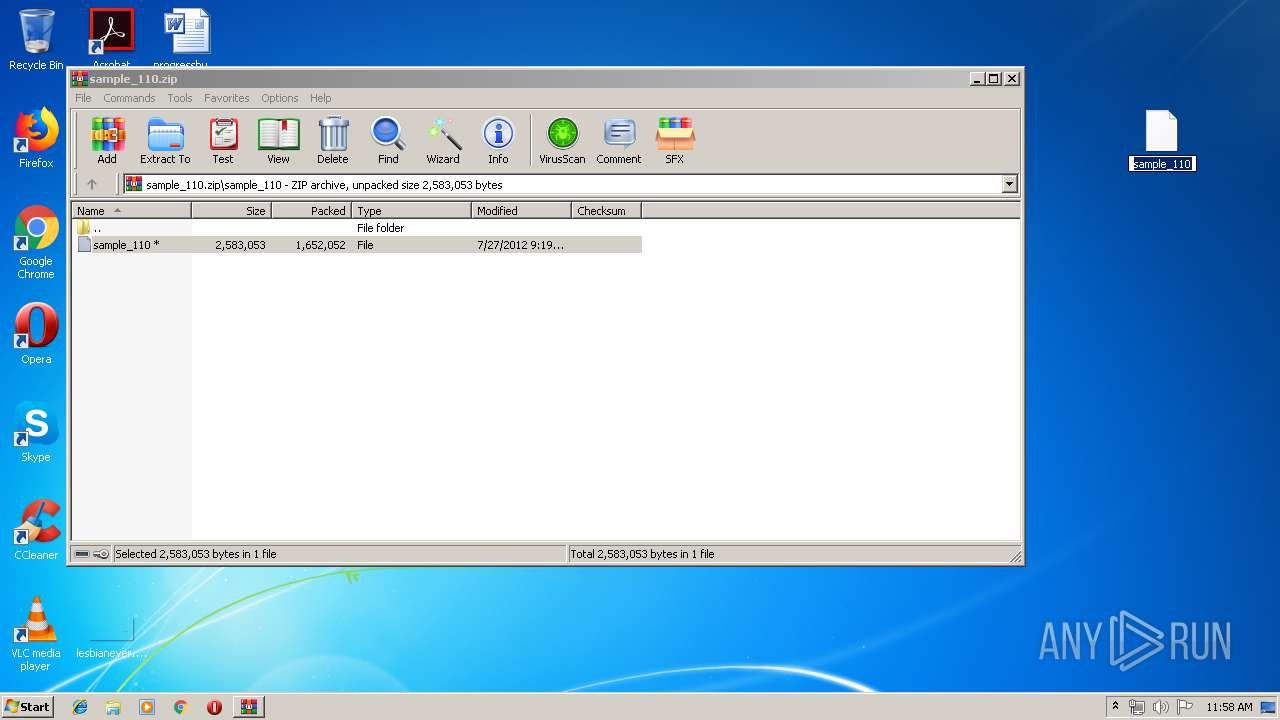
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
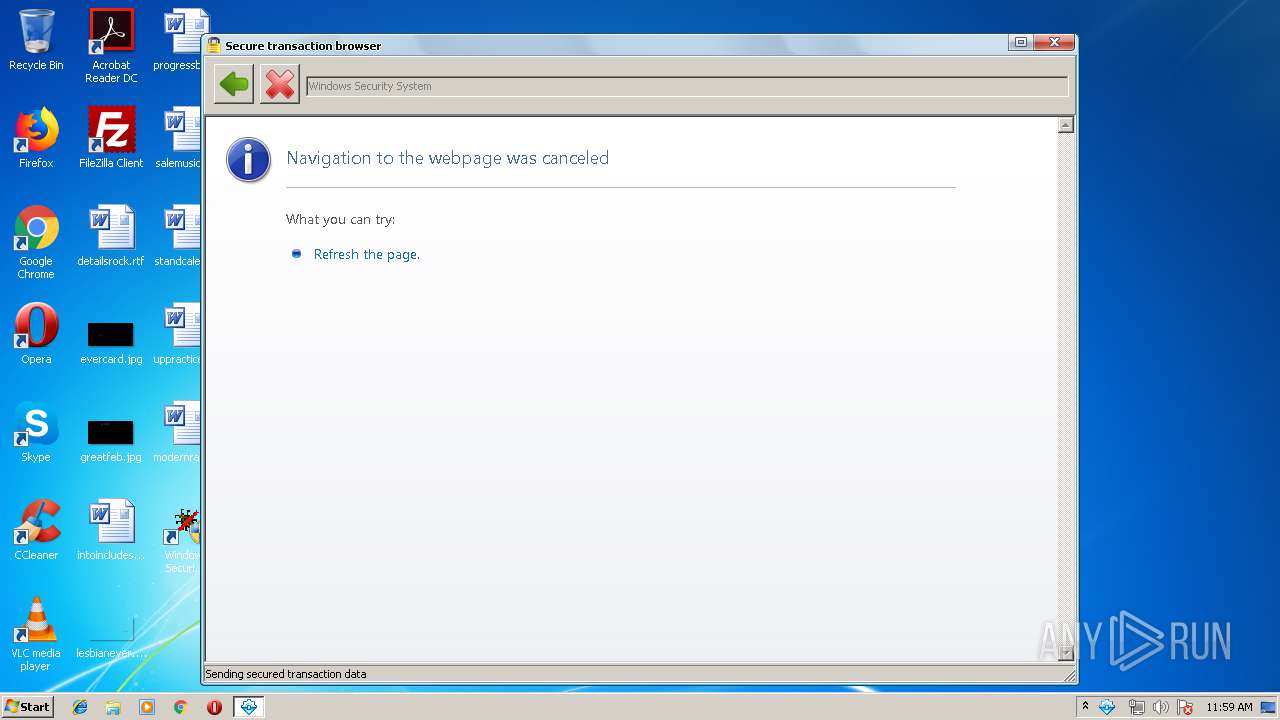
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\ErrorPageTemplate[1] | — | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\errorPageStrings[1] | — | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\httpErrorPagesScripts[1] | — | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Windows Security System.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\Desktop\Windows Security System.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Windows Security System\Windows Security System.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\navcancl[1] | html | |
MD5:4BCFE9F8DB04948CDDB5E31FE6A7F984 | SHA256:BEE0439FCF31DE76D6E2D7FD377A24A34AC8763D5BF4114DA5E1663009E24228 | |||
| 908 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb908.11976\sample_110\sample_110 | executable | |
MD5:F977008DE8B886F1684E219DA6576A03 | SHA256:C8C3249474335D57D963009C6B3D1E9EB5AA39DCFE1E2D090DED5552E280886E | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\dnserrordiagoff_webOC[2] | html | |
MD5:— | SHA256:— | |||
| 3264 | Windows Security System.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\dnserrordiagoff_webOC[1] | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
gerssfn.com |
| unknown |
allwinsecuritysys.com |
| unknown |