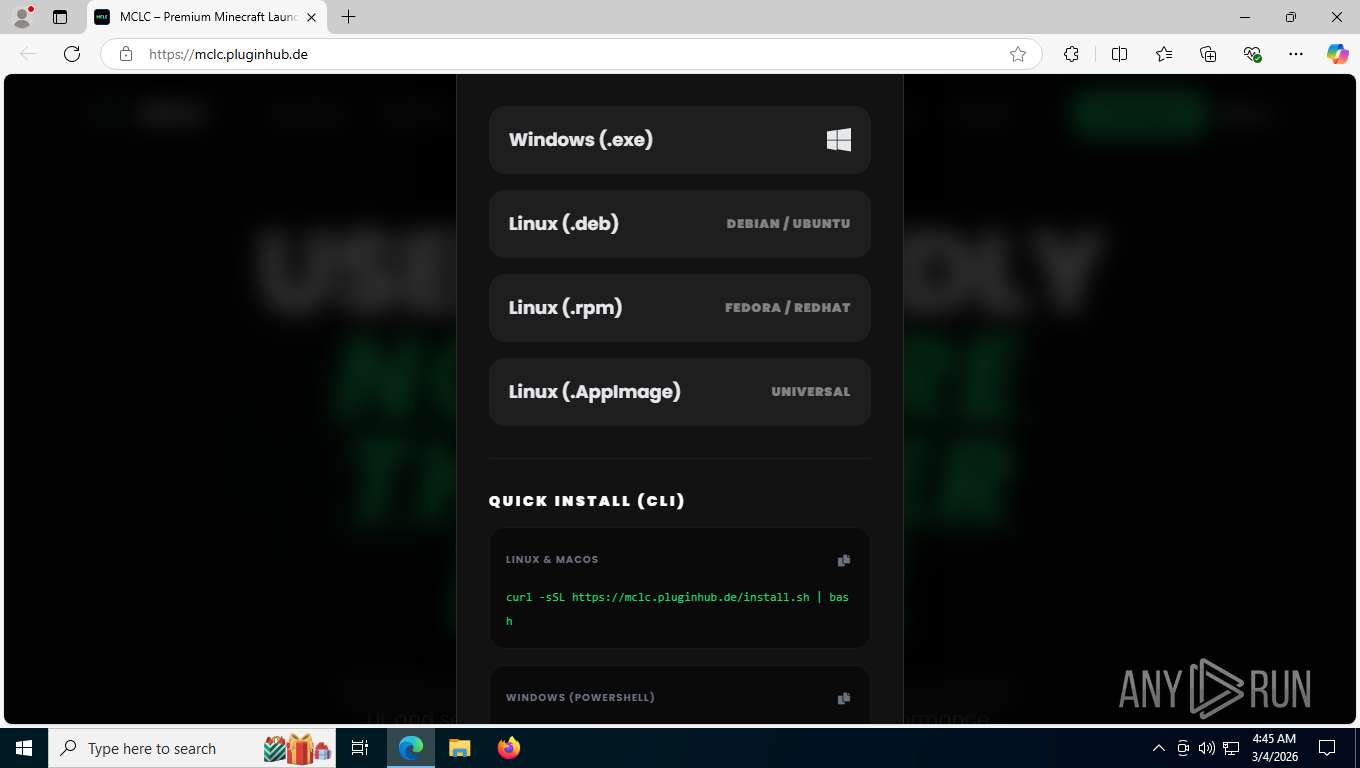
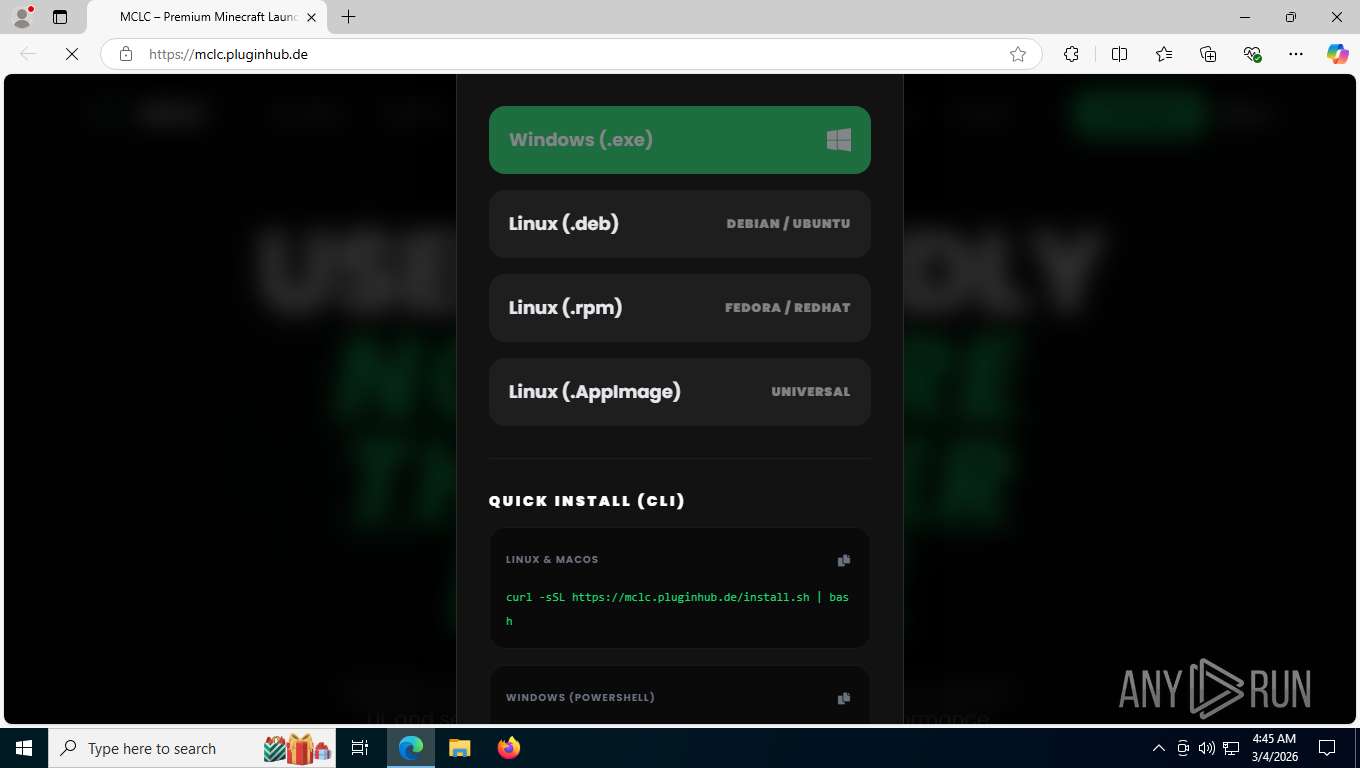
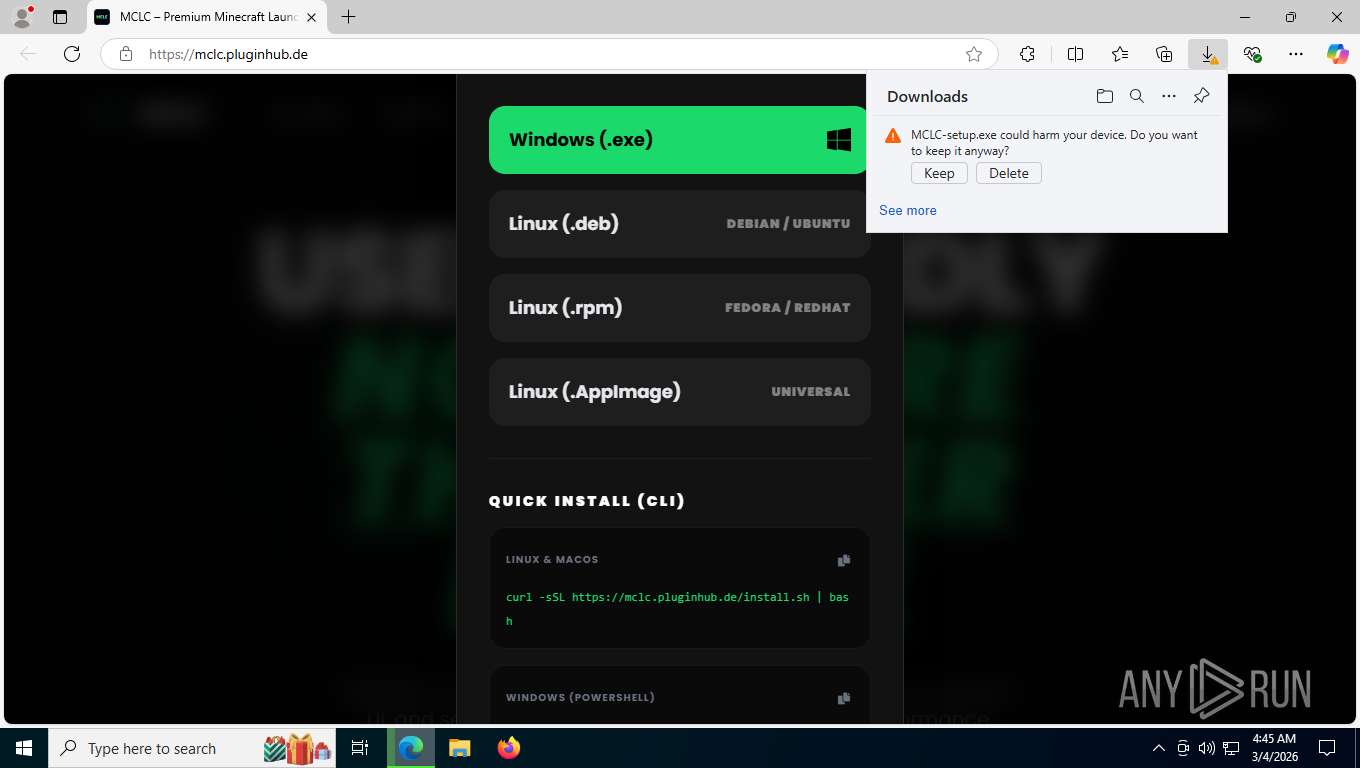
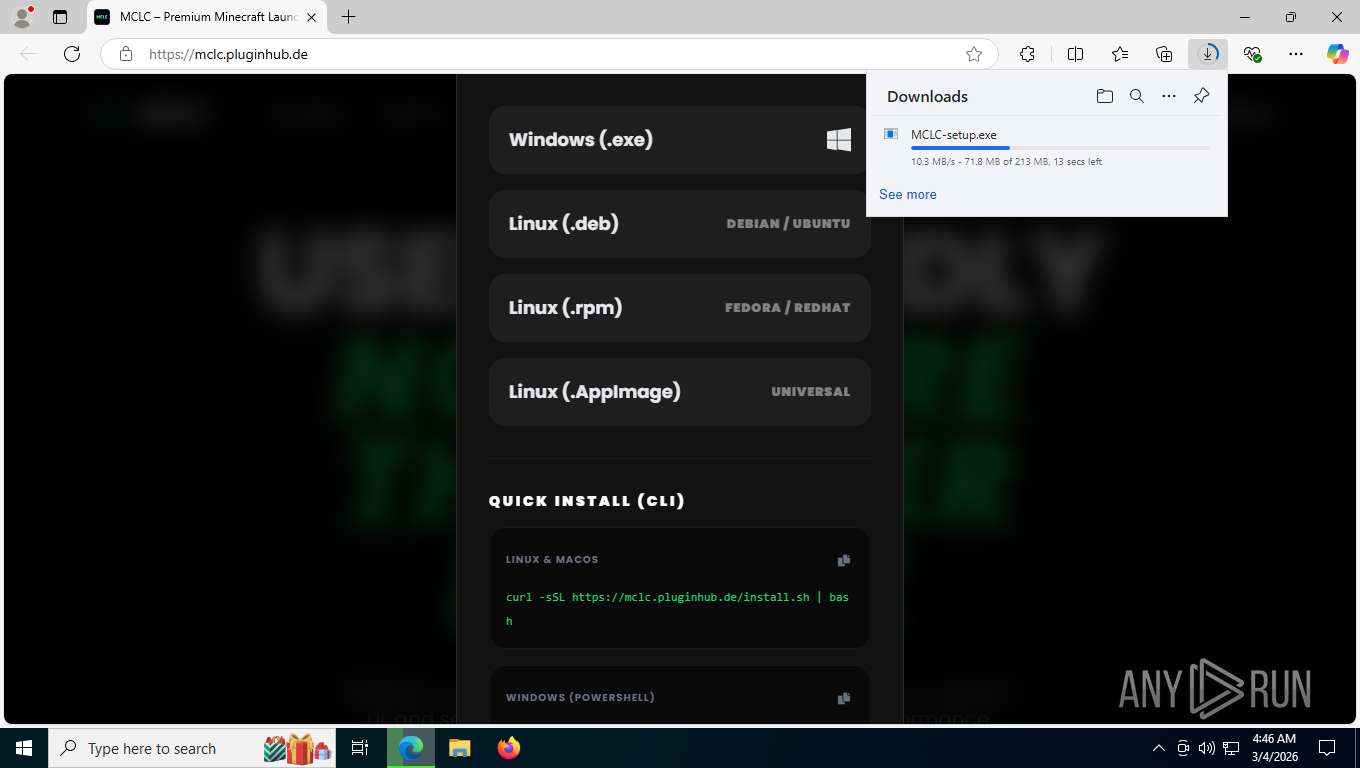
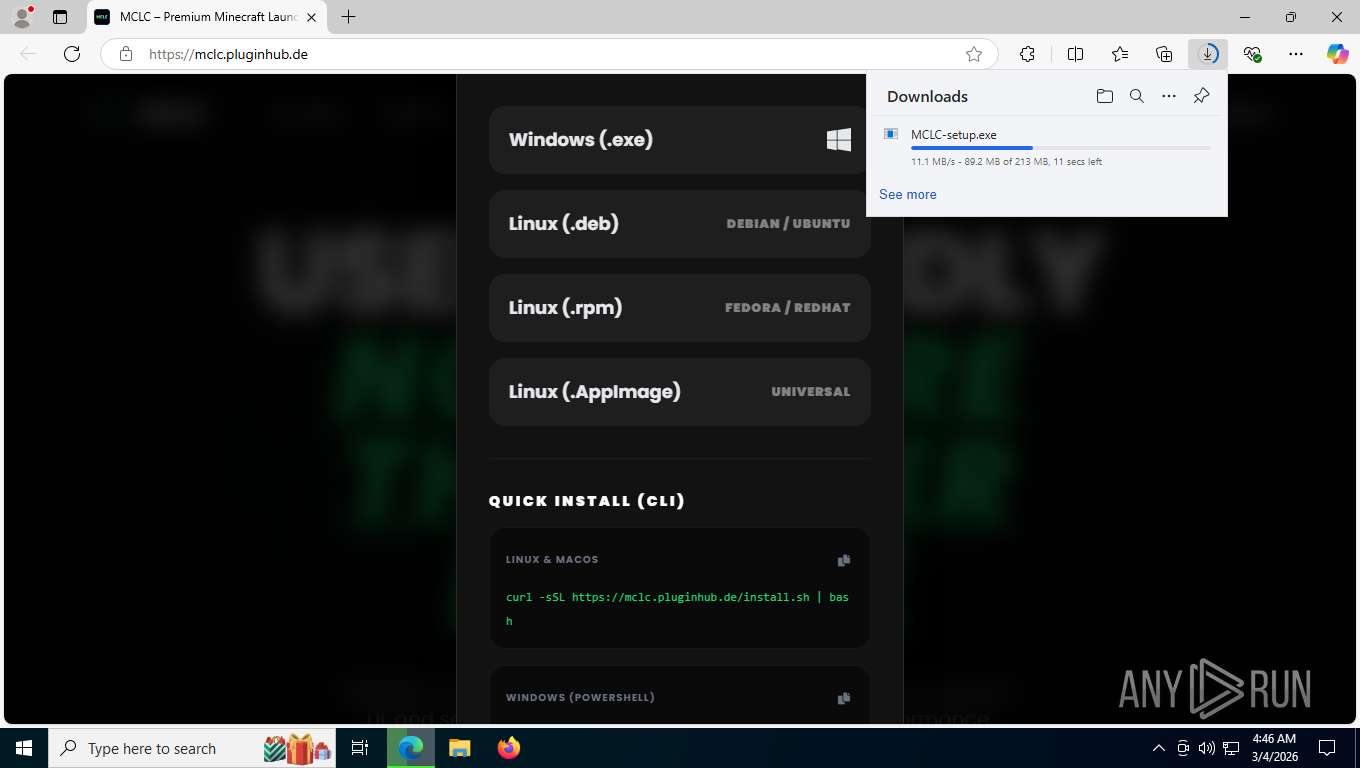
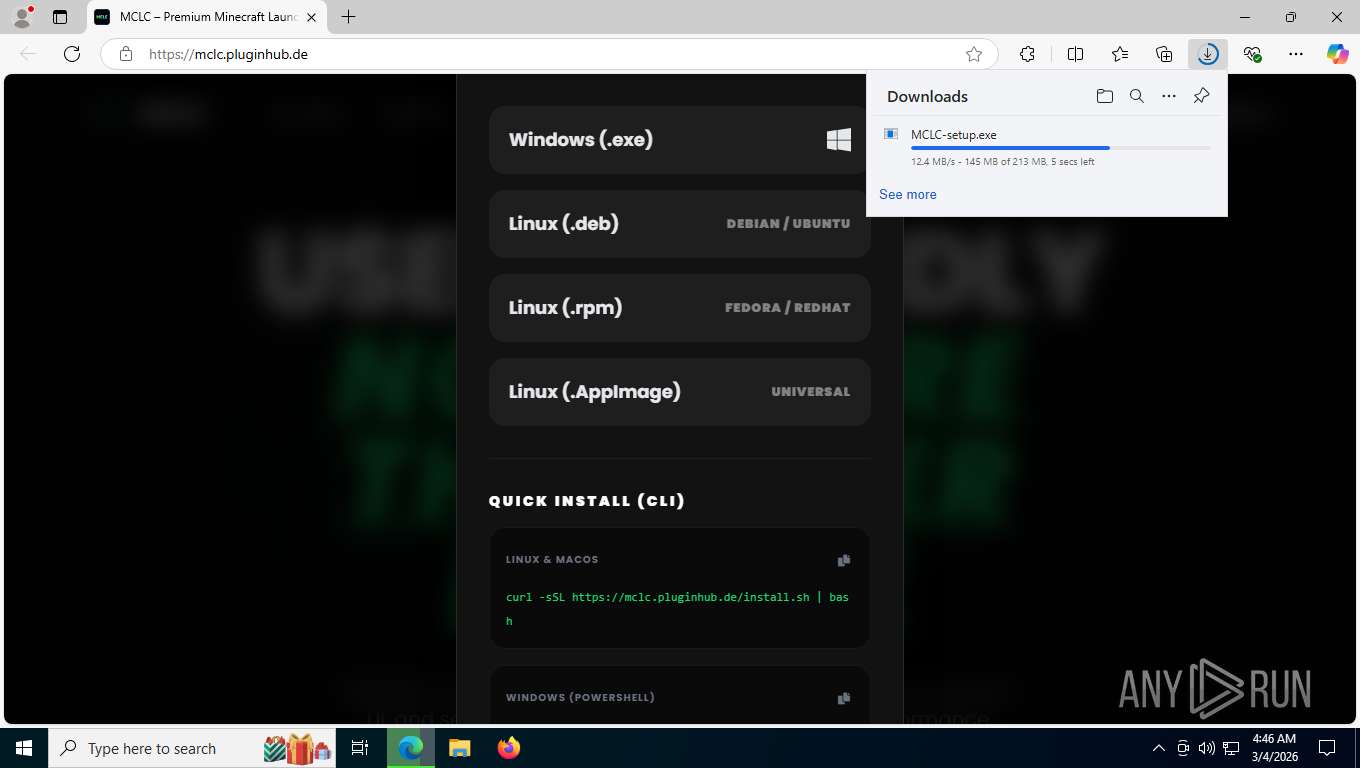
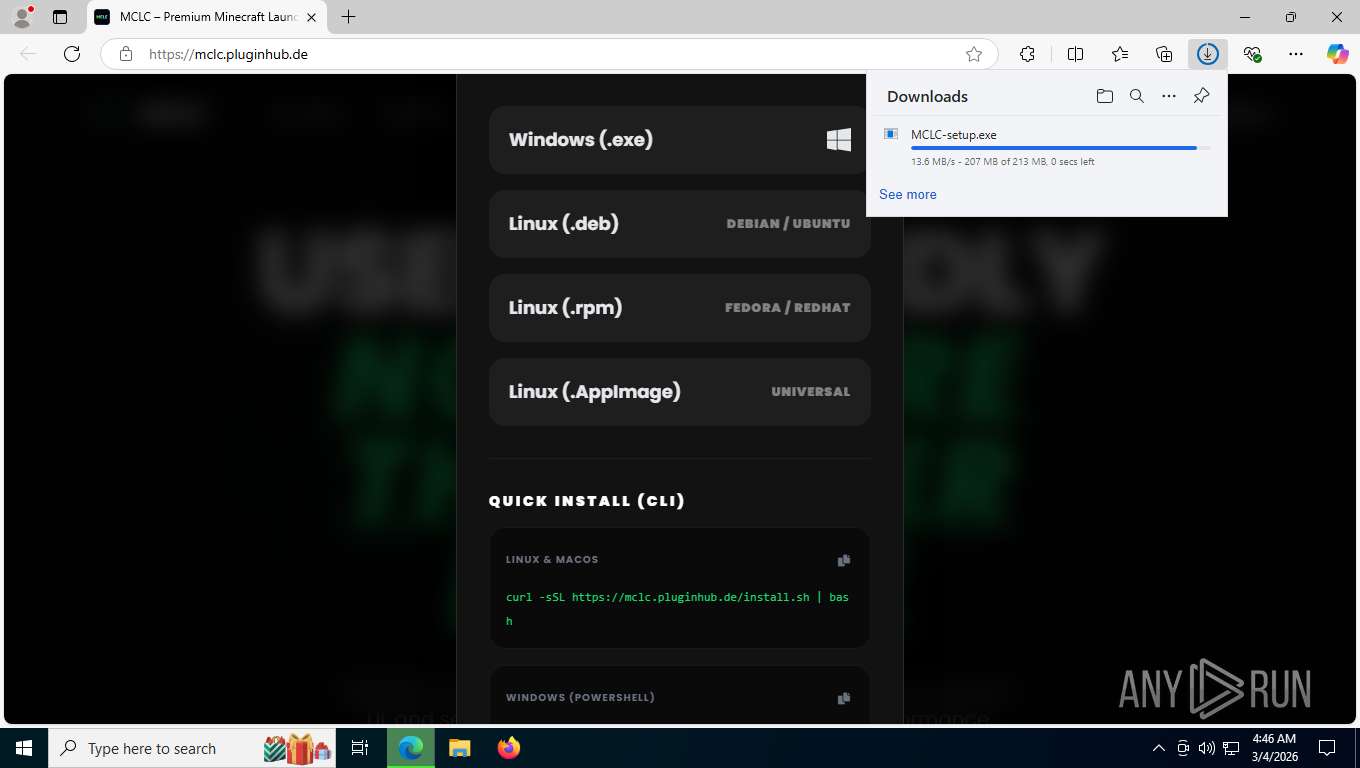
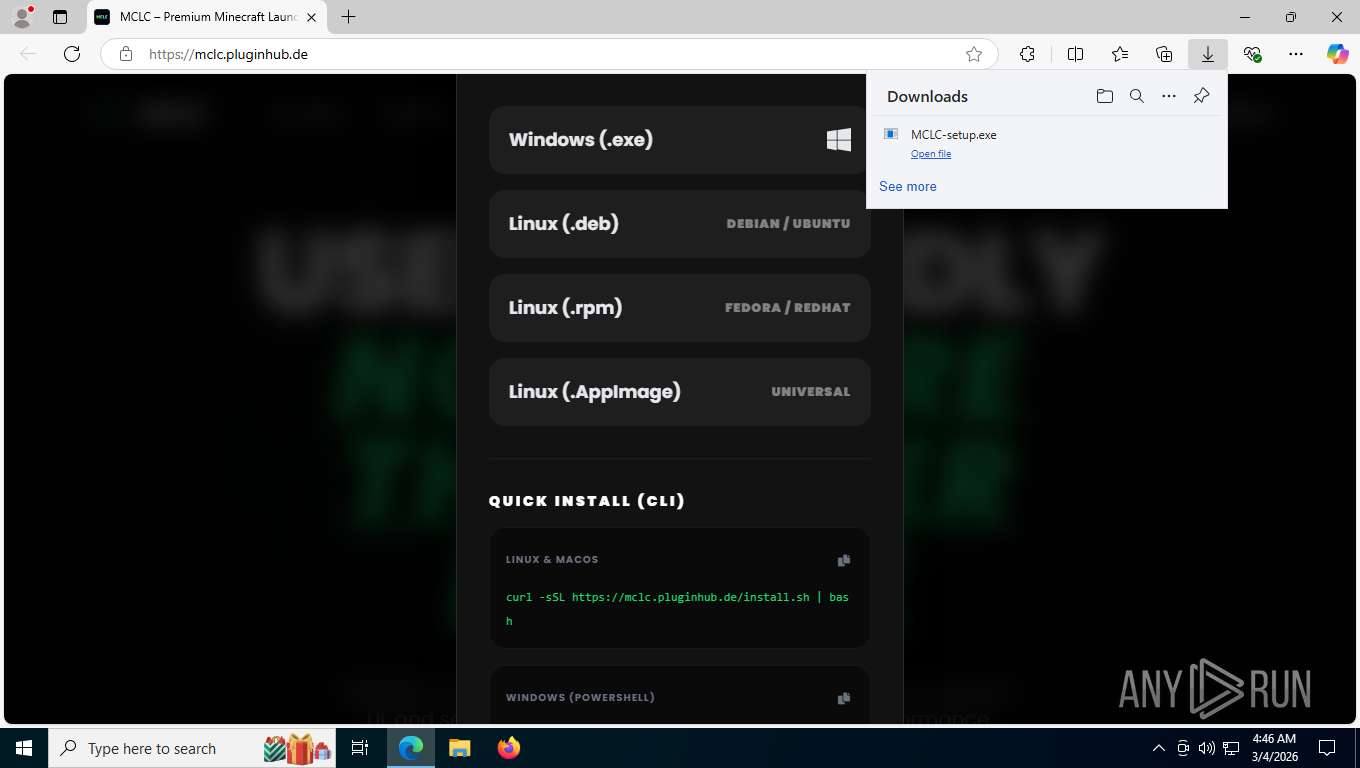
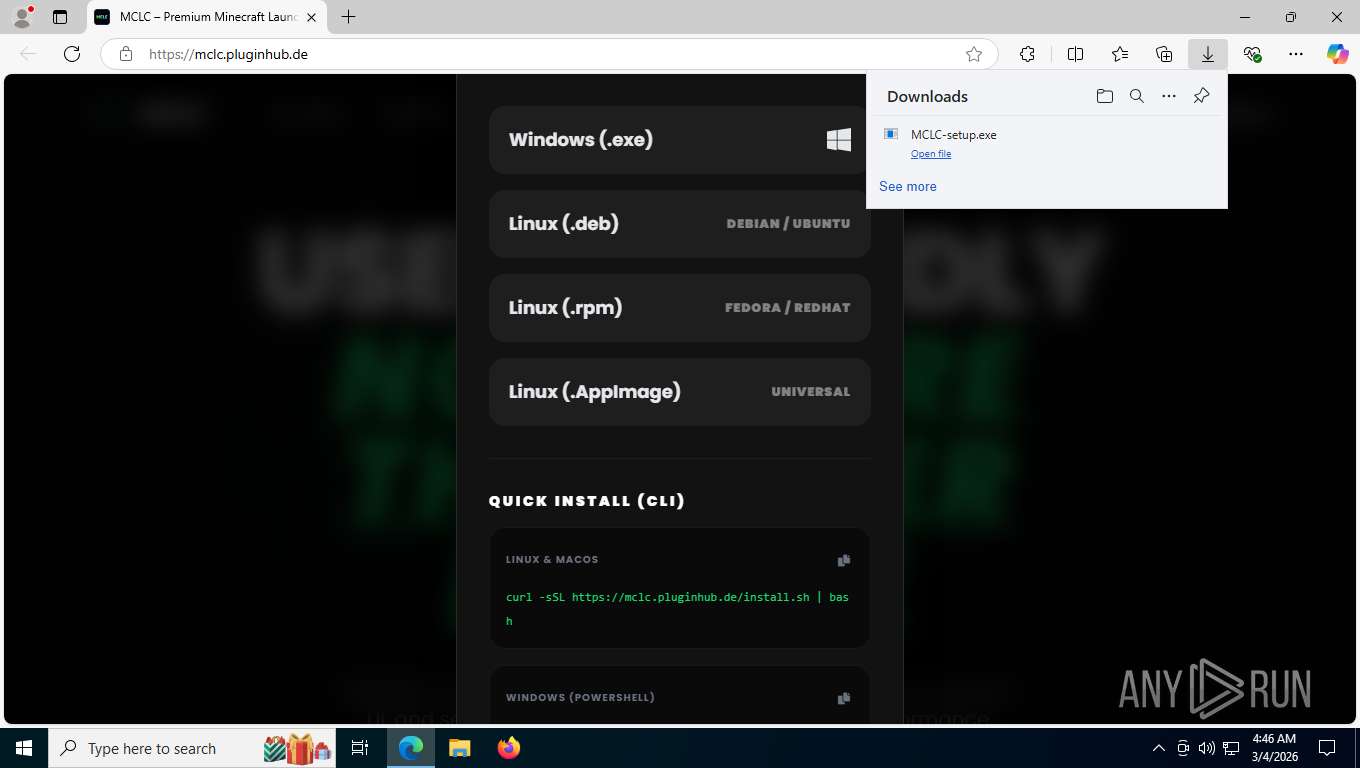
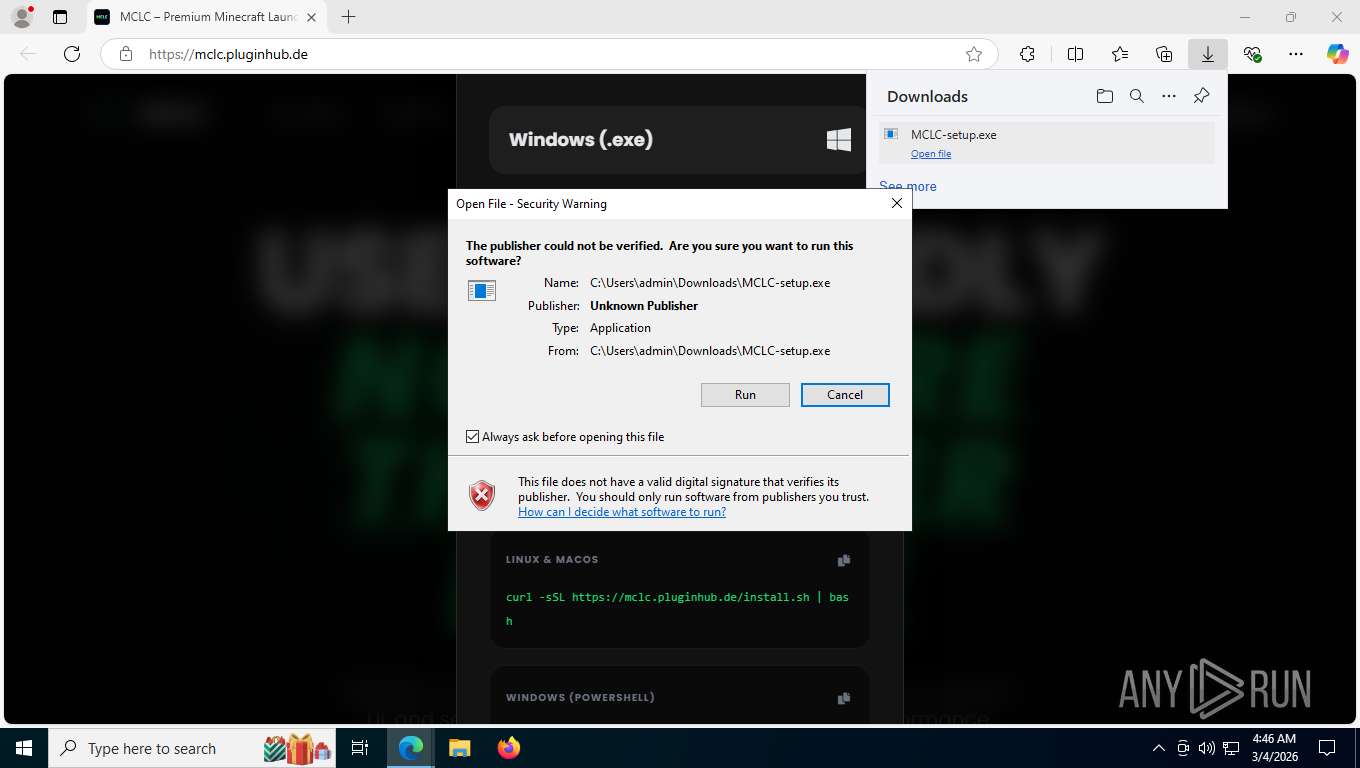
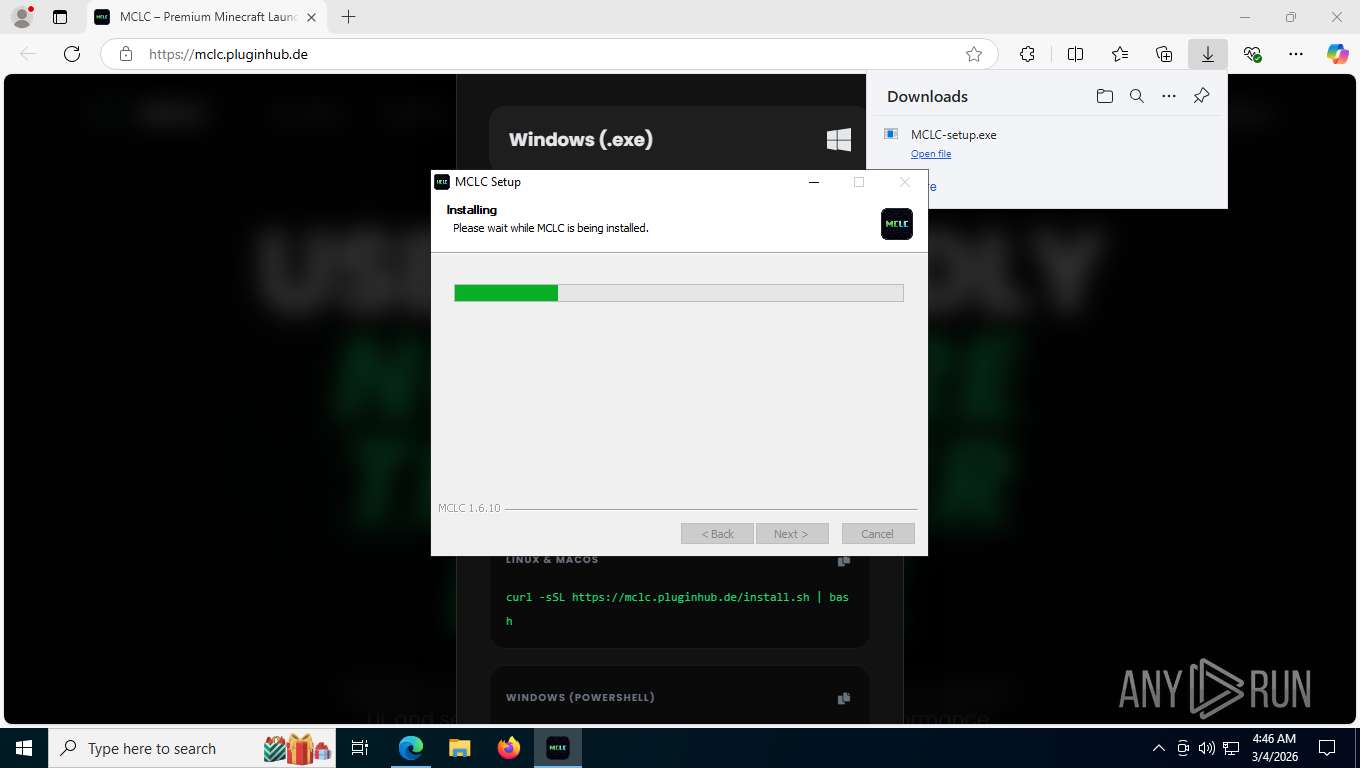
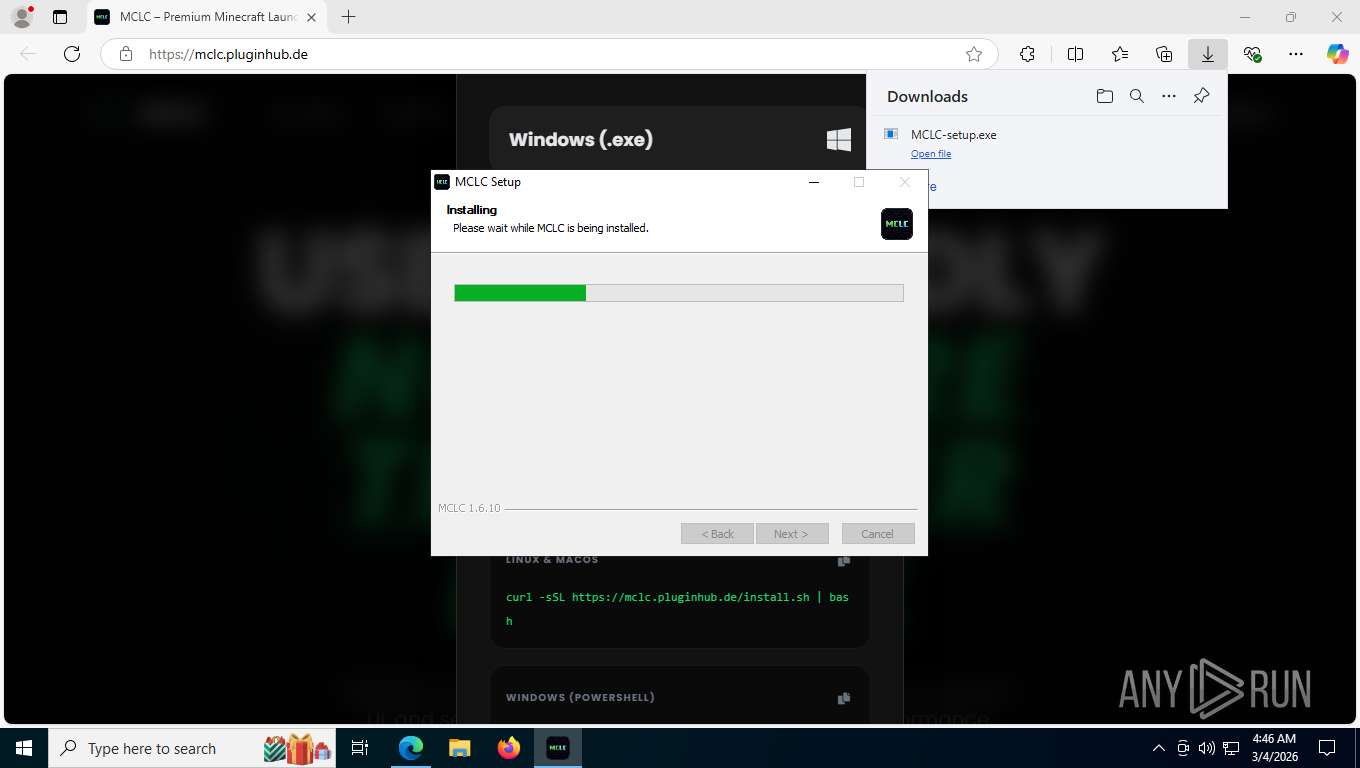
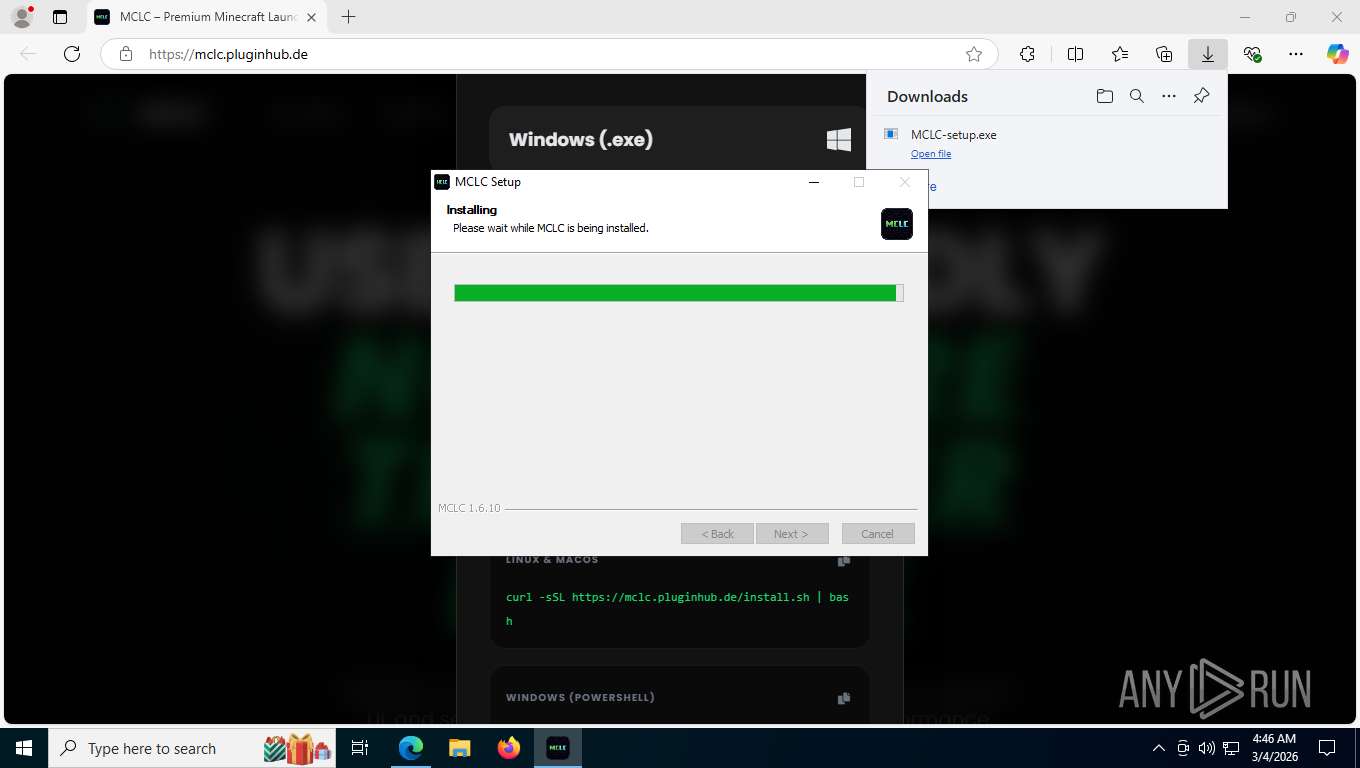
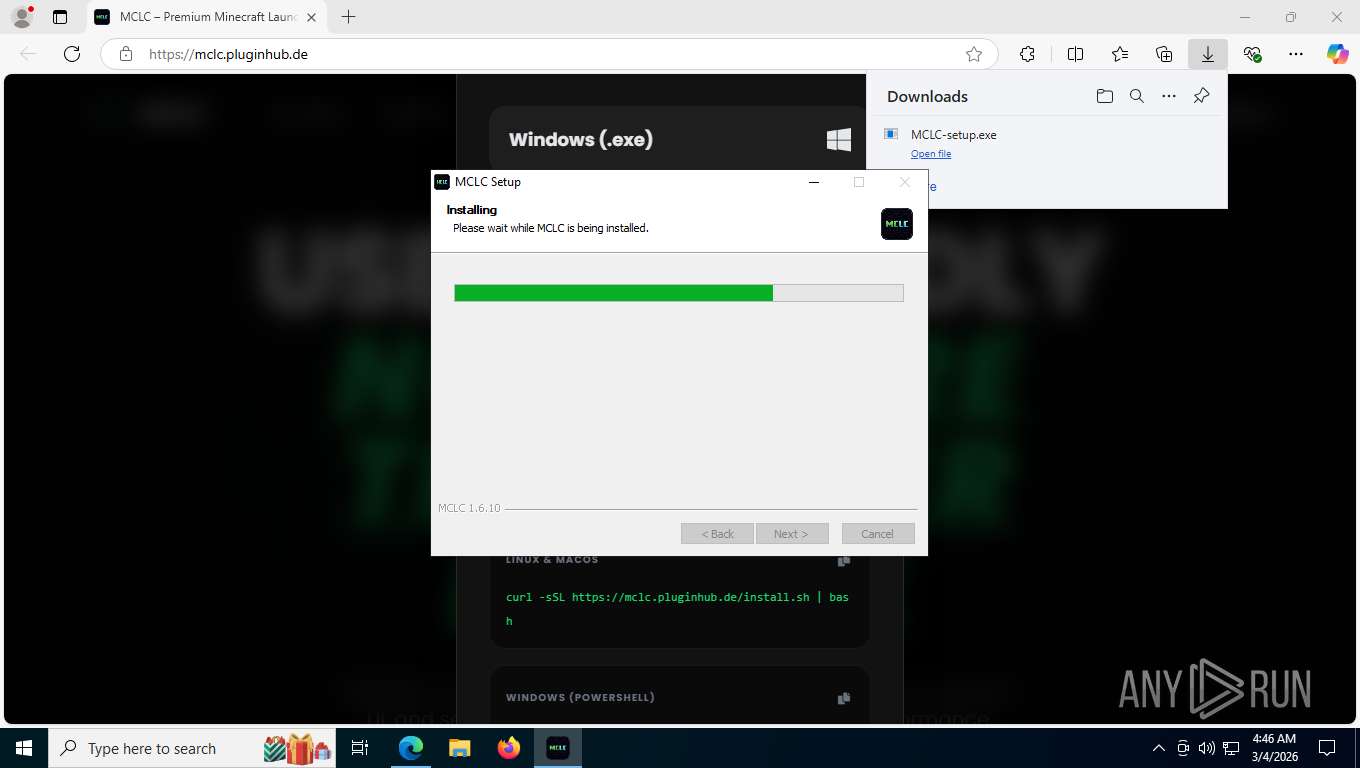
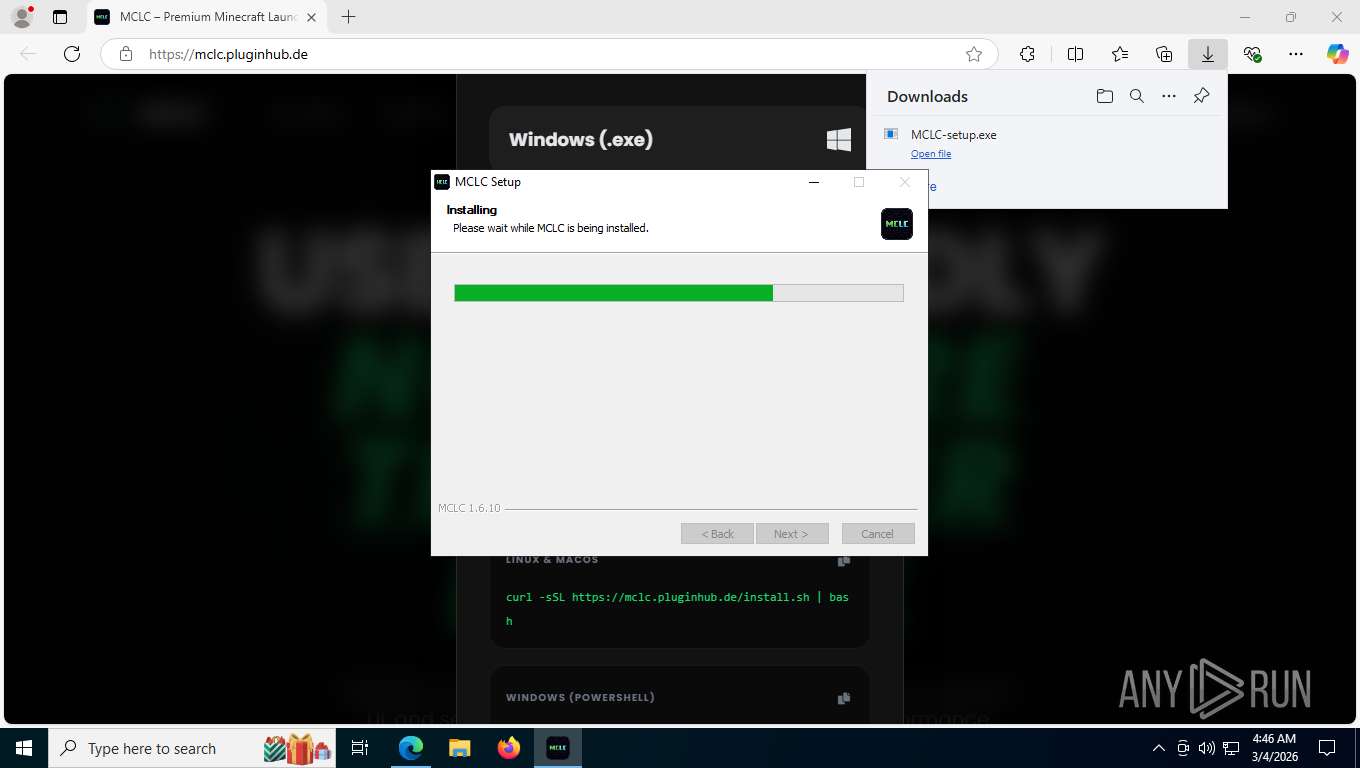
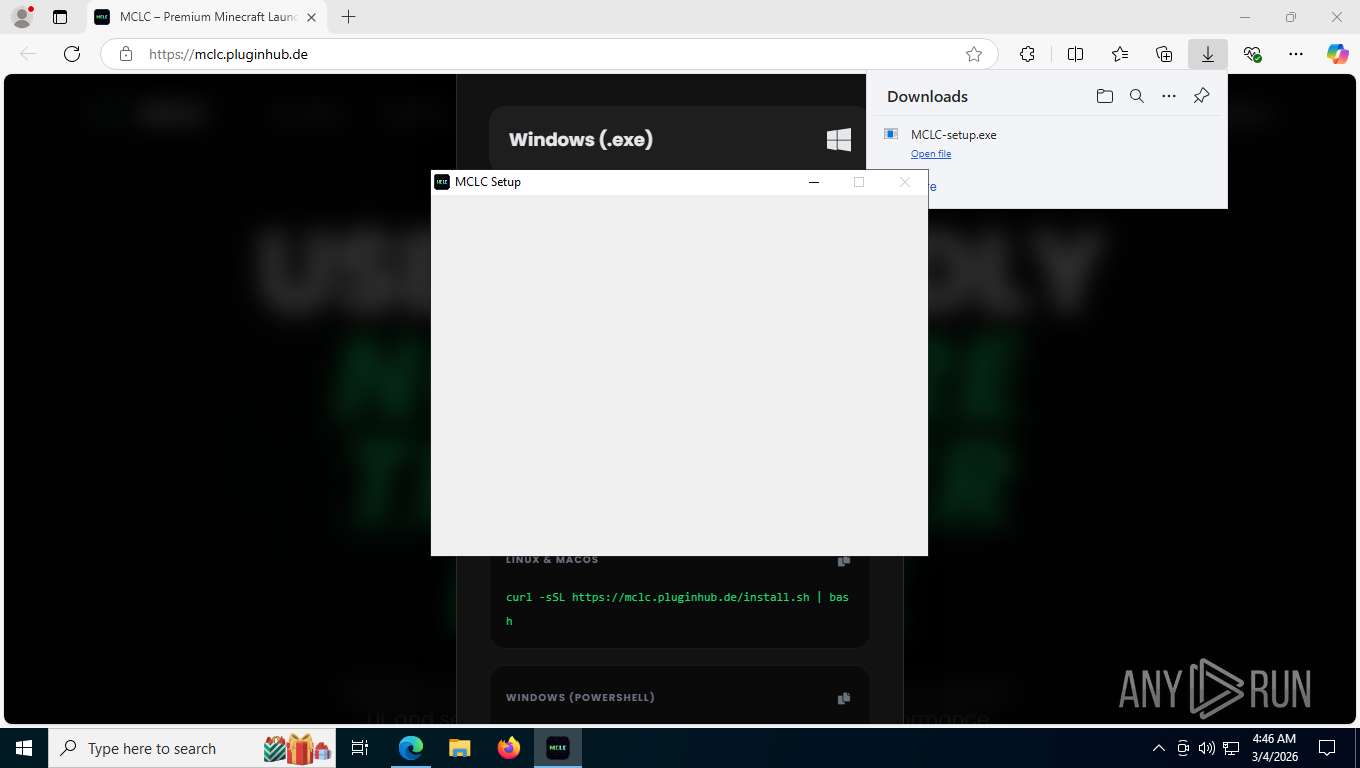
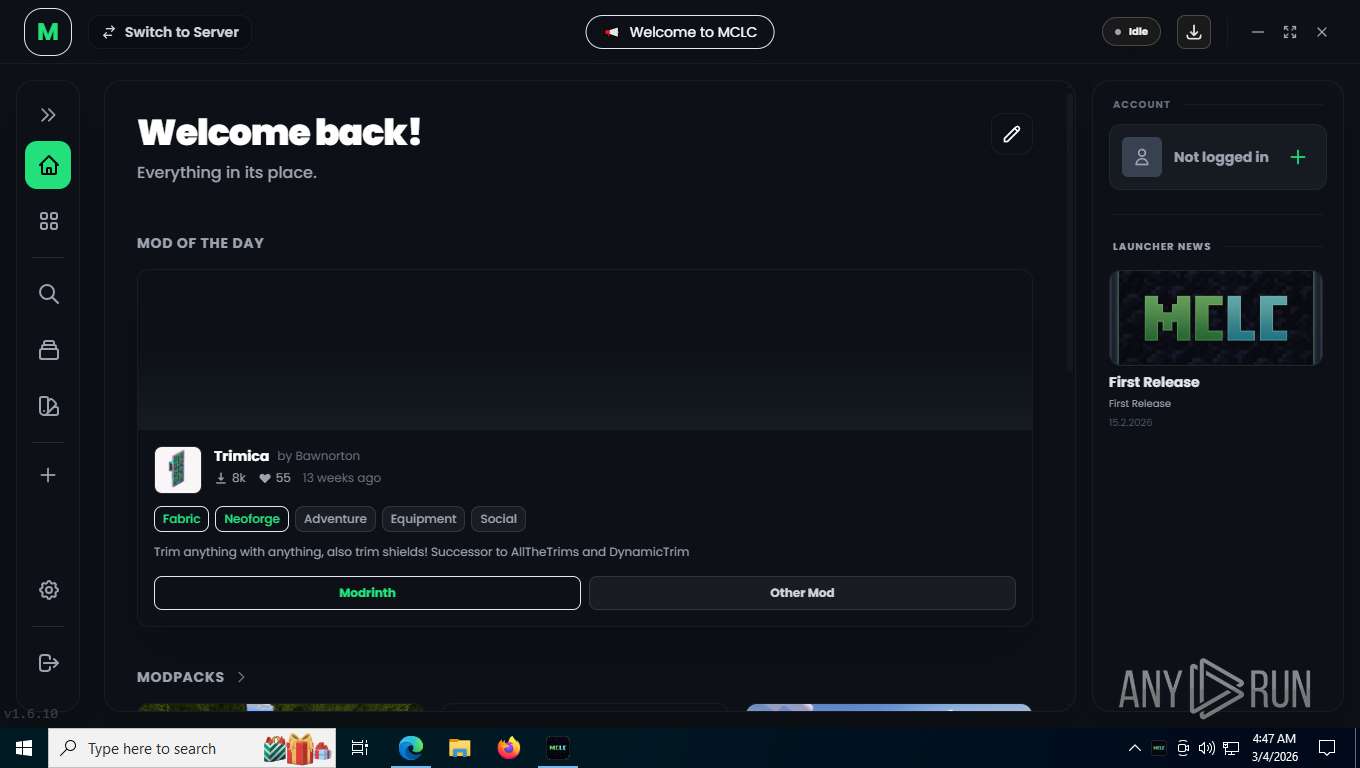
| URL: | https://mclc.pluginhub.de |
| Full analysis: | https://app.any.run/tasks/31631529-8197-4b7d-ac04-15eb4a6a2daa |
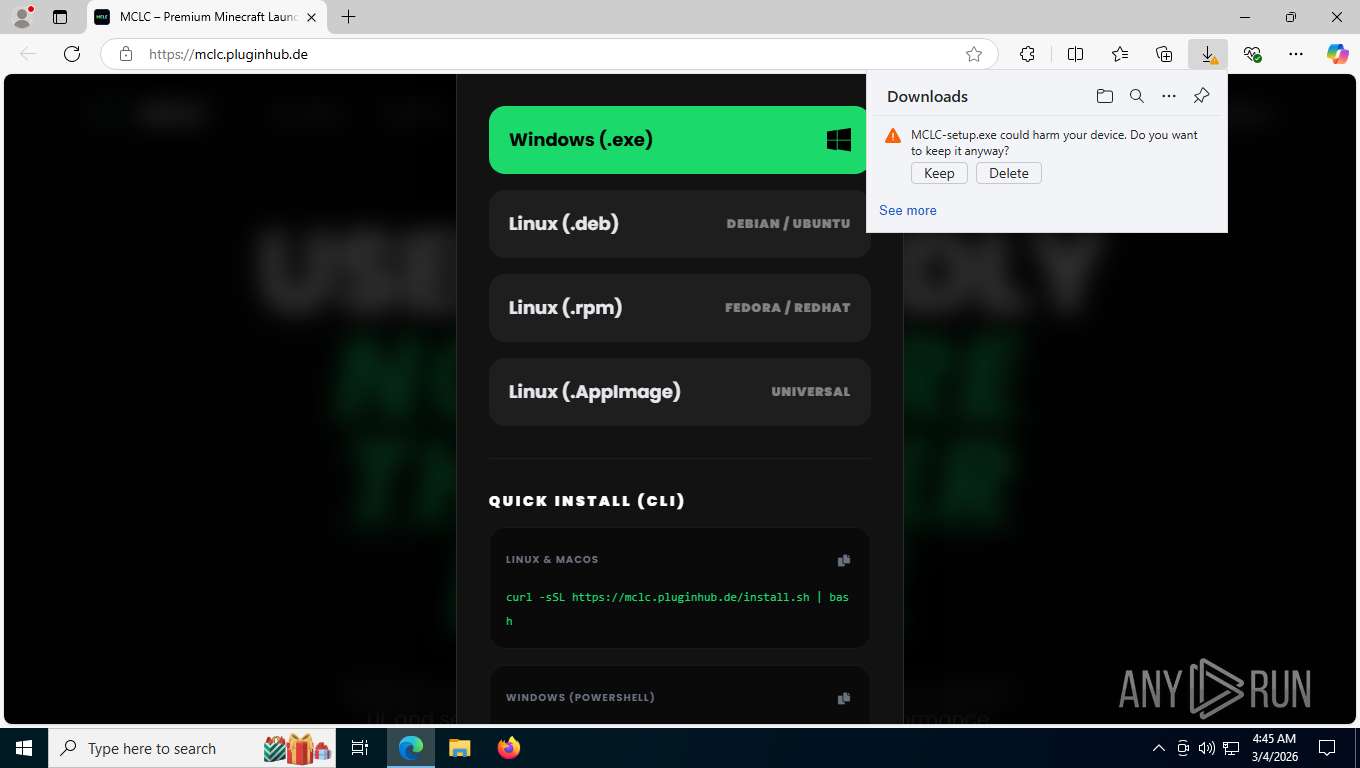
| Verdict: | Malicious activity |
| Analysis date: | March 04, 2026, 09:45:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
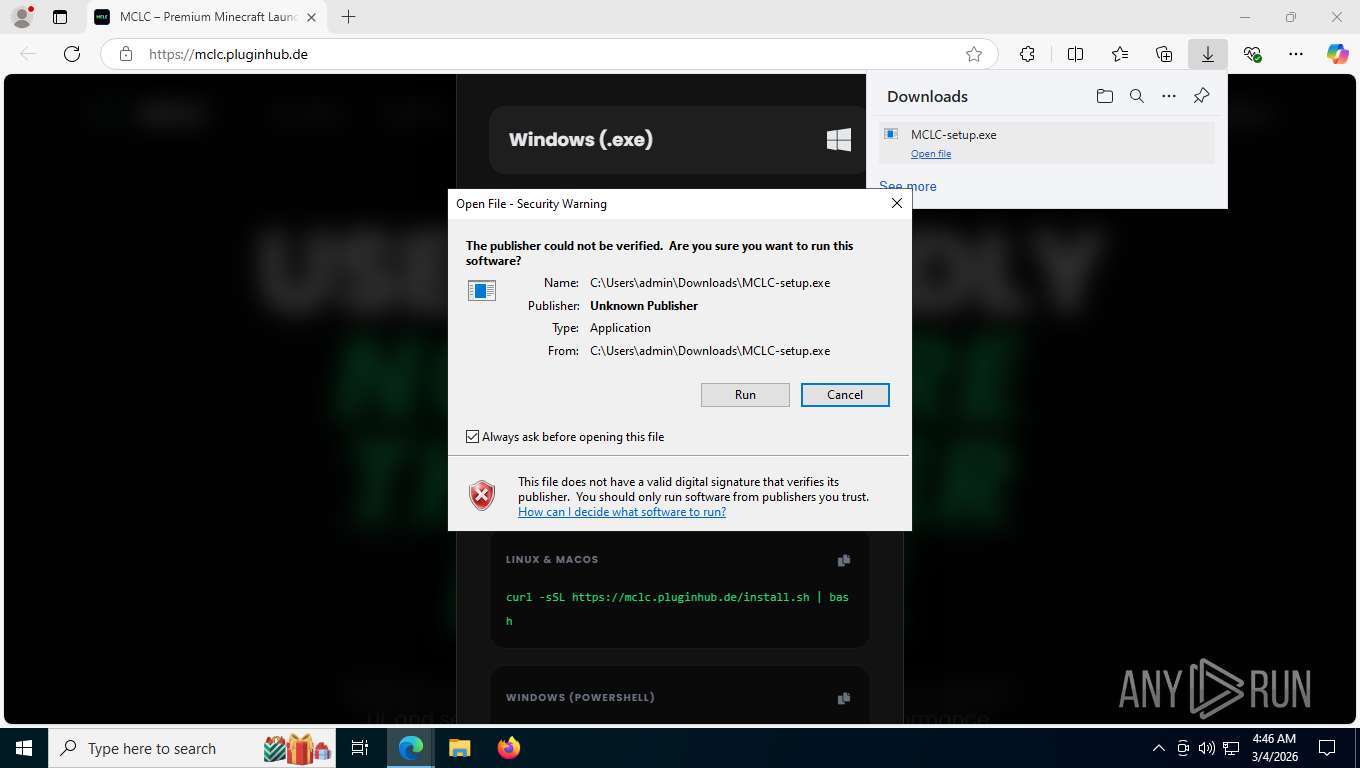
| MD5: | 7D90949D71122E331952610BC88110CC |
| SHA1: | FC81351DFBBF17F389F3C393EF19EF5D152FB633 |
| SHA256: | 2AF058A817F767271AE4A39ECB3C69615DC83DC71B5935051971D2B7C68129A0 |
| SSDEEP: | 3:N8PGL+:2+L+ |
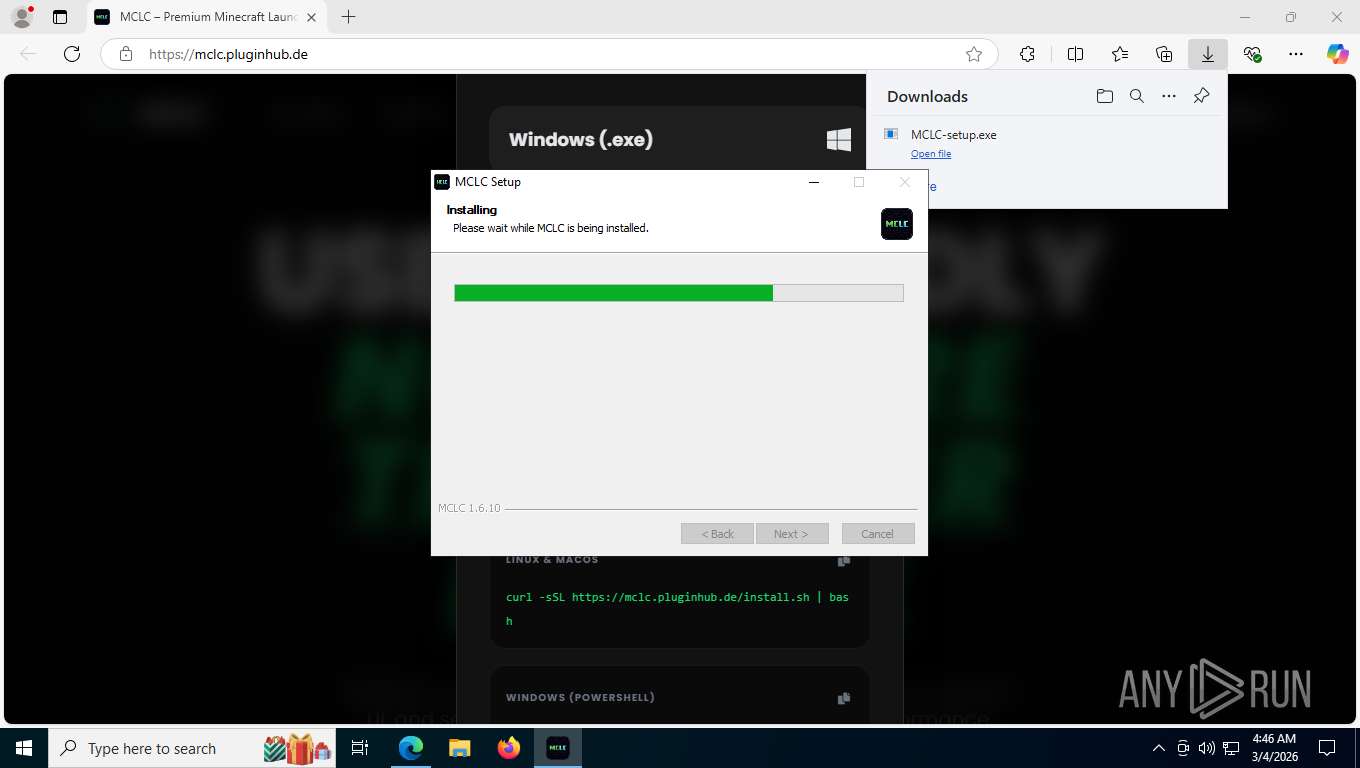
MALICIOUS
No malicious indicators.SUSPICIOUS
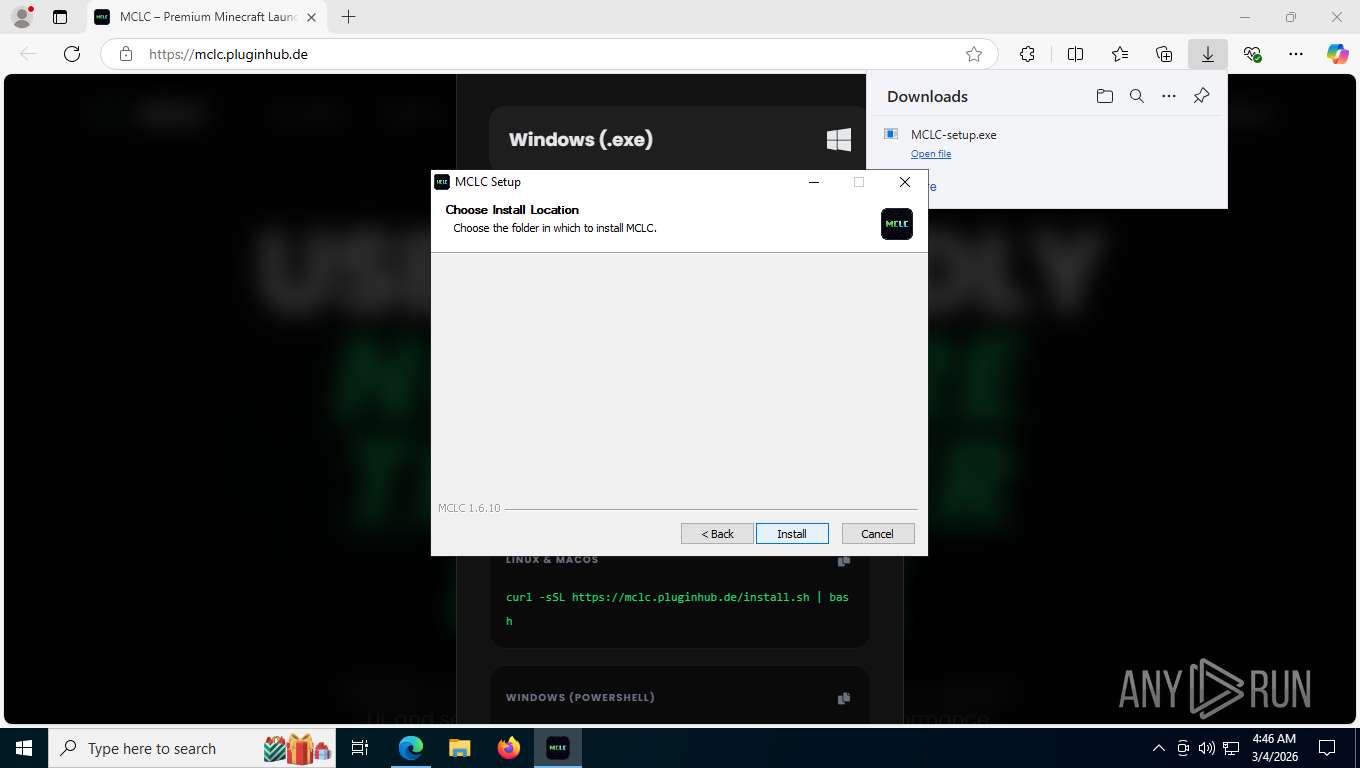
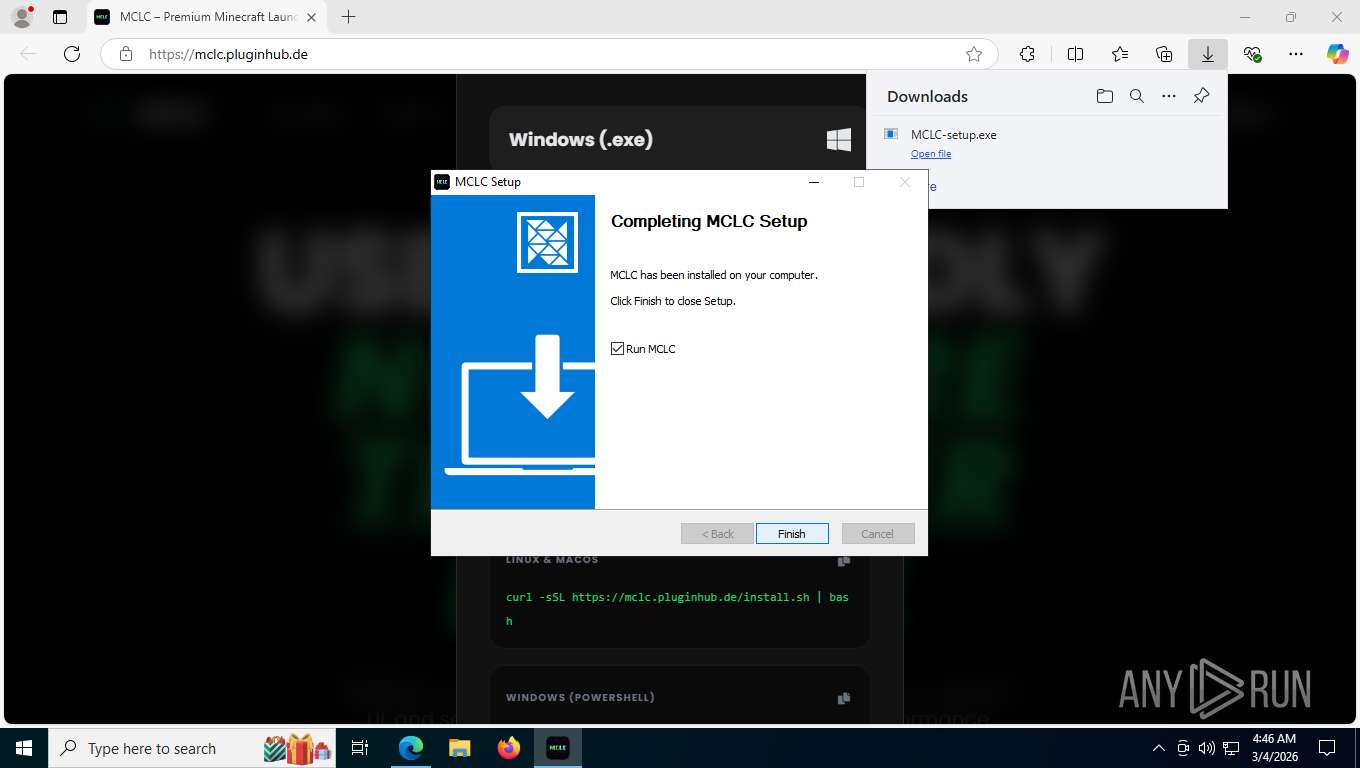
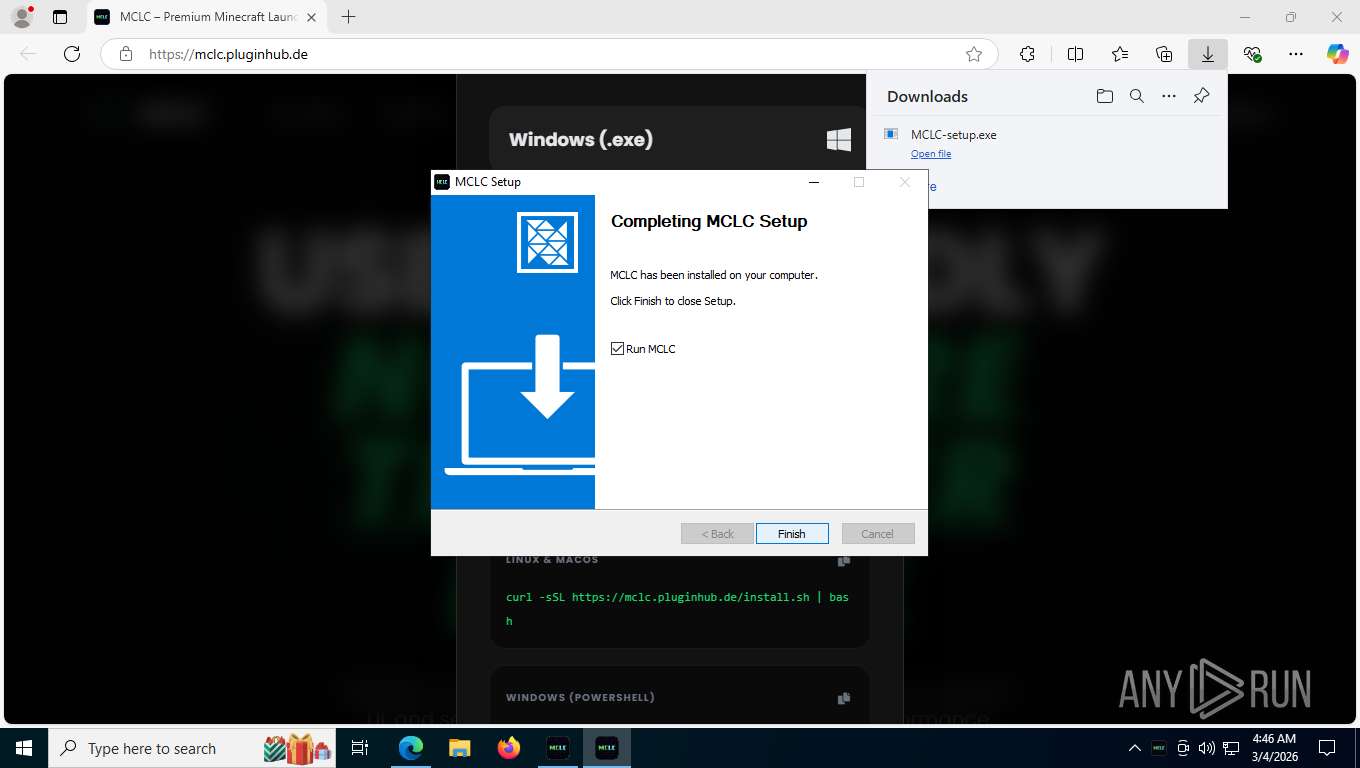
The process creates files with name similar to system file names
- MCLC-setup.exe (PID: 4852)
Malware-specific behavior (creating "System.dll" in Temp)
- MCLC-setup.exe (PID: 4852)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7428)
Starts POWERSHELL.EXE for commands execution
- MCLC-setup.exe (PID: 4852)
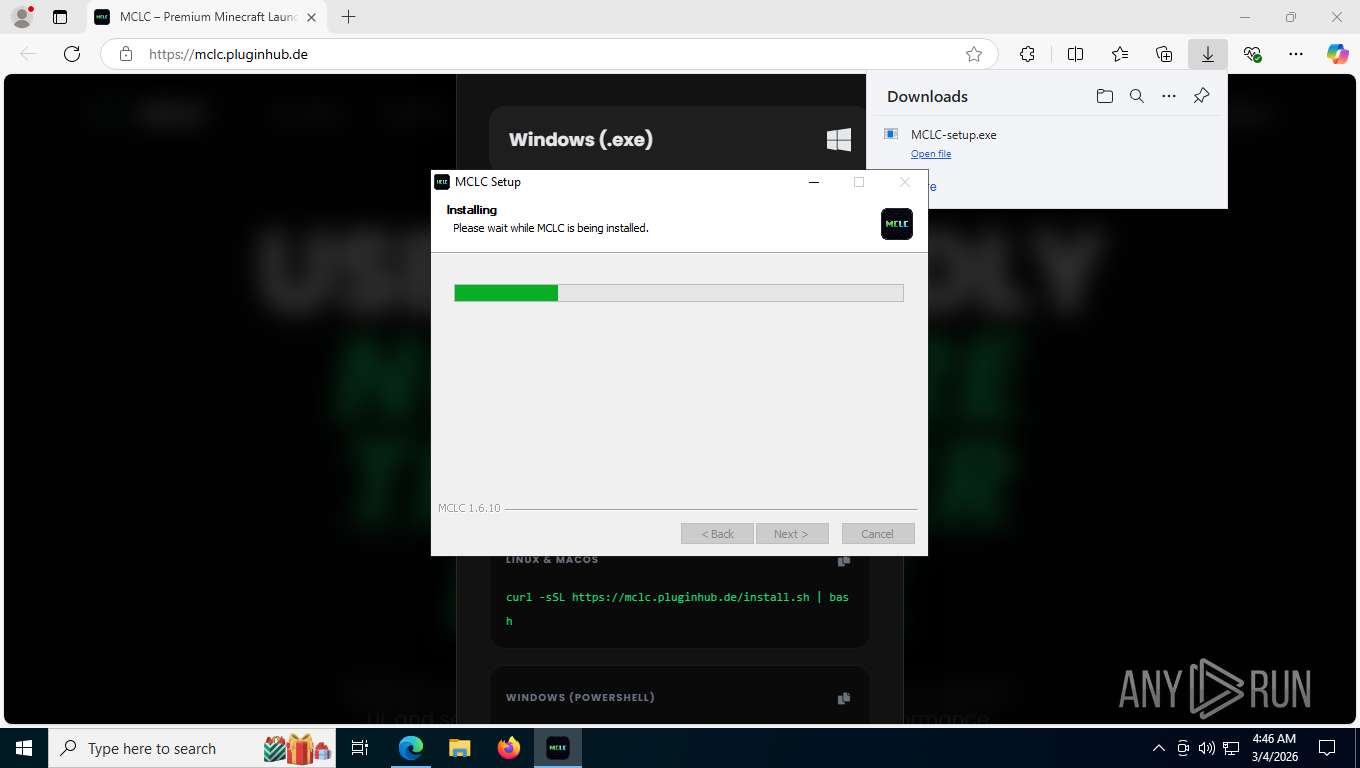
Executable content was dropped or overwritten
- MCLC-setup.exe (PID: 4852)
Application launched itself
- MCLC.exe (PID: 8416)
Get information on the list of running processes
- MCLC-setup.exe (PID: 4852)
Drops 7-zip archiver for unpacking
- MCLC-setup.exe (PID: 4852)
Starts CMD.EXE for commands execution
- MCLC.exe (PID: 8416)
INFO
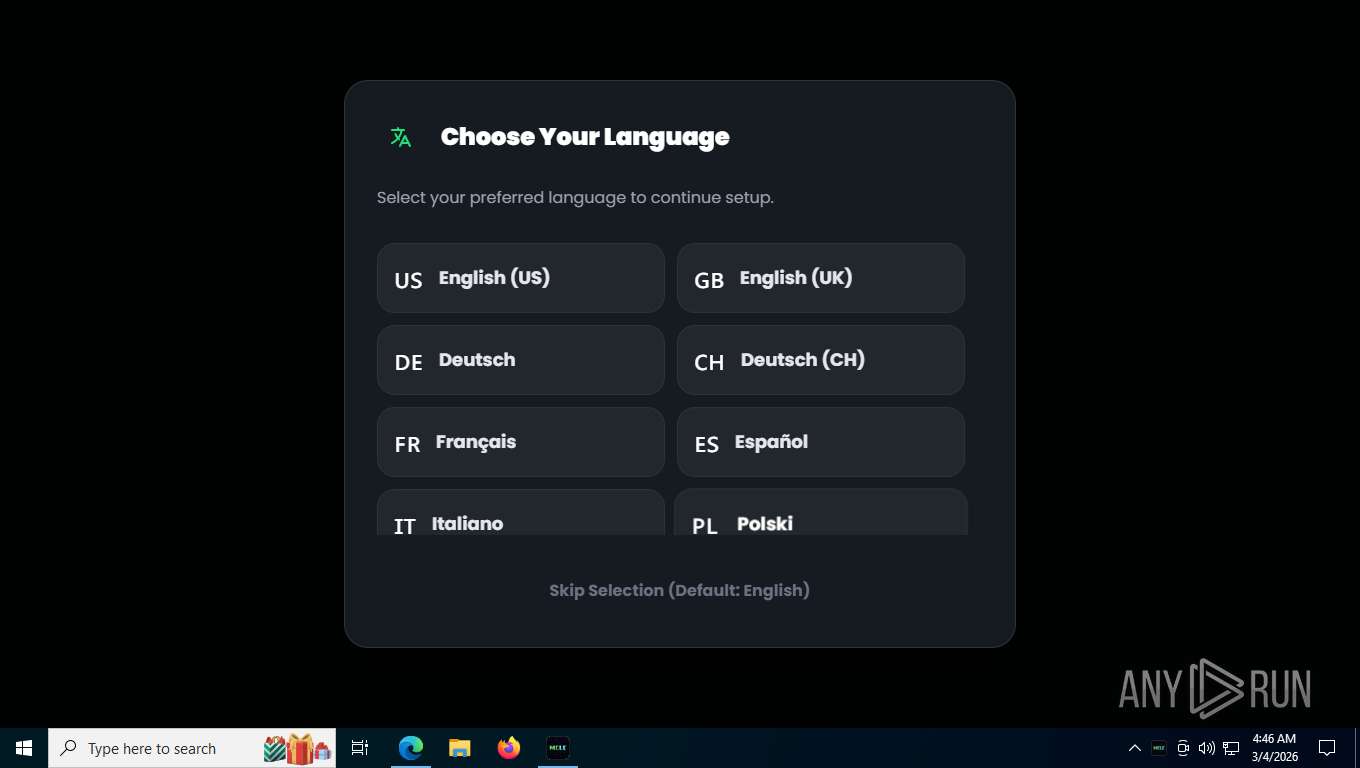
Checks supported languages
- identity_helper.exe (PID: 3584)
- MCLC-setup.exe (PID: 4852)
- MCLC.exe (PID: 8416)
- MCLC.exe (PID: 9044)
- MCLC.exe (PID: 5996)
- MCLC.exe (PID: 6980)
- MCLC.exe (PID: 6484)
Application launched itself
- msedge.exe (PID: 7392)
Executable content was dropped or overwritten
- msedge.exe (PID: 7392)
Reads Environment values
- identity_helper.exe (PID: 3584)
- MCLC.exe (PID: 8416)
- MCLC.exe (PID: 5996)
Reads the computer name
- identity_helper.exe (PID: 3584)
- MCLC-setup.exe (PID: 4852)
- MCLC.exe (PID: 8416)
- MCLC.exe (PID: 9044)
- MCLC.exe (PID: 6980)
Create files in a temporary directory
- MCLC-setup.exe (PID: 4852)
- MCLC.exe (PID: 8416)
Drops script file
- msedge.exe (PID: 772)
- powershell.exe (PID: 7428)
- powershell.exe (PID: 7932)
- powershell.exe (PID: 7240)
- MCLC-setup.exe (PID: 4852)
- MCLC.exe (PID: 8416)
The sample compiled with english language support
- MCLC-setup.exe (PID: 4852)
Gets the execution policy for the powershell session
- MCLC-setup.exe (PID: 4852)
Reads security settings of Internet Explorer
- MCLC-setup.exe (PID: 4852)
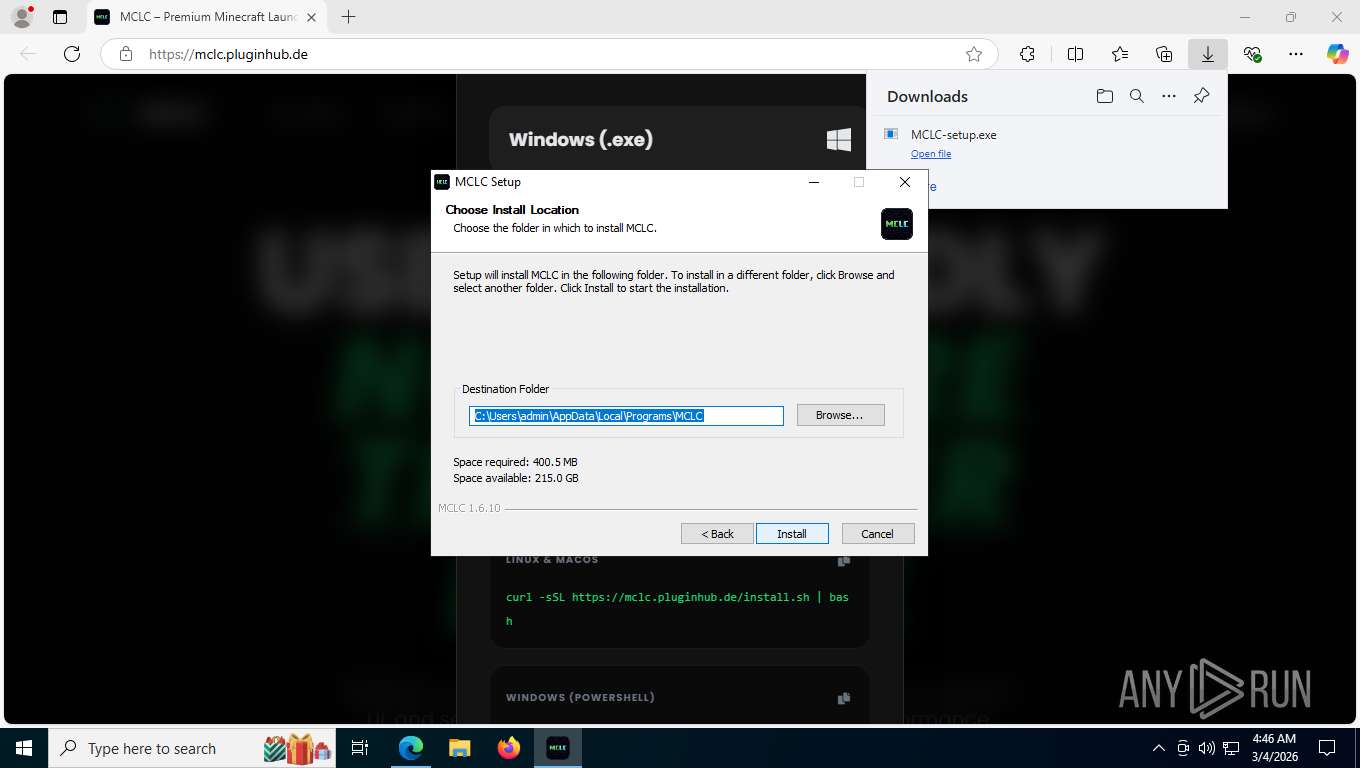
Creates files or folders in the user directory
- MCLC-setup.exe (PID: 4852)
- MCLC.exe (PID: 8416)
- MCLC.exe (PID: 6980)
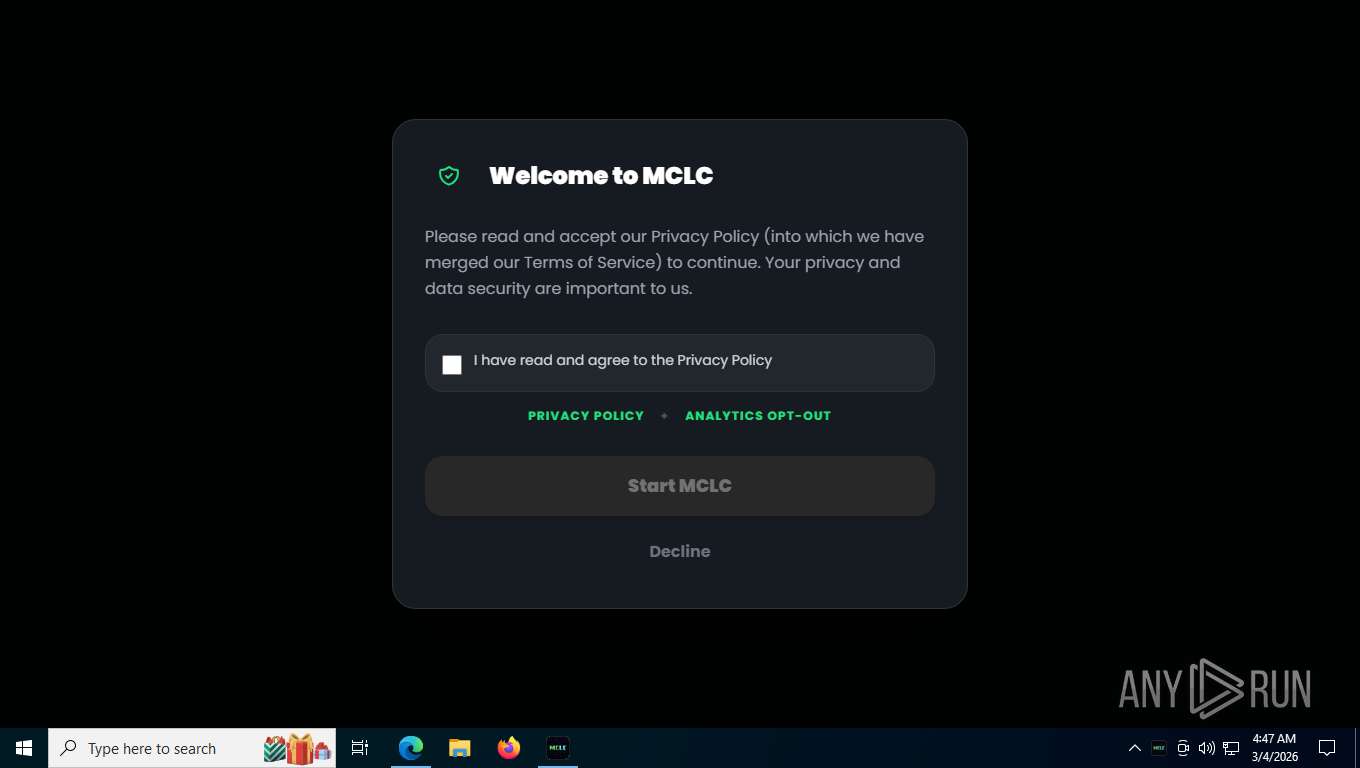
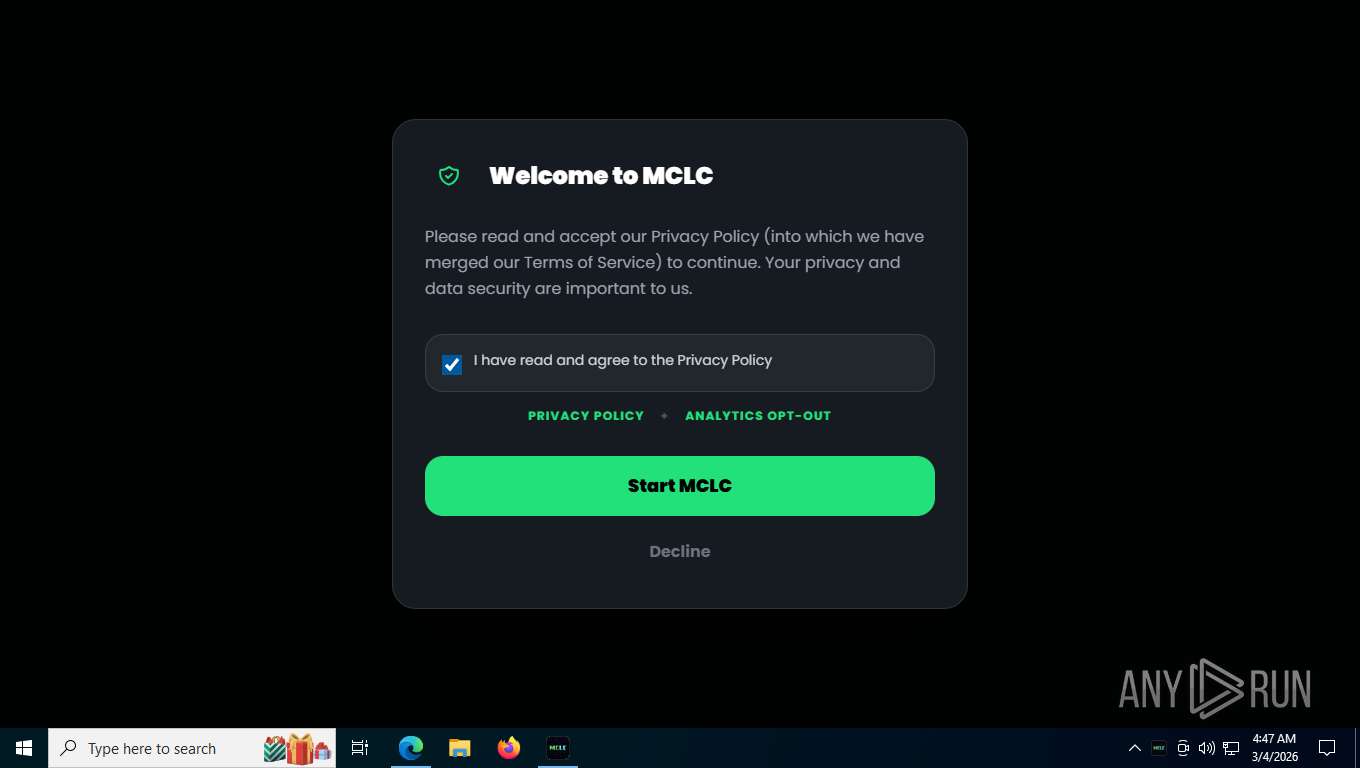
Creates a software uninstall entry
- MCLC-setup.exe (PID: 4852)
Process checks computer location settings
- MCLC.exe (PID: 8416)
- MCLC.exe (PID: 5996)
- MCLC.exe (PID: 6484)
Reads product name
- MCLC.exe (PID: 8416)
- MCLC.exe (PID: 5996)
Checks proxy server information
- MCLC.exe (PID: 8416)
- slui.exe (PID: 8356)
There is functionality for taking screenshot (YARA)
- MCLC-setup.exe (PID: 4852)
Manual execution by a user
- MCLC.exe (PID: 8416)
Reads the machine GUID from the registry
- MCLC.exe (PID: 8416)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
202
Monitored processes
50
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 772 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6528,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6524 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --string-annotations --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=2340,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=2332 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1324 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5772,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5744 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1432 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=796,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6784 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1572 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1760 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2280 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.Extractor --lang=en-US --service-sandbox-type=entity_extraction --disable-quic --onnx-enabled-for-ee --string-annotations --always-read-main-dll --field-trial-handle=5444,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5500 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2416 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7156,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=7076 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3516 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x294,0x298,0x29c,0x28c,0x2a4,0x7ffd6f4cf208,0x7ffd6f4cf214,0x7ffd6f4cf220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3584 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5824,i,8383541057589591014,2175078779678171330,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5860 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
20 660
Read events
20 628
Write events
14
Delete events
18
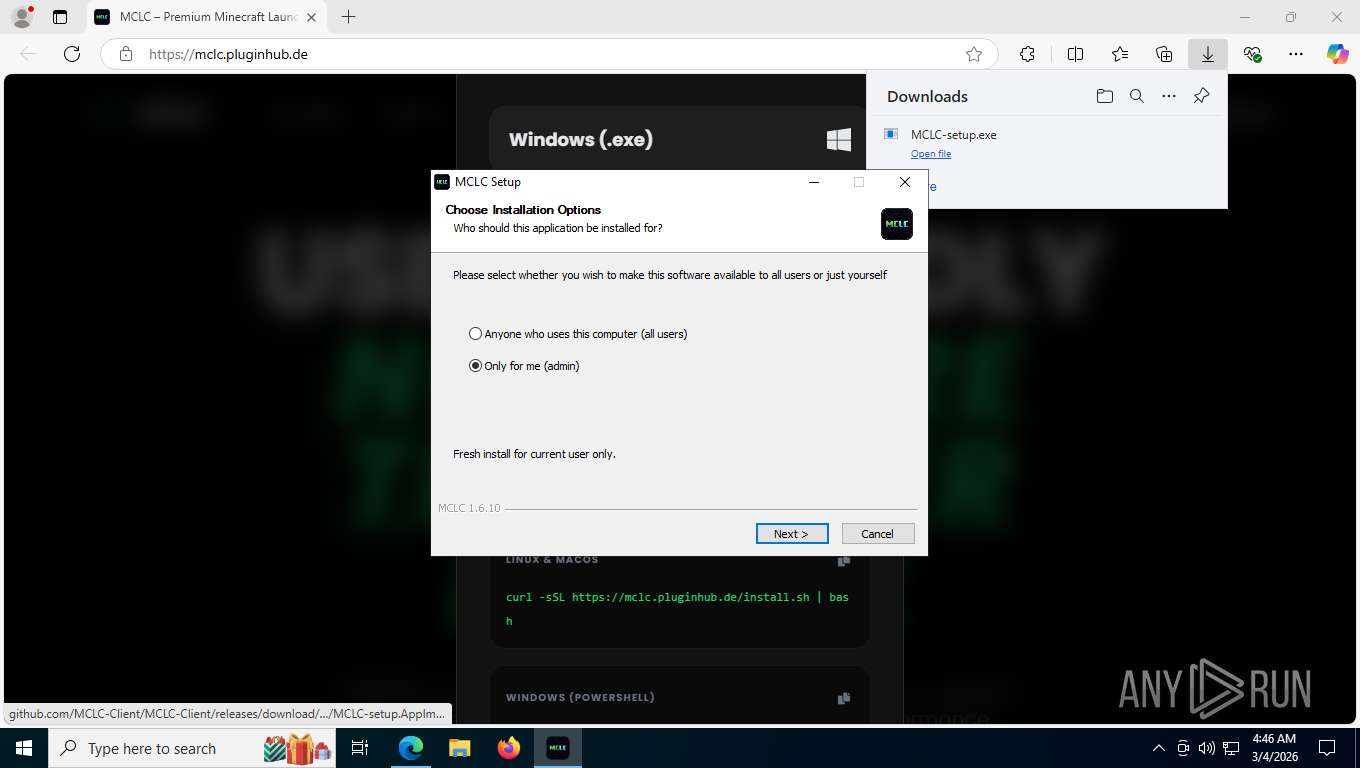
Modification events
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | GlobalAssocChangedCounter |
Value: 139 | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Users\admin\AppData\Local\Programs\MCLC | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | KeepShortcuts |
Value: true | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | ShortcutName |
Value: MCLC | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | DisplayName |
Value: MCLC 1.6.10 | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | UninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\MCLC\Uninstall MCLC.exe" /currentuser | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | QuietUninstallString |
Value: "C:\Users\admin\AppData\Local\Programs\MCLC\Uninstall MCLC.exe" /currentuser /S | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | DisplayVersion |
Value: 1.6.10 | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\Programs\MCLC\MCLC.exe,0 | |||
| (PID) Process: | (4852) MCLC-setup.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\41fd615f-5dcf-5cd9-9744-a0db54a54655 |
| Operation: | write | Name: | Publisher |
Value: MCLC Team | |||
Executable files
31
Suspicious files
216
Text files
552
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1e52d1.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1e52f0.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1e52e0.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1e52e0.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1e52f0.TMP | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7392 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
99
TCP/UDP connections
95
DNS requests
90
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
9048 | msedge.exe | GET | 302 | 104.26.3.143:443 | https://cdn.tailwindcss.com/ | unknown | — | — | whitelisted |
9048 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:xfAYovDN8p61rCcKdL5_3gpPdjXjo2Jqei3m7xmLQxQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
9048 | msedge.exe | GET | 200 | 104.21.29.219:443 | https://mclc.pluginhub.de/ | unknown | html | 21.5 Kb | unknown |
9048 | msedge.exe | GET | 200 | 104.21.29.219:443 | https://mclc.pluginhub.de/resources/icon.png?v=2 | unknown | image | 1.00 Mb | unknown |
9048 | msedge.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/font-awesome/6.0.0/css/all.min.css | unknown | text | 87.1 Kb | unknown |
9048 | msedge.exe | GET | 200 | 142.251.141.170:443 | https://fonts.googleapis.com/css2?family=Outfit:wght@300;400;600;700;800&family=Poppins:ital,wght@0,100;0,200;0,300;0,400;0,500;0,600;0,700;0,800;0,900;1,100;1,200;1,300;1,400;1,500;1,600;1,700;1,800;1,900&display=swap | unknown | text | 25.2 Kb | whitelisted |
9048 | msedge.exe | GET | 200 | 104.26.3.143:443 | https://cdn.tailwindcss.com/3.4.17 | unknown | text | 397 Kb | whitelisted |
9048 | msedge.exe | GET | 200 | 2.16.204.157:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | text | 665 Kb | whitelisted |
356 | svchost.exe | GET | 200 | 162.159.142.9:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAz1vQYrVgL0erhQLCPM8GY%3D | unknown | — | — | whitelisted |
9048 | msedge.exe | GET | 200 | 104.17.25.14:443 | https://cdnjs.cloudflare.com/ajax/libs/font-awesome/6.0.0/webfonts/fa-brands-400.woff2 | unknown | binary | 102 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
8756 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7240 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5568 | SearchApp.exe | 2.16.204.157:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
3412 | svchost.exe | 172.211.123.249:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
9048 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
9048 | msedge.exe | 150.171.28.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
9048 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
self.events.data.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mclc.pluginhub.de |
| unknown |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
9048 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
9048 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
9048 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
9048 | msedge.exe | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
9048 | msedge.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
6768 | MoUsoCoreWorker.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |