analyze malware
- Huge database of samples and IOCs
- Custom VM setup
- Unlimited submissions
- Interactive approach
| File name: | c720a8d271b1e0a35fcd9898c14ed4e8.7z |
| Full analysis: | https://app.any.run/tasks/17c88243-0681-4817-8b2a-041adecb3bb1 |
| Verdict: | Malicious activity |
| Threats: | Agent Tesla is spyware that collects information about the actions of its victims by recording keystrokes and user interactions. It is falsely marketed as a legitimate software on the dedicated website where this malware is sold. |
| Analysis date: | October 14, 2019, 13:52:06 |
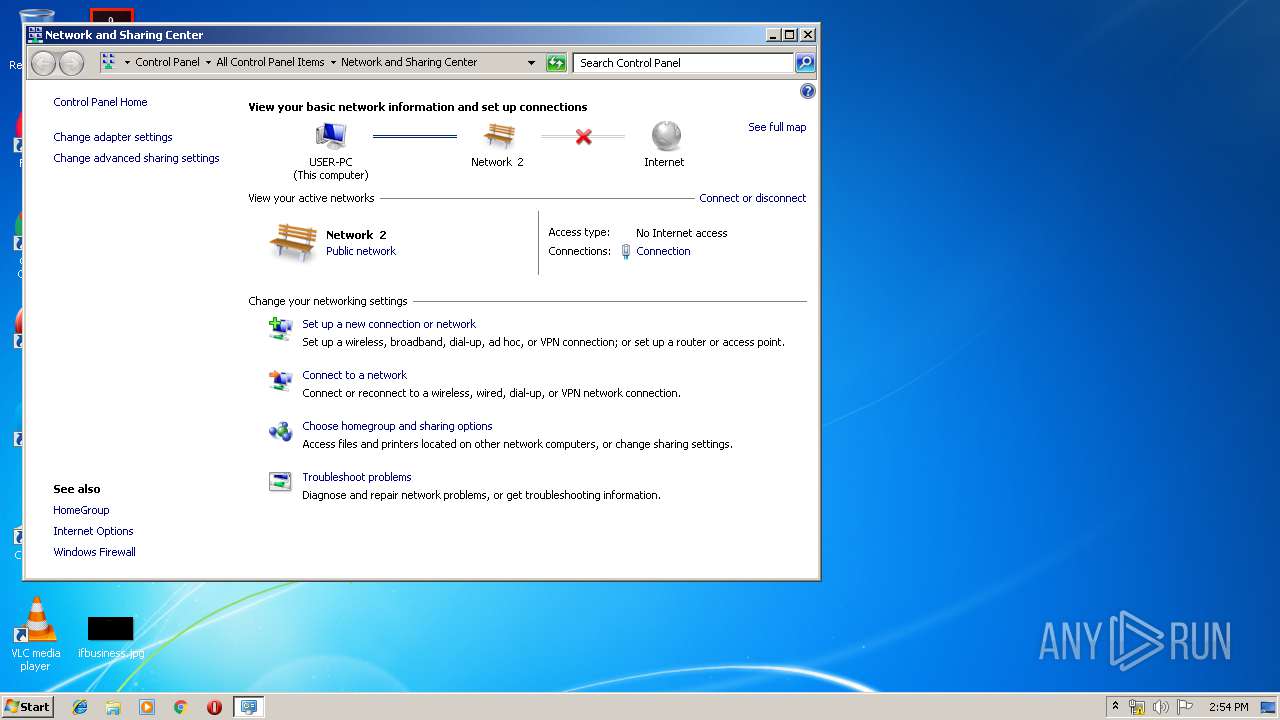
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 5EDCC648AAECD7B5133E50A271571A95 |
| SHA1: | CF43DAA4C9CCB03504A5A20185280C7BFF43A90E |
| SHA256: | 2AF9227C82DC4776EBF8B073CB0D932F749C9A5079993B335E343C7277F999AD |
| SSDEEP: | 12288:Oxp0Qz7T844J6iPPKdamuk1bybxq6QjWWa:Ox7TQ6jzF1X+ |
MALICIOUS
Application was dropped or rewritten from another process
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 3428)
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 2580)
Actions looks like stealing of personal data
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 2580)
AGENTTESLA was detected
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 2580)
SUSPICIOUS
Reads Windows Product ID
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 2580)
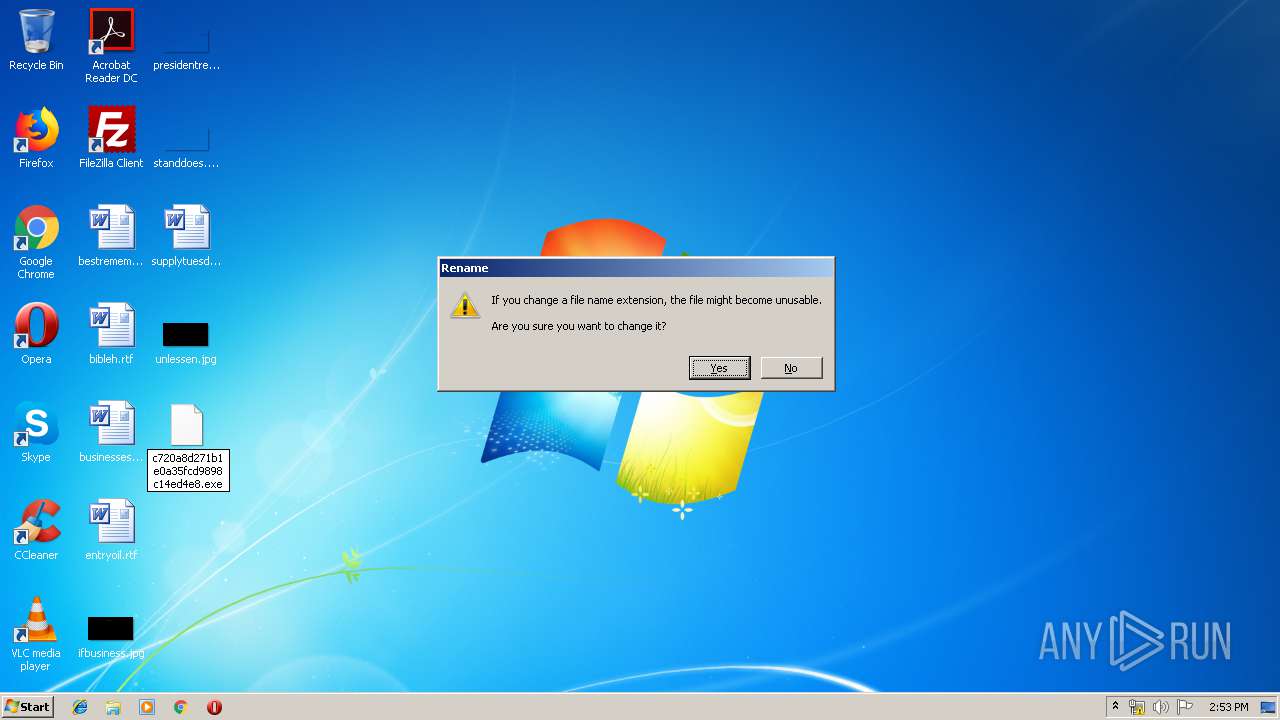
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2564)
Reads Environment values
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 2580)
Application launched itself
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 3428)
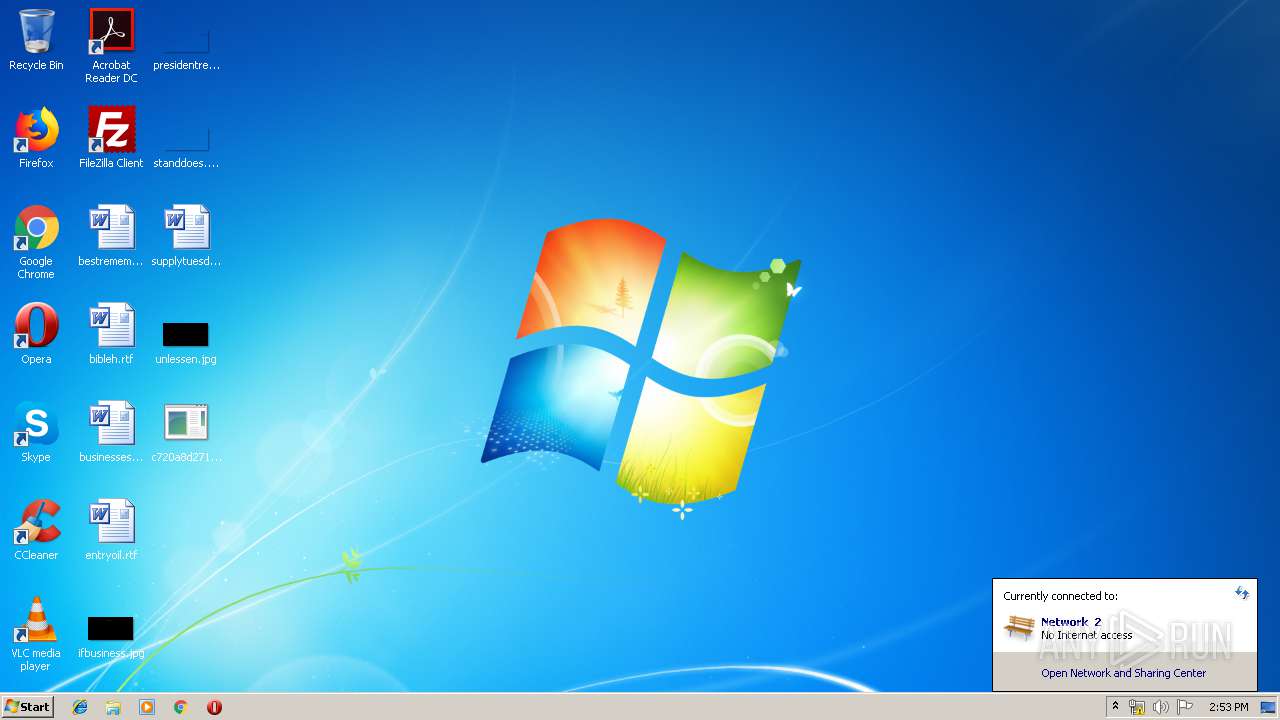
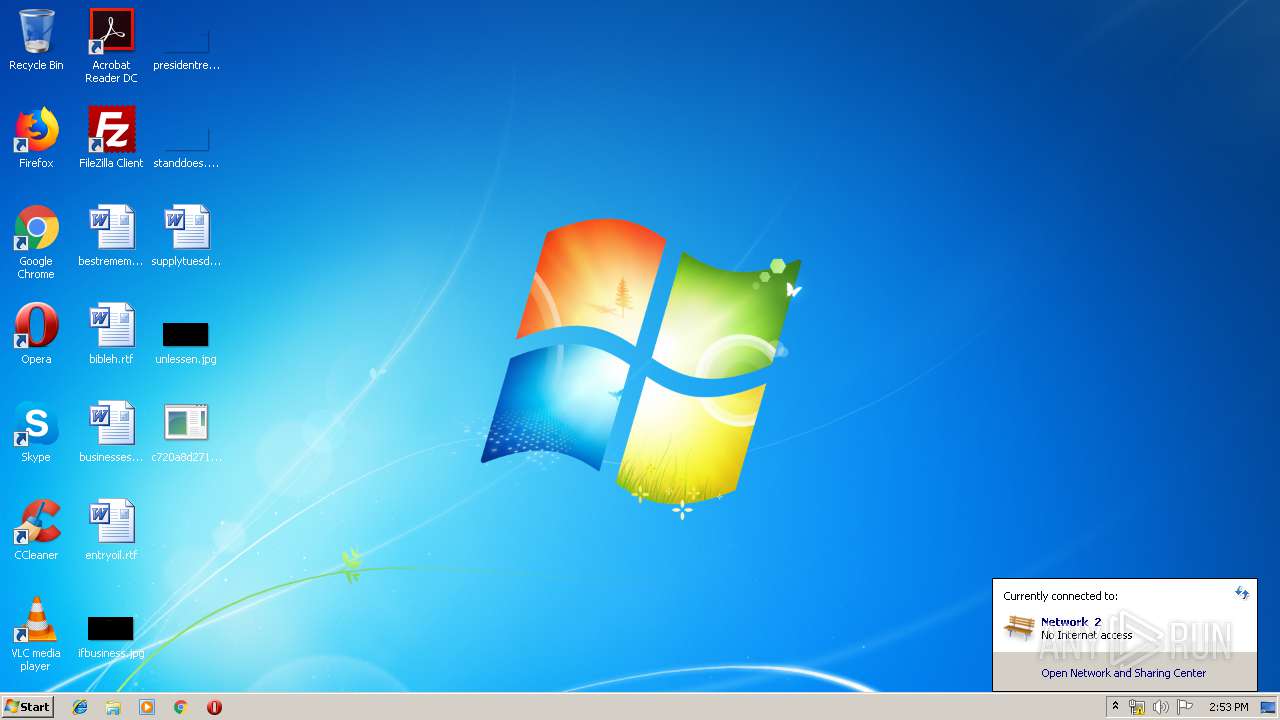
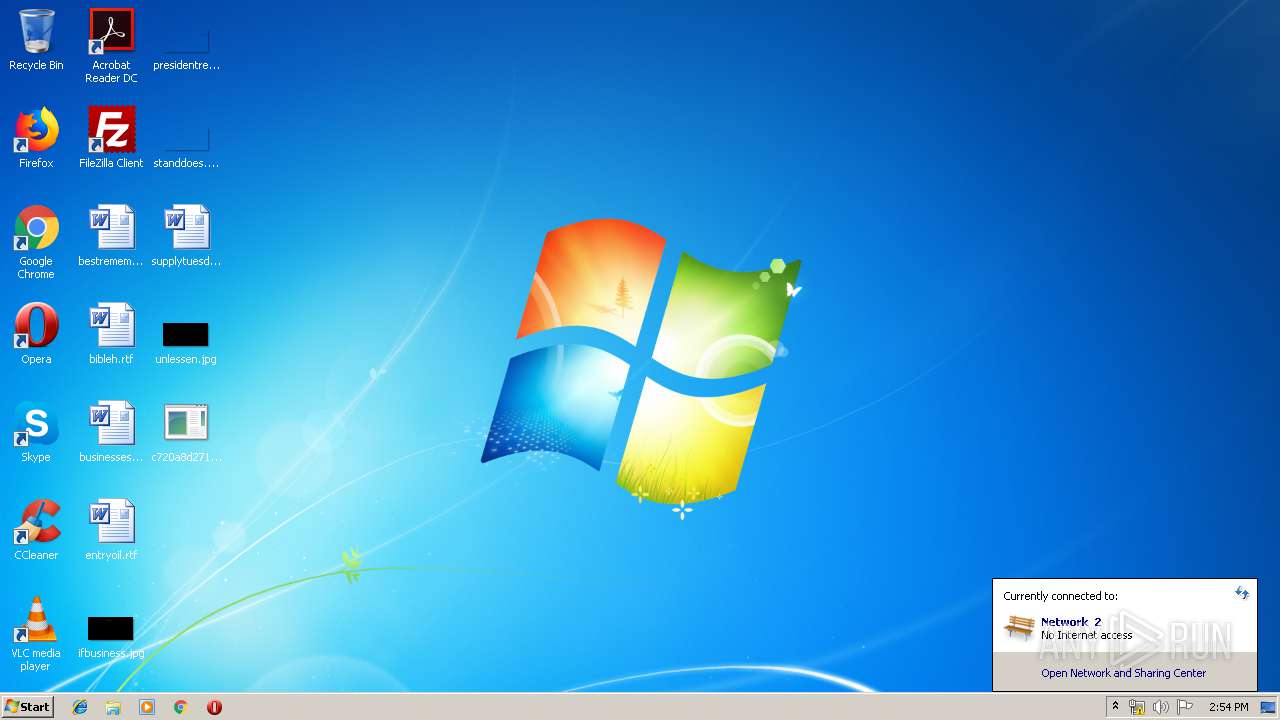
Checks for external IP
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 2580)
INFO
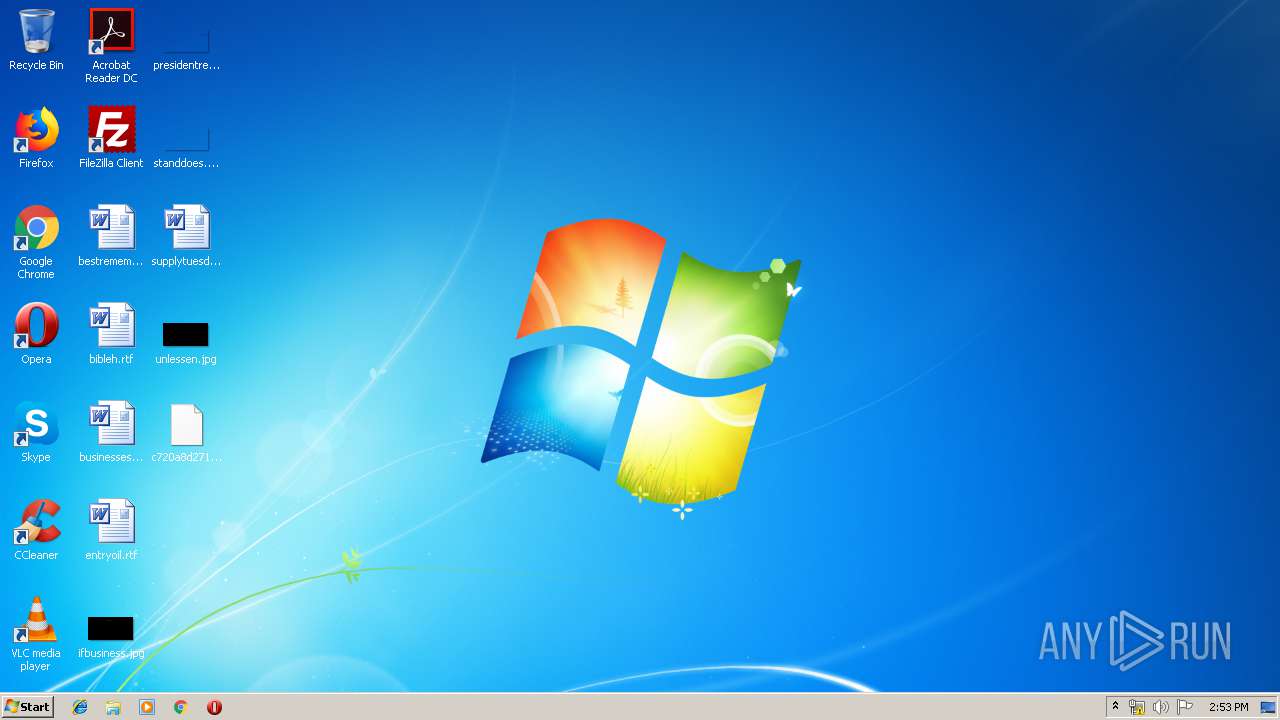
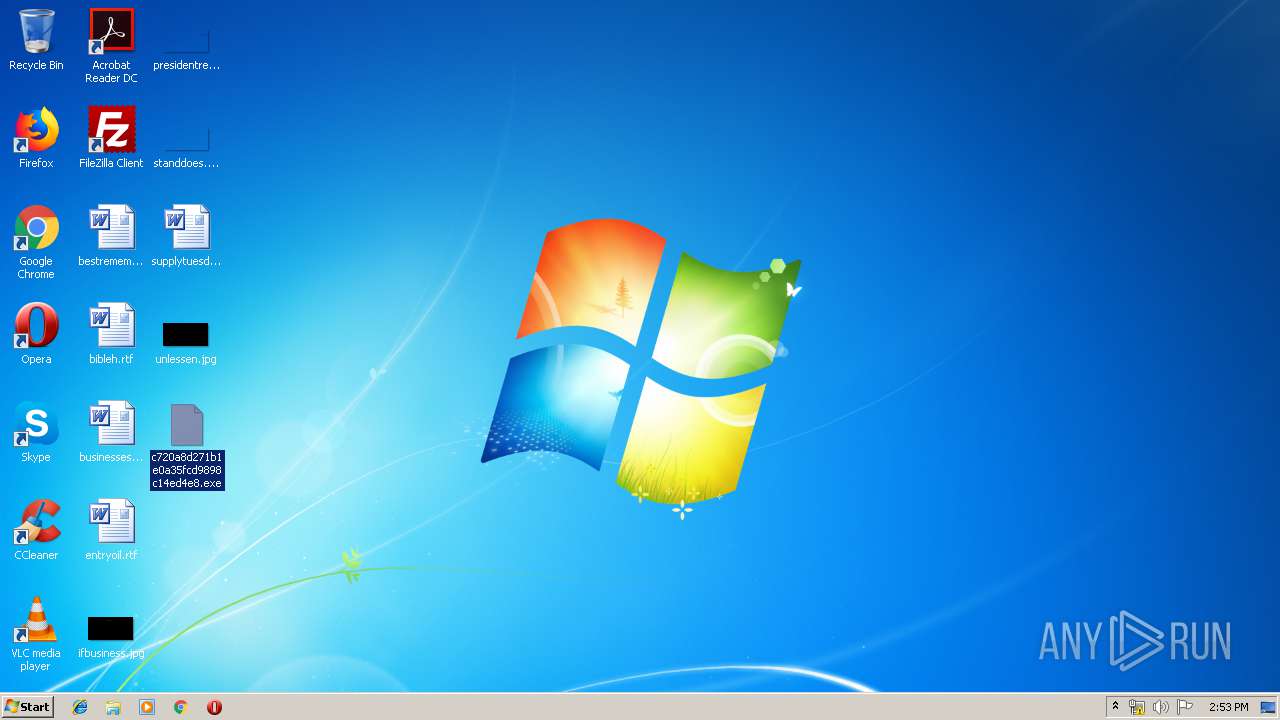
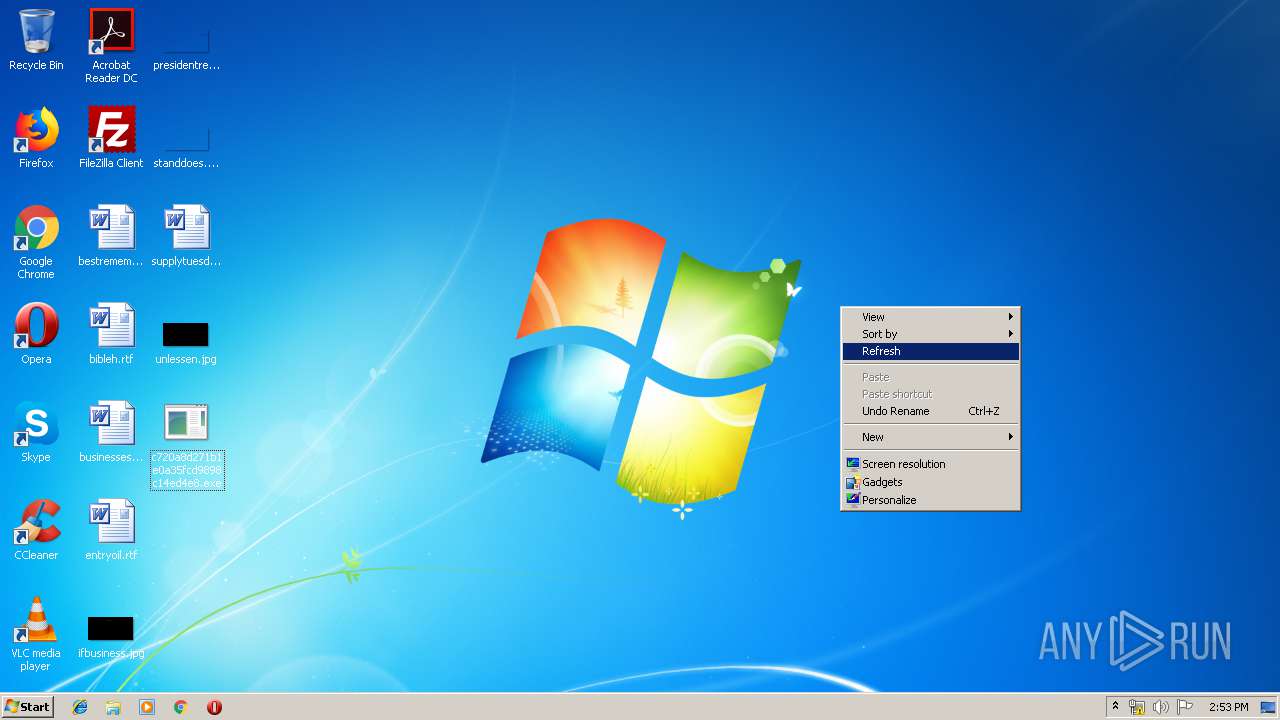
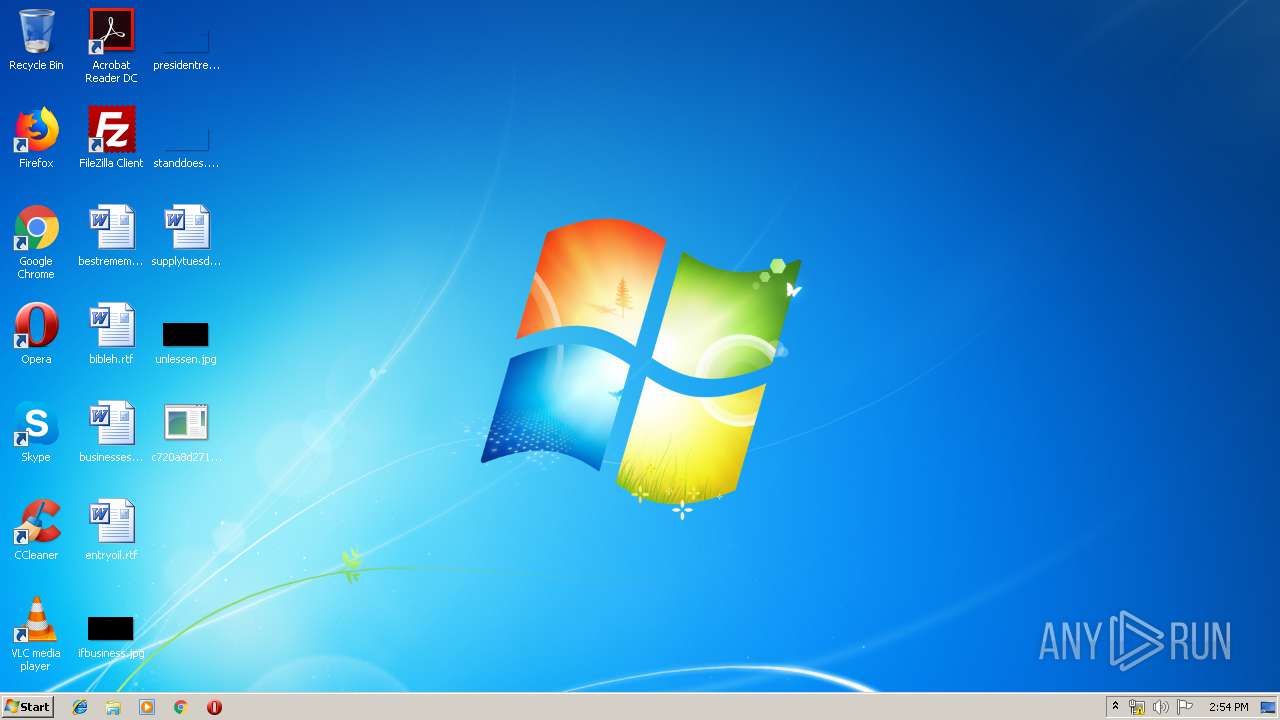
Manual execution by user
- c720a8d271b1e0a35fcd9898c14ed4e8.exe (PID: 3428)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
39
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
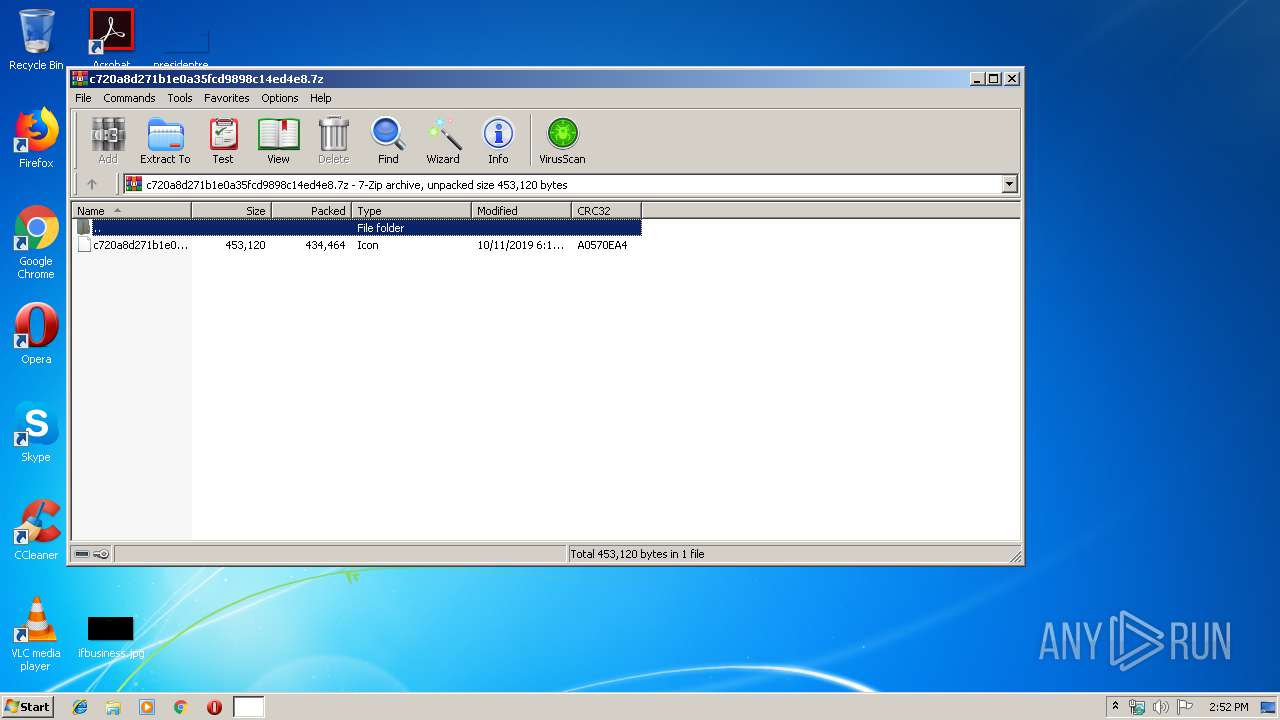
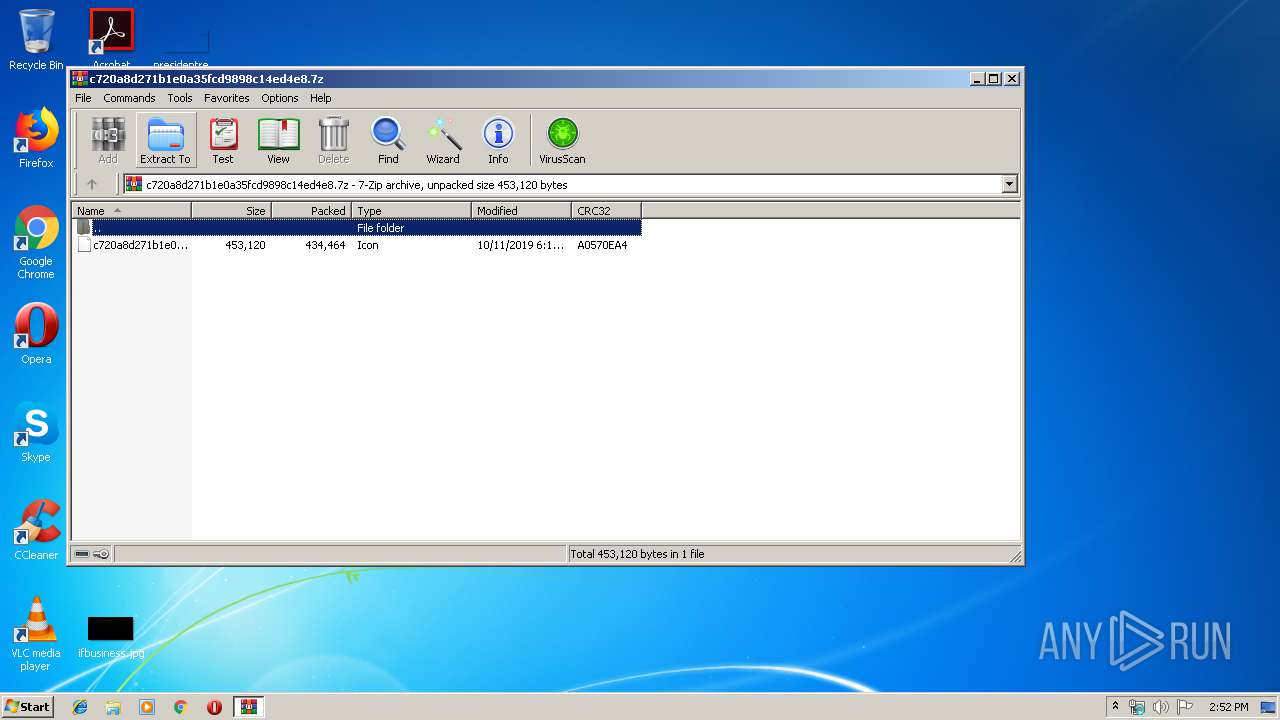
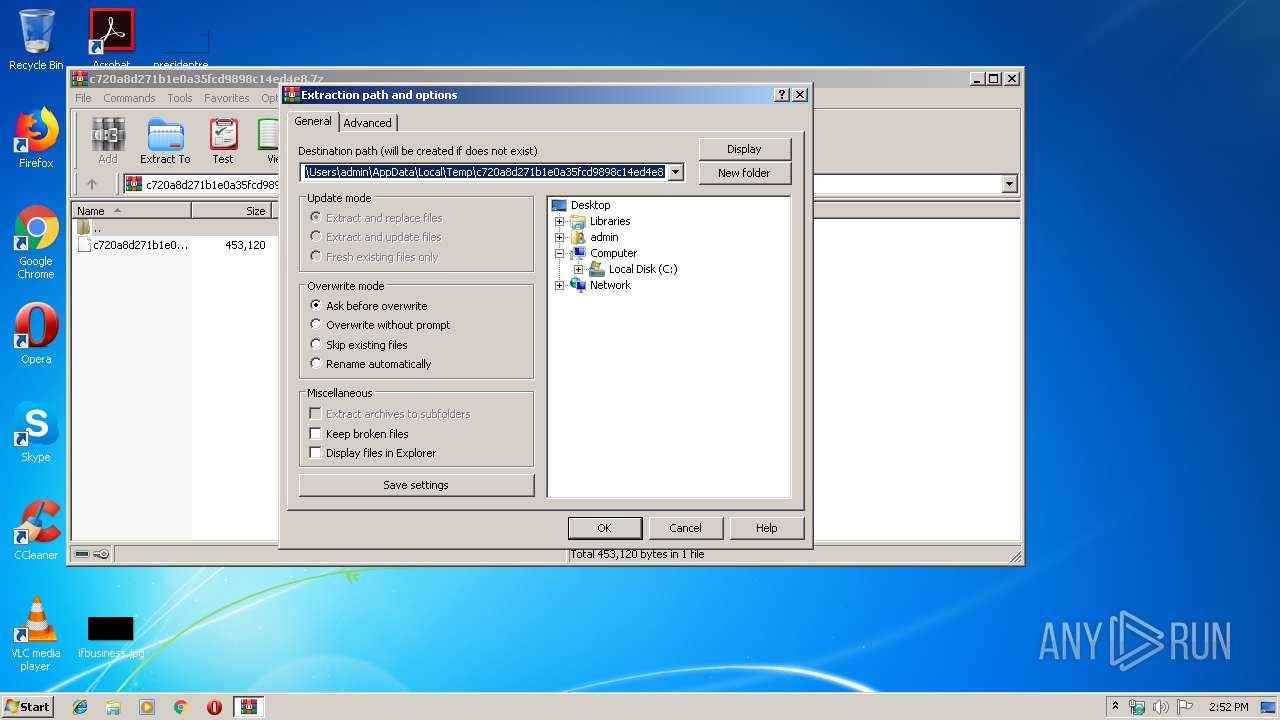
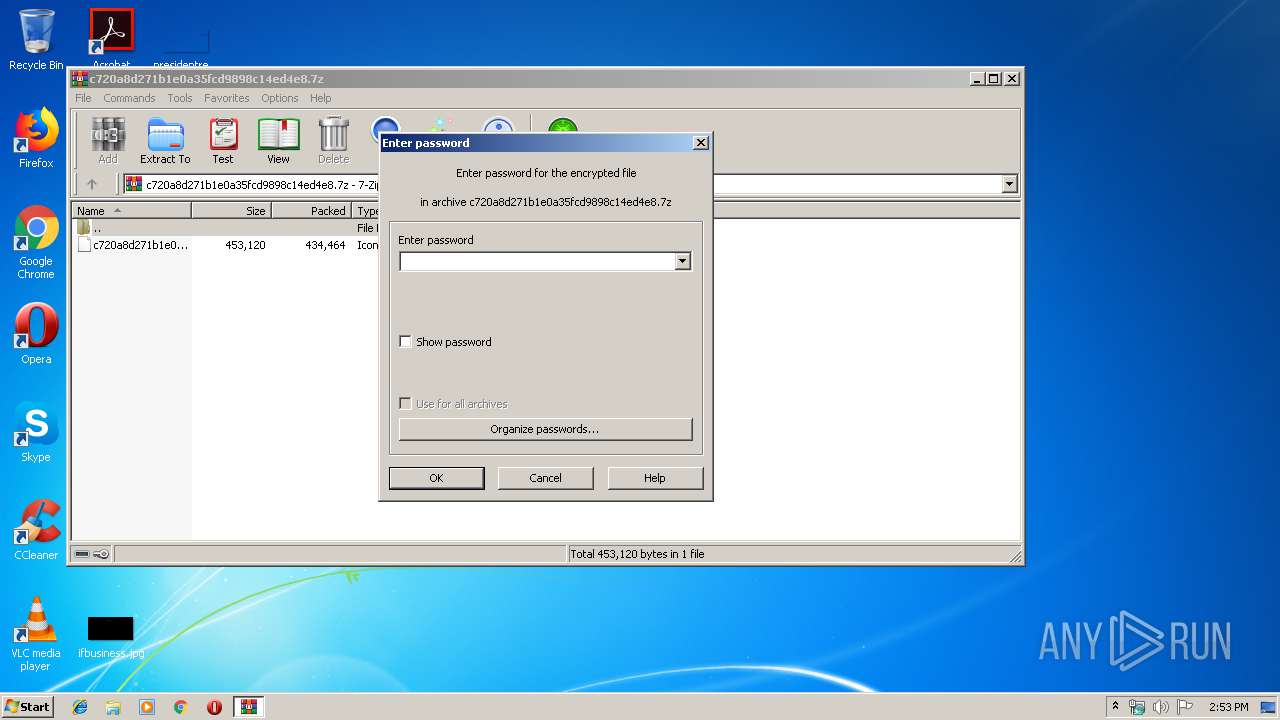
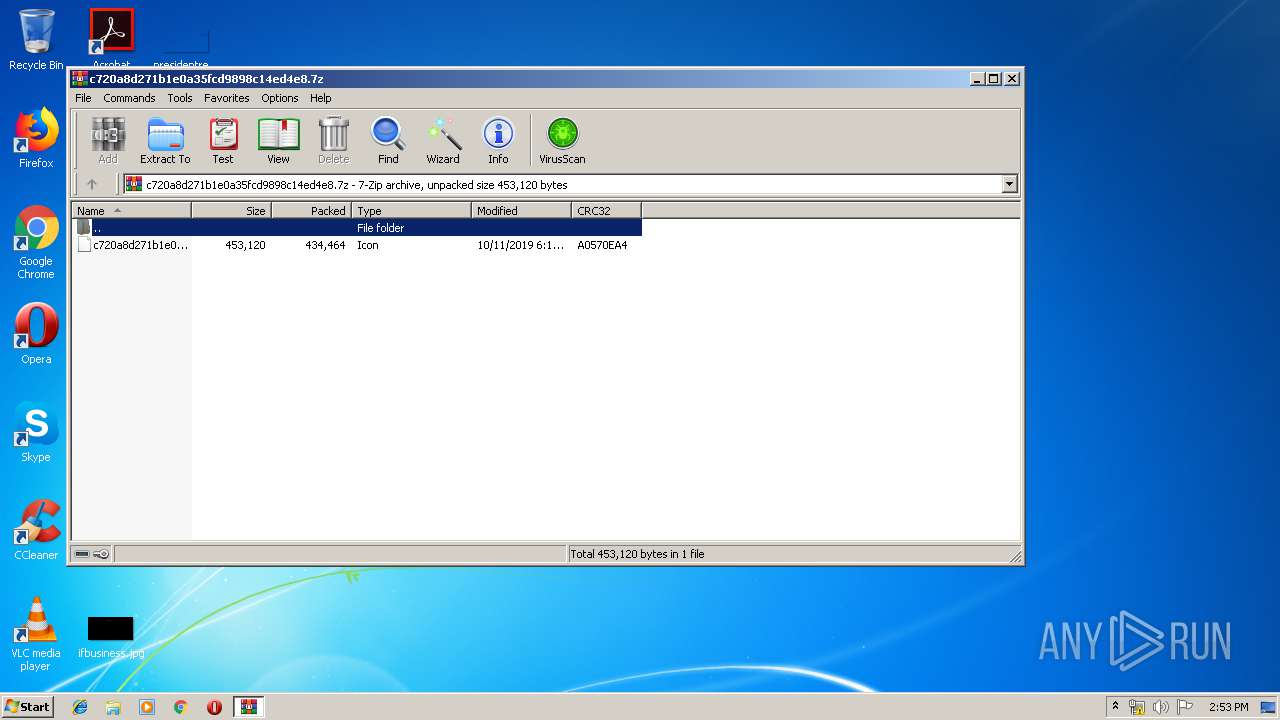
| 2564 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\c720a8d271b1e0a35fcd9898c14ed4e8.7z" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | |
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 | ||||
| 3428 | "C:\Users\admin\Desktop\c720a8d271b1e0a35fcd9898c14ed4e8.exe" | C:\Users\admin\Desktop\c720a8d271b1e0a35fcd9898c14ed4e8.exe | — | explorer.exe |
User: admin Integrity Level: MEDIUM Description: FractionCalculator Exit code: 0 Version: 1.8.8.8 | ||||
| 2580 | "C:\Users\admin\Desktop\c720a8d271b1e0a35fcd9898c14ed4e8.exe" | C:\Users\admin\Desktop\c720a8d271b1e0a35fcd9898c14ed4e8.exe | c720a8d271b1e0a35fcd9898c14ed4e8.exe | |
User: admin Integrity Level: MEDIUM Description: FractionCalculator Version: 1.8.8.8 | ||||
Total events
519
Read events
485
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2580 | c720a8d271b1e0a35fcd9898c14ed4e8.exe | C:\Users\admin\AppData\Local\Temp\637066616983561250_1023e48c-b7a6-4309-aa7b-5cbf6601257c.db | sqlite | |
MD5:0B3C43342CE2A99318AA0FE9E531C57B | SHA256:0CCB4915E00390685621DA3D75EBFD5EDADC94155A79C66415A7F4E9763D71B8 | |||
| 2564 | WinRAR.exe | C:\Users\admin\Desktop\c720a8d271b1e0a35fcd9898c14ed4e8.ico | executable | |
MD5:C720A8D271B1E0A35FCD9898C14ED4E8 | SHA256:3E0353E2DB479CBA4FB9D4637B2EEE0899E11D29D0142239C36A09A94065A122 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
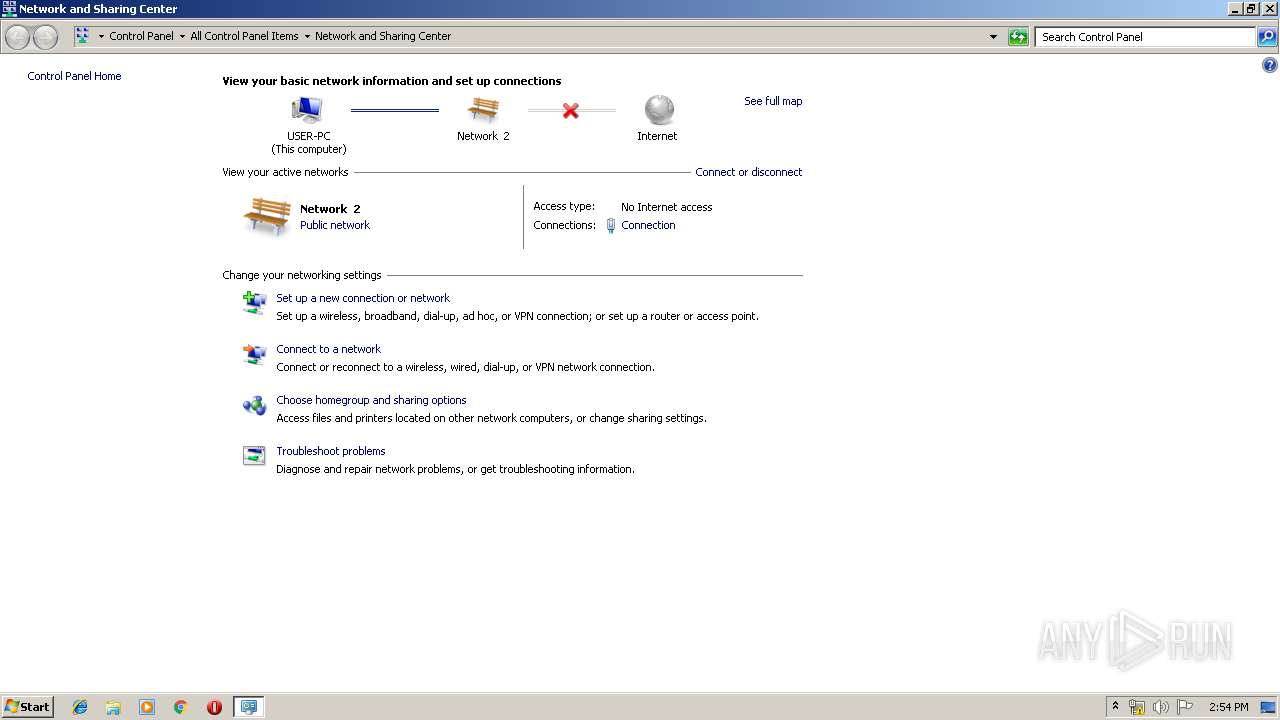
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2580 | c720a8d271b1e0a35fcd9898c14ed4e8.exe | GET | 200 | 18.214.132.216:80 | http://checkip.amazonaws.com/ | US | text | 15 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2580 | c720a8d271b1e0a35fcd9898c14ed4e8.exe | 198.187.29.28:587 | smtp.jsfunrides.com | Namecheap, Inc. | US | malicious |
2580 | c720a8d271b1e0a35fcd9898c14ed4e8.exe | 18.214.132.216:80 | checkip.amazonaws.com | — | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
checkip.amazonaws.com |
| shared |
smtp.jsfunrides.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2580 | c720a8d271b1e0a35fcd9898c14ed4e8.exe | A Network Trojan was detected | MALWARE [PTsecurity] AgentTesla IP Check |
2580 | c720a8d271b1e0a35fcd9898c14ed4e8.exe | Generic Protocol Command Decode | SURICATA Applayer Detect protocol only one direction |
2 ETPRO signatures available at the full report