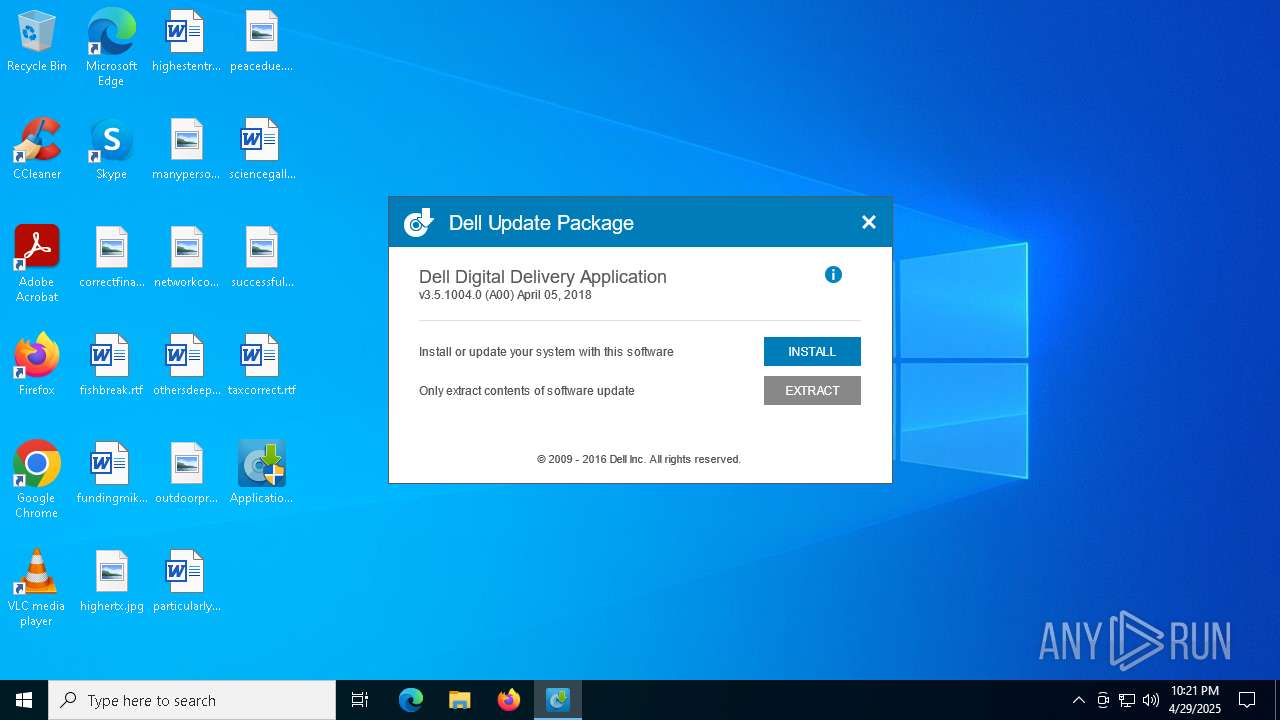
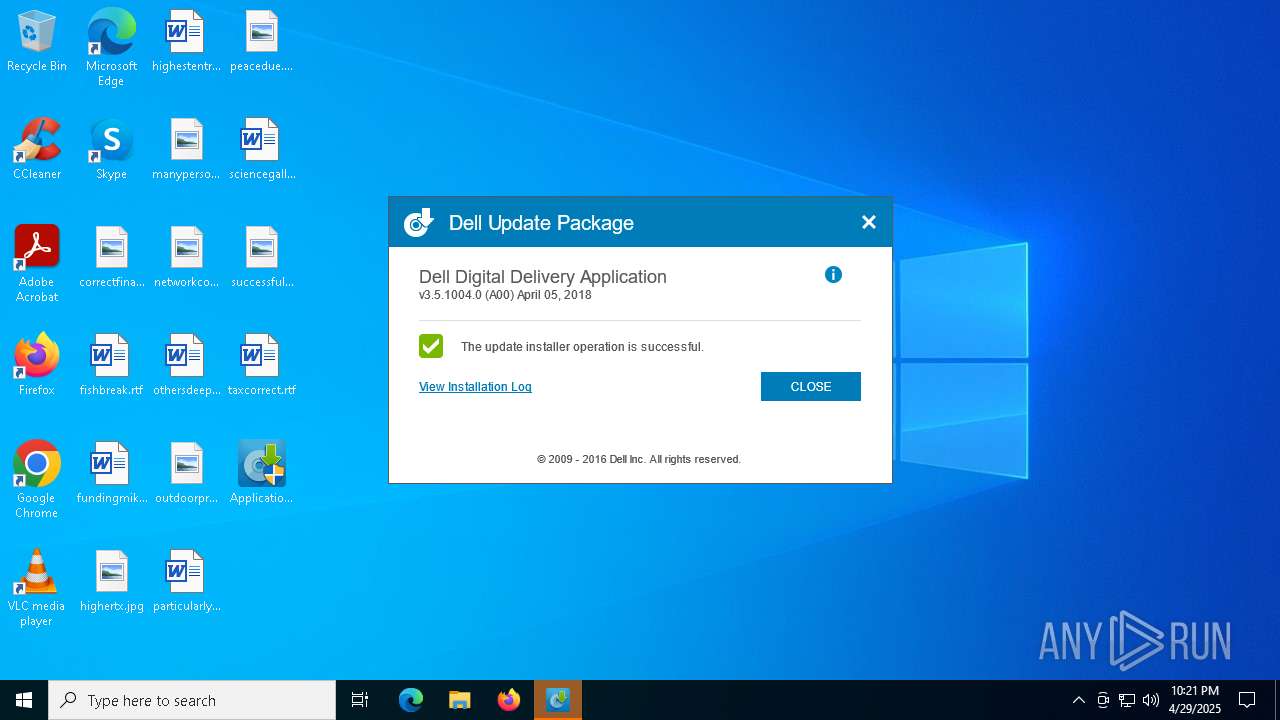
| File name: | Application_YD63W_WN32_3.5.1004.0_A00_01.EXE |
| Full analysis: | https://app.any.run/tasks/20accf5e-fef5-46be-952a-c4f9c46d9b44 |
| Verdict: | Malicious activity |
| Analysis date: | April 29, 2025, 22:21:18 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | CB2F61736B73E6360A08DE12422B76A4 |
| SHA1: | 2CC2CBCFF26E1EF7A3C5615B6CC534F2CF70B45D |
| SHA256: | 2B4BA882DEB7EA6A63B555A0D001BE94767904ACECBA5849EAFE4B035E1F1F2F |
| SSDEEP: | 98304:lC1DZcdGL+hNLlbMsfM+eFfOiH0PpoEx2w+hNThn/b8UzDV8ZBeEhAoJp7phXl6z:2jF |
MALICIOUS
Executing a file with an untrusted certificate
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 5392)
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
SUSPICIOUS
Reads security settings of Internet Explorer
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
- DeliveryService.exe (PID: 1388)
Reads Microsoft Outlook installation path
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
Executable content was dropped or overwritten
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
- rundll32.exe (PID: 664)
- miniunz.exe (PID: 2392)
Reads Internet Explorer settings
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 4268)
Adds/modifies Windows certificates
- msiexec.exe (PID: 5392)
Executes as Windows Service
- DeliveryService.exe (PID: 1388)
INFO
The sample compiled with english language support
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
Creates files in the program directory
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
- DeliveryService.exe (PID: 1388)
- miniunz.exe (PID: 2392)
- msiexec.exe (PID: 5392)
Reads the computer name
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
- msiexec.exe (PID: 4268)
- msiexec.exe (PID: 960)
- DeliveryService.exe (PID: 1388)
Checks supported languages
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
- miniunz.exe (PID: 2392)
- msiexec.exe (PID: 4268)
- msiexec.exe (PID: 960)
- DeliveryService.exe (PID: 1388)
Checks proxy server information
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
- msiexec.exe (PID: 5392)
Executable content was dropped or overwritten
- msiexec.exe (PID: 4268)
Reads the machine GUID from the registry
- msiexec.exe (PID: 4268)
- DeliveryService.exe (PID: 1388)
Reads the software policy settings
- msiexec.exe (PID: 4268)
- msiexec.exe (PID: 5392)
Creates files or folders in the user directory
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
Creates a software uninstall entry
- msiexec.exe (PID: 4268)
Process checks computer location settings
- Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe (PID: 6036)
Reads security settings of Internet Explorer
- msiexec.exe (PID: 5392)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (17.3) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (4.1) |
