| File name: | http://informatioshopname.ru/partiya/malashop.exe |
| Full analysis: | https://app.any.run/tasks/788bab3f-41b0-42f1-ae90-321bfca7c4da |
| Verdict: | Malicious activity |
| Analysis date: | July 17, 2019, 16:22:54 |
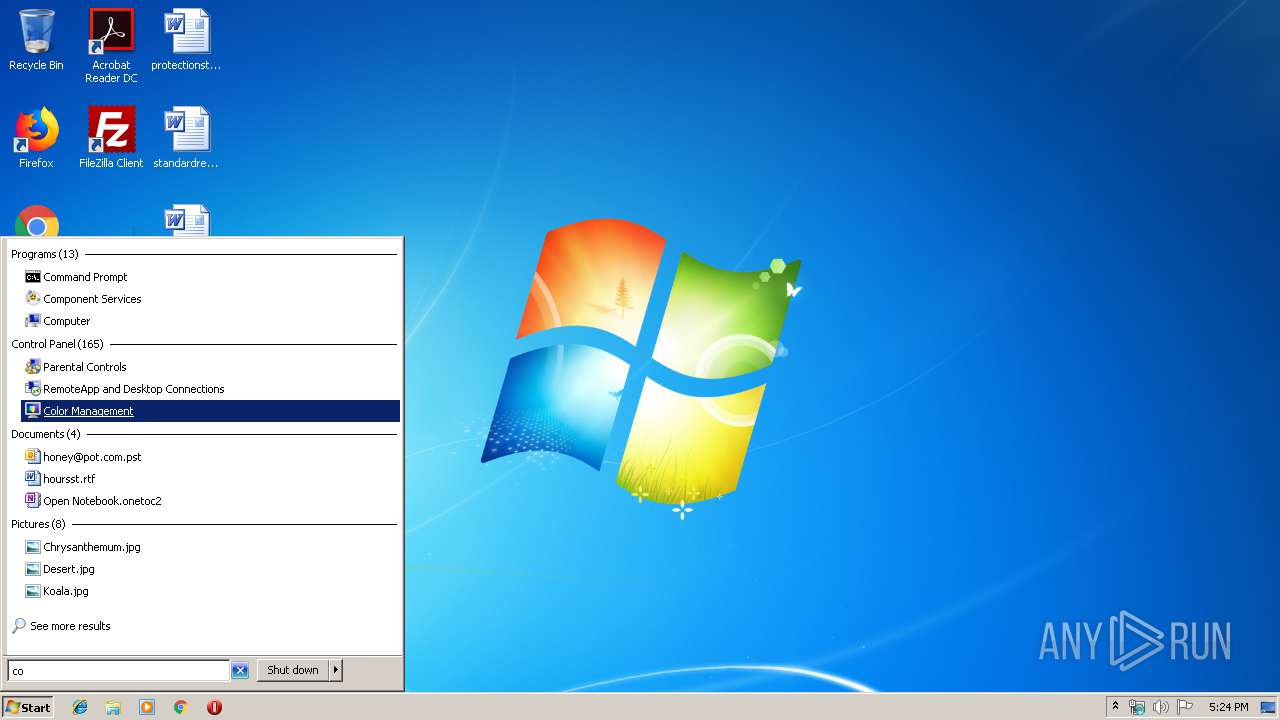
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 21B8EBED4DE64207DEDD935D8441E803 |
| SHA1: | 9782D3FCE822EBD2134F21189446F45D5FBE4BA6 |
| SHA256: | 2B3F9DF82BCC1235ED14C374D3967567F1EDB5AACADF5AB529DEDFC9B2D7F76F |
| SSDEEP: | 3072:WByUw+TkgRsyR3UhQxw8BHMj0SEp47r29l1fwo1x2TNl:WByUDnS24Q9ZMZEpQr2Zwo1x2z |
MALICIOUS
Loads dropped or rewritten executable
- svchost.exe (PID: 1260)
- windanr.exe (PID: 2728)
- malashop.exe (PID: 3484)
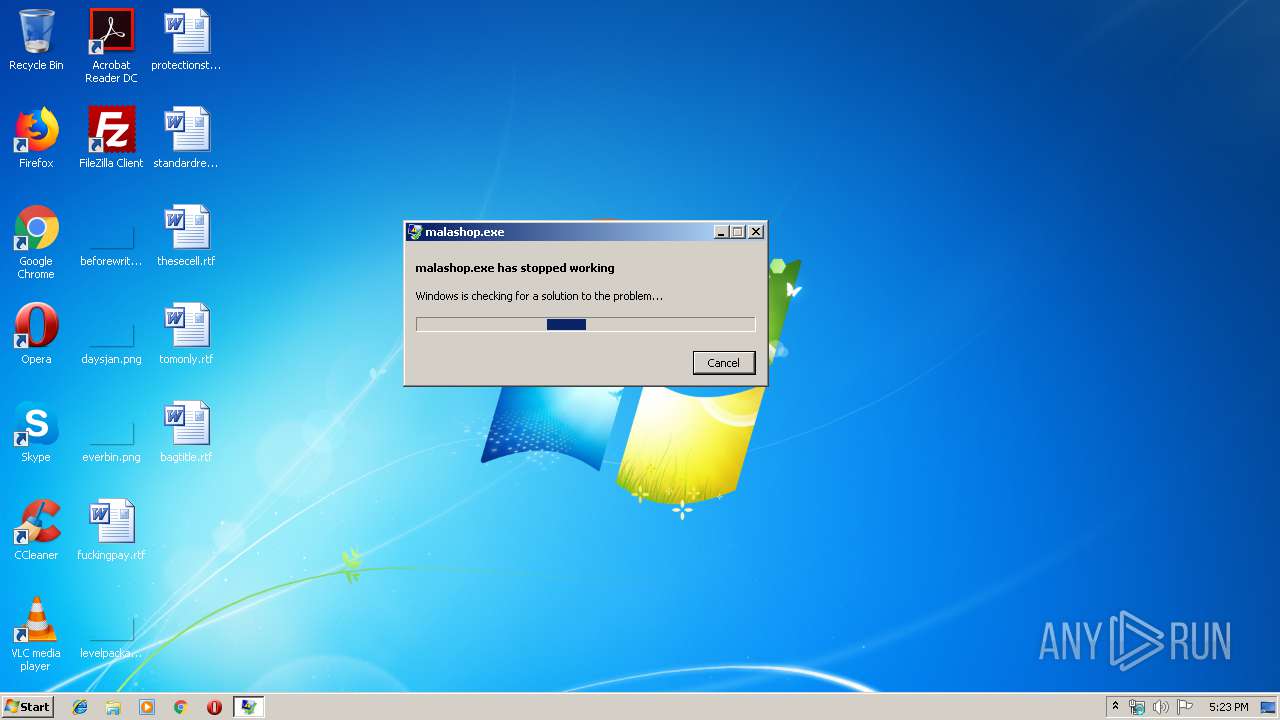
- WerFault.exe (PID: 2336)
- SearchProtocolHost.exe (PID: 2724)
SUSPICIOUS
Executable content was dropped or overwritten
- malashop.exe (PID: 3484)
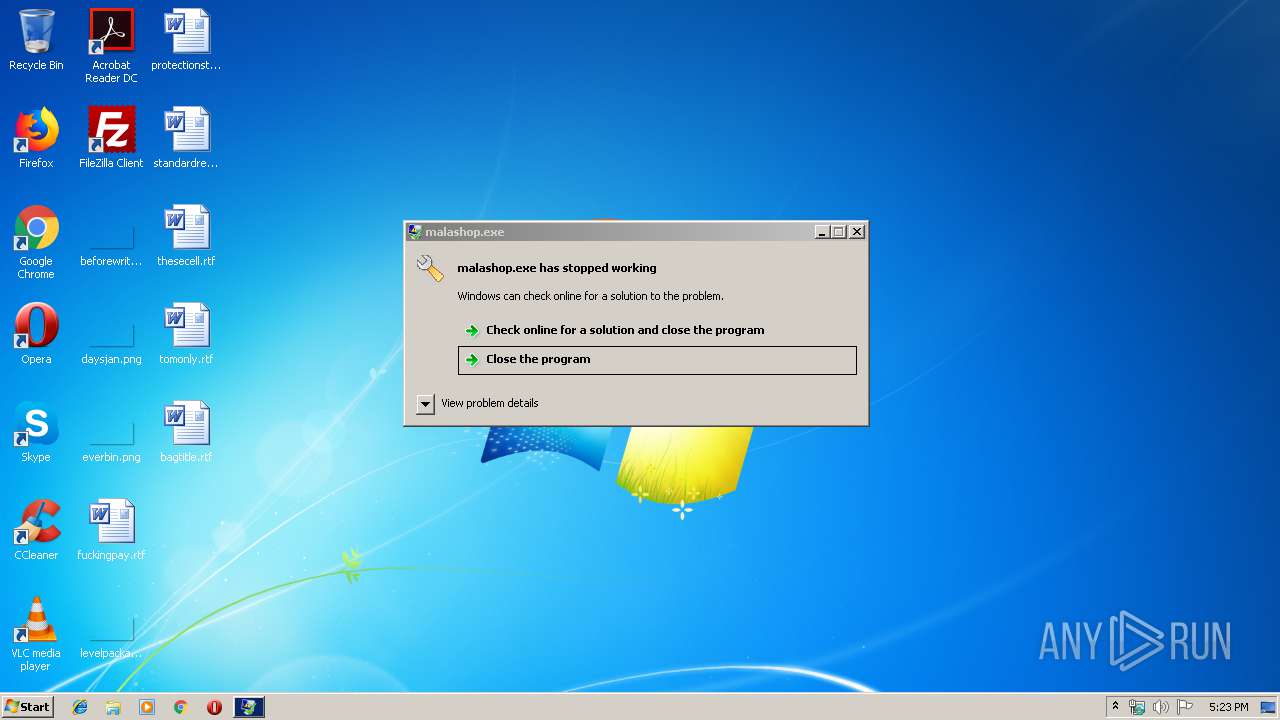
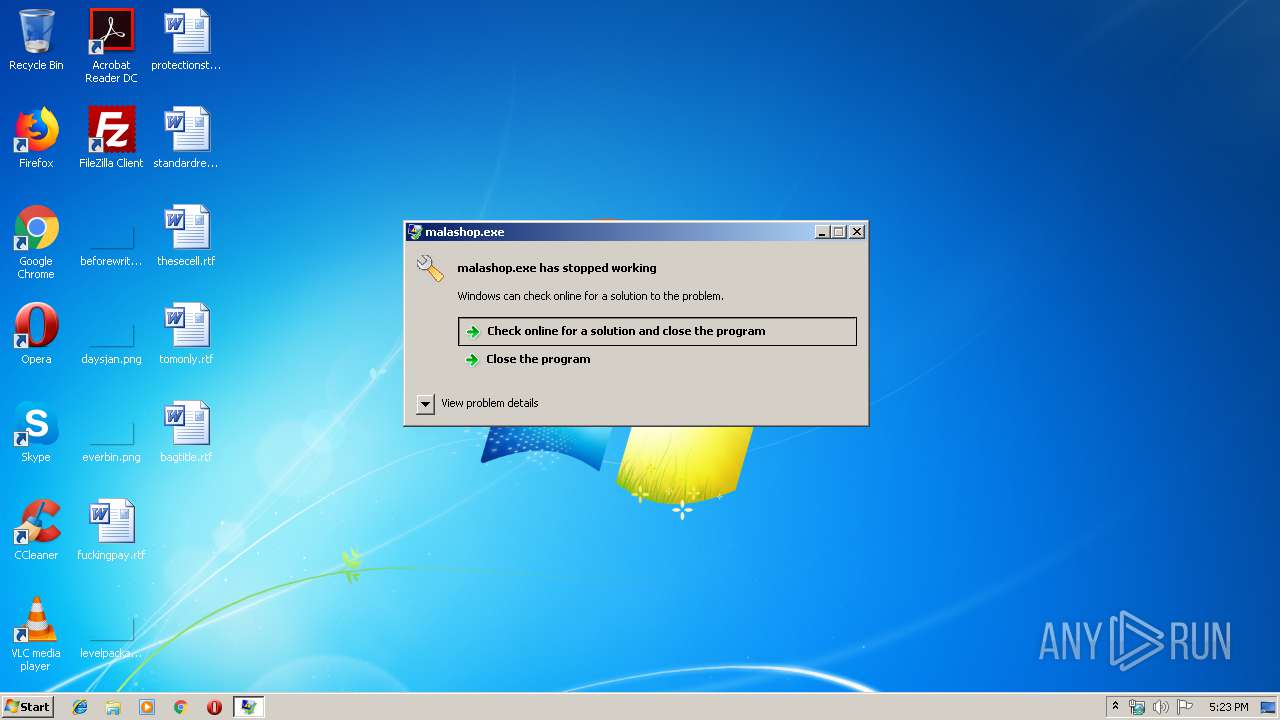
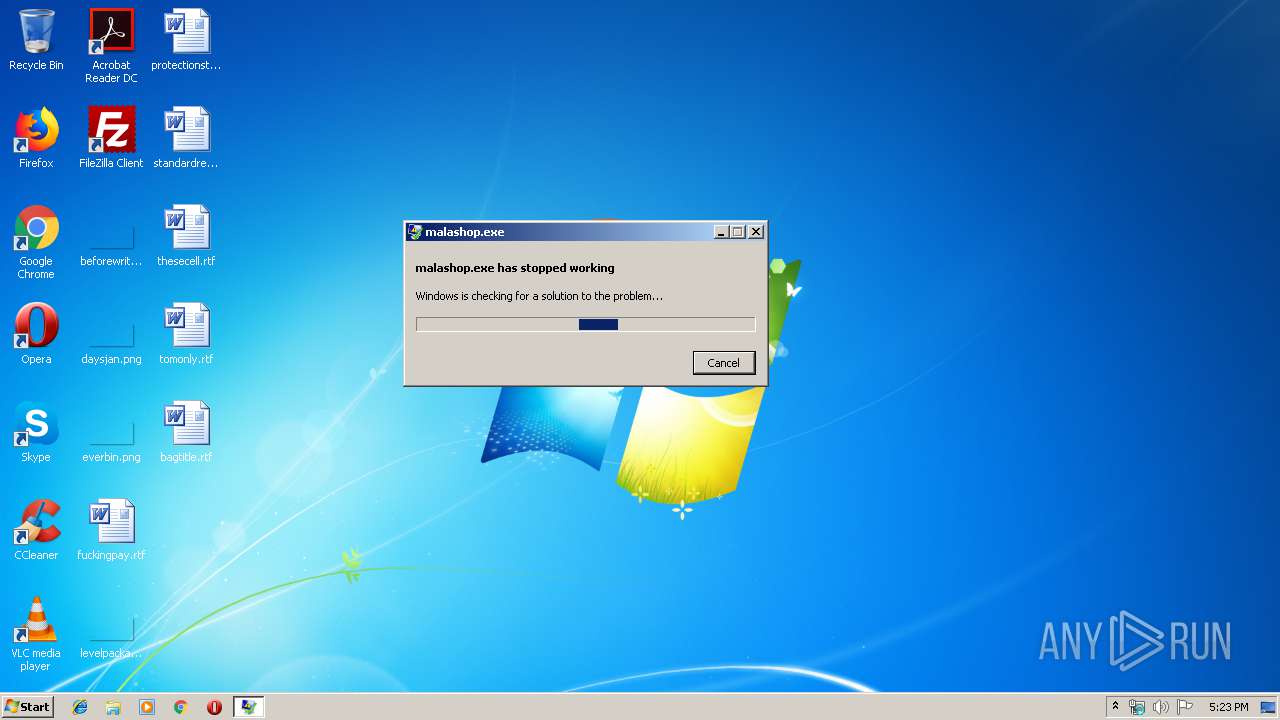
INFO
Application was crashed
- malashop.exe (PID: 3484)
Reads Microsoft Office registry keys
- SearchProtocolHost.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Clipper DOS Executable (2.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:22 00:06:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 146432 |
| InitializedDataSize: | 818688 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1a0a2 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 21-Jun-2018 22:06:50 |
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 21-Jun-2018 22:06:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00023A29 | 0x00023C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.09347 |
.rdata | 0x00025000 | 0x00003A74 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.56262 |
.data | 0x00029000 | 0x000AAB78 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.1897 |
.idata | 0x000D4000 | 0x00001BB9 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.75078 |
.teni | 0x000D6000 | 0x00000A99 | 0x00000C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x000D7000 | 0x0001632C | 0x00016400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34631 |
.reloc | 0x000EE000 | 0x00001484 | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 3.77694 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.93612 | 2216 | UNKNOWN | UNKNOWN | RT_ICON |
2 | 4.27916 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.80088 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.73167 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 6.46137 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.11676 | 3752 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.01053 | 1736 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 3.23725 | 1384 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 4.28123 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
10 | 5.14541 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
Imports
KERNEL32.dll |
Total processes
35
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1260 | C:\Windows\System32\svchost.exe -k WerSvcGroup | C:\Windows\System32\svchost.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | C:\Windows\system32\WerFault.exe -u -p 3484 -s 96 | C:\Windows\system32\WerFault.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10009_ Global\UsGthrCtrlFltPipeMssGthrPipe_S-1-5-21-1302019708-1500728564-335382590-10009 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" "1" | C:\Windows\system32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2728 | "windanr.exe" | C:\Windows\system32\windanr.exe | — | qemu-ga.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3484 | "C:\Users\admin\AppData\Local\Temp\malashop.exe" | C:\Users\admin\AppData\Local\Temp\malashop.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221225477 Modules
| |||||||||||||||
Total events
128
Read events
105
Write events
23
Delete events
0
Modification events
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | APPSTARTING |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | ARROW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | CROSS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HAND |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | HELP |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | IBEAM |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | NO |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZEALL |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENESW |
Value: %SystemRoot%\cursors\clearcur.cur | |||
| (PID) Process: | (2728) windanr.exe | Key: | HKEY_CURRENT_USER\Control Panel\Cursors |
| Operation: | write | Name: | SIZENS |
Value: %SystemRoot%\cursors\clearcur.cur | |||
Executable files
1
Suspicious files
1
Text files
5
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER6688.tmp.mdmp | — | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WERE455.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_malashop.exe_de6458a8ebc15883c85f4bff3a8fae858db864c_cab_093866c3\WER654D.tmp.appcompat.txt | xml | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\malashop.exe.3484.dmp | dmp | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_malashop.exe_de6458a8ebc15883c85f4bff3a8fae858db864c_cab_093866c3\WERE455.tmp.WERInternalMetadata.xml | xml | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_malashop.exe_de6458a8ebc15883c85f4bff3a8fae858db864c_cab_093866c3\WER6688.tmp.mdmp | dmp | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER654D.tmp.appcompat.txt | xml | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_malashop.exe_de6458a8ebc15883c85f4bff3a8fae858db864c_cab_093866c3\WER660A.tmp.hdmp | dmp | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\WER\ReportQueue\AppCrash_malashop.exe_de6458a8ebc15883c85f4bff3a8fae858db864c_cab_093866c3\Report.wer | binary | |
MD5:— | SHA256:— | |||
| 2336 | WerFault.exe | C:\Users\admin\AppData\Local\Temp\WER660A.tmp.hdmp | dmp | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2336 | WerFault.exe | GET | — | 20.44.86.127:80 | http://watson.microsoft.com/StageOne/Generic/BEX/malashop_exe/0_0_0_0/5d1c981c/StackHash_0a9e/0_0_0_0/00000000/0012f51c/c0000005/00000008.htm?LCID=1033&OS=6.1.7601.2.00010100.1.0.48.17514&SM=DELL&SPN=DELL&BV=DELL&MID=3ADE2C42-4AB9-49B7-B142-BE9AEEA69063 | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2336 | WerFault.exe | 20.44.86.127:80 | watson.microsoft.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
watson.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2336 | WerFault.exe | Potential Corporate Privacy Violation | ET POLICY Application Crash Report Sent to Microsoft |
2336 | WerFault.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |