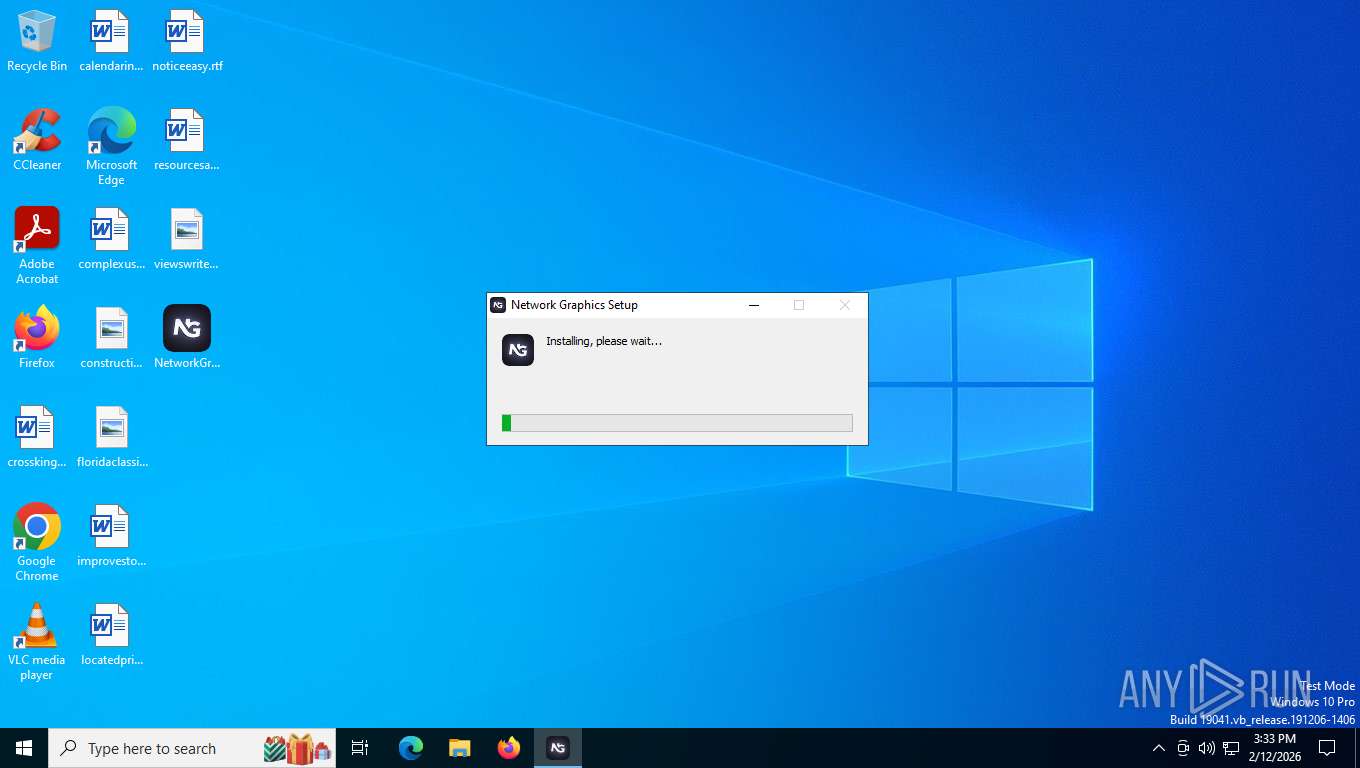
| File name: | NetworkGraphicsSetup.exe |
| Full analysis: | https://app.any.run/tasks/d17e54f7-7304-4b8d-b0e1-e756a51c24b1 |
| Verdict: | Malicious activity |
| Analysis date: | February 12, 2026, 20:32:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 7CB1BC28DB043C8310997EA65DD19967 |
| SHA1: | 419F51141C8E01DC0A8762EC365C5F62065DC8FD |
| SHA256: | 2B2937DF3E5AE5465058B45DDAF6E46432613FA5AC678D4D64A8DAF0C2F56BFC |
| SSDEEP: | 1572864:TiKfaInw6BTPIWQWy1A82mexe5BRefhrGvdDI:uiaInw6RPIWh8exe5BwfhqvxI |
MALICIOUS
Changes the autorun value in the registry
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
SUSPICIOUS
The process creates files with name similar to system file names
- NetworkGraphicsSetup.exe (PID: 8488)
Malware-specific behavior (creating "System.dll" in Temp)
- NetworkGraphicsSetup.exe (PID: 8488)
Executable content was dropped or overwritten
- NetworkGraphicsSetup.exe (PID: 8488)
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Drops 7-zip archiver for unpacking
- NetworkGraphicsSetup.exe (PID: 8488)
Process drops legitimate windows executable
- NetworkGraphicsSetup.exe (PID: 8488)
Starts CMD.EXE for commands execution
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Starts application with an unusual extension
- cmd.exe (PID: 7360)
- cmd.exe (PID: 8356)
Application launched itself
- Network Graphics.exe (PID: 6352)
INFO
Checks supported languages
- NetworkGraphicsSetup.exe (PID: 8488)
- Network Graphics.exe (PID: 6352)
- chcp.com (PID: 8156)
- Network Graphics.exe (PID: 3036)
- Network Graphics.exe (PID: 4724)
- Network Graphics.exe (PID: 1784)
- chcp.com (PID: 8684)
The sample compiled with english language support
- NetworkGraphicsSetup.exe (PID: 8488)
Reads the computer name
- NetworkGraphicsSetup.exe (PID: 8488)
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 3036)
Create files in a temporary directory
- NetworkGraphicsSetup.exe (PID: 8488)
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Drops script file
- NetworkGraphicsSetup.exe (PID: 8488)
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Reads security settings of Internet Explorer
- NetworkGraphicsSetup.exe (PID: 8488)
Creates files or folders in the user directory
- NetworkGraphicsSetup.exe (PID: 8488)
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 3036)
Creates a software uninstall entry
- NetworkGraphicsSetup.exe (PID: 8488)
Manual execution by a user
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Reads Environment values
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Reads product name
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Changes the display of characters in the console
- cmd.exe (PID: 7360)
- cmd.exe (PID: 8356)
Launching a file from a Registry key
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 1784)
Checks proxy server information
- Network Graphics.exe (PID: 6352)
- slui.exe (PID: 3376)
Process checks computer location settings
- Network Graphics.exe (PID: 6352)
- Network Graphics.exe (PID: 4724)
Reads the machine GUID from the registry
- Network Graphics.exe (PID: 6352)
Node.js compiler has been detected
- Network Graphics.exe (PID: 6352)
There is functionality for taking screenshot (YARA)
- Network Graphics.exe (PID: 6352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:12:15 22:26:14+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 473088 |
| UninitializedDataSize: | 16384 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.0.44.0 |
| ProductVersionNumber: | 4.0.44.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
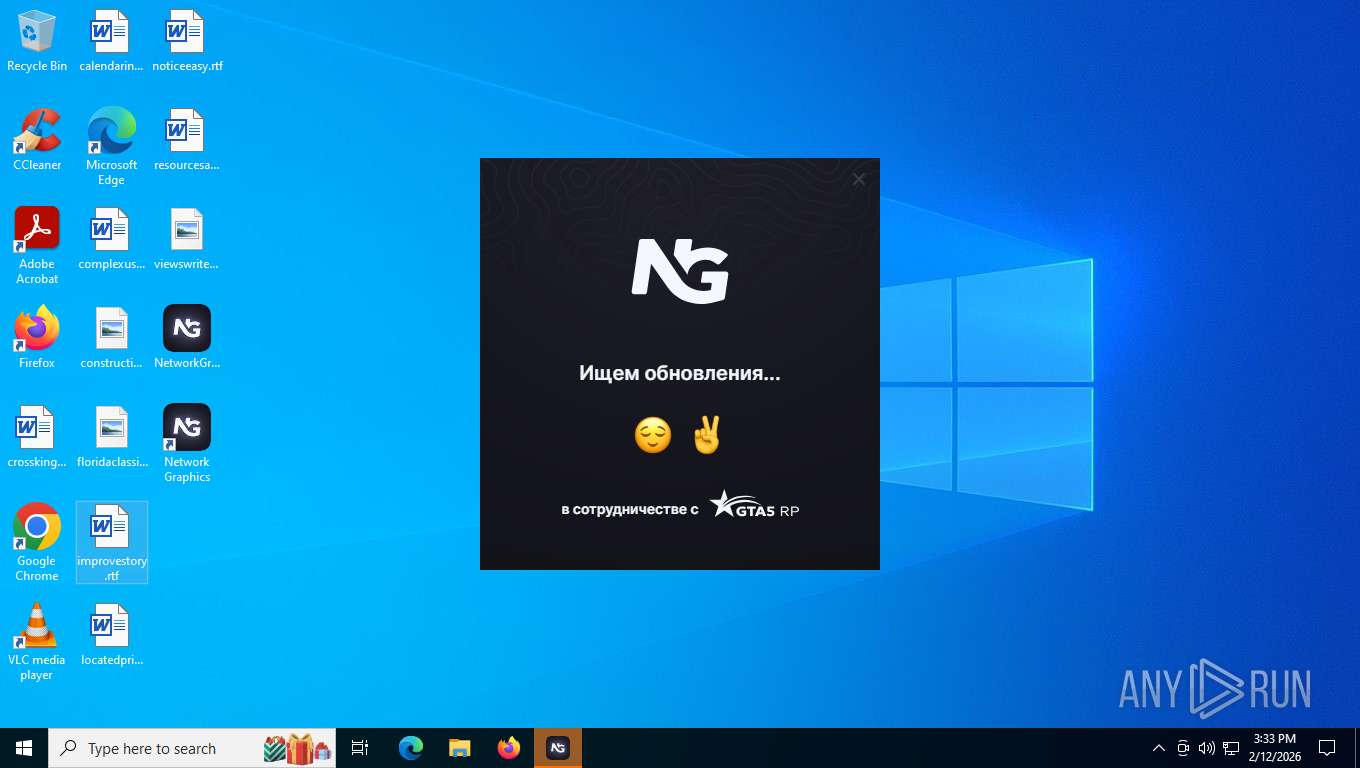
| CompanyName: | Network Group |
| FileDescription: | Mods, graphics, skins and optimization for the GTA 5 RP in one app |
| FileVersion: | 4.0.44 |
| LegalCopyright: | Copyright © 2026 Network Group |
| ProductName: | Network Graphics |
| ProductVersion: | 4.0.44 |
Total processes
147
Monitored processes
12
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1784 | "C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe" --autostart | C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe | explorer.exe | ||||||||||||
User: admin Company: Network Group Integrity Level: MEDIUM Description: Network Graphics Exit code: 0 Version: 4.0.44 Modules
| |||||||||||||||
| 3036 | "C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --use-angle=swiftshader-webgl --use-gl=angle --user-data-dir="C:\Users\admin\AppData\Roaming\Network Graphics" --field-trial-handle=2156,i,13125000219756517161,16687321841603192215,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2148 /prefetch:3 | C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe | — | Network Graphics.exe | |||||||||||
User: admin Company: Network Group Integrity Level: MEDIUM Description: Network Graphics Version: 4.0.44 Modules
| |||||||||||||||
| 3376 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4724 | "C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe" --type=renderer --user-data-dir="C:\Users\admin\AppData\Roaming\Network Graphics" --app-user-model-id="electron.app.Network Graphics" --app-path="C:\Users\admin\AppData\Local\Network Graphics\resources\app.asar" --no-sandbox --no-zygote --disable-breakpad --disable-lcd-text --js-flags=--expose-gc --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=3 --enable-zero-copy --disable-partial-raster --enable-gpu-memory-buffer-compositor-resources --enable-main-frame-before-activation --renderer-client-id=4 --field-trial-handle=2572,i,13125000219756517161,16687321841603192215,262144 --disable-features=SpareRendererForSitePerProcess,WinDelaySpellcheckServiceInit,WinRetrieveSuggestionsOnlyOnDemand --variations-seed-version --mojo-platform-channel-handle=2568 /prefetch:1 | C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe | — | Network Graphics.exe | |||||||||||
User: admin Company: Network Group Integrity Level: MEDIUM Description: Network Graphics Version: 4.0.44 Modules
| |||||||||||||||
| 6352 | "C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe" | C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe | explorer.exe | ||||||||||||
User: admin Company: Network Group Integrity Level: MEDIUM Description: Network Graphics Version: 4.0.44 Modules
| |||||||||||||||
| 7360 | C:\WINDOWS\system32\cmd.exe /d /s /c "chcp" | C:\Windows\System32\cmd.exe | — | Network Graphics.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8044 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8156 | chcp | C:\Windows\System32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8240 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8356 | C:\WINDOWS\system32\cmd.exe /d /s /c "chcp" | C:\Windows\System32\cmd.exe | — | Network Graphics.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 947
Read events
5 909
Write events
18
Delete events
20
Modification events
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Network Graphics | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 139 | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | ShortcutName |
Value: Network Graphics | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | DisplayName |
Value: Network Graphics 4.0.44 | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Network Graphics\Uninstall Network Graphics.exe" /currentuser | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Network Graphics\Uninstall Network Graphics.exe" /currentuser /S | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | DisplayVersion |
Value: 4.0.44 | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Network Graphics\Network Graphics.exe,0 | |||
| (PID) Process: | (8488) NetworkGraphicsSetup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\fc2e0712-968d-5a14-b2cc-fde1a0582edf |
| Operation: | write | Name: | Publisher |
Value: Network Group | |||
Executable files
37
Suspicious files
153
Text files
60
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\app-64.7z | — | |
MD5:— | SHA256:— | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\7z-out\icudtl.dat | — | |
MD5:— | SHA256:— | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\7z-out\LICENSES.chromium.html | — | |
MD5:— | SHA256:— | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\nsExec.dll | executable | |
MD5:EC0504E6B8A11D5AAD43B296BEEB84B2 | SHA256:5D9CEB1CE5F35AEA5F9E5A0C0EDEEEC04DFEFE0C77890C80C70E98209B58B962 | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\7z-out\chrome_200_percent.pak | binary | |
MD5:DC48A33BD20BFC7CACFC925A84B015B6 | SHA256:2C1B3E4B8A0CF837AE0A390FCA54F45D7D22418E040F1DFEA979622383ACCED6 | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\SpiderBanner.dll | executable | |
MD5:17309E33B596BA3A5693B4D3E85CF8D7 | SHA256:996A259E53CA18B89EC36D038C40148957C978C0FD600A268497D4C92F882A93 | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\Desktop\Network Graphics.lnk | binary | |
MD5:B0ADB7F69089333B6617A0D8CF9269A4 | SHA256:9B0FB7DA6BC1D23BB7CCA6674257EA711AEBA7E050D6DDBD4B57B8D8257577A1 | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\System.dll | executable | |
MD5:0D7AD4F45DC6F5AA87F606D0331C6901 | SHA256:3EB38AE99653A7DBC724132EE240F6E5C4AF4BFE7C01D31D23FAF373F9F2EACA | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\StdUtils.dll | executable | |
MD5:C6A6E03F77C313B267498515488C5740 | SHA256:B72E9013A6204E9F01076DC38DABBF30870D44DFC66962ADBF73619D4331601E | |||
| 8488 | NetworkGraphicsSetup.exe | C:\Users\admin\AppData\Local\Temp\nsxABB0.tmp\nsis7z.dll | executable | |
MD5:80E44CE4895304C6A3A831310FBF8CD0 | SHA256:B393F05E8FF919EF071181050E1873C9A776E1A0AE8329AEFFF7007D0CADF592 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
48
DNS requests
15
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
3344 | svchost.exe | GET | 200 | 2.16.164.42:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
— | — | GET | 200 | 2.16.204.135:443 | https://th.bing.com/th?id=OCGE.9n7hl5s06zk0_v7_main&w=80&h=80&c=1&rs=1&p=0 | unknown | image | 18.4 Kb | unknown |
— | — | GET | 200 | 2.16.204.135:443 | https://th.bing.com/th?id=OCGE.9nq9j864v30w_v5_main&w=80&h=80&c=1&rs=1&p=0 | unknown | image | 17.4 Kb | unknown |
— | — | GET | 200 | 2.16.204.135:443 | https://th.bing.com/th?id=OCGE.9njb654d39wx_v12_main&w=80&h=80&c=1&rs=1&p=0 | unknown | image | 12.5 Kb | unknown |
— | — | GET | 200 | 2.16.204.135:443 | https://th.bing.com/th?id=OCGE.9p3610rr8qt5_v3_main&w=80&h=80&c=1&rs=1&p=0 | unknown | image | 12.0 Kb | unknown |
— | — | GET | 200 | 2.16.204.135:443 | https://th.bing.com/th?id=OBTQ.BTA3F5A7A467B5115A55C093D4D4B4ABBC0B3FB175279B272BB3AF67D261D81DFF&w=132&h=154&c=1&rs=1&p=0 | unknown | image | 6.31 Kb | unknown |
— | — | GET | 200 | 2.16.204.135:443 | https://th.bing.com/th?id=OCGE.9nbckjw55fsv_v6_main&w=80&h=80&c=1&rs=1&p=0 | unknown | image | 14.3 Kb | unknown |
5568 | SearchApp.exe | GET | 200 | 2.16.204.155:443 | https://th.bing.com/th?id=OCGE.9njb654d39wx_v12_main&w=80&h=80&c=1&rs=1&p=0 | NL | image | 12.5 Kb | whitelisted |
5568 | SearchApp.exe | GET | 200 | 2.16.204.155:443 | https://th.bing.com/th?id=OCGE.9nbckjw55fsv_v6_main&w=80&h=80&c=1&rs=1&p=0 | NL | image | 14.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 23.11.206.114:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.204.150:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
— | — | 2.16.164.42:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.42:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
3344 | svchost.exe | 2.16.164.42:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.155:443 | th.bing.com | AKAMAI-ASN1 | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
th.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
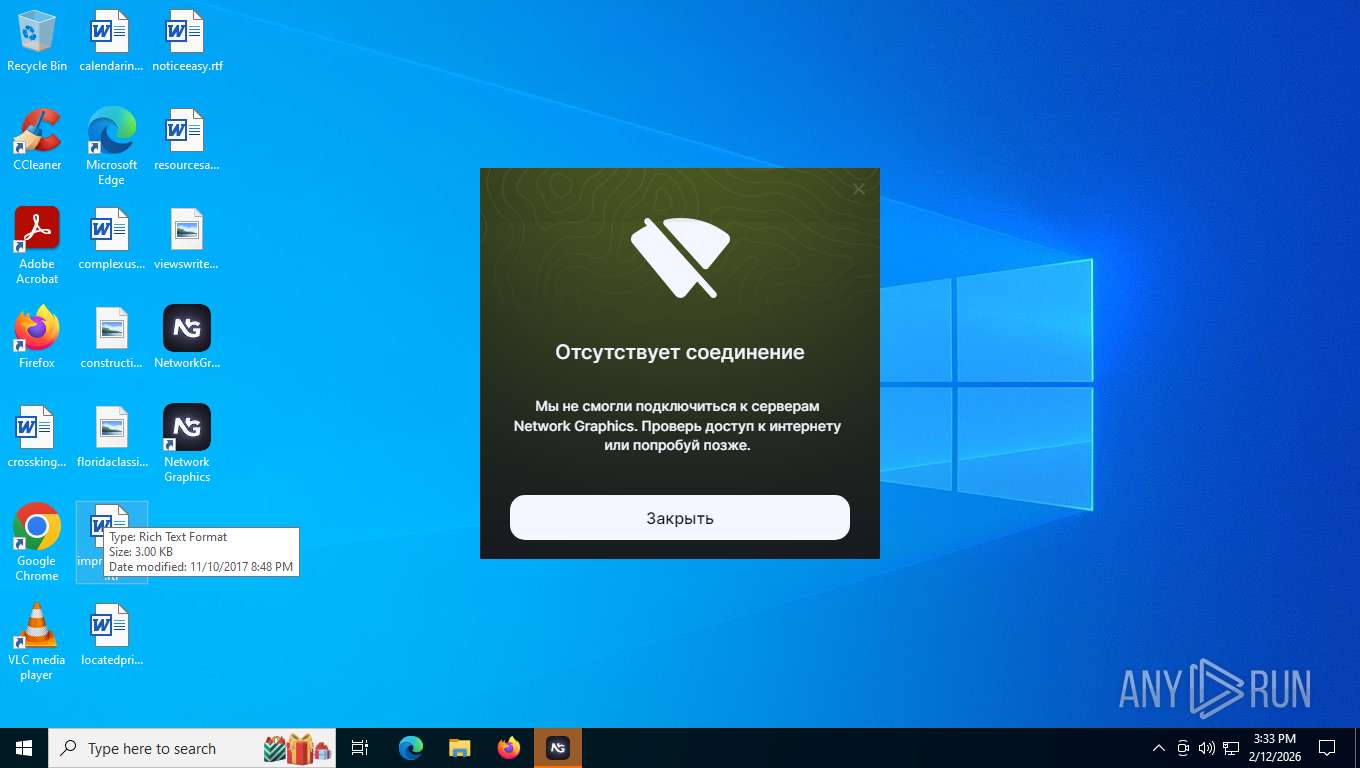
api.ntw.graphics |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |