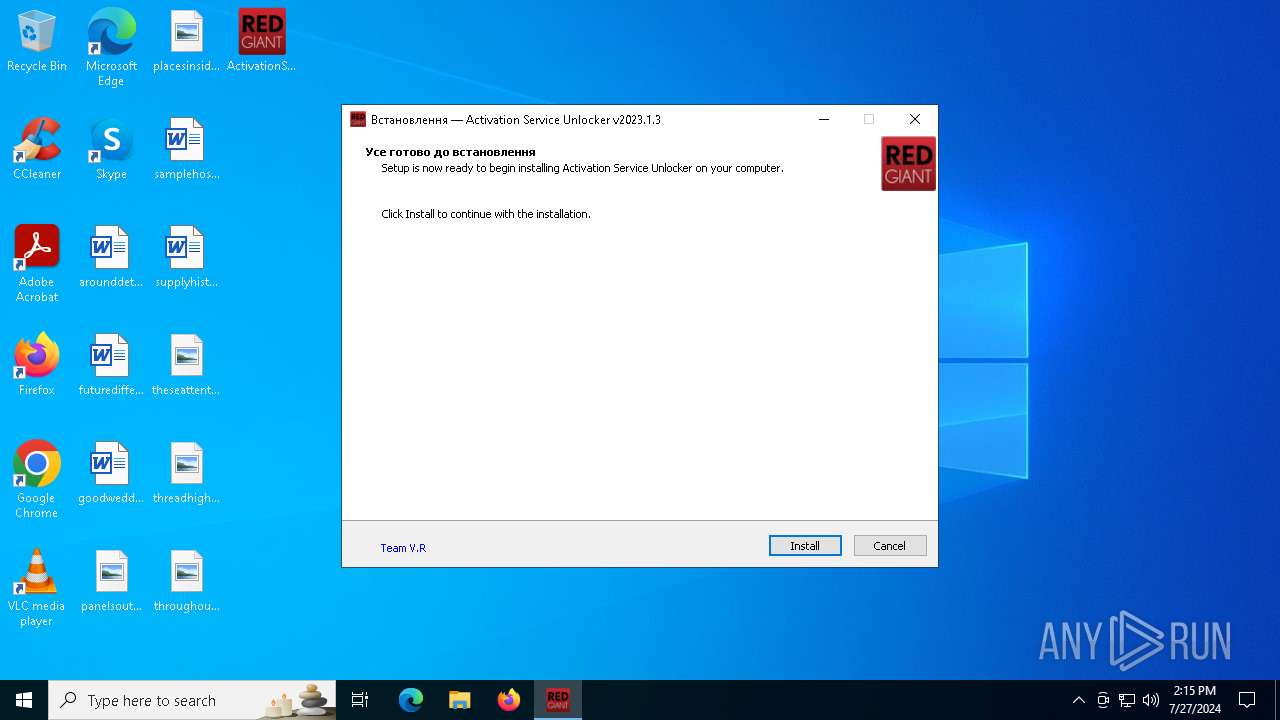
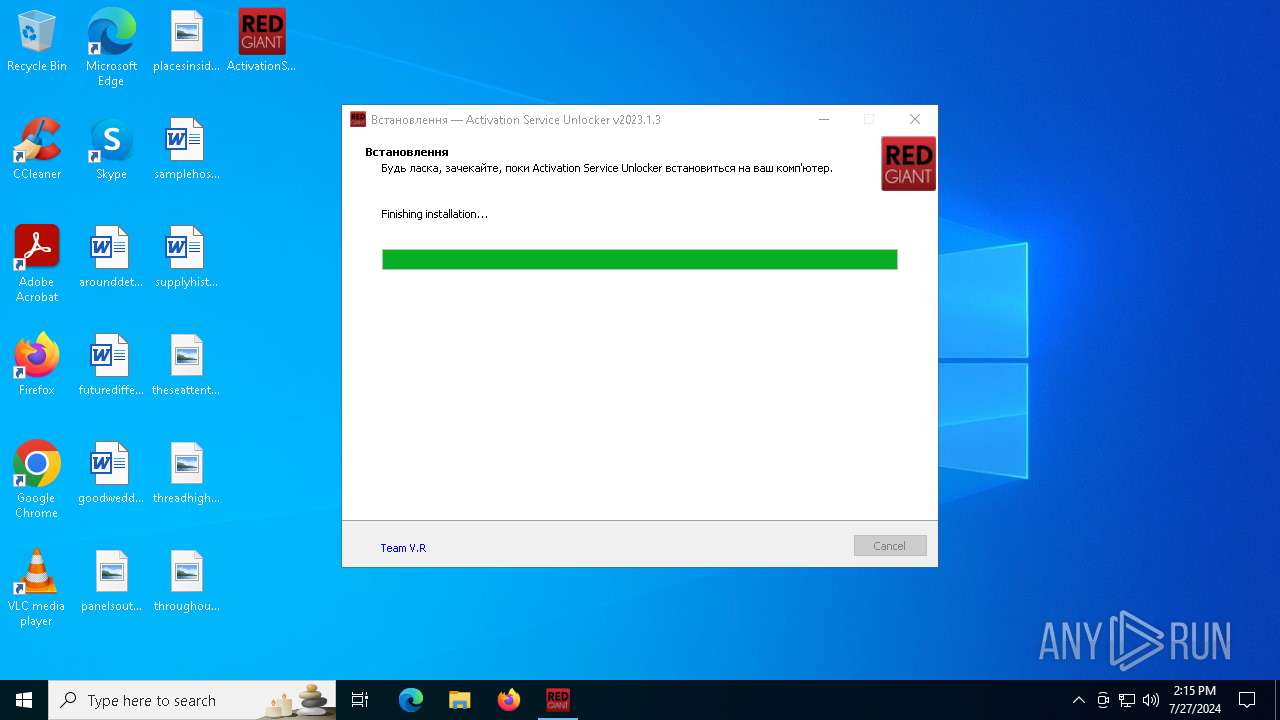
| File name: | ActivationServiceUnlocker2023.1.3.exe |
| Full analysis: | https://app.any.run/tasks/5a10e2e1-2021-4fd6-98b3-23c49f70c414 |
| Verdict: | Malicious activity |
| Analysis date: | July 27, 2024, 14:15:13 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | EE1BFA29F0759F33BBAEA9F282218567 |
| SHA1: | 45CB22EE9A3D56364EEFD2EC7C38CCBB0663EDF6 |
| SHA256: | 2AE8D809D34BEE8D388DA5E741650B97B4B8AE92835AB3C49C6D3984CC14CD10 |
| SSDEEP: | 98304:lSiO9V8LRfMNKYYHl16/Xb/mZOQDNUcQlUcaFW0Qy0ea245j:aKivbP6NUllUZQqIj |
MALICIOUS
Drops the executable file immediately after the start
- ActivationServiceUnlocker2023.1.3.exe (PID: 7076)
- ActivationServiceUnlocker2023.1.3.exe (PID: 6932)
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.exe (PID: 1112)
- deep.tmp (PID: 1272)
Starts NET.EXE for service management
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- net.exe (PID: 2300)
- net.exe (PID: 4500)
- net.exe (PID: 6856)
SUSPICIOUS
Reads security settings of Internet Explorer
- ActivationServiceUnlocker2023.1.3.tmp (PID: 6668)
Reads the date of Windows installation
- ActivationServiceUnlocker2023.1.3.tmp (PID: 6668)
Executable content was dropped or overwritten
- ActivationServiceUnlocker2023.1.3.exe (PID: 7076)
- ActivationServiceUnlocker2023.1.3.exe (PID: 6932)
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.exe (PID: 1112)
- deep.tmp (PID: 1272)
Reads the Windows owner or organization settings
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.tmp (PID: 1272)
Uses TIMEOUT.EXE to delay execution
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
Uses TASKKILL.EXE to kill process
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.tmp (PID: 1272)
INFO
Process checks computer location settings
- ActivationServiceUnlocker2023.1.3.tmp (PID: 6668)
Checks supported languages
- ActivationServiceUnlocker2023.1.3.exe (PID: 6932)
- ActivationServiceUnlocker2023.1.3.tmp (PID: 6668)
- ActivationServiceUnlocker2023.1.3.exe (PID: 7076)
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.exe (PID: 1112)
- deep.tmp (PID: 1272)
Reads the computer name
- ActivationServiceUnlocker2023.1.3.tmp (PID: 6668)
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.tmp (PID: 1272)
Create files in a temporary directory
- ActivationServiceUnlocker2023.1.3.exe (PID: 7076)
- ActivationServiceUnlocker2023.1.3.exe (PID: 6932)
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.tmp (PID: 1272)
- deep.exe (PID: 1112)
Creates files in the program directory
- ActivationServiceUnlocker2023.1.3.tmp (PID: 5296)
- deep.tmp (PID: 1272)
Checks proxy server information
- slui.exe (PID: 7100)
Reads the software policy settings
- slui.exe (PID: 7100)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2021:06:05 15:54:43+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 741376 |
| InitializedDataSize: | 57344 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xb5eec |
| OSVersion: | 6.1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2023.1.3.0 |
| ProductVersionNumber: | 2023.1.3.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Red Giant, LLC |
| FileDescription: | Activation Service Unlocker Setup |
| FileVersion: | 2023.1.3 |
| LegalCopyright: | © Red Giant LLC |
| OriginalFileName: | |
| ProductName: | Activation Service Unlocker |
| ProductVersion: | 2023.1.3 |
Total processes
157
Monitored processes
24
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1112 | "C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\deep.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\deep.exe | ActivationServiceUnlocker2023.1.3.tmp | ||||||||||||
User: admin Company: Red Giant, LLC Integrity Level: HIGH Description: Activation Service Unlocker Setup Exit code: 0 Version: 2023.1.3 Modules
| |||||||||||||||
| 1272 | "C:\Users\admin\AppData\Local\Temp\is-BKDSP.tmp\deep.tmp" /SL5="$1202A2,3598703,799744,C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\deep.exe" /verysilent | C:\Users\admin\AppData\Local\Temp\is-BKDSP.tmp\deep.tmp | deep.exe | ||||||||||||
User: admin Company: Red Giant, LLC Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 2300 | "C:\WINDOWS\system32\net.exe" stop "Red Giant Service" | C:\Windows\System32\net.exe | — | ActivationServiceUnlocker2023.1.3.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2328 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | timeout.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2368 | C:\WINDOWS\system32\net1 stop mxredirect | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2376 | "C:\WINDOWS\system32\taskkill.exe" /f /im maxon.exe | C:\Windows\System32\taskkill.exe | — | deep.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2380 | C:\WINDOWS\system32\net1 stop "Red Giant Service" | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 2 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2672 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2988 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3848 | "C:\WINDOWS\system32\taskkill.exe" /f /im "RGContentService.exe" | C:\Windows\System32\taskkill.exe | — | ActivationServiceUnlocker2023.1.3.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 224