| .exe | | | Win32 Executable (generic) (2.8) |
| .exe | | | Generic Win/DOS Executable (1.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2017:06:09 10:09:55+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 3830272 |
| InitializedDataSize: | 2111488 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x30fbfb |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 103.4.6.59 |
| ProductVersionNumber: | 3.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Dell Inc. |
| FileDescription: | Update Package: Dell Digital Delivery Application, 3.5.1004.0, A00 |
| FileVersion: | 003.000.000.000 |
| InternalName: | DUPFramework.exe |
| LegalCopyright: | Copyright (C) Dell Inc. 2003. All rights reserved. |
| OriginalFileName: | DUPFramework.exe |
| ProductName: | Dell Digital Delivery Application, 3.5.1004.0, A00 |
| ProductVersion: | 3.5.1004.0 |
Total processes
141
Monitored processes
11
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 664 | rundll32.exe "C:\WINDOWS\Installer\MSIE457.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1107109 2 DetectAlienware!DetectAlienware.CustomActions.DetectAlienware | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 960 | C:\Windows\syswow64\MsiExec.exe -Embedding CE85F0E3D14F08909EB2CCBAD2AE1578 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1388 | "C:\Program Files (x86)\Dell Digital Delivery\DeliveryService.exe" | C:\Program Files (x86)\Dell Digital Delivery\DeliveryService.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Dell Products, LP. Integrity Level: SYSTEM Description: Dell Digital Delivery Windows Service Version: 3.5.1004 Modules
| |||||||||||||||
| 2392 | -x C:\Users\admin\Desktop\APPLIC~1.EXE -o -d C:\PROGRA~3\dell\drivers\APPLIC~1.EXE | C:\ProgramData\Dell\drivers\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE\miniunz.exe | Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 4268 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5392 | "C:\Users\admin\Desktop\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe" | C:\Users\admin\Desktop\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | — | explorer.exe | |||||||||||
User: admin Company: Dell Inc. Integrity Level: MEDIUM Description: Update Package: Dell Digital Delivery Application, 3.5.1004.0, A00 Exit code: 3221226540 Version: 003.000.000.000 Modules
| |||||||||||||||
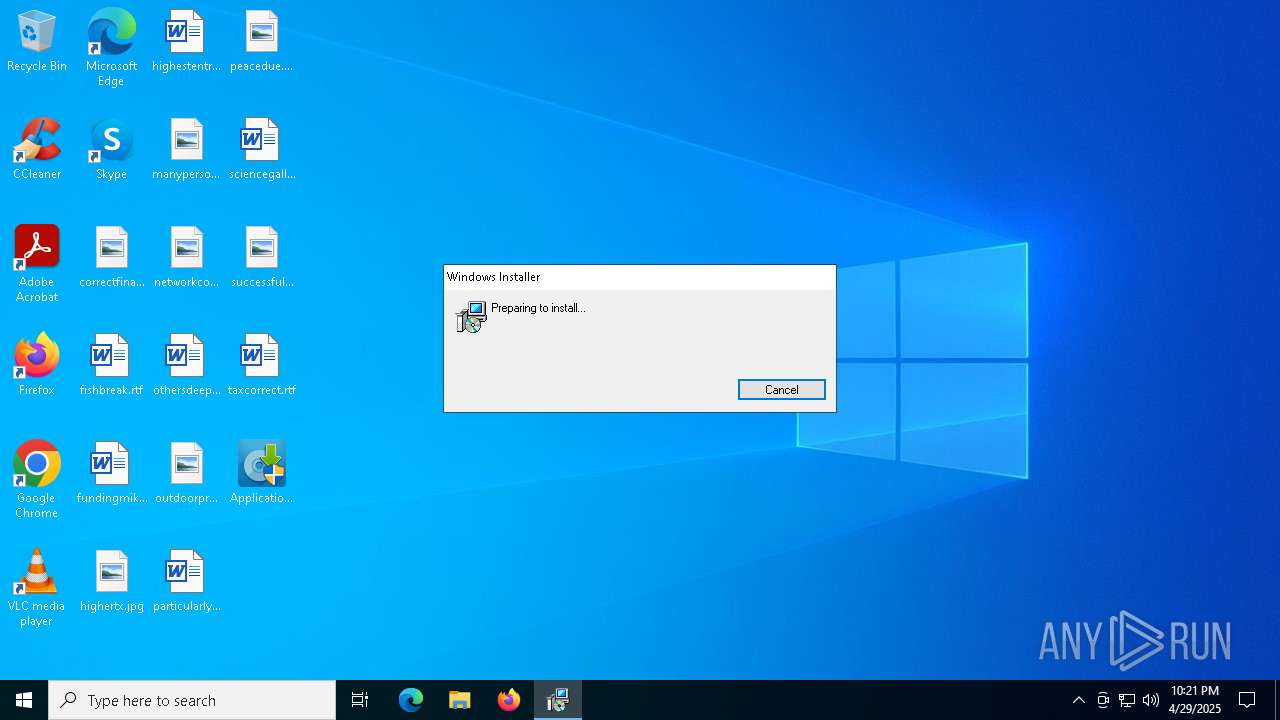
| 5392 | "C:\Windows\System32\msiexec.exe" /i DellDigitalDelivery.3.5.1004.0.msi /log C:\ProgramData\dell\drivers\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE\DUPD9C8.tmp | C:\Windows\SysWOW64\msiexec.exe | Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6032 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6036 | "C:\Users\admin\Desktop\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe" | C:\Users\admin\Desktop\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | explorer.exe | ||||||||||||
User: admin Company: Dell Inc. Integrity Level: HIGH Description: Update Package: Dell Digital Delivery Application, 3.5.1004.0, A00 Exit code: 0 Version: 003.000.000.000 Modules
| |||||||||||||||
| 6640 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | miniunz.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
15 222
Read events
15 024
Write events
184
Delete events
14
Modification events
| (PID) Process: | (6036) Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6036) Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6036) Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (5392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 8CF427FD790C3AD166068DE81E57EFBB932272D4 |
Value: | |||
| (PID) Process: | (5392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8CF427FD790C3AD166068DE81E57EFBB932272D4 |
| Operation: | write | Name: | Blob |
Value: 0400000001000000100000004BE2C99196650CF40E5A9392A00AFEB21D0000000100000010000000521B5F4582C1DCAAE381B05E37CA2D340B000000010000001800000045006E00740072007500730074002E006E006500740000007F000000010000002C000000302A060A2B0601040182370A030406082B0601050507030506082B0601050507030606082B06010505070307090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F0000000100000020000000FDE5F2D9CE2026E1E10064C0A468C9F355B90ACF85BAF5CE6F52D4016837FD940300000001000000140000008CF427FD790C3AD166068DE81E57EFBB932272D4190000000100000010000000FA46CE7CBB85CFB4310075313A09EE05530000000100000041000000303F3020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C062000000010000002000000043DF5774B03E7FEF5FE40D931A7BEDF1BB2E6B42738C4E6D3841103D3AA7F3391400000001000000140000006A72267AD01EEF7DE73B6951D46C8D9F901266AB7E000000010000000800000000C001B39667D6012000000001000000420400003082043E30820326A00302010202044A538C28300D06092A864886F70D01010B05003081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D204732301E170D3039303730373137323535345A170D3330313230373137353535345A3081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BA84B672DB9E0C6BE299E93001A776EA32B895411AC9DA614E5872CFFEF68279BF7361060AA527D8B35FD3454E1C72D64E32F2728A0FF78319D06A808000451EB0C7E79ABF1257271CA3682F0A87BD6A6B0E5E65F31C77D5D4858D7021B4B332E78BA2D5863902B1B8D247CEE4C949C43BA7DEFB547D57BEF0E86EC279B23A0B55E250981632135C2F7856C1C294B3F25AE4279A9F24D7C6ECD09B2582E3CCC2C445C58C977A066B2A119FA90A6E483B6FDBD4111942F78F07BFF5535F9C3EF4172CE669AC4E324C6277EAB7E8E5BB34BC198BAE9C51E7B77EB553B13322E56DCF703C1AFAE29B67B683F48DA5AF624C4DE058AC64341203F8B68D946324A4710203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604146A72267AD01EEF7DE73B6951D46C8D9F901266AB300D06092A864886