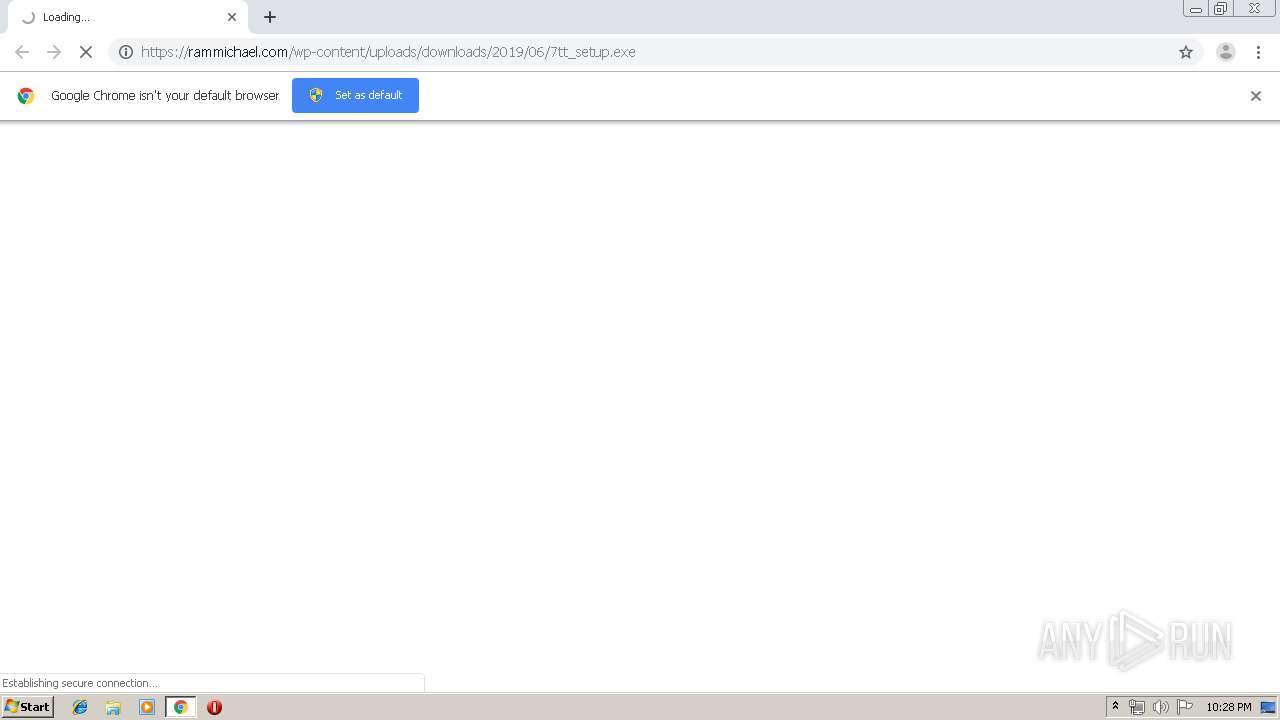
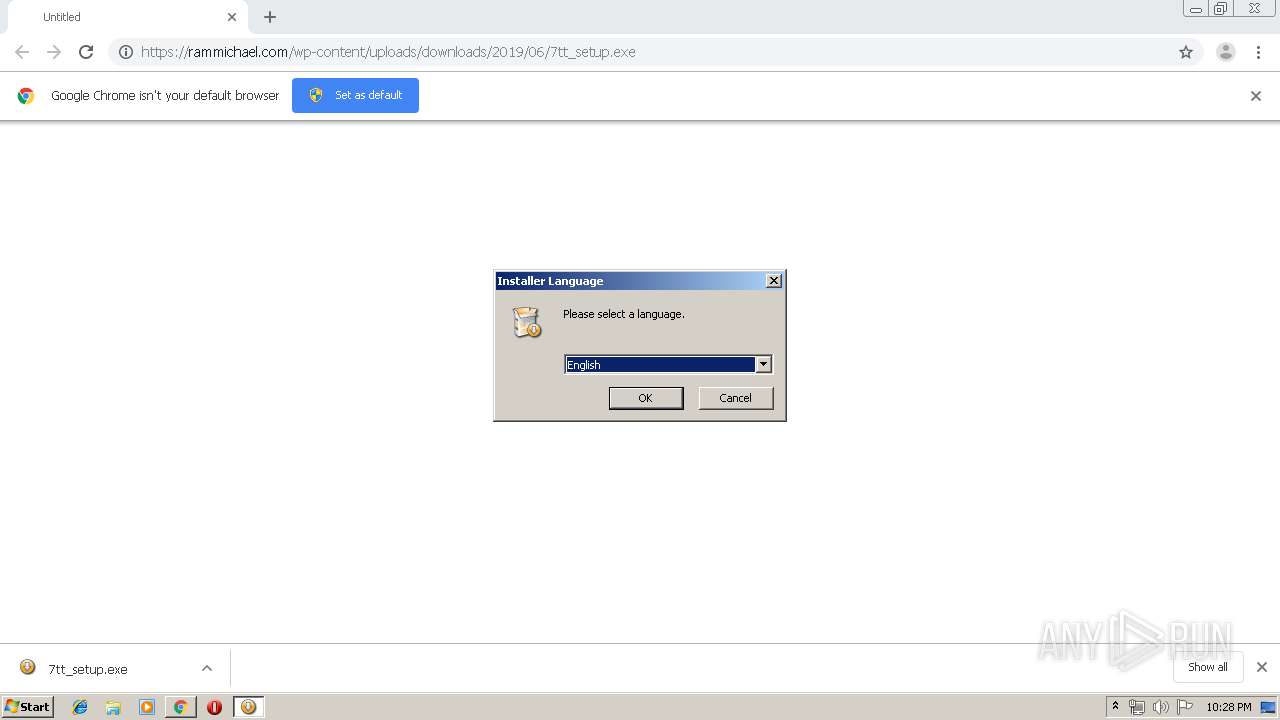
| URL: | https://rammichael.com/wp-content/uploads/downloads/2019/06/7tt_setup.exe |
| Full analysis: | https://app.any.run/tasks/1242edc2-62fa-4324-bfef-3583933bb323 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 21:27:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 8FA0C16F6BDE7B17581DCB8E43087830 |
| SHA1: | 7F5A6F6E7154DC4811BC71BB6552CF74AED47A96 |
| SHA256: | 2B187242E3A81854DBF9AAAC0CF9DCC65AF1131FD7D5A5BF00B1073EEB350938 |
| SSDEEP: | 3:N8JVOlAQy846KX25fcWP4A:2JVOlAZ8aG5fP4A |
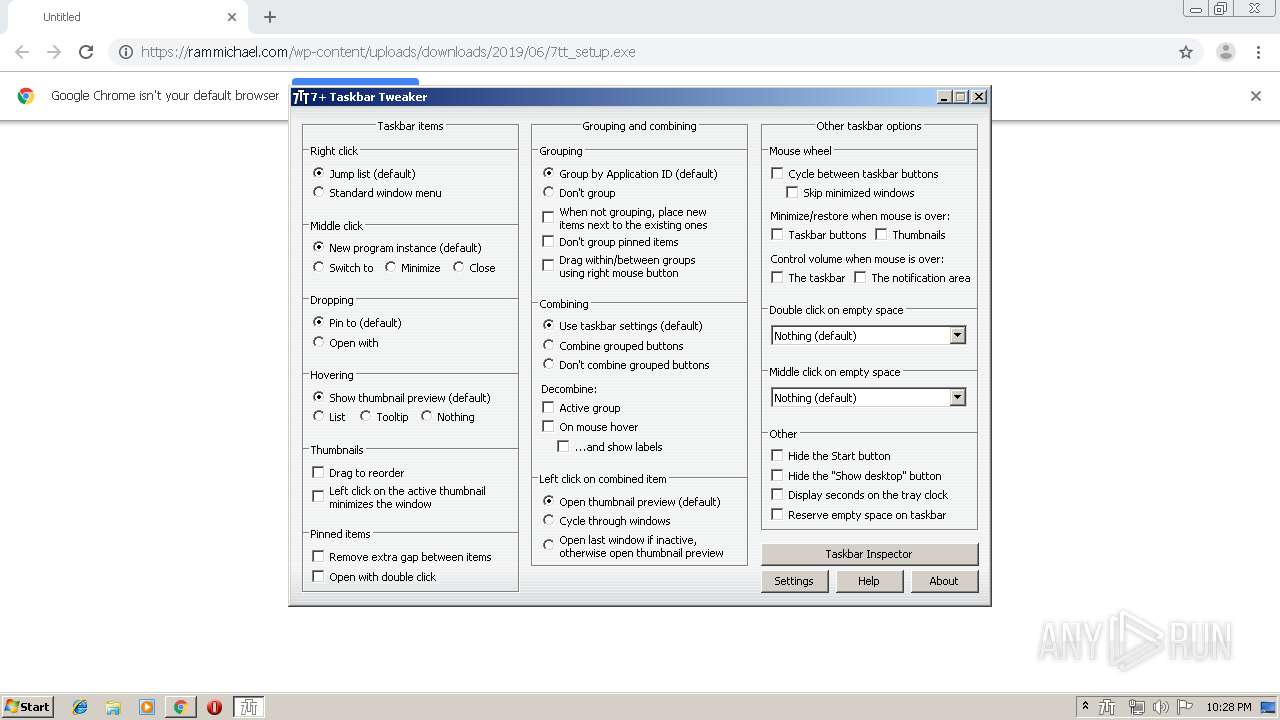
MALICIOUS
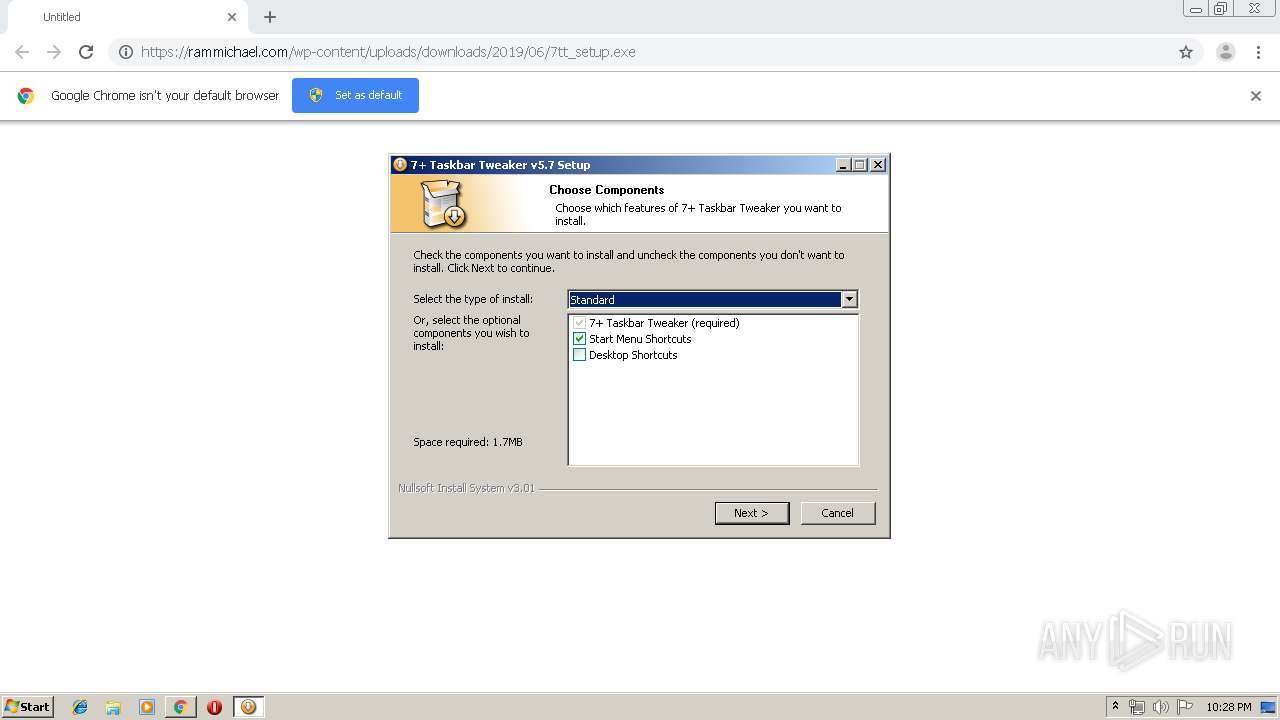
Application was dropped or rewritten from another process
- 7tt_setup.exe (PID: 2232)
- 7+ Taskbar Tweaker.exe (PID: 2816)
Loads dropped or rewritten executable
- 7tt_setup.exe (PID: 2232)
- explorer.exe (PID: 128)
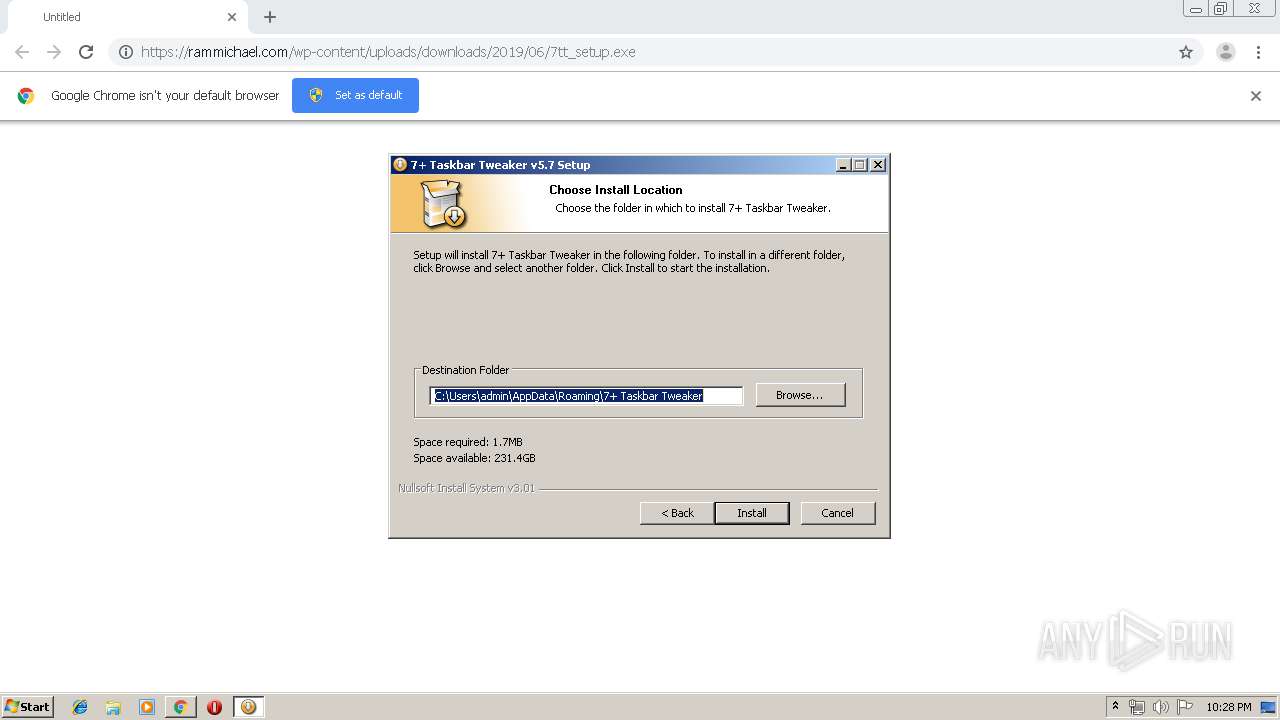
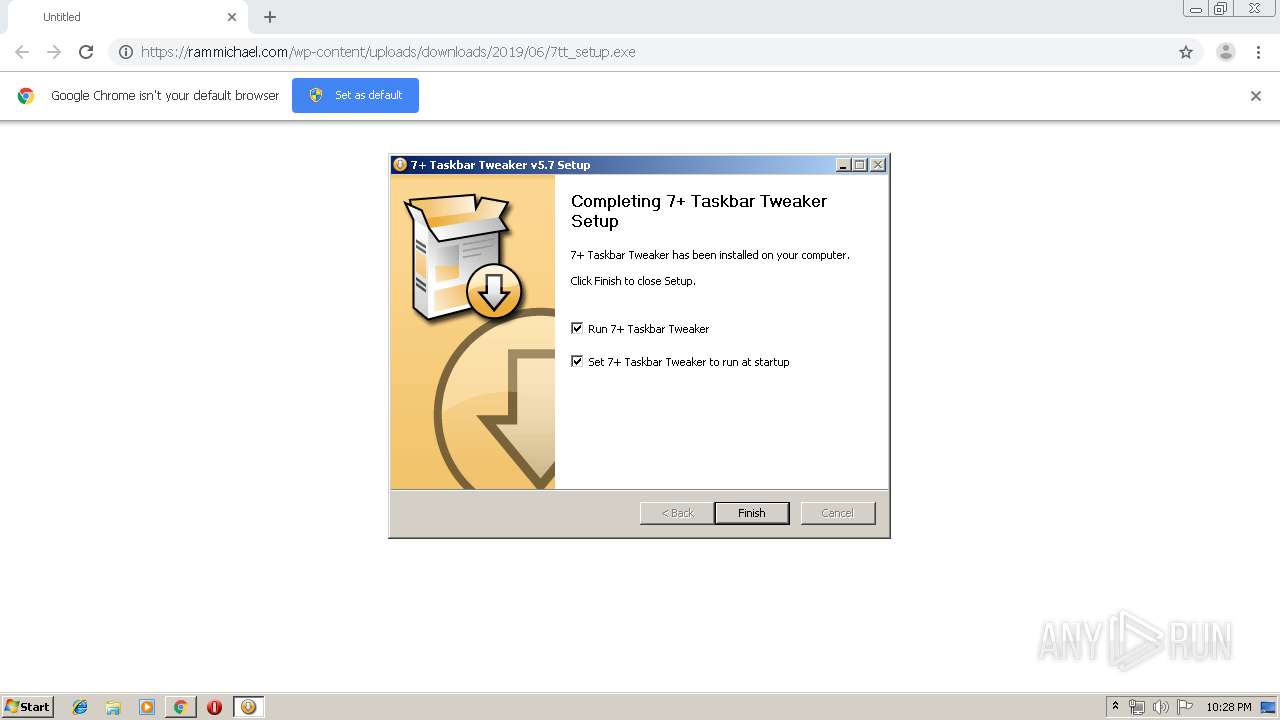
Changes the autorun value in the registry
- 7tt_setup.exe (PID: 2232)
Runs injected code in another process
- 7+ Taskbar Tweaker.exe (PID: 2816)
Application was injected by another process
- explorer.exe (PID: 128)
Connects to CnC server
- 7+ Taskbar Tweaker.exe (PID: 2816)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2436)
- chrome.exe (PID: 2176)
- 7tt_setup.exe (PID: 2232)
Creates a software uninstall entry
- 7tt_setup.exe (PID: 2232)
Creates files in the user directory
- 7+ Taskbar Tweaker.exe (PID: 2816)
- 7tt_setup.exe (PID: 2232)
INFO
Application launched itself
- chrome.exe (PID: 2176)
Reads Internet Cache Settings
- chrome.exe (PID: 2176)
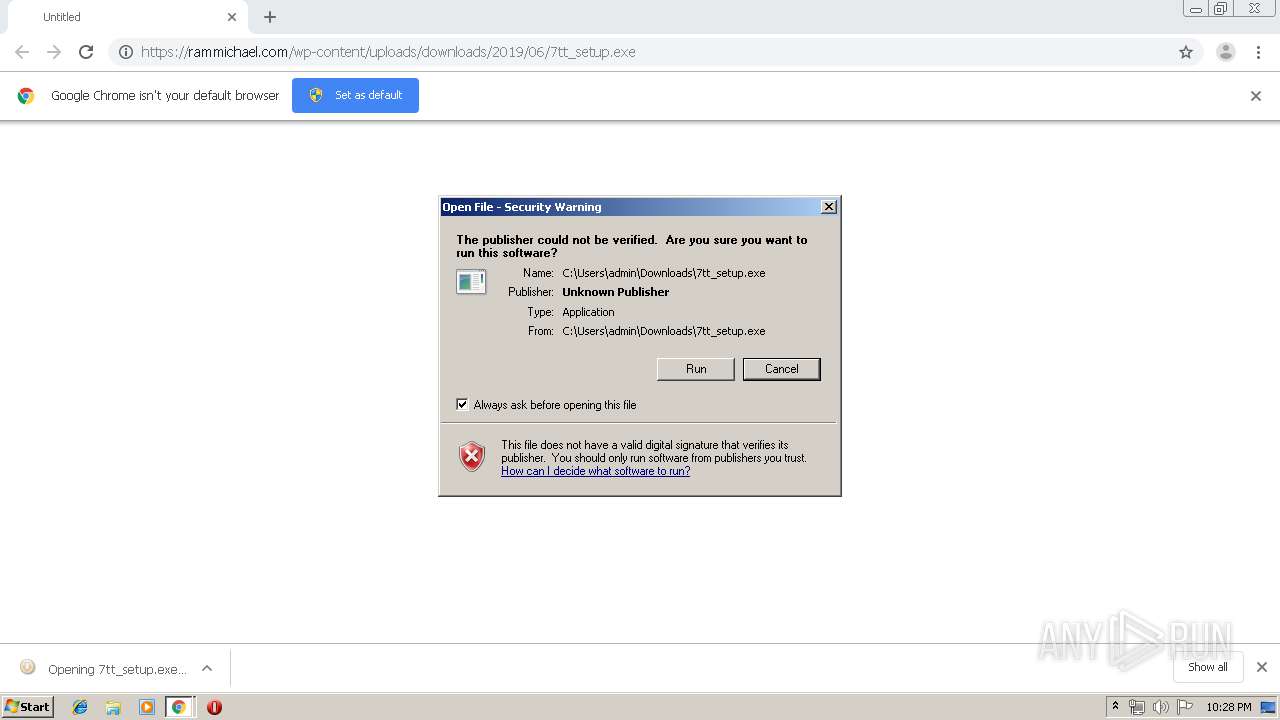
Manual execution by user
- 7+ Taskbar Tweaker.exe (PID: 2816)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
47
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 128 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1128 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,7542531819750187282,2747733045872467602,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10618810543064553895 --mojo-platform-channel-handle=1004 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1996 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,7542531819750187282,2747733045872467602,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5359700975823473596 --mojo-platform-channel-handle=1276 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2176 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://rammichael.com/wp-content/uploads/downloads/2019/06/7tt_setup.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=4056 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2232 | "C:\Users\admin\Downloads\7tt_setup.exe" | C:\Users\admin\Downloads\7tt_setup.exe | chrome.exe | ||||||||||||
User: admin Company: RaMMicHaeL Integrity Level: MEDIUM Description: 7+ Taskbar Tweaker Exit code: 0 Version: 5.7 Modules
| |||||||||||||||
| 2436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,7542531819750187282,2747733045872467602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=16890795938517776266 --mojo-platform-channel-handle=1496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2544 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=984,7542531819750187282,2747733045872467602,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=13107799399838191293 --mojo-platform-channel-handle=3728 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2672 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=984,7542531819750187282,2747733045872467602,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6726457389240254206 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2816 | "C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\7+ Taskbar Tweaker.exe" | C:\Users\admin\AppData\Roaming\7+ Taskbar Tweaker\7+ Taskbar Tweaker.exe | explorer.exe | ||||||||||||
User: admin Company: RaMMicHaeL Integrity Level: MEDIUM Description: 7+ Taskbar Tweaker Exit code: 0 Version: 5.7 Modules
| |||||||||||||||
Total events
2 224
Read events
2 082
Write events
138
Delete events
4
Modification events
| (PID) Process: | (2184) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2176-13210205294864000 |
Value: 259 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2176) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
12
Suspicious files
11
Text files
169
Unknown types
12
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\cdef9f9a-a636-4d5a-9ea7-64d72b57201c.tmp | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF36e8e2.TMP | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2176 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
14
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2816 | 7+ Taskbar Tweaker.exe | POST | 200 | 104.31.93.187:80 | http://rammichael.com/downloads/7tt_setup.exe?version&changelog=5.7 | US | text | 4 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2436 | chrome.exe | 104.31.92.187:443 | rammichael.com | Cloudflare Inc | US | shared |
2436 | chrome.exe | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2436 | chrome.exe | 172.217.23.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
— | — | 172.217.22.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2436 | chrome.exe | 172.217.16.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2436 | chrome.exe | 172.217.16.164:443 | www.google.com | Google Inc. | US | whitelisted |
2436 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2816 | 7+ Taskbar Tweaker.exe | 104.31.93.187:80 | rammichael.com | Cloudflare Inc | US | shared |
2436 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2436 | chrome.exe | 216.58.210.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
rammichael.com |
| malicious |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
clients1.google.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report