Read events
6 200
Write events
12
Delete events
12
Modification events
| (PID) Process: | (5296) ActivationServiceUnlocker2023.1.3.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: B0140000B529C16E2FE0DA01 | |||
| (PID) Process: | (5296) ActivationServiceUnlocker2023.1.3.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1E7BB4817EED3EFD1B43C8357918B416924D9470FC5C602AB1FEAEB68C01ED80 | |||
| (PID) Process: | (5296) ActivationServiceUnlocker2023.1.3.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (5296) ActivationServiceUnlocker2023.1.3.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\deep.exe | |||
| (PID) Process: | (5296) ActivationServiceUnlocker2023.1.3.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 617B3709CAB3DB56E78536A514FE48013C2C8EECA7B967DB4153C631F8044B4C | |||
| (PID) Process: | (1272) deep.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Owner |
Value: F80400002ABF90722FE0DA01 | |||
| (PID) Process: | (1272) deep.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | SessionHash |
Value: 5D3CBDC374FD39B60D120C30CD836DDF5CC3D69A5AF84153F5C40BF0B141C4E3 | |||
| (PID) Process: | (1272) deep.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (1272) deep.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Red Giant\Services\Red Giant Service.exe | |||
| (PID) Process: | (1272) deep.tmp | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\RestartManager\Session0001 |
| Operation: | write | Name: | RegFilesHash |
Value: 5552F2A583D5F82C0D299BA4A2348615439073A7520BD595845ED63156318A39 | |||
Executable files
11
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6932 | ActivationServiceUnlocker2023.1.3.exe | C:\Users\admin\AppData\Local\Temp\is-7TQPI.tmp\ActivationServiceUnlocker2023.1.3.tmp | executable | |
MD5:A5ECAEE602A2196E4F26C09976C5934C | SHA256:76AA359896801DF734425BA007F3080E7E08E9CC307BF3B3CC796ED104E0594B | |||
| 7076 | ActivationServiceUnlocker2023.1.3.exe | C:\Users\admin\AppData\Local\Temp\is-4LO5U.tmp\ActivationServiceUnlocker2023.1.3.tmp | executable | |
MD5:A5ECAEE602A2196E4F26C09976C5934C | SHA256:76AA359896801DF734425BA007F3080E7E08E9CC307BF3B3CC796ED104E0594B | |||
| 5296 | ActivationServiceUnlocker2023.1.3.tmp | C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\deep.exe | executable | |
MD5:1236D7FA121E89A15EB8762E027D87D0 | SHA256:C6F14962863E54092B2A719D4AAEC866511F5943B0E8F9ED48180ECC21D5630B | |||
| 5296 | ActivationServiceUnlocker2023.1.3.tmp | C:\ProgramData\Maxon\RLM\vr.lic | text | |
MD5:683896C6A48196B6597116AA99823530 | SHA256:63931D59B463CECA304853DE2E6C68526F975D6B530EFB17A98801896C412F56 | |||
| 5296 | ActivationServiceUnlocker2023.1.3.tmp | C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\_isetup\_iscrypt.dll | executable | |
MD5:A69559718AB506675E907FE49DEB71E9 | SHA256:2F6294F9AA09F59A574B5DCD33BE54E16B39377984F3D5658CDA44950FA0F8FC | |||
| 5296 | ActivationServiceUnlocker2023.1.3.tmp | C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 5296 | ActivationServiceUnlocker2023.1.3.tmp | C:\ProgramData\Maxon\RLM\is-QT4EP.tmp | text | |
MD5:683896C6A48196B6597116AA99823530 | SHA256:63931D59B463CECA304853DE2E6C68526F975D6B530EFB17A98801896C412F56 | |||
| 5296 | ActivationServiceUnlocker2023.1.3.tmp | C:\Users\admin\AppData\Local\Temp\is-6NOJH.tmp\is-G6HKD.tmp | executable | |
MD5:1236D7FA121E89A15EB8762E027D87D0 | SHA256:C6F14962863E54092B2A719D4AAEC866511F5943B0E8F9ED48180ECC21D5630B | |||
| 1112 | deep.exe | C:\Users\admin\AppData\Local\Temp\is-BKDSP.tmp\deep.tmp | executable | |
MD5:A5ECAEE602A2196E4F26C09976C5934C | SHA256:76AA359896801DF734425BA007F3080E7E08E9CC307BF3B3CC796ED104E0594B | |||
| 1272 | deep.tmp | C:\Program Files\Red Giant\Services\is-7V019.tmp | executable | |
MD5:C41F0C9EDD42533A2E9DF4BB5936FF48 | SHA256:87BDA1EAB6783E941387B646D5BBA0F0428E38A8EB73AE7BCD3AB2B60AAB128C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
21
DNS requests
7
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | POST | 200 | 52.182.143.209:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
— | — | POST | 200 | 52.168.112.66:443 | https://self.events.data.microsoft.com/OneCollector/1.0/ | US | binary | 9 b | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4128 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 92.123.104.14:443 | www.bing.com | Akamai International B.V. | DE | unknown |
— | — | 131.253.33.254:443 | a-ring-fallback.msedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2856 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6012 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2616 | RUXIMICS.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3952 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2432 | slui.exe | 20.83.72.98:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
t-ring-fdv2.msedge.net |
| unknown |
a-ring-fallback.msedge.net |
| unknown |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |