| File name: | Release.exe |
| Full analysis: | https://app.any.run/tasks/bad9e613-e44e-42c5-b73f-3eb6195a1f9a |
| Verdict: | Malicious activity |
| Analysis date: | February 10, 2024, 09:25:03 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B25A3878793963A4479E74FDF60AE03E |
| SHA1: | 68B511E35868F8C7D7868198D20DC978E4E3A3A3 |
| SHA256: | 2B1A022CEE7D88FAB206A4F355E8EFABEDEB319EDABFE3784A8750E3C8971B75 |
| SSDEEP: | 12288:EjV8Uox9oUFydRxsQPyhv7qtoc3J851Jq//mq//06yl+XEw:rAY5qtPJ85PnLJl+Uw |
MALICIOUS
Drops the executable file immediately after the start
- Release.exe (PID: 3672)
SUSPICIOUS
Reads security settings of Internet Explorer
- Release.exe (PID: 3672)
- proxy2.exe (PID: 3536)
Reads the Internet Settings
- Release.exe (PID: 3672)
- proxy2.exe (PID: 3536)
- sysproxy.exe (PID: 2692)
- sysproxy.exe (PID: 2960)
- sysproxy.exe (PID: 2832)
- sysproxy.exe (PID: 980)
- sysproxy.exe (PID: 3980)
- sysproxy.exe (PID: 844)
Executable content was dropped or overwritten
- Release.exe (PID: 3672)
Reads Microsoft Outlook installation path
- proxy2.exe (PID: 3536)
Reads Internet Explorer settings
- proxy2.exe (PID: 3536)
Reads settings of System Certificates
- proxy2.exe (PID: 3536)
Checks Windows Trust Settings
- proxy2.exe (PID: 3536)
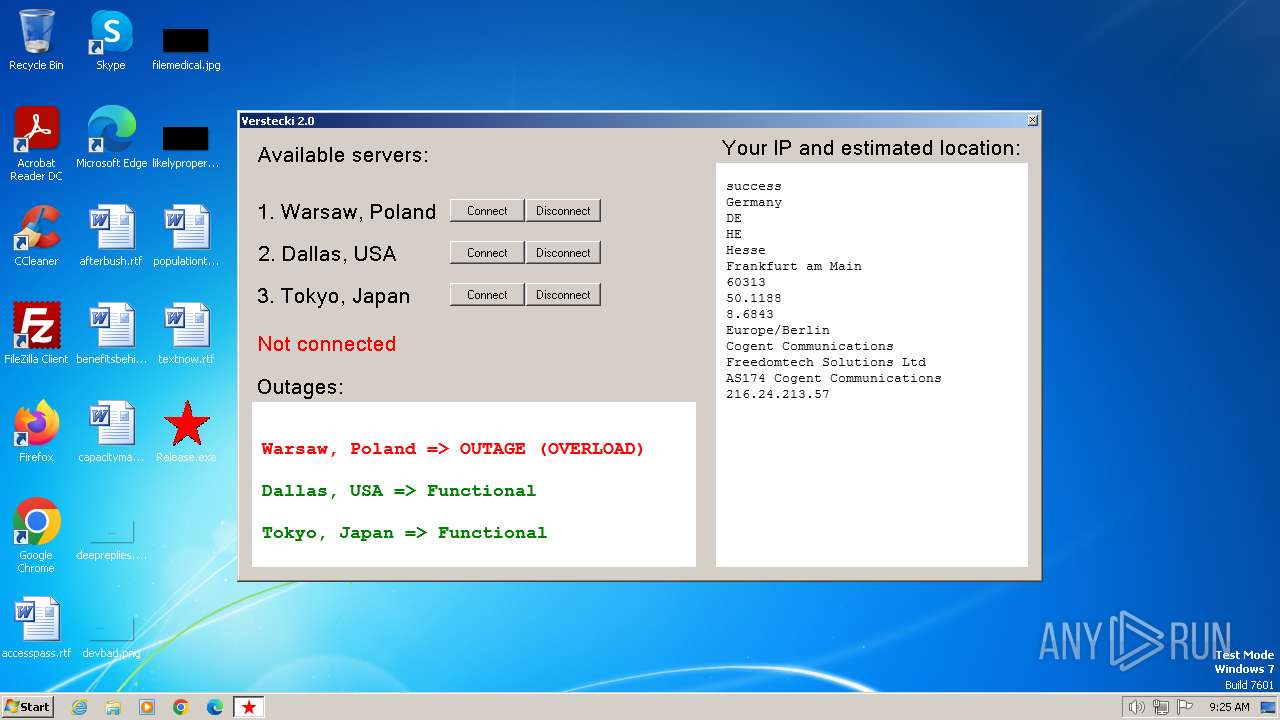
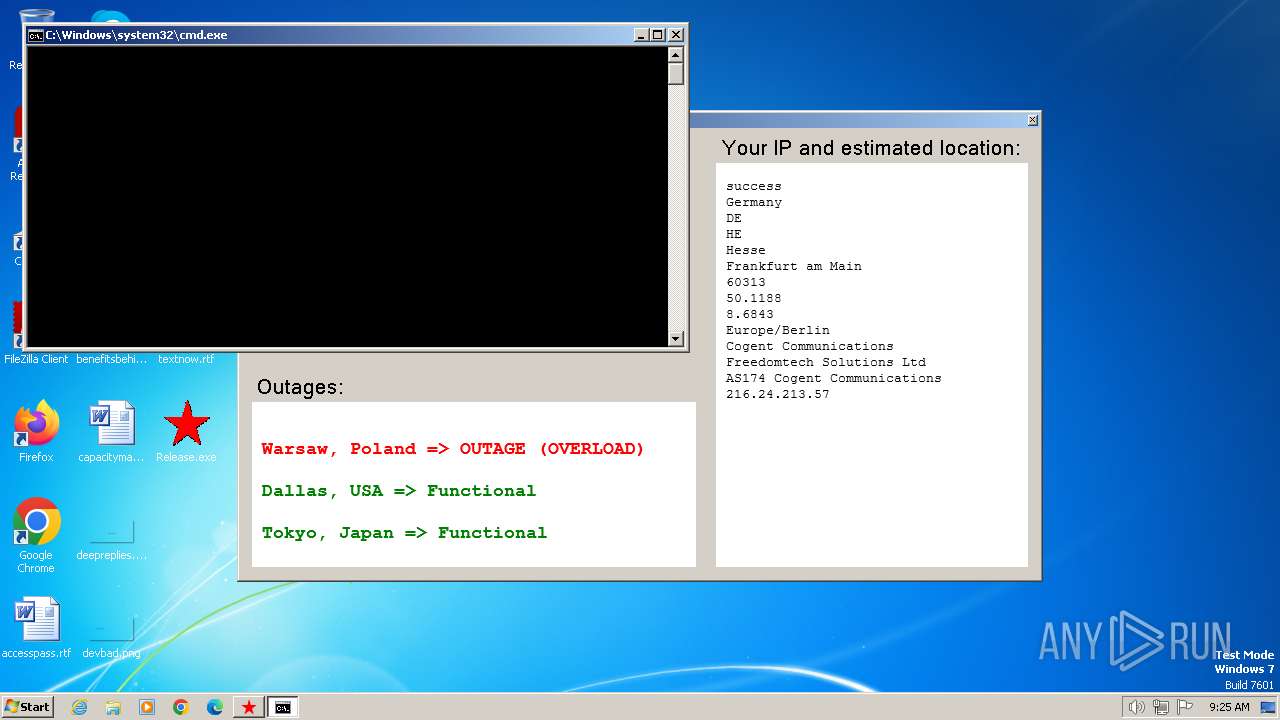
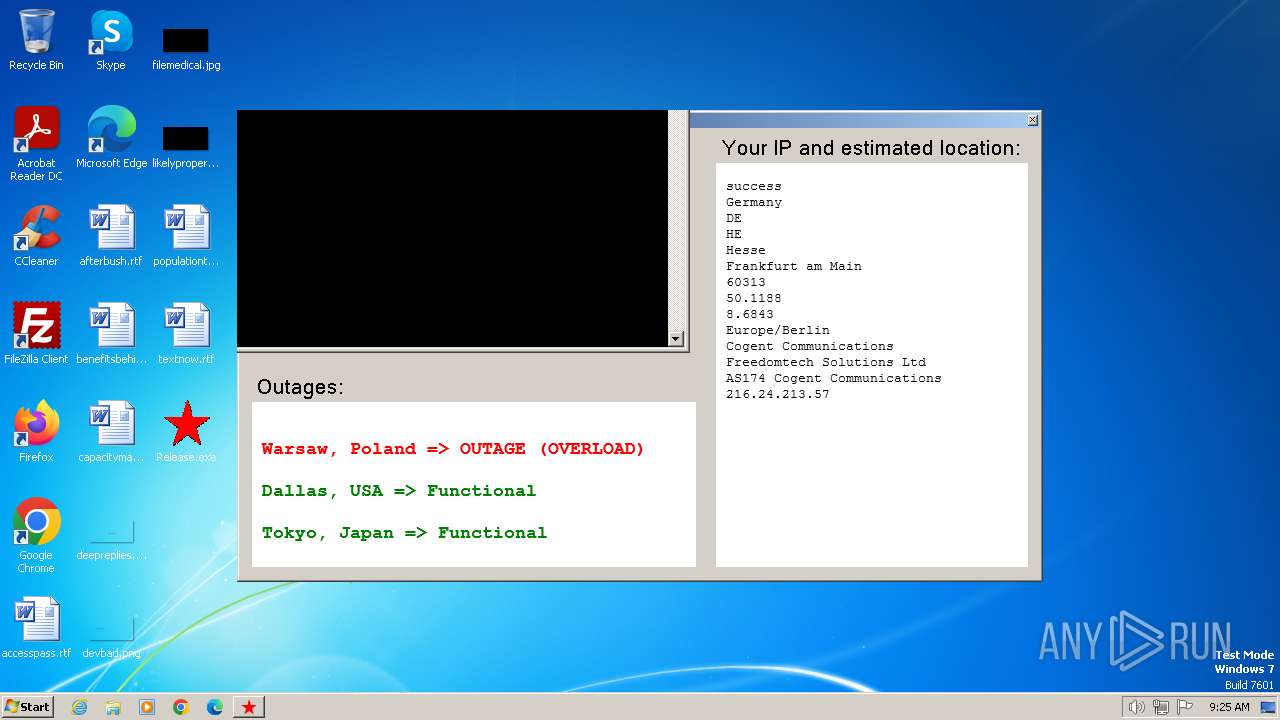
Executing commands from a ".bat" file
- proxy2.exe (PID: 3536)
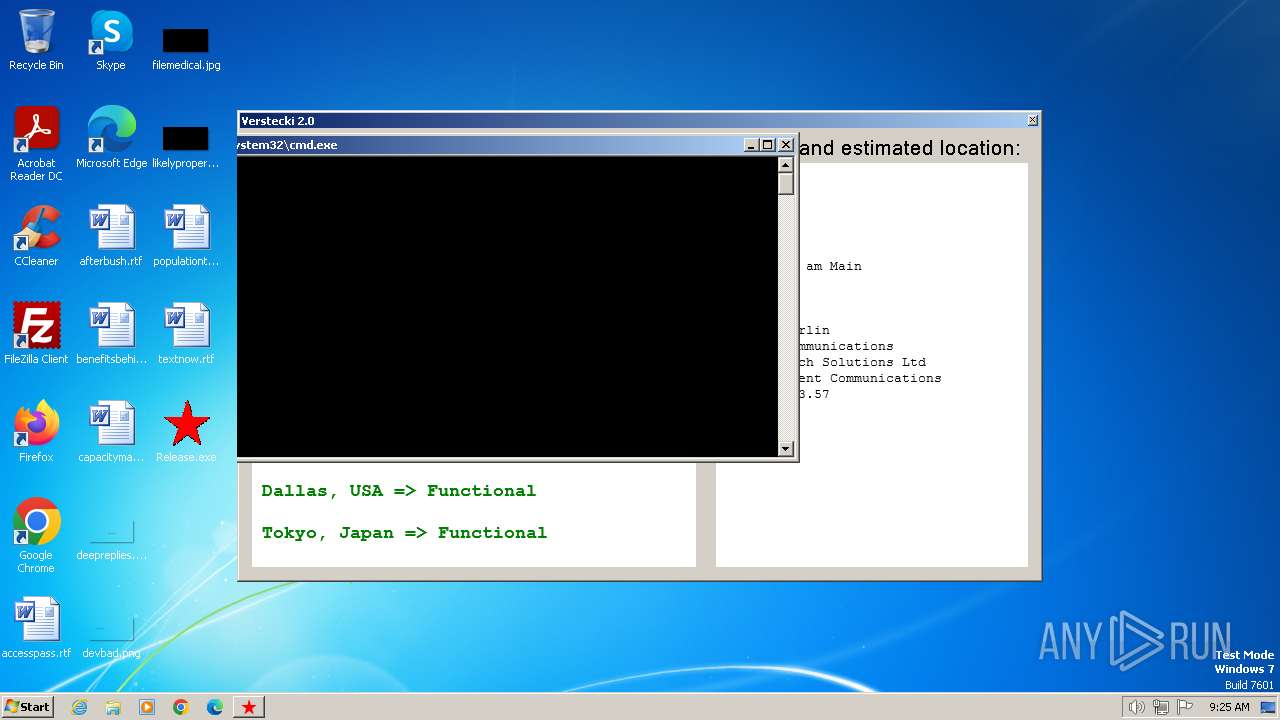
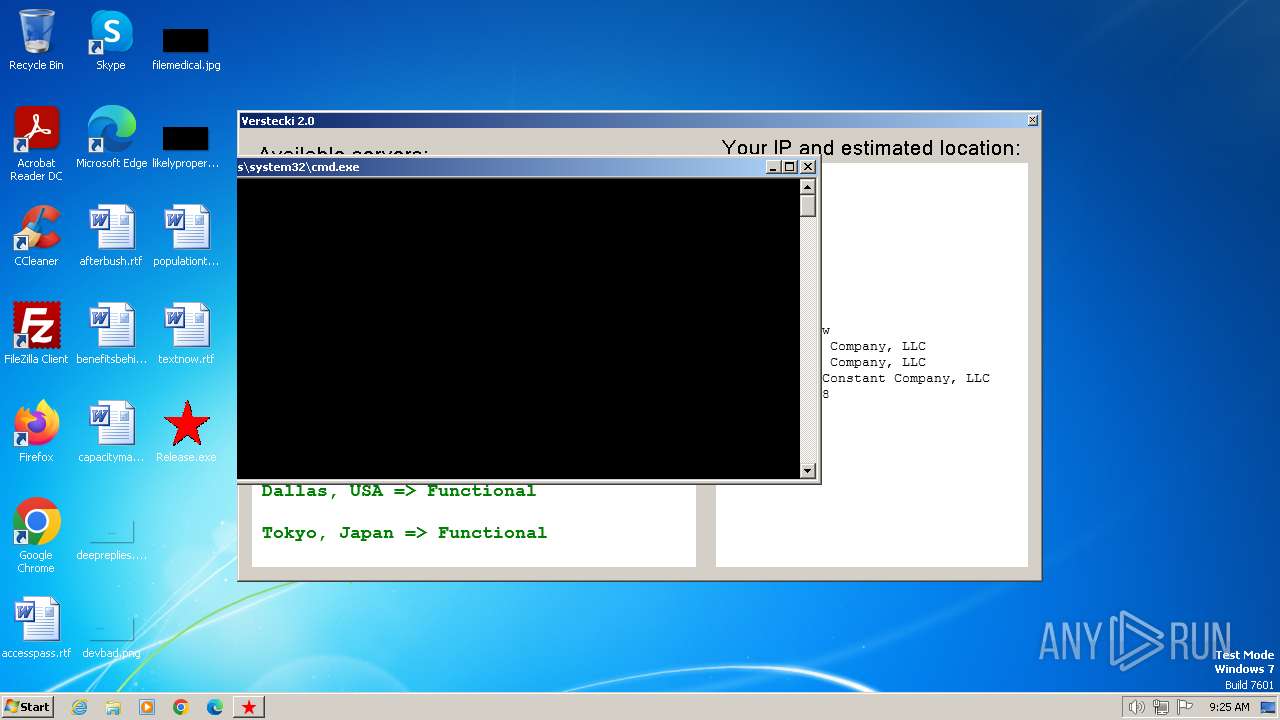
Starts CMD.EXE for commands execution
- proxy2.exe (PID: 3536)
The executable file from the user directory is run by the CMD process
- sysproxy.exe (PID: 2692)
- sysproxy.exe (PID: 2960)
- sysproxy.exe (PID: 2832)
- sysproxy.exe (PID: 3980)
- sysproxy.exe (PID: 980)
- sysproxy.exe (PID: 844)
Connects to unusual port
- proxy2.exe (PID: 3536)
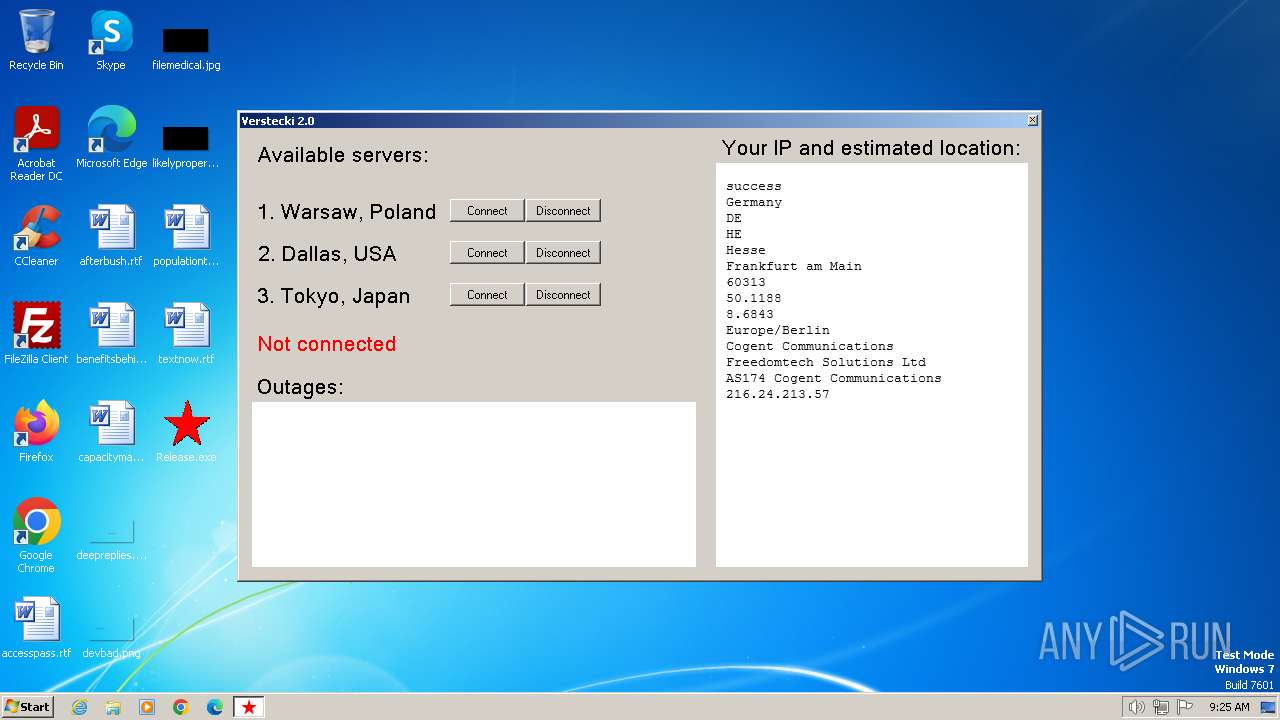
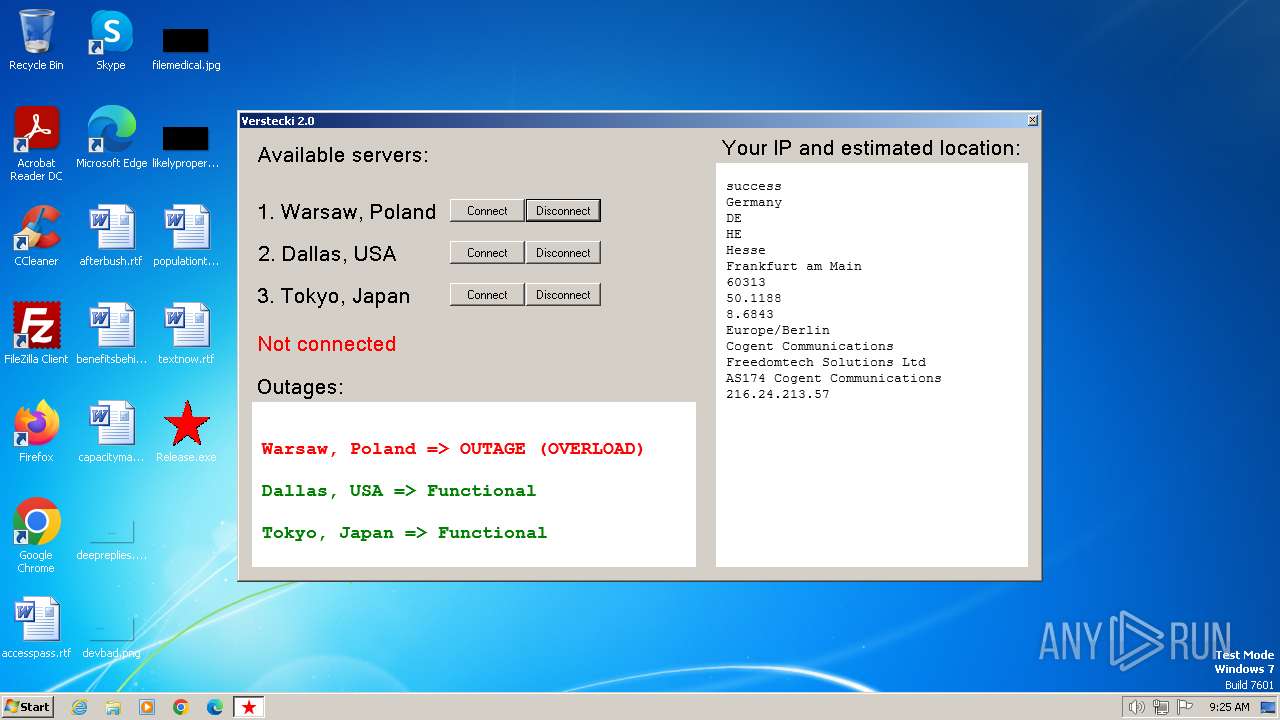
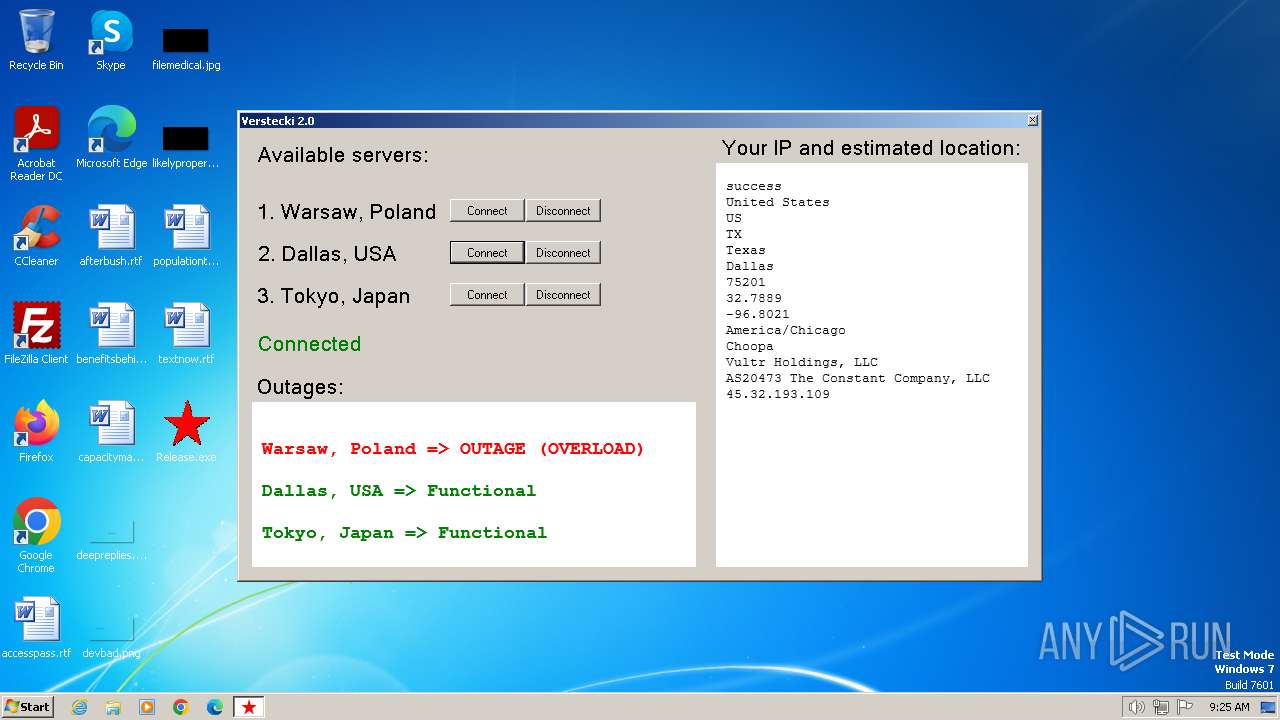
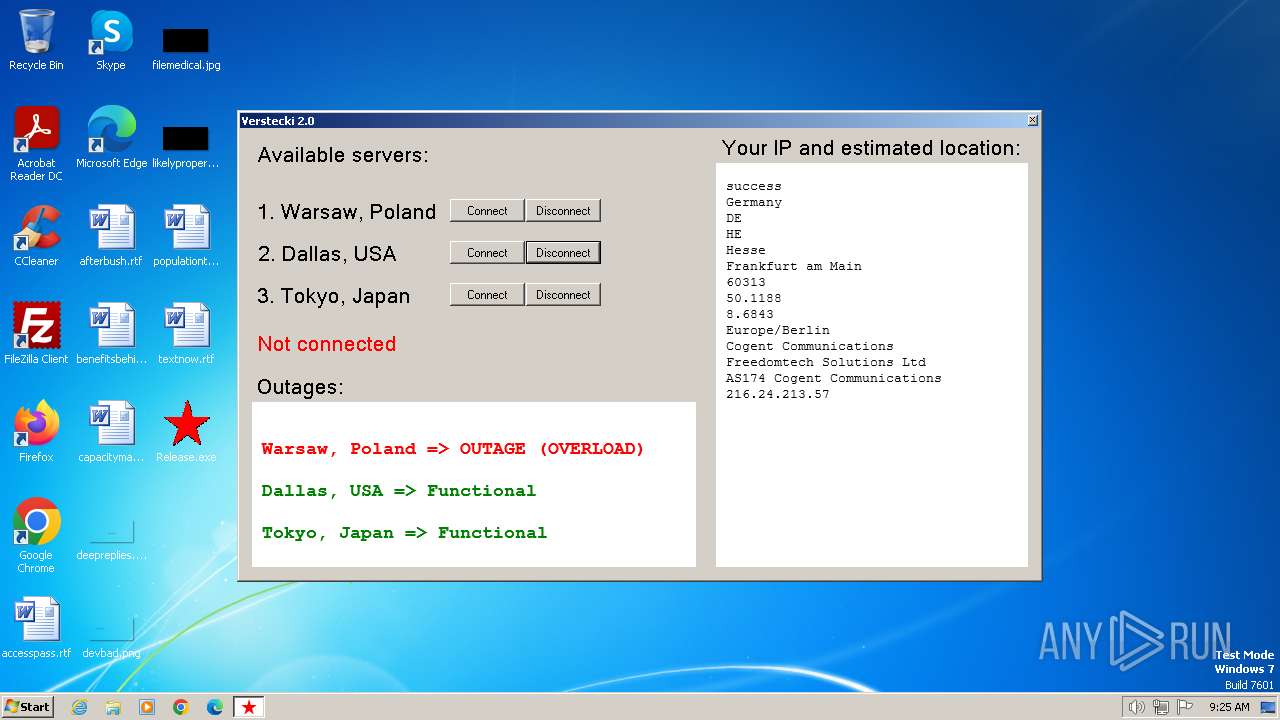
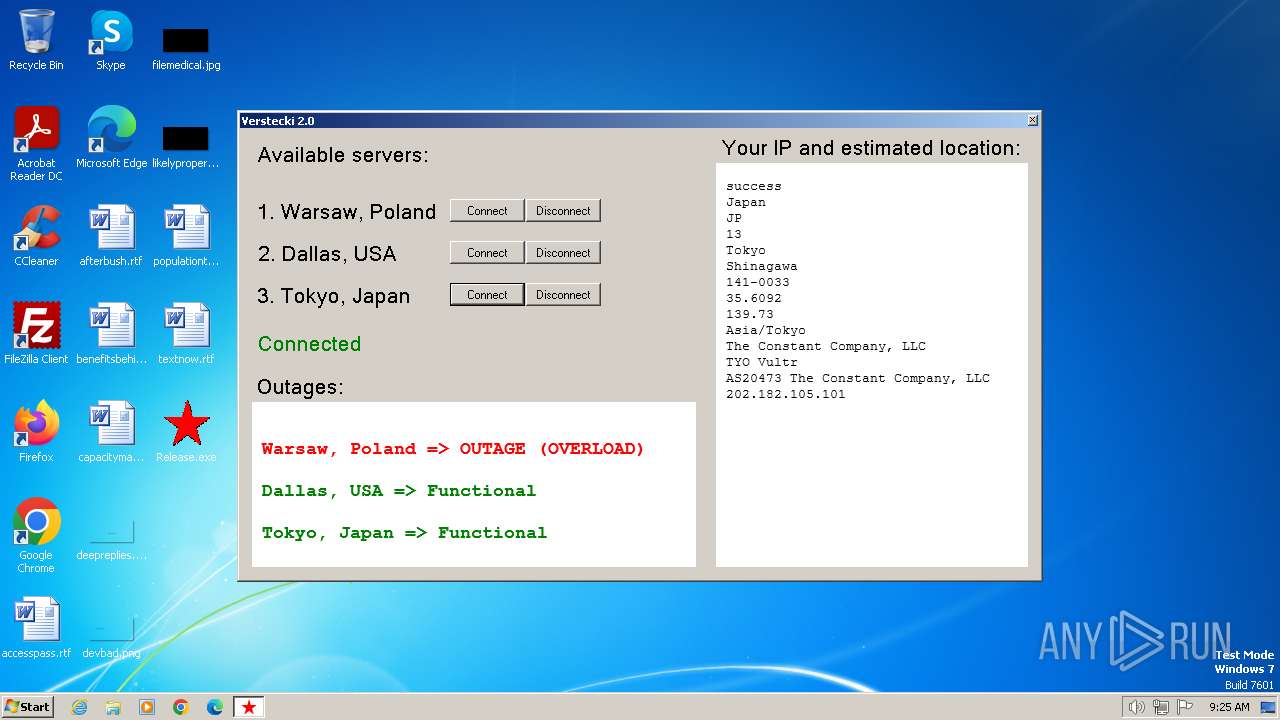
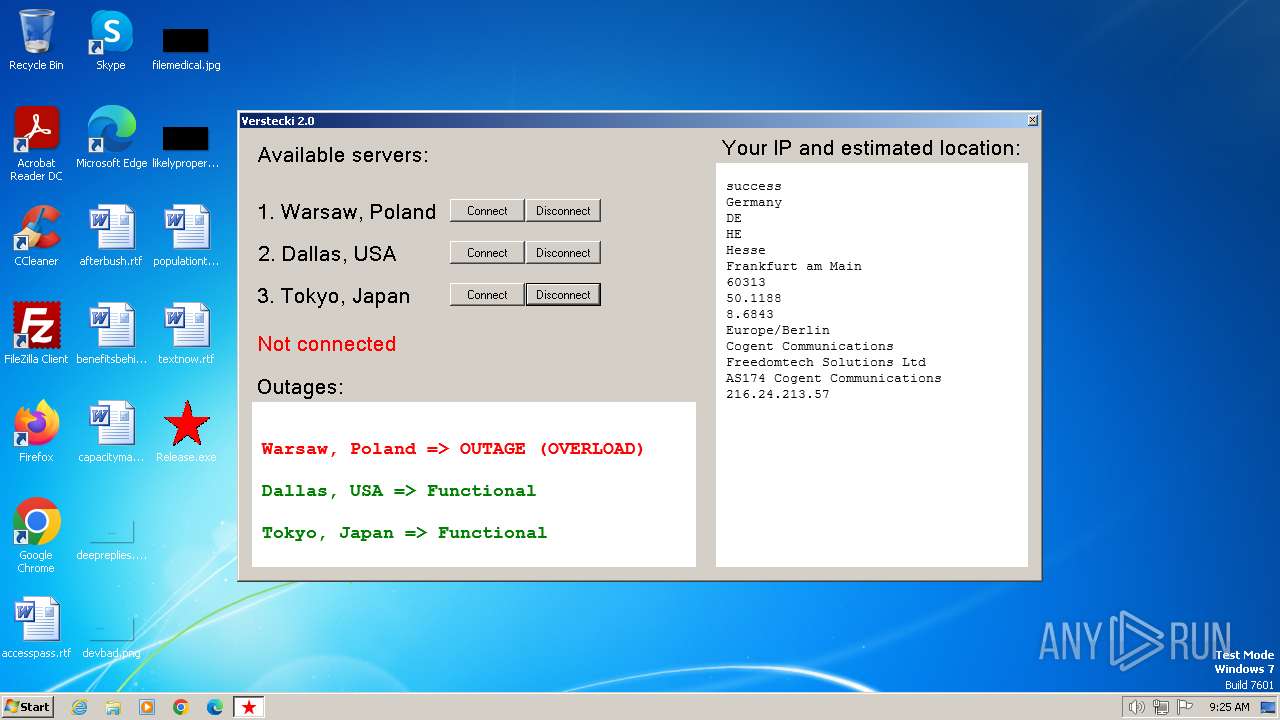
Checks for external IP
- proxy2.exe (PID: 3536)
INFO
Checks supported languages
- Release.exe (PID: 3672)
- proxy2.exe (PID: 3536)
- sysproxy.exe (PID: 2692)
- sysproxy.exe (PID: 2960)
- sysproxy.exe (PID: 980)
- sysproxy.exe (PID: 3980)
- sysproxy.exe (PID: 2832)
- sysproxy.exe (PID: 844)
Reads the computer name
- Release.exe (PID: 3672)
- proxy2.exe (PID: 3536)
- sysproxy.exe (PID: 2960)
- sysproxy.exe (PID: 2692)
- sysproxy.exe (PID: 980)
- sysproxy.exe (PID: 3980)
- sysproxy.exe (PID: 2832)
- sysproxy.exe (PID: 844)
Create files in a temporary directory
- Release.exe (PID: 3672)
- proxy2.exe (PID: 3536)
Reads the machine GUID from the registry
- proxy2.exe (PID: 3536)
- sysproxy.exe (PID: 2960)
- sysproxy.exe (PID: 2692)
- sysproxy.exe (PID: 2832)
- sysproxy.exe (PID: 980)
- sysproxy.exe (PID: 3980)
- sysproxy.exe (PID: 844)
Checks proxy server information
- proxy2.exe (PID: 3536)
- sysproxy.exe (PID: 2692)
- sysproxy.exe (PID: 2960)
- sysproxy.exe (PID: 2832)
- sysproxy.exe (PID: 980)
- sysproxy.exe (PID: 3980)
- sysproxy.exe (PID: 844)
Creates files or folders in the user directory
- proxy2.exe (PID: 3536)
Reads the software policy settings
- proxy2.exe (PID: 3536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:11 09:16:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 79872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1eef0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
62
Monitored processes
14
Malicious processes
8
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 844 | sysproxy off tyo1.madhacker.biz 8118 | C:\Users\admin\AppData\Local\Temp\proxy2\sysproxy.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 980 | sysproxy off dal1.madhacker.biz 8118 | C:\Users\admin\AppData\Local\Temp\proxy2\sysproxy.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2096 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\tokyo.bat" " | C:\Windows\System32\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2256 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\warsaw-off.bat" " | C:\Windows\System32\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2644 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\dallas.bat" " | C:\Windows\System32\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
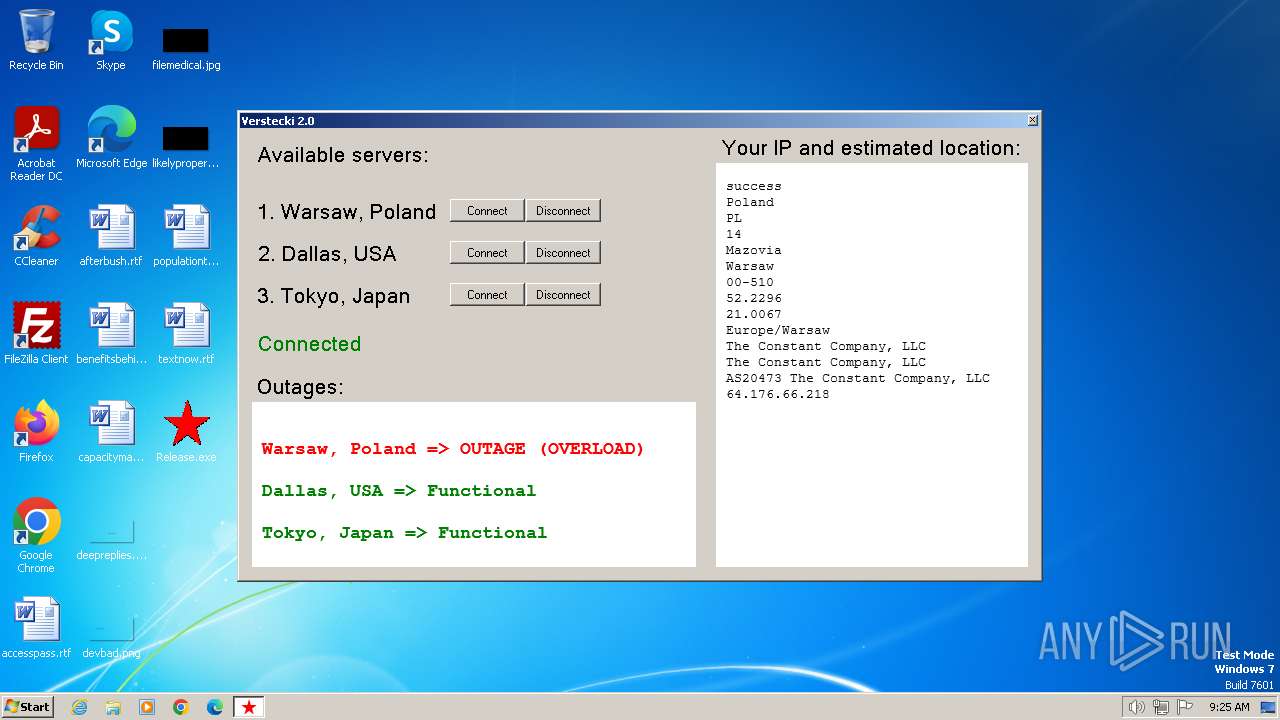
| 2692 | sysproxy on ams3.madhacker.biz 8118 | C:\Users\admin\AppData\Local\Temp\proxy2\sysproxy.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2728 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\dallas-off.bat" " | C:\Windows\System32\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2772 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\tokyo-off.bat" " | C:\Windows\System32\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2832 | sysproxy on dal1.madhacker.biz 8118 | C:\Users\admin\AppData\Local\Temp\proxy2\sysproxy.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2856 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\warsaw.bat" " | C:\Windows\System32\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
14 590
Read events
14 362
Write events
147
Delete events
81
Modification events
| (PID) Process: | (3672) Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3672) Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3672) Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3672) Release.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3536) proxy2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3536) proxy2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3536) proxy2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3536) proxy2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3536) proxy2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3536) proxy2.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | delete value | Name: | ProxyServer |
Value: | |||
Executable files
2
Suspicious files
5
Text files
11
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\warsaw.bat | text | |
MD5:829C4553AC0215C7CC76BB5FA9C01B26 | SHA256:7E225A2D5C51769C400CCD13B75F01C675317CE560F662699121D60160E5A110 | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\tokyo.bat | text | |
MD5:4A02329C4CCF6D8DB159F51CF2423A6C | SHA256:F0B512BE81F1A379AA121974A977603002017E238E68A8F8415D57C5DC89BEDB | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\tokyo-off.bat | text | |
MD5:F89A8509BA39FCB1A0EDE5289810E3C3 | SHA256:5DBF5582D046F8B2B2DE4E6A17D64ABADCA238FBEE1C13947ECBEA3F1E0025D7 | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\proxy2.exe | executable | |
MD5:43063D30F8A5DC9C6C8EED52AAC20F9C | SHA256:A3D7F85CC0CD373C6B8C14010468009C5B1E757D5D5D427079701BB639C5AF78 | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\sysproxy.exe | executable | |
MD5:380D58A33FAF71547FB97C3FC12A38A9 | SHA256:A918AA182DD57A545B0416E406432A6D09D1232AA0C33A0969DCD39A432D0D6B | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\warsaw-off.bat | text | |
MD5:D6A72512B7299CD617C46921DE2E3E57 | SHA256:839B3CC35C26B6BD03A15A1CB9DCD663CF18E40408233270F609C87DB40A1BB4 | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\dallas-off.bat | text | |
MD5:AC347D2EFCBBB2FF0EEF8EF07E1F250F | SHA256:F84E6CA9C1BAE6443BBBA93FF2551A805B1B55D00923B523059C99424ABB22E6 | |||
| 3672 | Release.exe | C:\Users\admin\AppData\Local\Temp\proxy2\dallas.bat | text | |
MD5:70037C73F14AC22D218B82B333918594 | SHA256:DB9166DE287BEF8D6CFA1D8A3E1F7892D0EF4CCC6996406F5AB28104477E0CF9 | |||
| 3536 | proxy2.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\line[1].txt | text | |
MD5:906E4EC243AB70D6F2231A80F882295B | SHA256:FFF5180CAA1FE8114F4DF13D687511B13BAE94D1F6566FE7FE7C725F537D1B12 | |||
| 3536 | proxy2.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\103621DE9CD5414CC2538780B4B75751 | binary | |
MD5:45951D517DD7610CDBDF09561F9B5DAE | SHA256:D1A0A8DFE63D817A2BB22C0B100BD15E458710AD6511DD3006403FF6D48C031F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
13
DNS requests
7
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3536 | proxy2.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line | unknown | text | 171 b | unknown |
3536 | proxy2.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a8eff655f4df9ffc | unknown | — | — | unknown |
3536 | proxy2.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?9f073e77455bfaf9 | unknown | compressed | 65.2 Kb | unknown |
3536 | proxy2.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | binary | 717 b | unknown |
3536 | proxy2.exe | GET | 200 | 95.101.54.114:80 | http://r3.o.lencr.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBRI2smg%2ByvTLU%2Fw3mjS9We3NfmzxAQUFC6zF7dYVsuuUAlA5h%2BvnYsUwsYCEgTA2ZbveOPYUdm86t%2FX4bavGw%3D%3D | unknown | binary | 503 b | unknown |
3536 | proxy2.exe | GET | 200 | 64.176.66.218:8118 | http://ip-api.com/line | unknown | text | 173 b | unknown |
3536 | proxy2.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line | unknown | text | 171 b | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?e90c163b6659448e | unknown | — | — | unknown |
3536 | proxy2.exe | GET | 200 | 45.32.193.109:8118 | http://ip-api.com/line | unknown | text | 155 b | unknown |
3536 | proxy2.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line | unknown | text | 171 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
3536 | proxy2.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
3536 | proxy2.exe | 64.176.66.218:443 | ams3.madhacker.biz | — | US | unknown |
3536 | proxy2.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
3536 | proxy2.exe | 69.192.161.44:80 | x1.c.lencr.org | AKAMAI-AS | DE | unknown |
3536 | proxy2.exe | 95.101.54.114:80 | r3.o.lencr.org | Akamai International B.V. | DE | unknown |
3536 | proxy2.exe | 64.176.66.218:8118 | ams3.madhacker.biz | — | US | unknown |
3536 | proxy2.exe | 45.32.193.109:8118 | dal1.madhacker.biz | AS-CHOOPA | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ip-api.com |
| shared |
ams3.madhacker.biz |
| unknown |
ctldl.windowsupdate.com |
| whitelisted |
x1.c.lencr.org |
| whitelisted |
r3.o.lencr.org |
| shared |
dal1.madhacker.biz |
| unknown |
tyo1.madhacker.biz |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.madhacker .biz Domain |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
3536 | proxy2.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3536 | proxy2.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3536 | proxy2.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3536 | proxy2.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
3536 | proxy2.exe | Potential Corporate Privacy Violation | AV POLICY Internal Host Retrieving External IP Address (ip-api. com) |
3536 | proxy2.exe | Device Retrieving External IP Address Detected | ET POLICY External IP Lookup ip-api.com |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
1080 | svchost.exe | Potentially Bad Traffic | ET INFO DYNAMIC_DNS Query to a *.madhacker .biz Domain |