| File name: | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe |
| Full analysis: | https://app.any.run/tasks/3f242d4f-8b0f-4d32-a9f5-f94b45be0ad8 |
| Verdict: | Malicious activity |
| Analysis date: | September 25, 2020, 11:28:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 7E18E36380A6B21DFB309939A5A043C4 |
| SHA1: | 46D4DD2551E70AFFA252904A77335AF041F014D3 |
| SHA256: | 2B019468707A787E2EC498F993D336664F2391F35980CD50CD33F295FF80636C |
| SSDEEP: | 196608:5V/KJjWe4fQO+j++xpQii0BYG7LM5FKtNRmxWMY2:5YFGtGRiDyNkxXY2 |
MALICIOUS
Application was dropped or rewritten from another process
- EModelViewer.exe (PID: 3652)
Loads dropped or rewritten executable
- EModelViewer.exe (PID: 3652)
SUSPICIOUS
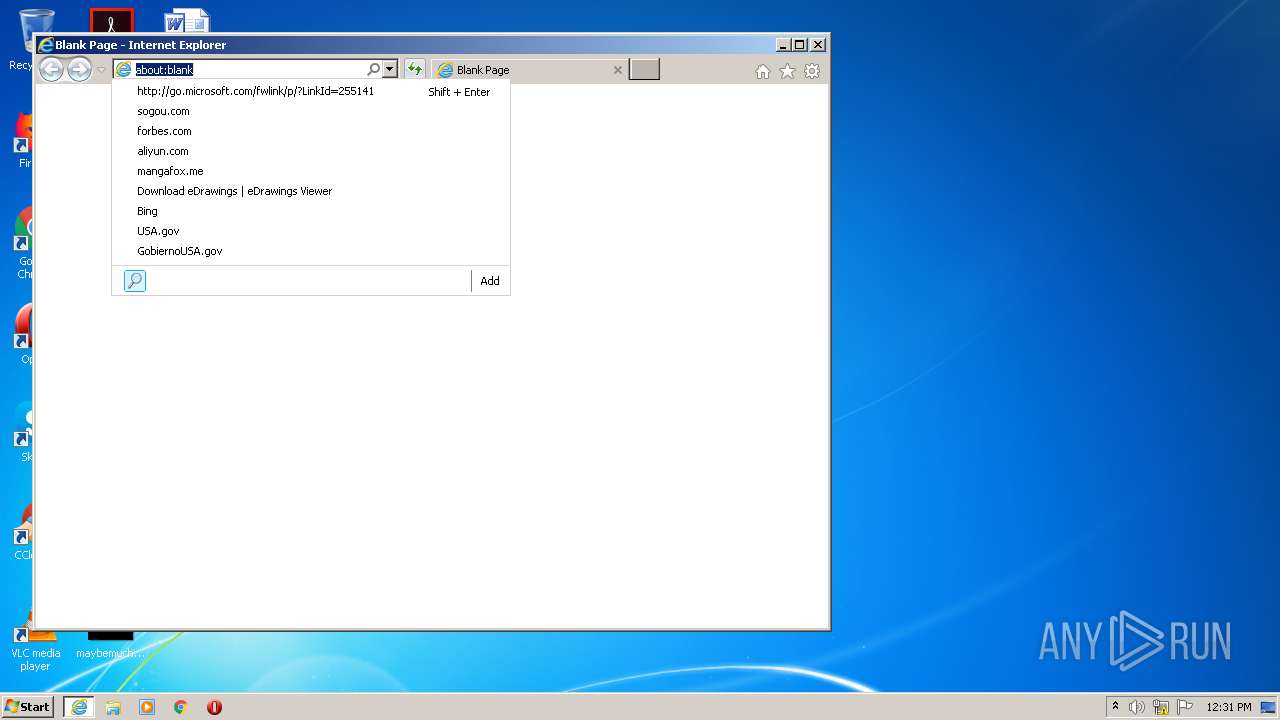
Reads internet explorer settings
- EModelViewer.exe (PID: 3652)
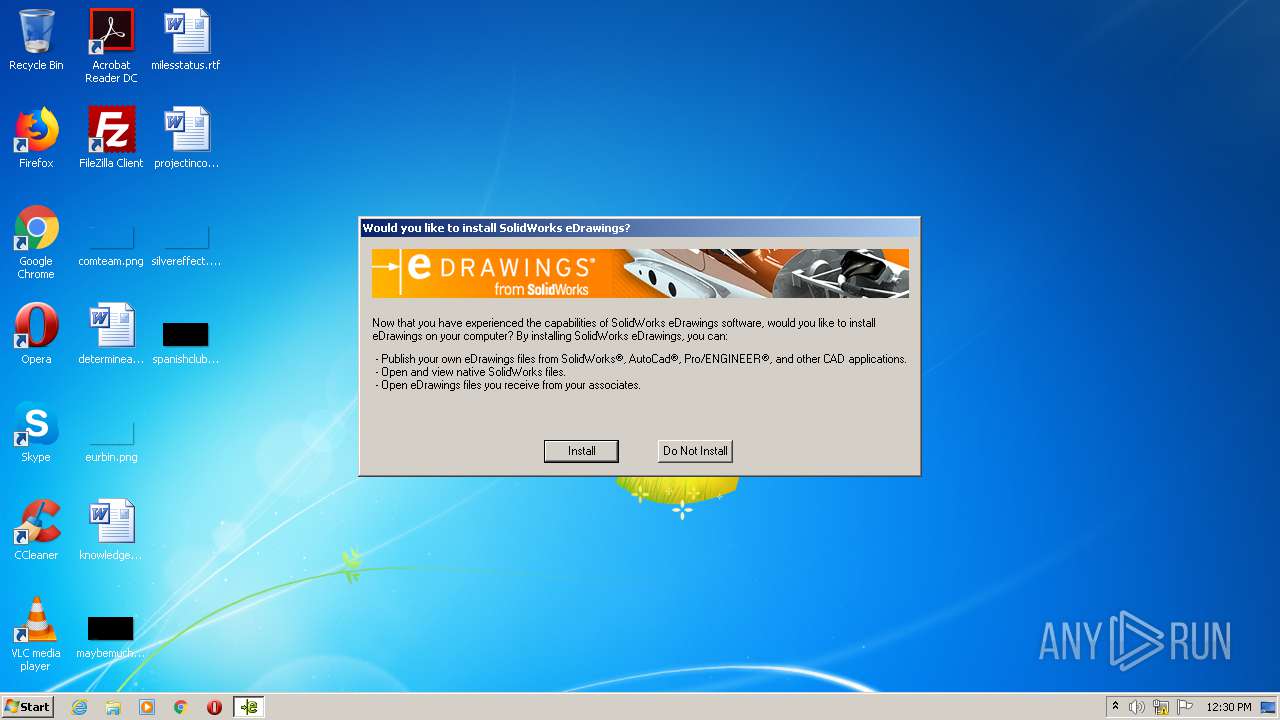
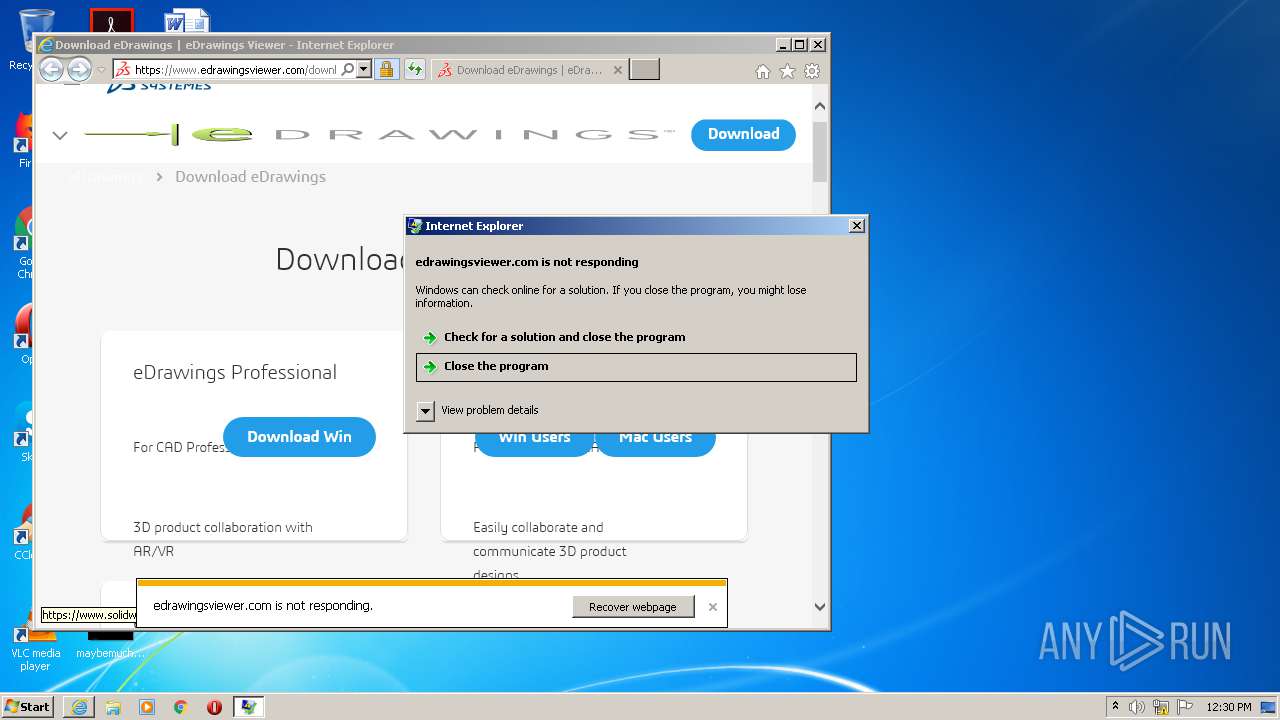
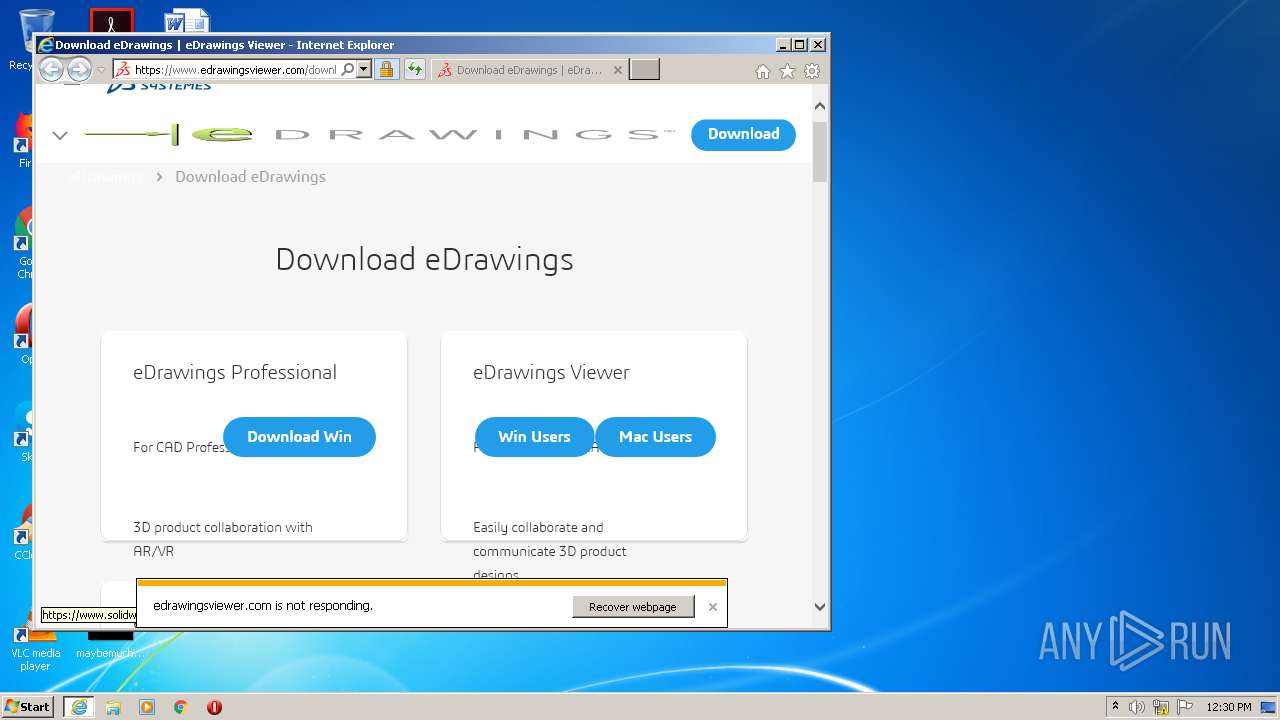
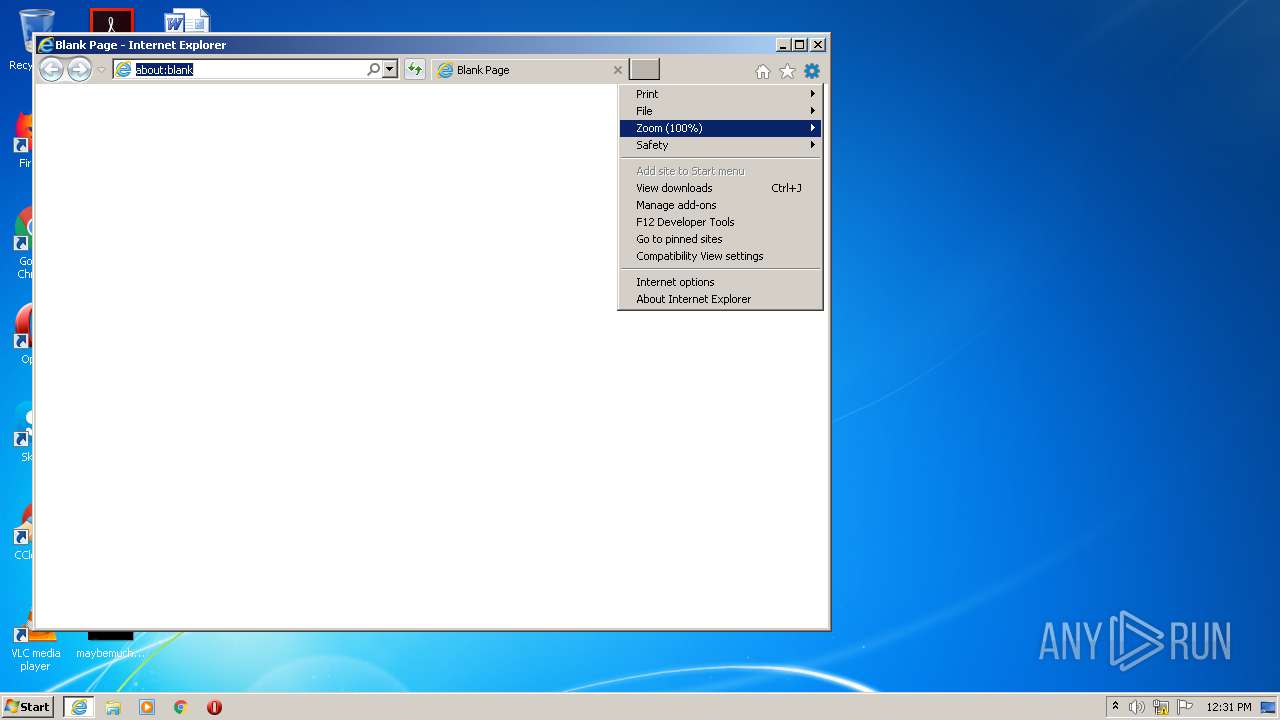
Starts Internet Explorer
- EModelViewer.exe (PID: 3652)
Executable content was dropped or overwritten
- 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe (PID: 1064)
Starts CMD.EXE for commands execution
- EModelViewer.exe (PID: 3652)
Reads Internet Cache Settings
- EModelViewer.exe (PID: 3652)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 532)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 2688)
Reads settings of System Certificates
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3032)
Reads Internet Cache Settings