F70D01010B05000382010100799F1D96C6B6793F228D87D3870304606A6B9A2E59897311AC43D1F513FF8D392BC0F2BD4F708CA92FEA17C40B549ED41B9698333CA8AD62A20076AB59696E061D7EC4B9448D98AF12D461DB0A194647F3EBF763C1400540A5D2B7F4B59A36BFA98876880455042B9C877F1A373C7E2DA51AD8D4895ECABDAC3D6CD86DAFD5F3760FCD3B8838229D6C939AC43DBF821B653FA60F5DAAFCE5B215CAB5ADC6BC3DD084E8EA0672B04D393278BF3E119C0BA49D9A21F3F09B0B3078DBC1DC8743FEBC639ACAC5C21CC9C78DFF3B125808E6B63DEC7A2C4EFB8396CE0C3C69875473A473C293FF5110AC155401D8FC05B189A17F74839A49D7DC4E7B8A486F8B45F6 | |||
| (PID) Process: | (5392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\8CF427FD790C3AD166068DE81E57EFBB932272D4 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800007E000000010000000800000000C001B39667D6011400000001000000140000006A72267AD01EEF7DE73B6951D46C8D9F901266AB62000000010000002000000043DF5774B03E7FEF5FE40D931A7BEDF1BB2E6B42738C4E6D3841103D3AA7F339530000000100000041000000303F3020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C0190000000100000010000000FA46CE7CBB85CFB4310075313A09EE050300000001000000140000008CF427FD790C3AD166068DE81E57EFBB932272D40F0000000100000020000000FDE5F2D9CE2026E1E10064C0A468C9F355B90ACF85BAF5CE6F52D4016837FD94090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703087F000000010000002C000000302A060A2B0601040182370A030406082B0601050507030506082B0601050507030606082B060105050703070B000000010000001800000045006E00740072007500730074002E006E006500740000001D0000000100000010000000521B5F4582C1DCAAE381B05E37CA2D340400000001000000100000004BE2C99196650CF40E5A9392A00AFEB22000000001000000420400003082043E30820326A00302010202044A538C28300D06092A864886F70D01010B05003081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D204732301E170D3039303730373137323535345A170D3330313230373137353535345A3081BE310B300906035504061302555331163014060355040A130D456E74727573742C20496E632E31283026060355040B131F536565207777772E656E74727573742E6E65742F6C6567616C2D7465726D7331393037060355040B1330286329203230303920456E74727573742C20496E632E202D20666F7220617574686F72697A656420757365206F6E6C793132303006035504031329456E747275737420526F6F742043657274696669636174696F6E20417574686F72697479202D20473230820122300D06092A864886F70D01010105000382010F003082010A0282010100BA84B672DB9E0C6BE299E93001A776EA32B895411AC9DA614E5872CFFEF68279BF7361060AA527D8B35FD3454E1C72D64E32F2728A0FF78319D06A808000451EB0C7E79ABF1257271CA3682F0A87BD6A6B0E5E65F31C77D5D4858D7021B4B332E78BA2D5863902B1B8D247CEE4C949C43BA7DEFB547D57BEF0E86EC279B23A0B55E250981632135C2F7856C1C294B3F25AE4279A9F24D7C6ECD09B2582E3CCC2C445C58C977A066B2A119FA90A6E483B6FDBD4111942F78F07BFF5535F9C3EF4172CE669AC4E324C6277EAB7E8E5BB34BC198BAE9C51E7B77EB553B13322E56DCF703C1AFAE29B67B683F48DA5AF624C4DE058AC64341203F8B68D946324A4710203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E041604146A72267AD01EEF7DE73B6951D46C8D9F901266AB300D06092A864886F70D01010B05000382010100799F1D96C6B6793F228D87D3870304606A6B9A2E59897311AC43D1F513FF8D392BC0F2BD4F708CA92FEA17C40B549ED41B9698333CA8AD62A20076AB59696E061D7EC4B9448D98AF12D461DB0A194647F3EBF763C1400540A5D2B7F4B59A36BFA98876880455042B9C877F1A373C7E2DA51AD8D4895ECABDAC3D6CD86DAFD5F3760FCD3B8838229D6C939AC43DBF821B653FA60F5DAAFCE5B215CAB5ADC6BC3DD084E8EA0672B04D393278BF3E119C0BA49D9A21F3F09B0B3078DBC1DC8743FEBC639ACAC5C21CC9C78DFF3B125808E6B63DEC7A2C4EFB8396CE0C3C69875473A473C293FF5110AC155401D8FC05B189A17F74839A49D7DC4E7B8A486F8B45F6 | |||
| (PID) Process: | (5392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates |
| Operation: | delete value | Name: | 503006091D97D4F5AE39F7CBE7927D7D652D3431 |
Value: | |||
| (PID) Process: | (5392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\503006091D97D4F5AE39F7CBE7927D7D652D3431 |
| Operation: | write | Name: | Blob |
Value: 040000000100000010000000EE2931BC327E9AE6E8B5F751B43471901D0000000100000010000000E871723E266F38AF5D49CDA2A502669C0B000000010000001E00000045006E0074007200750073007400200028003200300034003800290000007F000000010000002C000000302A060A2B0601040182370A030406082B0601050507030506082B0601050507030606082B06010505070307090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703080F0000000100000014000000327FC447408DE9BF596F83D4B2FA4B8E3E7097D8030000000100000014000000503006091D97D4F5AE39F7CBE7927D7D652D343119000000010000001000000091FAD483F14848A8A69B18B805CDBB3A530000000100000041000000303F3020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C06200000001000000200000006DC47172E01CBCB0BF62580D895FE2B8AC9AD4F873801E0C10B9C837D21EB17714000000010000001400000055E481D11180BED889B908A331F9A1240916B9707E000000010000000800000000C001B39667D60120000000010000002E0400003082042A30820312A00302010202043863DEF8300D06092A864886F70D01010505003081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F7269747920283230343829301E170D3939313232343137353035315A170D3239303732343134313531325A3081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F726974792028323034382930820122300D06092A864886F70D01010105000382010F003082010A0282010100AD4D4BA91286B2EAA320071516642A2B4BD1BF0B4A4D8EED8076A567B77840C07342C868C0DB532BDD5EB8769835938B1A9D7C133A0E1F5BB71ECFE524141EB181A98D7DB8CC6B4B03F1020CDCABA54024007F7494A19D0829B3880BF587779D55CDE4C37ED76A64AB851486955B9732506F3DC8BA660CE3FCBDB849C176894919FDC0A8BD89A3672FC69FBC711960B82DE92CC99076667B94E2AF78D665535D3CD69CB2CF2903F92FA450B2D448CE0532558AFDB2644C0EE4980775DB7FDFB9085560853029F97B48A46986E3353F1E865D7A7A15BDEF008E1522541700902693BC0E496891BFF847D39D9542C10E4DDF6F26CFC3182162664370D6D5C007E10203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E0416041455E481D11180BED889B908A331F9A1240916B970300D06092A864886F70D010105050003820101003B9B8F569B30E753997C7A79A74D97D7199590FB061FCA337C46638F966624FA401B2127CAE67273F24FFE3199FDC80C4C6853C680821398FAB6ADDA5D3DF1CE6EF6151194820CEE3F95AF11AB0FD72FDE1F038F572C1EC9BB9A1A4495EB184FA61FCD7D57102F9B04095A84B56ED81D3AE1D69ED16C795E791C14C5E3D04C933B653CEDDF3DBEA6E5951AC3B519C3BD5E5BBBFF23EF6819CB1293275C032D6F30D01EB61AACDE5AF7D1AAA827A6FE7981C479993357BA12B0A9E0426C93CA56DEFE6D840B088B7E8DEAD79821C6F3E73C792F5E9CD14C158DE1EC2237CC9A430B97DC80908DB3679B6F48081556CFBFF12B7C5E9A76E95990C57C8335116551 | |||
| (PID) Process: | (5392) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\SystemCertificates\AuthRoot\Certificates\503006091D97D4F5AE39F7CBE7927D7D652D3431 |
| Operation: | write | Name: | Blob |
Value: 5C0000000100000004000000000800007E000000010000000800000000C001B39667D60114000000010000001400000055E481D11180BED889B908A331F9A1240916B9706200000001000000200000006DC47172E01CBCB0BF62580D895FE2B8AC9AD4F873801E0C10B9C837D21EB177530000000100000041000000303F3020060A6086480186FA6C0A010230123010060A2B0601040182373C0101030200C0301B060567810C010330123010060A2B0601040182373C0101030200C019000000010000001000000091FAD483F14848A8A69B18B805CDBB3A030000000100000014000000503006091D97D4F5AE39F7CBE7927D7D652D34310F0000000100000014000000327FC447408DE9BF596F83D4B2FA4B8E3E7097D8090000000100000054000000305206082B0601050507030206082B06010505070303060A2B0601040182370A030406082B0601050507030406082B0601050507030606082B0601050507030706082B0601050507030106082B060105050703087F000000010000002C000000302A060A2B0601040182370A030406082B0601050507030506082B0601050507030606082B060105050703070B000000010000001E00000045006E0074007200750073007400200028003200300034003800290000001D0000000100000010000000E871723E266F38AF5D49CDA2A502669C040000000100000010000000EE2931BC327E9AE6E8B5F751B434719020000000010000002E0400003082042A30820312A00302010202043863DEF8300D06092A864886F70D01010505003081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F7269747920283230343829301E170D3939313232343137353035315A170D3239303732343134313531325A3081B431143012060355040A130B456E74727573742E6E65743140303E060355040B14377777772E656E74727573742E6E65742F4350535F3230343820696E636F72702E206279207265662E20286C696D697473206C6961622E2931253023060355040B131C286329203139393920456E74727573742E6E6574204C696D69746564313330310603550403132A456E74727573742E6E65742043657274696669636174696F6E20417574686F726974792028323034382930820122300D06092A864886F70D01010105000382010F003082010A0282010100AD4D4BA91286B2EAA320071516642A2B4BD1BF0B4A4D8EED8076A567B77840C07342C868C0DB532BDD5EB8769835938B1A9D7C133A0E1F5BB71ECFE524141EB181A98D7DB8CC6B4B03F1020CDCABA54024007F7494A19D0829B3880BF587779D55CDE4C37ED76A64AB851486955B9732506F3DC8BA660CE3FCBDB849C176894919FDC0A8BD89A3672FC69FBC711960B82DE92CC99076667B94E2AF78D665535D3CD69CB2CF2903F92FA450B2D448CE0532558AFDB2644C0EE4980775DB7FDFB9085560853029F97B48A46986E3353F1E865D7A7A15BDEF008E1522541700902693BC0E496891BFF847D39D9542C10E4DDF6F26CFC3182162664370D6D5C007E10203010001A3423040300E0603551D0F0101FF040403020106300F0603551D130101FF040530030101FF301D0603551D0E0416041455E481D11180BED889B908A331F9A1240916B970300D06092A864886F70D010105050003820101003B9B8F569B30E753997C7A79A74D97D7199590FB061FCA337C46638F966624FA401B2127CAE67273F24FFE3199FDC80C4C6853C680821398FAB6ADDA5D3DF1CE6EF6151194820CEE3F95AF11AB0FD72FDE1F038F572C1EC9BB9A1A4495EB184FA61FCD7D57102F9B04095A84B56ED81D3AE1D69ED16C795E791C14C5E3D04C933B653CEDDF3DBEA6E5951AC3B519C3BD5E5BBBFF23EF6819CB1293275C032D6F30D01EB61AACDE5AF7D1AAA827A6FE7981C479993357BA12B0A9E0426C93CA56DEFE6D840B088B7E8DEAD79821C6F3E73C792F5E9CD14C158DE1EC2237CC9A430B97DC80908DB3679B6F48081556CFBFF12B7C5E9A76E95990C57C8335116551 | |||
| (PID) Process: | (4268) msiexec.exe | Key: | HKEY_USERS\S-1-5-21-1693682860-607145093-2874071422-1001\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: AC1000009BB9841355B9DB01 | |||
Executable files
49
Suspicious files
27
Text files
11
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6036 | Application_YD63W_WN32_3.5.1004.0_A00_01.EXE.exe | C:\ProgramData\Dell\drivers\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE\miniunz.exe | executable | |
MD5:E766FB50873A6255F6CE015F7E692F22 | SHA256:B252EA293FFD0CE83160E27ED98BB94A526C21CB13F26E45E0F3AACA70CA00E0 | |||
| 4268 | msiexec.exe | C:\Windows\Installer\MSIE8DC.tmp | binary | |
MD5:C6D20BC6E65D7E1A2754D113A528FBE0 | SHA256:2270FC0C83FD1192C3B538EC581E20581C62927C486677BDB292915970AC062D | |||
| 2392 | miniunz.exe | C:\ProgramData\Dell\drivers\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE\DellDigitalDelivery.3.5.1004.0.msi | executable | |
MD5:24D5B5CF0D9FCCB1EFE890E6F83AE700 | SHA256:4FD19FCD2BFD7EB449624099B13E154952081566A7EC02ED3D447A987C0FFE98 | |||
| 2392 | miniunz.exe | C:\ProgramData\Dell\drivers\Application_YD63W_WN32_3.5.1004.0_A00_01.EXE\mup.xml | xml | |
MD5:D05C624940A6BAF790F4B3D41982201A | SHA256:42C7030CFA5201838522D693B7254A65E92DFB036B1E7A0B92BD86B1CB99398C | |||
| 4268 | msiexec.exe | C:\Windows\Installer\10e205.msi | executable | |
MD5:24D5B5CF0D9FCCB1EFE890E6F83AE700 | SHA256:4FD19FCD2BFD7EB449624099B13E154952081566A7EC02ED3D447A987C0FFE98 | |||
| 4268 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:03FDFDBFEFFB4FE5B8D933961A6C16BC | SHA256:09A8196572F7A502E338B369B93BC68C5F809D14F3B6B3018FBC4D6C53C7A1E7 | |||
| 4268 | msiexec.exe | C:\Windows\Installer\MSIE457.tmp | executable | |
MD5:EDC4985DBC9AE14B9517FD30C4B2D7AB | SHA256:6A010A2AFD883AC1EFDE2A8544714855727146F95423FF91F5914AA85059F2A0 | |||
| 4268 | msiexec.exe | C:\Windows\Temp\~DFD8769EA70FC2BC17.TMP | binary | |
MD5:BF619EAC0CDF3F68D496EA9344137E8B | SHA256:076A27C79E5ACE2A3D47F9DD2E83E4FF6EA8872B3C2218F66C92B89B55F36560 | |||
| 4268 | msiexec.exe | C:\Windows\Temp\~DF2FA3EB21BEA4BE17.TMP | binary | |
MD5:2991B7B62B06797E979B6AFCA6ACEC49 | SHA256:87CBC9D287F9DD32805ADFF77673AAE916EC32CC4C44351DBB20E7E99F53B1B7 | |||
| 4268 | msiexec.exe | C:\Windows\Installer\inprogressinstallinfo.ipi | binary | |
MD5:2991B7B62B06797E979B6AFCA6ACEC49 | SHA256:87CBC9D287F9DD32805ADFF77673AAE916EC32CC4C44351DBB20E7E99F53B1B7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
39
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5392 | msiexec.exe | GET | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLXNCzDvBhHecWjg70iJhBW0InywQUanImetAe733nO2lR1GyNn5ASZqsCDEPBCxwAAAAAUdNz2g%3D%3D | unknown | — | — | whitelisted |
5392 | msiexec.exe | POST | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/ | unknown | — | — | whitelisted |
5392 | msiexec.exe | GET | 404 | 23.50.131.88:80 | http://crl.entrust.net/g2ca.crl | unknown | — | — | whitelisted |
5392 | msiexec.exe | GET | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSgzf9cSnJr%2BqITIlPzCwhkRjQmwQUfhofGhF0XGTJDB%2BUAav9gWQuoSwCEBgsqLeVNXMHAAAAAFVmLZw%3D | unknown | — | — | whitelisted |
5392 | msiexec.exe | POST | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/ | unknown | — | — | whitelisted |
5392 | msiexec.exe | GET | 404 | 23.50.131.88:80 | http://crl.entrust.net/ovcs1.crl | unknown | — | — | whitelisted |
4268 | msiexec.exe | GET | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTLXNCzDvBhHecWjg70iJhBW0InywQUanImetAe733nO2lR1GyNn5ASZqsCDEPBCxwAAAAAUdNz2g%3D%3D | unknown | — | — | whitelisted |
4268 | msiexec.exe | GET | 404 | 23.50.131.88:80 | http://crl.entrust.net/g2ca.crl | unknown | — | — | whitelisted |
4268 | msiexec.exe | POST | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/ | unknown | — | — | whitelisted |
4268 | msiexec.exe | GET | 404 | 69.192.162.201:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTSgzf9cSnJr%2BqITIlPzCwhkRjQmwQUfhofGhF0XGTJDB%2BUAav9gWQuoSwCEBgsqLeVNXMHAAAAAFVmLZw%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2112 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.17:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5392 | msiexec.exe | 69.192.162.201:80 | ocsp.entrust.net | AKAMAI-AS | DE | whitelisted |
5392 | msiexec.exe | 23.50.131.88:80 | crl.entrust.net | Akamai International B.V. | DE | whitelisted |
4268 | msiexec.exe | 69.192.162.201:80 | ocsp.entrust.net | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.entrust.net |
| whitelisted |
crl.entrust.net |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
198.187.3.20.in-addr.arpa |
| unknown |
6.0.1.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.0.7.0.0.0.0.3.0.1.3.0.6.2.ip6.arpa |
| unknown |