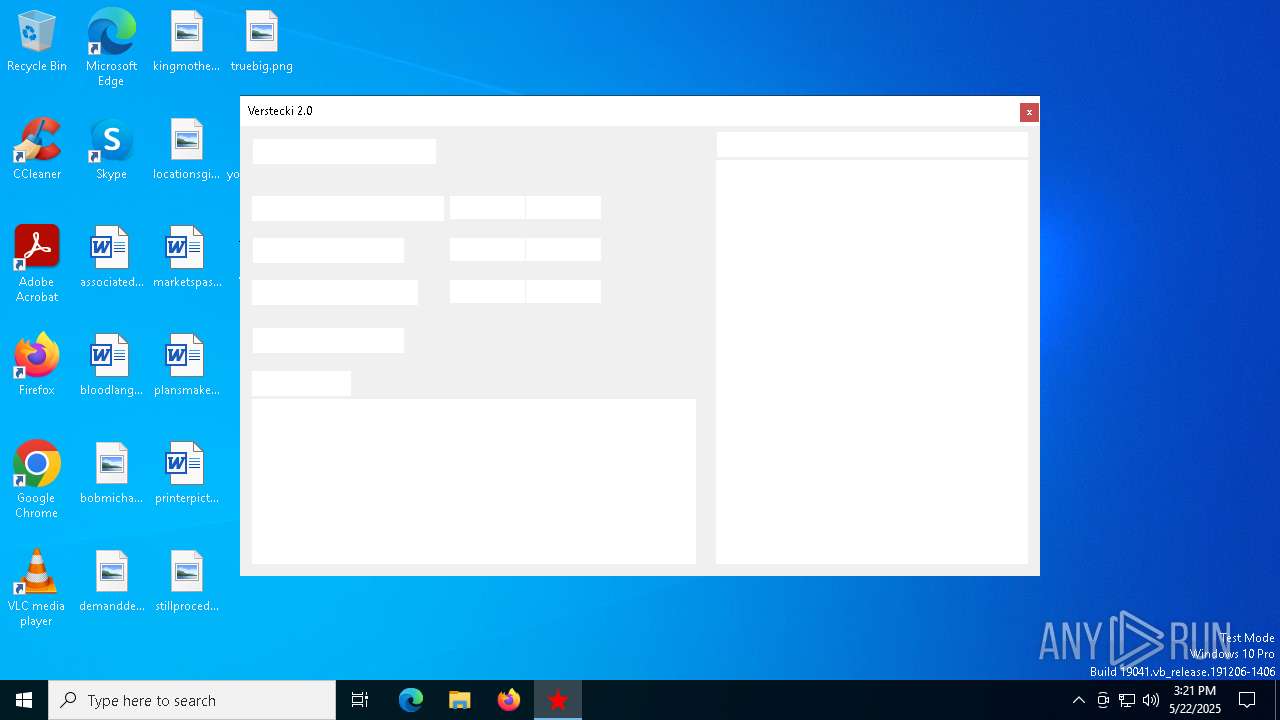
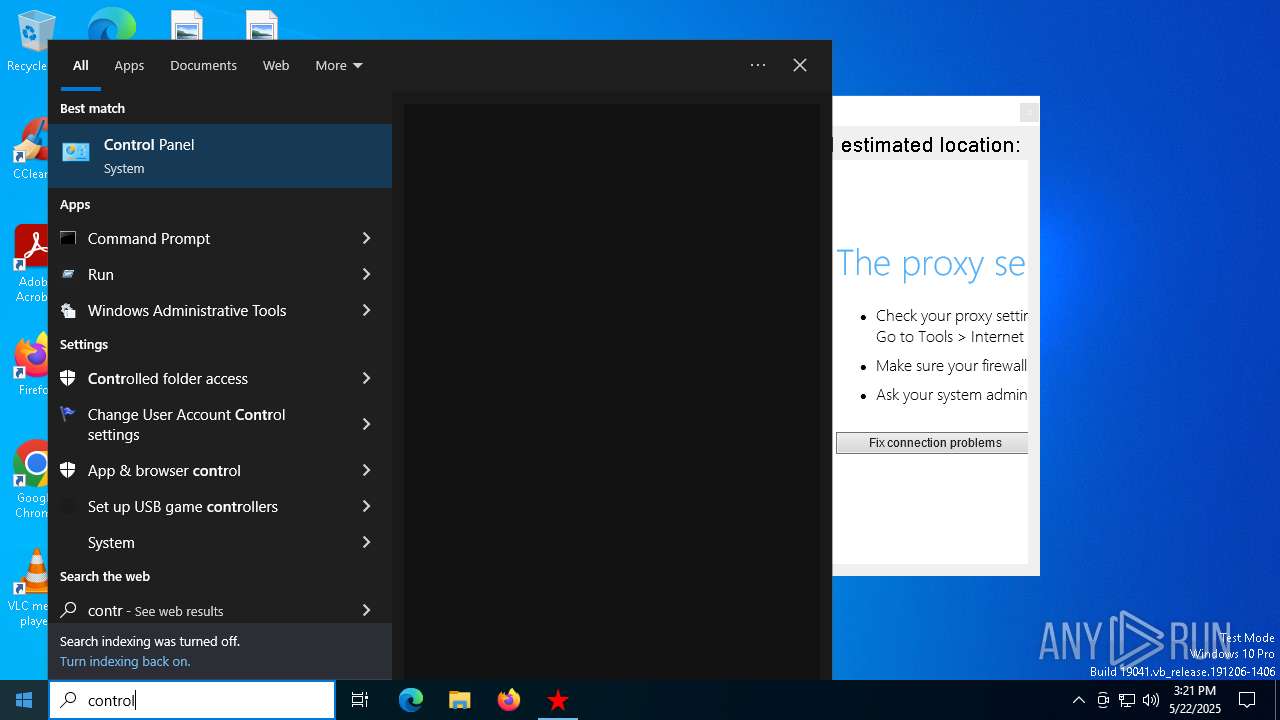
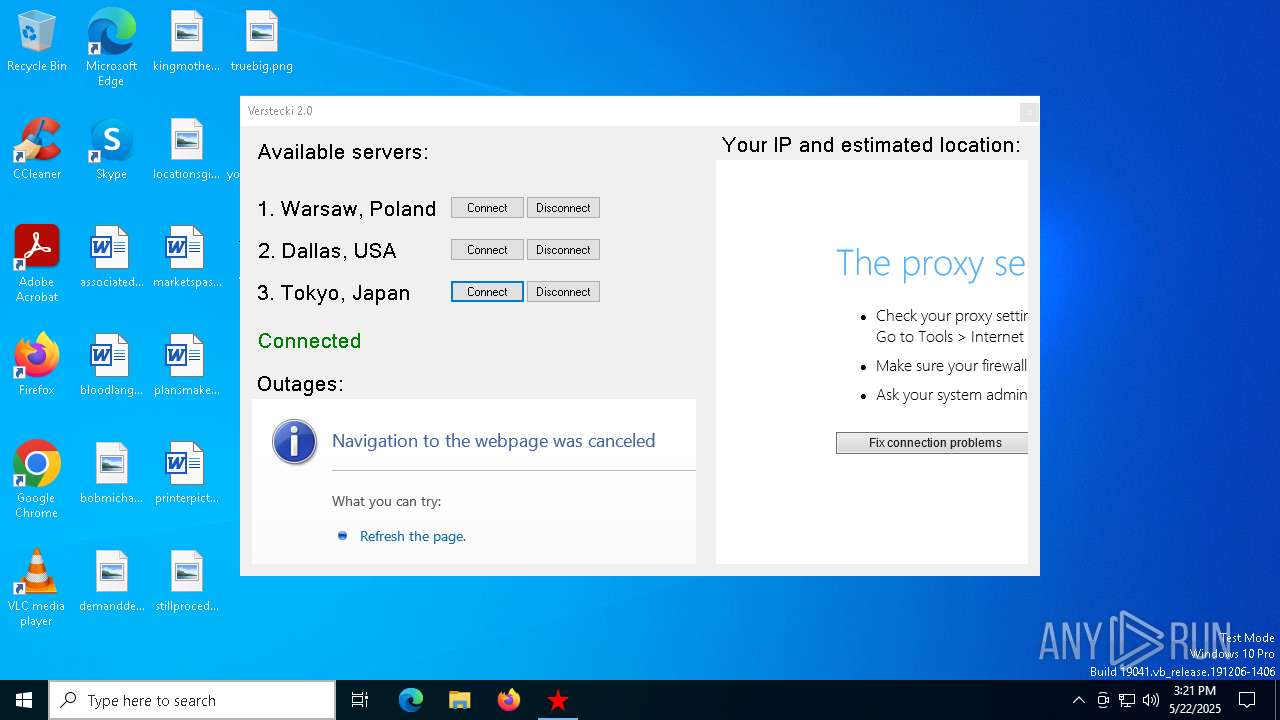
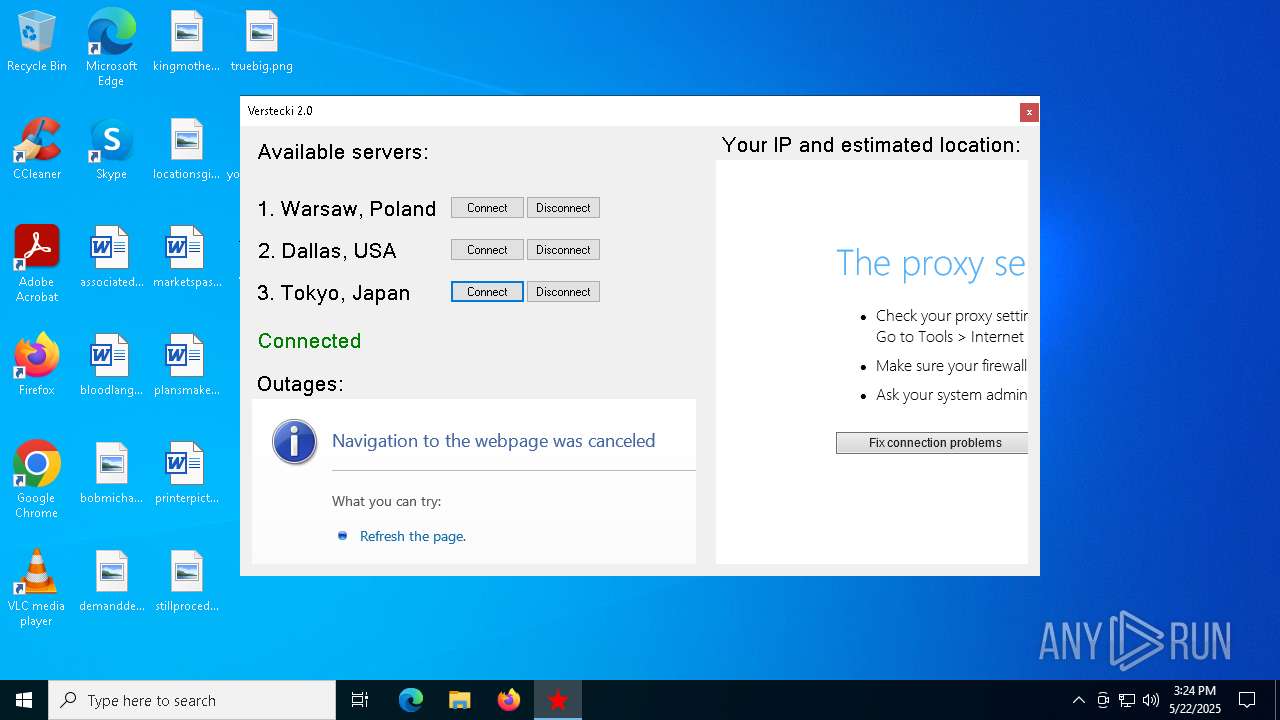
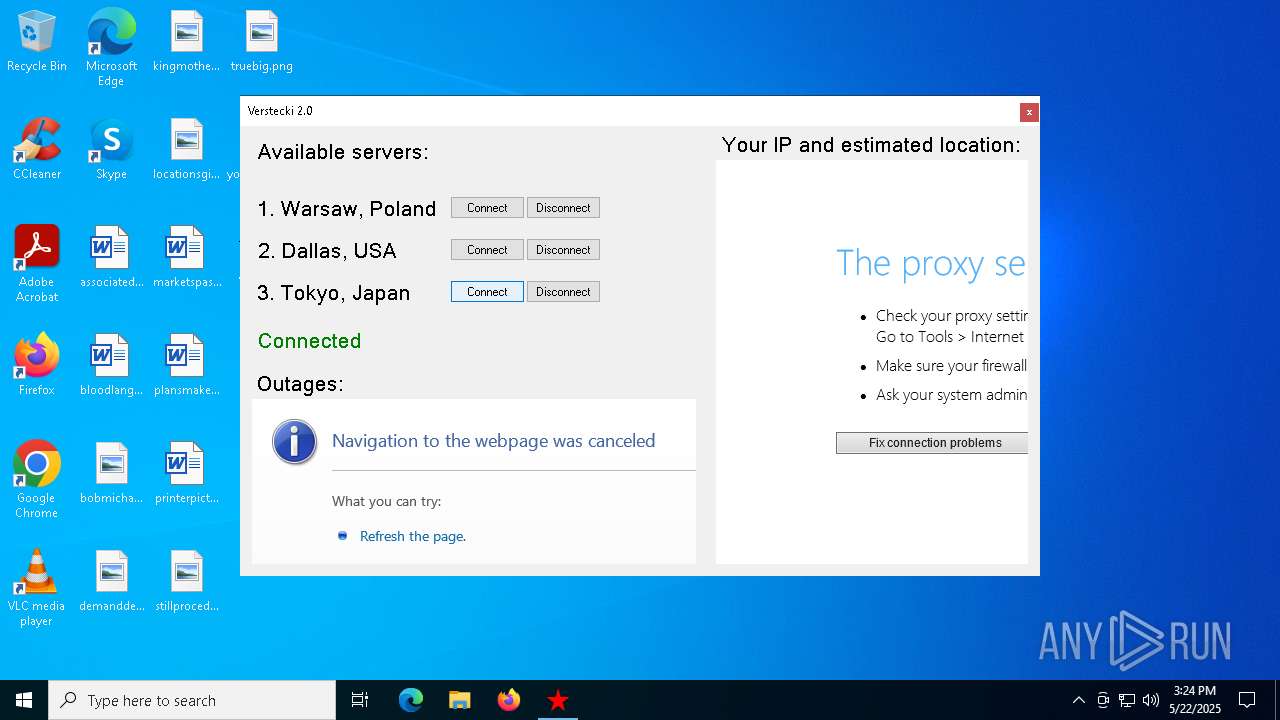
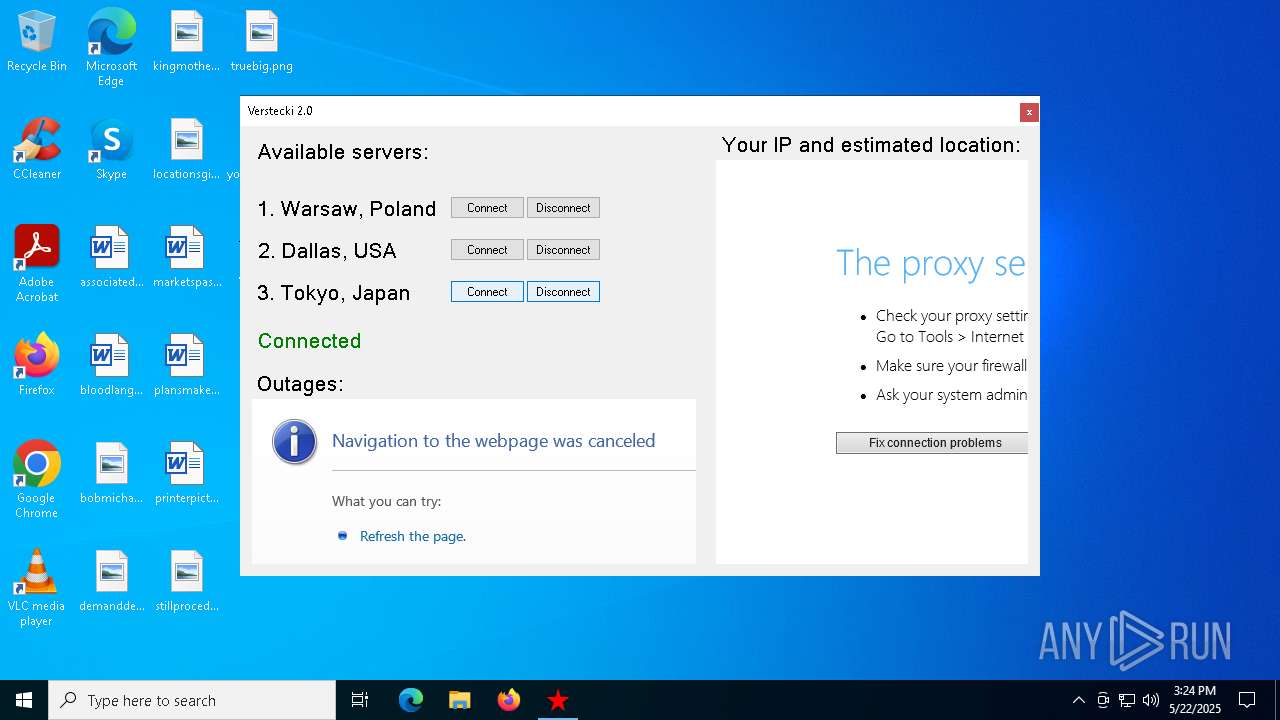
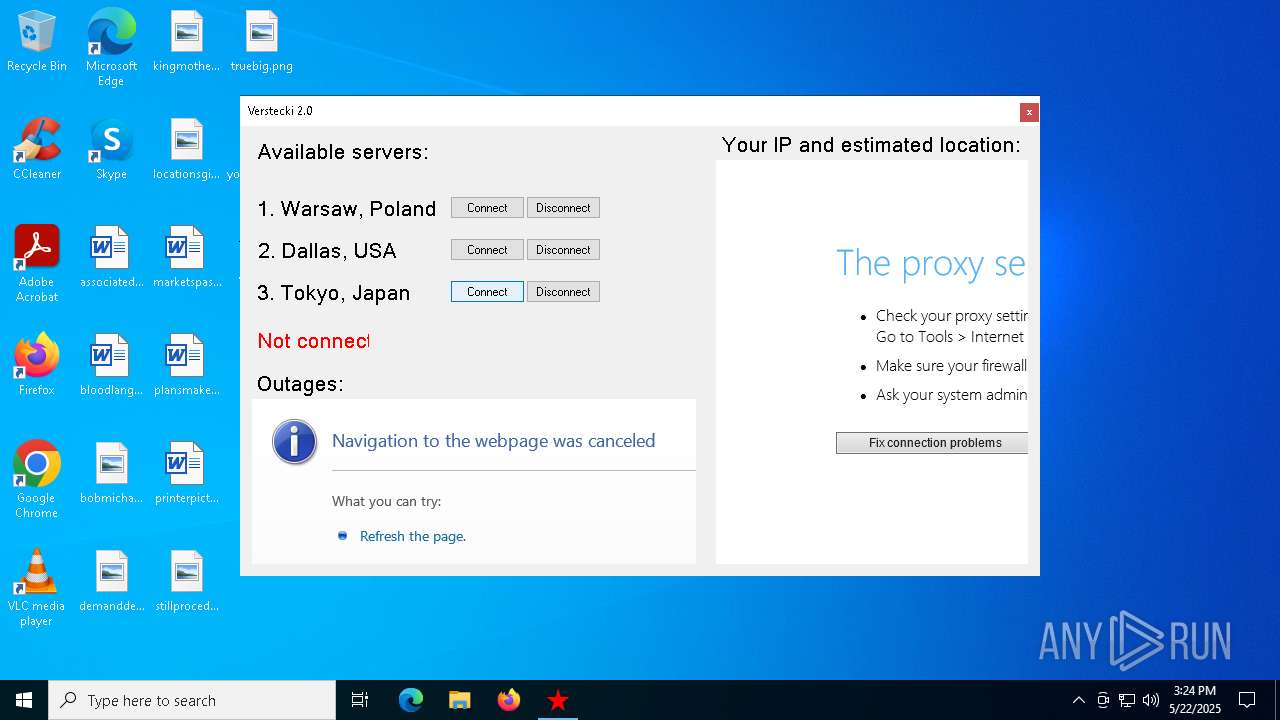
| File name: | Verstecki 2.0.exe |
| Full analysis: | https://app.any.run/tasks/096d0ba3-38a2-4e97-ab41-8769378b9f9c |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2025, 15:20:28 |
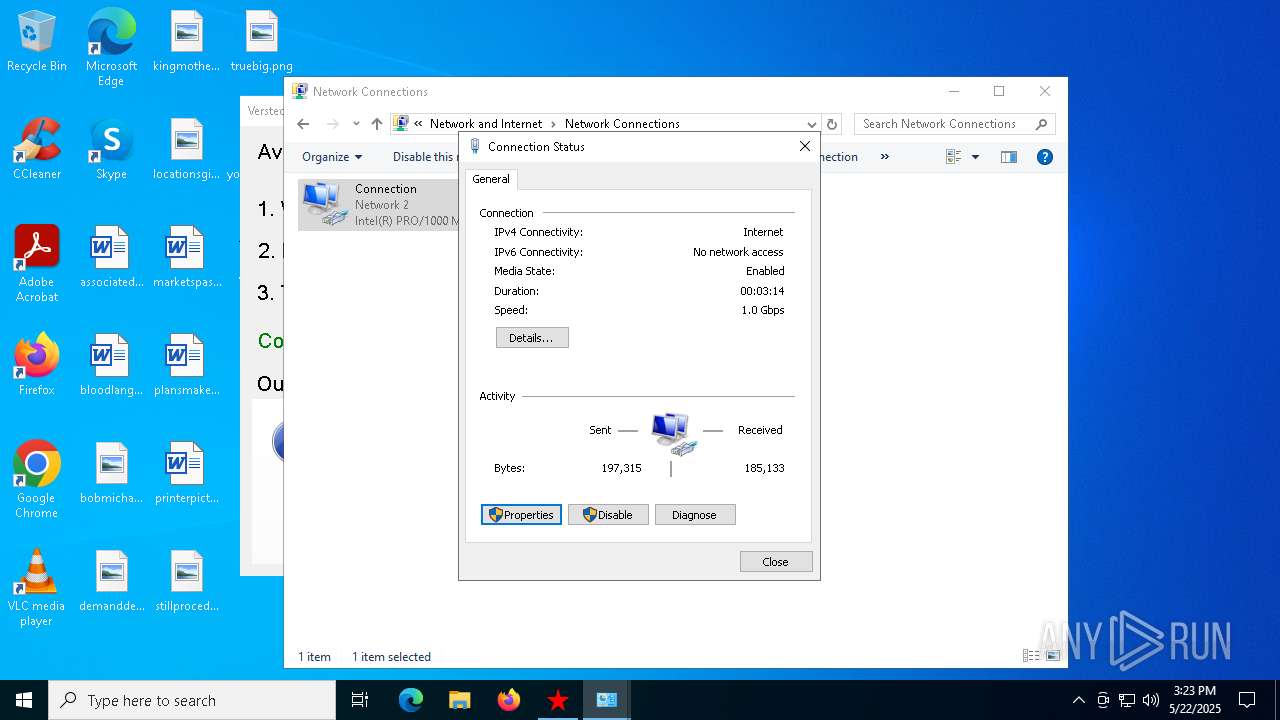
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 6 sections |
| MD5: | B25A3878793963A4479E74FDF60AE03E |
| SHA1: | 68B511E35868F8C7D7868198D20DC978E4E3A3A3 |
| SHA256: | 2B1A022CEE7D88FAB206A4F355E8EFABEDEB319EDABFE3784A8750E3C8971B75 |
| SSDEEP: | 12288:EjV8Uox9oUFydRxsQPyhv7qtoc3J851Jq//mq//06yl+XEw:rAY5qtPJ85PnLJl+Uw |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executable content was dropped or overwritten
- Verstecki 2.0.exe (PID: 4452)
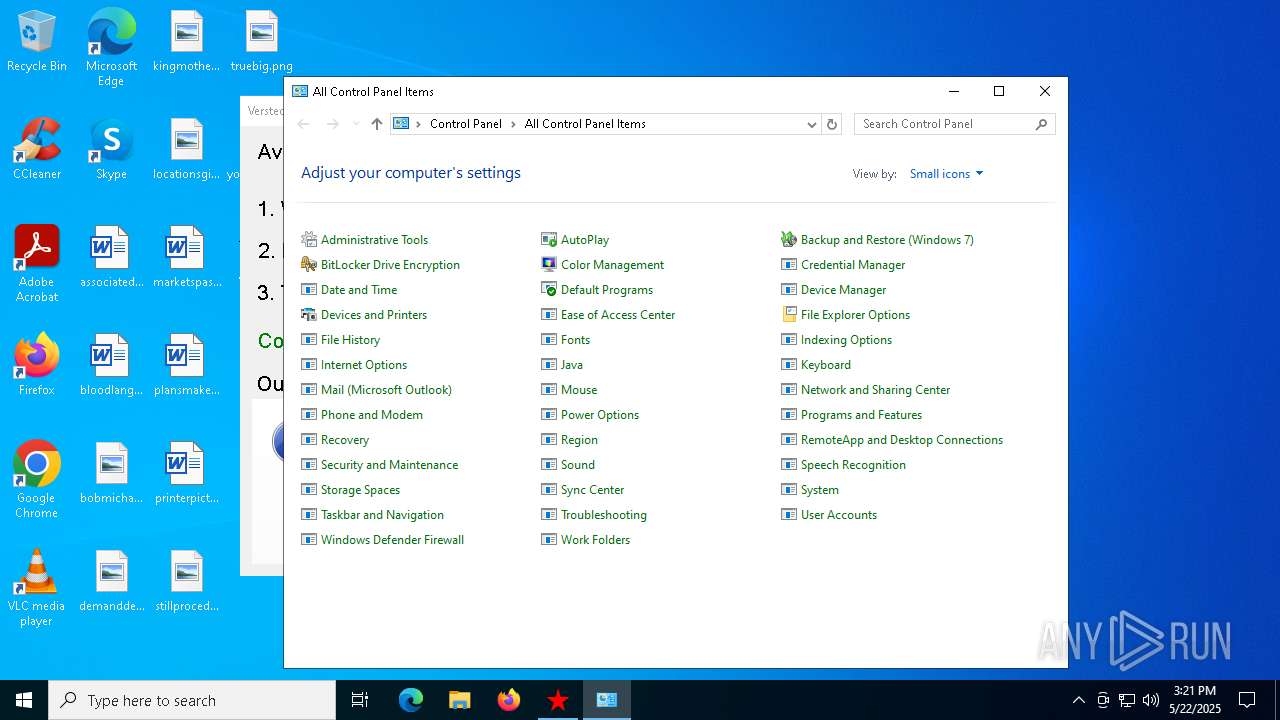
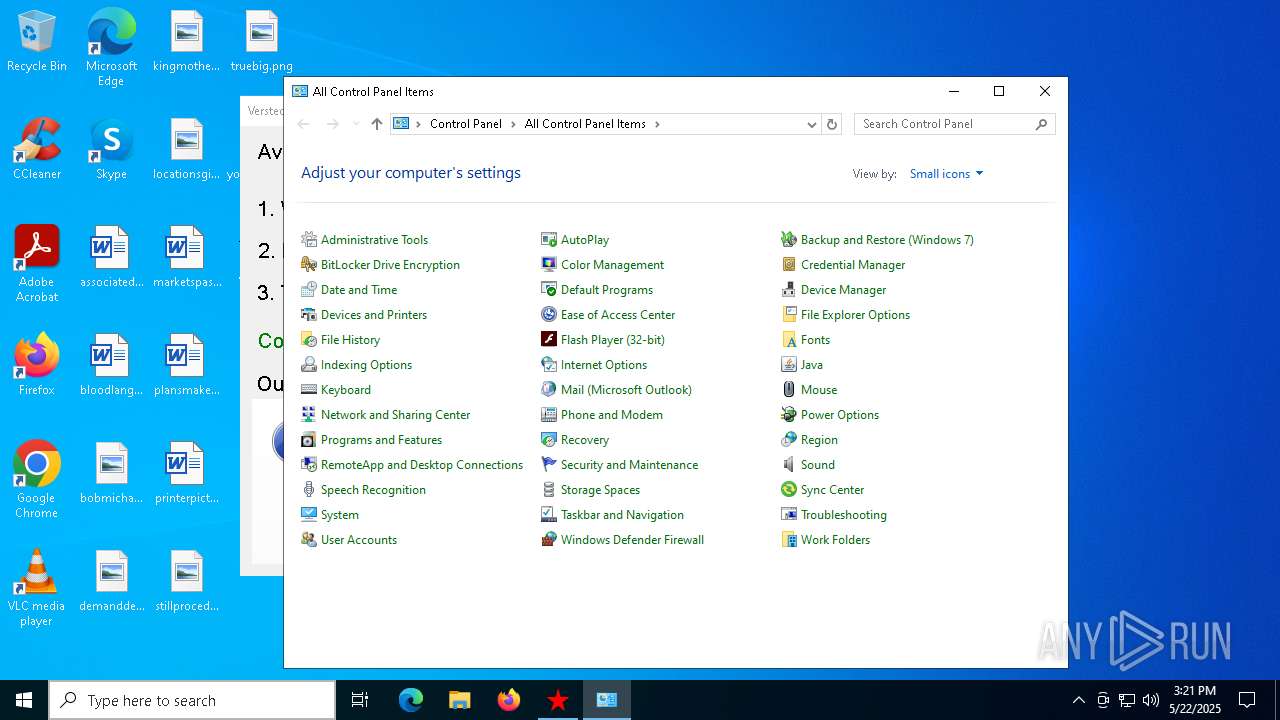
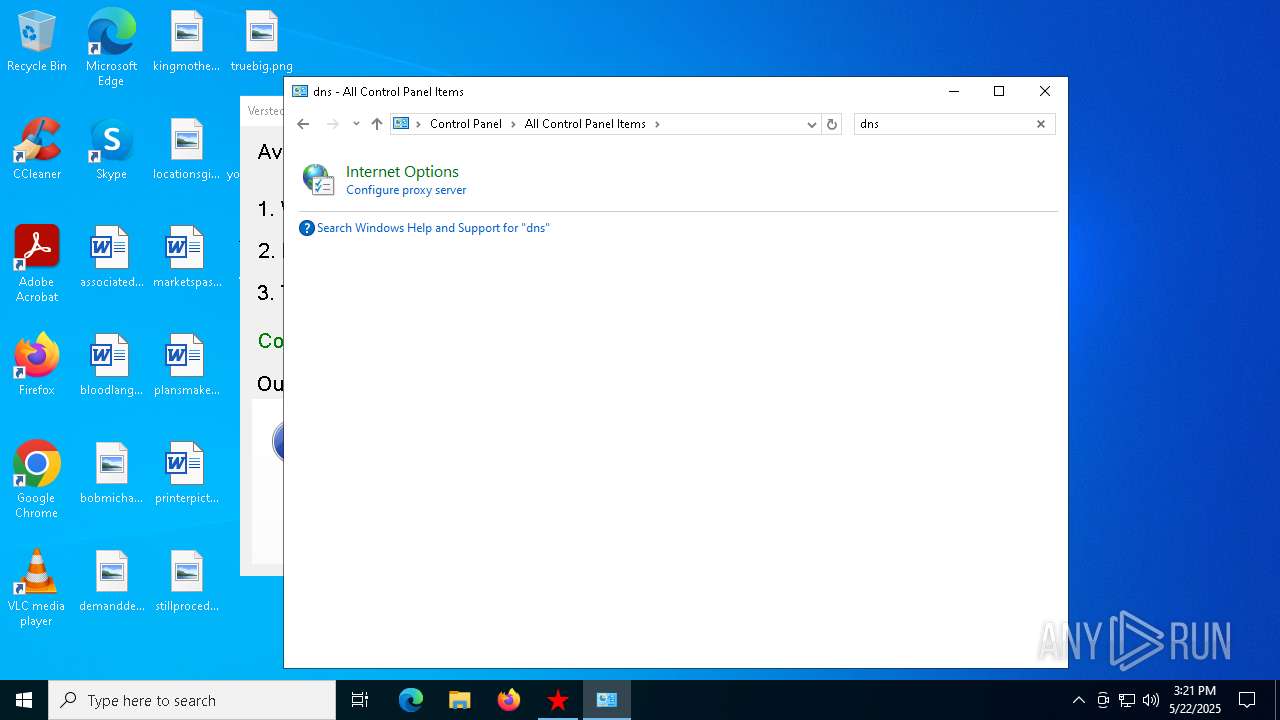
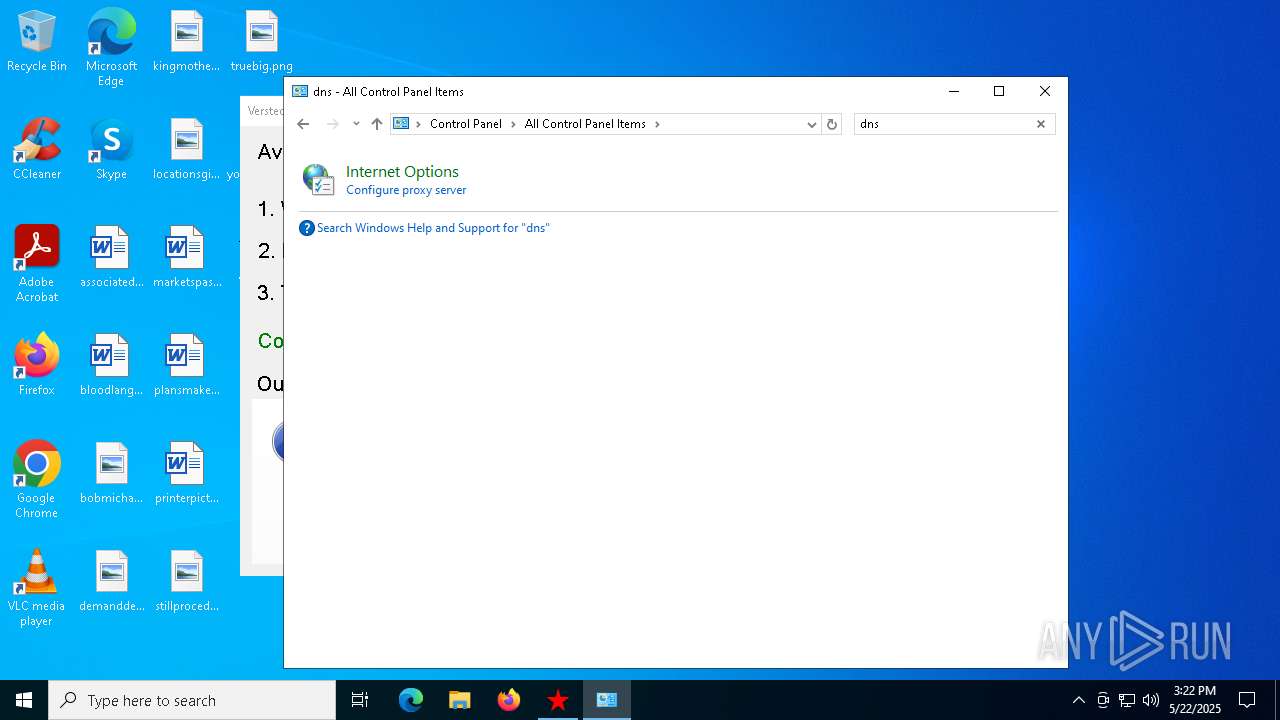
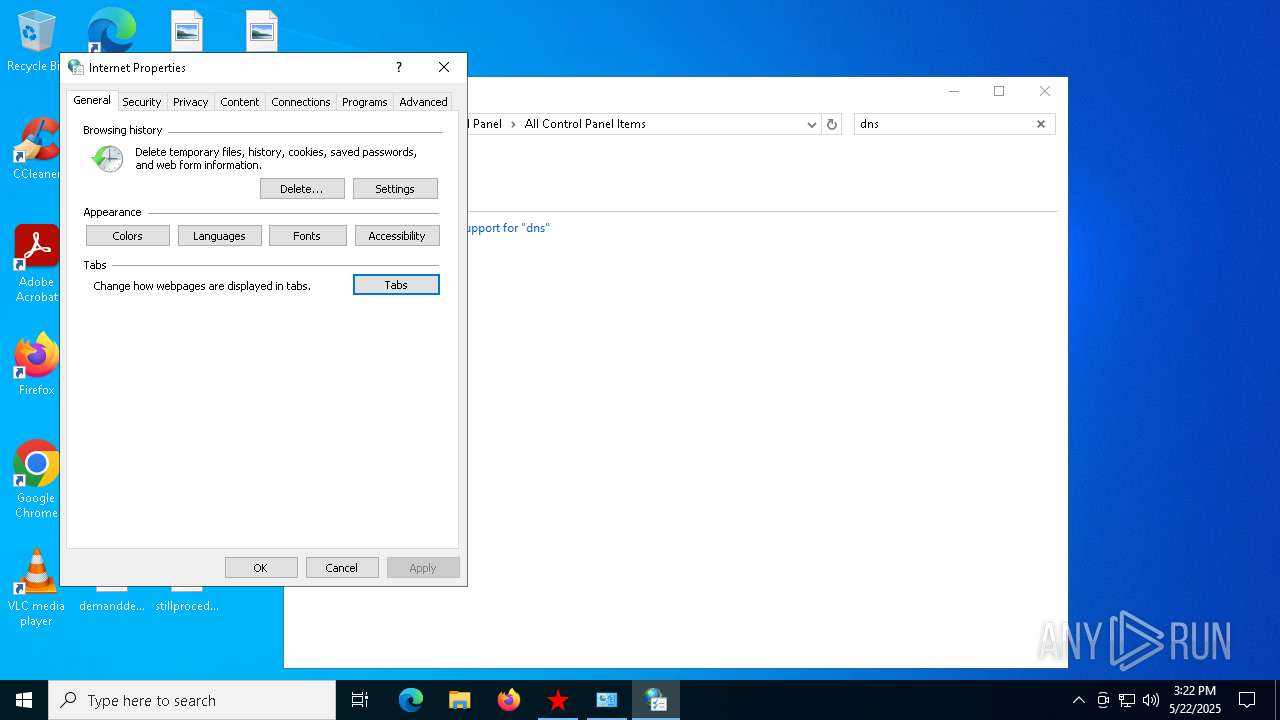
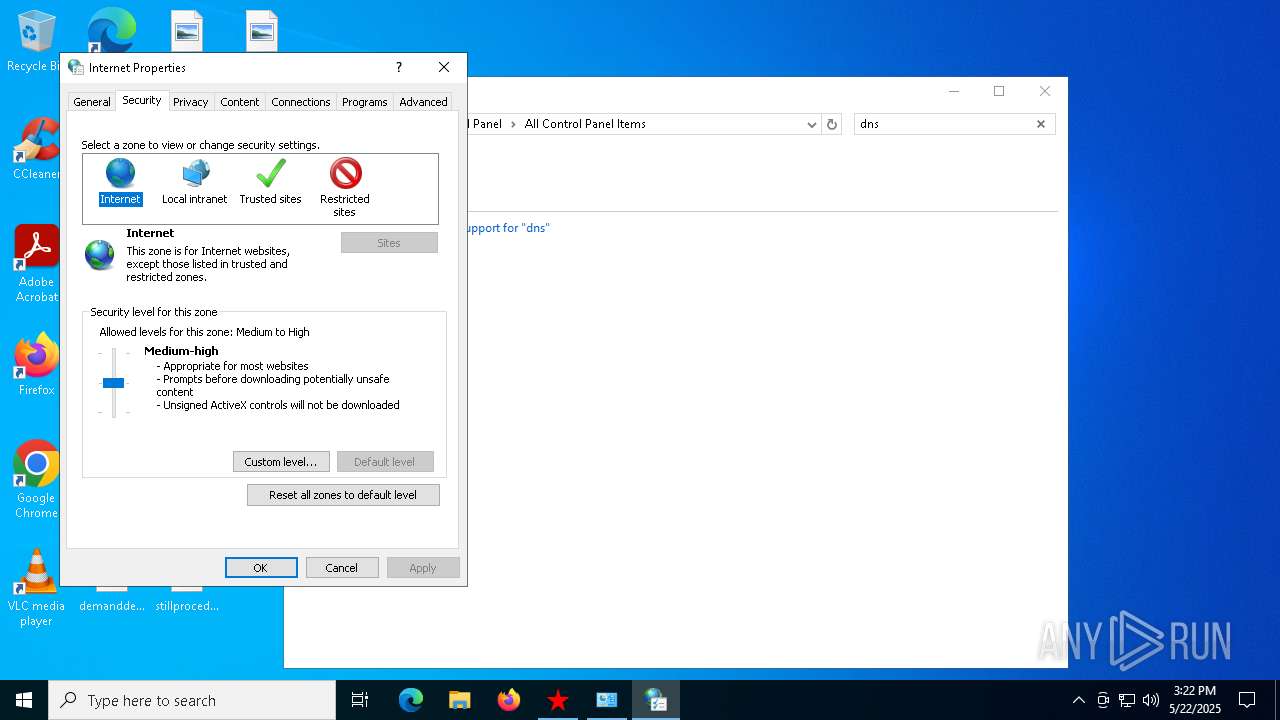
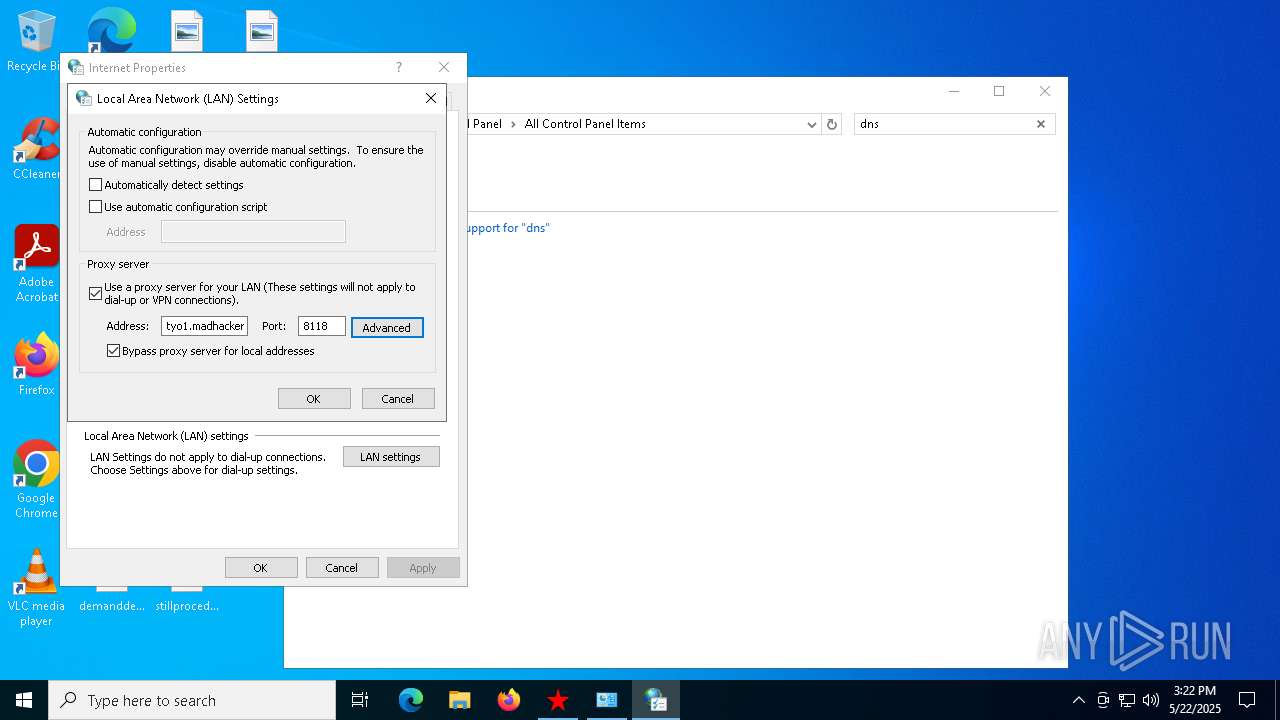
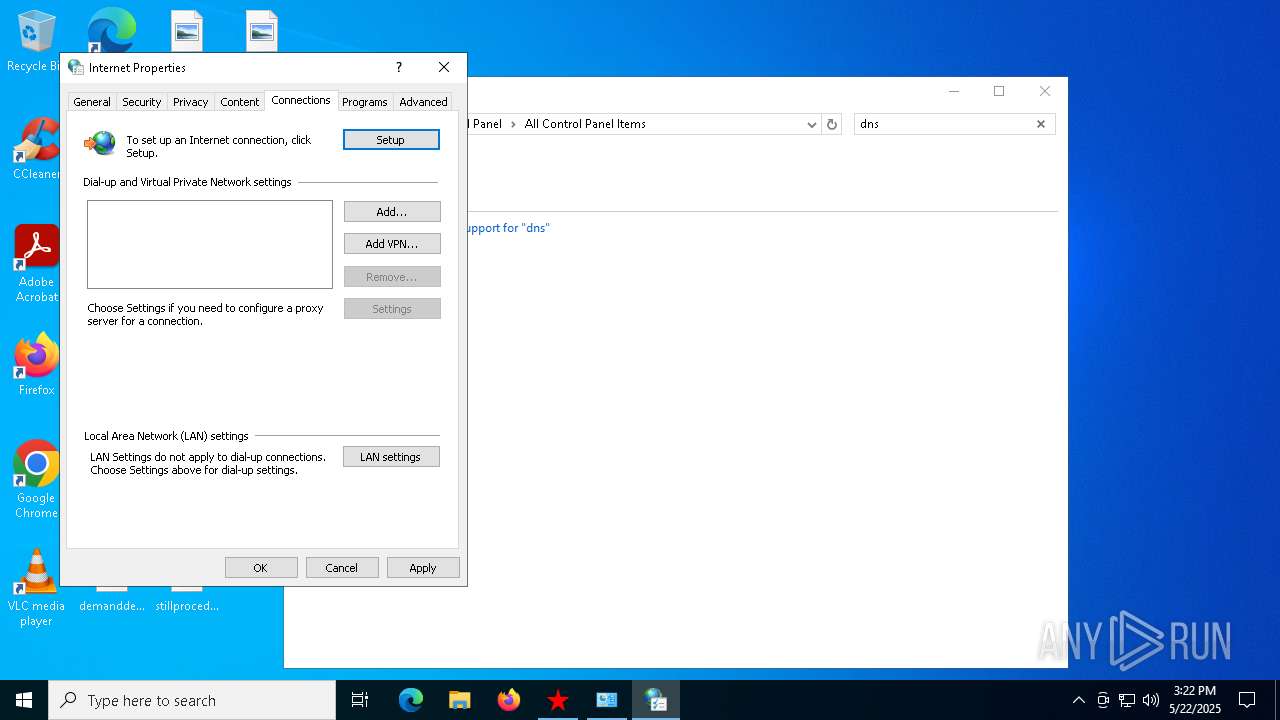
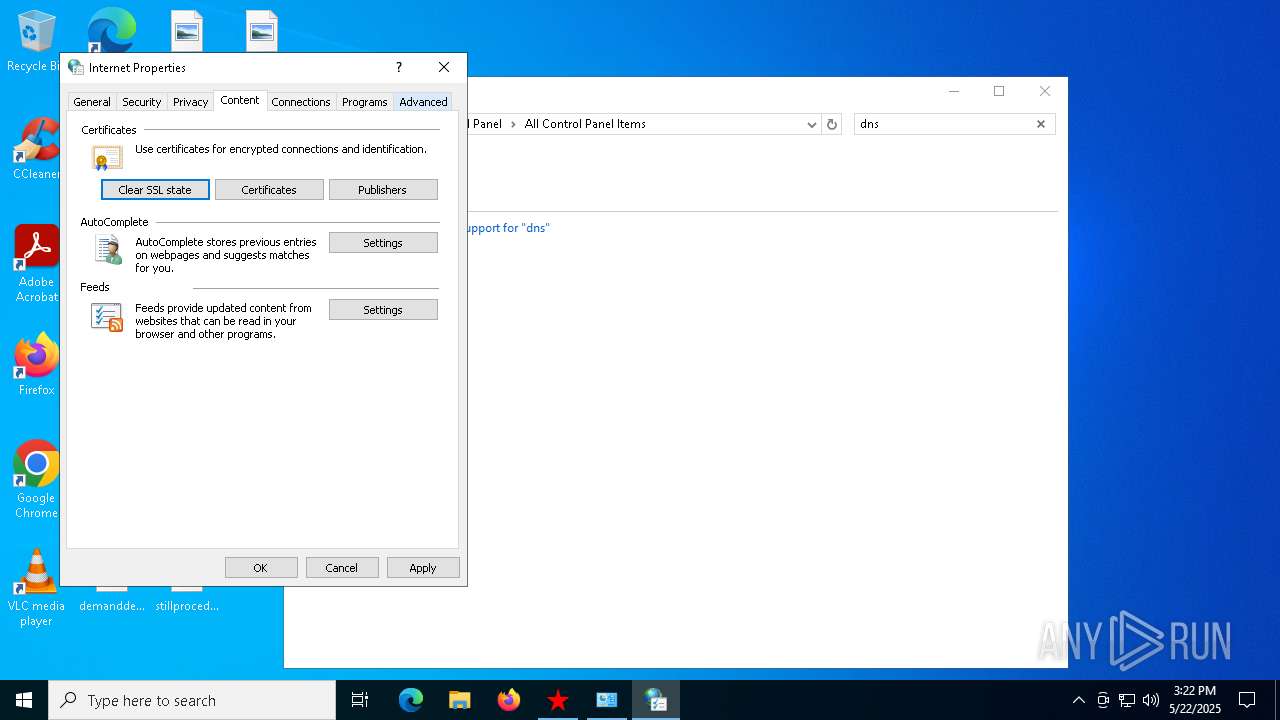
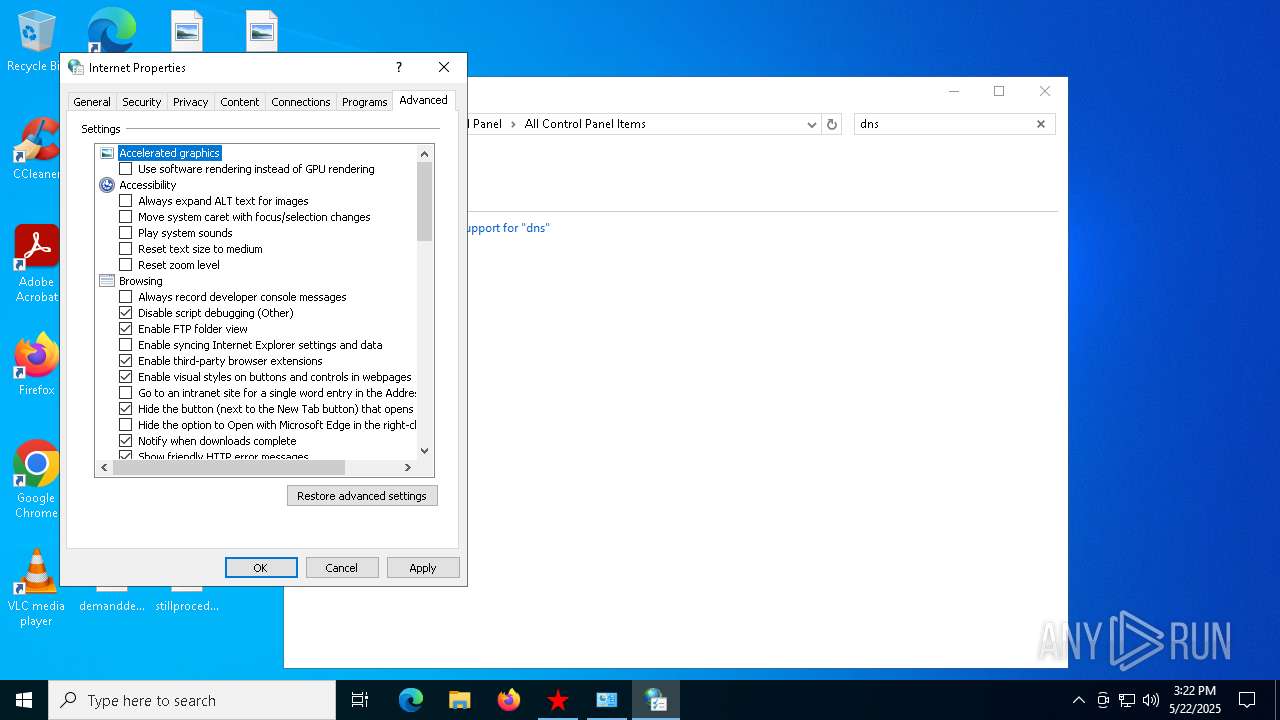
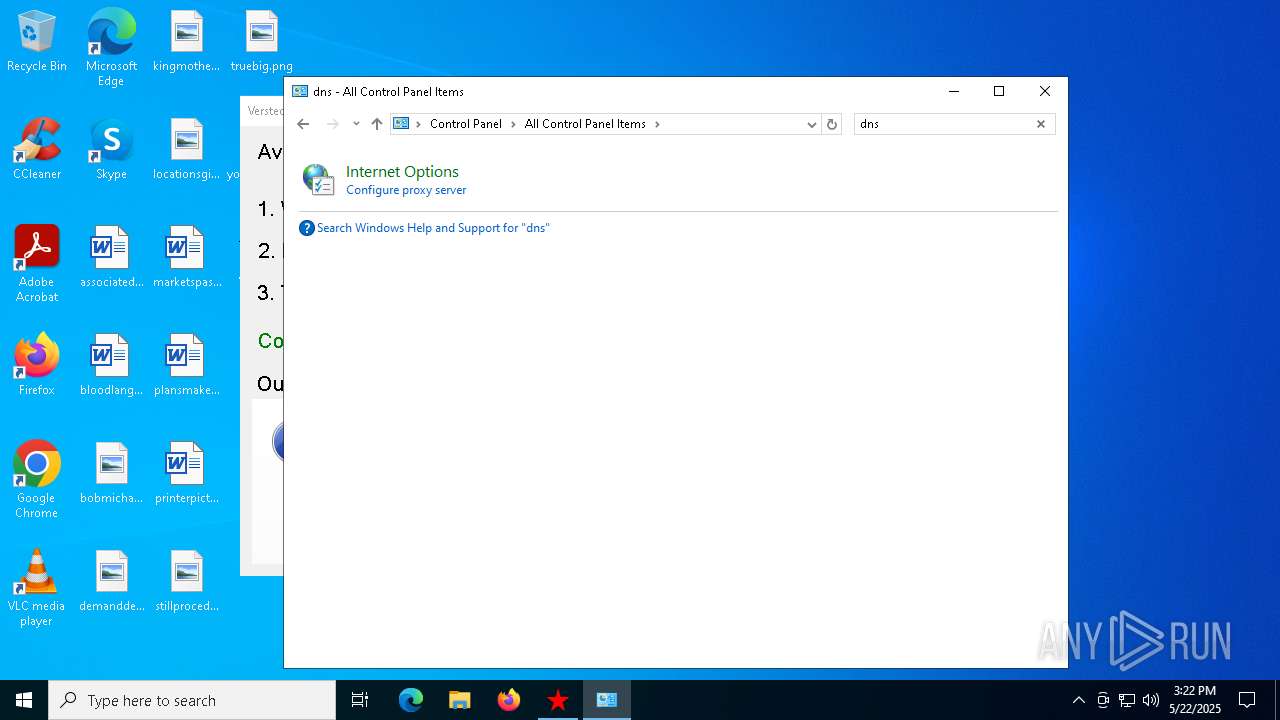
Reads security settings of Internet Explorer
- Verstecki 2.0.exe (PID: 4452)
- proxy2.exe (PID: 7184)
- sysproxy.exe (PID: 7972)
- sysproxy.exe (PID: 7804)
Reads Microsoft Outlook installation path
- proxy2.exe (PID: 7184)
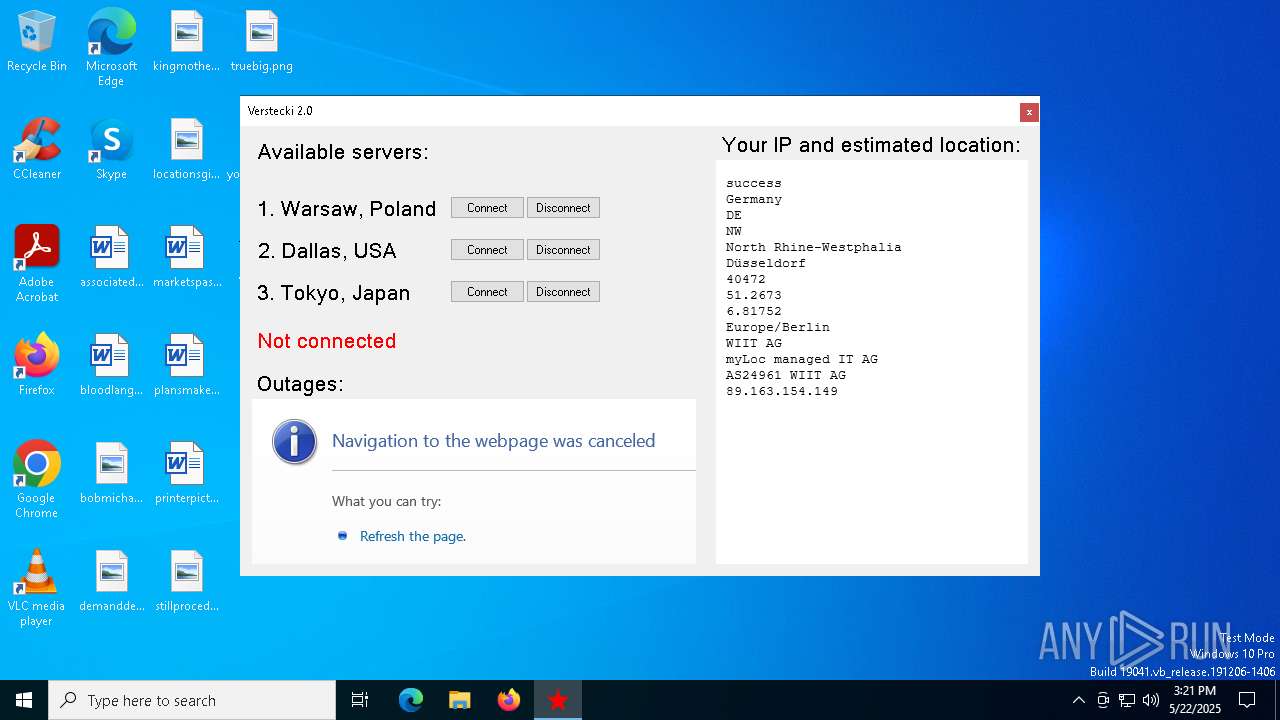
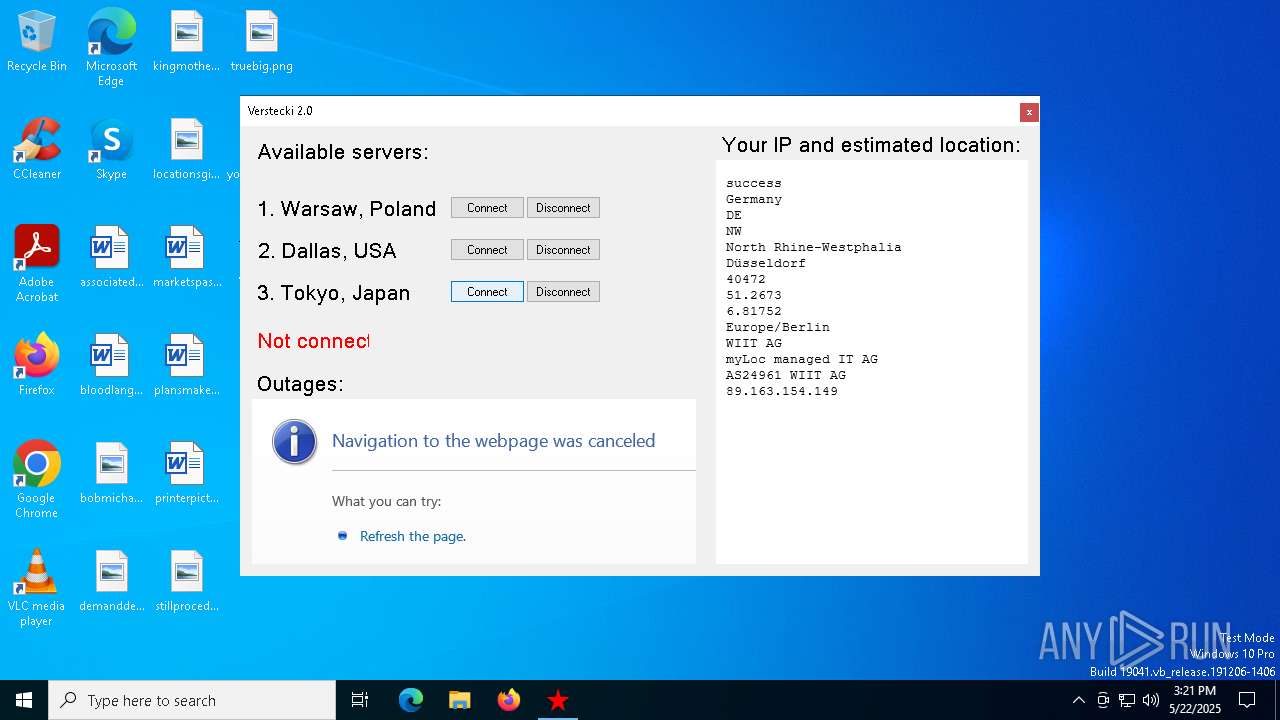
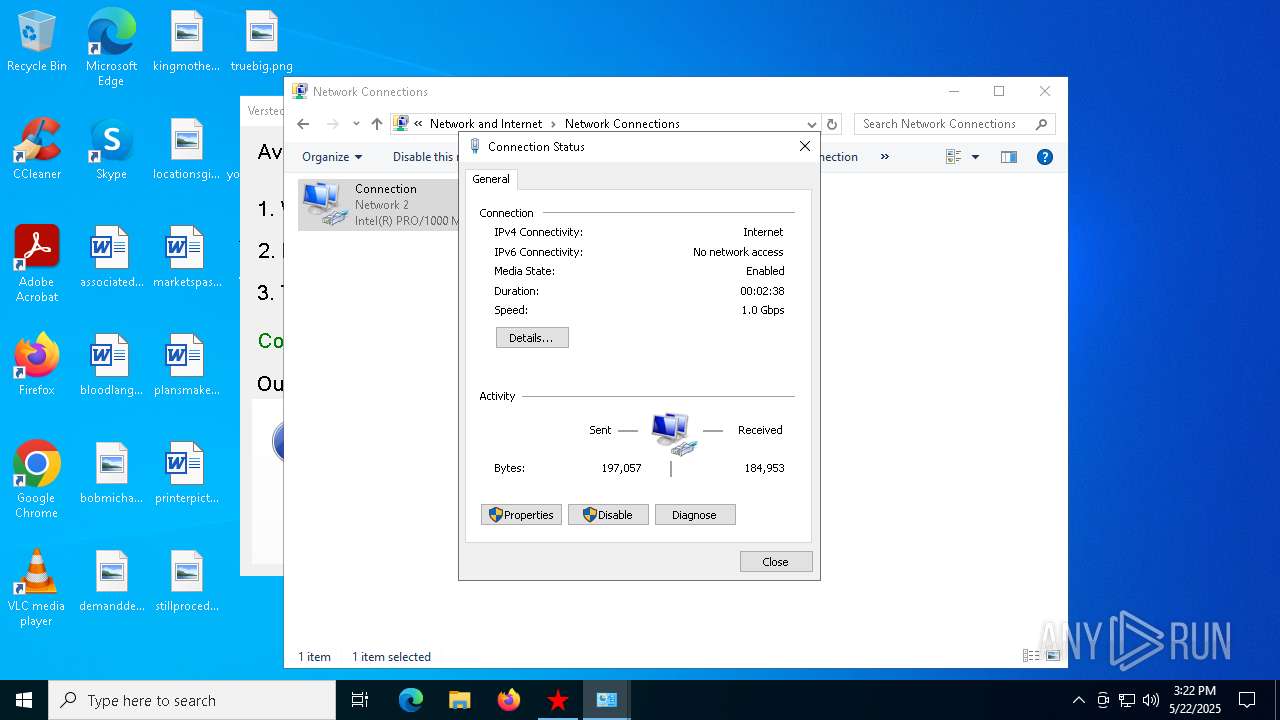
Checks for external IP
- svchost.exe (PID: 2196)
- proxy2.exe (PID: 7184)
The executable file from the user directory is run by the CMD process
- sysproxy.exe (PID: 7972)
- sysproxy.exe (PID: 7804)
- sysproxy.exe (PID: 5988)
- sysproxy.exe (PID: 7944)
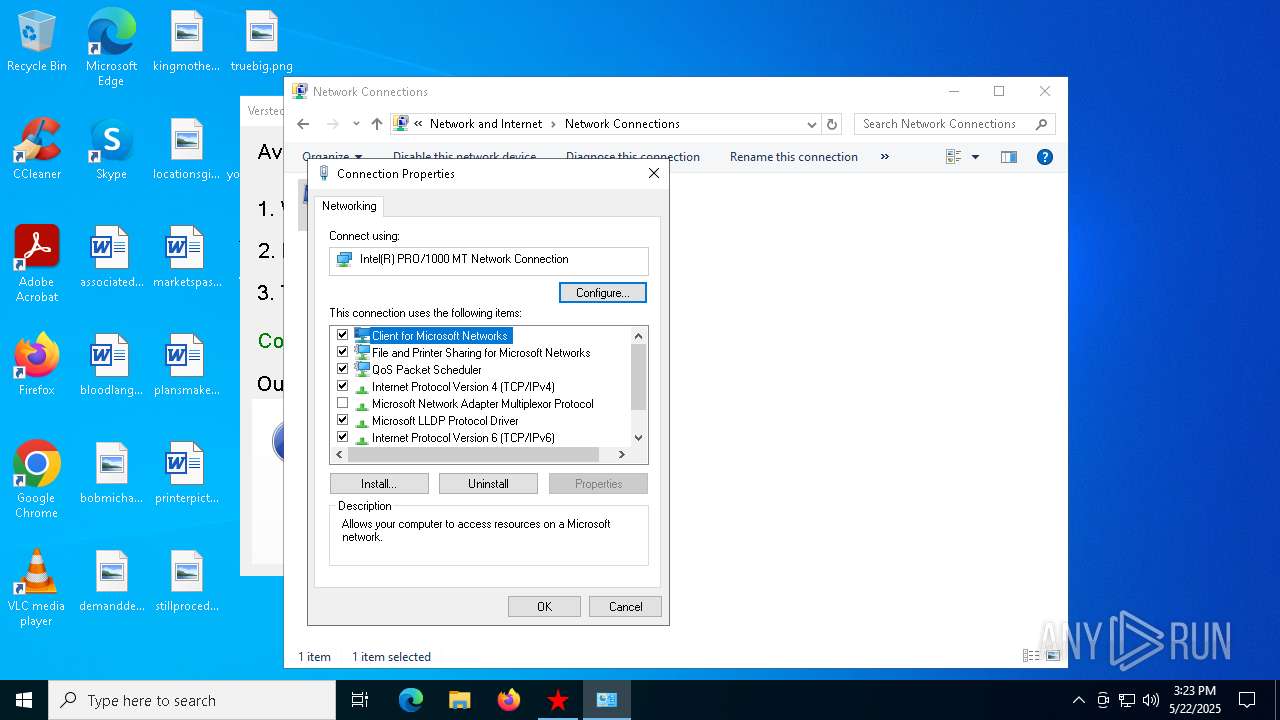
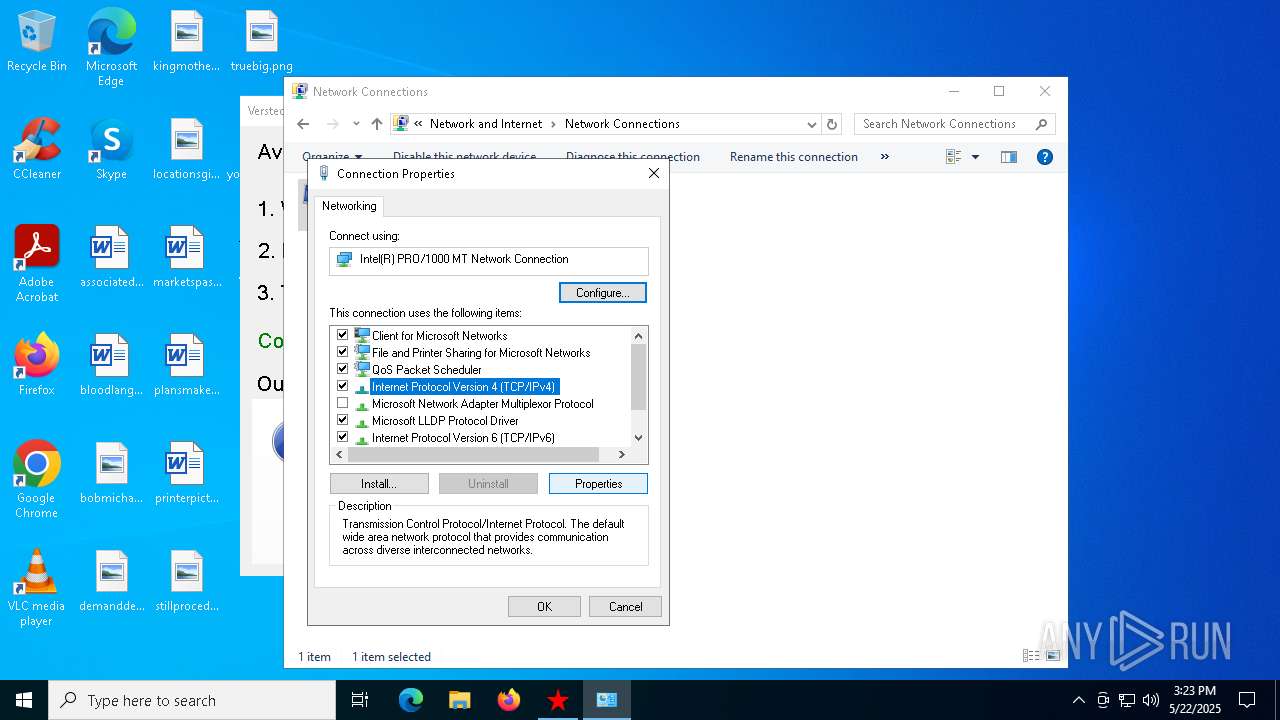
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 4380)
- dllhost.exe (PID: 7360)
- dllhost.exe (PID: 7692)
Connects to unusual port
- proxy2.exe (PID: 7184)
Executing commands from a ".bat" file
- proxy2.exe (PID: 7184)
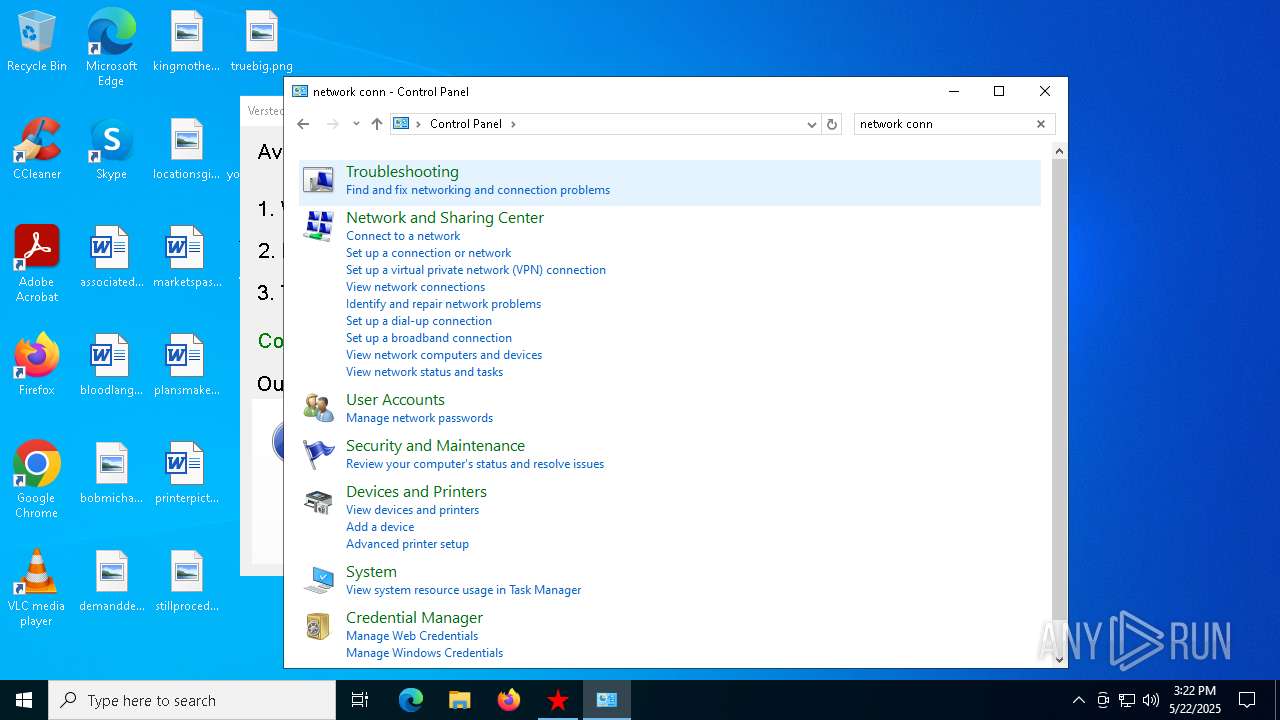
Reads Internet Explorer settings
- proxy2.exe (PID: 7184)
Starts CMD.EXE for commands execution
- proxy2.exe (PID: 7184)
INFO
Create files in a temporary directory
- Verstecki 2.0.exe (PID: 4452)
Checks supported languages
- Verstecki 2.0.exe (PID: 4452)
- proxy2.exe (PID: 7184)
- sysproxy.exe (PID: 7972)
- sysproxy.exe (PID: 7804)
Reads the computer name
- Verstecki 2.0.exe (PID: 4452)
- proxy2.exe (PID: 7184)
- sysproxy.exe (PID: 7972)
- sysproxy.exe (PID: 7804)
Process checks computer location settings
- Verstecki 2.0.exe (PID: 4452)
- proxy2.exe (PID: 7184)
Reads the machine GUID from the registry
- proxy2.exe (PID: 7184)
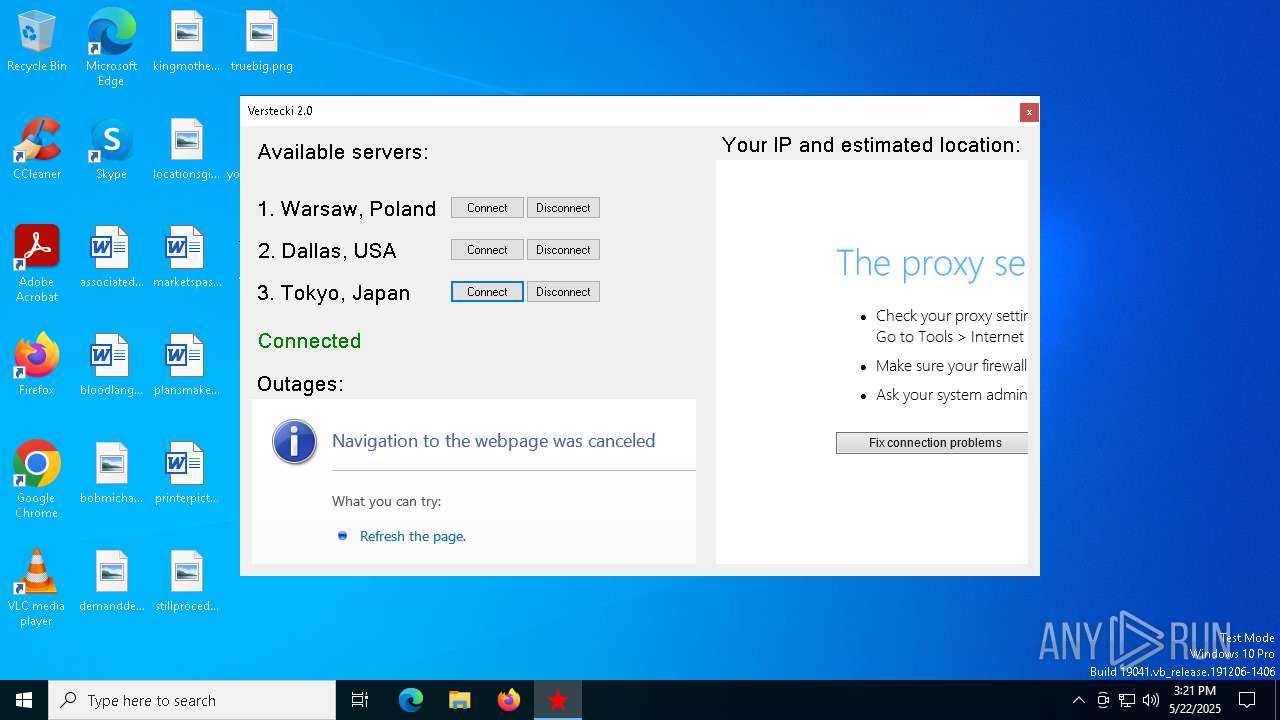
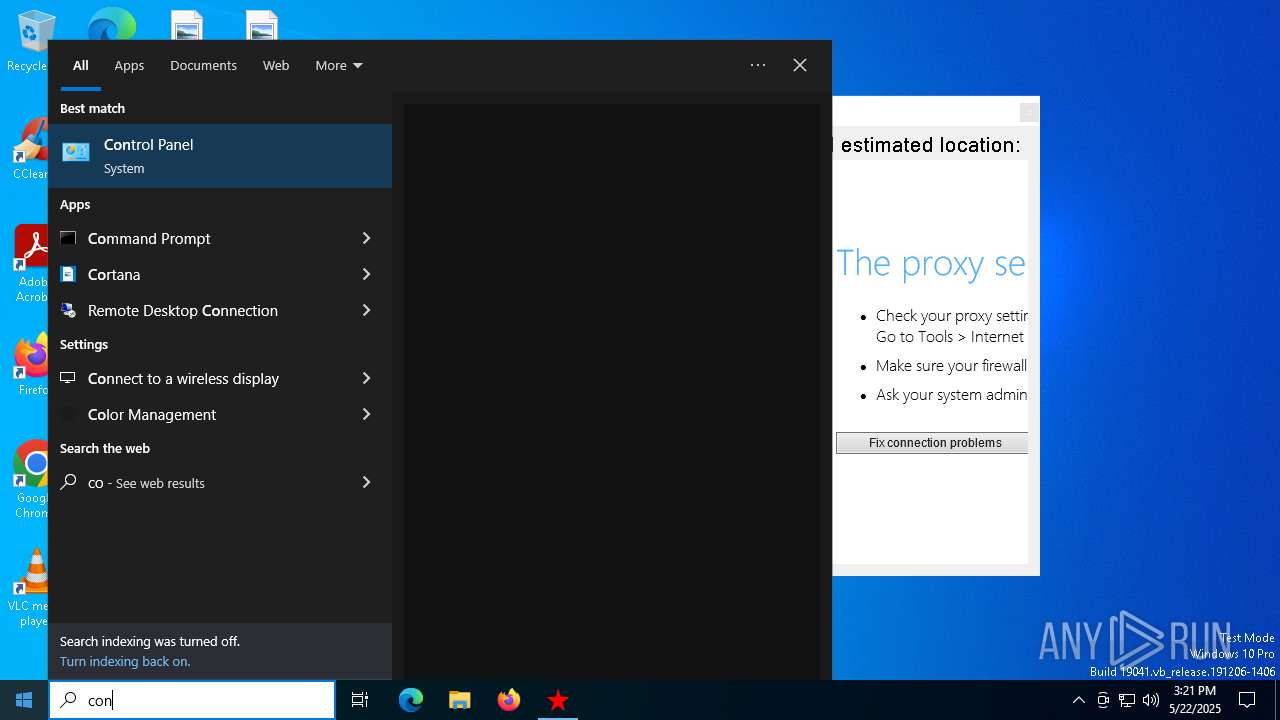
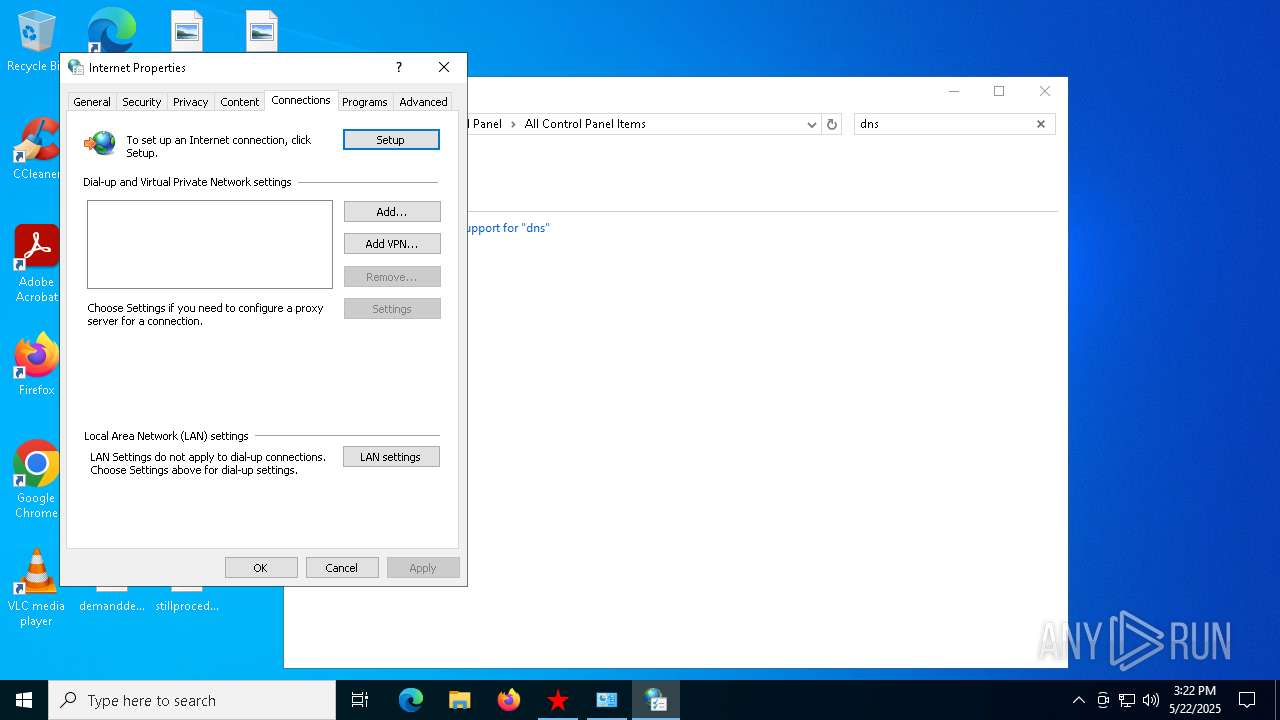
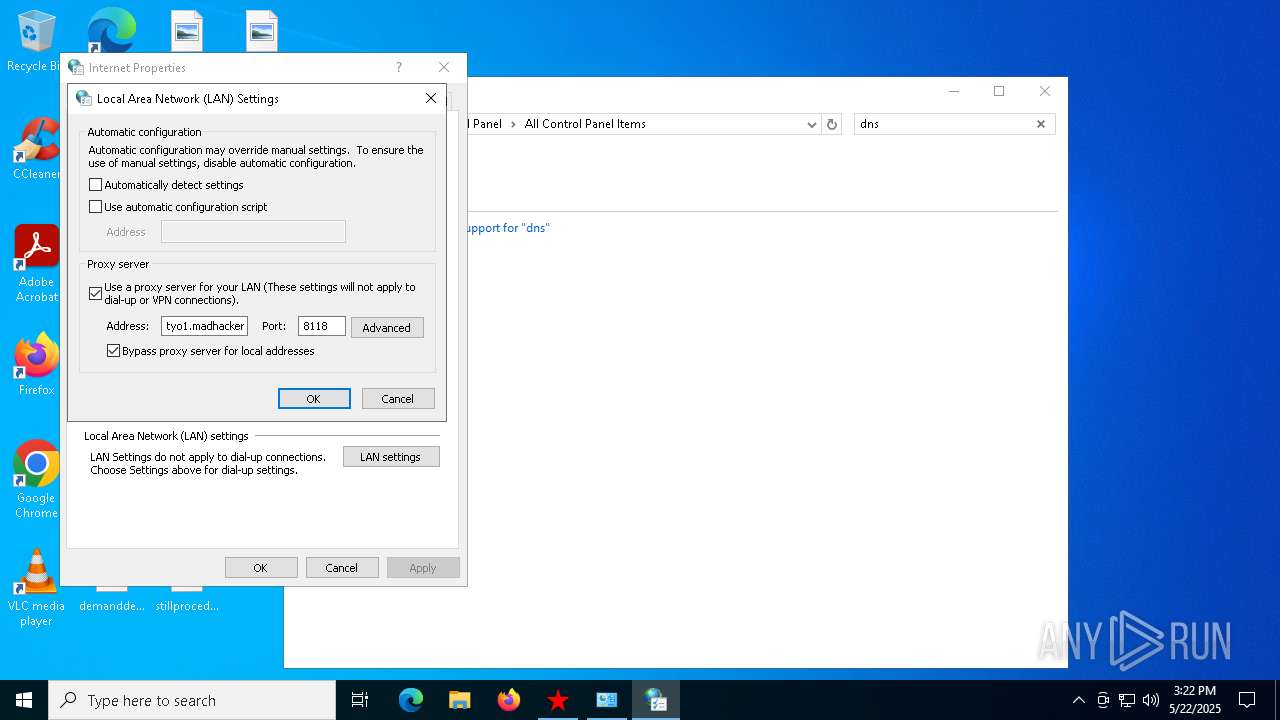
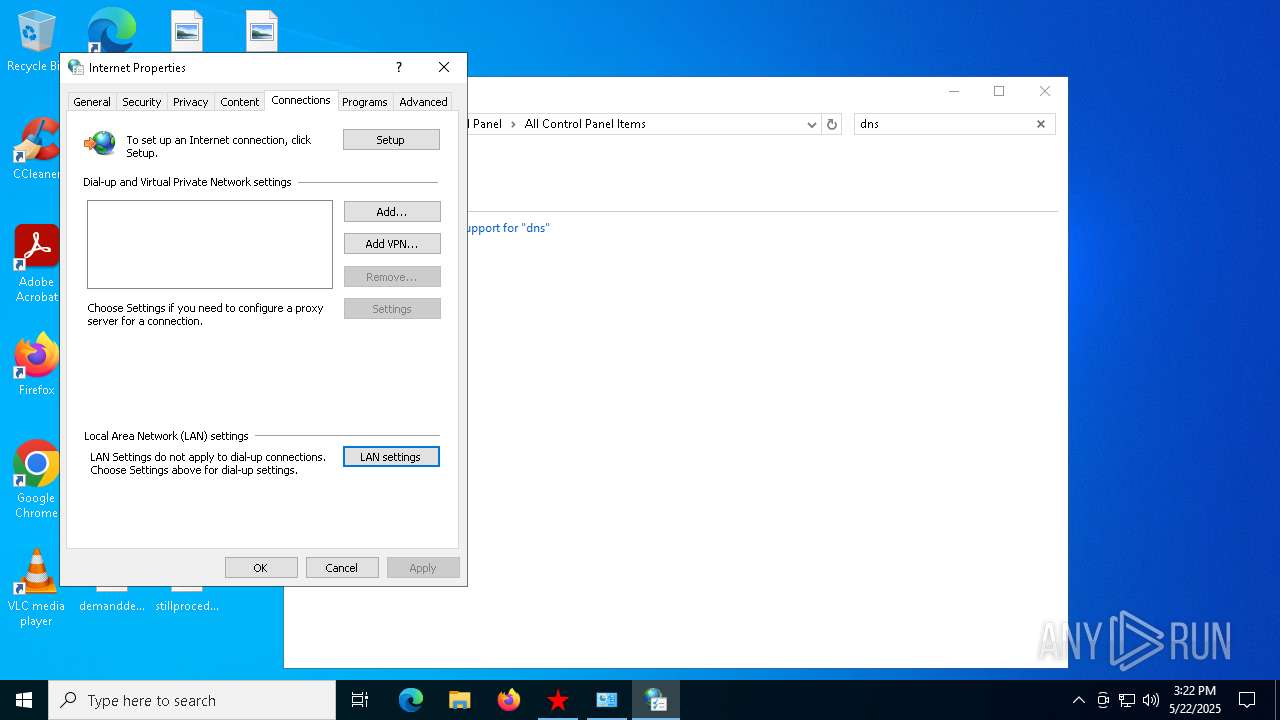
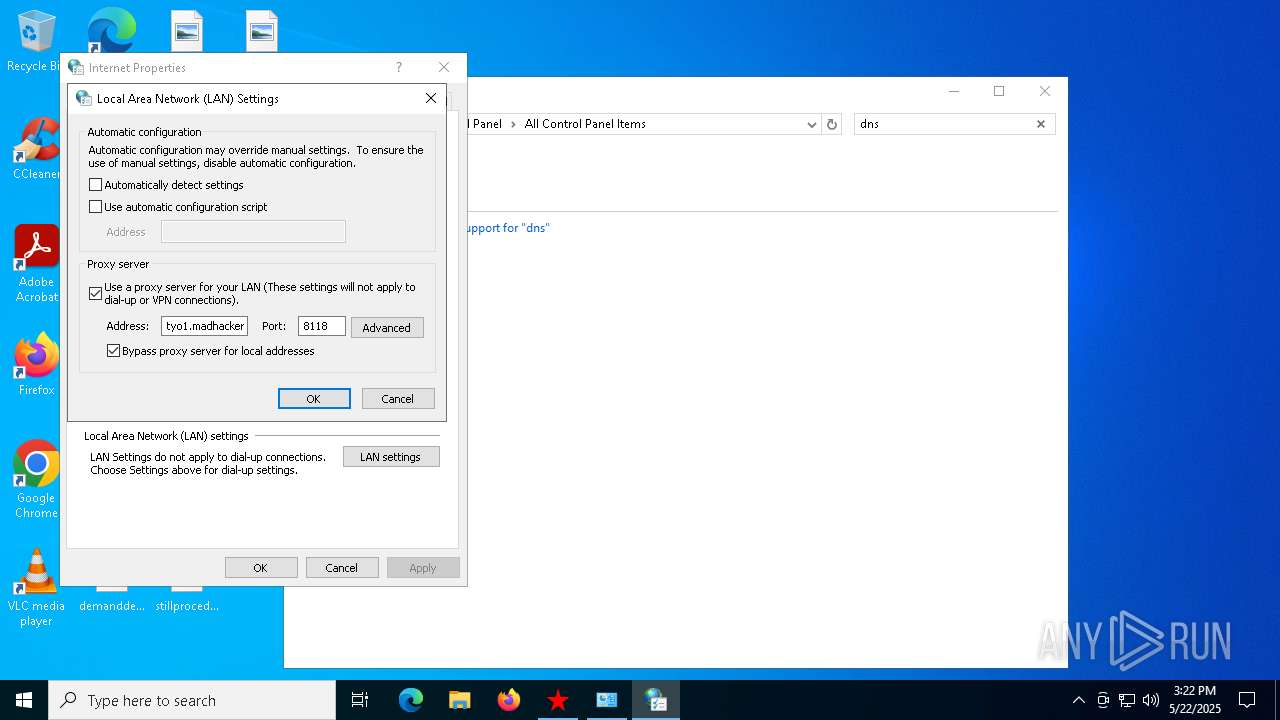
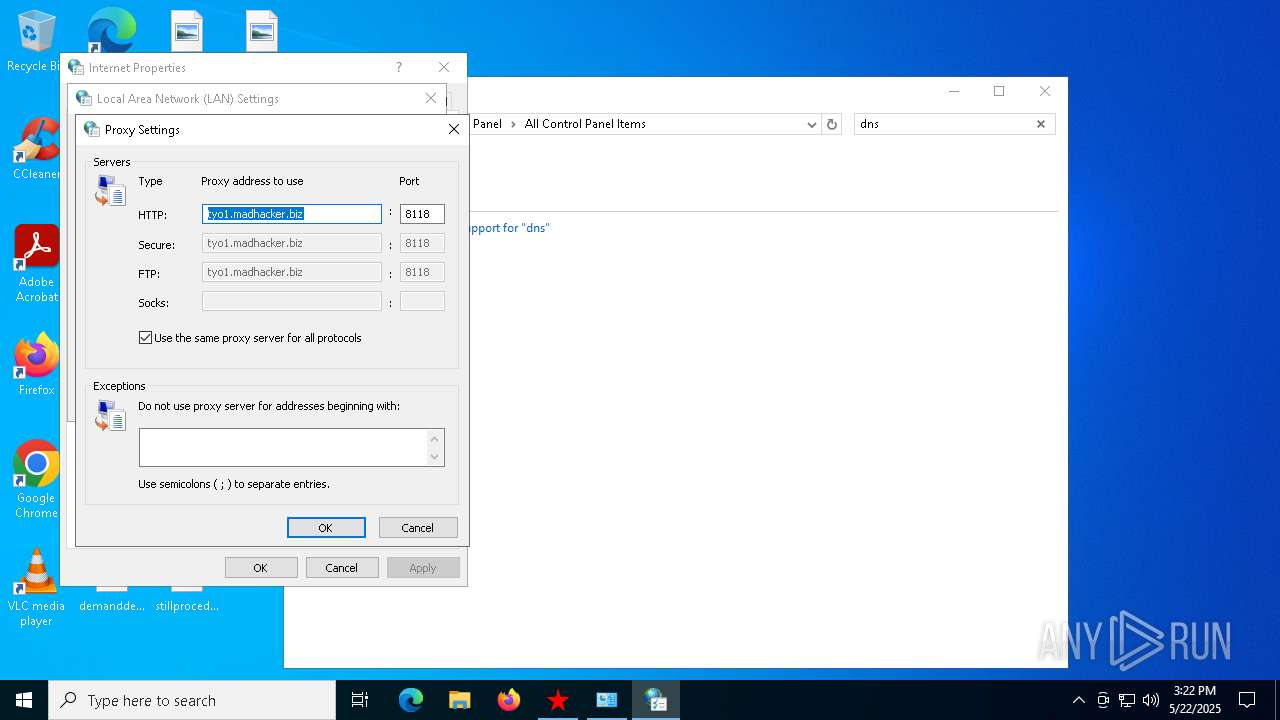
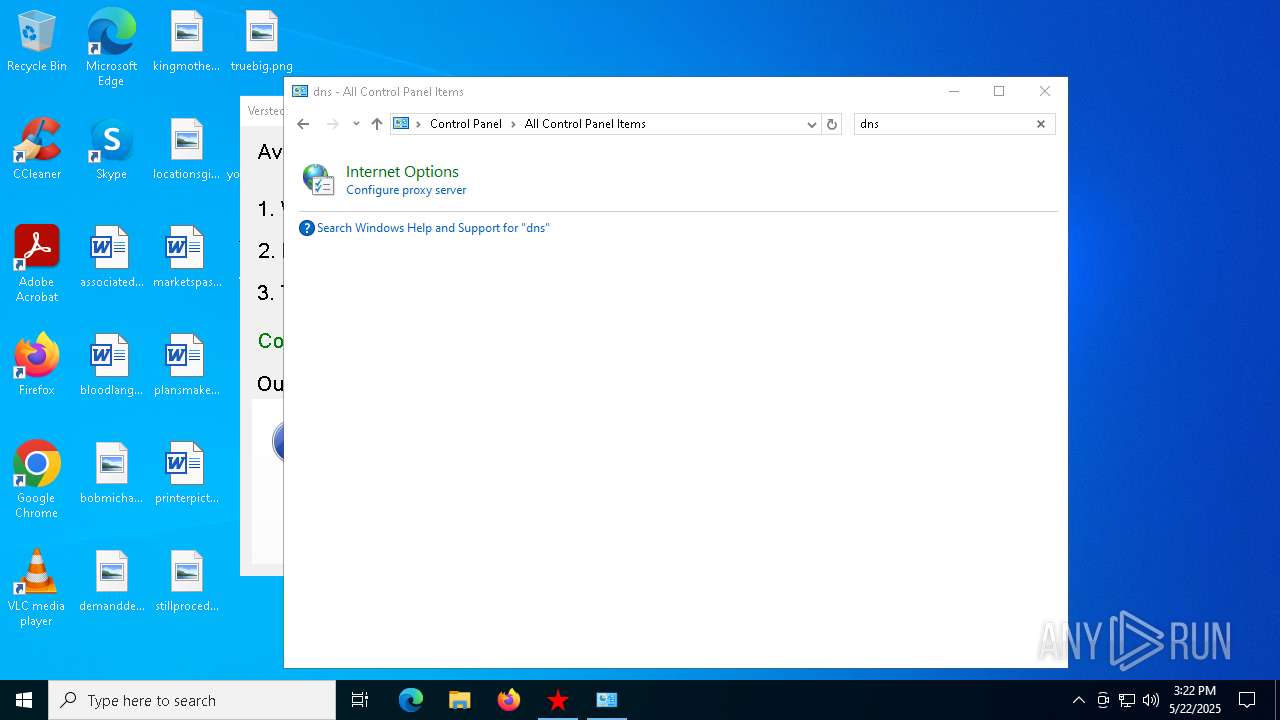
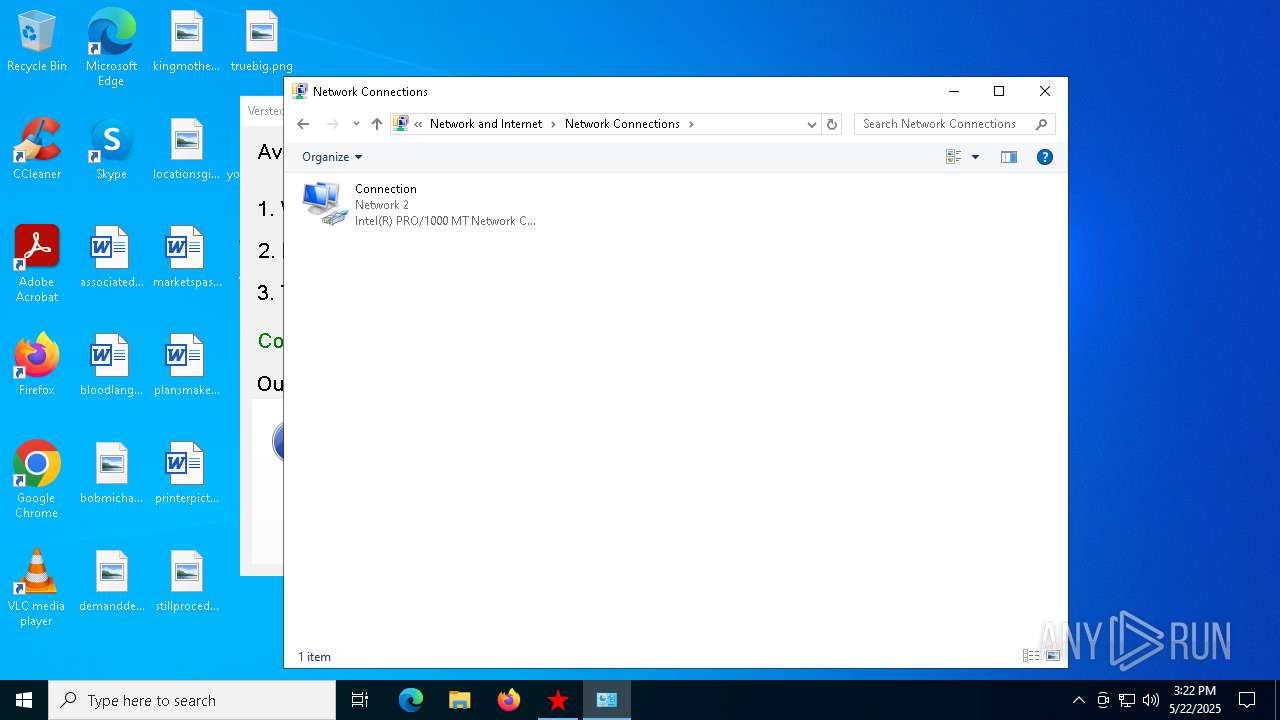
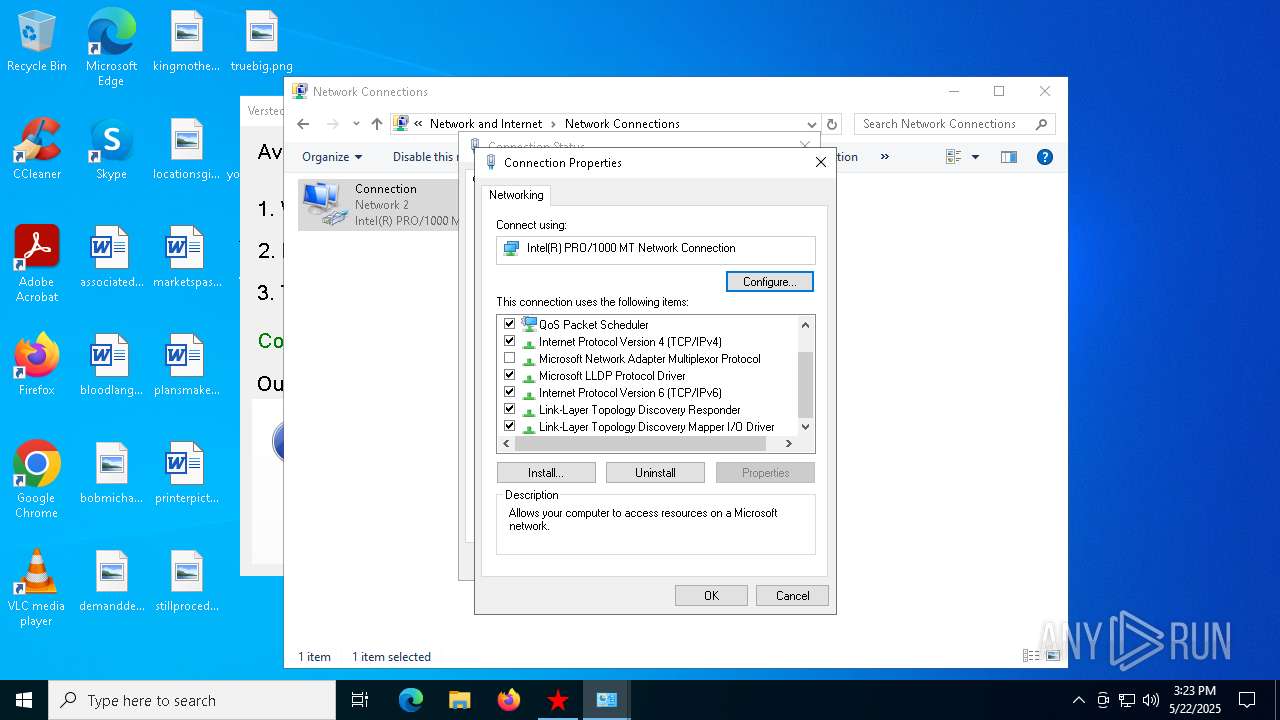
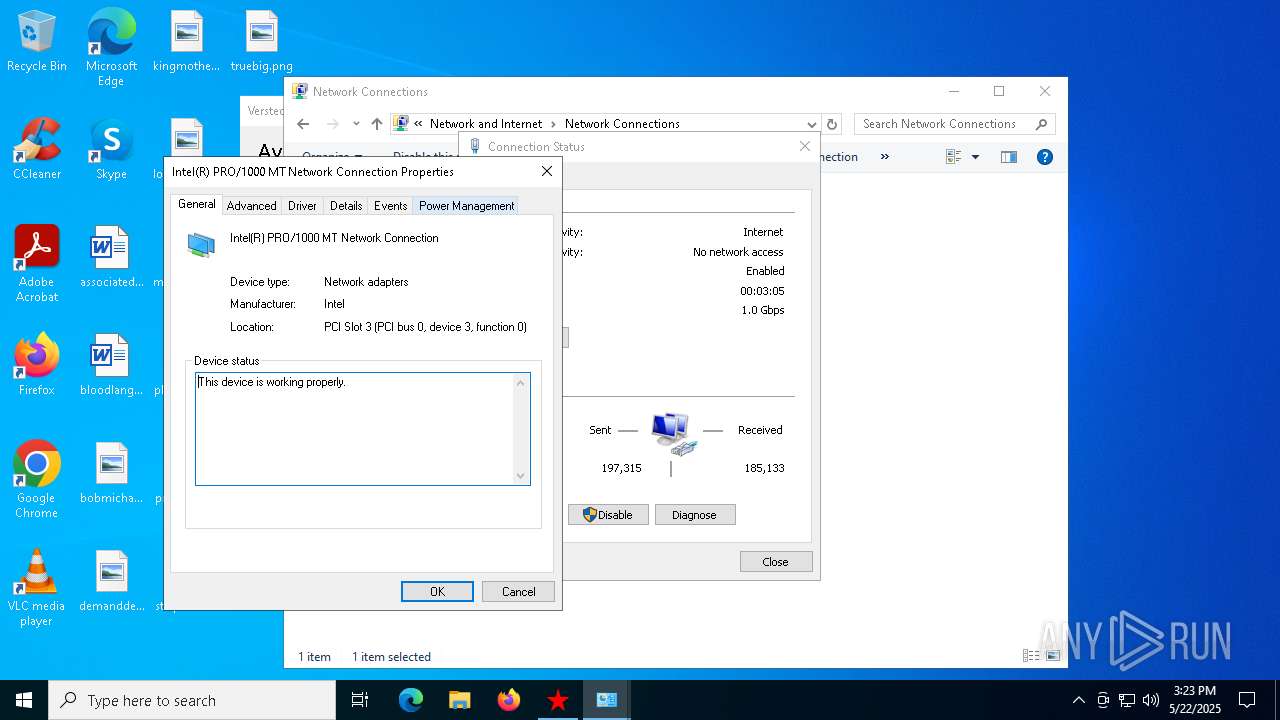
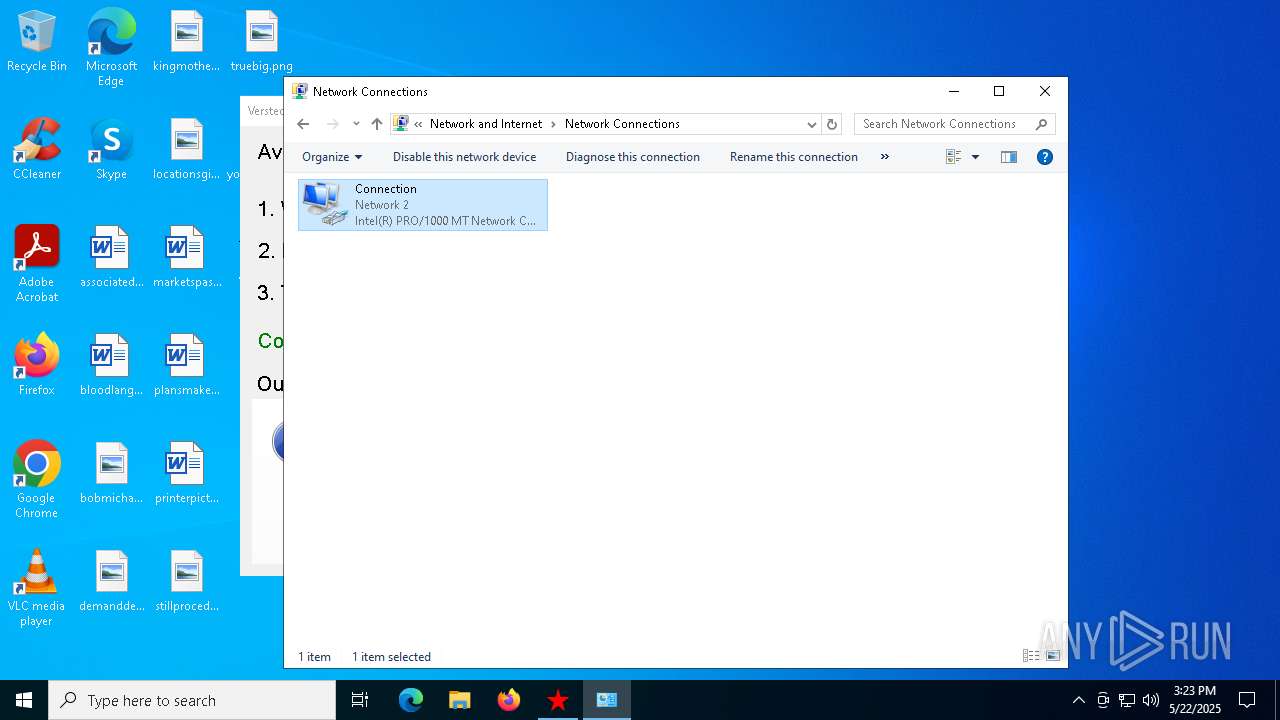
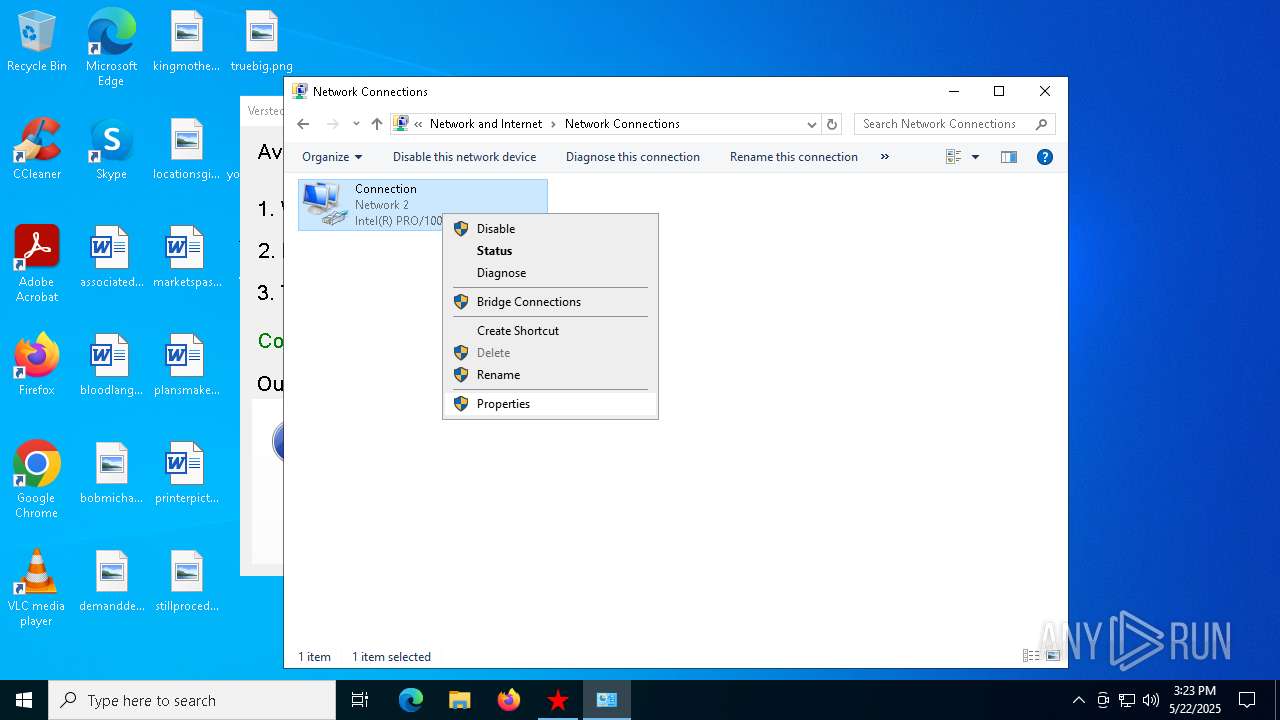
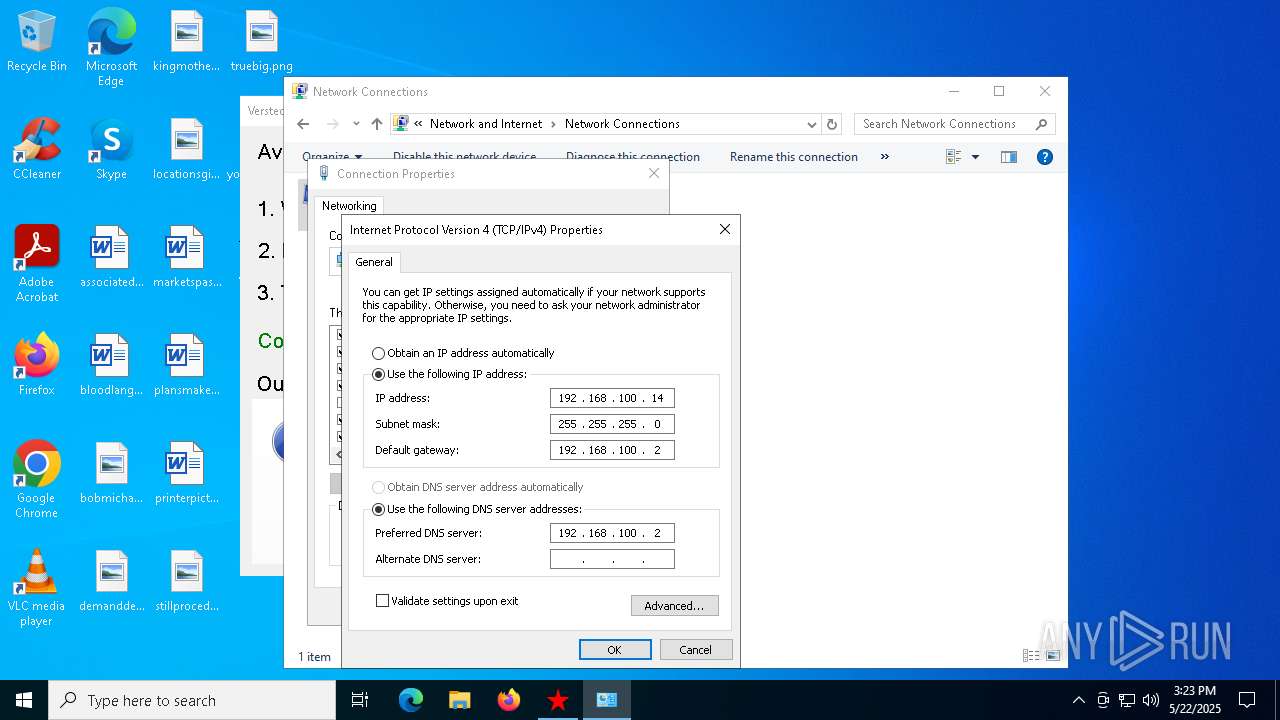
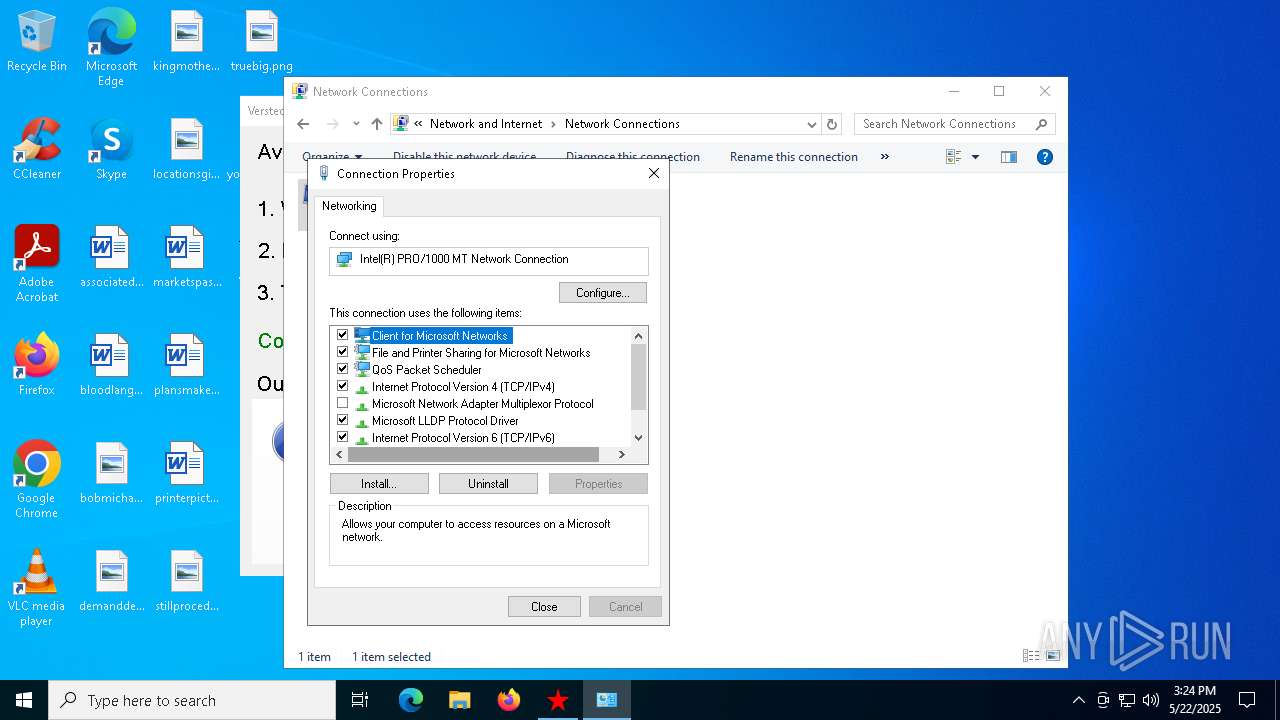
Checks proxy server information
- proxy2.exe (PID: 7184)
- rundll32.exe (PID: 5064)
- sysproxy.exe (PID: 7972)
- slui.exe (PID: 6760)
- sysproxy.exe (PID: 7804)
Disables trace logs
- sysproxy.exe (PID: 7972)
- explorer.exe (PID: 4380)
- rundll32.exe (PID: 5064)
- sysproxy.exe (PID: 7804)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4380)
- rundll32.exe (PID: 5064)
- dllhost.exe (PID: 7360)
- dllhost.exe (PID: 7692)
Checks transactions between databases Windows and Oracle
- explorer.exe (PID: 4380)
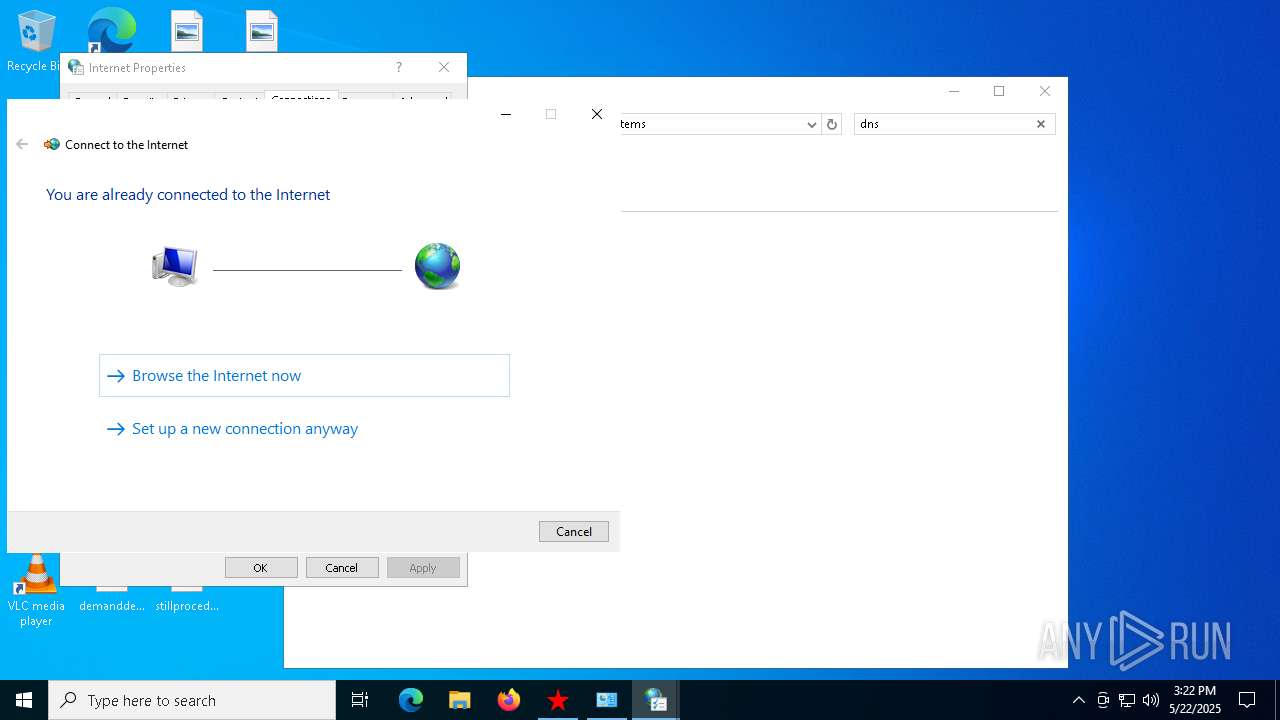
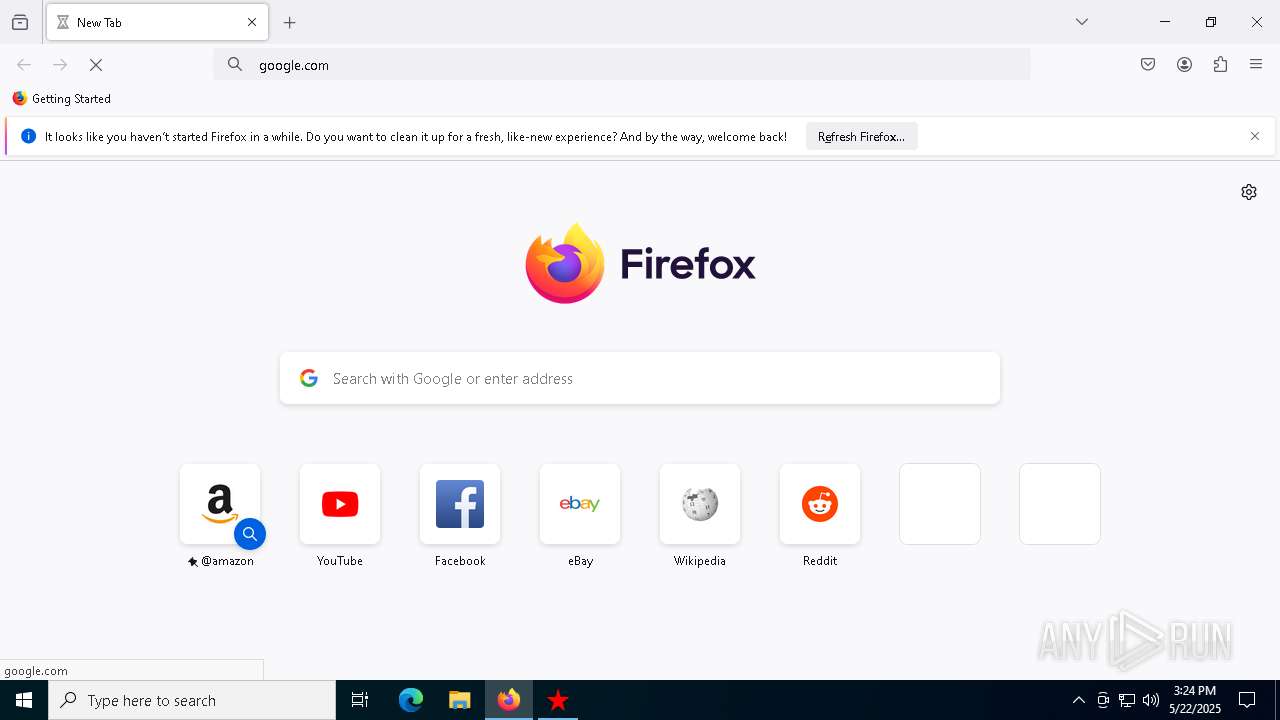
Manual execution by a user
- firefox.exe (PID: 208)
Application launched itself
- firefox.exe (PID: 208)
- firefox.exe (PID: 7272)
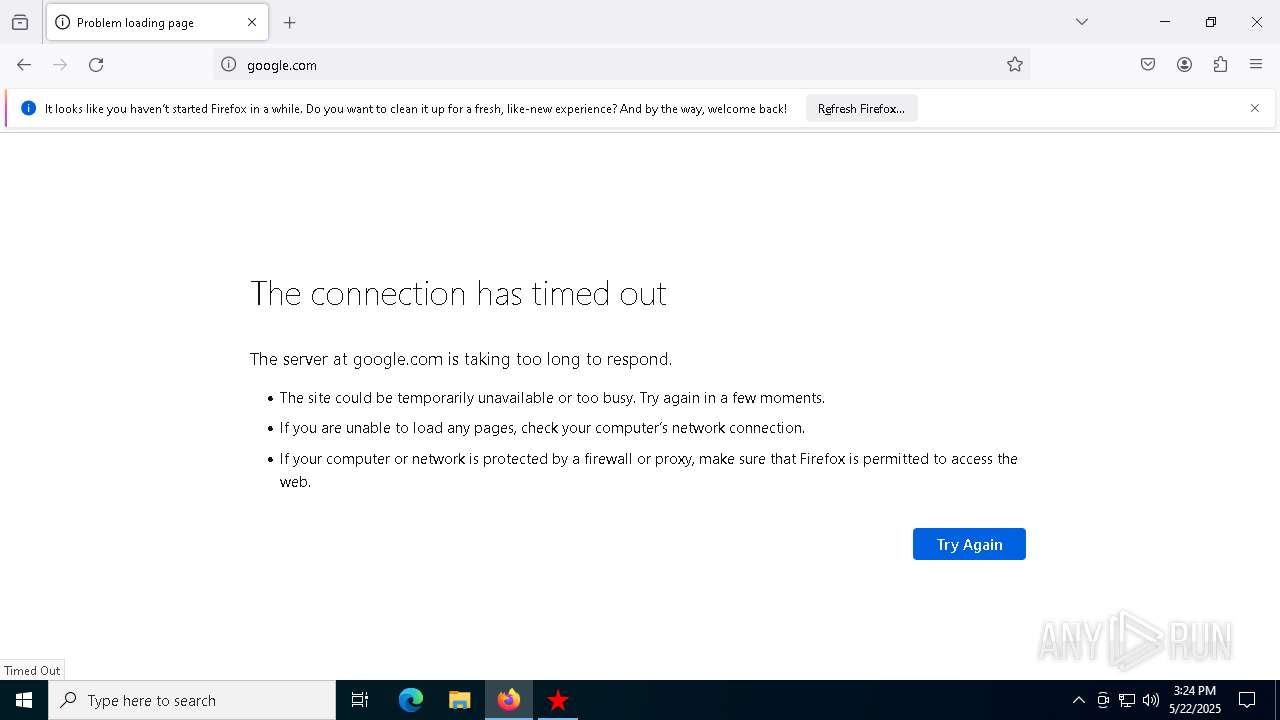
Connects to unusual port
- firefox.exe (PID: 7272)
Creates files or folders in the user directory
- proxy2.exe (PID: 7184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:11 09:16:47+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 201728 |
| InitializedDataSize: | 79872 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1eef0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
169
Monitored processes
37
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | — | explorer.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 123.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=1908 -parentBuildID 20240213221259 -prefsHandle 1848 -prefMapHandle 1840 -prefsLen 31031 -prefMapSize 244583 -appDir "C:\Program Files\Mozilla Firefox\browser" - {4a8c8fe0-b944-43cb-a3df-3cbfcf5c655f} 7272 "\\.\pipe\gecko-crash-server-pipe.7272" 2404d2eae10 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4016 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4260 -childID 2 -isForBrowser -prefsHandle 4252 -prefMapHandle 3080 -prefsLen 36588 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {830a67ec-7141-4c85-ad7e-c63603c829c7} 7272 "\\.\pipe\gecko-crash-server-pipe.7272" 240544c8850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 4180 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\proxy2\tokyo.bat" " | C:\Windows\SysWOW64\cmd.exe | — | proxy2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4336 | C:\WINDOWS\SysWOW64\DllHost.exe /Processid:{06622D85-6856-4460-8DE1-A81921B41C4B} | C:\Windows\SysWOW64\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4380 | C:\WINDOWS\explorer.exe /factory,{5BD95610-9434-43C2-886C-57852CC8A120} -Embedding | C:\Windows\explorer.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4452 | "C:\Users\admin\Desktop\Verstecki 2.0.exe" | C:\Users\admin\Desktop\Verstecki 2.0.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 4528 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel=4896 -childID 4 -isForBrowser -prefsHandle 4948 -prefMapHandle 4924 -prefsLen 31144 -prefMapSize 244583 -jsInitHandle 1520 -jsInitLen 235124 -parentBuildID 20240213221259 -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - {ba7f4198-9e32-4731-b7f0-98ff7ab56f15} 7272 "\\.\pipe\gecko-crash-server-pipe.7272" 24057b3e850 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 123.0 Modules
| |||||||||||||||
| 5064 | "C:\Windows\System32\rundll32.exe" C:\Windows\System32\shell32.dll,Control_RunDLL C:\Windows\System32\inetcpl.cpl | C:\Windows\System32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
28 384
Read events
28 216
Write events
160
Delete events
8
Modification events
| (PID) Process: | (7184) proxy2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (7184) proxy2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (7184) proxy2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (7184) proxy2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main\WindowsSearch |
| Operation: | write | Name: | Version |
Value: WS not running | |||
| (PID) Process: | (7184) proxy2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | DisableFirstRunCustomize |
Value: 1 | |||
| (PID) Process: | (7972) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (7972) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | EnableAutoFileTracing |
Value: 0 | |||
| (PID) Process: | (7972) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (7972) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: | |||
| (PID) Process: | (7972) sysproxy.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Tracing\sysproxy_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: | |||
Executable files
2
Suspicious files
64
Text files
23
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7272 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 4452 | Verstecki 2.0.exe | C:\Users\admin\AppData\Local\Temp\proxy2\tokyo.bat | text | |
MD5:4A02329C4CCF6D8DB159F51CF2423A6C | SHA256:F0B512BE81F1A379AA121974A977603002017E238E68A8F8415D57C5DC89BEDB | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\9kie7cg6.default-release\startupCache\urlCache-current.bin | binary | |
MD5:297E88D7CEB26E549254EC875649F4EB | SHA256:8B75D4FB1845BAA06122888D11F6B65E6A36B140C54A72CC13DF390FD7C95702 | |||
| 4452 | Verstecki 2.0.exe | C:\Users\admin\AppData\Local\Temp\proxy2\warsaw.bat | text | |
MD5:829C4553AC0215C7CC76BB5FA9C01B26 | SHA256:7E225A2D5C51769C400CCD13B75F01C675317CE560F662699121D60160E5A110 | |||
| 4452 | Verstecki 2.0.exe | C:\Users\admin\AppData\Local\Temp\proxy2\tokyo-off.bat | text | |
MD5:F89A8509BA39FCB1A0EDE5289810E3C3 | SHA256:5DBF5582D046F8B2B2DE4E6A17D64ABADCA238FBEE1C13947ECBEA3F1E0025D7 | |||
| 7272 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\9kie7cg6.default-release\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
| 4452 | Verstecki 2.0.exe | C:\Users\admin\AppData\Local\Temp\proxy2\dallas-off.bat | text | |
MD5:AC347D2EFCBBB2FF0EEF8EF07E1F250F | SHA256:F84E6CA9C1BAE6443BBBA93FF2551A805B1B55D00923B523059C99424ABB22E6 | |||
| 4452 | Verstecki 2.0.exe | C:\Users\admin\AppData\Local\Temp\proxy2\sysproxy.exe | executable | |
MD5:380D58A33FAF71547FB97C3FC12A38A9 | SHA256:A918AA182DD57A545B0416E406432A6D09D1232AA0C33A0969DCD39A432D0D6B | |||
| 4452 | Verstecki 2.0.exe | C:\Users\admin\AppData\Local\Temp\proxy2\proxy2.exe | executable | |
MD5:43063D30F8A5DC9C6C8EED52AAC20F9C | SHA256:A3D7F85CC0CD373C6B8C14010468009C5B1E757D5D5D427079701BB639C5AF78 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
110
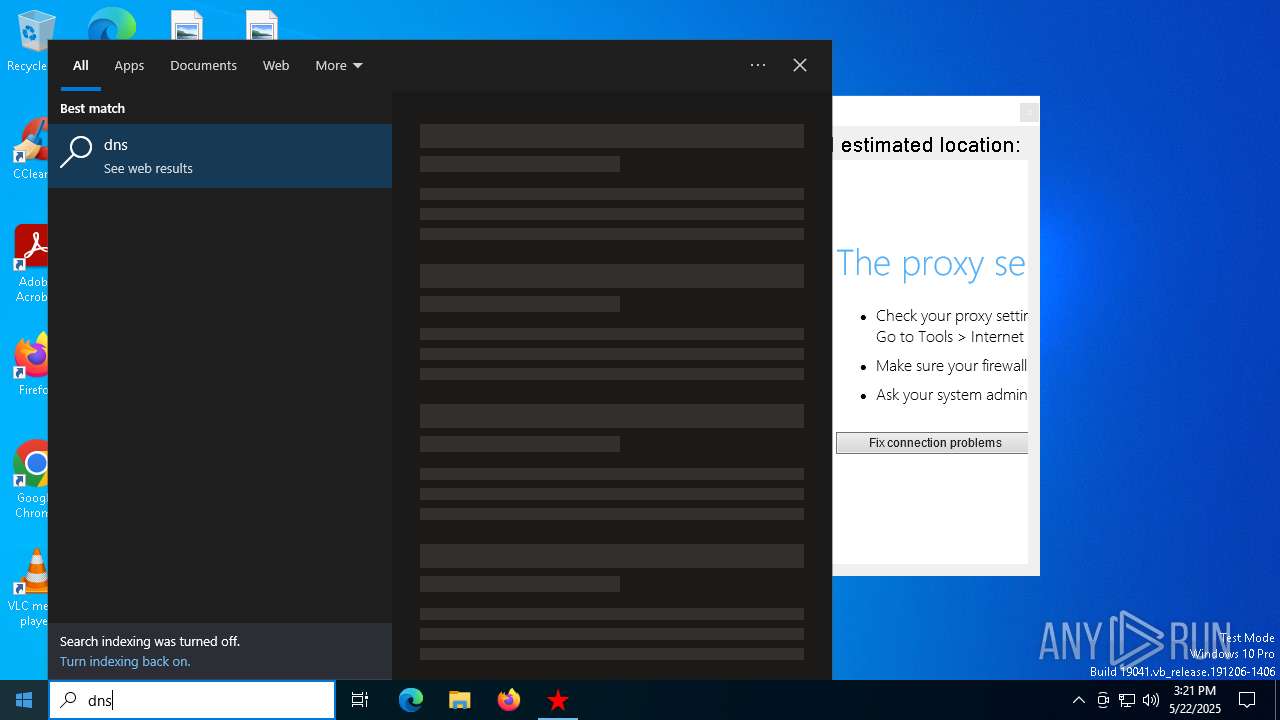
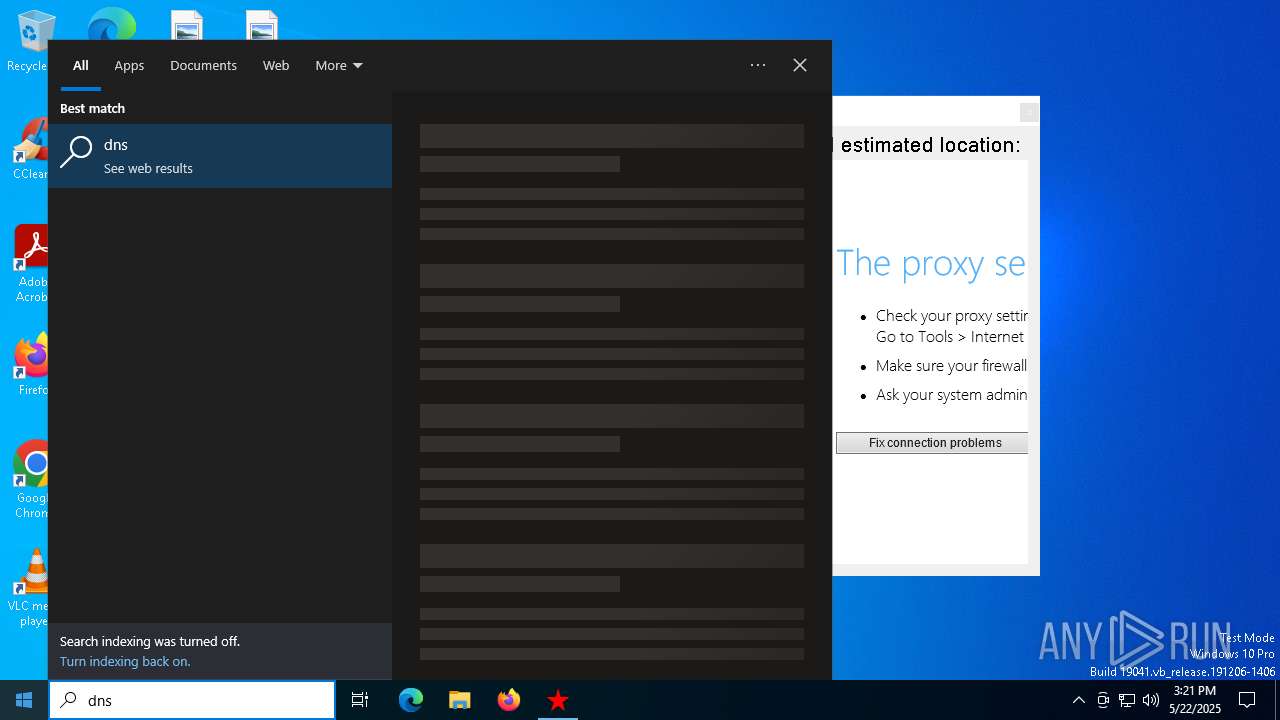
DNS requests
45
Threats
45
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.48.23.175:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7184 | proxy2.exe | GET | 200 | 208.95.112.1:80 | http://ip-api.com/line | unknown | — | — | whitelisted |
7528 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7528 | SIHClient.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.175:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7184 | proxy2.exe | 208.95.112.1:80 | ip-api.com | TUT-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ip-api.com |
| whitelisted |
ams3.madhacker.biz |
| unknown |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Check (ip-api .com) |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.madhacker .biz Domain |
2196 | svchost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain in DNS Lookup (ip-api .com) |
7184 | proxy2.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup ip-api.com |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.madhacker .biz Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.madhacker .biz Domain |
2196 | svchost.exe | Potentially Bad Traffic | ET INFO Observed DNS Query to .biz TLD |
2196 | svchost.exe | Potentially Bad Traffic | ET DYN_DNS DYNAMIC_DNS Query to a *.madhacker .biz Domain |