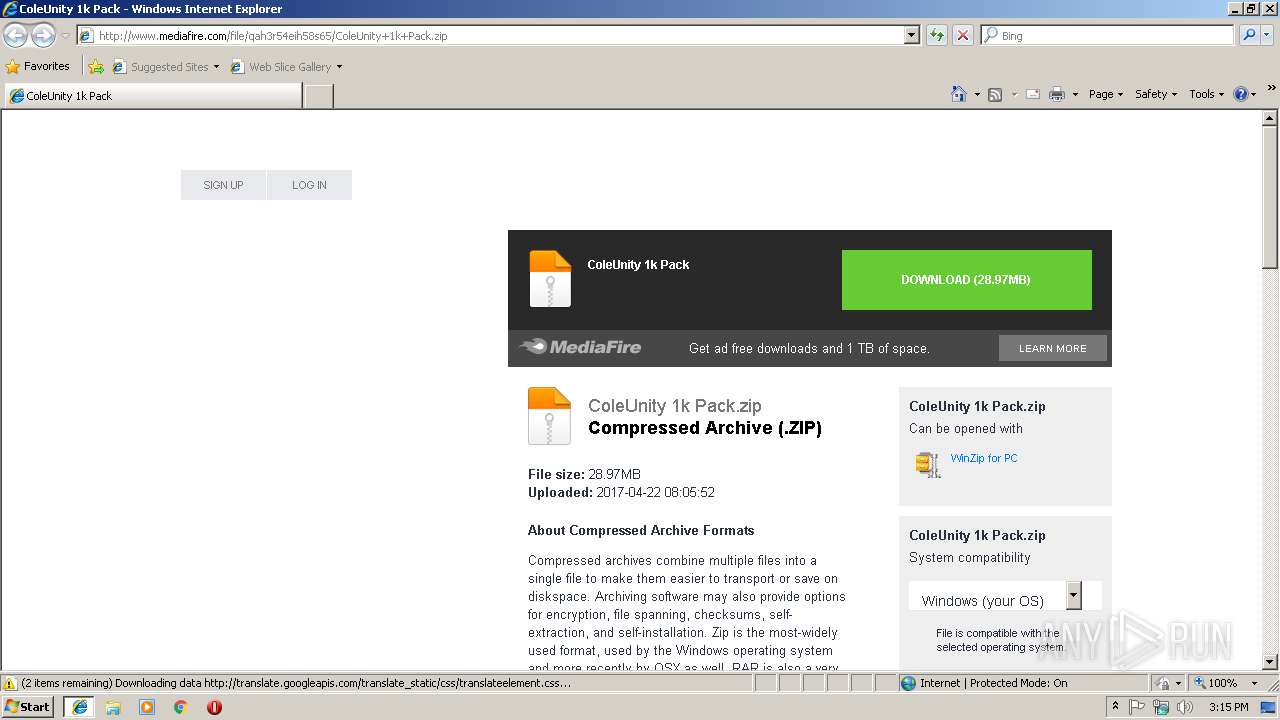
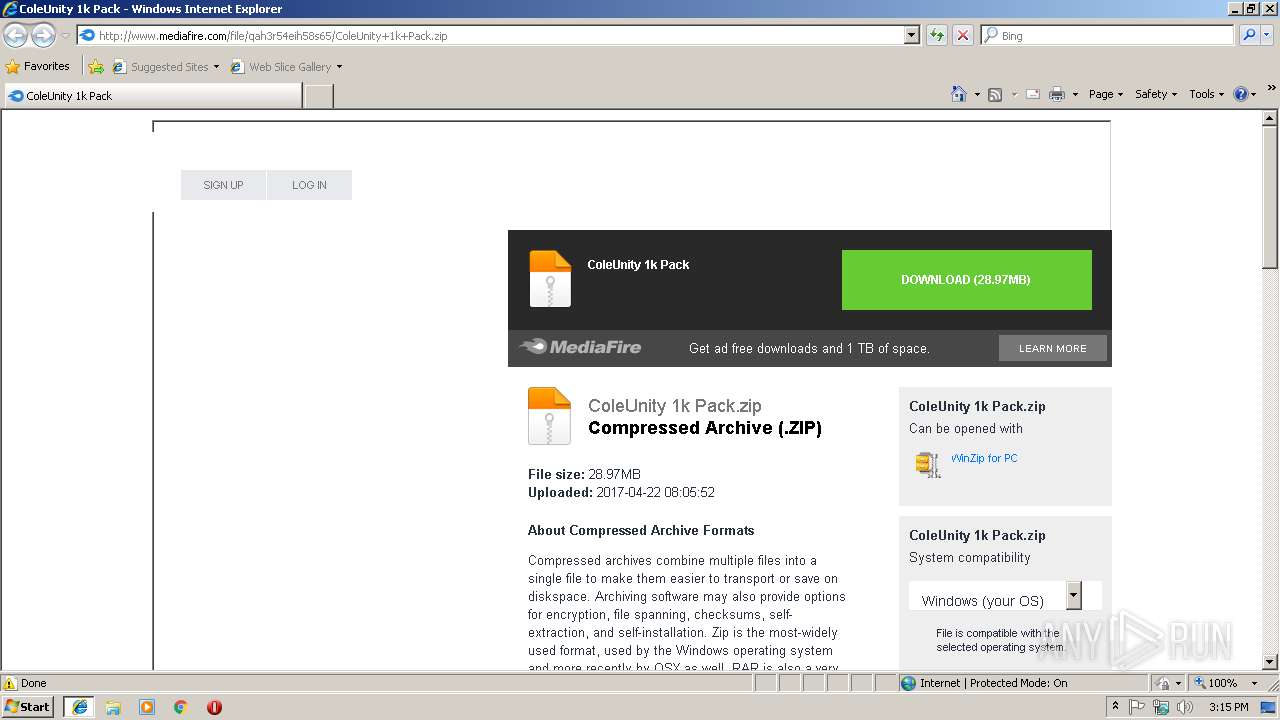
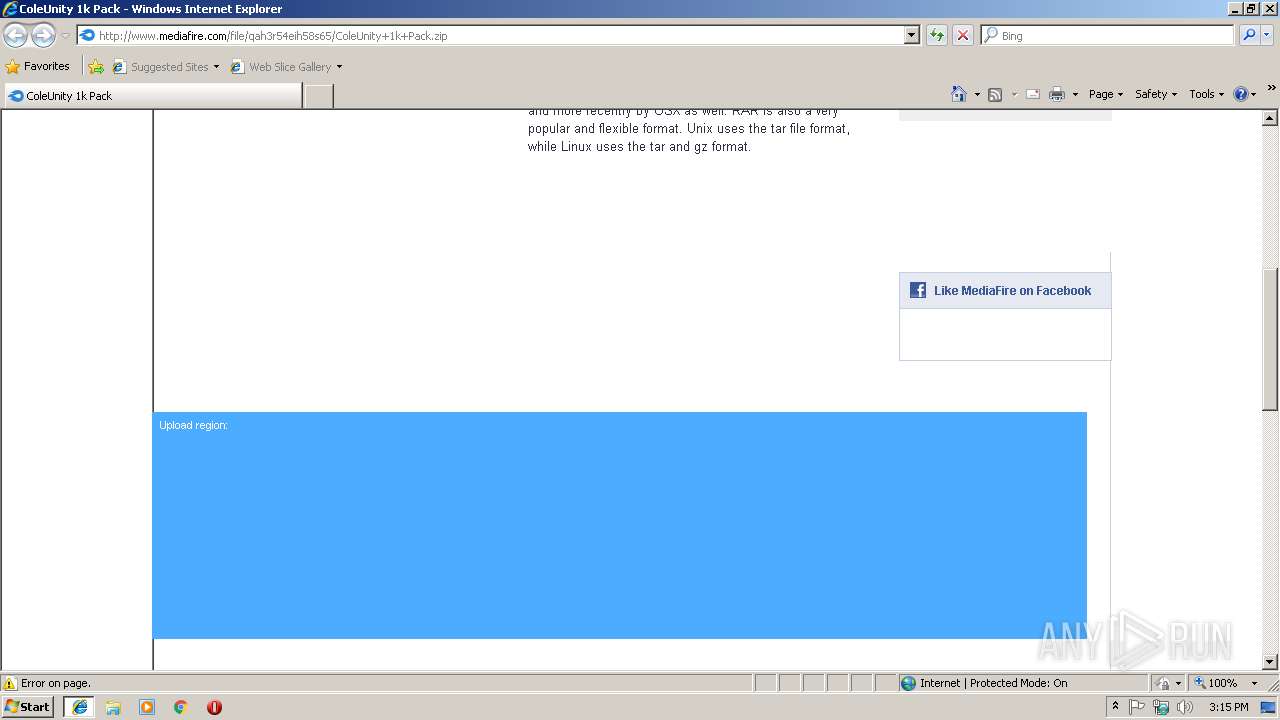
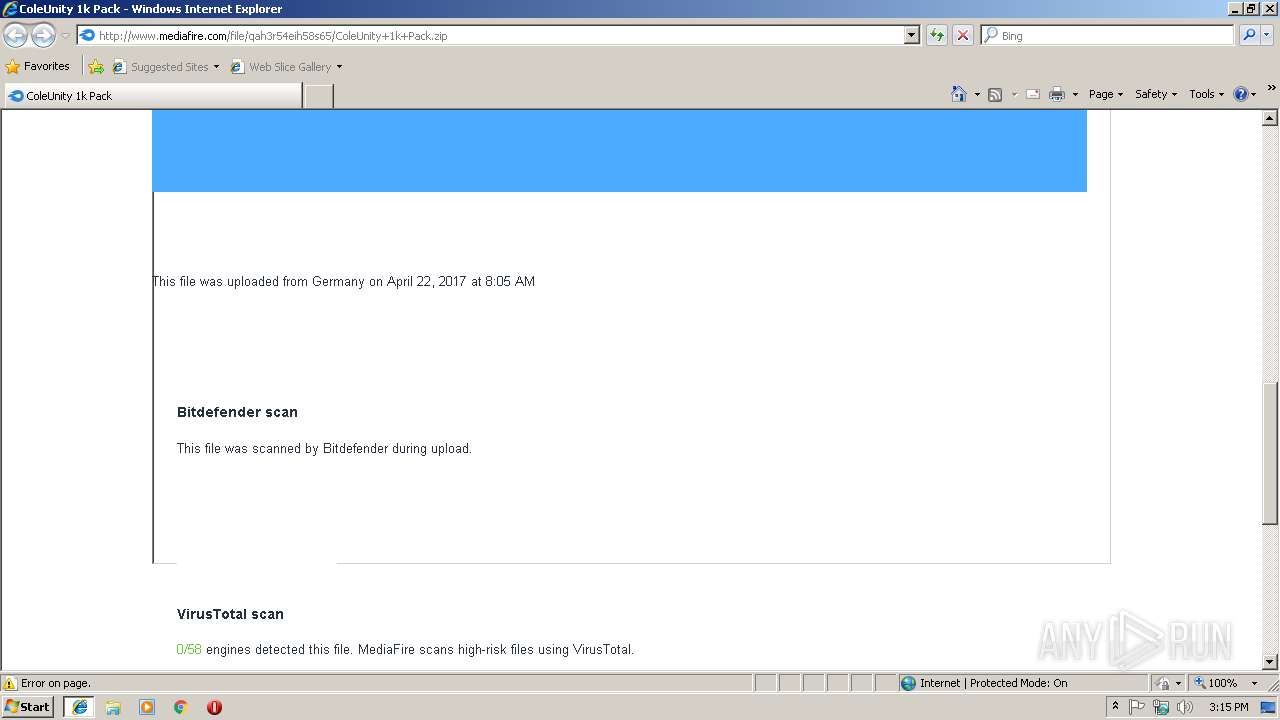
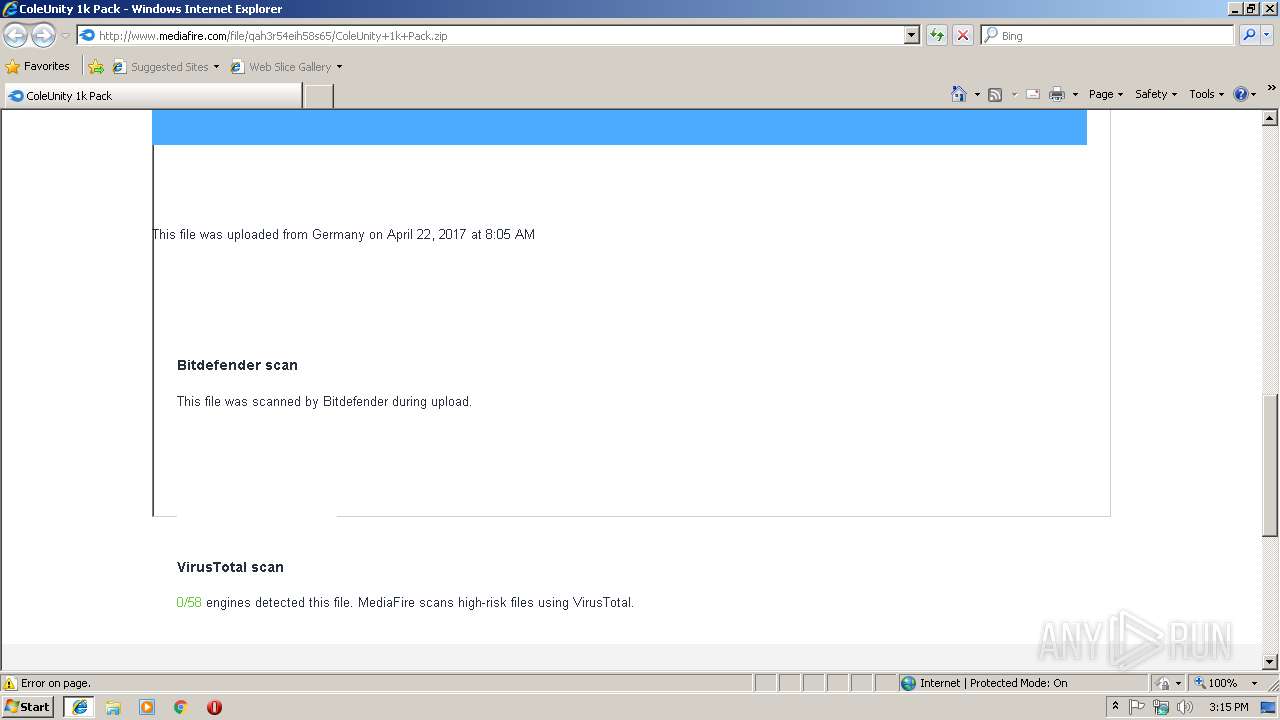
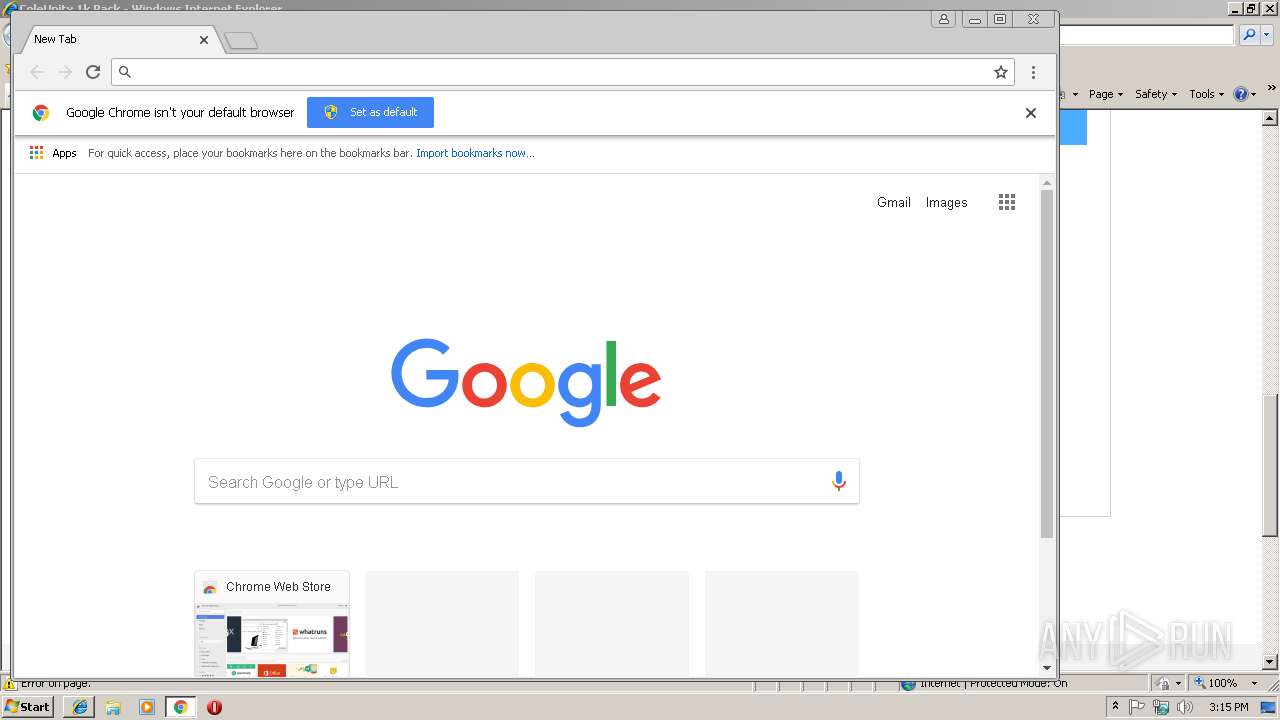
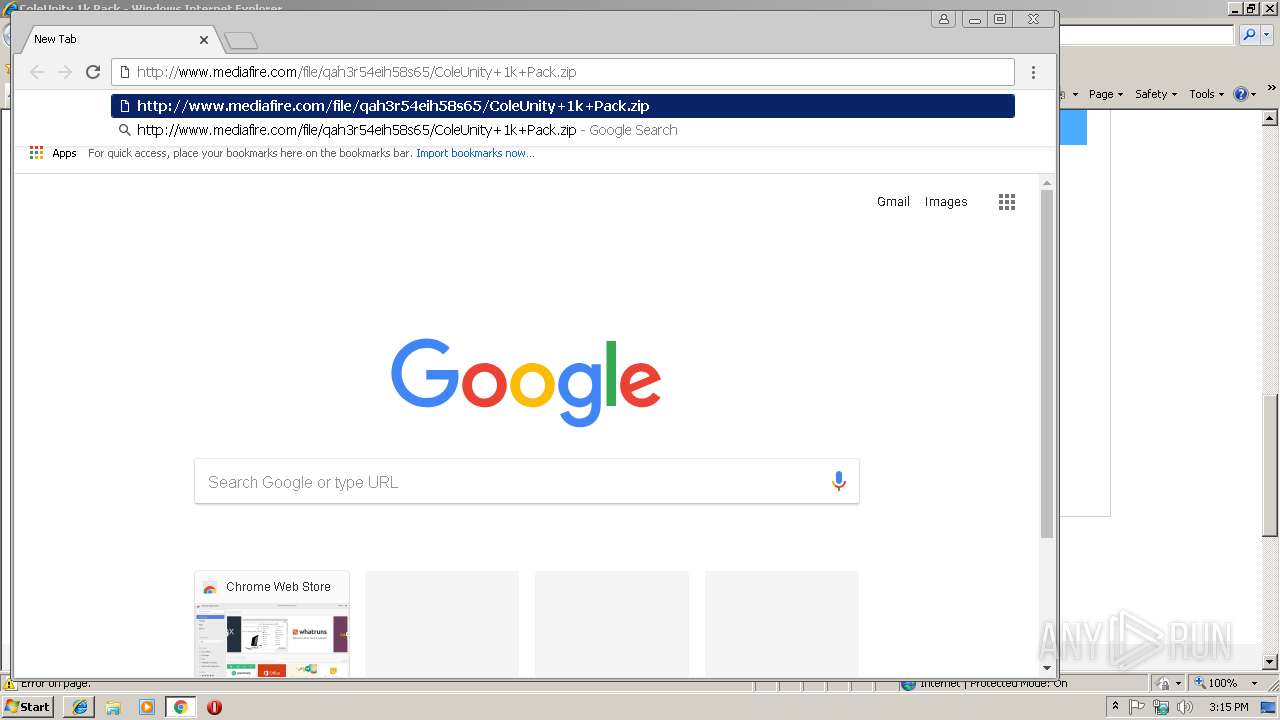
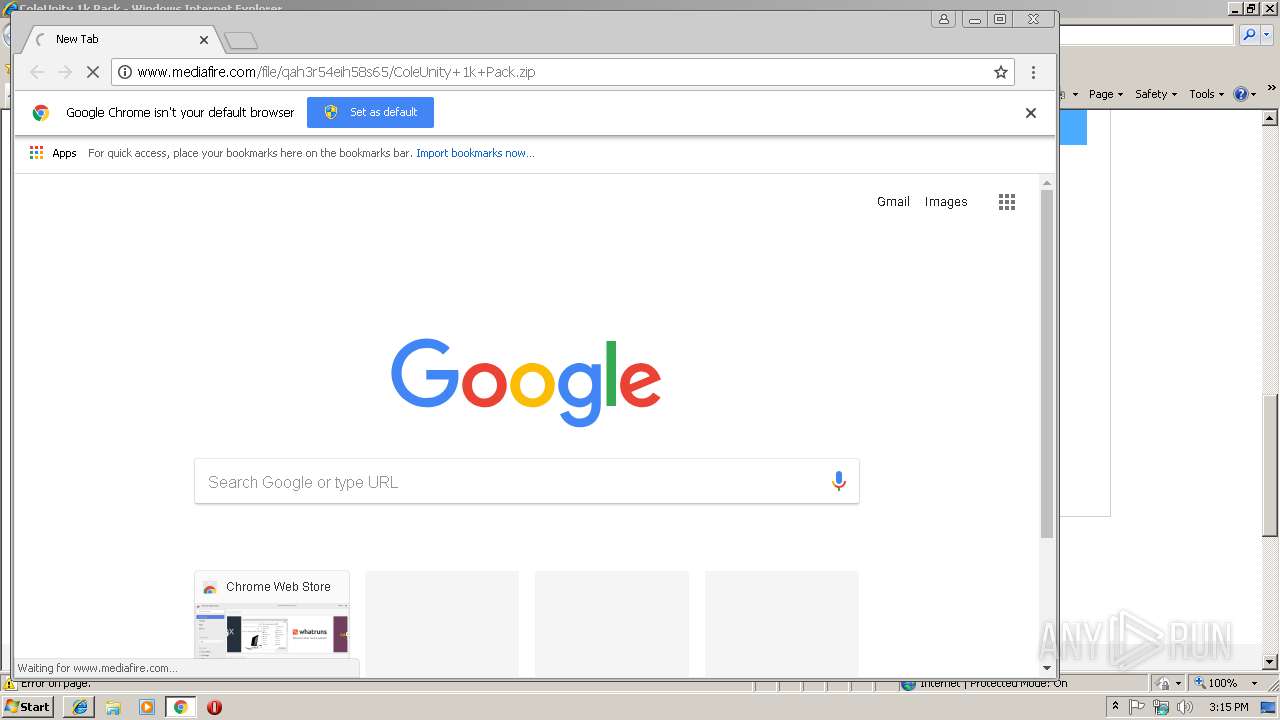
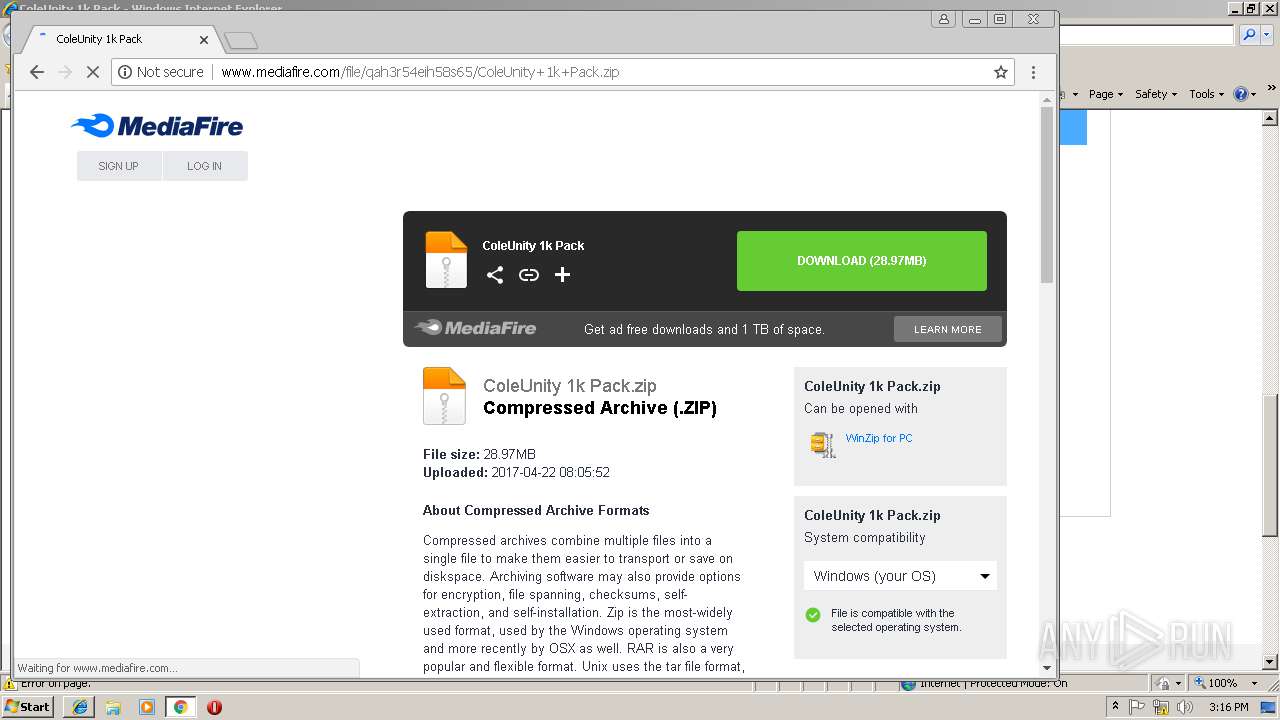
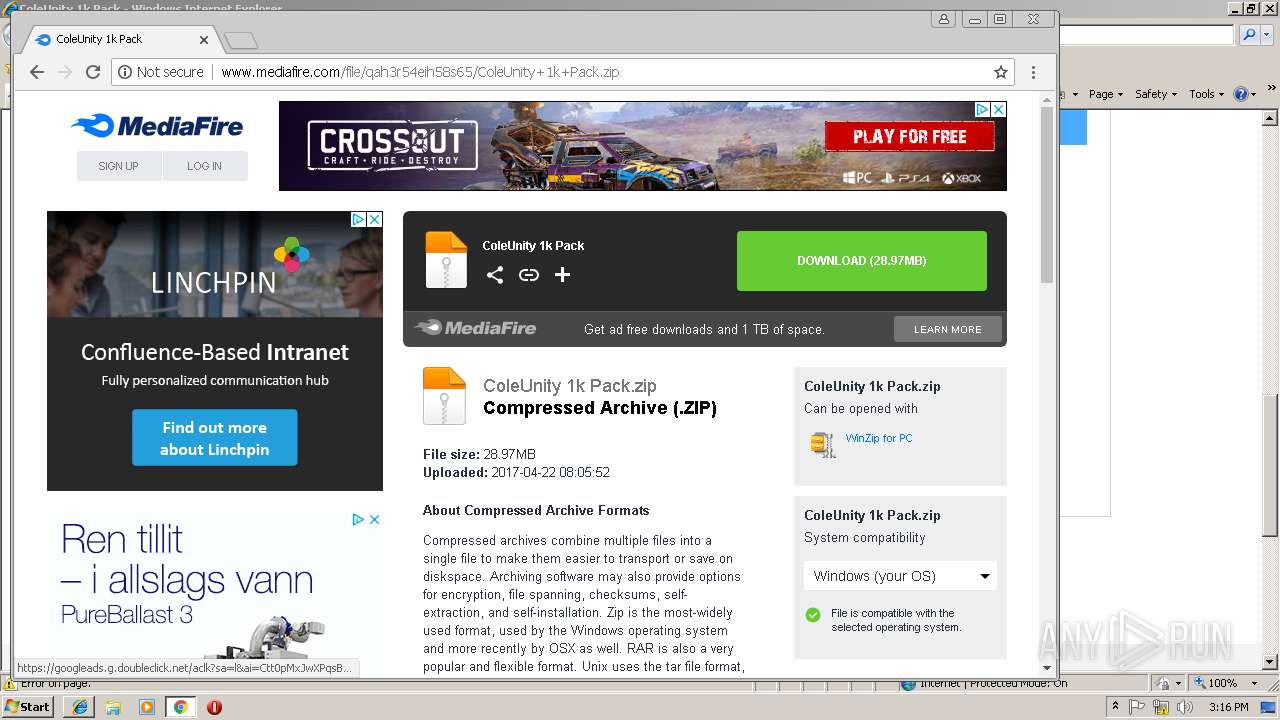
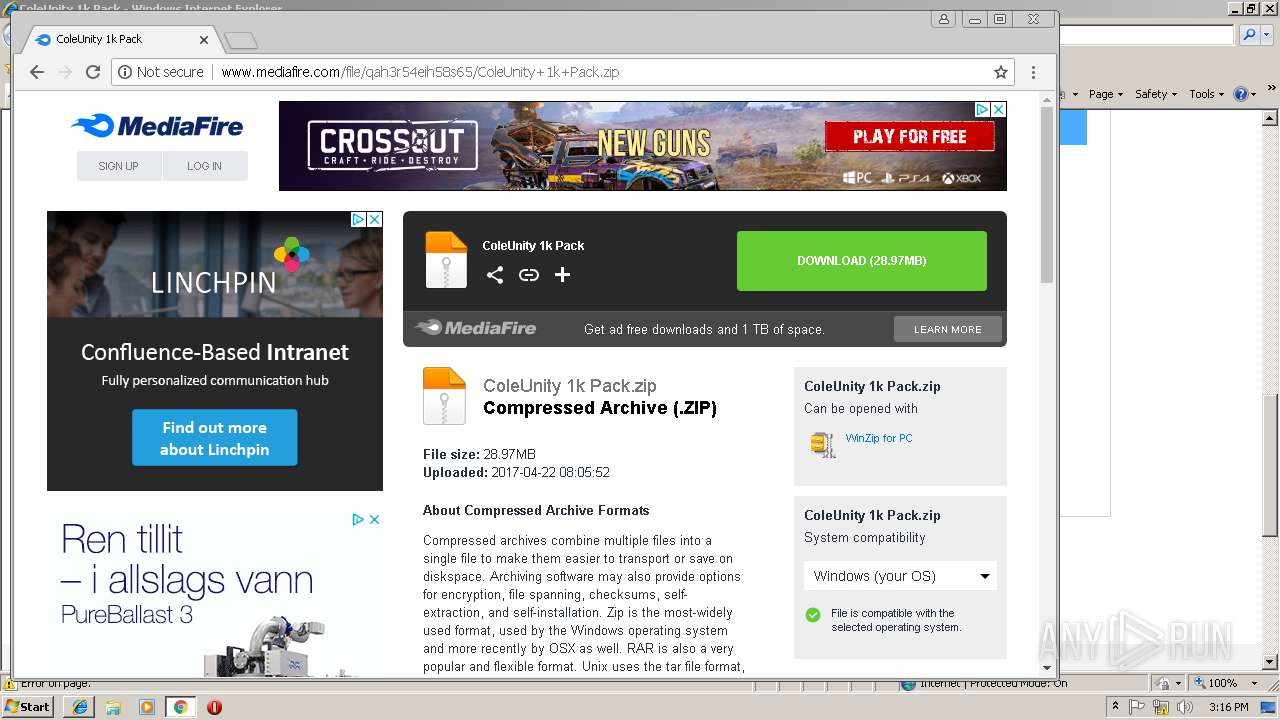
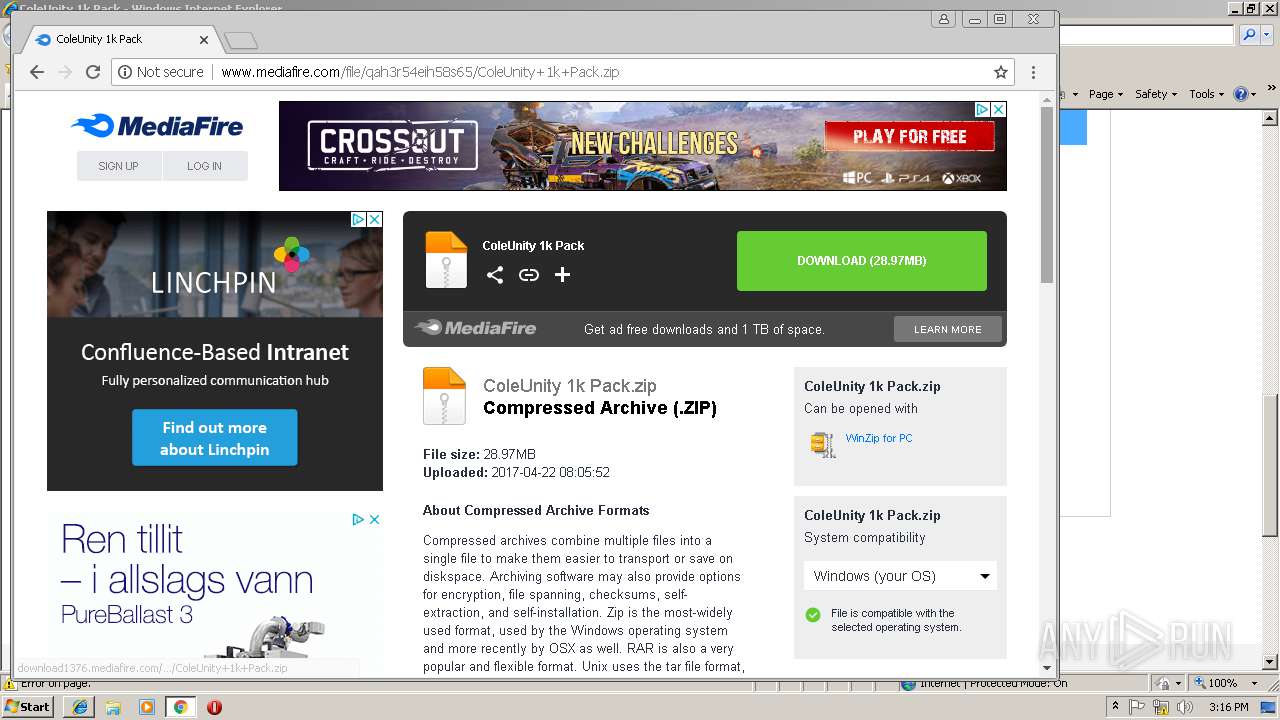
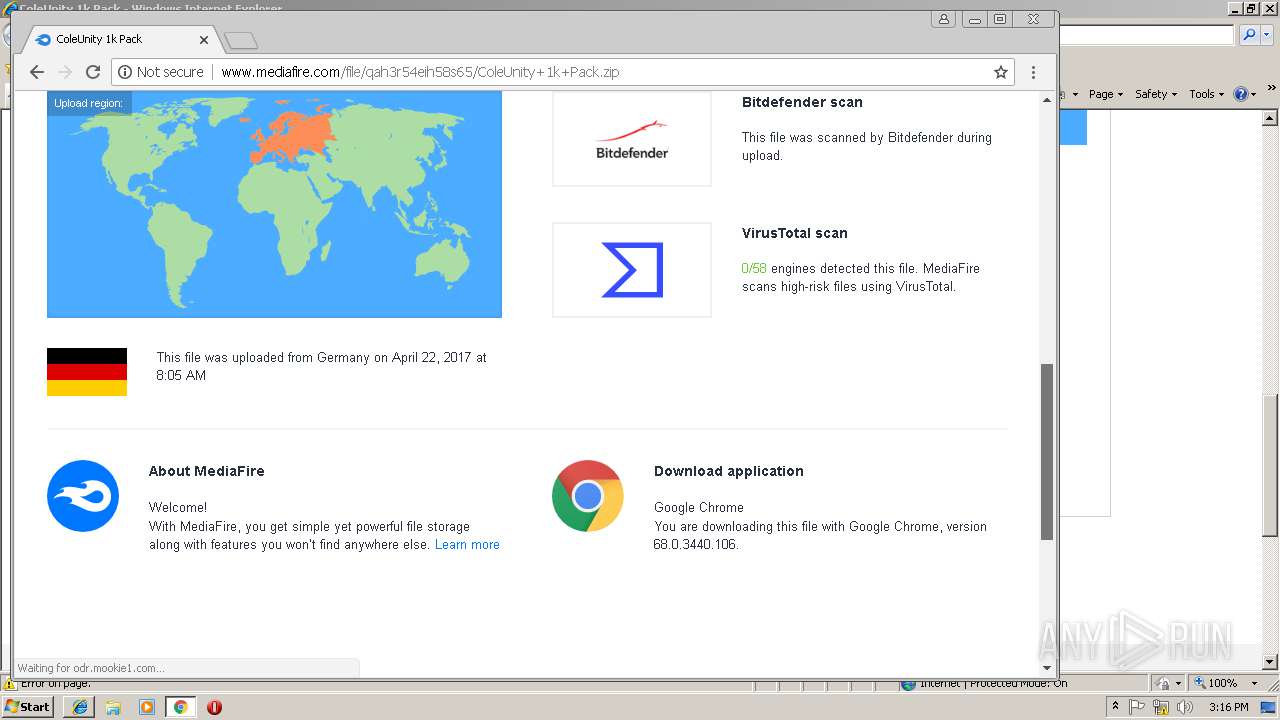
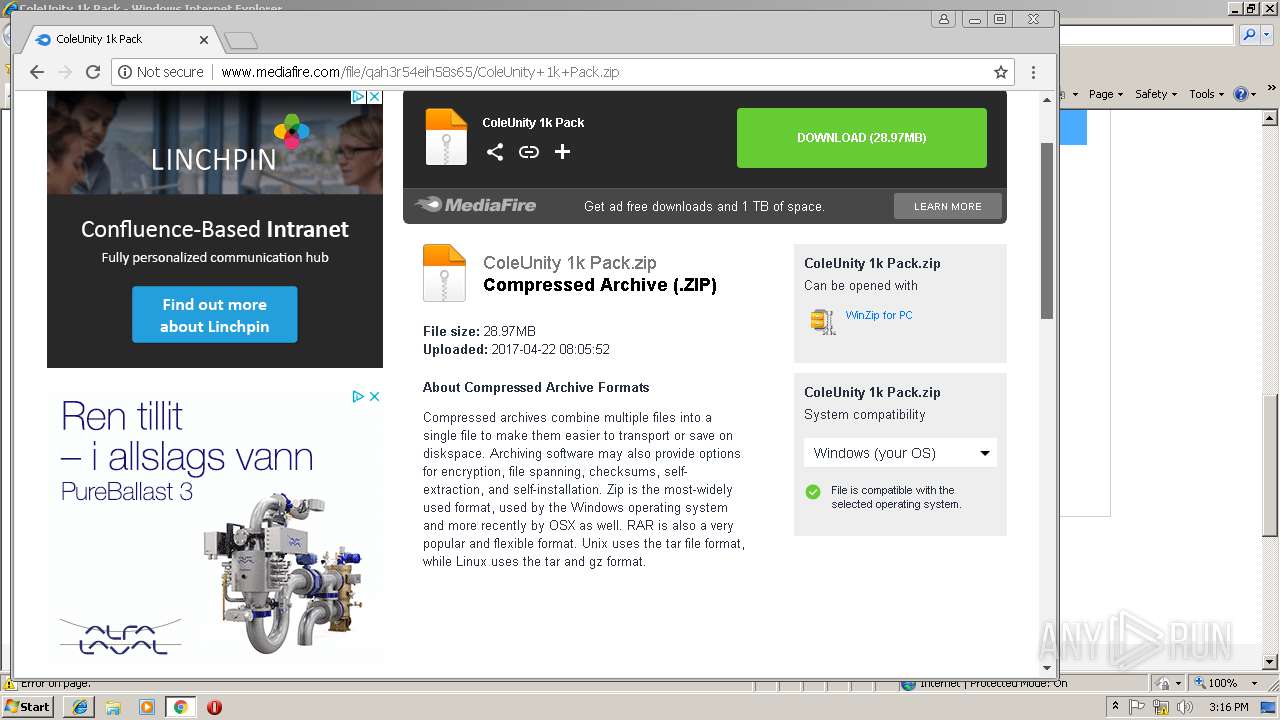
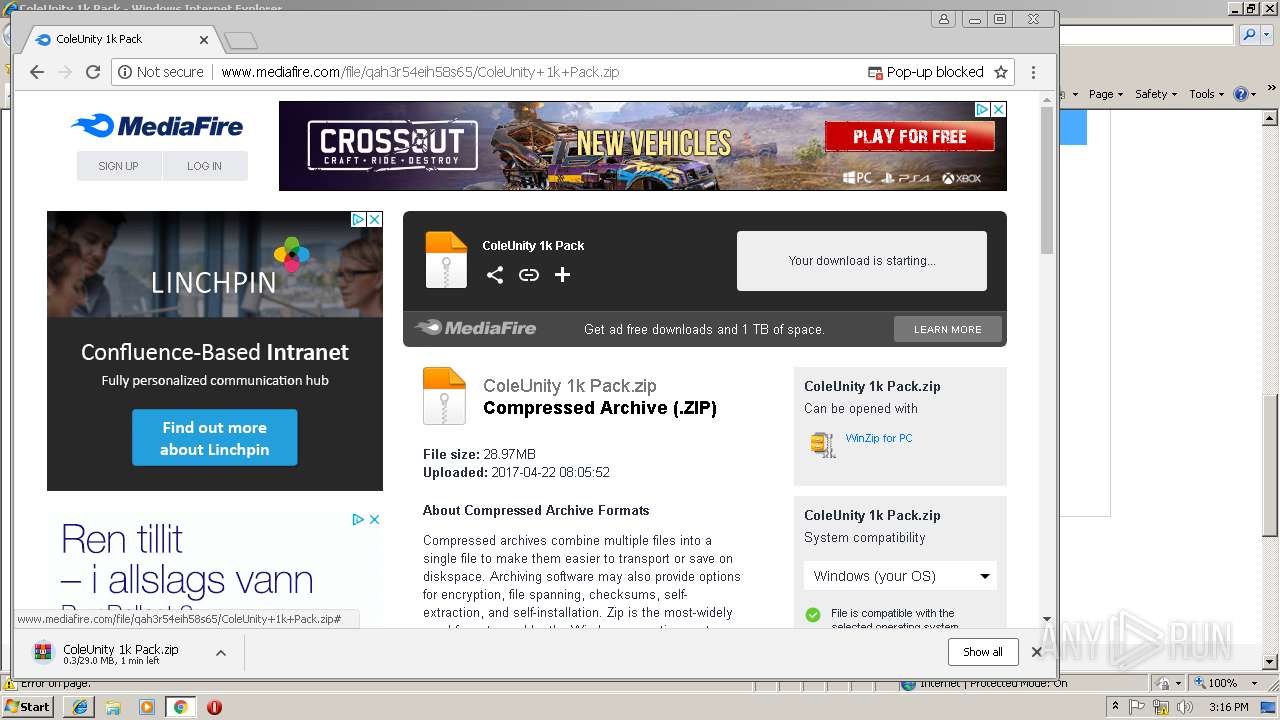
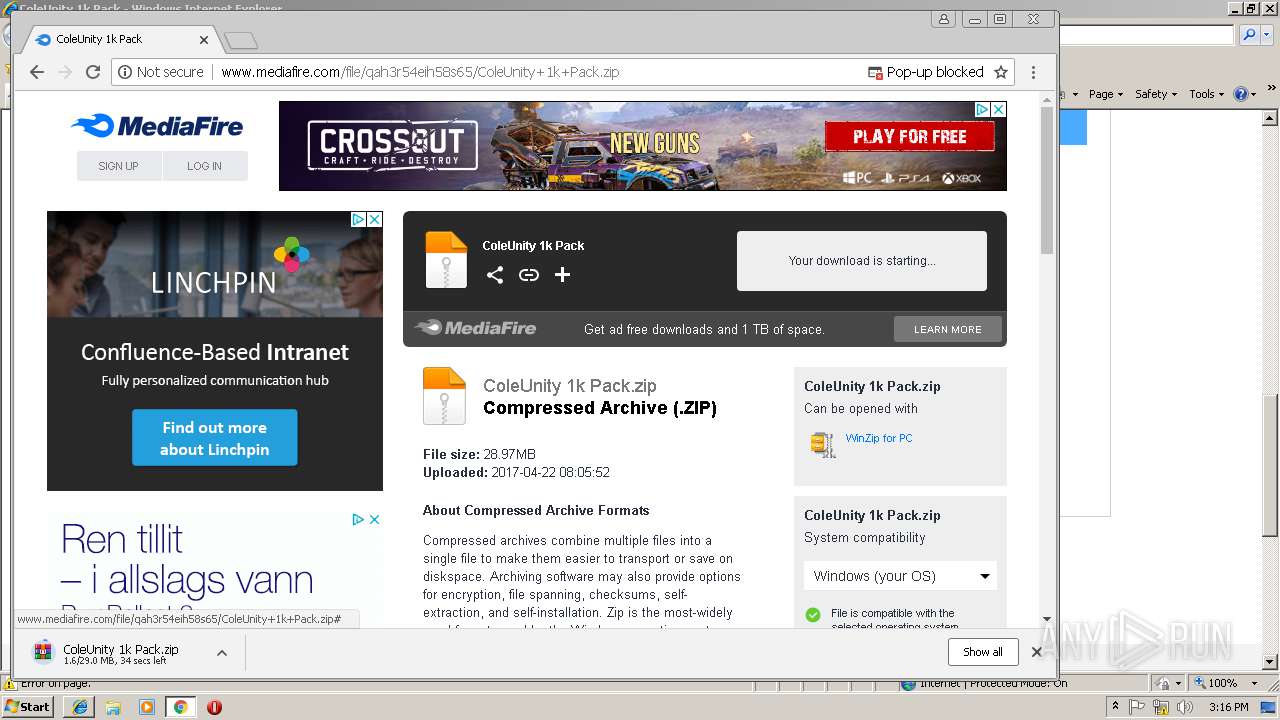
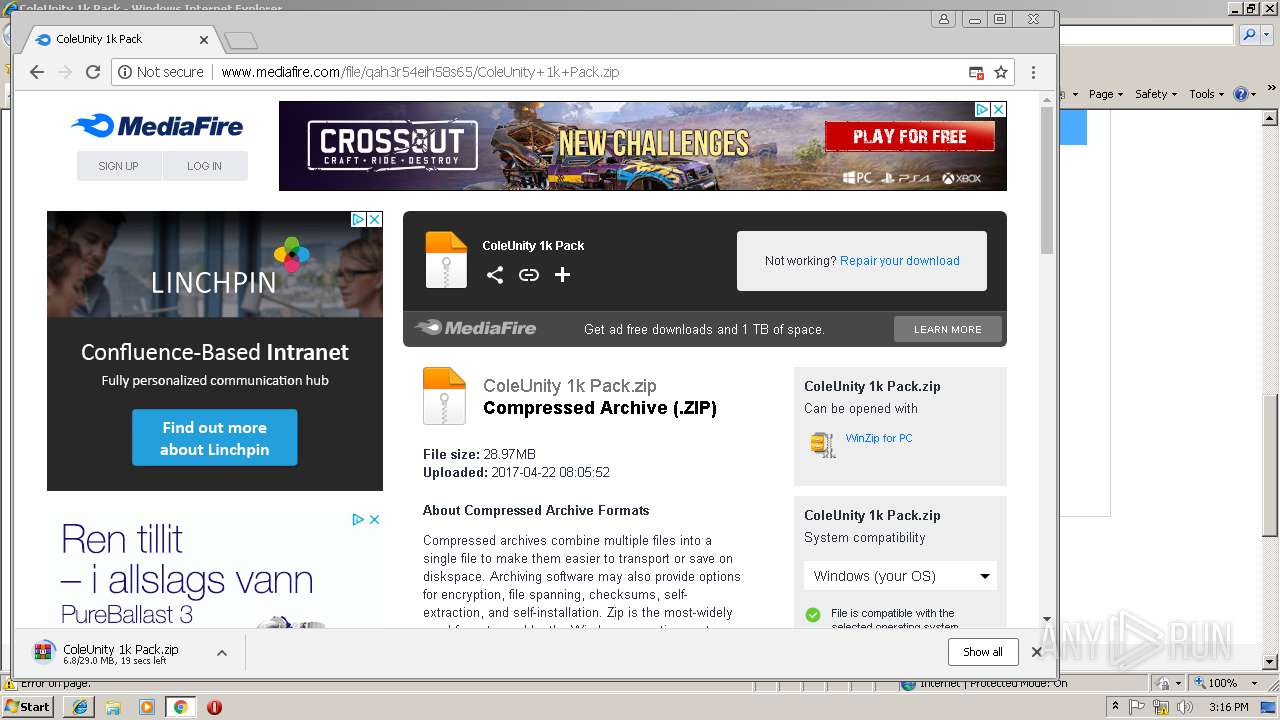
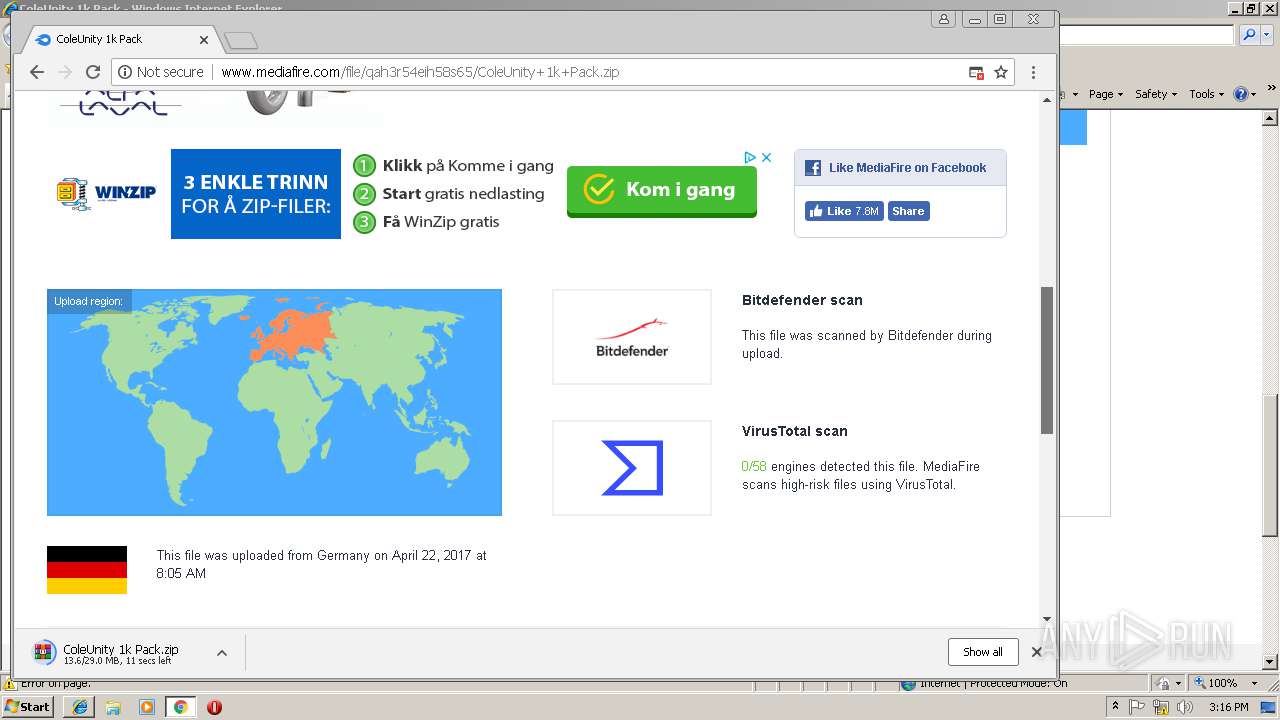
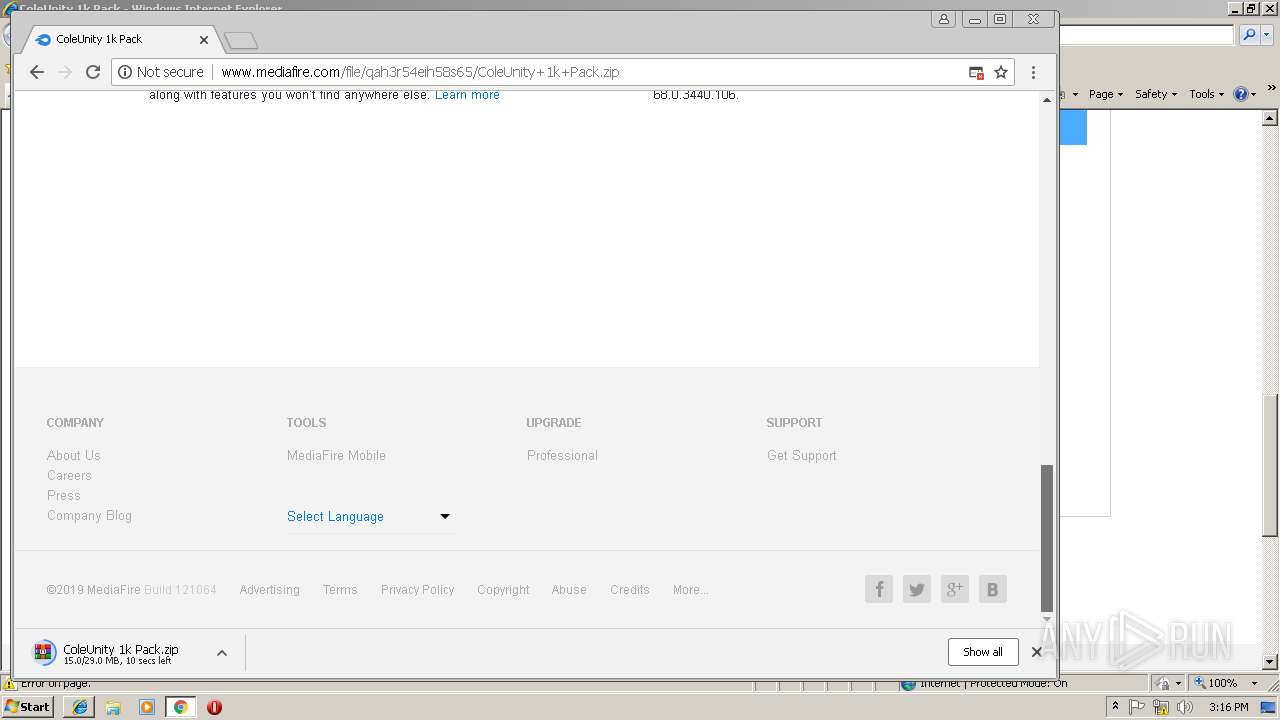
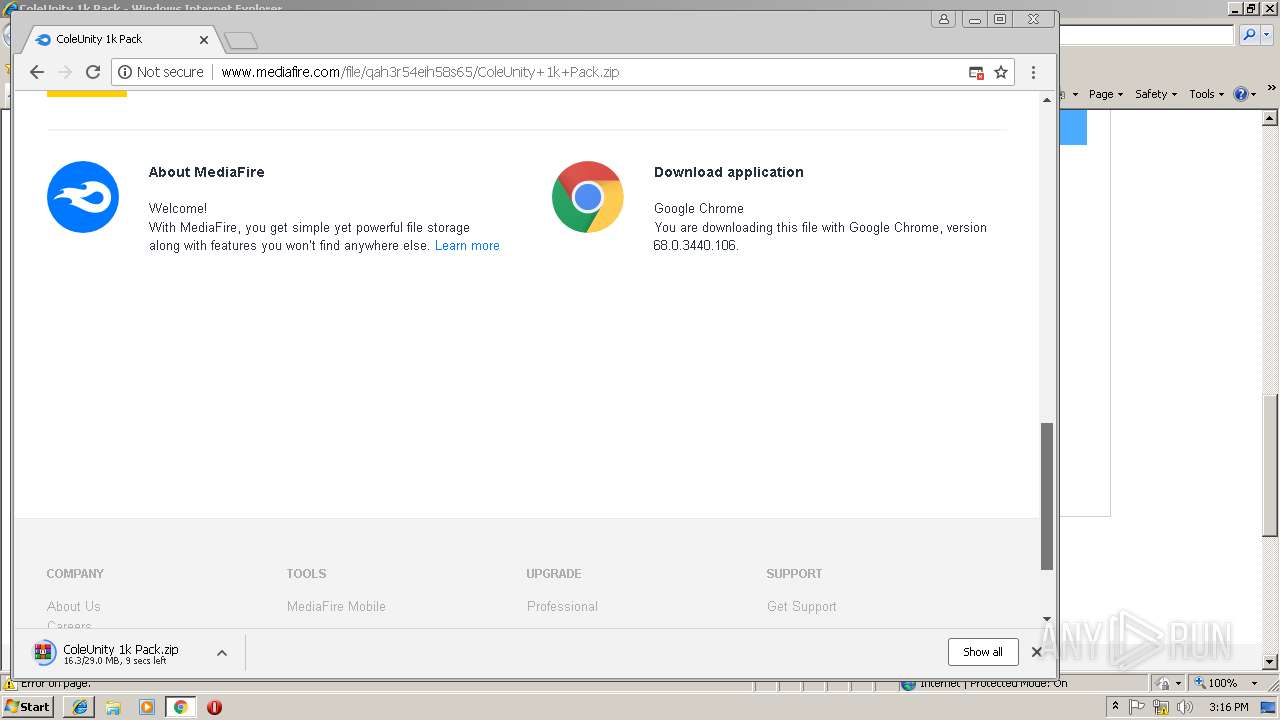
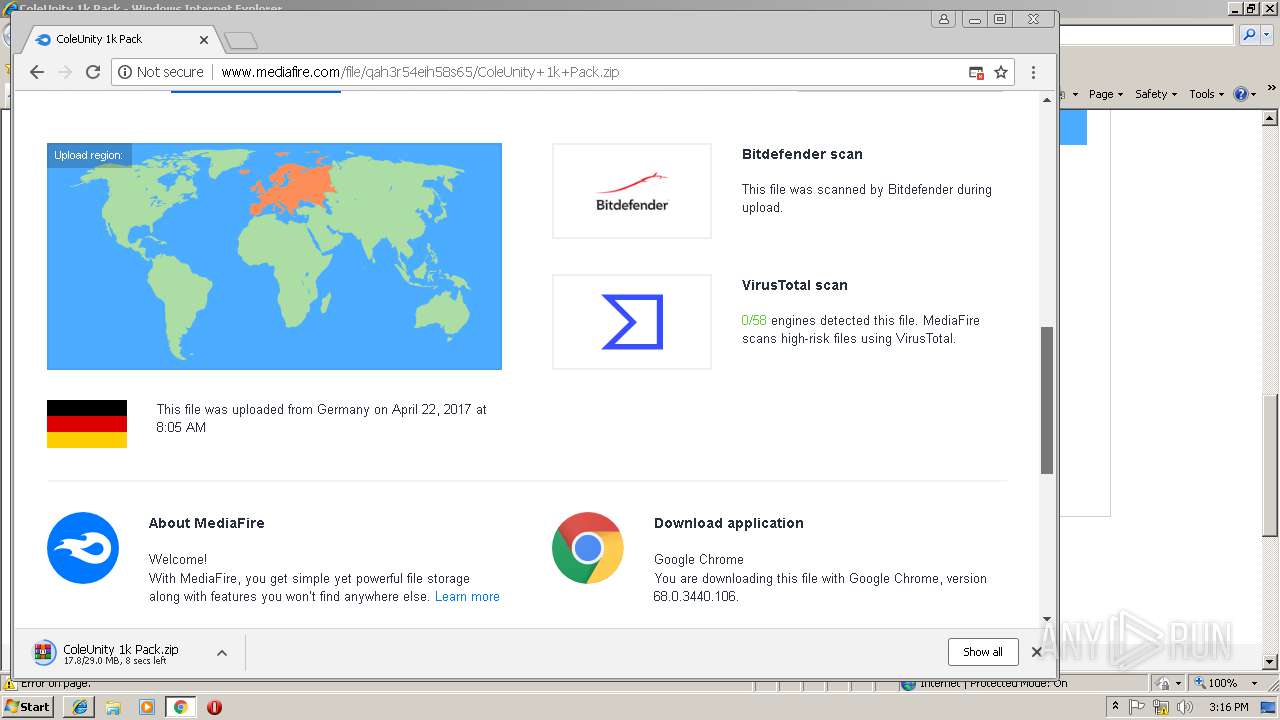
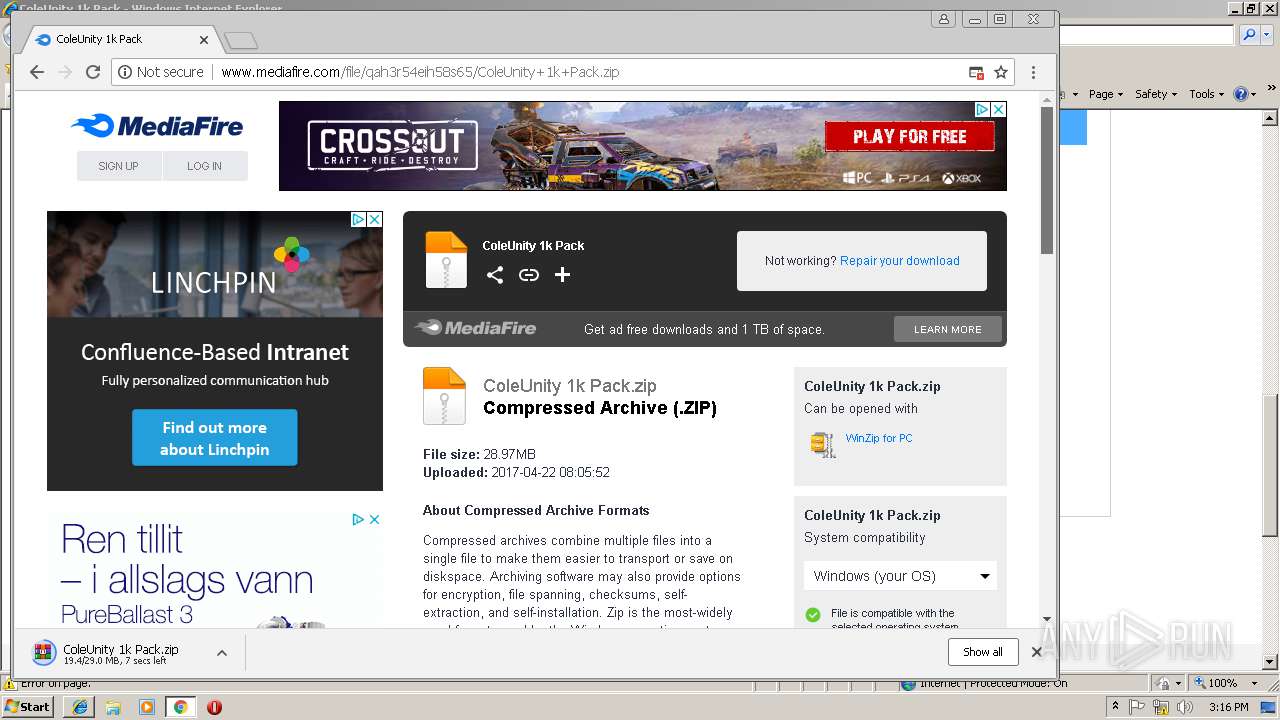
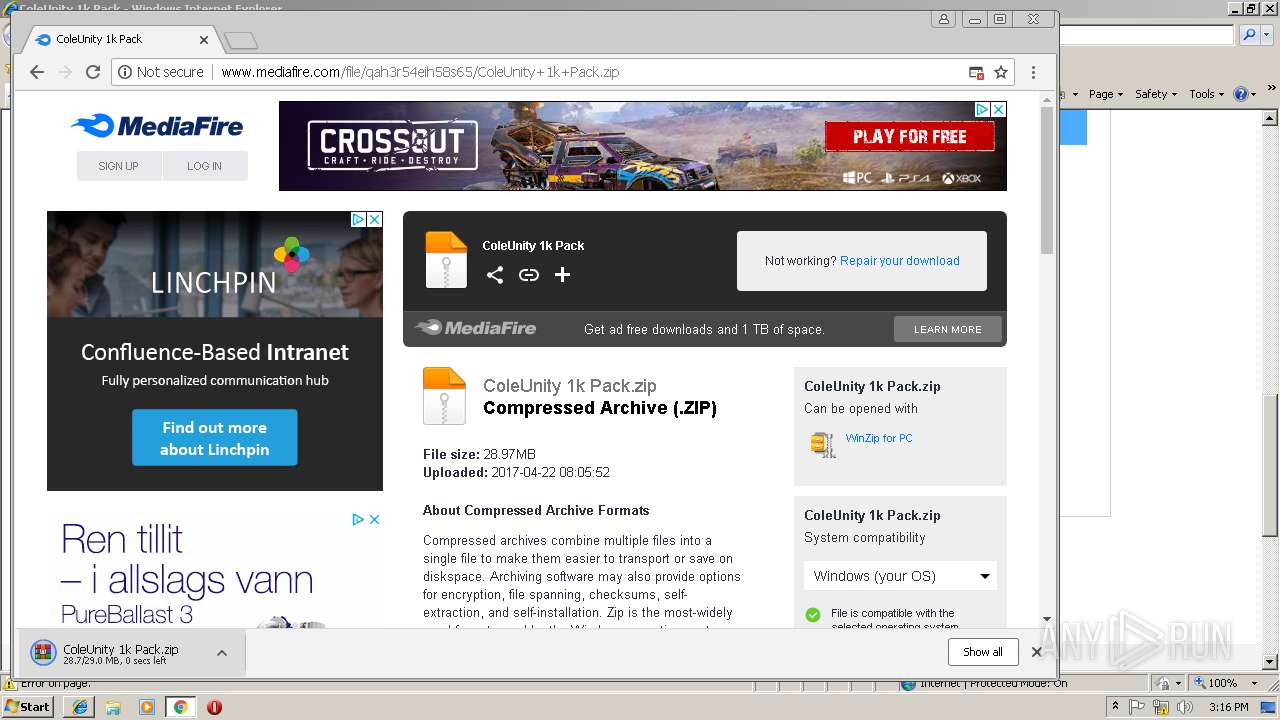
| URL: | http://www.mediafire.com/file/qah3r54eih58s65/ColeUnity+1k+Pack.zip |
| Full analysis: | https://app.any.run/tasks/35e5deff-1ddc-4346-a929-1a06cc703eab |
| Verdict: | Malicious activity |
| Analysis date: | February 22, 2019, 15:14:45 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A5C7BF3BE5D9FBDBDFB36B52730F5B02 |
| SHA1: | 039B65B2F49D663961D2A0270524A1F4FF2F0F05 |
| SHA256: | 2B23EAC4A6261C61CED3FAA3D01EC317F0D478D6662D1239BD90E72A96A19143 |
| SSDEEP: | 3:N1KJS4w3eGUodNQpMNrTO6kcn:Cc4w3eG0pMHwc |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- iexplore.exe (PID: 2980)
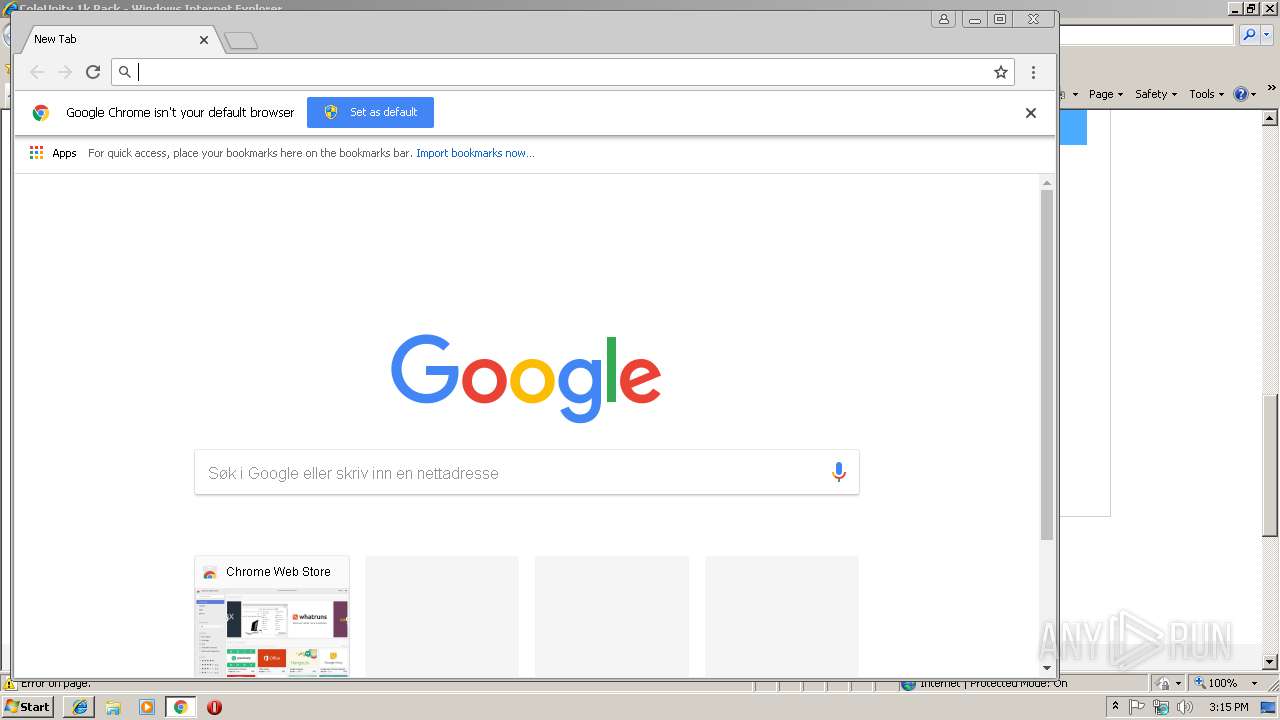
- chrome.exe (PID: 3404)
Reads internet explorer settings
- iexplore.exe (PID: 3248)
Changes internet zones settings
- iexplore.exe (PID: 2980)
Creates files in the user directory
- iexplore.exe (PID: 2980)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 3944)
- iexplore.exe (PID: 3248)
Reads Internet Cache Settings
- iexplore.exe (PID: 3248)
- chrome.exe (PID: 3404)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1040 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --service-pipe-token=B8778E54EE289427276EA3C14C794E24 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=B8778E54EE289427276EA3C14C794E24 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1508 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=E7F1992911A19224644890855C12AD03 --mojo-platform-channel-handle=4588 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2288 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=68.0.3440.106 --initial-client-data=0x78,0x7c,0x80,0x74,0x84,0x6dc500b0,0x6dc500c0,0x6dc500cc | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=96BEC27BE0A1023F23BC556DC86EBDCF --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=96BEC27BE0A1023F23BC556DC86EBDCF --renderer-client-id=6 --mojo-platform-channel-handle=3552 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2360 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5F9947D4F414DA5BFA17D99FB6030305 --mojo-platform-channel-handle=3984 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A18463411498358C083EDF0552087422 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A18463411498358C083EDF0552087422 --renderer-client-id=7 --mojo-platform-channel-handle=3652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=5EF3137F7D089B6FB29A97ECB318D8F8 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 3248 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2980 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=920,15327561891935576778,5986851538245209098,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=9F97017F9FAD1819476D6B54B16EA6FF --mojo-platform-channel-handle=4564 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 043
Read events
907
Write events
130
Delete events
6
Modification events
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {9F792C47-36B4-11E9-BEEC-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 3 | |||
| (PID) Process: | (2980) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070200050016000F000F000200B900 | |||
Executable files
0
Suspicious files
78
Text files
122
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2980 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2980 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mediafire[1].txt | — | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ColeUnity+1k+Pack[1].zip | — | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\icons_sprite[1].svg | — | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\U2ZG9DE0\ads[1].php | — | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\OCDM6JB6\ColeUnity+1k+Pack[1].htm | html | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\apps_list_sprite-v3[1].png | image | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\admin@mediafire[2].txt | text | |
MD5:— | SHA256:— | |||
| 3248 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\f[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
106
TCP/UDP connections
131
DNS requests
91
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3248 | iexplore.exe | GET | — | 104.19.194.29:80 | http://www.mediafire.com/images/icons/svg_light/icons_sprite.svg | US | — | — | shared |
3248 | iexplore.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/file/qah3r54eih58s65/ColeUnity+1k+Pack.zip | US | html | 48.4 Kb | shared |
3248 | iexplore.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/templates/linkto/ads.php?o=0&d=1&t=0 | US | html | 3.25 Kb | shared |
3248 | iexplore.exe | GET | 200 | 216.58.205.238:80 | http://translate.google.com/translate_a/element.js?cb=googFooterTranslate | US | text | 728 b | whitelisted |
3248 | iexplore.exe | GET | 200 | 104.17.72.92:80 | http://cdn.engine.addroplet.com/Scripts/infinity.js.aspx?guid=5ff0fb62-0643-4ff1-aaee-c737f9ffc0e0 | US | text | 55.9 Kb | whitelisted |
3248 | iexplore.exe | GET | 200 | 104.19.194.29:80 | http://static.mediafire.com/images/backgrounds/download/apps_list_sprite-v3.png | US | image | 7.36 Kb | shared |
3248 | iexplore.exe | GET | 302 | 216.58.206.14:80 | http://www.google-analytics.com/r/collect?v=1&_v=j73&a=1068112849&t=pageview&_s=1&dl=http%3A%2F%2Fwww.mediafire.com%2Ffile%2Fqah3r54eih58s65%2FColeUnity%2B1k%2BPack.zip&ul=en-us&de=utf-8&dt=ColeUnity%201k%20Pack&sd=32-bit&sr=1280x720&vp=1260x560&je=0&fl=26.0%20r0&_u=YEBAAE~&jid=1811892832&gjid=1835530465&cid=720814588.1550848505&tid=UA-829541-1&_gid=201053685.1550848505&_r=1&cd1=unregistered&cd7=legacy&cd3=archive&cd4=1&cd5=zip&cd8=%2F50%2F100%2F&z=827062212 | US | html | 415 b | whitelisted |
3248 | iexplore.exe | GET | 200 | 216.58.210.10:80 | http://translate.googleapis.com/translate_static/js/element/main.js | US | text | 1.49 Kb | whitelisted |
3248 | iexplore.exe | GET | 200 | 216.58.210.10:80 | http://translate.googleapis.com/element/TE_20181015_01/e/js/element/element_main.js | US | html | 86.3 Kb | whitelisted |
3248 | iexplore.exe | GET | 200 | 104.25.227.6:80 | http://2hanwriten.com/0/5ff0fb62-0643-4ff1-aaee-c737f9ffc0e0/92532/asynch/null/123/null/true/0/2/1260/560/null/Tag.a1b | US | text | 967 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2980 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3248 | iexplore.exe | 104.19.194.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
3248 | iexplore.exe | 216.58.206.14:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
3248 | iexplore.exe | 216.58.205.238:80 | translate.google.com | Google Inc. | US | whitelisted |
3248 | iexplore.exe | 172.217.16.168:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
3248 | iexplore.exe | 104.17.72.92:80 | cdn.engine.addroplet.com | Cloudflare Inc | US | shared |
3248 | iexplore.exe | 216.58.210.10:80 | translate.googleapis.com | Google Inc. | US | whitelisted |
3248 | iexplore.exe | 74.125.133.156:443 | stats.g.doubleclick.net | Google Inc. | US | whitelisted |
2980 | iexplore.exe | 104.19.194.29:80 | www.mediafire.com | Cloudflare Inc | US | shared |
3248 | iexplore.exe | 104.25.227.6:80 | 2hanwriten.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.mediafire.com |
| shared |
www.bing.com |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
static.mediafire.com |
| shared |
translate.google.com |
| whitelisted |
cdn.engine.addroplet.com |
| whitelisted |
translate.googleapis.com |
| whitelisted |
stats.g.doubleclick.net |
| whitelisted |
2hanwriten.com |
| whitelisted |