| download: | trn10oem.exe |
| Full analysis: | https://app.any.run/tasks/5d805ead-055a-4f75-96ea-cb045f64c762 |
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2018, 12:32:52 |
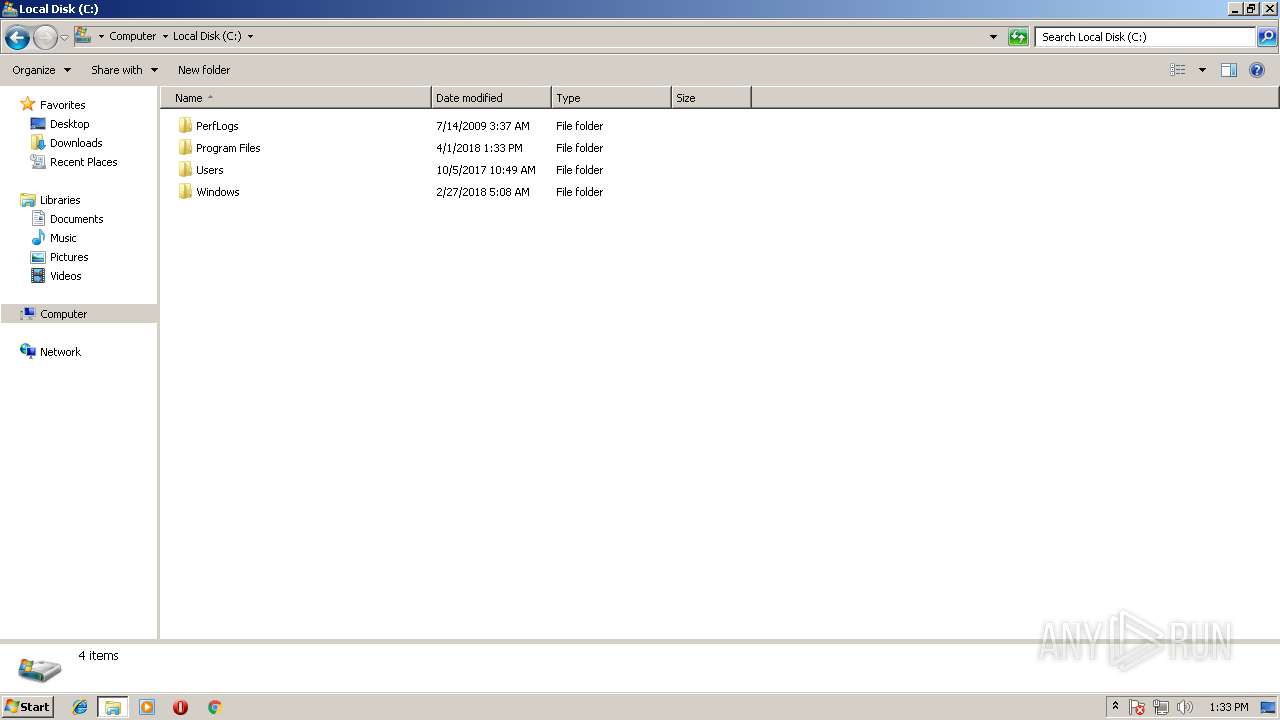
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed, RAR self-extracting archive |
| MD5: | 554D57DDE72FAF55303E0C6F7A791C68 |
| SHA1: | B9420109AF74B7AD9057FFCEF5EB9F9A66E5278E |
| SHA256: | 2AEB6DC783F20CED29892FF9AEC7FE13E6EDF8D63D66A0AA3E2867AB7BF7522F |
| SSDEEP: | 49152:belg1EGD0ziN0guYcKeJacau56QNGRoAZHHU0OnO0fcaBYc+s+0PmogM:qlns0zetOK9Fy6QNGOdEagdnM |
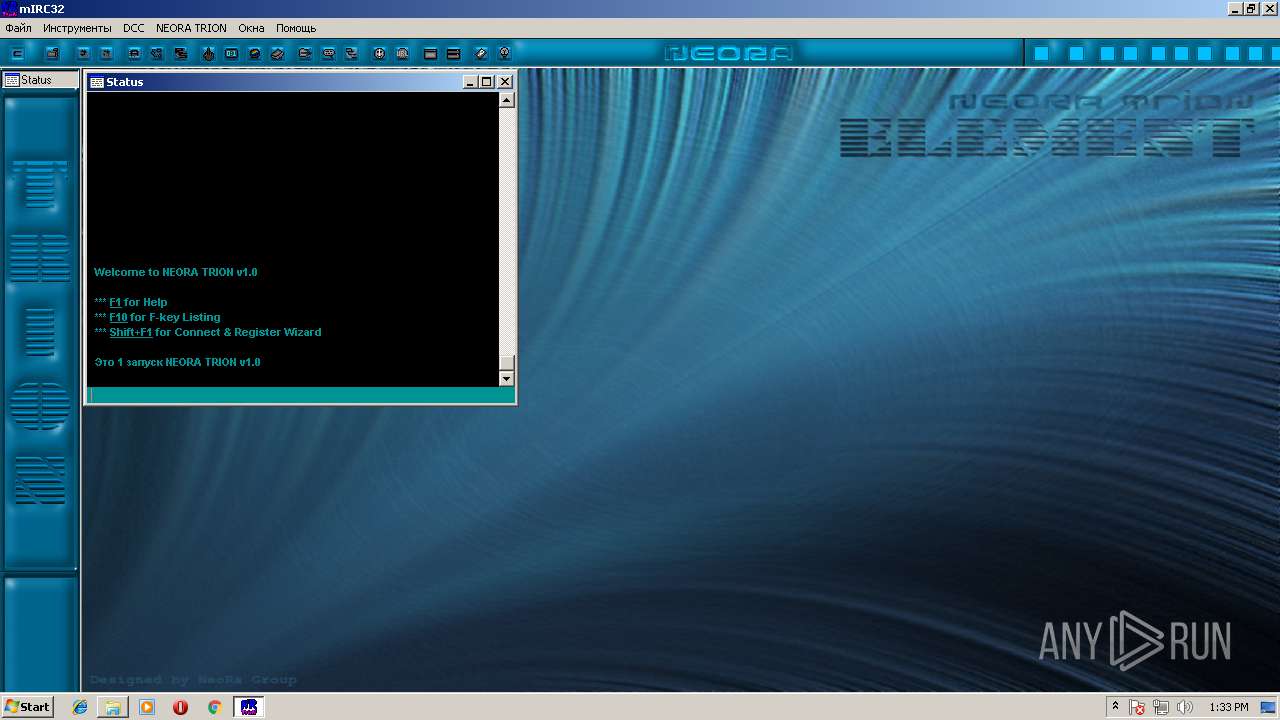
MALICIOUS
Application was dropped or rewritten from another process
- mirc32.exe (PID: 276)
SUSPICIOUS
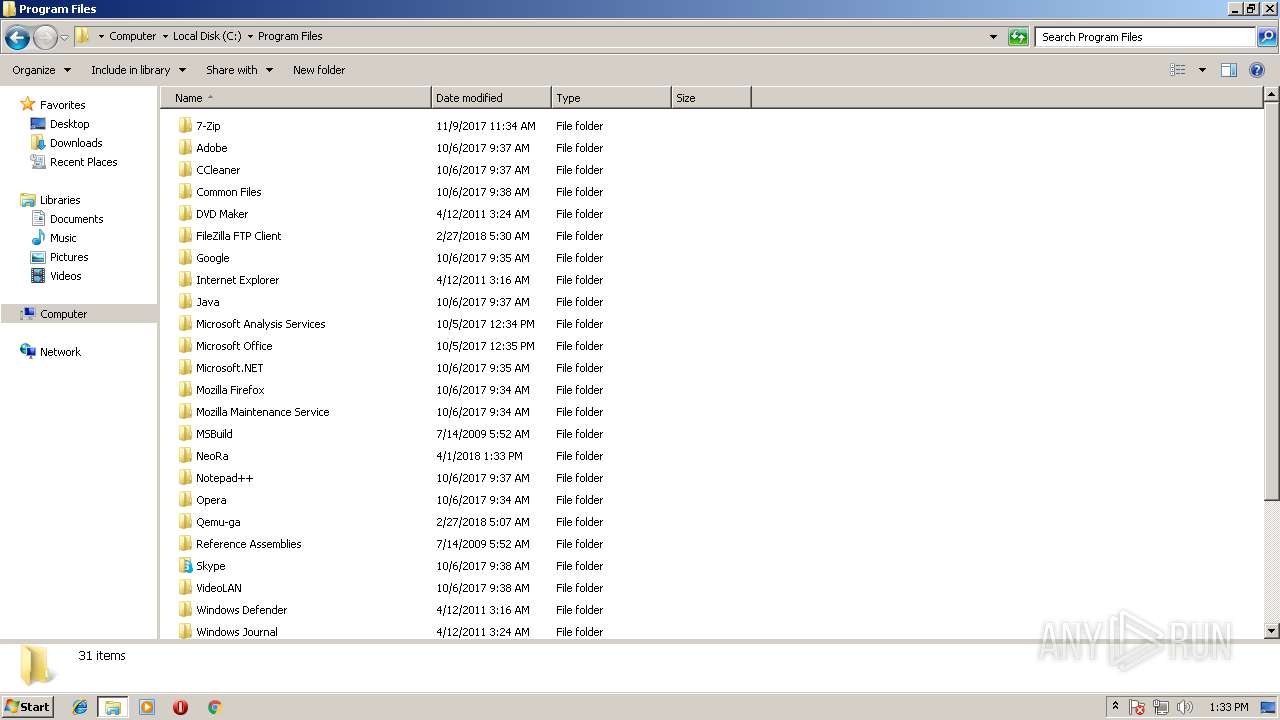
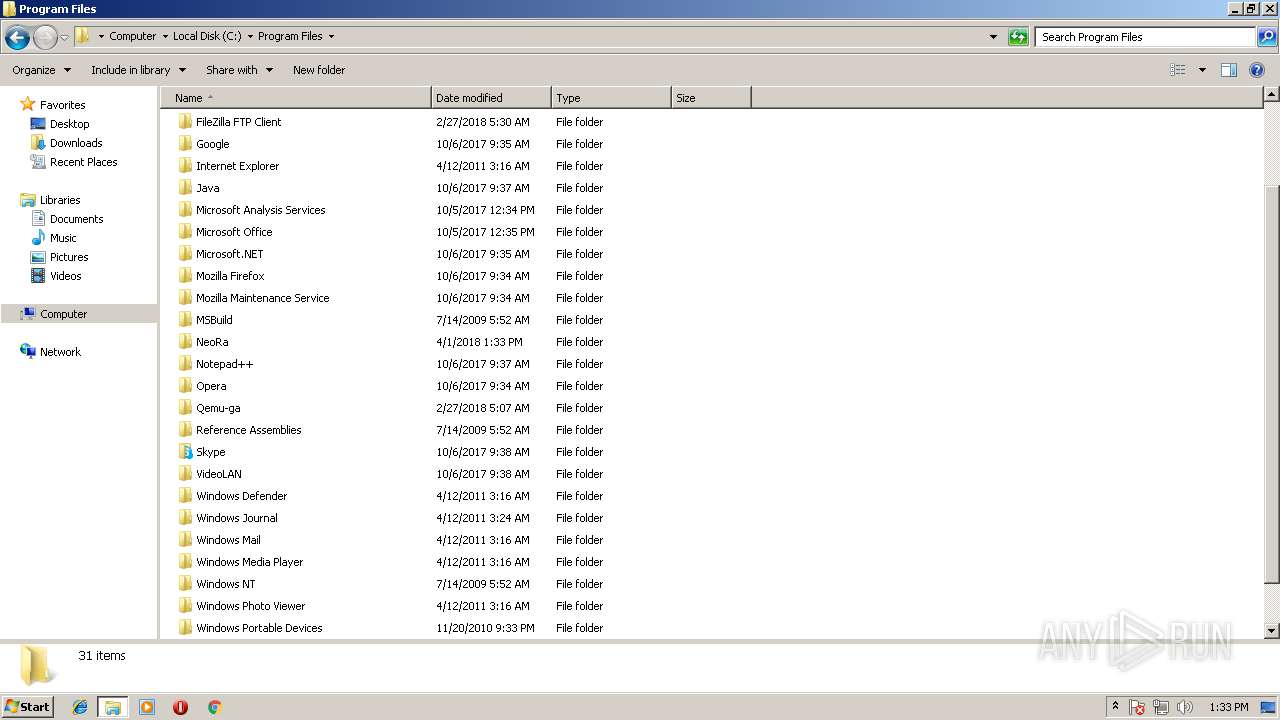
Creates files in the program directory
- mirc32.exe (PID: 276)
- trn10oem.exe (PID: 2188)
INFO
Loads rich edit control libraries
- trn10oem.exe (PID: 2188)
- mirc32.exe (PID: 276)
Dropped object may contain URL's
- trn10oem.exe (PID: 2188)
- mirc32.exe (PID: 276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | WinRAR Self Extracting archive (88.2) |
|---|---|---|
| .exe | | | UPX compressed Win32 Executable (4.6) |
| .exe | | | Win32 EXE Yoda's Crypter (4.5) |
| .dll | | | Win32 Dynamic Link Library (generic) (1.1) |
| .exe | | | Win32 Executable (generic) (0.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2001:02:27 12:02:00+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 5 |
| CodeSize: | 20480 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 57344 |
| EntryPoint: | 0x13200 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Feb-2001 11:02:00 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000200 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 27-Feb-2001 11:02:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0000F000 | 0x00005000 | 0x00004400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.86692 |
.rsrc | 0x00014000 | 0x00002000 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.609 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.34153 | 296 | UNKNOWN | Ukrainian - Ukraine | RT_ICON |
2 | 4.10013 | 744 | UNKNOWN | Ukrainian - Ukraine | RT_ICON |
3 | 4.68705 | 2216 | UNKNOWN | Ukrainian - Ukraine | RT_ICON |
7 | 7.51909 | 596 | UNKNOWN | Ukrainian - Ukraine | RT_STRING |
8 | 7.69333 | 998 | UNKNOWN | Ukrainian - Ukraine | RT_STRING |
9 | 7.47785 | 464 | UNKNOWN | Ukrainian - Ukraine | RT_STRING |
10 | 7.53908 | 556 | UNKNOWN | Ukrainian - Ukraine | RT_STRING |
100 | 2.63597 | 48 | UNKNOWN | Ukrainian - Ukraine | RT_GROUP_ICON |
GETPASSWORD1 | 7.13635 | 310 | UNKNOWN | Ukrainian - Ukraine | RT_DIALOG |
LICENSEDLG | 7.01191 | 226 | UNKNOWN | Ukrainian - Ukraine | RT_DIALOG |
Imports
ADVAPI32.DLL |
GDI32.DLL |
KERNEL32.DLL |
SHELL32.DLL |
USER32.DLL |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
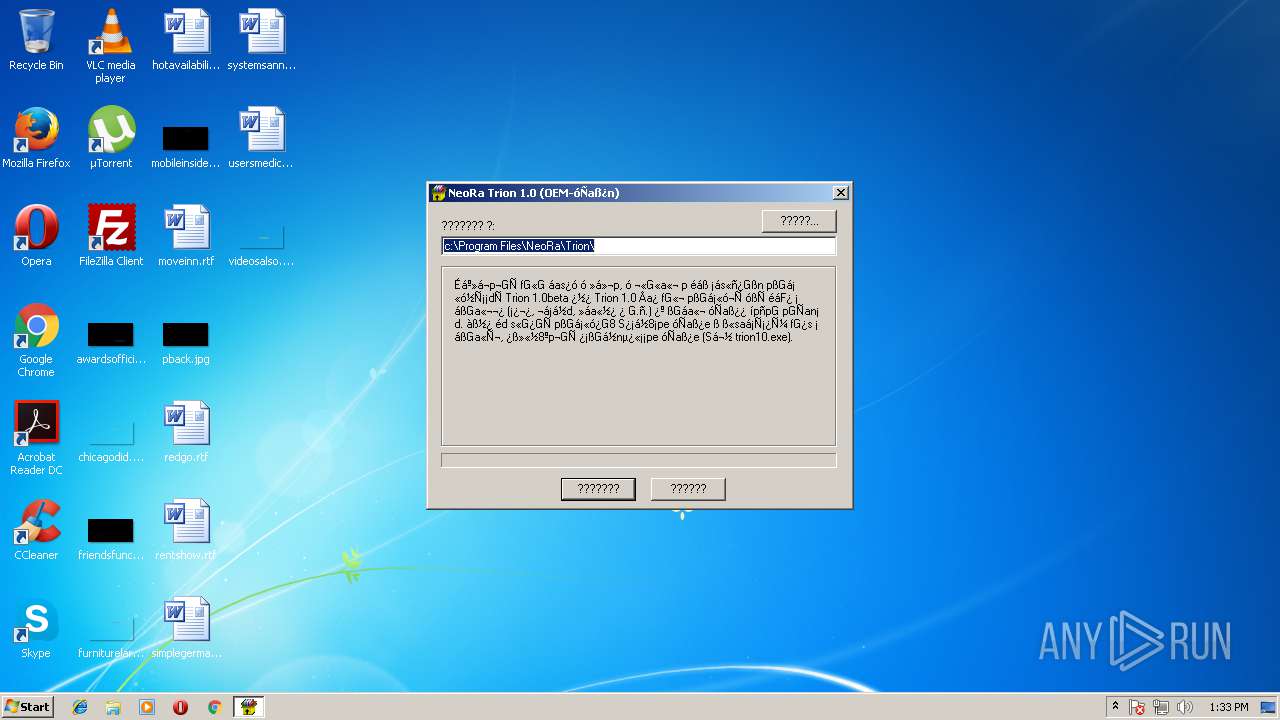
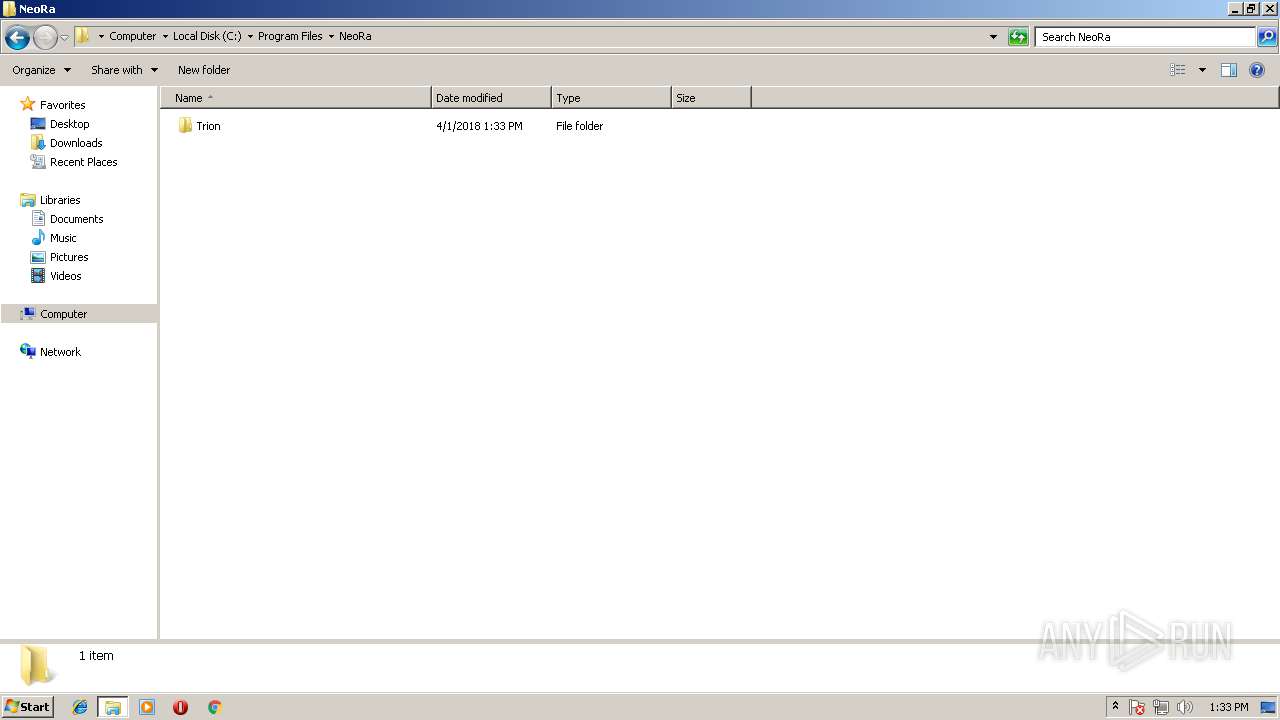
| 276 | "C:\Program Files\NeoRa\Trion\mirc32.exe" | C:\Program Files\NeoRa\Trion\mirc32.exe | — | explorer.exe | |||||||||||
User: admin Company: mIRC Co. Ltd. Integrity Level: MEDIUM Description: mIRC Exit code: 0 Version: 5.9 Modules
| |||||||||||||||
| 588 | "C:\Users\admin\AppData\Local\Temp\trn10oem.exe" | C:\Users\admin\AppData\Local\Temp\trn10oem.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 2188 | "C:\Users\admin\AppData\Local\Temp\trn10oem.exe" | C:\Users\admin\AppData\Local\Temp\trn10oem.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2300 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
30
Read events
29
Write events
1
Delete events
0
Modification events
| (PID) Process: | (276) mirc32.exe | Key: | HKEY_CURRENT_USER\Software\mIRC\DateUsed |
| Operation: | write | Name: | |
Value: 1522586036 | |||
Executable files
1
Suspicious files
16
Text files
132
Unknown types
46
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\logs\LogMNGer.txt | — | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\Wiz6.jpg | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\mirc.ini | text | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col11.BMP | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col1.BMP | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col2.BMP | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col12.BMP | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col13.BMP | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col14.BMP | image | |
MD5:— | SHA256:— | |||
| 2188 | trn10oem.exe | C:\Program Files\NeoRa\Trion\Pics\col10.BMP | image | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
3
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 154.35.175.101:6667 | irc.dal.net | Rethem Hosting LLC | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
irc.dal.net |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET CHAT IRC USER command |
— | — | Misc activity | ET CHAT IRC NICK command |
— | — | Misc activity | ET CHAT IRC authorization message |