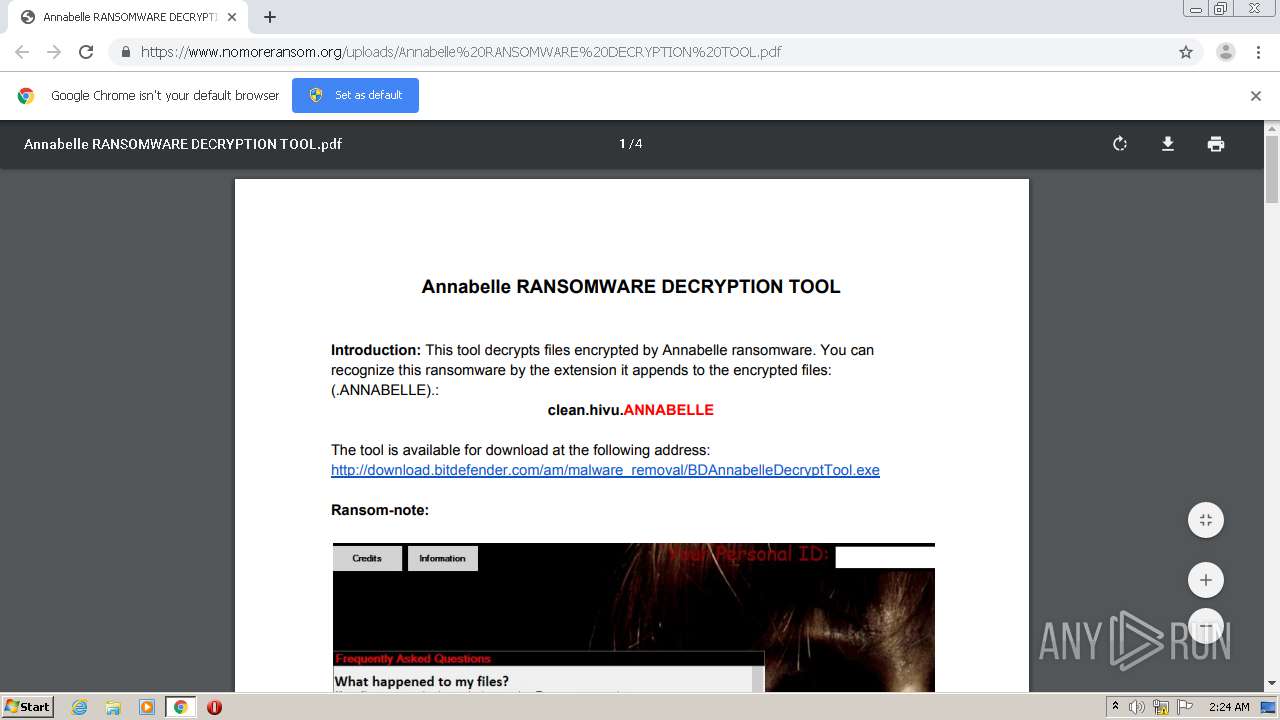
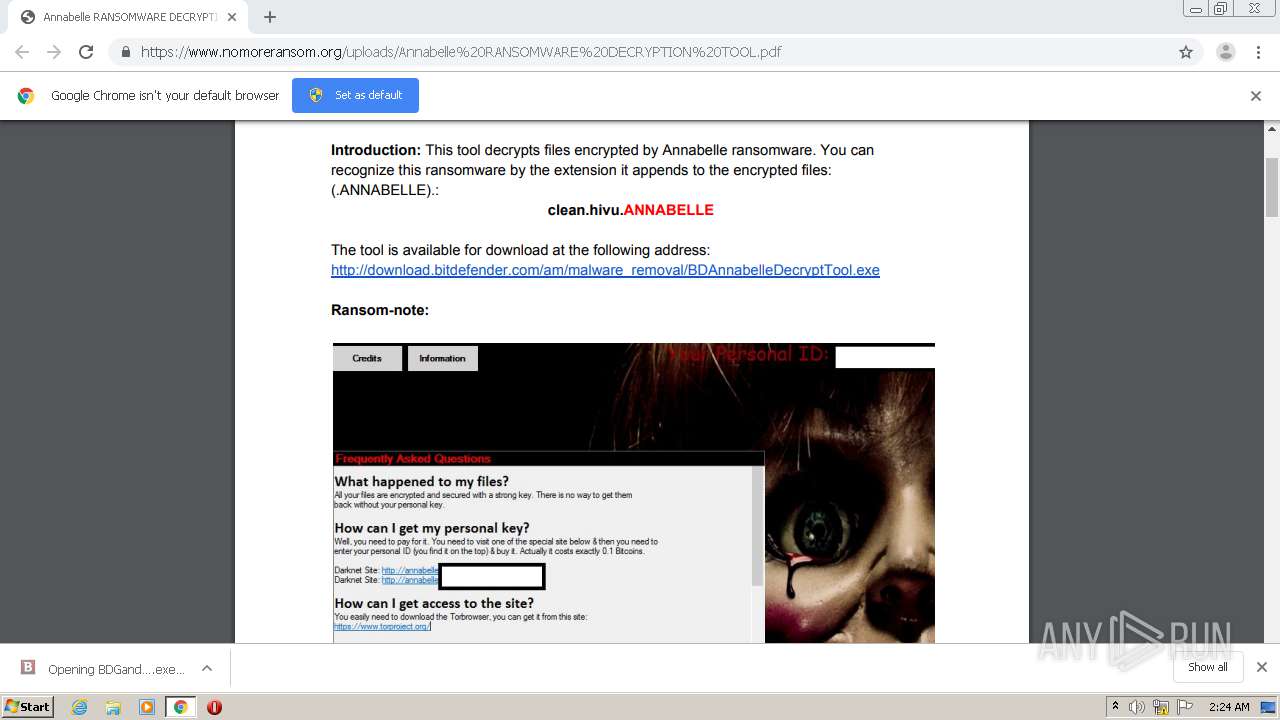
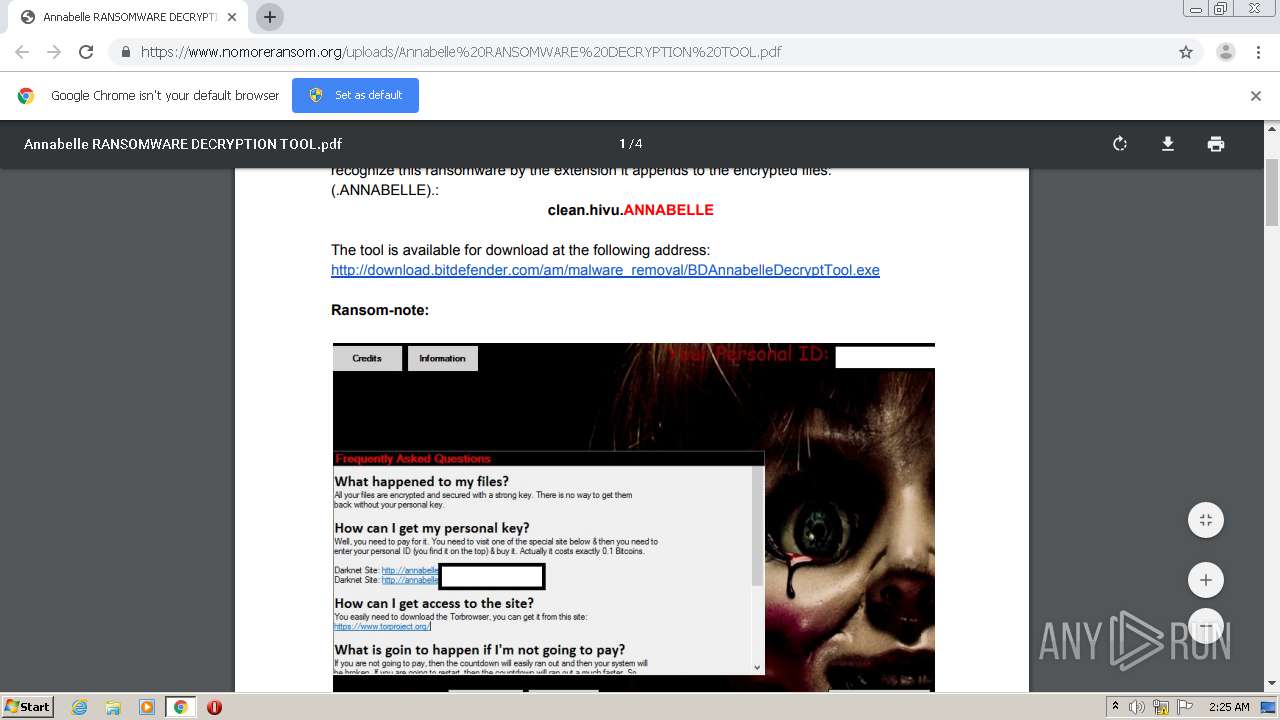
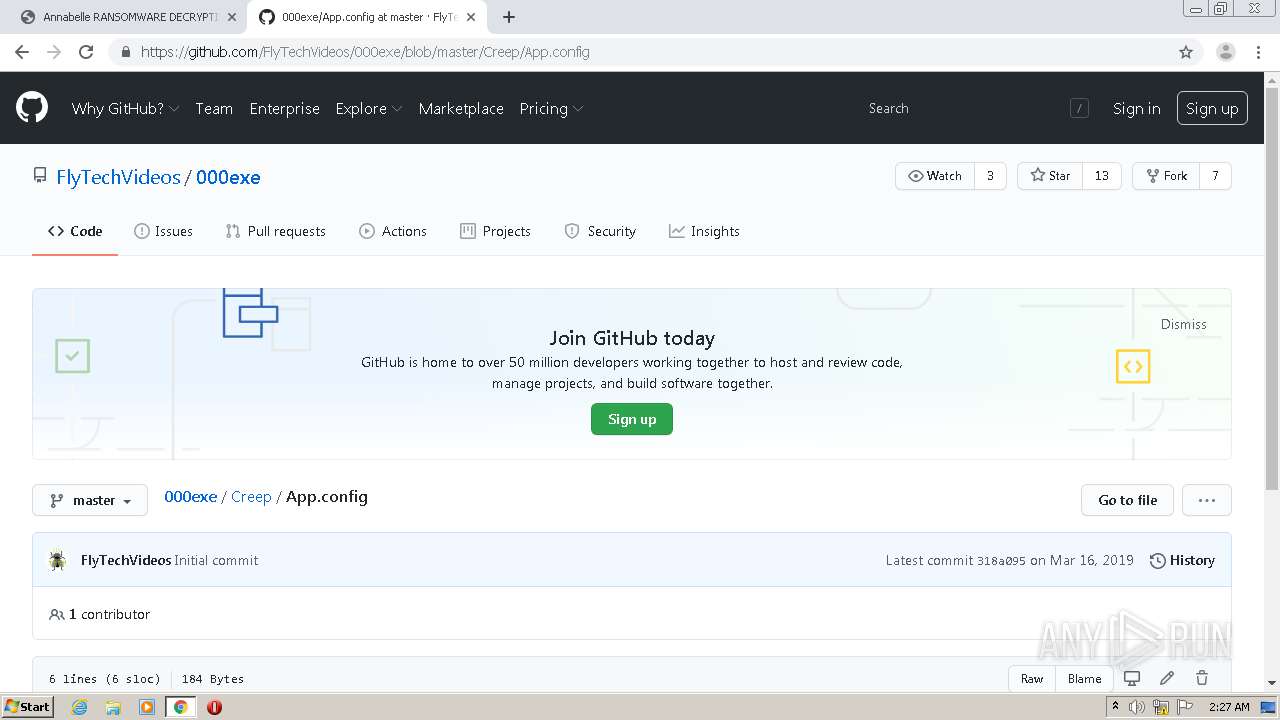
| URL: | https://www.nomoreransom.org/uploads/Annabelle%20RANSOMWARE%20DECRYPTION%20TOOL.pdf |
| Full analysis: | https://app.any.run/tasks/32a29f2f-a459-4394-b070-93c2469e107d |
| Verdict: | Malicious activity |
| Analysis date: | November 30, 2020, 02:24:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 0D8C6546EF61E710322C15EACB84C689 |
| SHA1: | 9B3A3892CDCEF08B12674CF78312409CE732DEB2 |
| SHA256: | 2B34AE69D9BCBD7ABA0F0A362D9FED754CC83A90884ACD0BF6834CA2184051BB |
| SSDEEP: | 3:N8DSL+baLKSP20a3gAFhL8KxRlVBD:2OL+bADo3g2LJLlVBD |
MALICIOUS
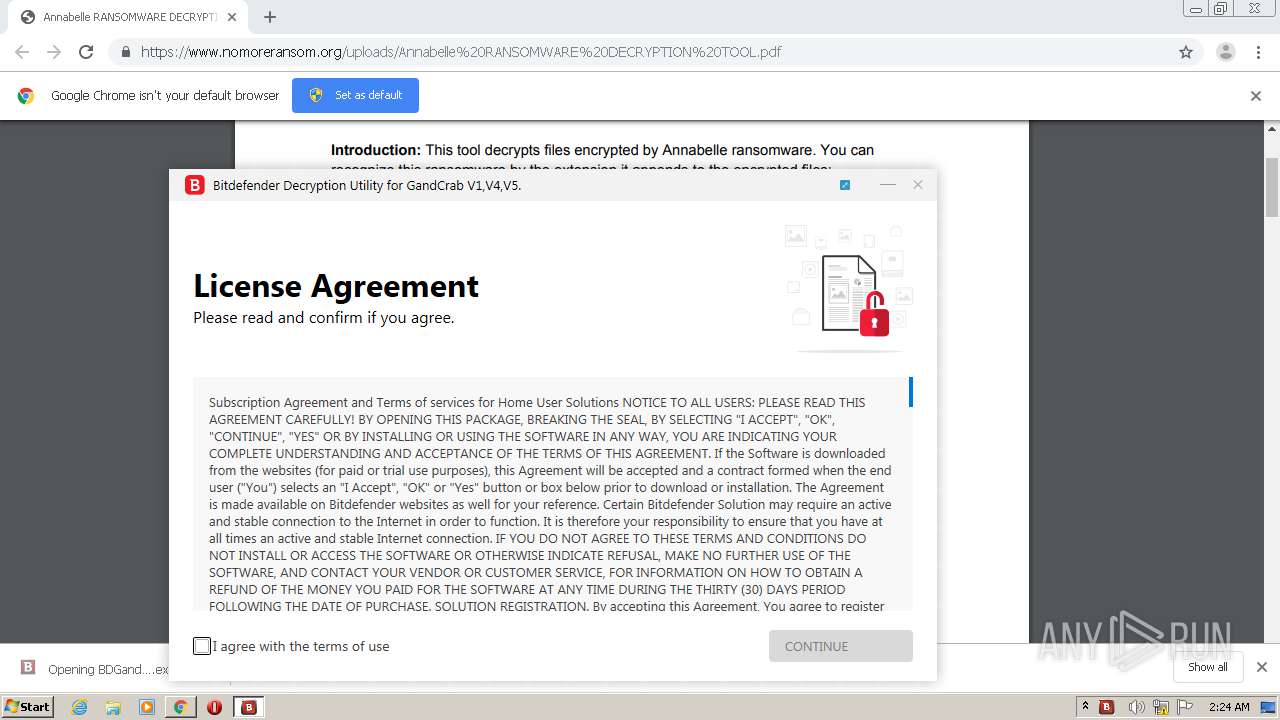
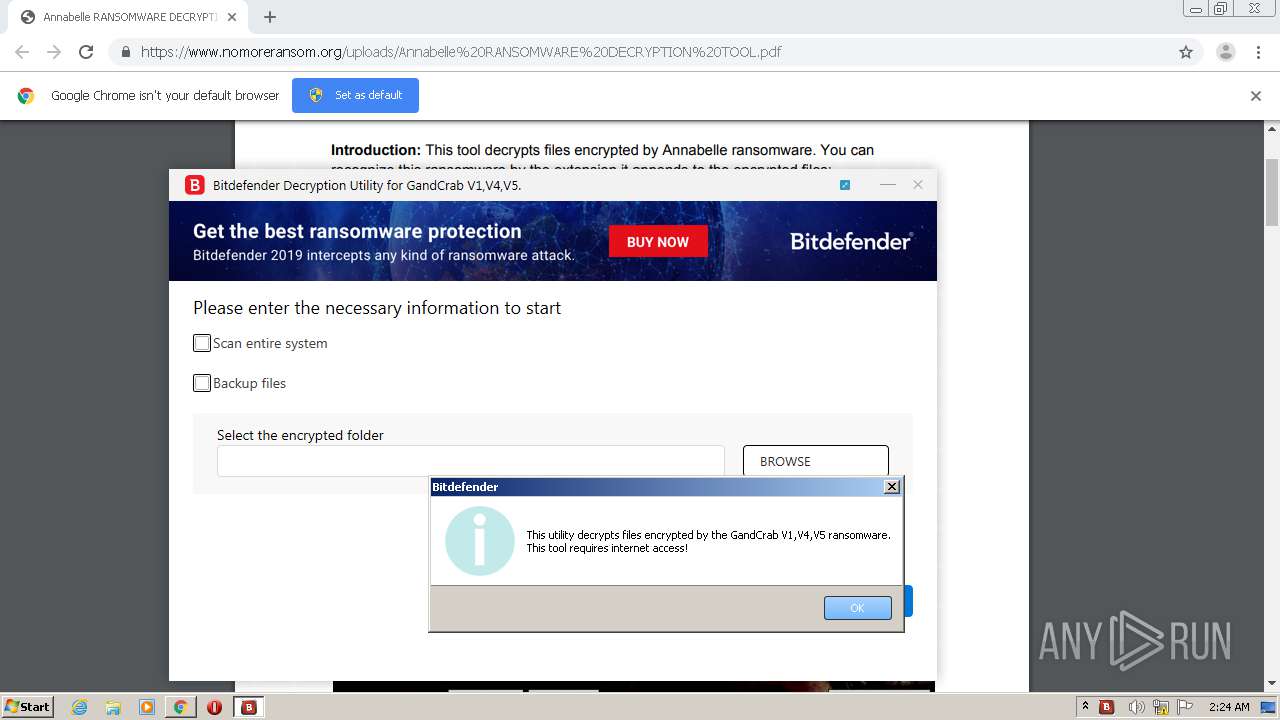
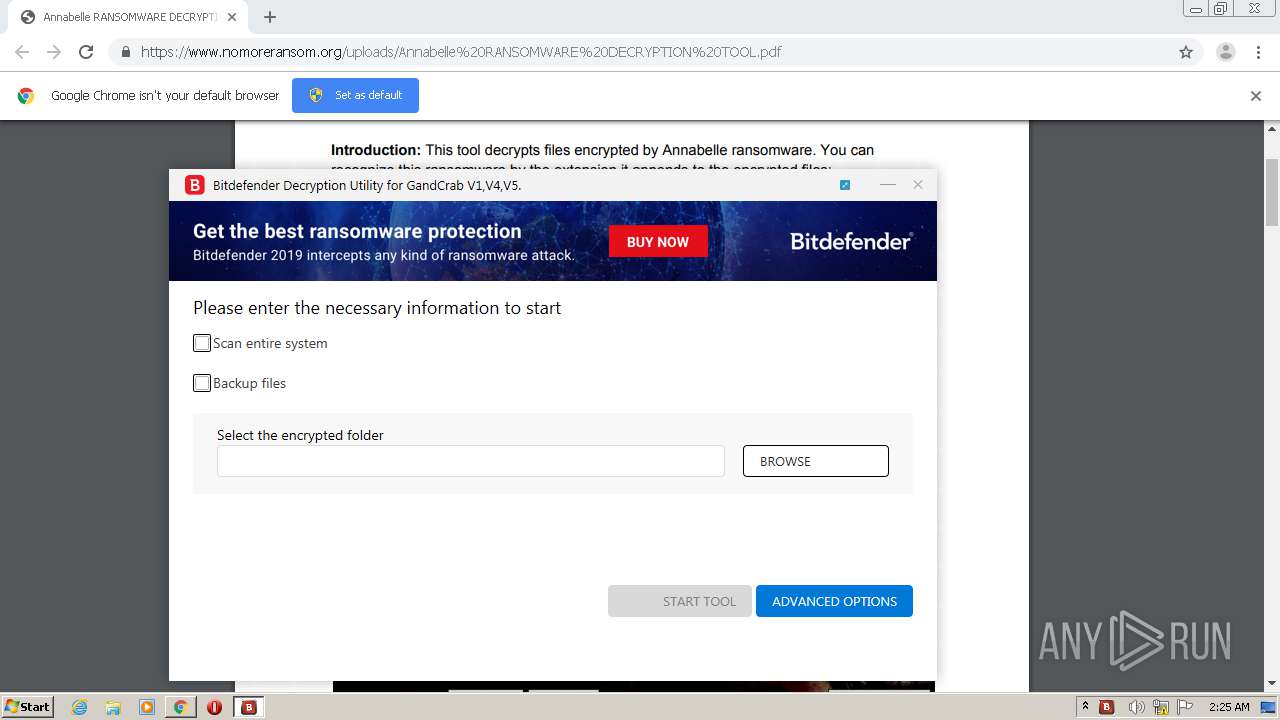
Application was dropped or rewritten from another process
- BDGandCrabDecryptTool.exe (PID: 3120)
- BDGandCrabDecryptTool.exe (PID: 2504)
- BDRansomDecryptor.exe (PID: 3668)
- BDRemovalToolLauncher_x86.exe (PID: 920)
Drops executable file immediately after starts
- BDGandCrabDecryptTool.exe (PID: 3120)
- BDRemovalToolLauncher_x86.exe (PID: 920)
Loads dropped or rewritten executable
- BDRansomDecryptor.exe (PID: 3668)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2784)
- BDRemovalToolLauncher_x86.exe (PID: 920)
- BDGandCrabDecryptTool.exe (PID: 3120)
Drops a file with a compile date too recent
- chrome.exe (PID: 2784)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 2784)
- BDRemovalToolLauncher_x86.exe (PID: 920)
INFO
Reads the hosts file
- chrome.exe (PID: 2784)
- chrome.exe (PID: 2576)
Application launched itself
- chrome.exe (PID: 2784)
Creates files in the user directory
- chrome.exe (PID: 2784)
Reads settings of System Certificates
- chrome.exe (PID: 2576)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
76
Monitored processes
37
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2369643993366006111 --renderer-client-id=25 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4412 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 920 | "BDRemovalToolLauncher_x86.exe" | C:\Users\admin\AppData\Local\Temp\BDUnifiedLauncher\BDRemovalToolLauncher_x86.exe | BDGandCrabDecryptTool.exe | ||||||||||||
User: admin Company: Bitdefender LLC Integrity Level: HIGH Description: Bitdefender Tool Exit code: 1 Version: 1,0,1,5 Modules
| |||||||||||||||
| 1196 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=1712822461256224293 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2344 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1260 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=282766884022086342 --renderer-client-id=13 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1804 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14574884758002873138 --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1492 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=535029067562643711 --mojo-platform-channel-handle=1044 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6346088719992531747 --mojo-platform-channel-handle=4124 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2244 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=5389882526057673855 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3884 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2300 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9202785892689443244 --renderer-client-id=12 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3224 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2348 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1000,661175576690612383,16062675059935731539,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=14964272480881158159 --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4364 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
955
Read events
874
Write events
78
Delete events
3
Modification events
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2560) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2784-13251176664189375 |
Value: 259 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (2784) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
9
Suspicious files
123
Text files
145
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FC457D8-AE0.pma | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c0a3ac82-ddf9-42d5-89e0-8d9b65683339.tmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF18d2ac.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF18d2ac.TMP | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2784 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF18d472.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
104
DNS requests
68
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
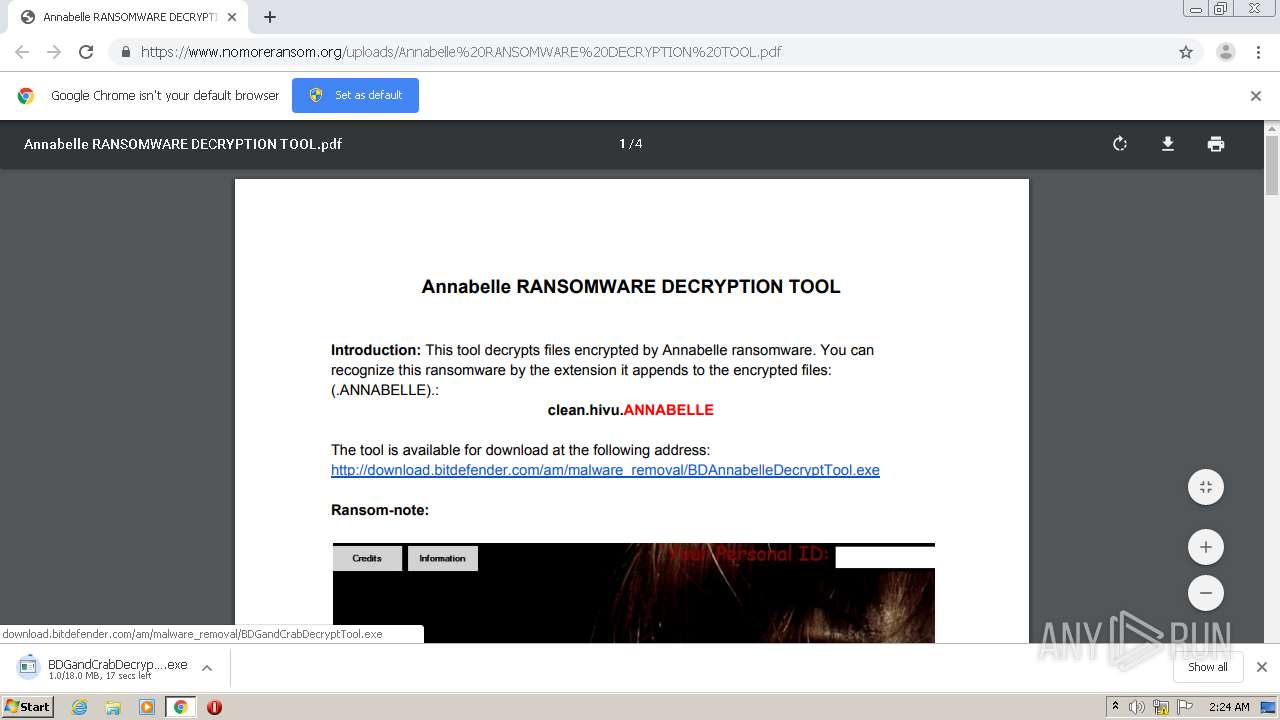
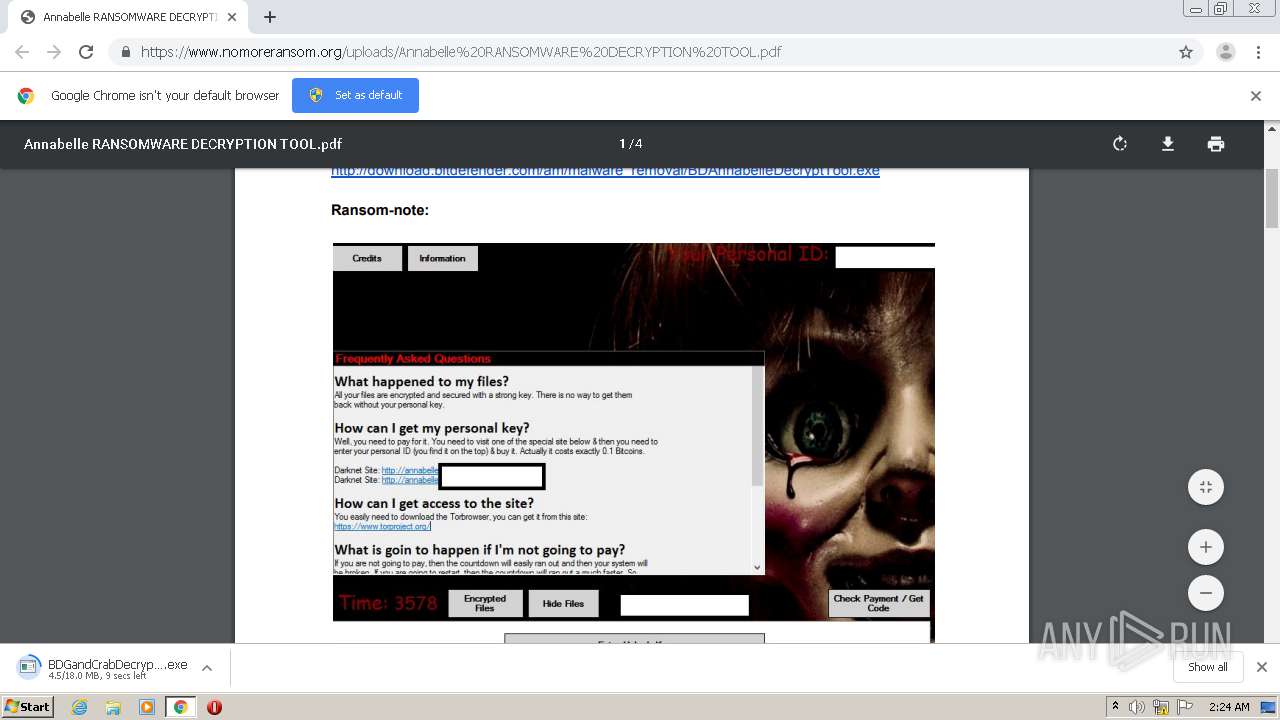
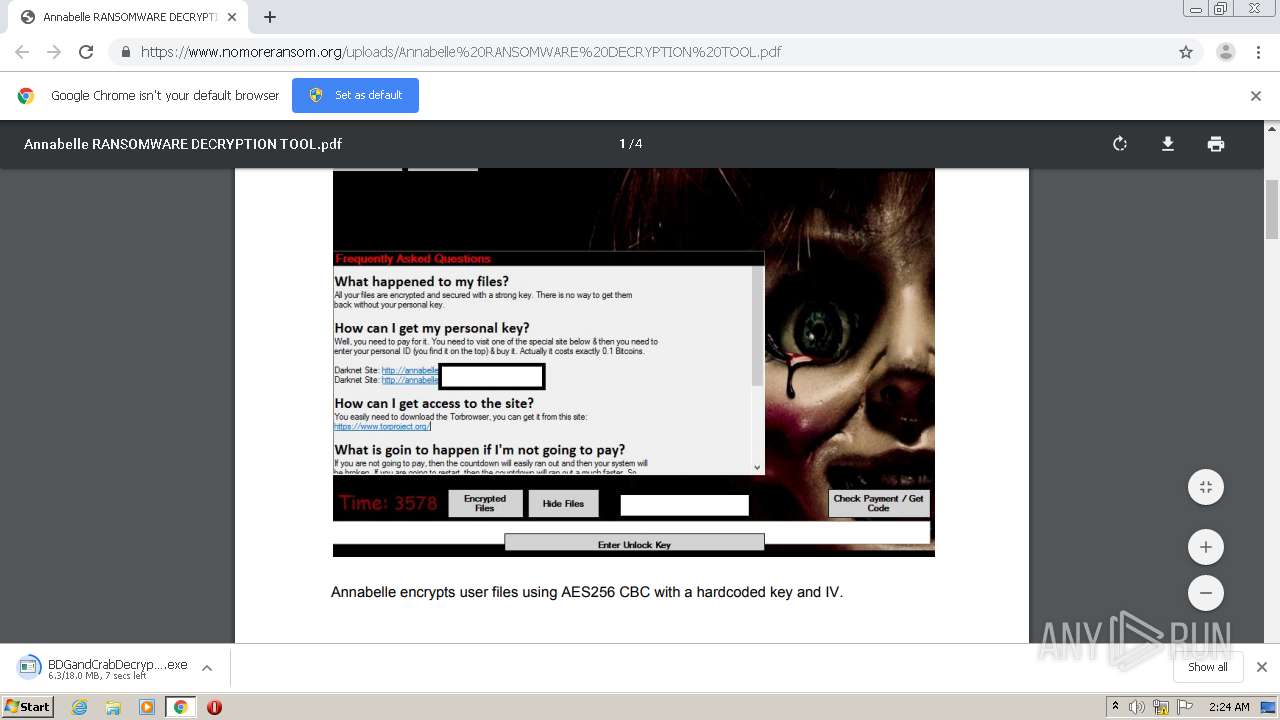
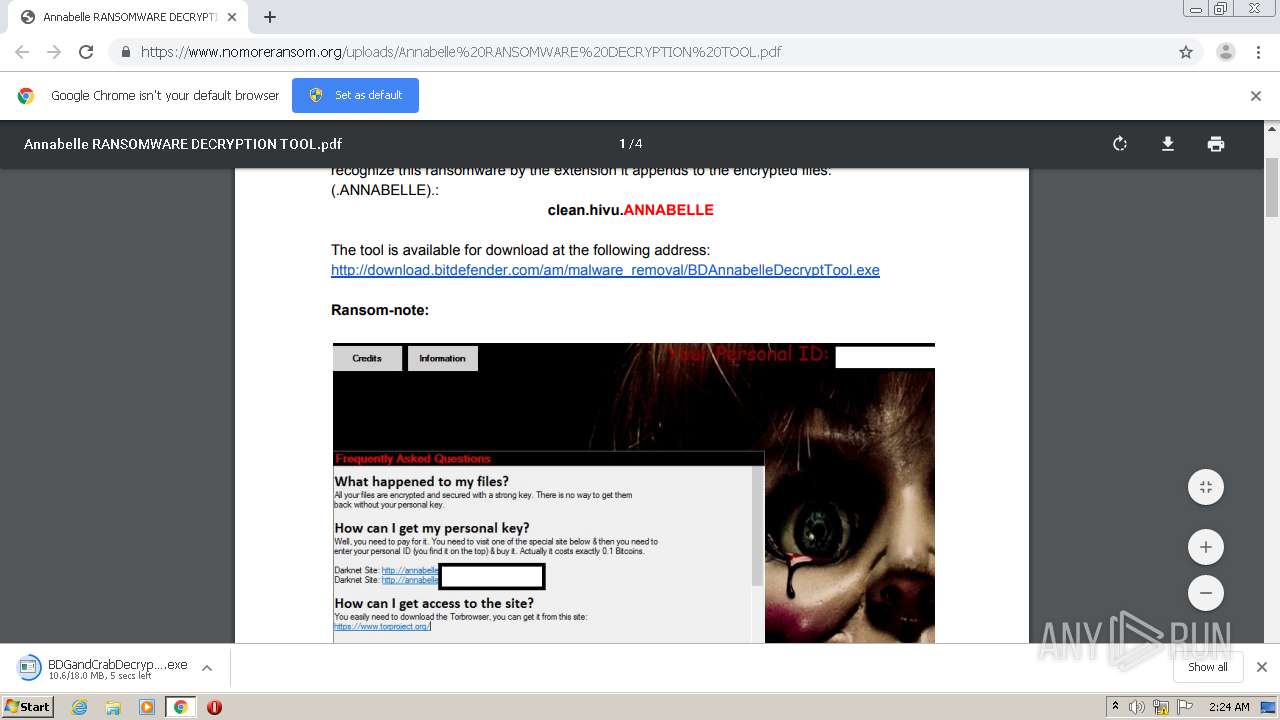
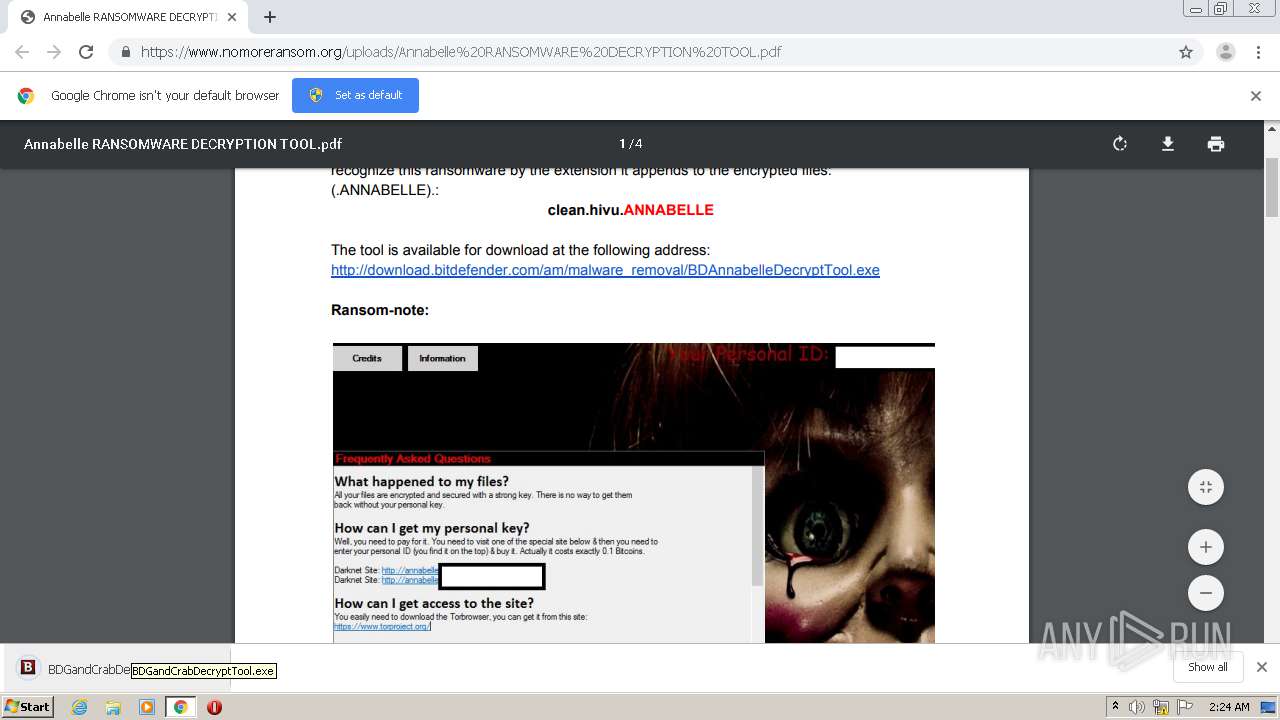
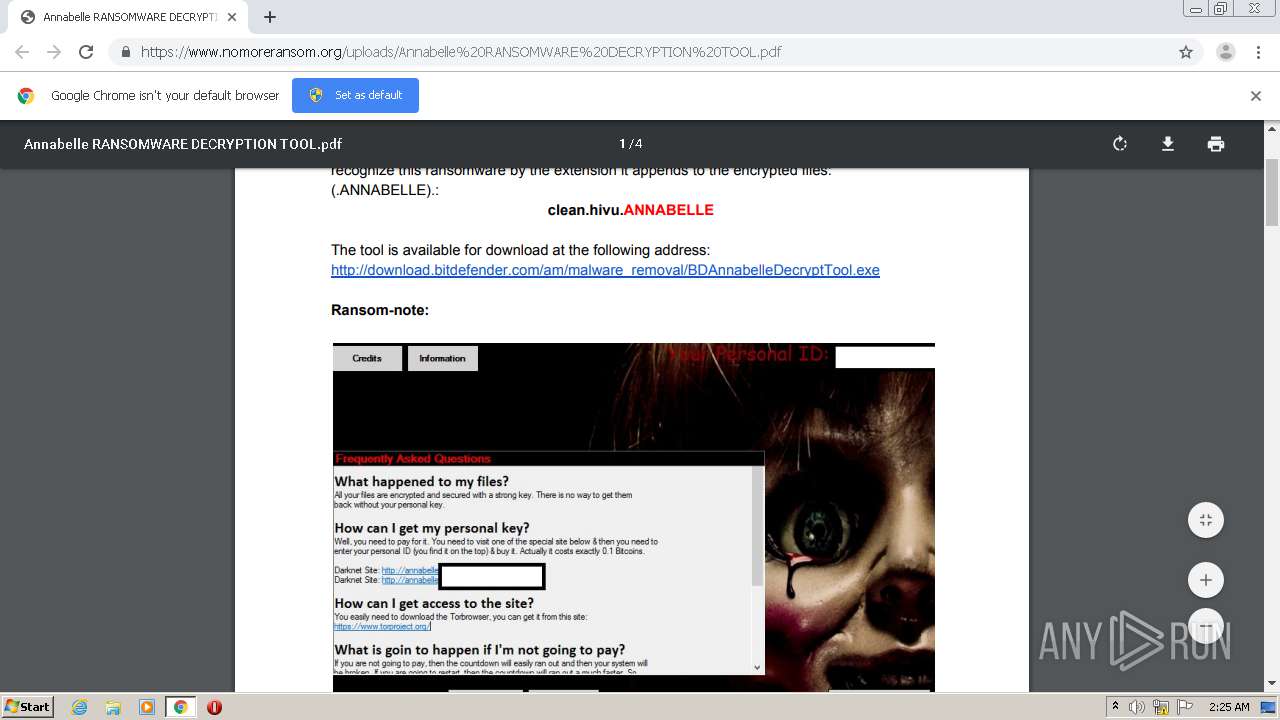
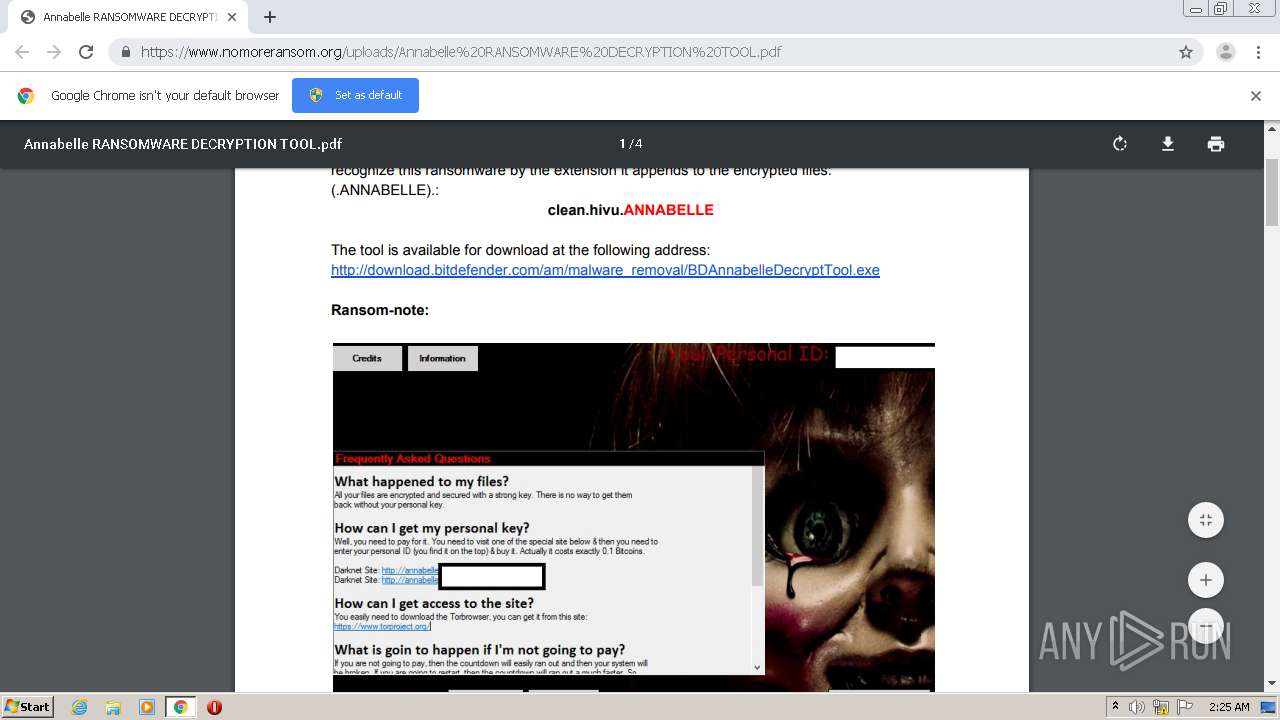
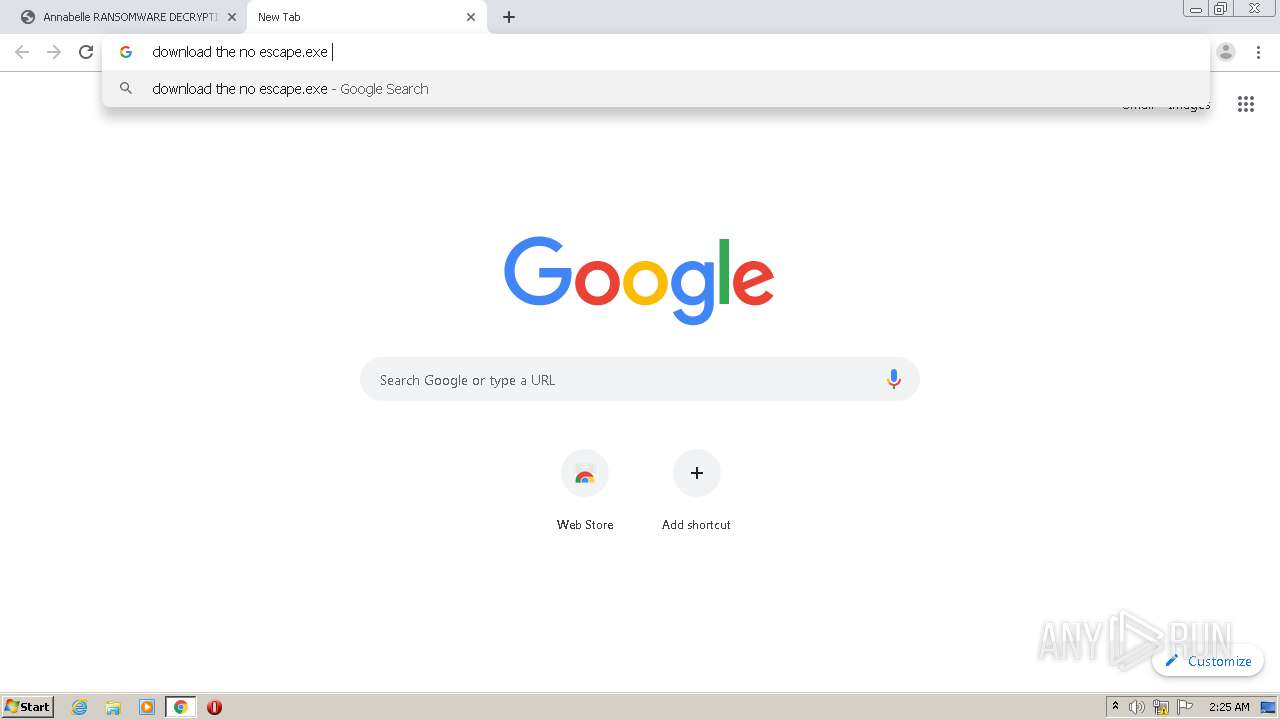
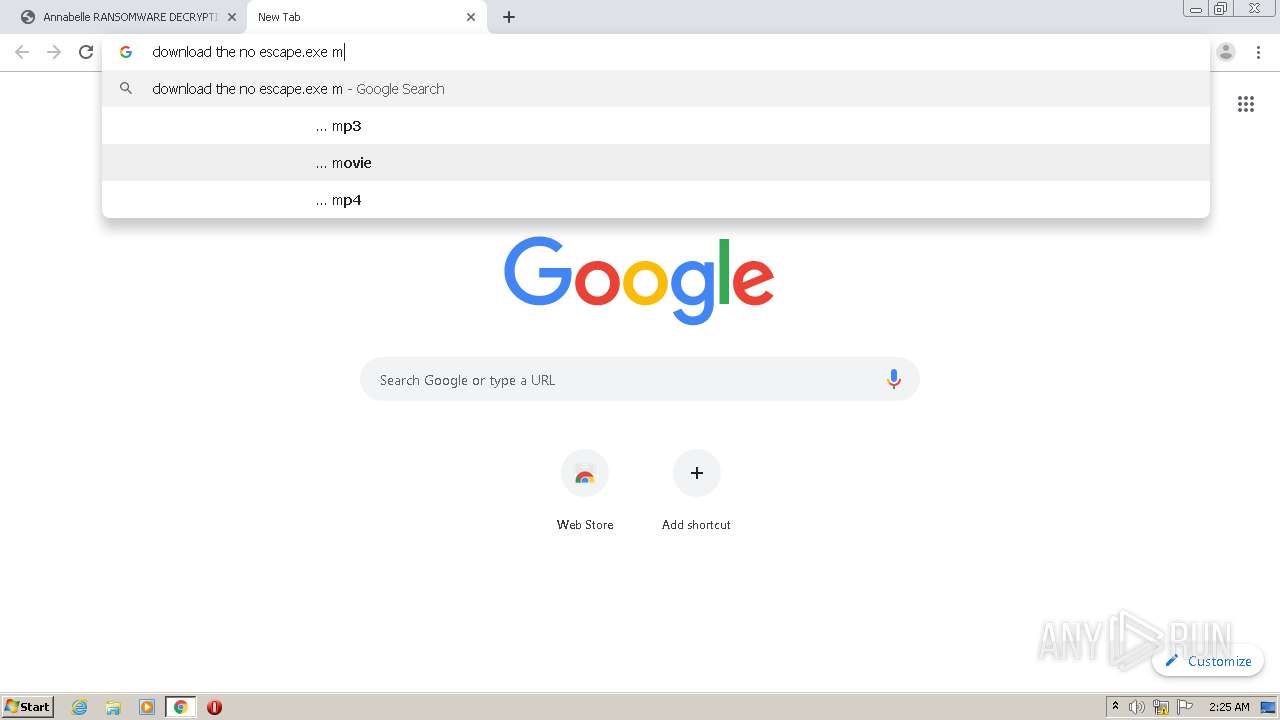
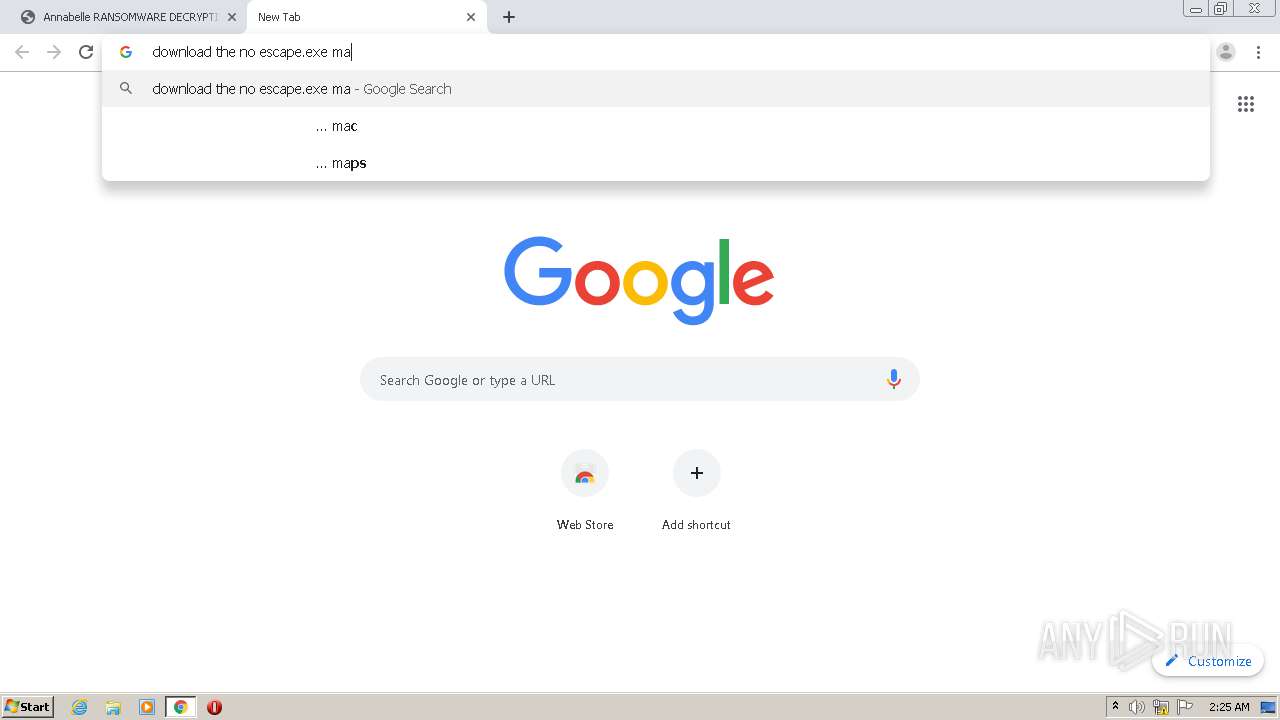
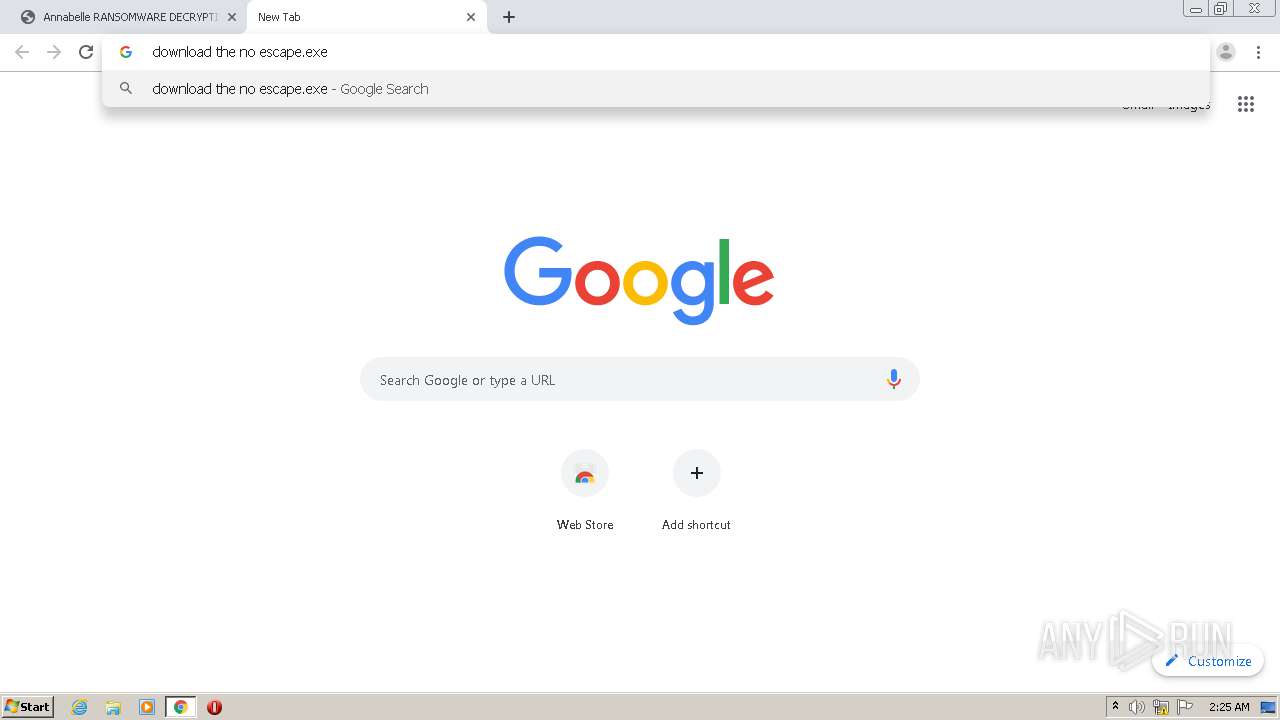
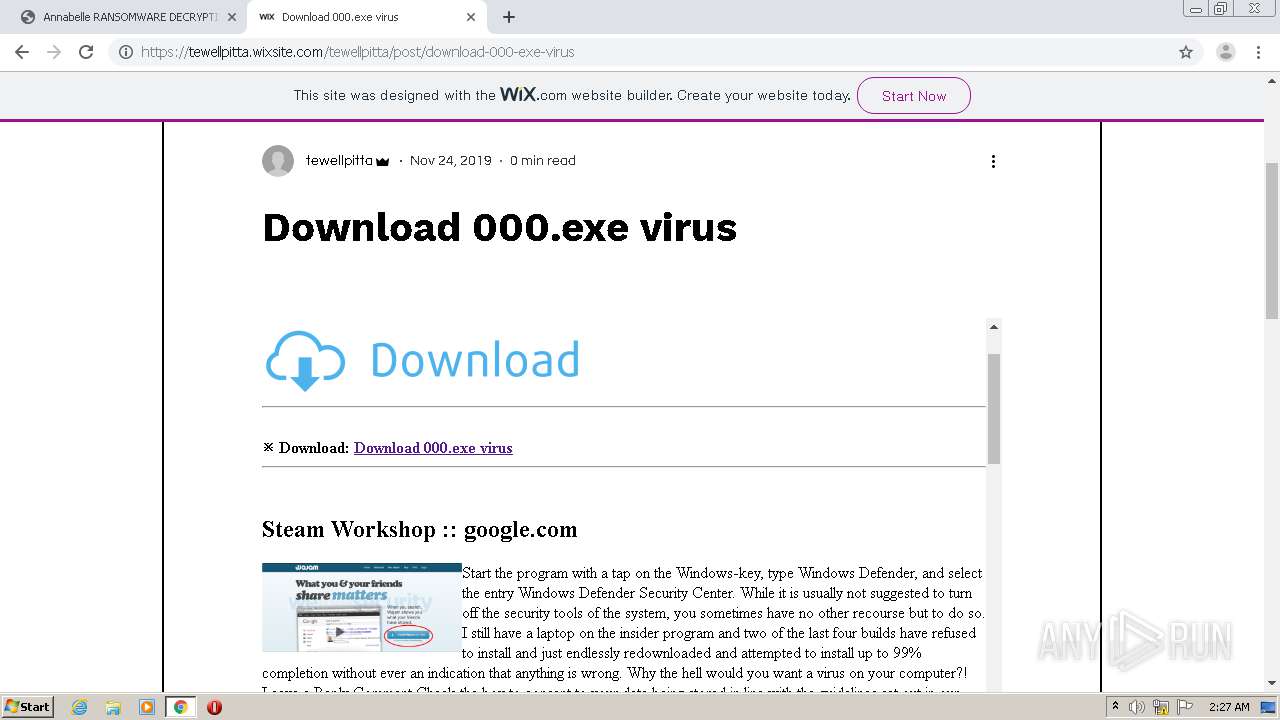
2576 | chrome.exe | GET | — | 192.229.220.142:80 | http://download.bitdefender.com/am/malware_removal/BDGandCrabDecryptTool.exe | US | — | — | suspicious |
2576 | chrome.exe | GET | 206 | 192.229.220.142:80 | http://download.bitdefender.com/am/malware_removal/BDGandCrabDecryptTool.exe | US | binary | 11.6 Mb | suspicious |
2576 | chrome.exe | GET | 200 | 192.0.77.2:80 | http://i0.wp.com/i.stack.imgur.com/inKsm.png?quality=80&strip=all | US | image | 18.7 Kb | whitelisted |
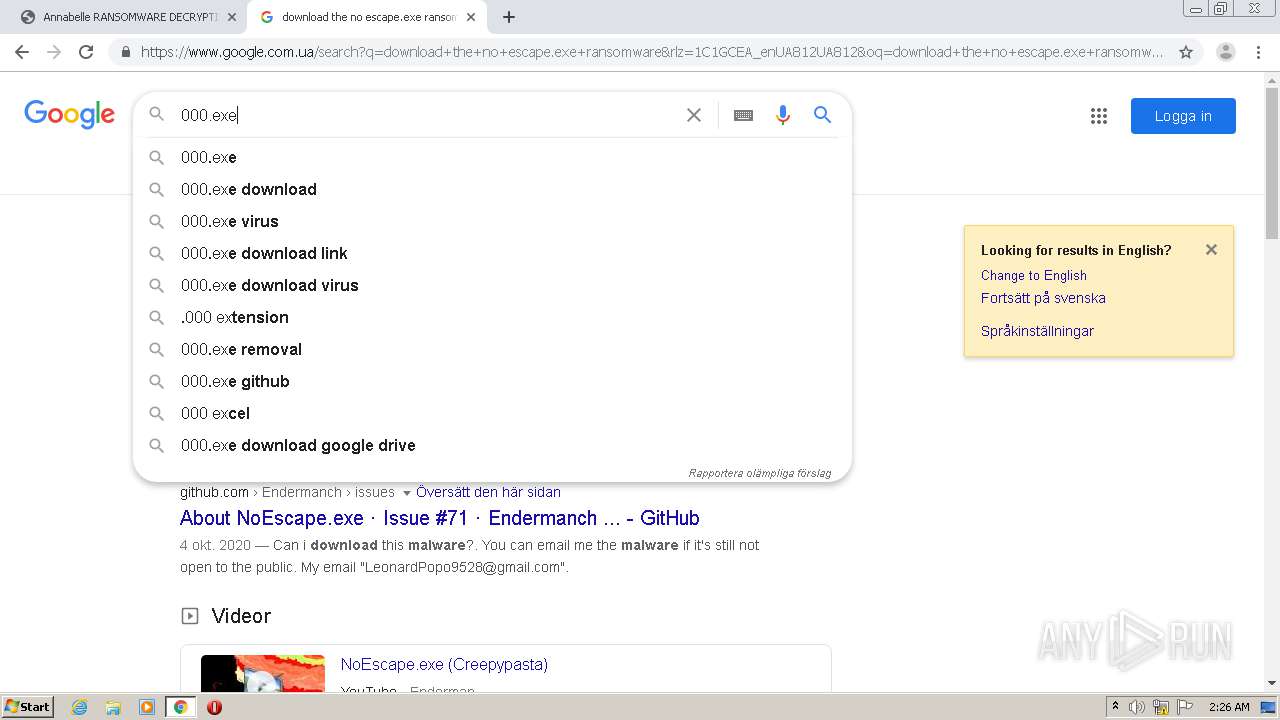
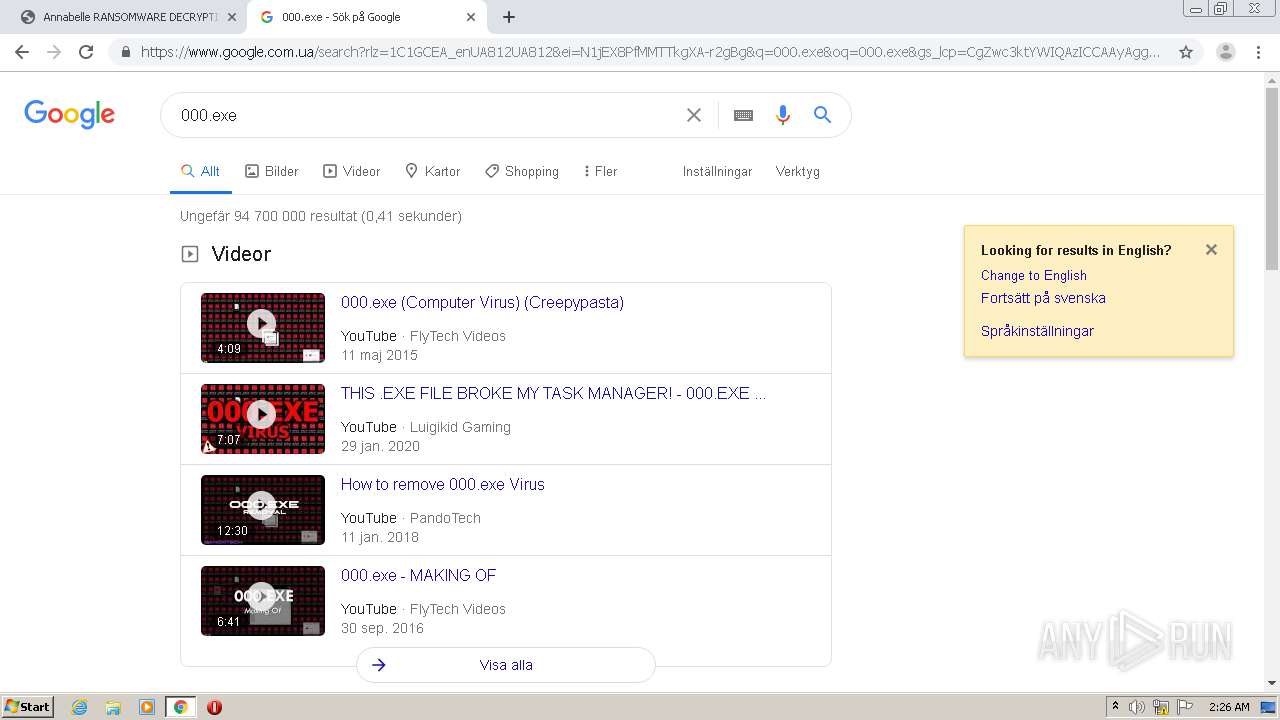
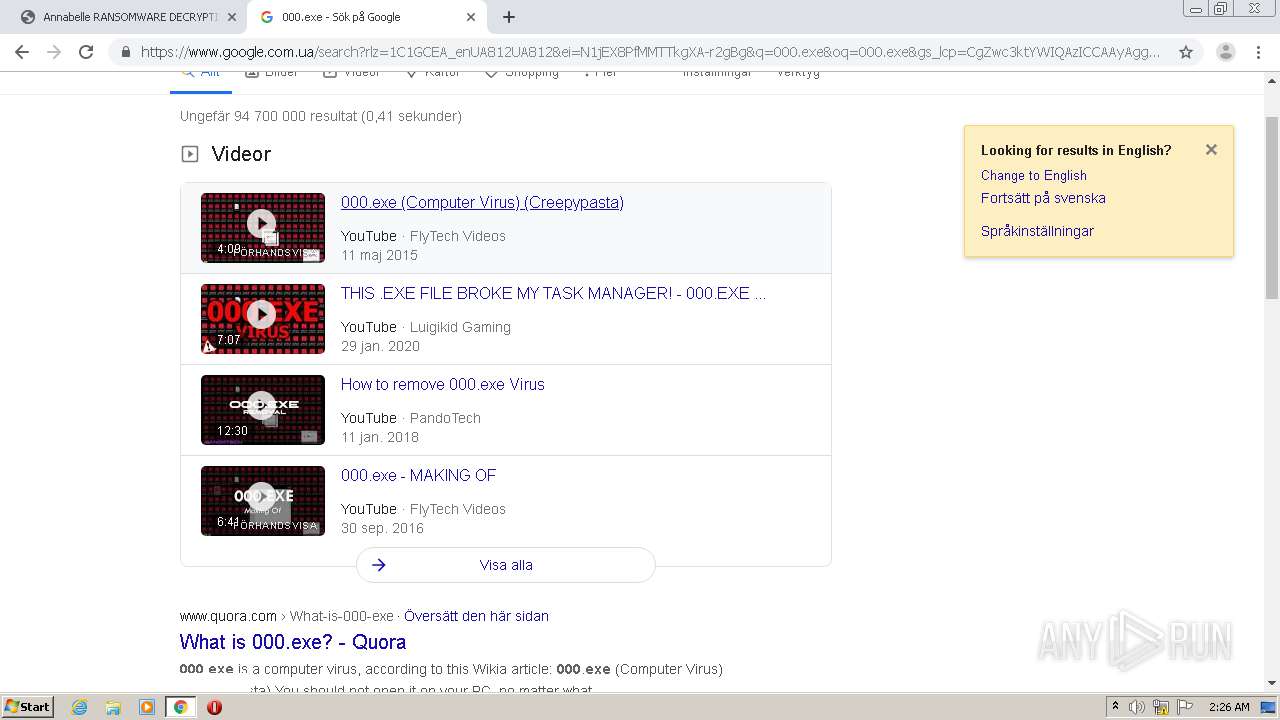
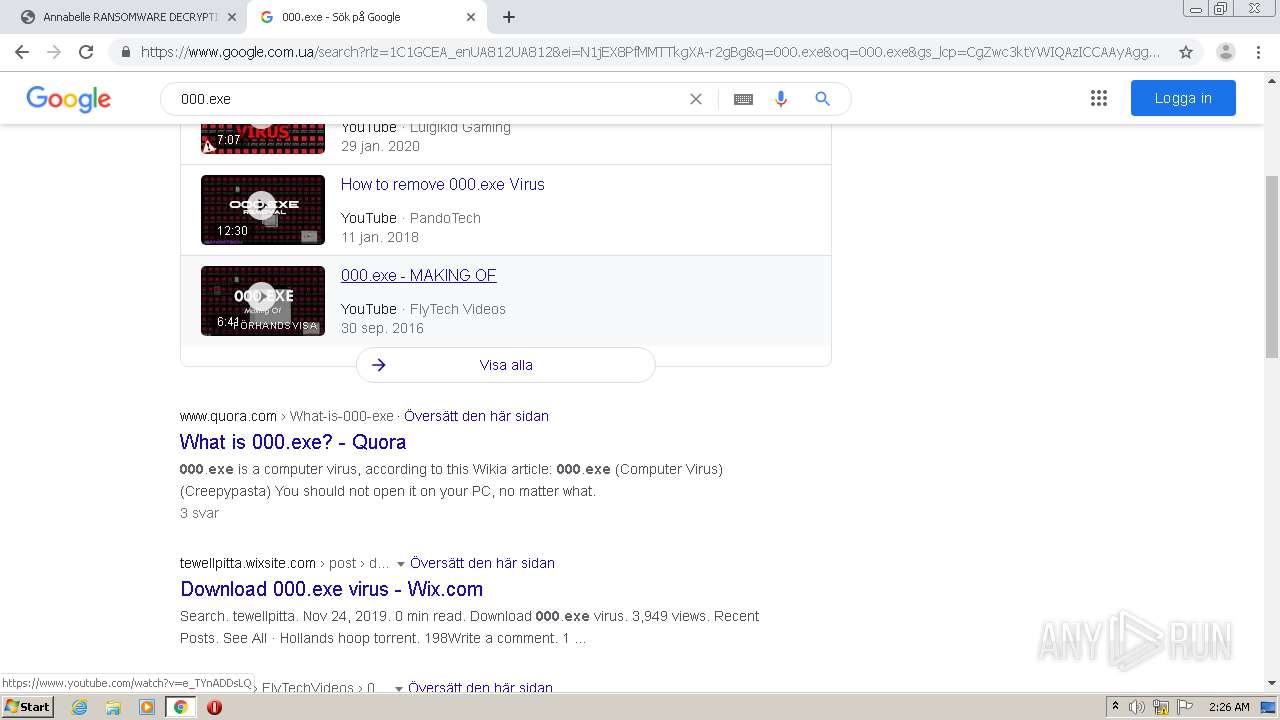
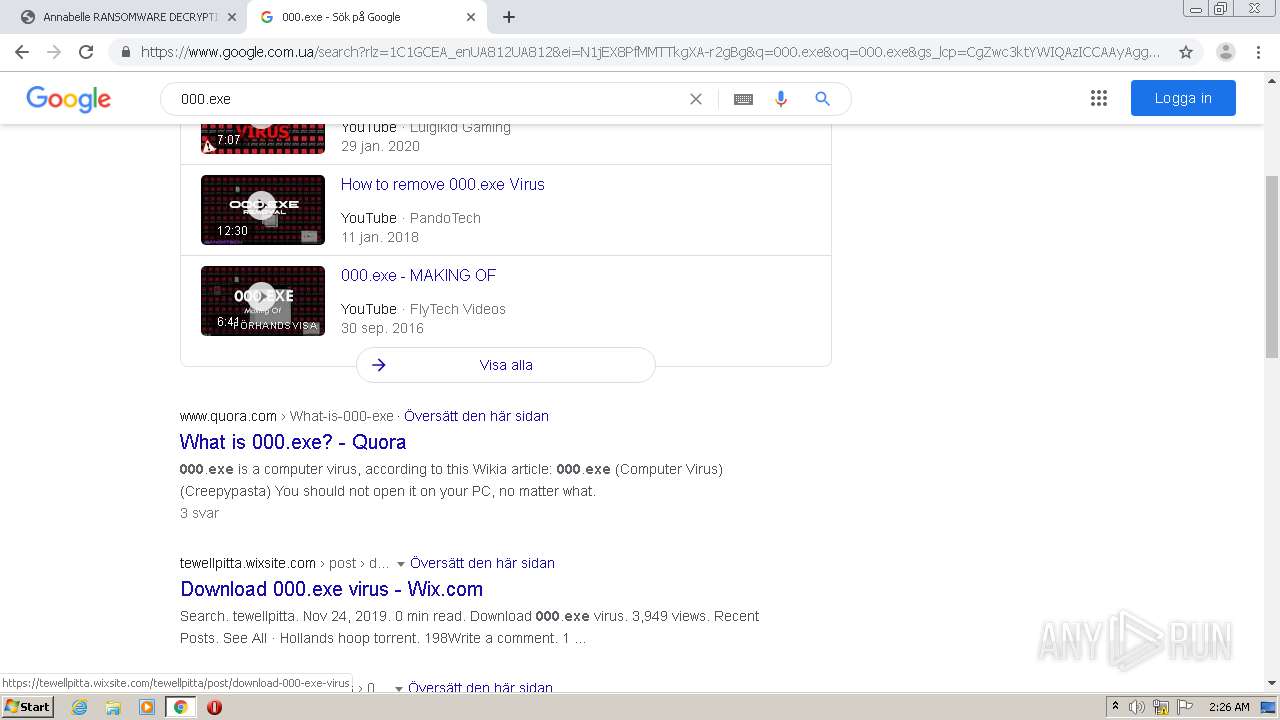
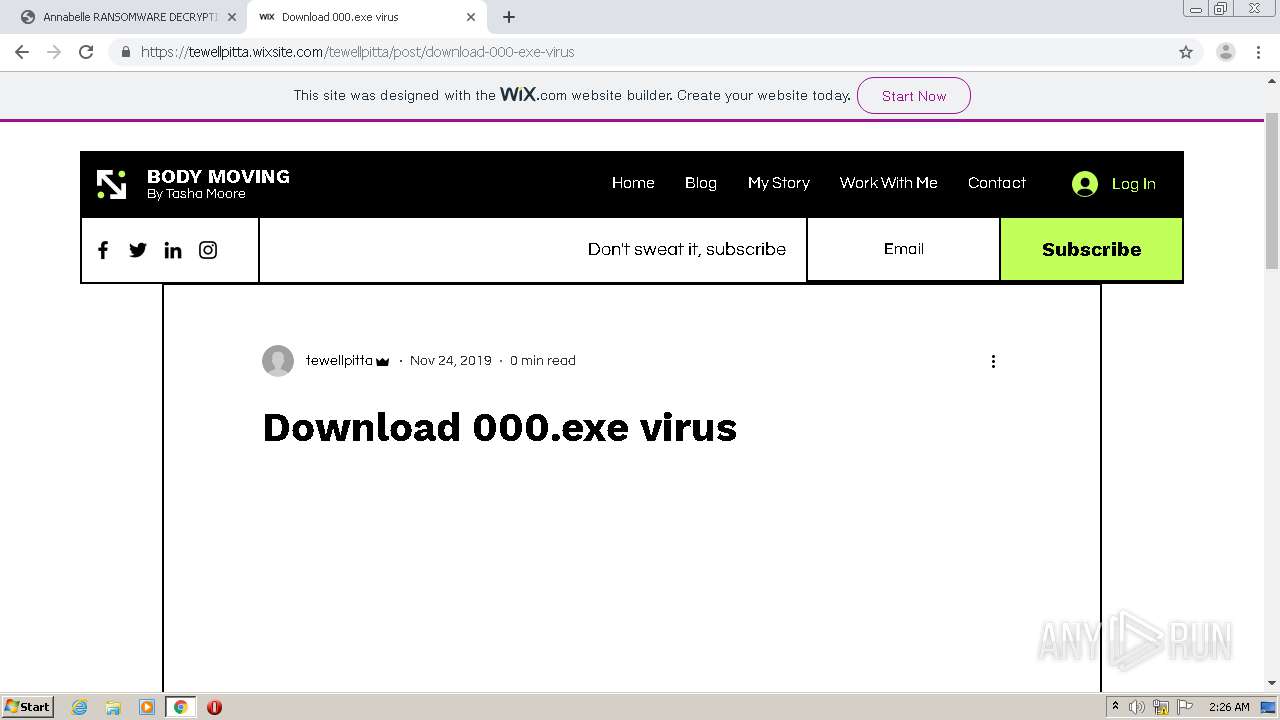
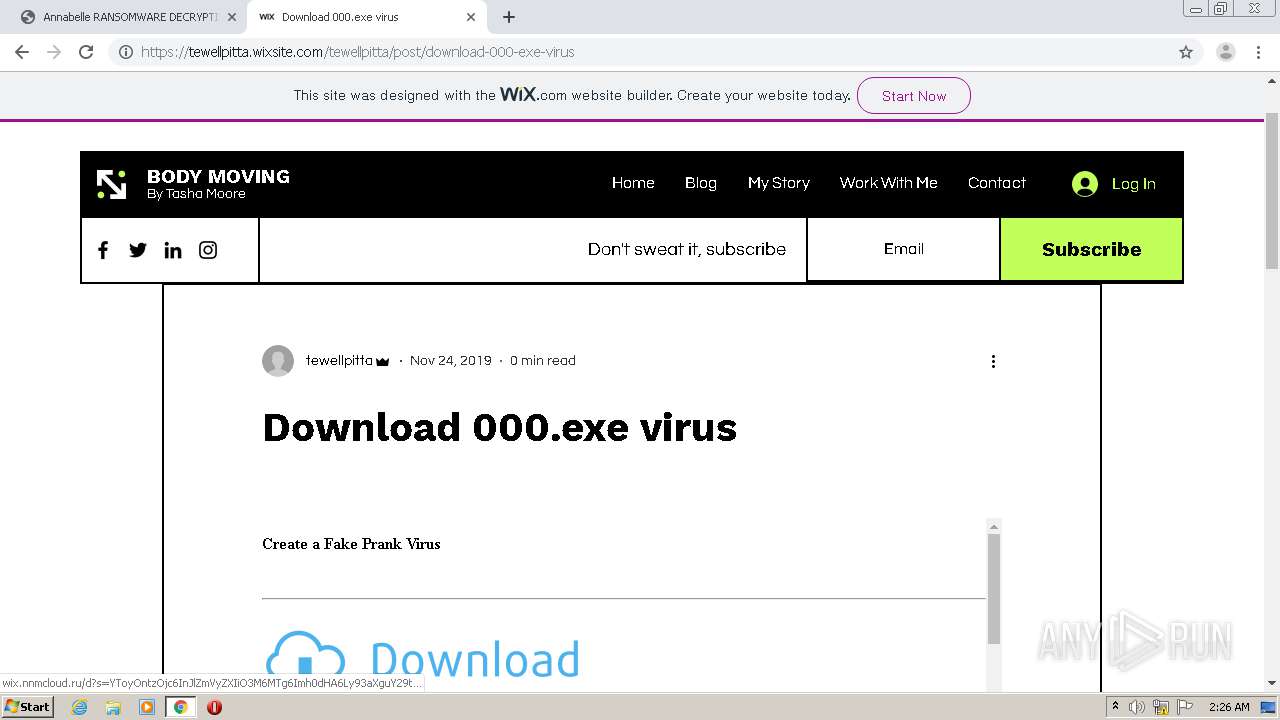
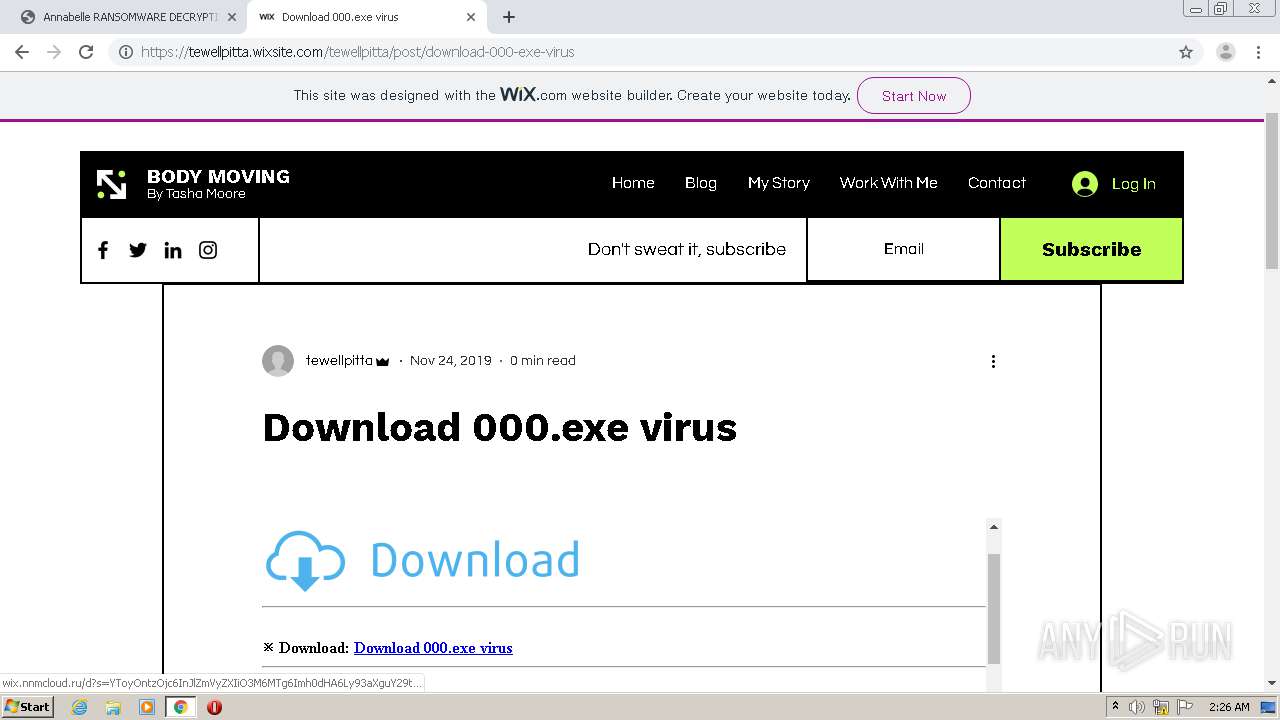
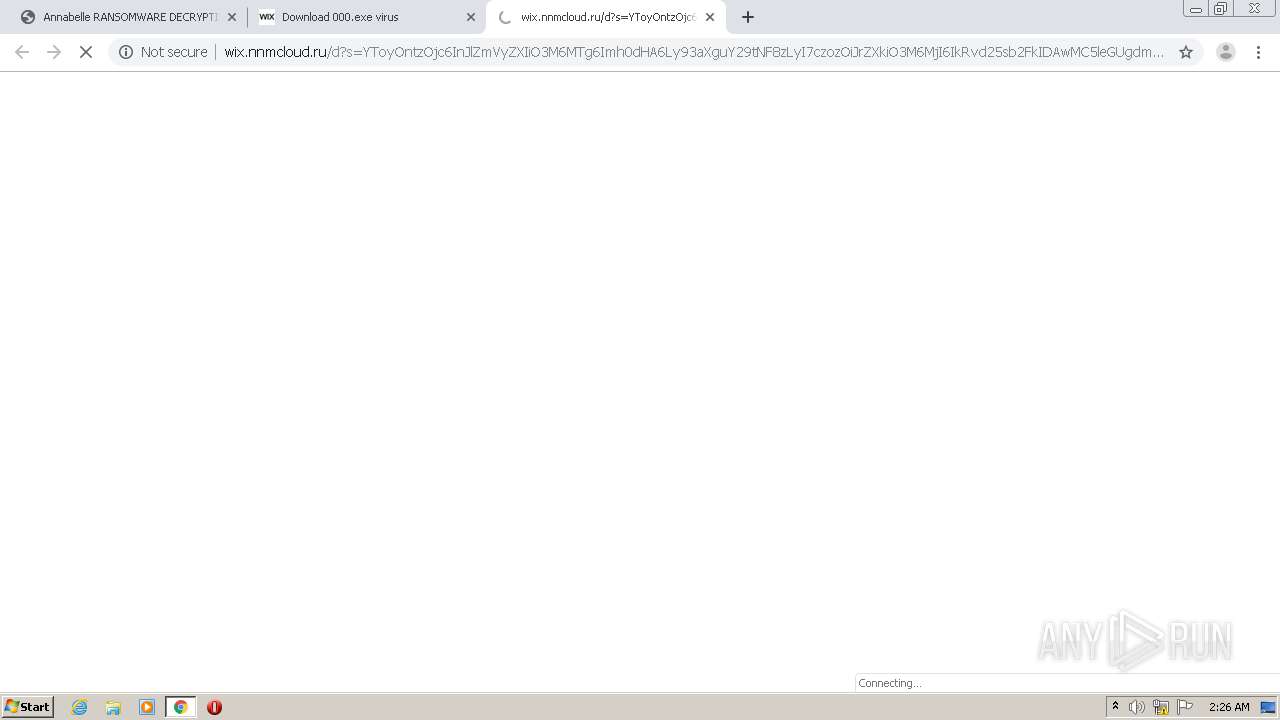
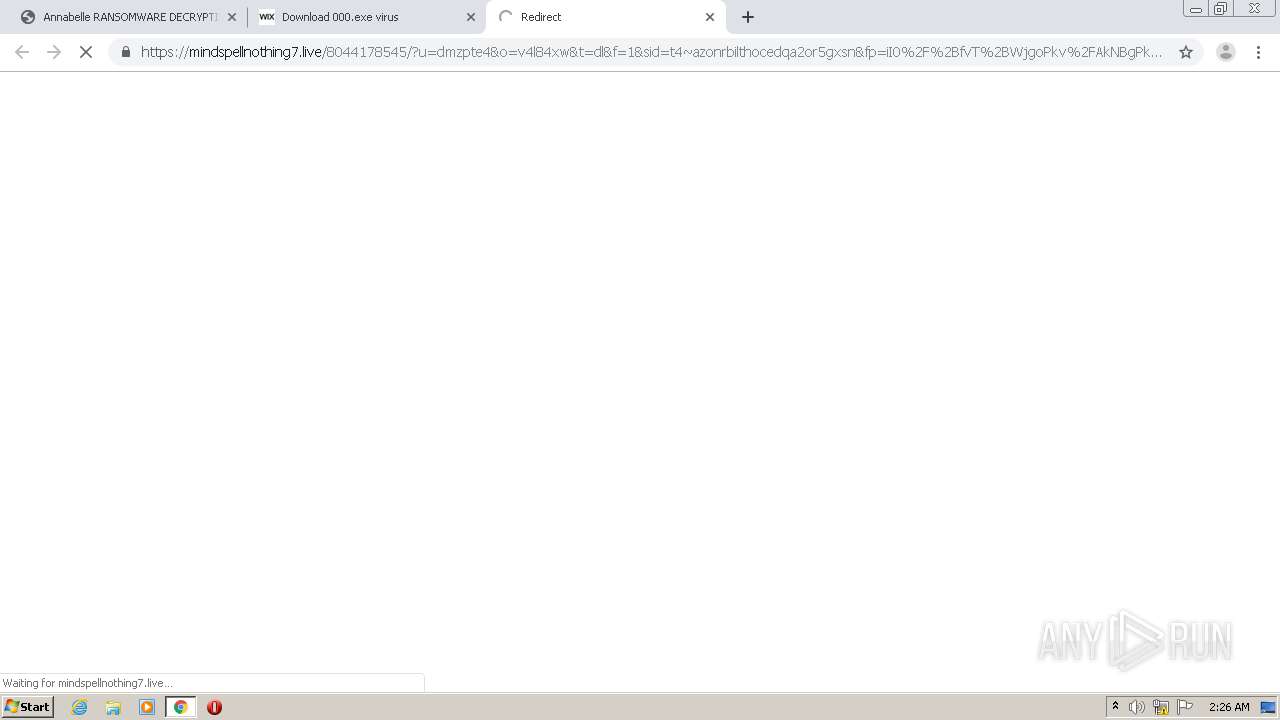
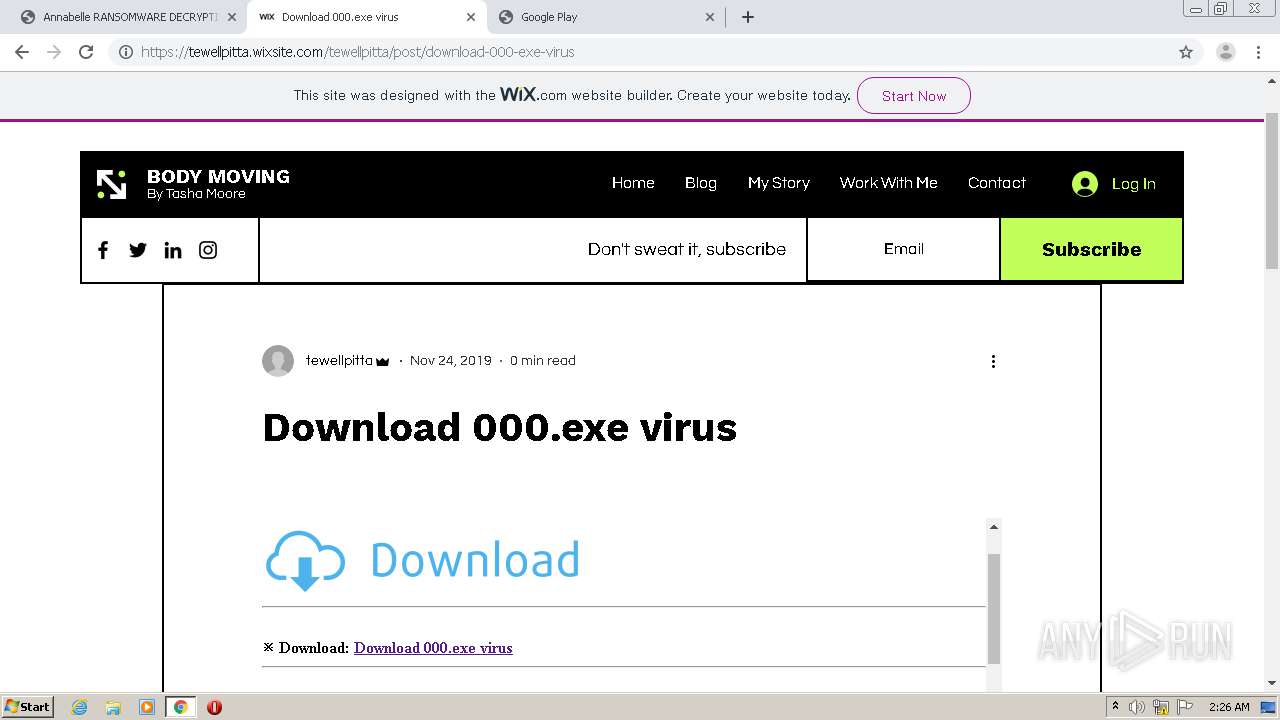
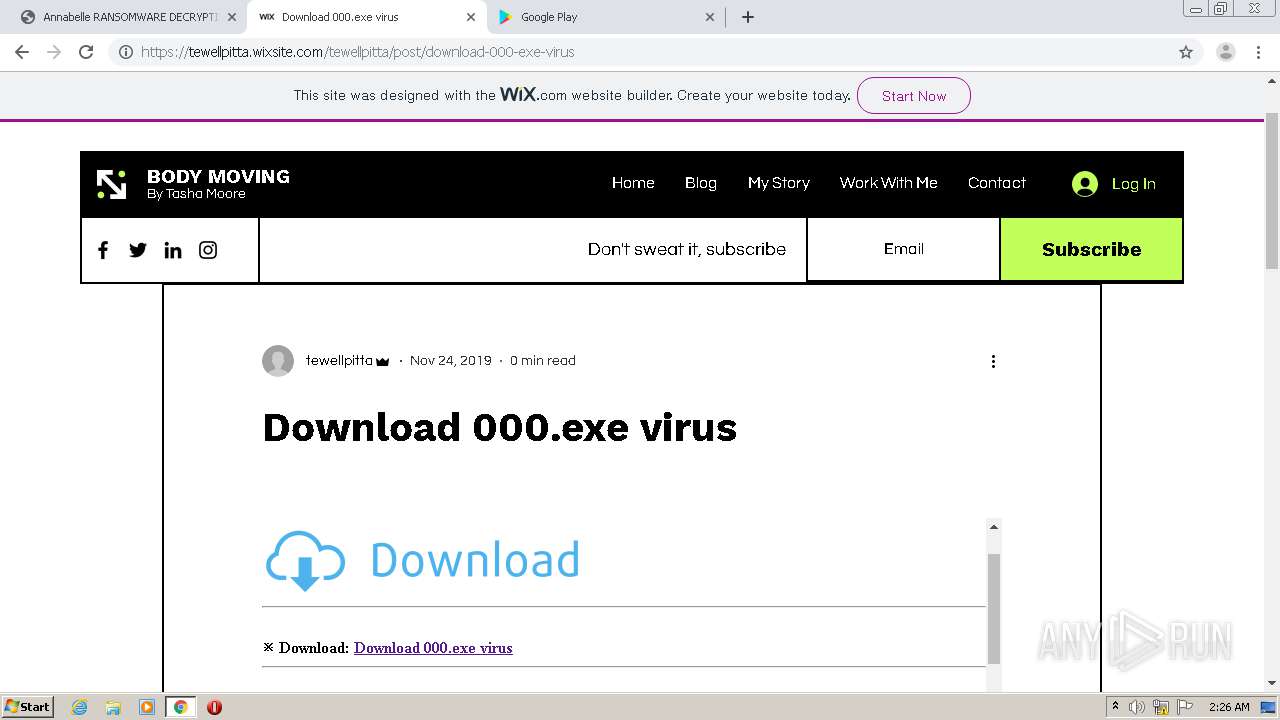
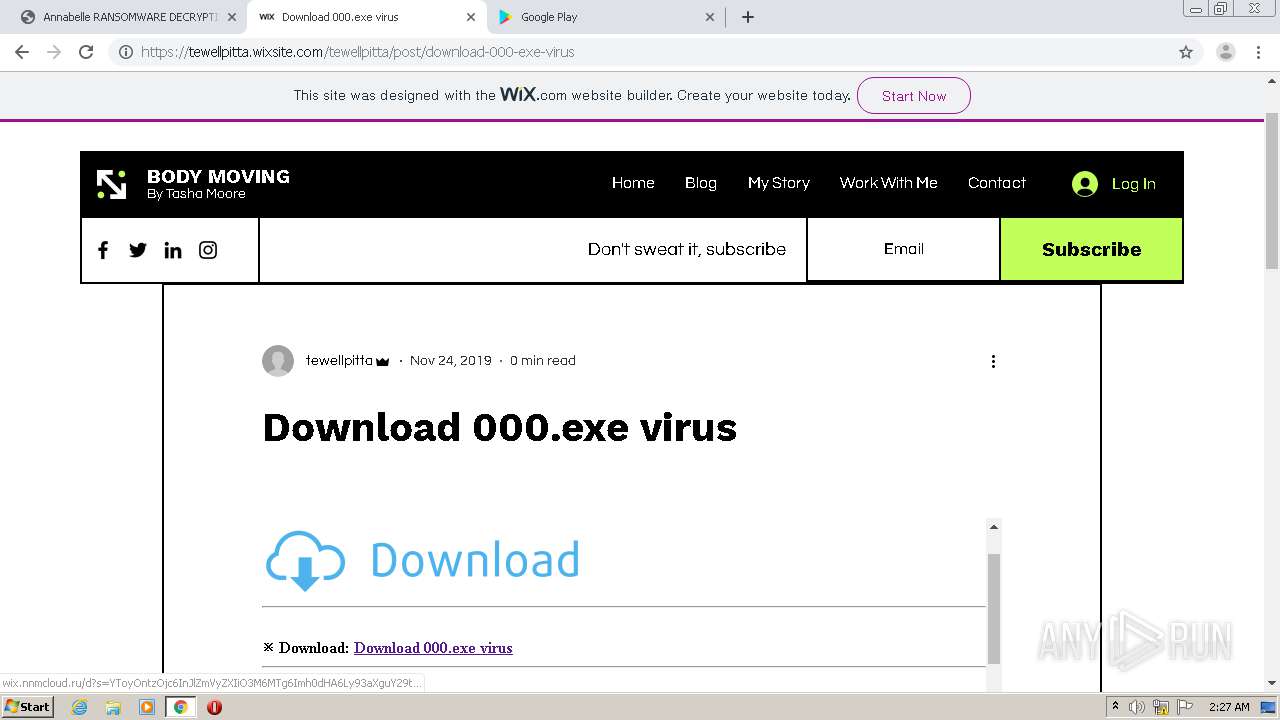
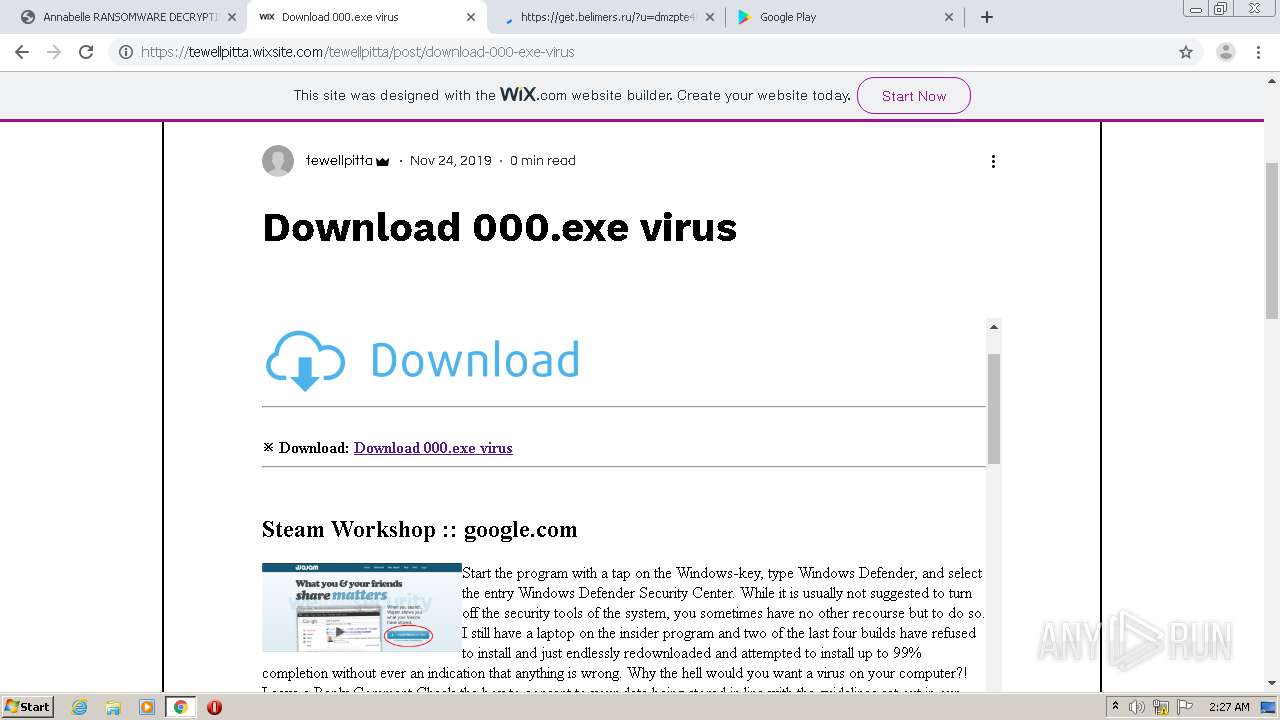
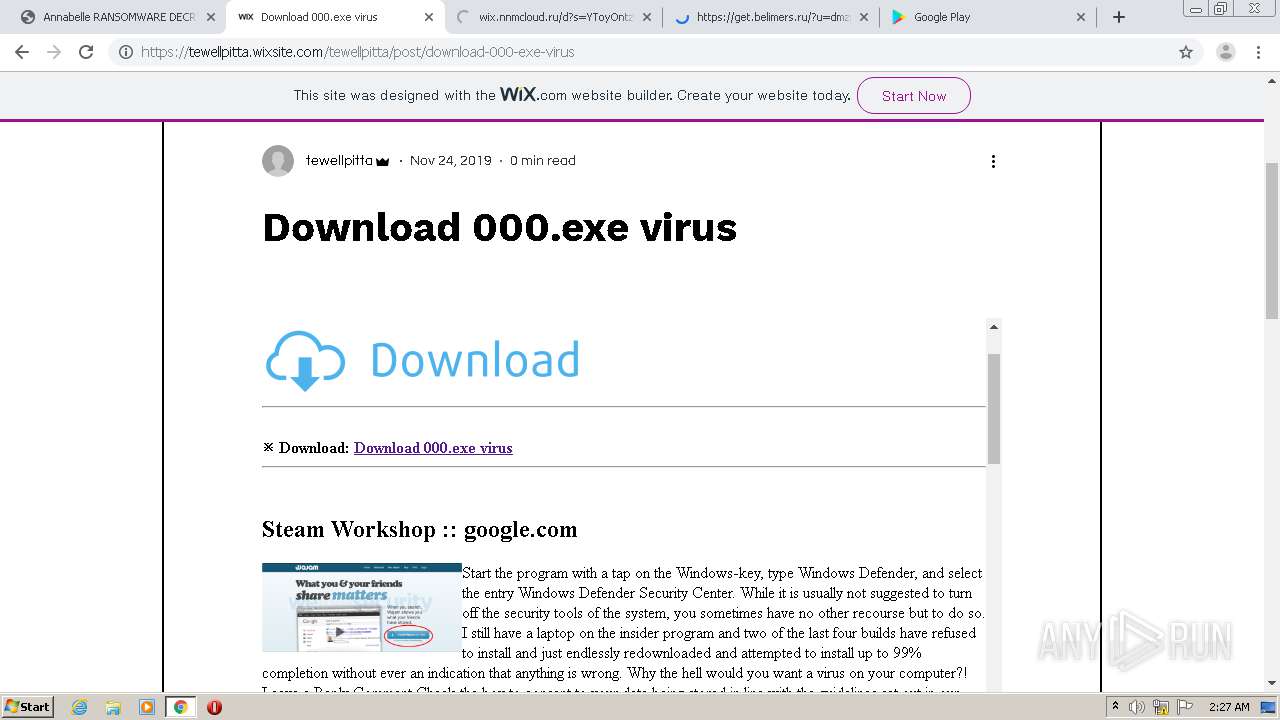
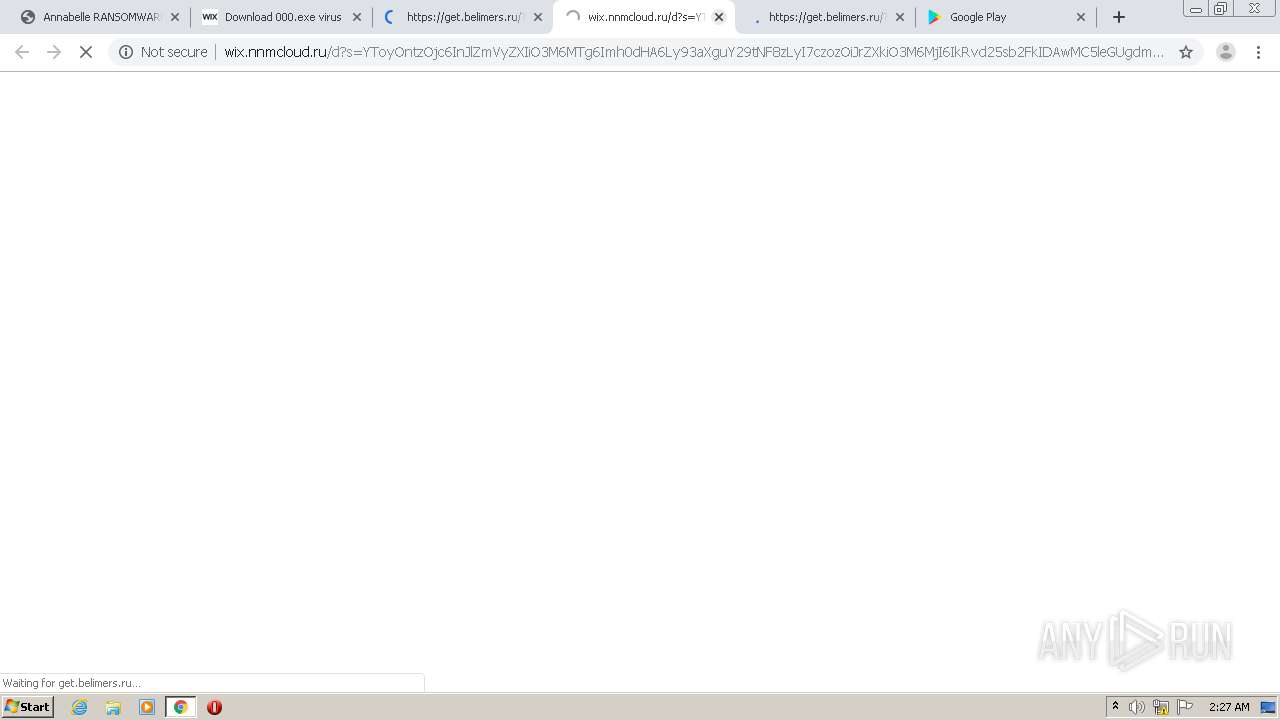
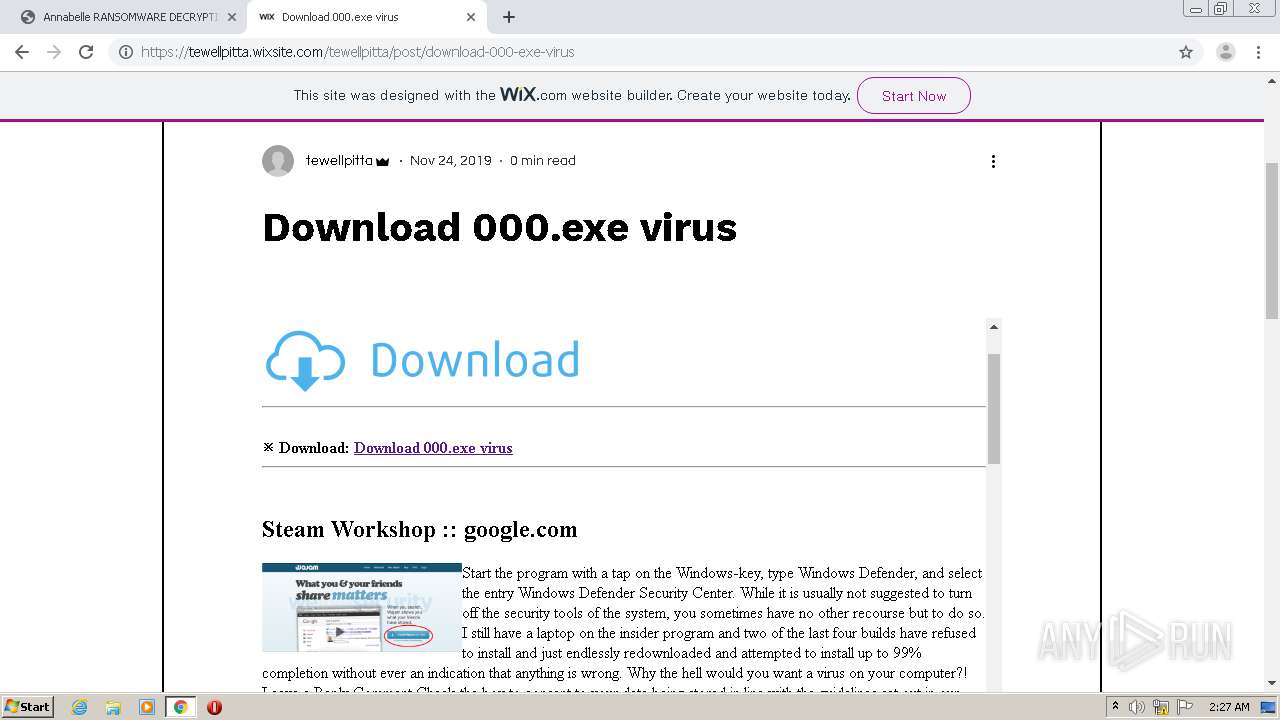
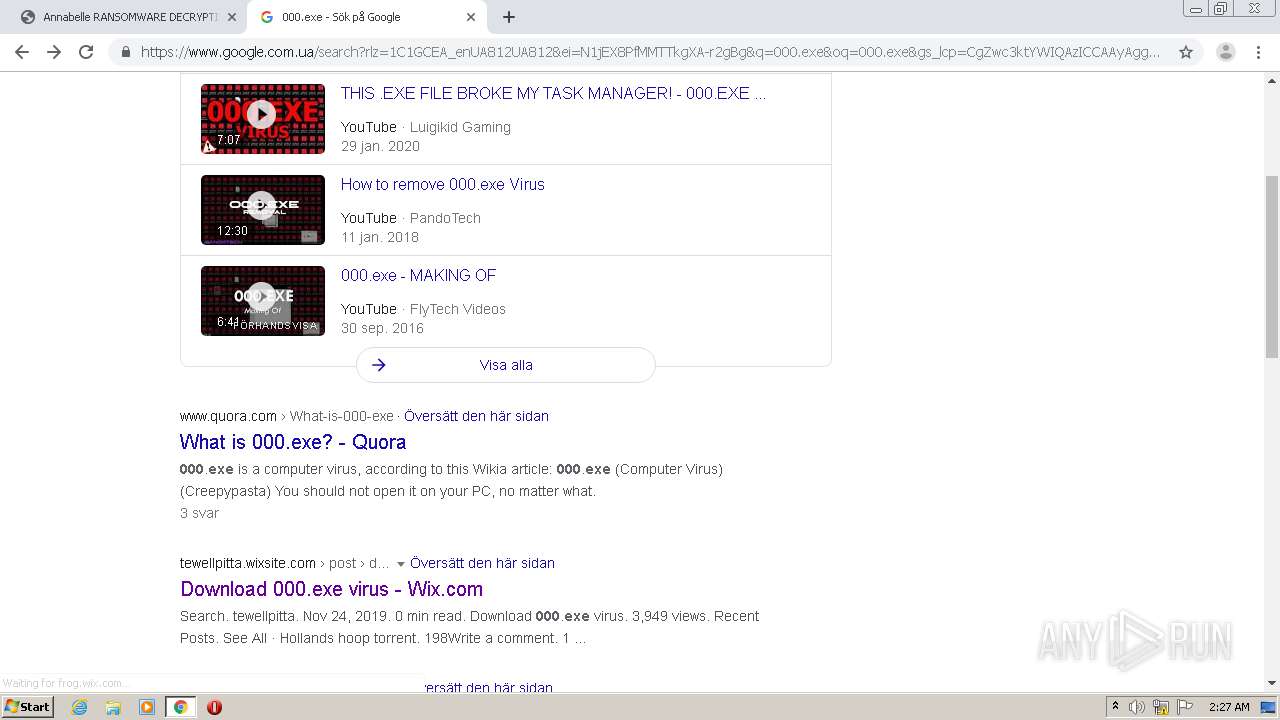
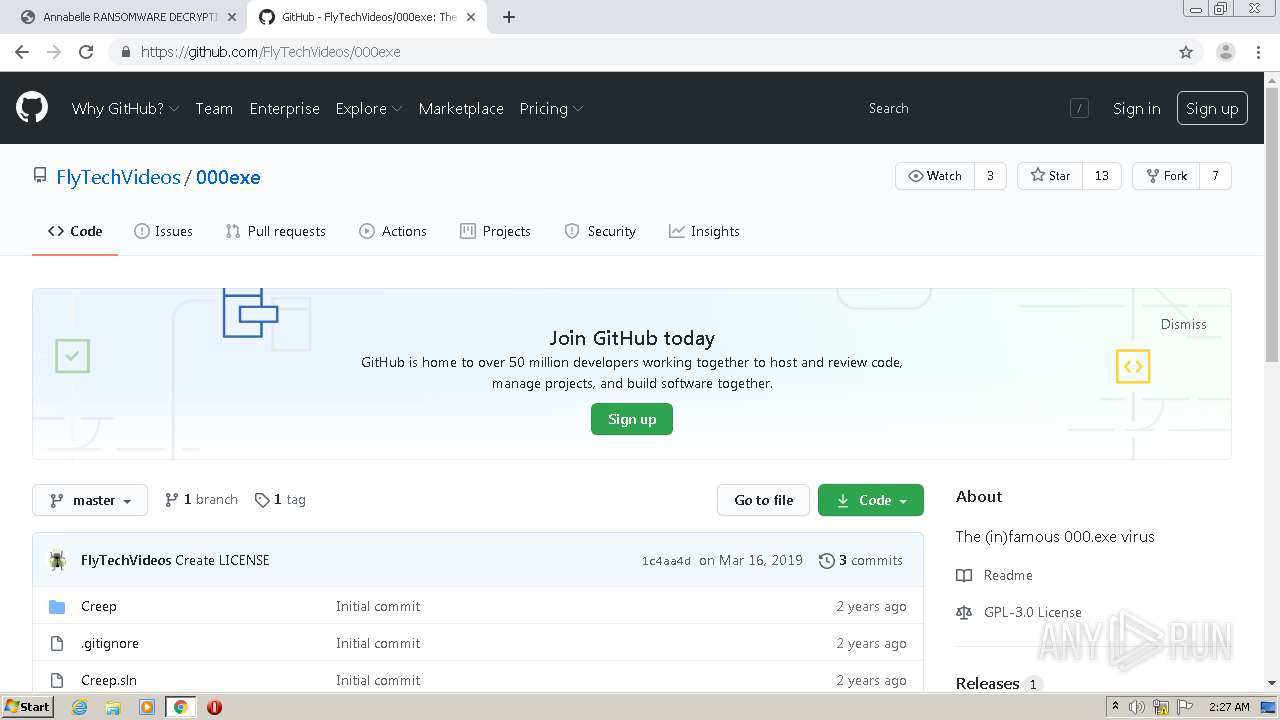
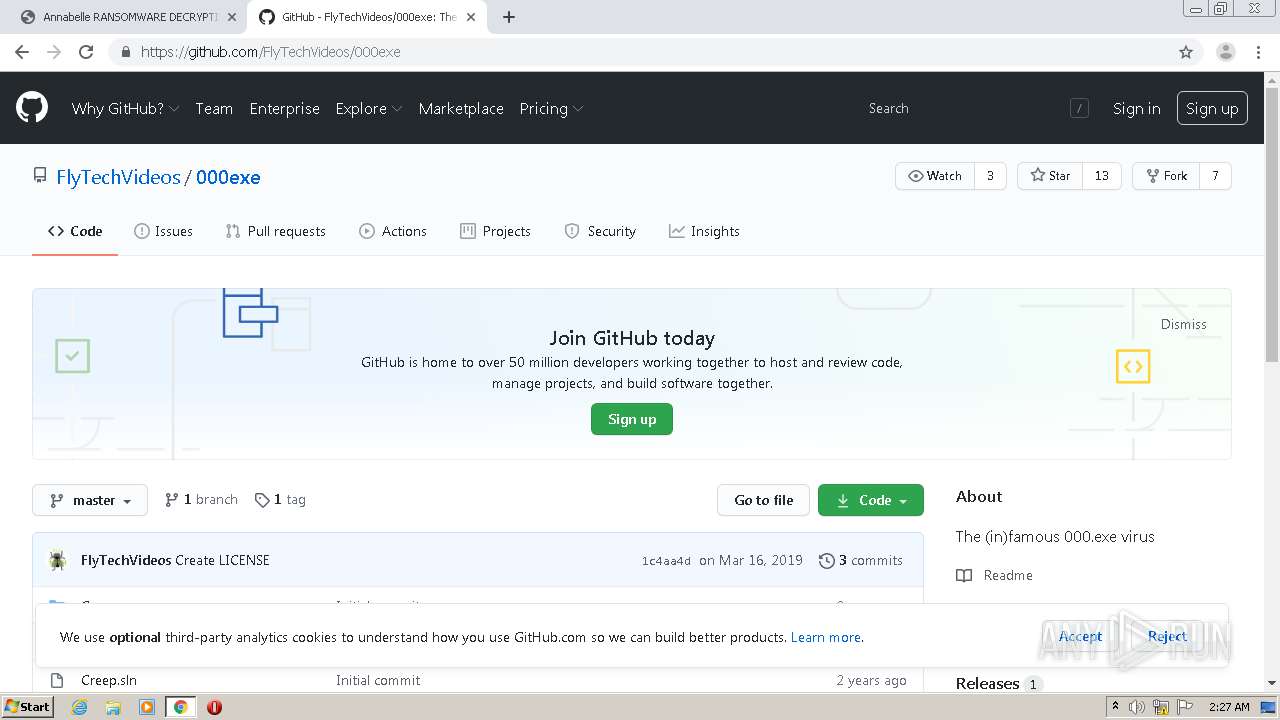
2576 | chrome.exe | GET | 200 | 78.31.67.56:80 | http://wix.nnmcloud.ru/d?s=YToyOntzOjc6InJlZmVyZXIiO3M6MTg6Imh0dHA6Ly93aXguY29tNF8zLyI7czozOiJrZXkiO3M6MjI6IkRvd25sb2FkIDAwMC5leGUgdmlydXMiO30= | DE | html | 354 b | malicious |
2576 | chrome.exe | GET | 200 | 78.31.67.56:80 | http://wix.nnmcloud.ru/d?s=YToyOntzOjc6InJlZmVyZXIiO3M6MTg6Imh0dHA6Ly93aXguY29tNF8zLyI7czozOiJrZXkiO3M6MjI6IkRvd25sb2FkIDAwMC5leGUgdmlydXMiO30= | DE | html | 354 b | malicious |
2576 | chrome.exe | GET | 200 | 78.31.67.56:80 | http://wix.nnmcloud.ru/d?s=YToyOntzOjc6InJlZmVyZXIiO3M6MTg6Imh0dHA6Ly93aXguY29tNF8zLyI7czozOiJrZXkiO3M6MjI6IkRvd25sb2FkIDAwMC5leGUgdmlydXMiO30= | DE | html | 354 b | malicious |
2576 | chrome.exe | GET | 301 | 13.224.78.126:80 | http://community.kaspersky.com/ | US | html | 183 b | malicious |
2576 | chrome.exe | GET | 200 | 78.31.67.56:80 | http://wix.nnmcloud.ru/d?s=YToyOntzOjc6InJlZmVyZXIiO3M6MTg6Imh0dHA6Ly93aXguY29tNF8zLyI7czozOiJrZXkiO3M6MjI6IkRvd25sb2FkIDAwMC5leGUgdmlydXMiO30= | DE | html | 354 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2576 | chrome.exe | 172.217.16.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 172.217.21.227:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 216.58.212.174:443 | encrypted-vtbn1.gstatic.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 216.58.207.46:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
2576 | chrome.exe | 172.217.18.13:443 | accounts.google.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 143.204.215.79:443 | www.nomoreransom.org | — | US | suspicious |
2576 | chrome.exe | 192.229.220.142:80 | download.bitdefender.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2576 | chrome.exe | 216.58.210.14:443 | consent.google.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 172.217.12.170:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
2576 | chrome.exe | 172.217.22.66:443 | adservice.google.com.ua | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.nomoreransom.org |
| whitelisted |
accounts.google.com |
| shared |
download.bitdefender.com |
| suspicious |
ssl.gstatic.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2576 | chrome.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1044 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .life TLD |
Process | Message |
|---|---|
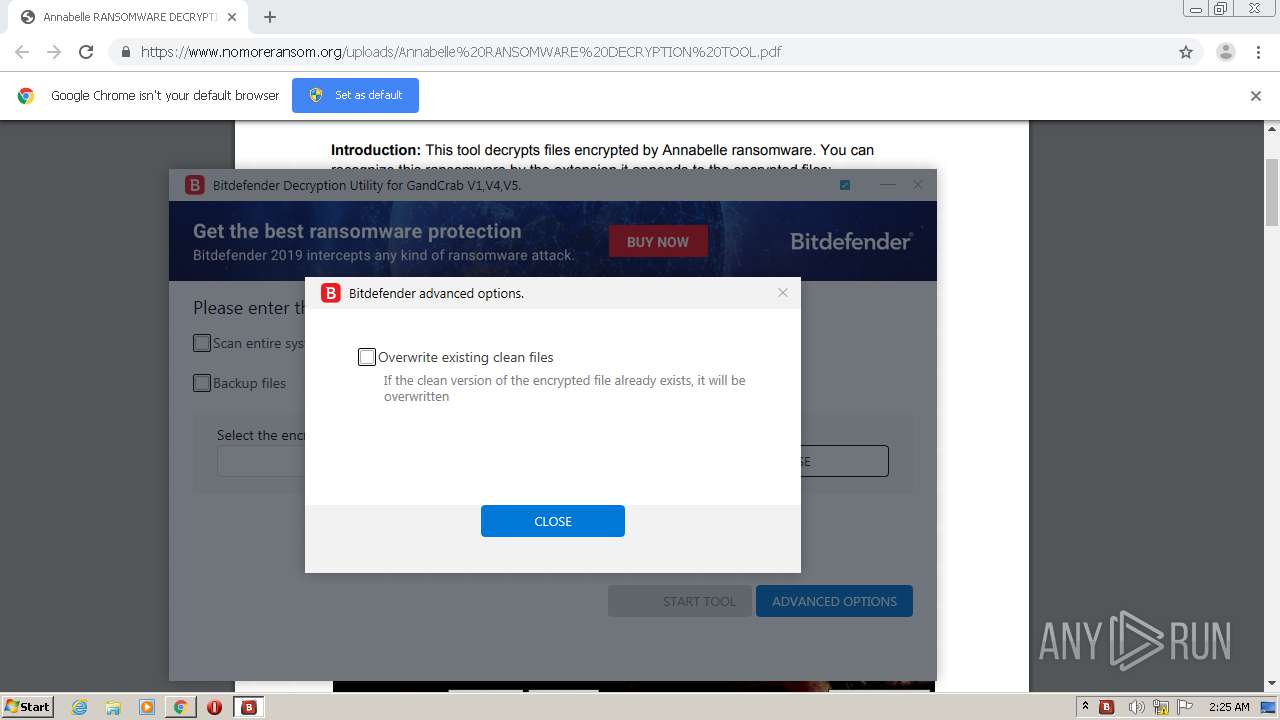
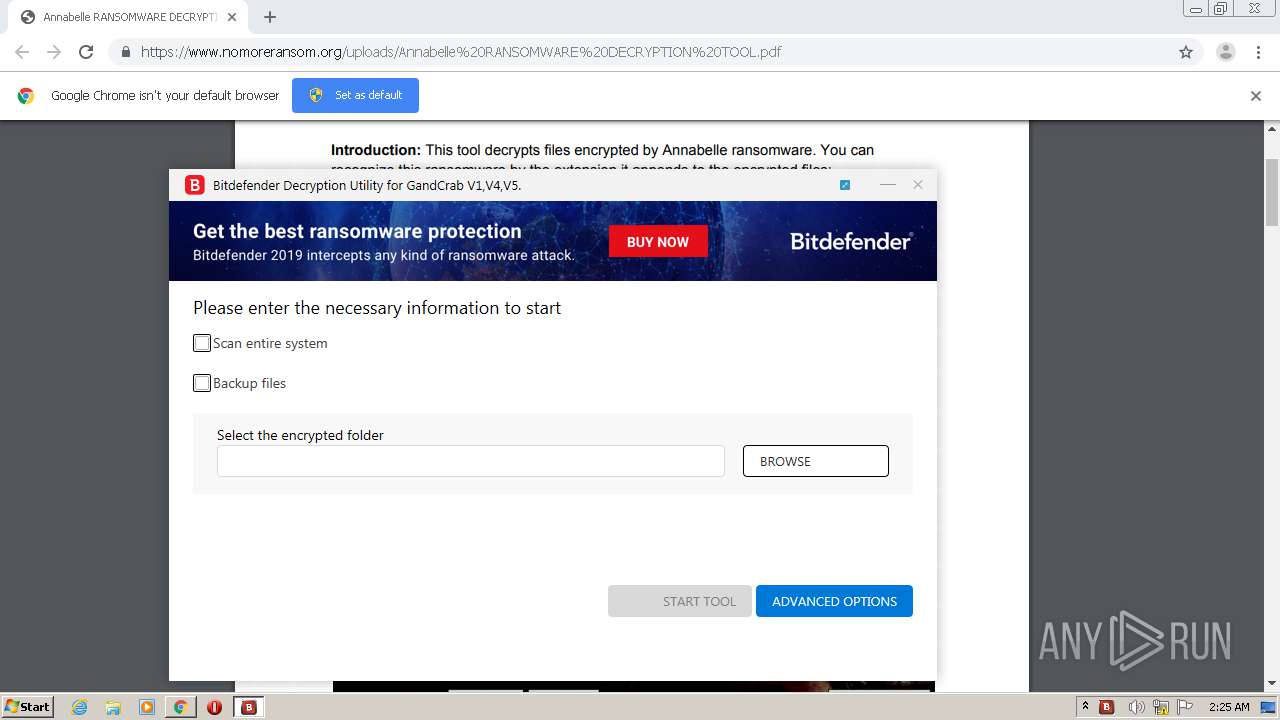
BDRansomDecryptor.exe | unknown property 'enable-background' at (this://app/img/check-on.svg(1))
|
BDRansomDecryptor.exe | unknown property 'enable-background' at (this://app/img/check-on.svg(1))
|
BDRansomDecryptor.exe | unknown property 'enable-background' at (this://app/img/check-on.svg(1))
|