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 556)
- iexplore.exe (PID: 532)
- iexplore.exe (PID: 3032)
Reads internet explorer settings
- iexplore.exe (PID: 3768)
- iexplore.exe (PID: 556)
- iexplore.exe (PID: 3032)
- iexplore.exe (PID: 2688)
Changes settings of System certificates
- iexplore.exe (PID: 3632)
Application launched itself
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 532)
Creates files in the user directory
- iexplore.exe (PID: 2688)
- iexplore.exe (PID: 3632)
- iexplore.exe (PID: 3032)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3632)
Manual execution by user
- iexplore.exe (PID: 532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2010:06:14 18:55:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 52224 |
| InitializedDataSize: | 44032 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x6884 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
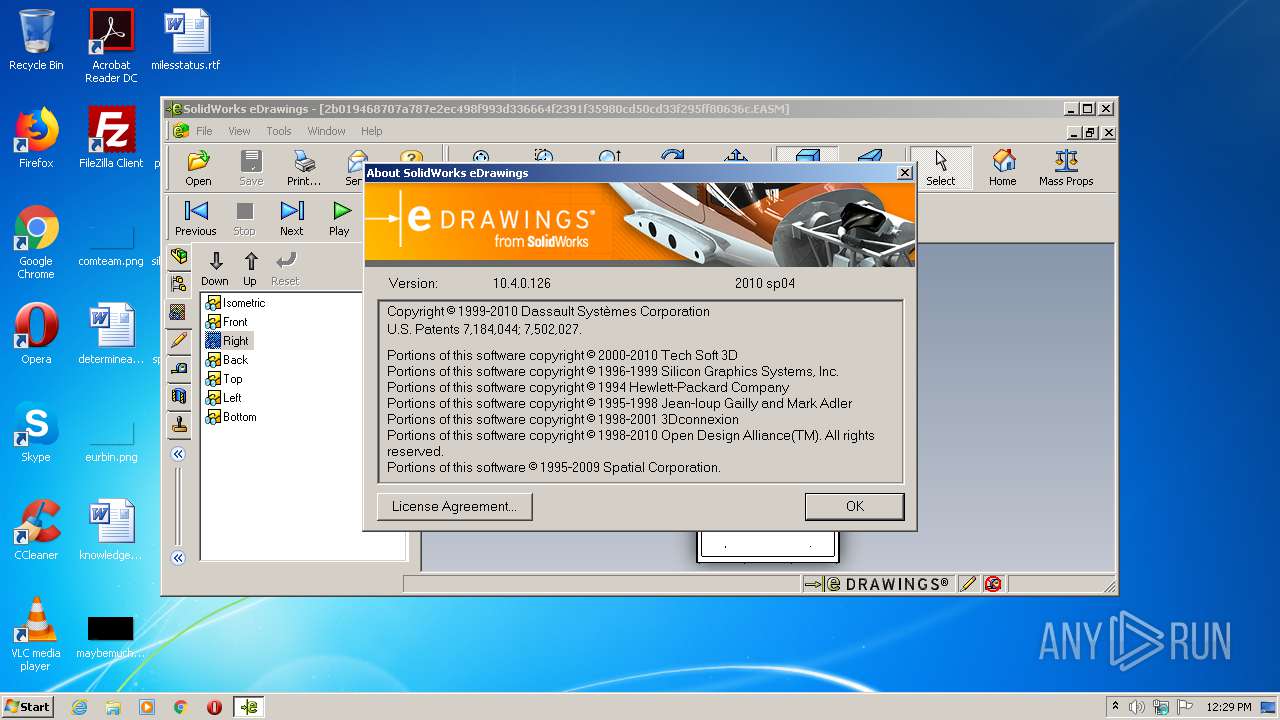
| FileVersionNumber: | 10.4.0.126 |
| ProductVersionNumber: | 10.4.0.126 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Dynamic link library |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Dassault Systèmes SolidWorks Corp. |
| FileDescription: | EModelSelfExtracter Module |
| FileVersion: | 10.4.0.126 |
| InternalName: | EModelSelfExtracter |
| LegalCopyright: | Copyright © 2008 Dassault Systèmes SolidWorks Corp. |
| OriginalFileName: | EModelSelfExtracter.DLL |
| ProductName: | eDrawings 2009 |
| ProductVersion: | 10.4.0.126 |
| OLESelfRegister: | - |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2010 16:55:12 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | Dassault Systèmes SolidWorks Corp. |
| FileDescription: | EModelSelfExtracter Module |
| FileVersion: | 10.4.0.126 |
| InternalName: | EModelSelfExtracter |
| LegalCopyright: | Copyright © 2008 Dassault Systèmes SolidWorks Corp. |
| OriginalFilename: | EModelSelfExtracter.DLL |
| ProductName: | eDrawings 2009 |
| ProductVersion: | 10.4.0.126 |
| OLESelfRegister: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 14-Jun-2010 16:55:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000CAB4 | 0x0000CC00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.63649 |
.rdata | 0x0000E000 | 0x0000363A | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.18968 |
.data | 0x00012000 | 0x00002C00 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.69091 |
.rsrc | 0x00015000 | 0x00005394 | 0x00005400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 3.51582 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.65542 | 86 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.44994 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 3.84247 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 4.05106 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 2.76104 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 2.49175 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 2.38788 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
101 | 2.7862 | 104 | Latin 1 / Western European | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
USER32.dll |
ole32.dll |
Total processes
50
Monitored processes
9
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 556 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3632 CREDAT:2430217 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1064 | "C:\Users\admin\AppData\Local\Temp\2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe" | C:\Users\admin\AppData\Local\Temp\2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | explorer.exe | ||||||||||||
User: admin Company: Dassault Systèmes SolidWorks Corp. Integrity Level: MEDIUM Description: EModelSelfExtracter Module Exit code: 0 Version: 10.4.0.126 Modules
| |||||||||||||||
| 2464 | cmd /c C:\Users\admin\AppData\Local\Temp\DelEMOViewer.bat | C:\Windows\system32\cmd.exe | — | EModelViewer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2688 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3632 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 3489660927 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3032 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:532 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
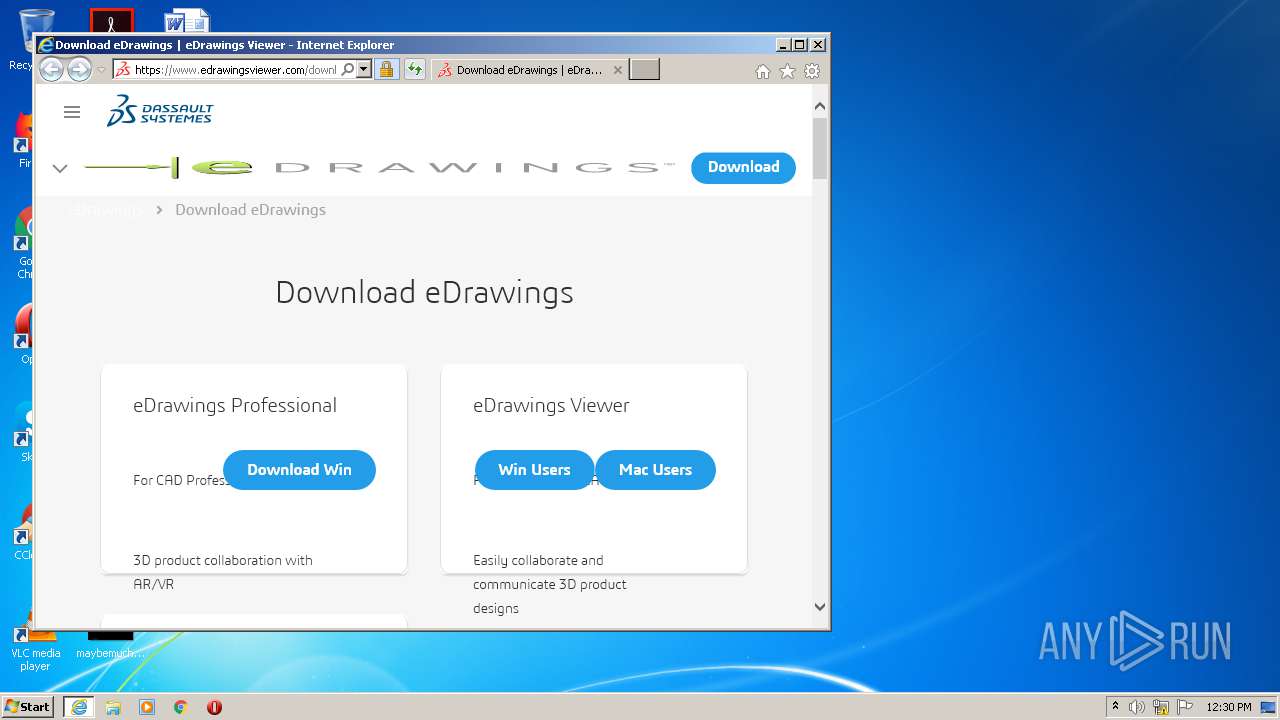
| 3632 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.eDrawingsViewer.com/download | C:\Program Files\Internet Explorer\iexplore.exe | EModelViewer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
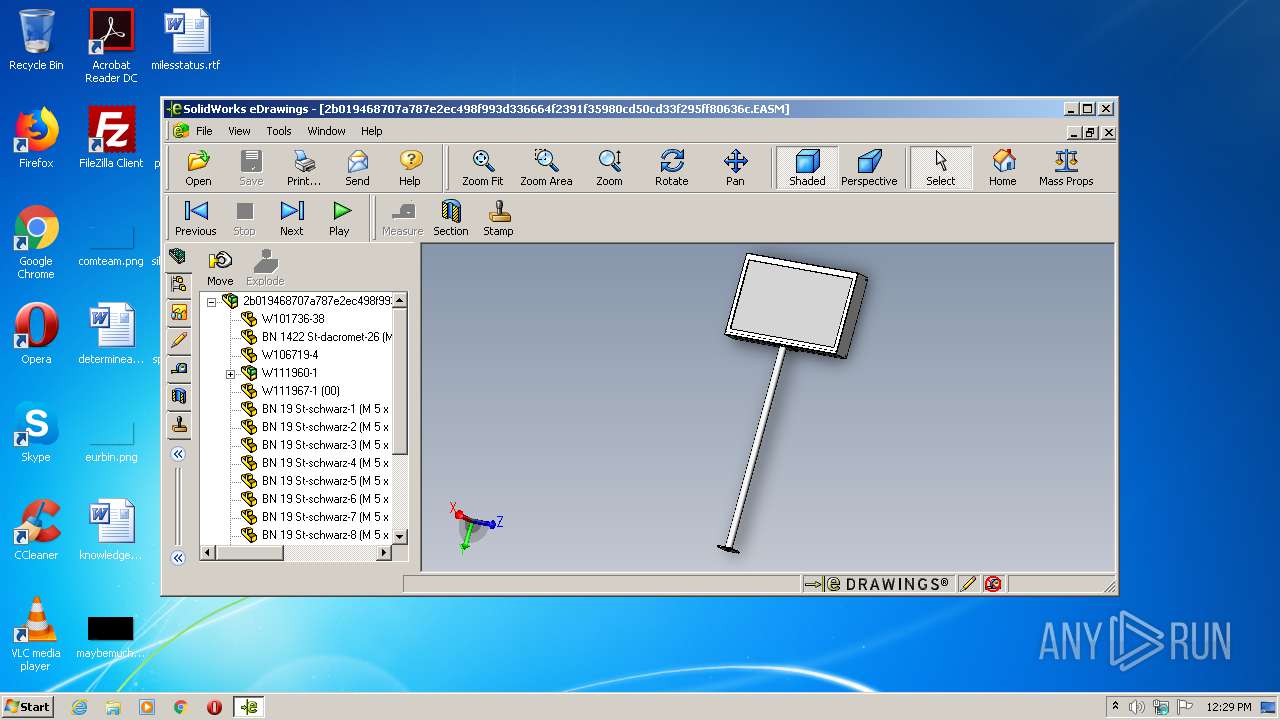
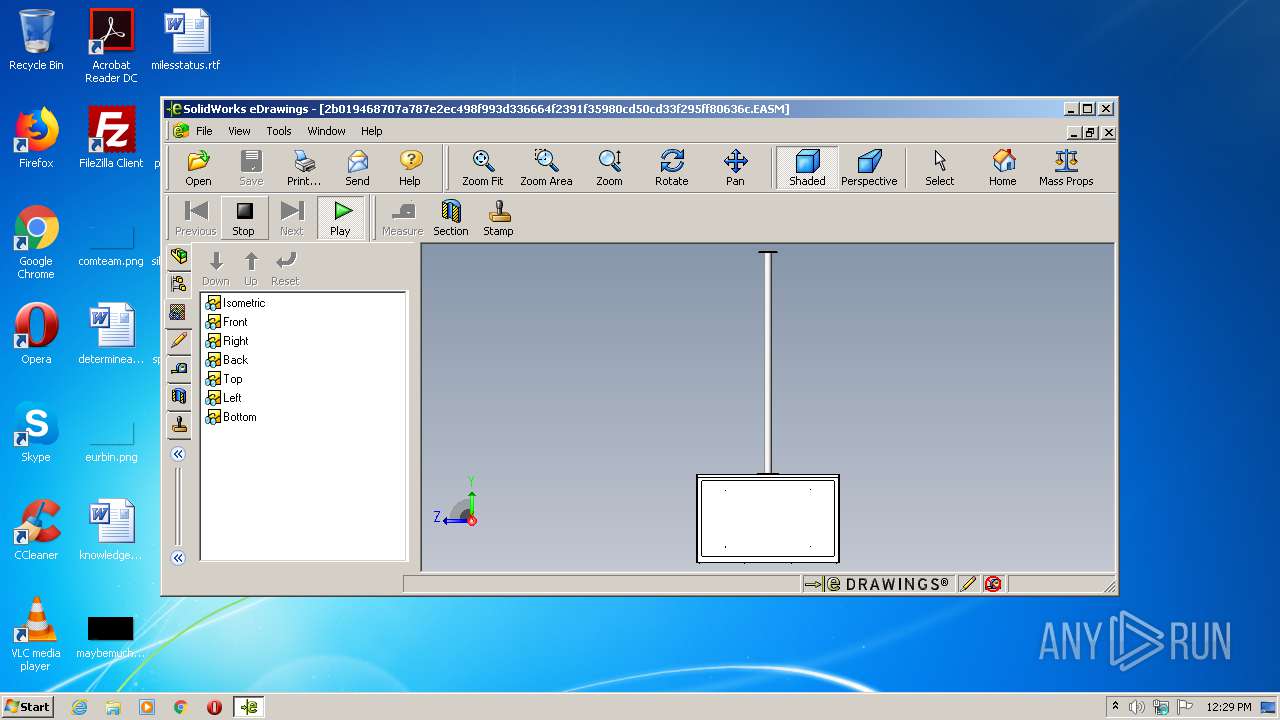
| 3652 | C:\Users\admin\AppData\Local\Temp\EMOD954\EModelViewer.exe C:\Users\admin\AppData\Local\Temp\EMOD954\W111959.EASM -SelfExtracted C:\Users\admin\AppData\Local\Temp\2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\EModelViewer.exe | — | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | |||||||||||
User: admin Company: Dassault Systèmes SolidWorks Corp. Integrity Level: MEDIUM Description: EModelViewer Module Exit code: 1 Version: 10.4.0.126 Modules
| |||||||||||||||
| 3768 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3632 CREDAT:4003080 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 723
Read events
1 425
Write events
289
Delete events
9
Modification events
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
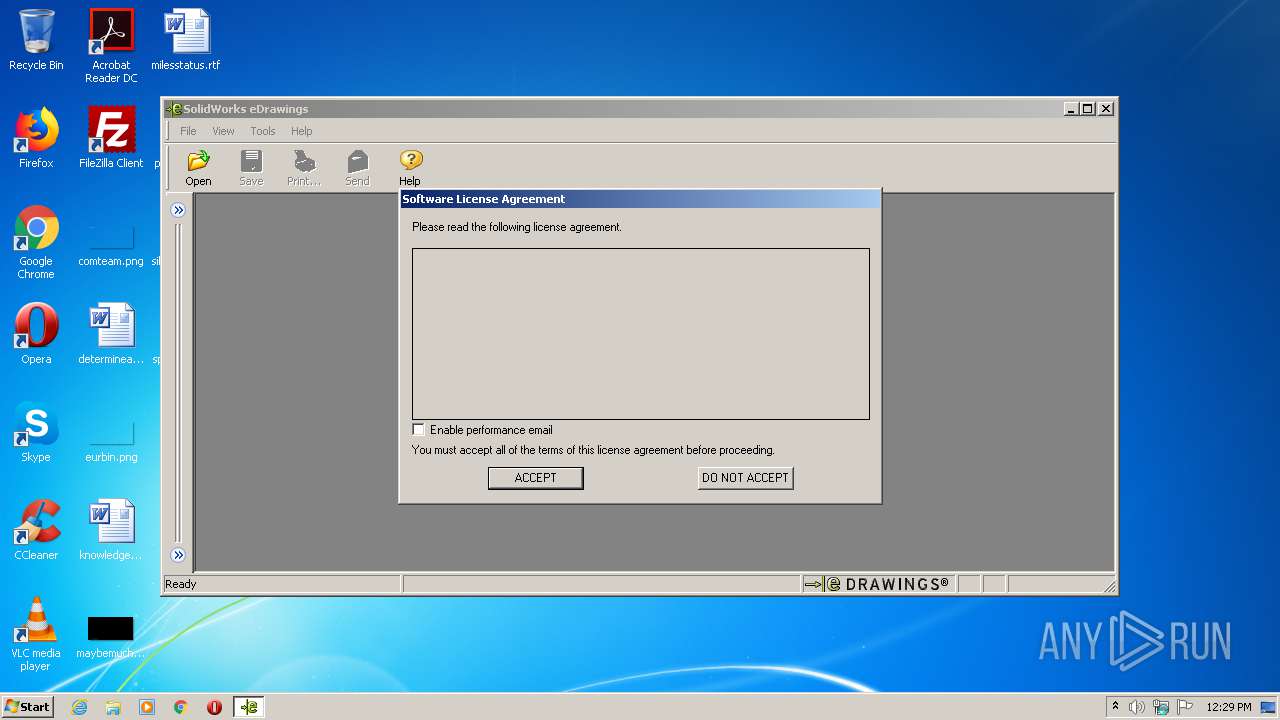
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\eDrawings\Performance Logging |
| Operation: | write | Name: | Email Enabled |
Value: 0 | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\eDrawings\e2010\General |
| Operation: | write | Name: | ShowLicense |
Value: 0 | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\eDrawings\e2010\Recent Document List |
| Operation: | write | Name: | DocumentCount |
Value: 15 | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\eDrawings\e2010\Recent Document List |
| Operation: | write | Name: | Document1 |
Value: C:\Users\admin\AppData\Local\Temp\EMOD954\W111959.EASM | |||
| (PID) Process: | (3652) EModelViewer.exe | Key: | HKEY_CURRENT_USER\Software\eDrawings\e2010\General |
| Operation: | write | Name: | Main Rect |
Value: 0160 0096 1120 0597 | |||
Executable files
19
Suspicious files
73
Text files
57
Unknown types
61
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\W111959.EASM | easm | |
MD5:— | SHA256:— | |||
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\EModelUtils.dll | executable | |
MD5:E66045196122E607EFF28E5492516606 | SHA256:E57121352B066102931F736CD57E70B5394AC9E202249652C1BF689EFC1B104E | |||
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\Microsoft.VC80.CRT\Microsoft.VC80.CRT.manifest | xml | |
MD5:541423A06EFDCD4E4554C719061F82CF | SHA256:17AD1A64BA1C382ABF89341B40950F9B31F95015C6B0D3E25925BFEBC1B53EB5 | |||
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\EModelViewer.exe | executable | |
MD5:D07A570123469CECA4A4704D01AC86FD | SHA256:FCFF2A7A1C32C1162D140CE3374889BE79048D58ADCCE8CEE37C0ABAFCA42750 | |||
| 3652 | EModelViewer.exe | C:\Users\admin\AppData\Local\Temp\xmlEFE9.tmp.xml | — | |
MD5:— | SHA256:— | |||
| 3652 | EModelViewer.exe | C:\Users\admin\AppData\Local\Temp\xmlF00A.tmp.xml | — | |
MD5:— | SHA256:— | |||
| 3652 | EModelViewer.exe | C:\Users\admin\AppData\Local\Temp\jpgF00B.tmp.jpg | — | |
MD5:— | SHA256:— | |||
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\EModelEx | executable | |
MD5:DD60A7D9B4CE935D9745CFBBDF753FFE | SHA256:E7C1876020870FA886201E696D82F810A8786056E969AA41C469B0EF19C587CE | |||
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\lang\english\EModelUtilsVistaRes.dll | executable | |
MD5:4531FA105A3D24C136FBAAE508E9DE0B | SHA256:1E9367CDEFD80873F785C19EA657093766FA7EAB365EB5A585E0ECD783ABFF97 | |||
| 1064 | 2b019468707a787e2ec498f993d336664f2391f35980cd50cd33f295ff80636c.exe | C:\Users\admin\AppData\Local\Temp\EMOD954\EModelUtilsVista.dll | executable | |
MD5:B66E874923A451510106FBDDB72007ED | SHA256:B08CDC0B5A21984FA7E5445869E2409A3D33D3E18BFB4A7EA07D4D37A313984A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
35
TCP/UDP connections
85
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2688 | iexplore.exe | GET | 301 | 23.37.38.216:80 | http://www.edrawingsviewer.com/download | NL | — | — | unknown |
2688 | iexplore.exe | GET | 200 | 99.86.116.25:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2688 | iexplore.exe | GET | 200 | 99.86.116.217:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2688 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRDC9IOTxN6GmyRjyTl2n4yTUczyAQUjYxexFStiuF36Zv5mwXhuAGNYeECEFTg02Ax1quPKOTX3Pe6T3s%3D | US | der | 471 b | whitelisted |
2688 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
2688 | iexplore.exe | GET | 200 | 99.86.116.217:80 | http://o.ss2.us//MEowSDBGMEQwQjAJBgUrDgMCGgUABBSLwZ6EW5gdYc9UaSEaaLjjETNtkAQUv1%2B30c7dH4b0W1Ws3NcQwg6piOcCCQCnDkpMNIK3fw%3D%3D | US | der | 1.70 Kb | whitelisted |
2688 | iexplore.exe | GET | 200 | 99.86.116.25:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2688 | iexplore.exe | GET | 200 | 99.86.116.95:80 | http://ocsp.rootca1.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBRPWaOUU8%2B5VZ5%2Fa9jFTaU9pkK3FAQUhBjMhTTsvAyUlC4IWZzHshBOCggCEwZ%2FlFeFh%2Bisd96yUzJbvJmLVg0%3D | US | der | 1.39 Kb | shared |
2688 | iexplore.exe | GET | 200 | 99.86.116.25:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
2688 | iexplore.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | der | 727 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2688 | iexplore.exe | 23.37.38.216:80 | www.edrawingsviewer.com | Akamai Technologies, Inc. | NL | unknown |
2688 | iexplore.exe | 2.17.190.243:443 | www.3ds.com | Akamai Technologies, Inc. | — | unknown |
3632 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2688 | iexplore.exe | 91.103.43.149:443 | chatbot.dsxclient.3ds.com | Dassault Systemes Se | FR | unknown |
2688 | iexplore.exe | 2.17.176.16:443 | www.solidworks.com | Akamai Technologies, Inc. | — | unknown |
2688 | iexplore.exe | 91.199.212.52:80 | crt.sectigo.com | Comodo CA Ltd | GB | suspicious |
2688 | iexplore.exe | 99.86.116.217:80 | o.ss2.us | AT&T Services, Inc. | US | unknown |
2688 | iexplore.exe | 99.86.111.129:443 | ui.3ds.com | AT&T Services, Inc. | US | unknown |
2688 | iexplore.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
2688 | iexplore.exe | 99.86.116.95:80 | ocsp.rootg2.amazontrust.com | AT&T Services, Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.edrawingsviewer.com |
| unknown |
ocsp.digicert.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.3ds.com |
| unknown |
tracking.3ds.com |
| whitelisted |
chatbot.dsxclient.3ds.com |
| suspicious |
www.solidworks.com |
| whitelisted |
ui.3ds.com |
| whitelisted |
crt.sectigo.com |
| whitelisted |