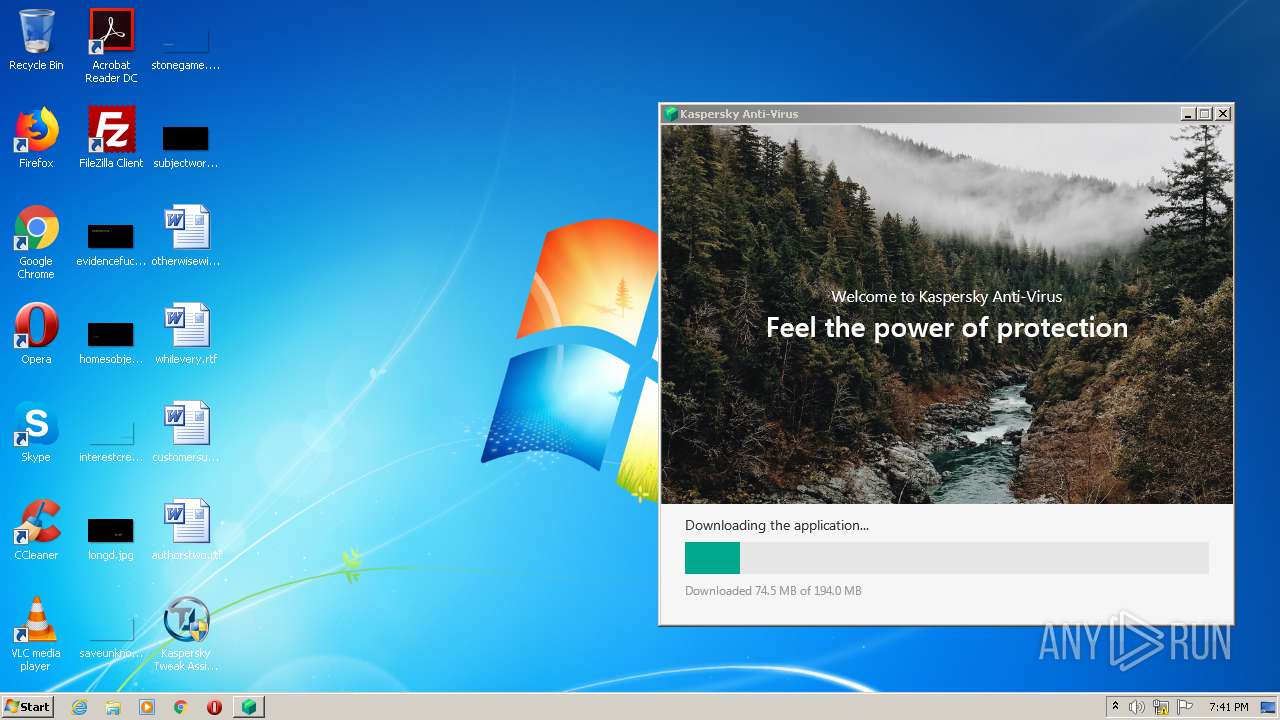
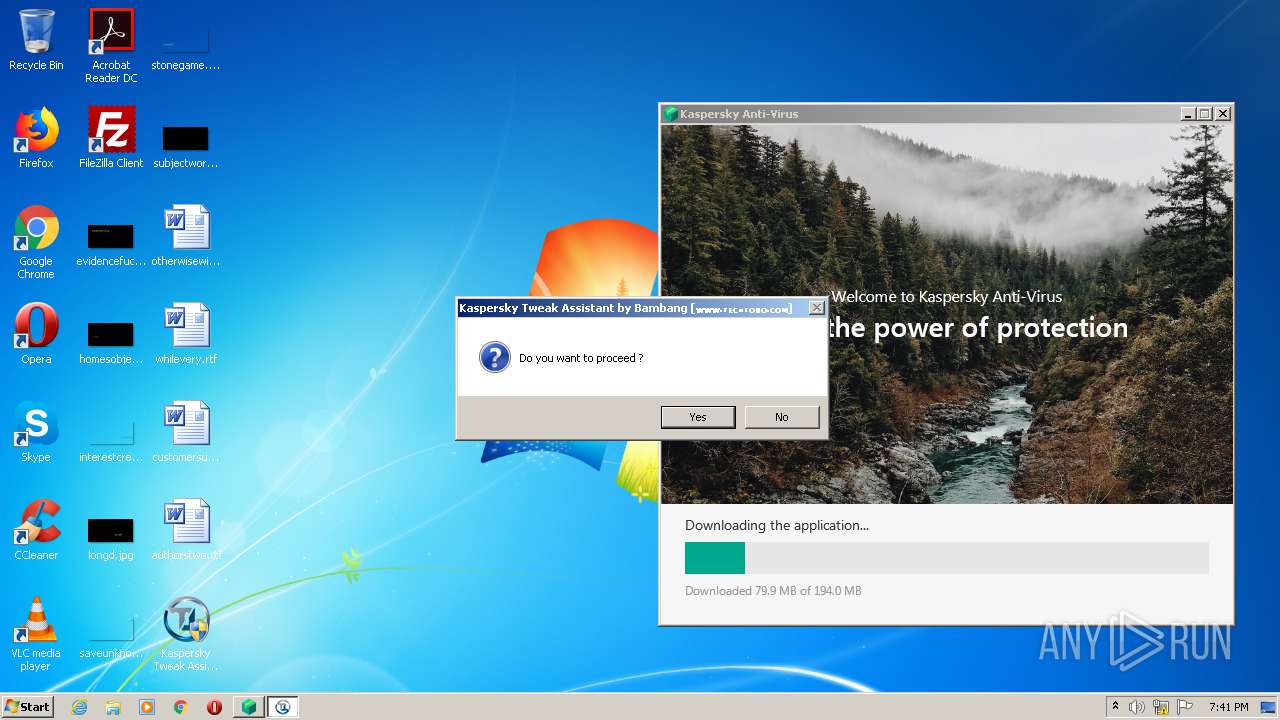
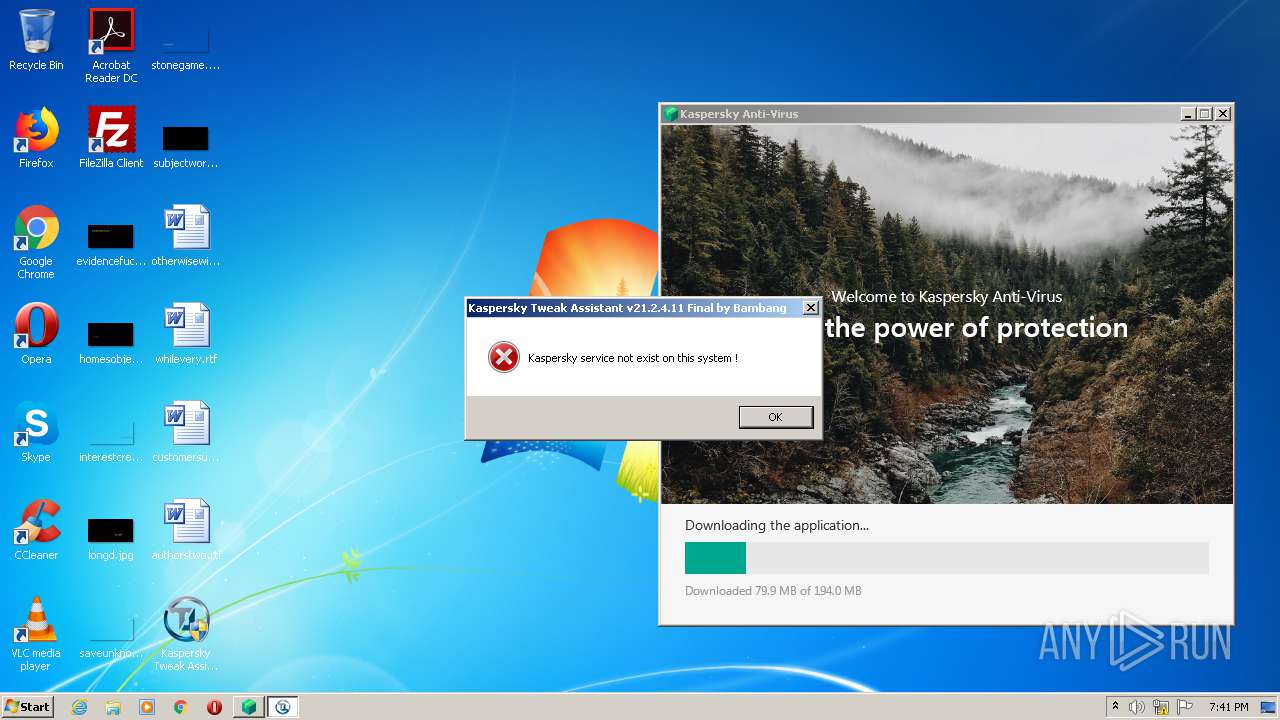
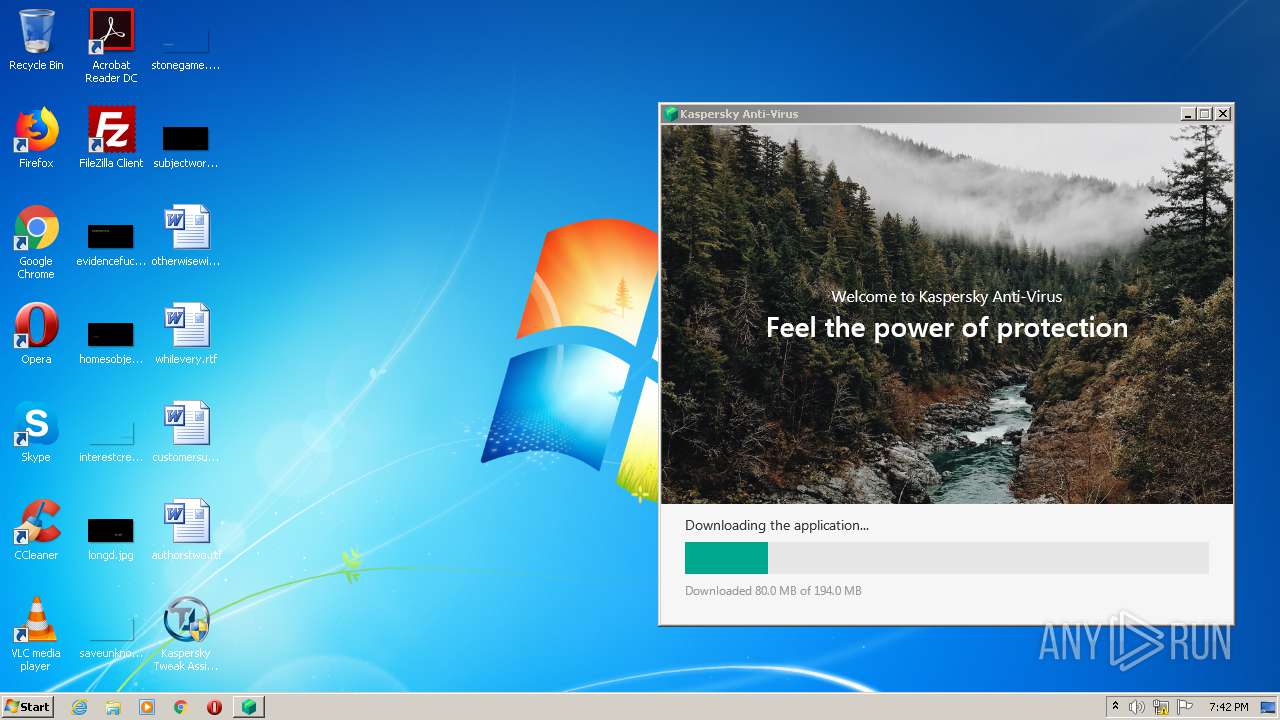
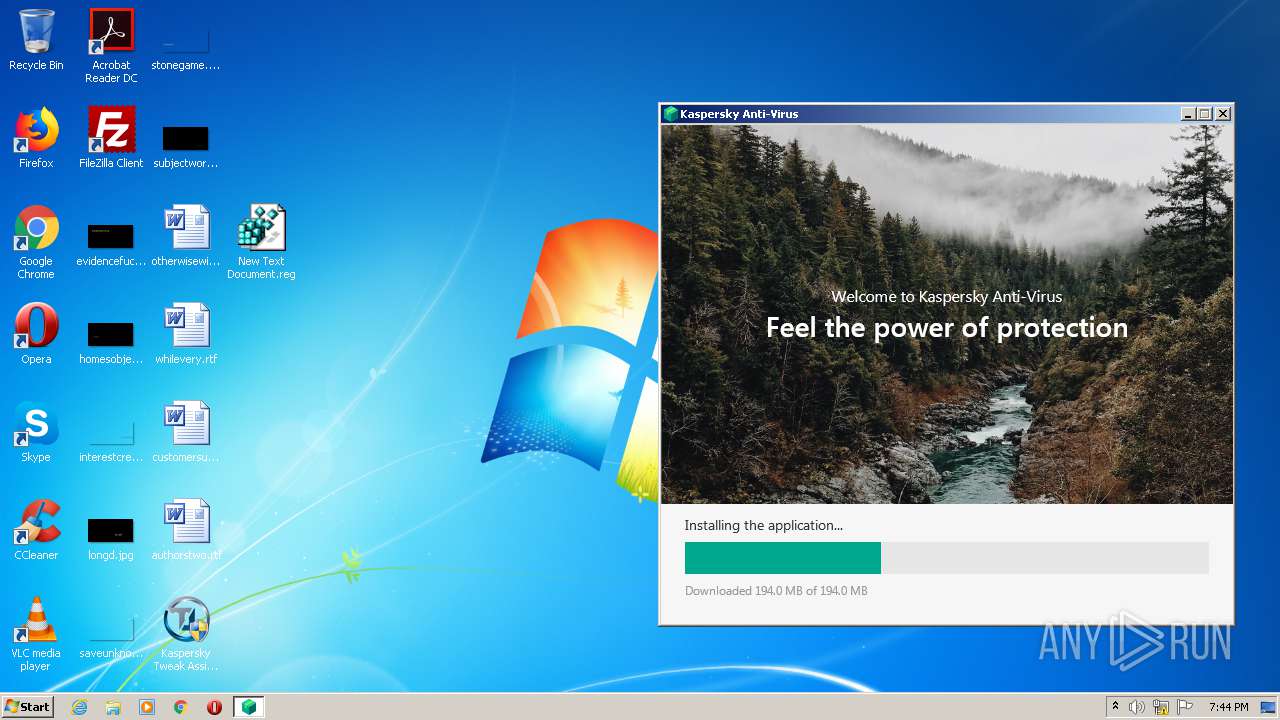
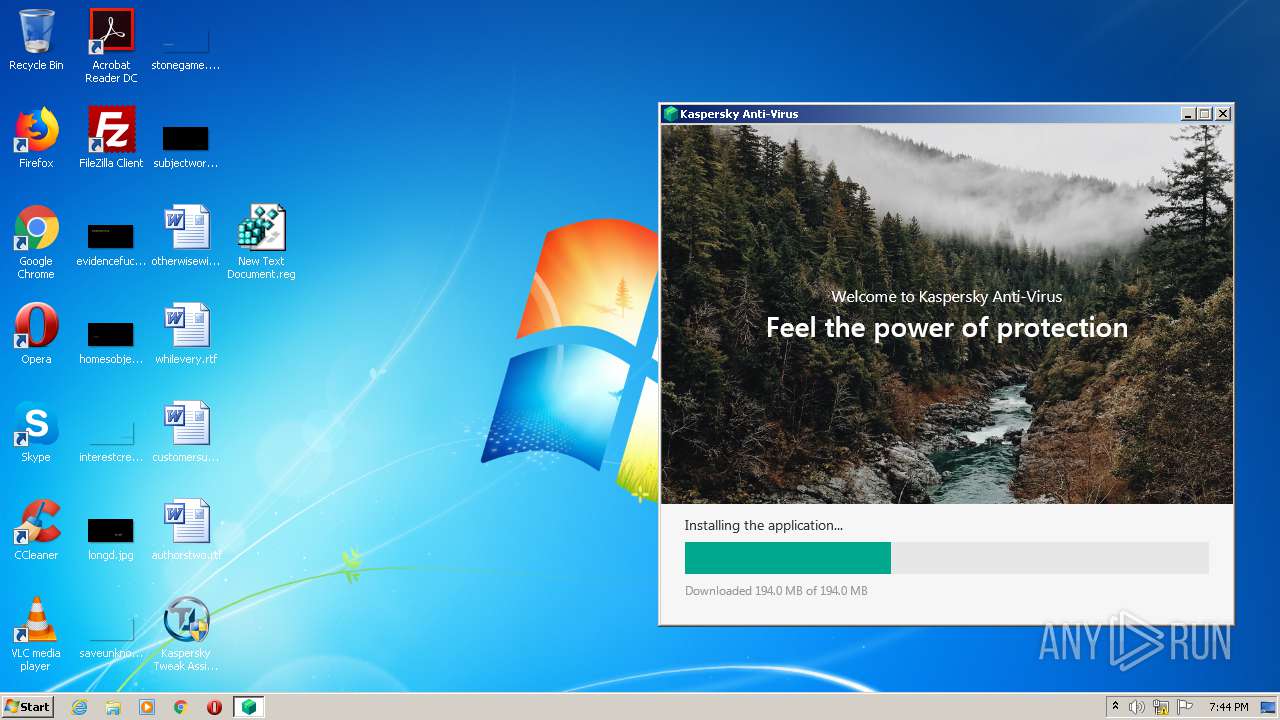
| File name: | Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe |
| Full analysis: | https://app.any.run/tasks/81424fa2-132e-4097-ad61-87076b297c6d |
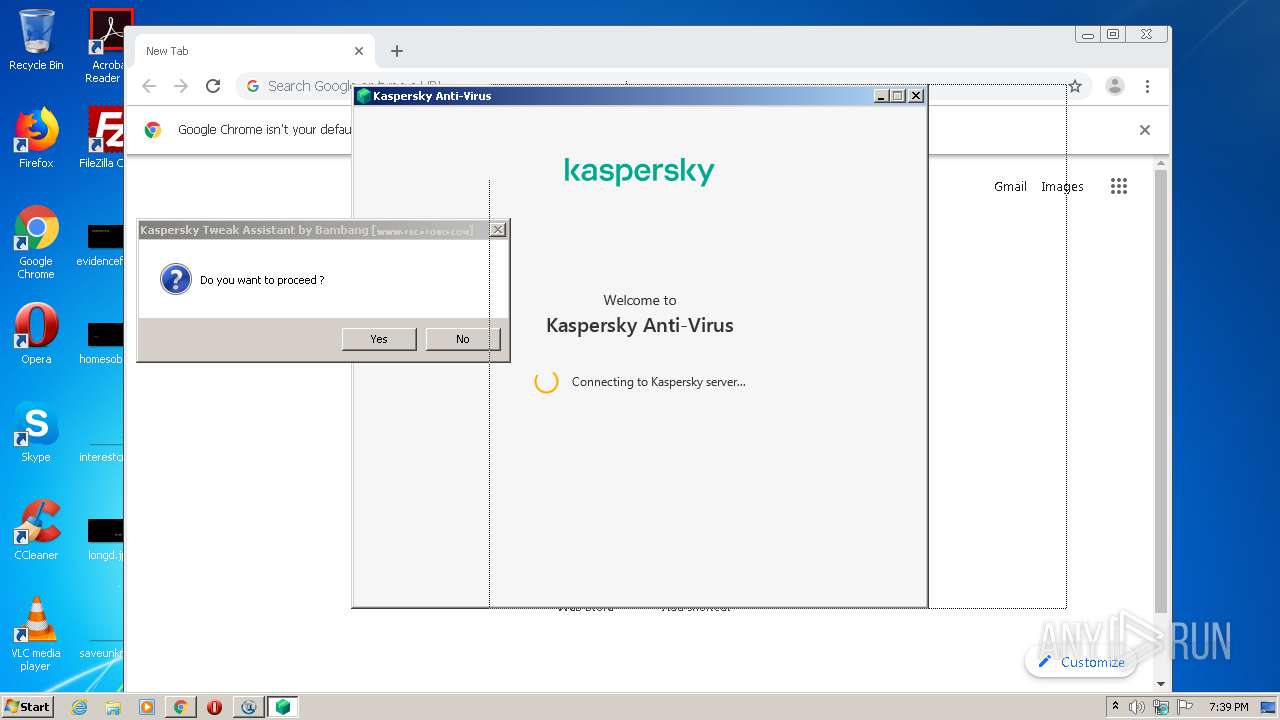
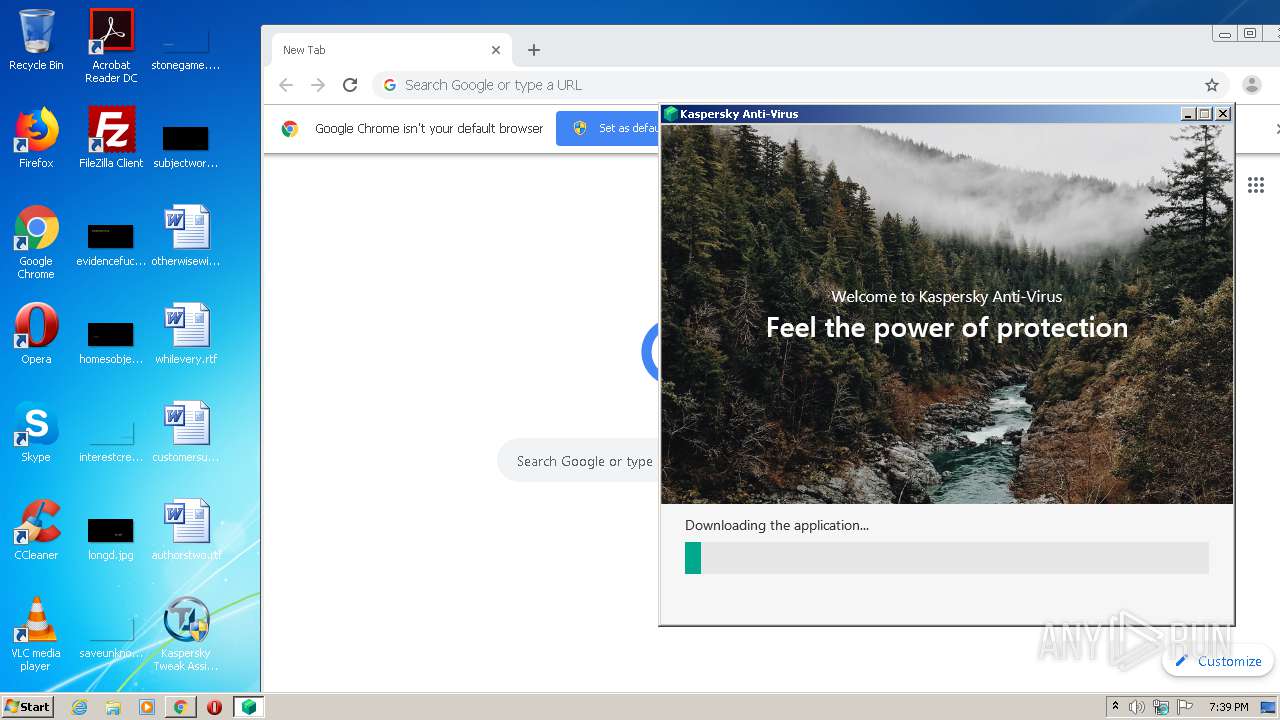
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2021, 19:38:42 |
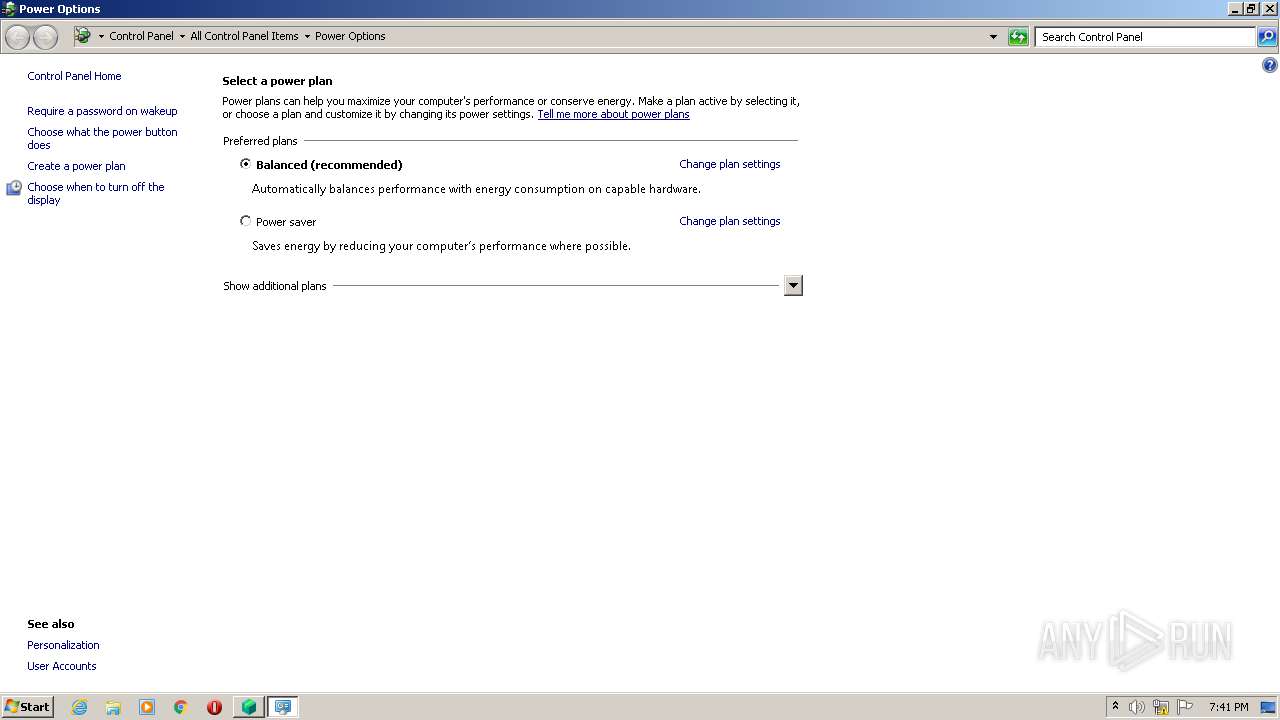
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 476ABA0D7DBF198D2988591A79DA8D2C |
| SHA1: | 17A45550465B481842C2E5B8DFEB45D059129D33 |
| SHA256: | 2ACBC29704B797ED85BDA3C204B092A78B4D371D20BCA2ADE2292EAFA196B85B |
| SSDEEP: | 98304:GLOY4Z9IOZmwWYjbB1zYjt4xMJHFZrG0RTj0Pfryr+wFe:G8PZxbEjtoQHFpGWGyHF |
MALICIOUS
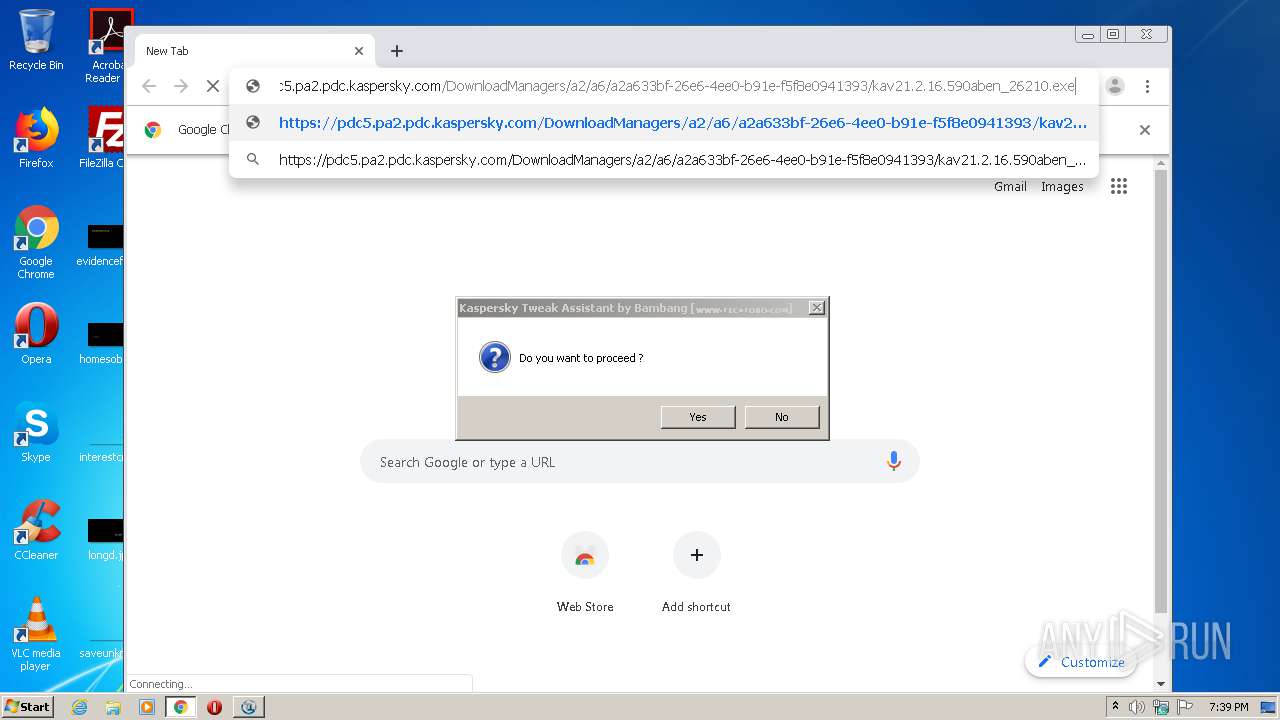
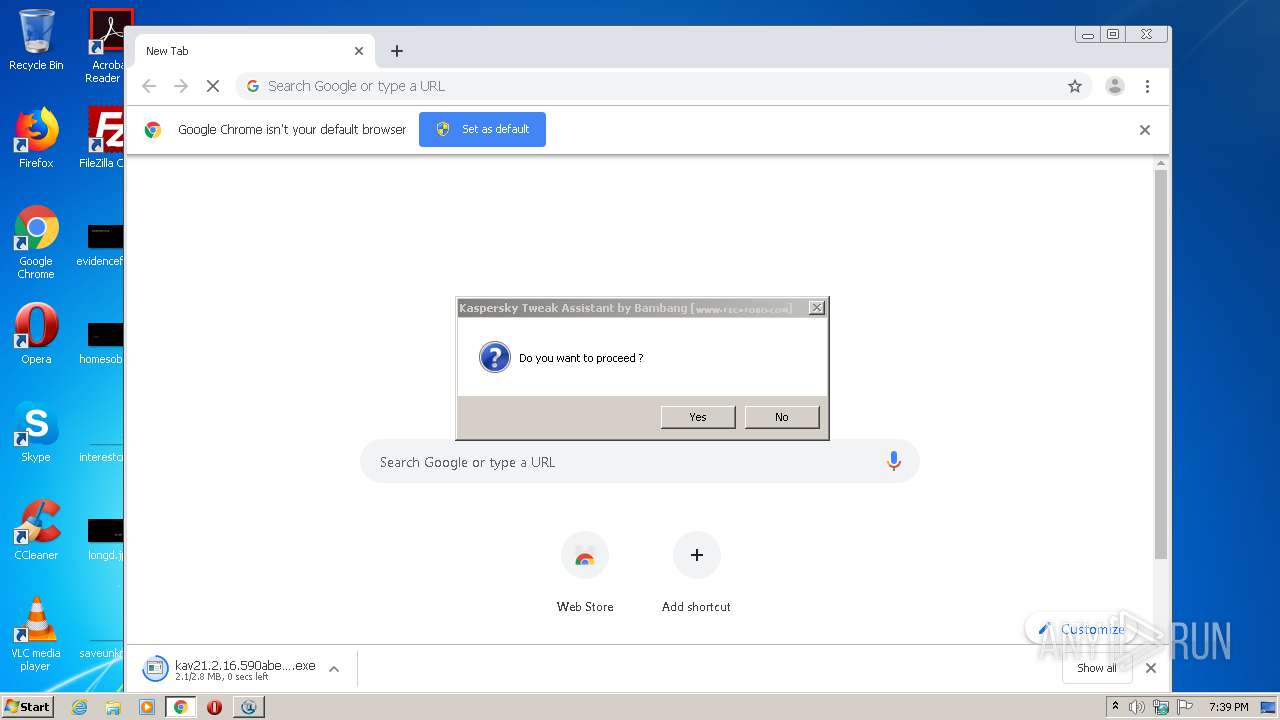
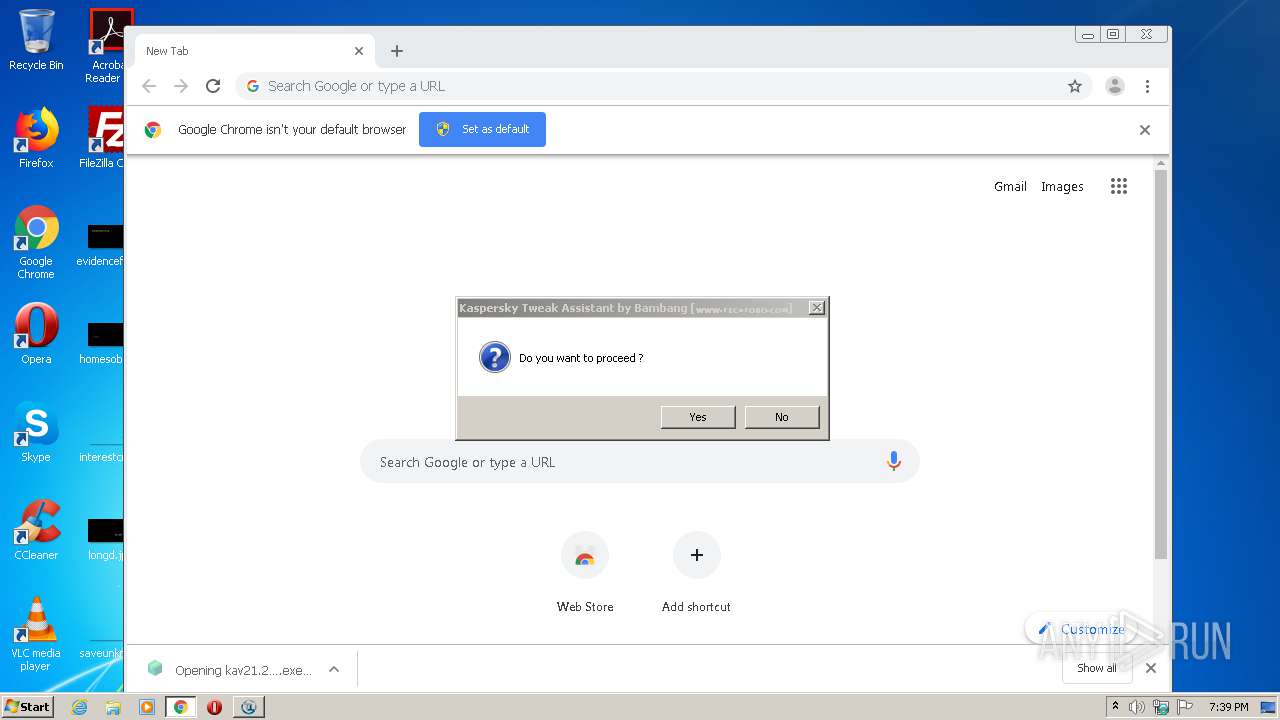
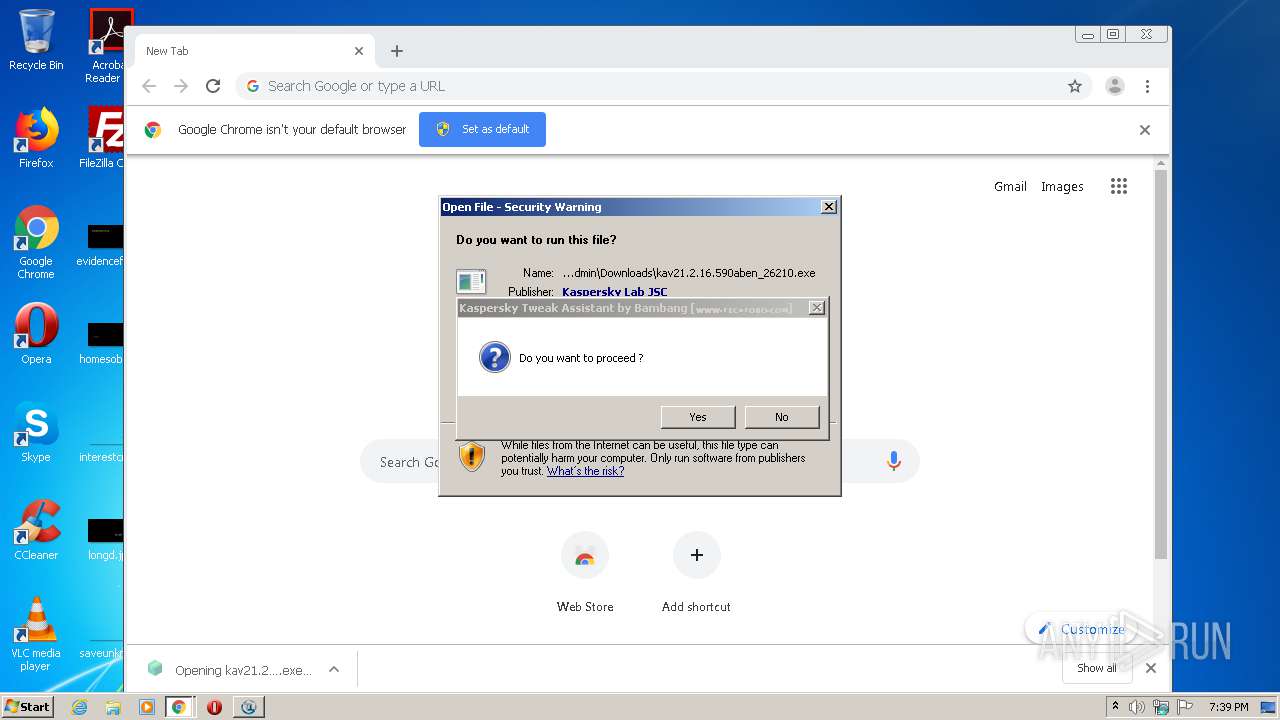
Application was dropped or rewritten from another process
- kav21.2.16.590aben_26210.exe (PID: 2444)
- kav21.2.16.590aben_26210.exe (PID: 2168)
- TEST_WPF.EXE (PID: 3820)
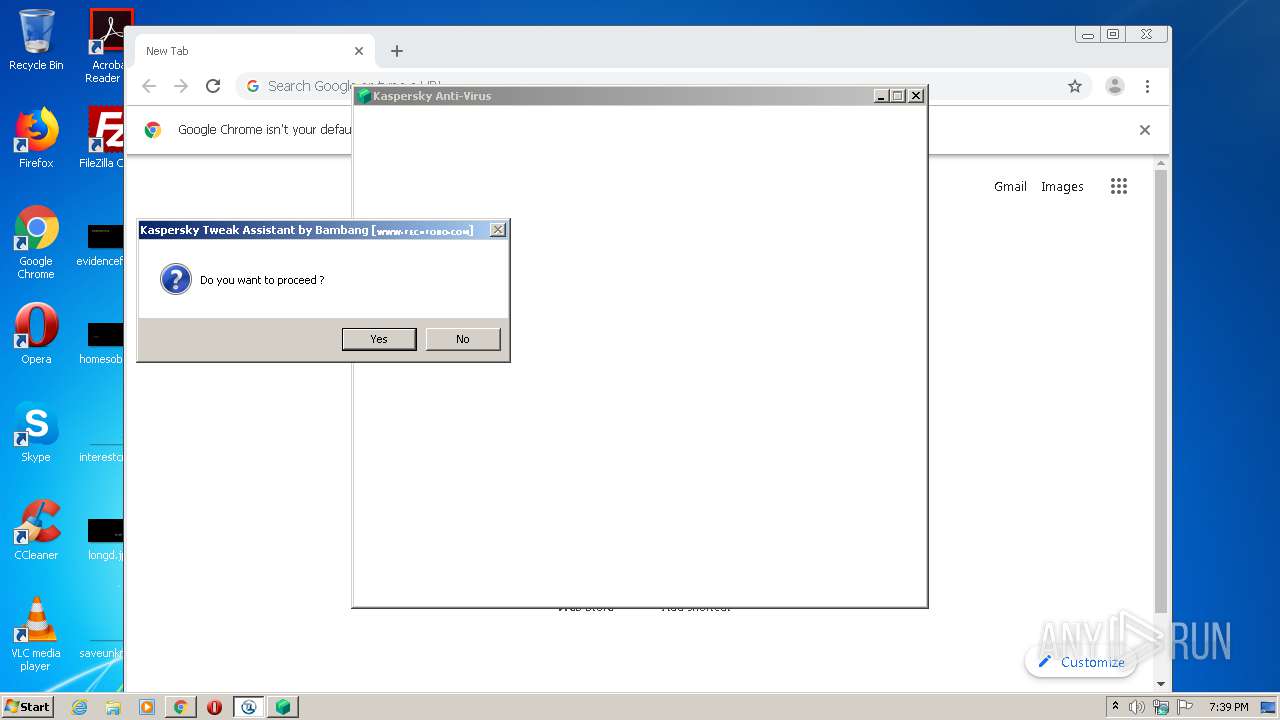
Loads dropped or rewritten executable
- kav21.2.16.590aben_26210.exe (PID: 2444)
- kav21.2.16.590aben_26210.exe (PID: 2168)
- TEST_WPF.EXE (PID: 3820)
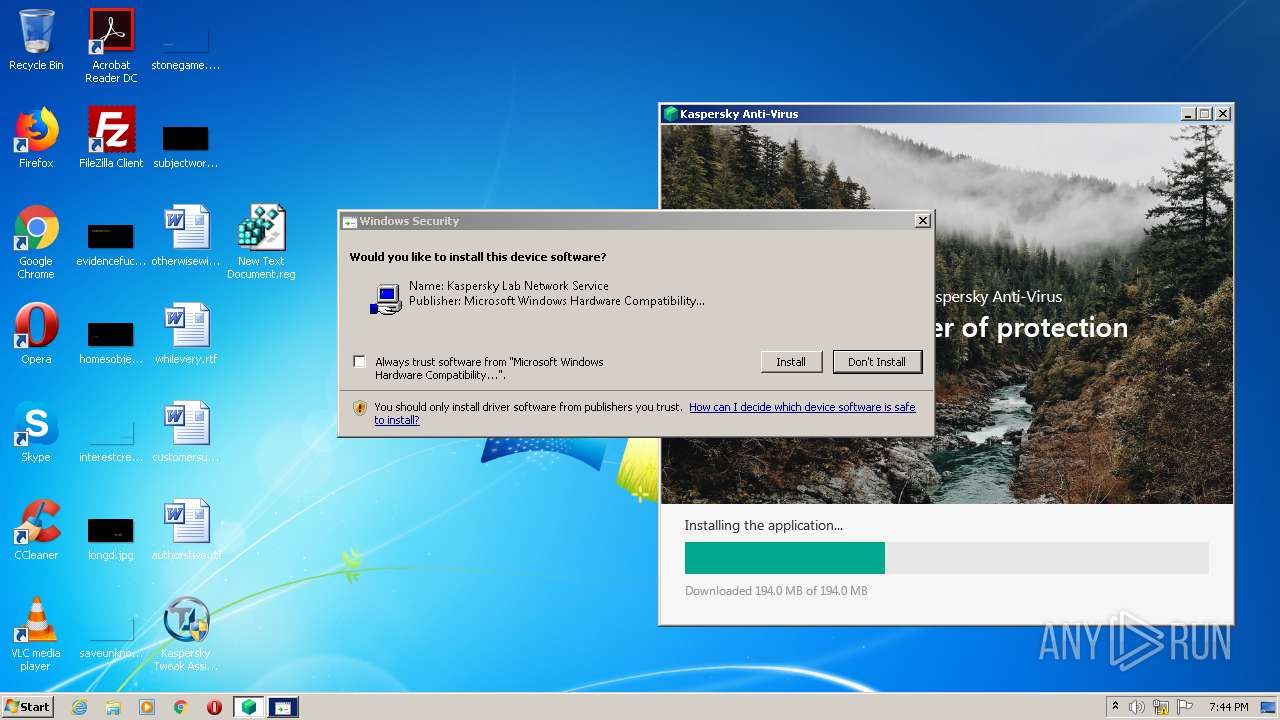
Changes settings of System certificates
- kav21.2.16.590aben_26210.exe (PID: 2168)
- MsiExec.exe (PID: 396)
Drops executable file immediately after starts
- MsiExec.exe (PID: 3416)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 1704)
- chrome.exe (PID: 1648)
- kav21.2.16.590aben_26210.exe (PID: 2444)
- kav21.2.16.590aben_26210.exe (PID: 2168)
- MsiExec.exe (PID: 3416)
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 396)
- DrvInst.exe (PID: 3392)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1704)
- chrome.exe (PID: 1648)
- kav21.2.16.590aben_26210.exe (PID: 2444)
- kav21.2.16.590aben_26210.exe (PID: 2168)
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 3416)
- MsiExec.exe (PID: 396)
- DrvInst.exe (PID: 3392)
Drops a file with a compile date too recent
- chrome.exe (PID: 1648)
- chrome.exe (PID: 1704)
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 396)
Creates files in the user directory
- kav21.2.16.590aben_26210.exe (PID: 2444)
Drops a file with too old compile date
- kav21.2.16.590aben_26210.exe (PID: 2444)
- kav21.2.16.590aben_26210.exe (PID: 2168)
- MsiExec.exe (PID: 396)
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 3416)
- DrvInst.exe (PID: 3392)
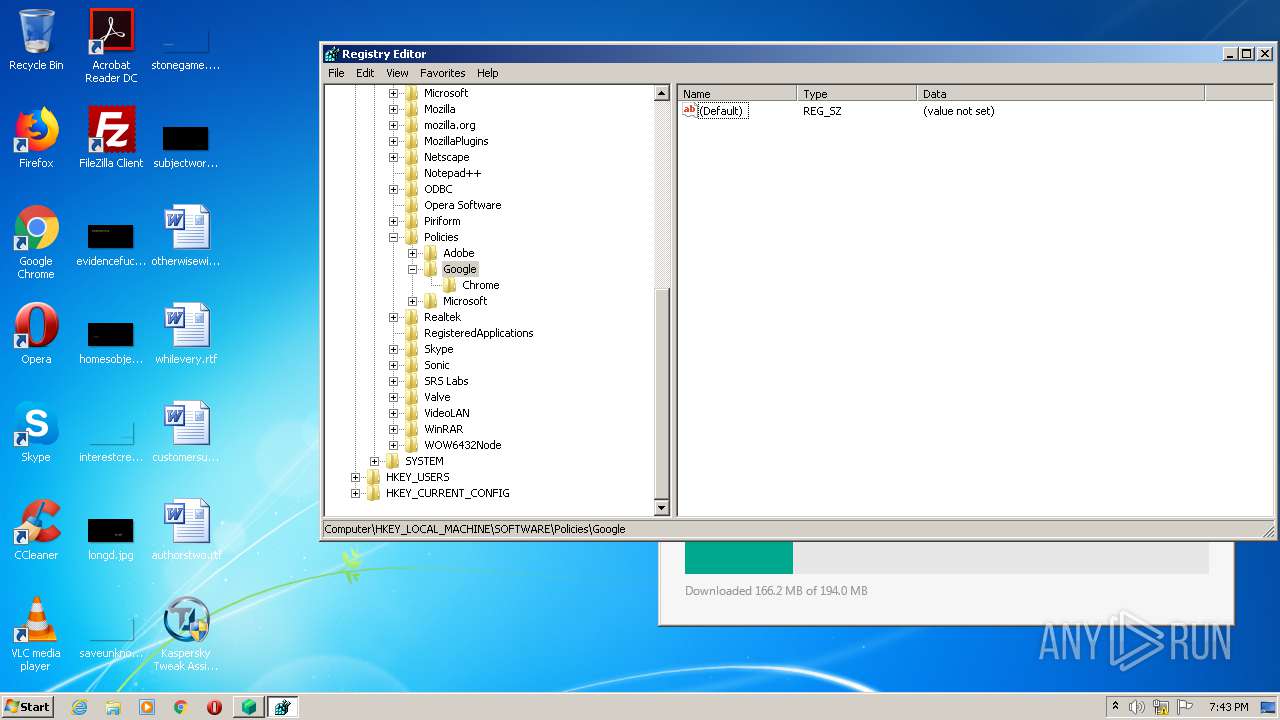
Modifies files in Chrome extension folder
- chrome.exe (PID: 1704)
Application launched itself
- kav21.2.16.590aben_26210.exe (PID: 2444)
Adds / modifies Windows certificates
- kav21.2.16.590aben_26210.exe (PID: 2168)
- MsiExec.exe (PID: 396)
Creates files in the program directory
- kav21.2.16.590aben_26210.exe (PID: 2168)
Creates files in the driver directory
- MsiExec.exe (PID: 3416)
- DrvInst.exe (PID: 3392)
Removes files from Windows directory
- MsiExec.exe (PID: 3416)
- DrvInst.exe (PID: 3392)
Creates files in the Windows directory
- MsiExec.exe (PID: 3416)
- DrvInst.exe (PID: 3392)
- msiexec.exe (PID: 2760)
Creates a directory in Program Files
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 396)
Executed via COM
- DrvInst.exe (PID: 3392)
Uses RUNDLL32.EXE to load library
- DrvInst.exe (PID: 3392)
Executed as Windows Service
- vssvc.exe (PID: 1736)
INFO
Reads settings of System Certificates
- chrome.exe (PID: 1648)
- kav21.2.16.590aben_26210.exe (PID: 2444)
- kav21.2.16.590aben_26210.exe (PID: 2168)
- MsiExec.exe (PID: 396)
- MsiExec.exe (PID: 3416)
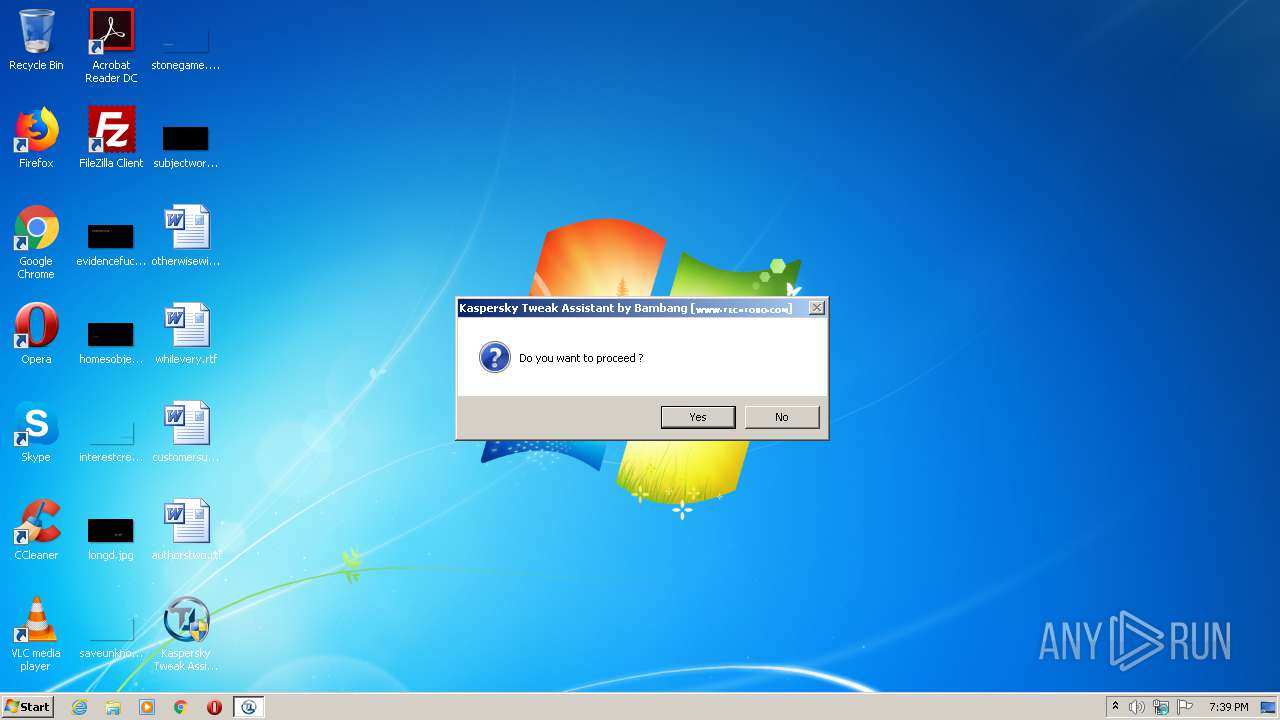
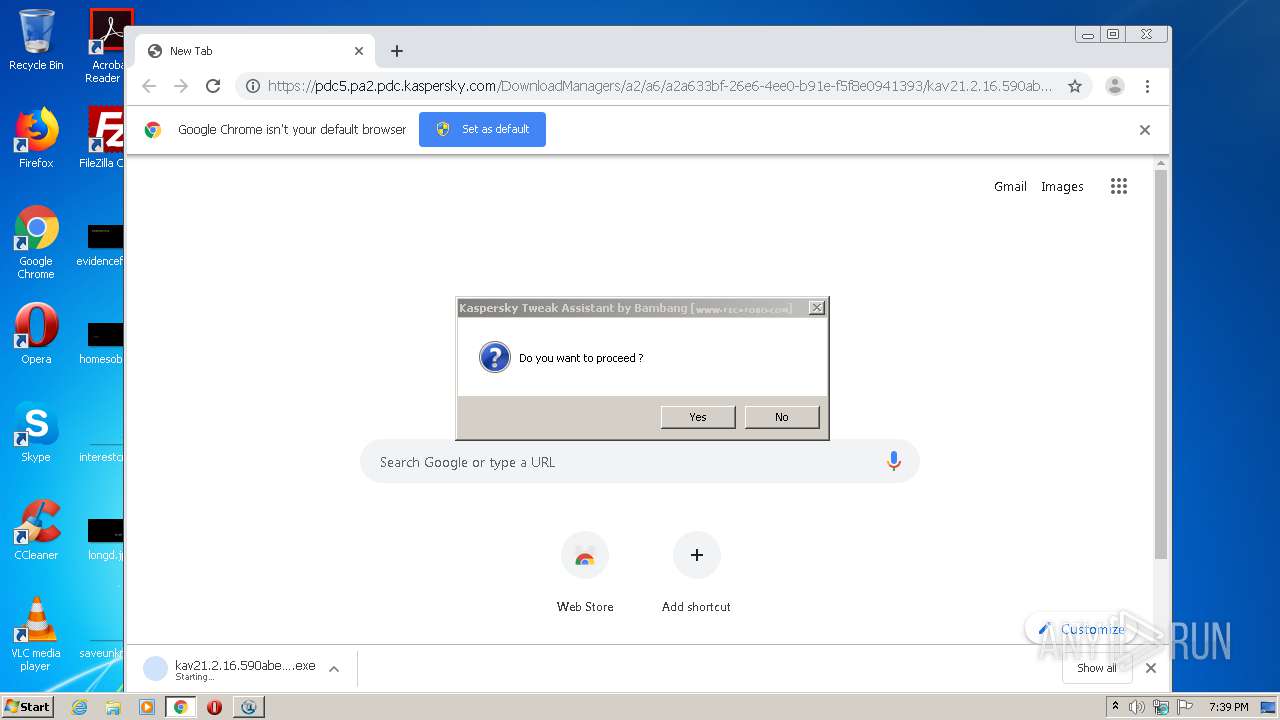
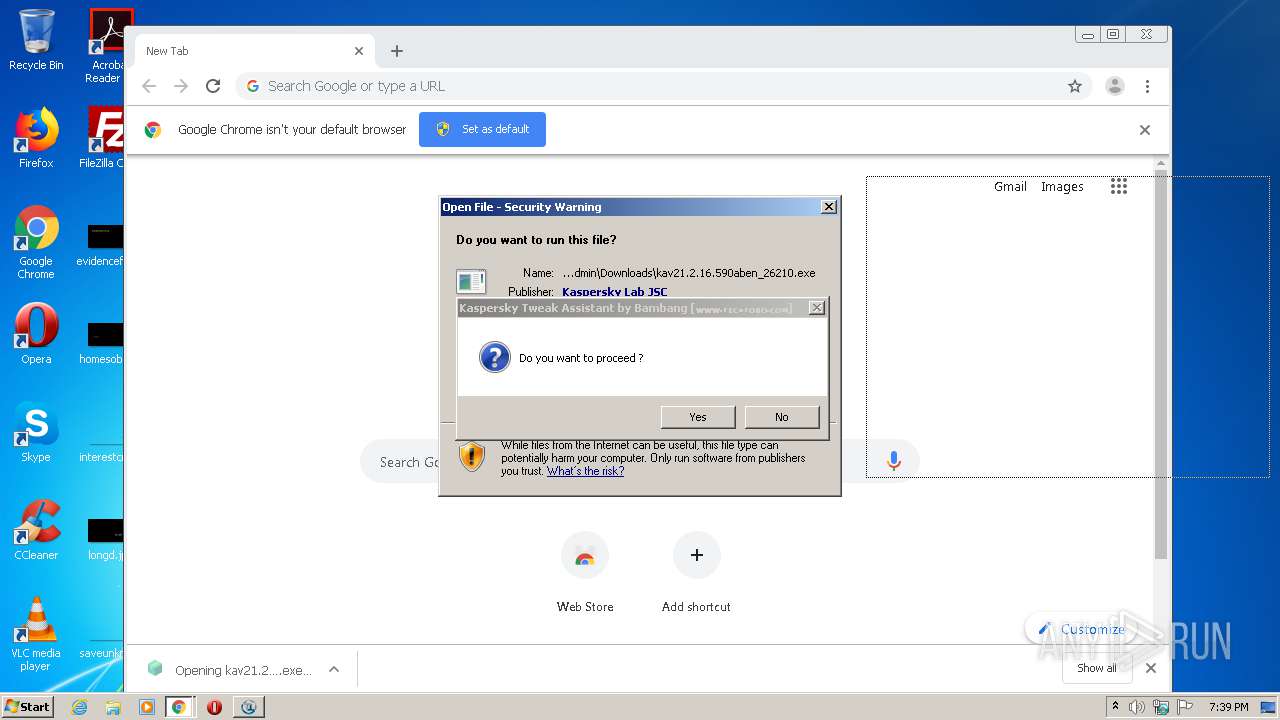
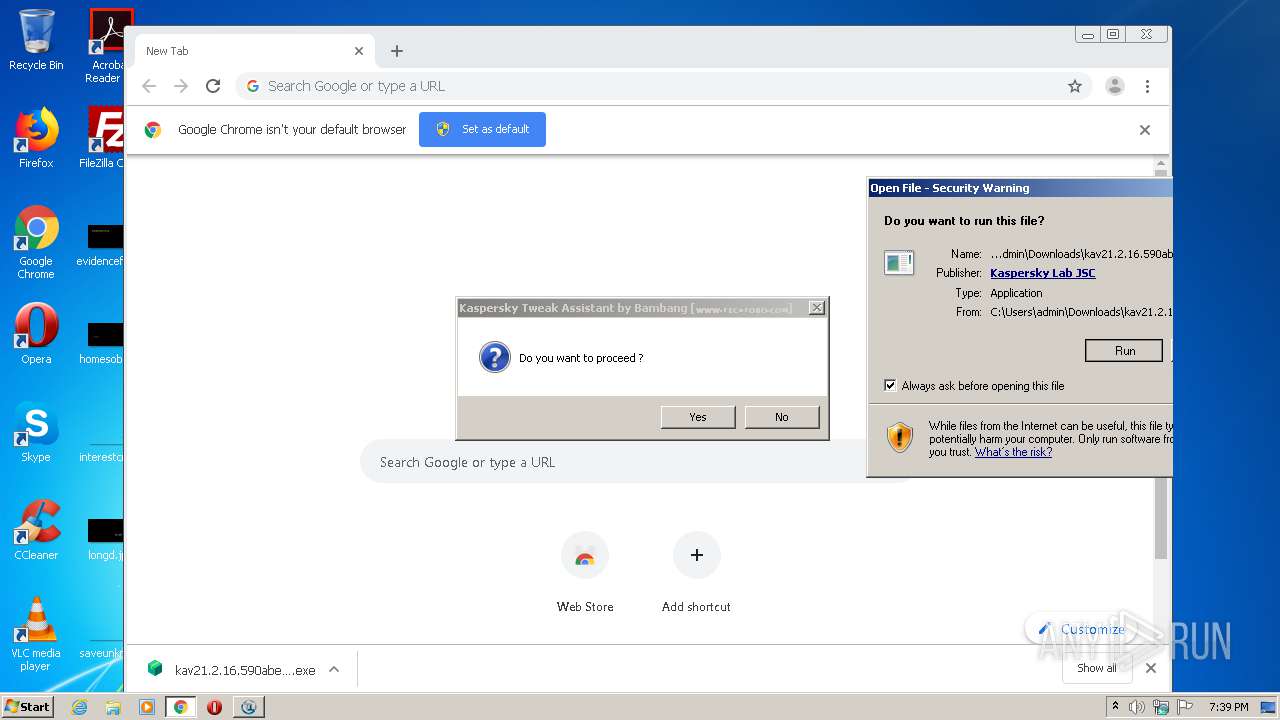
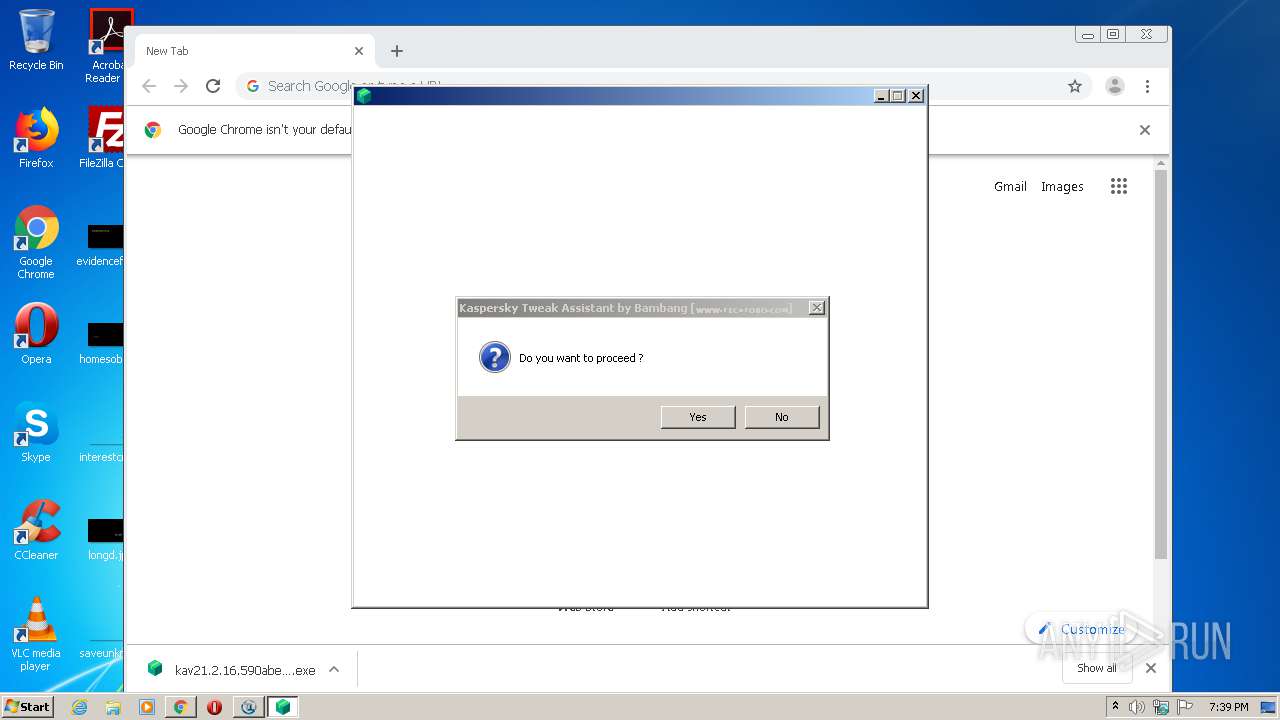
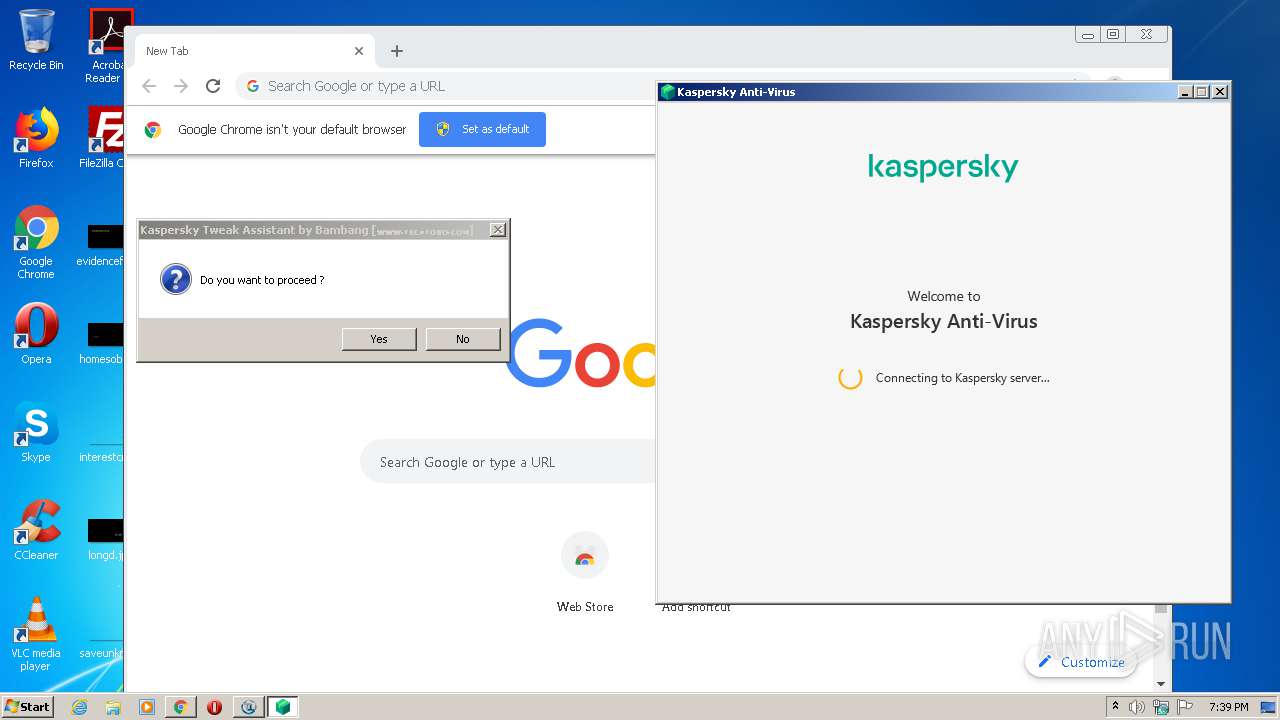
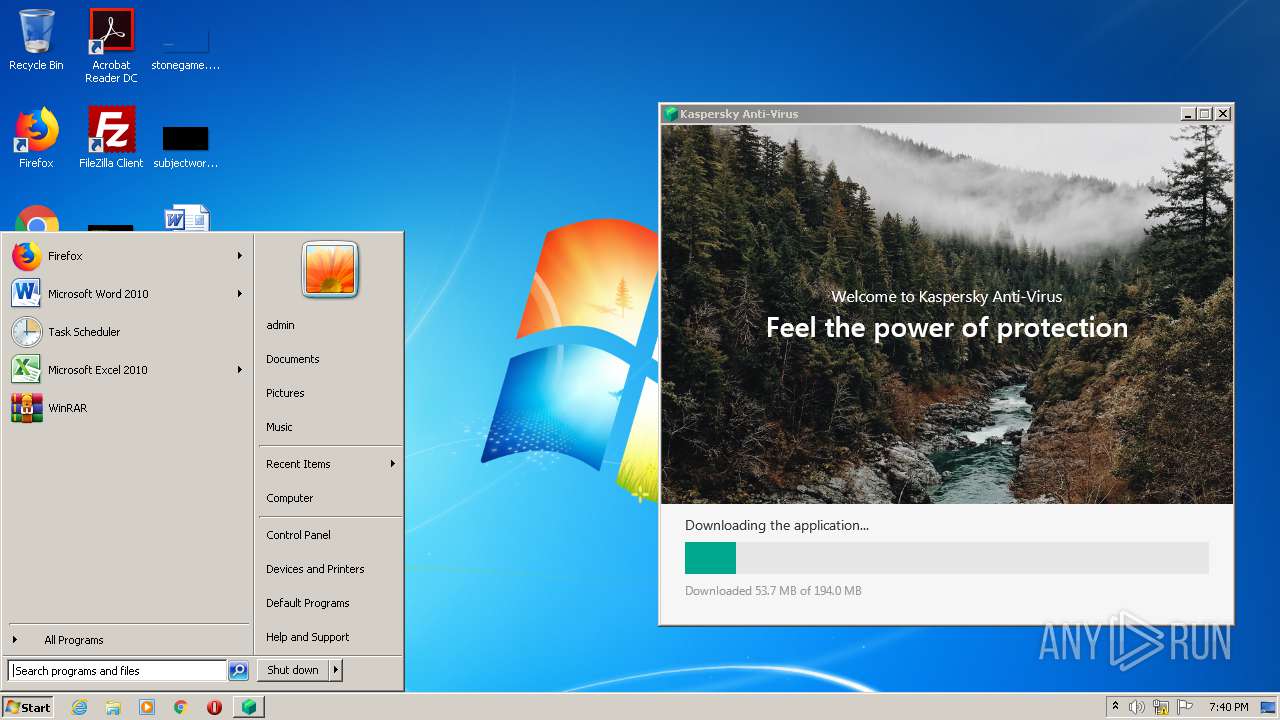
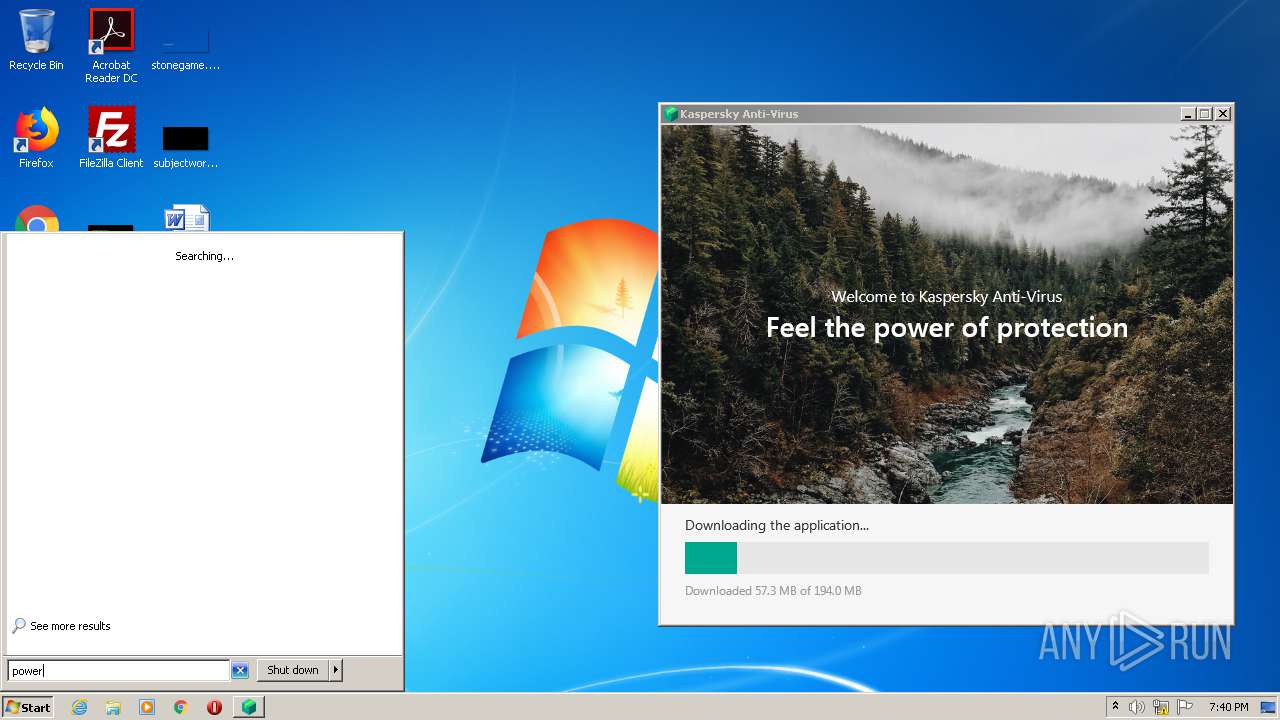
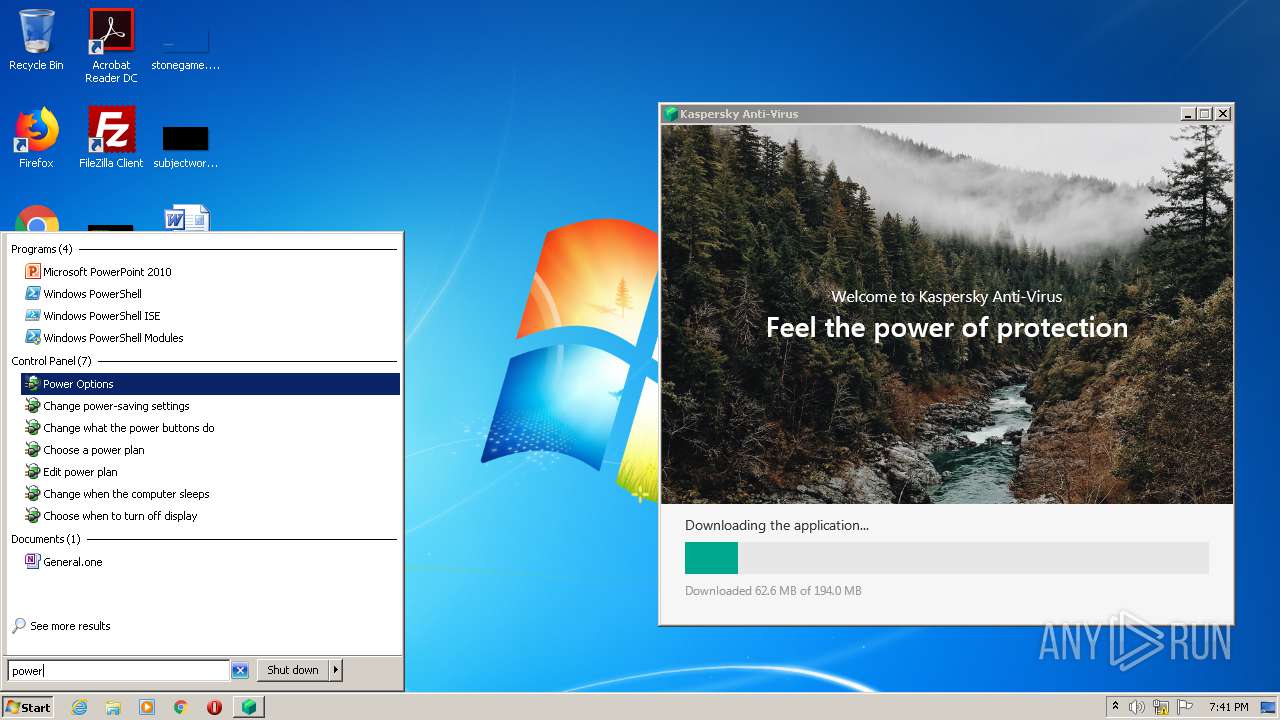
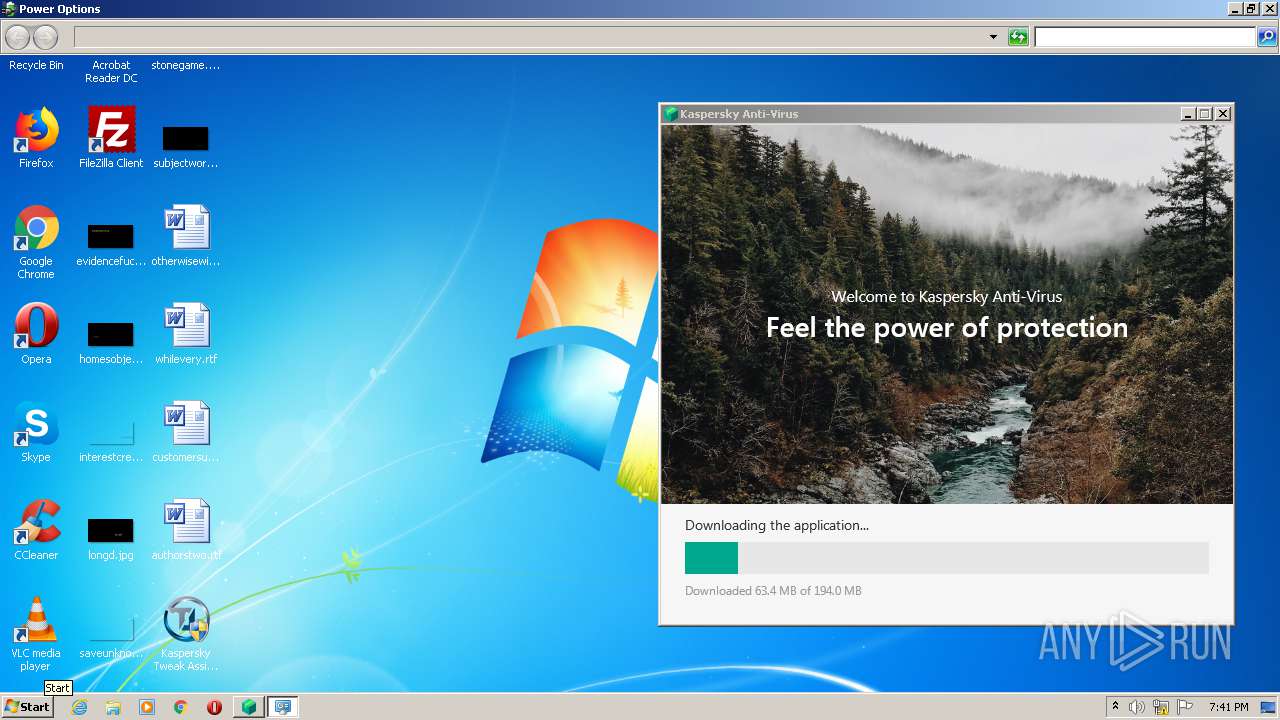
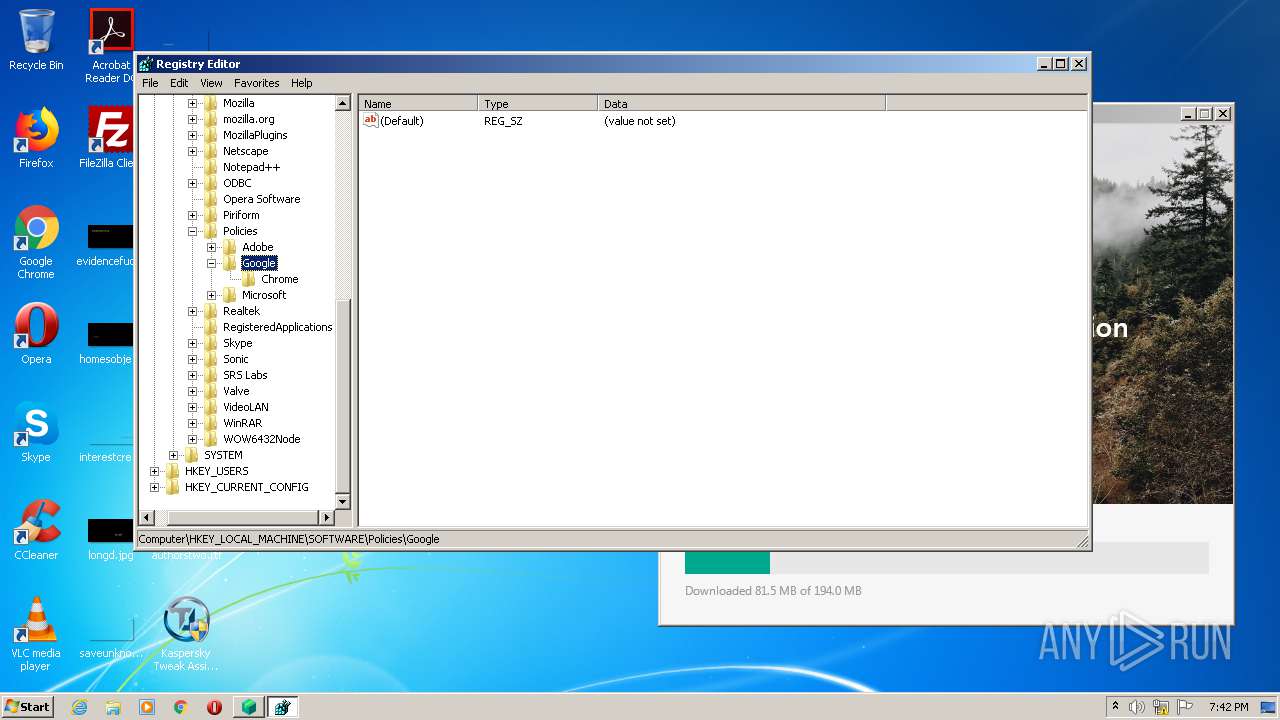
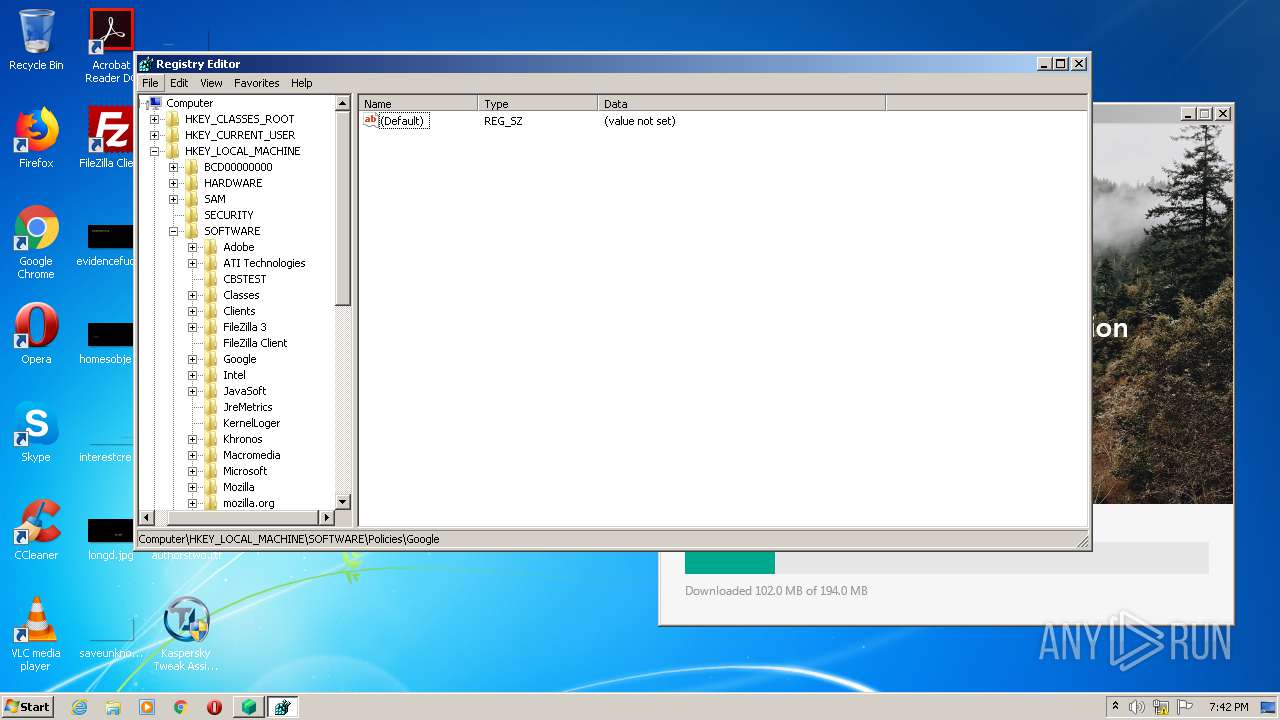
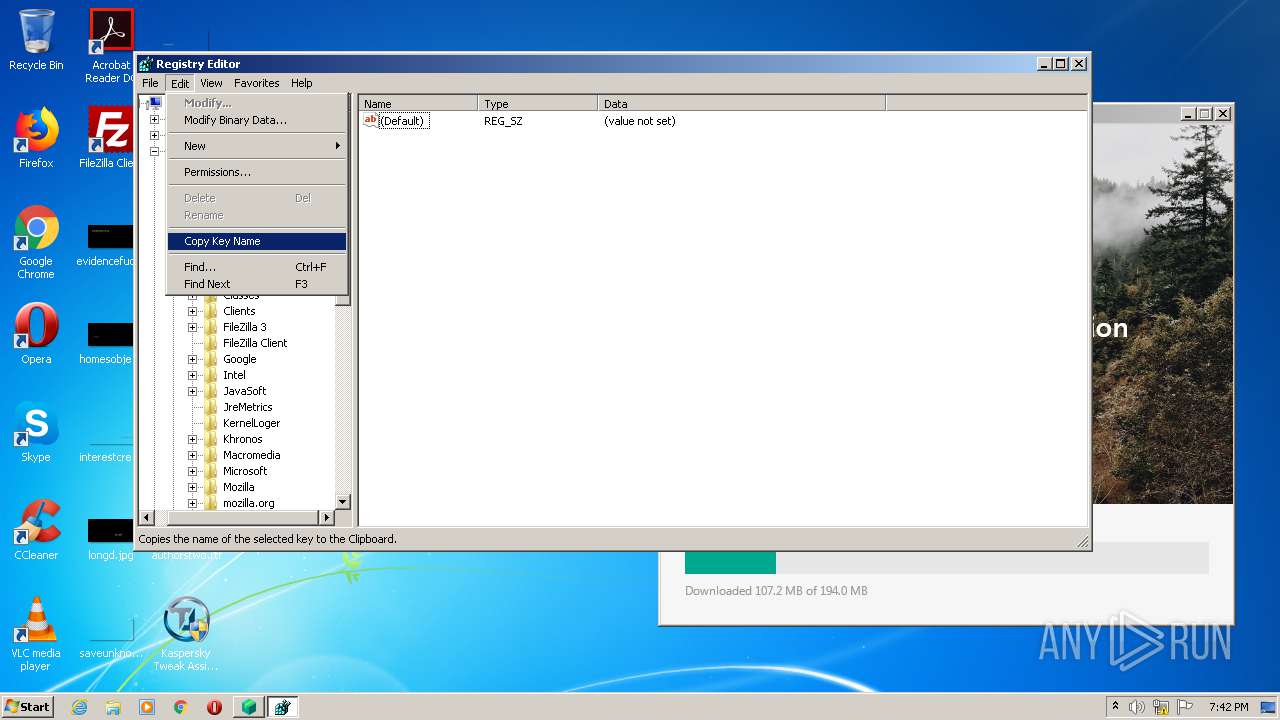
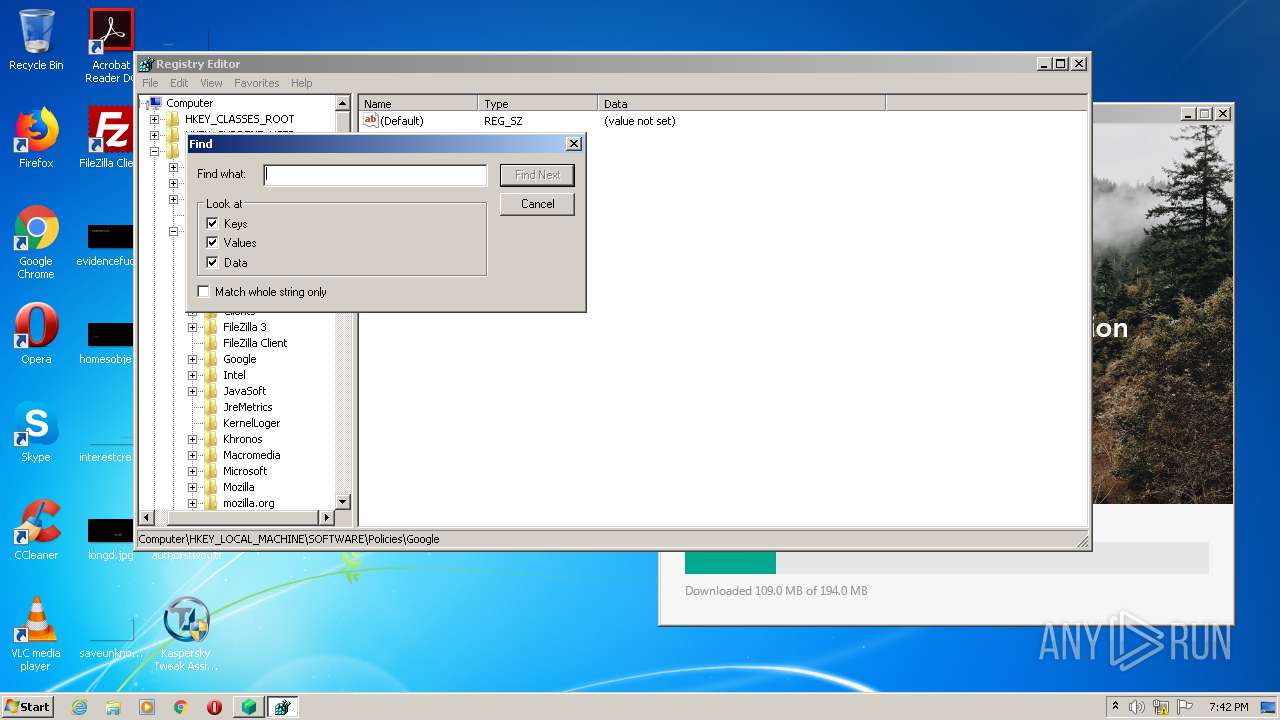
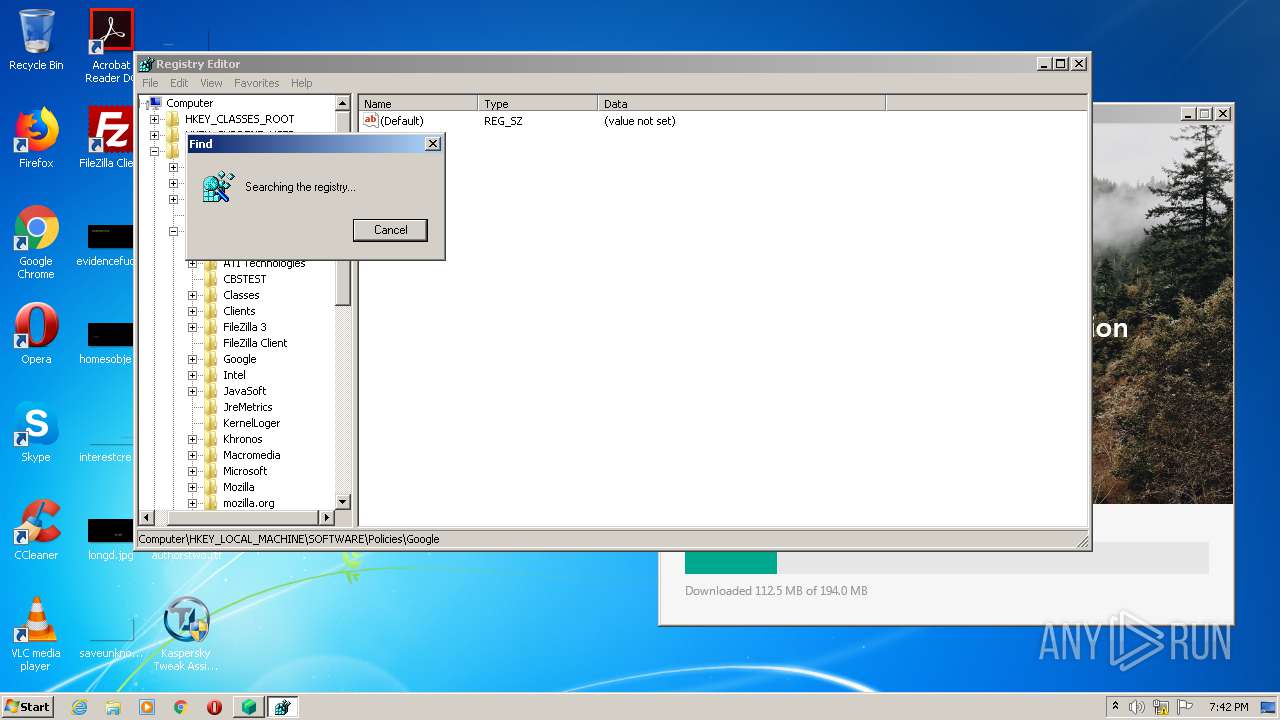
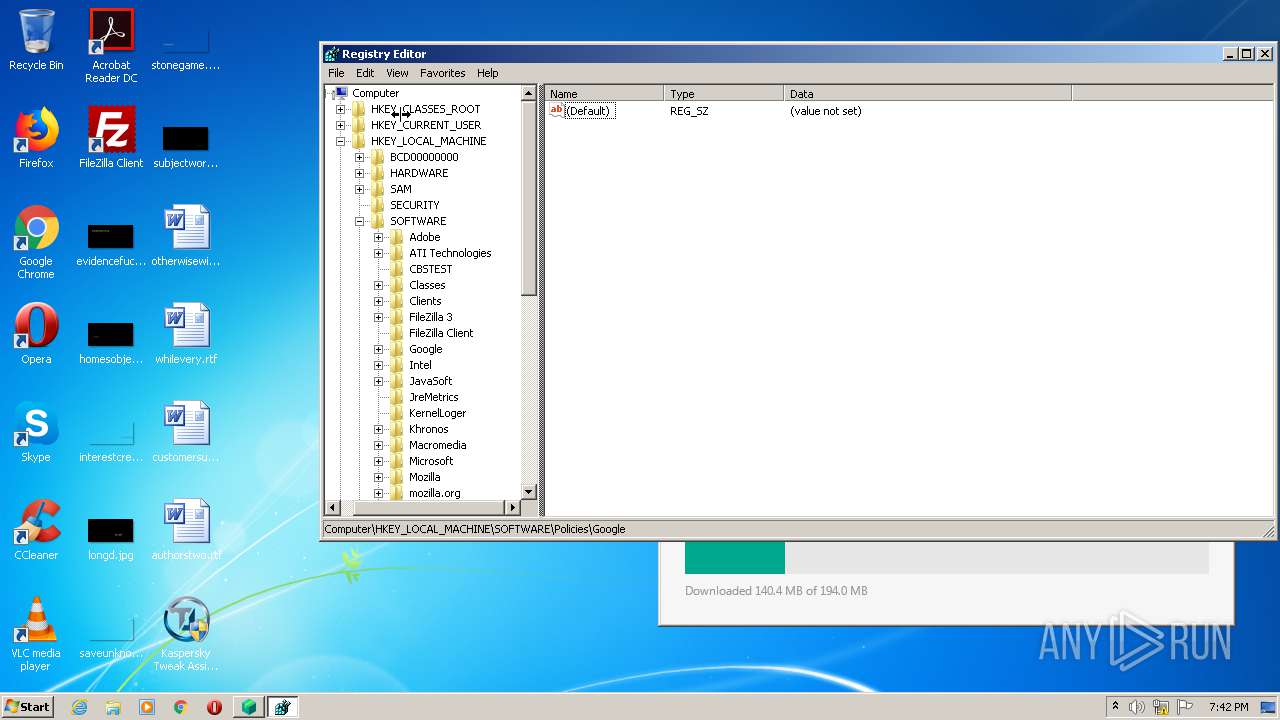
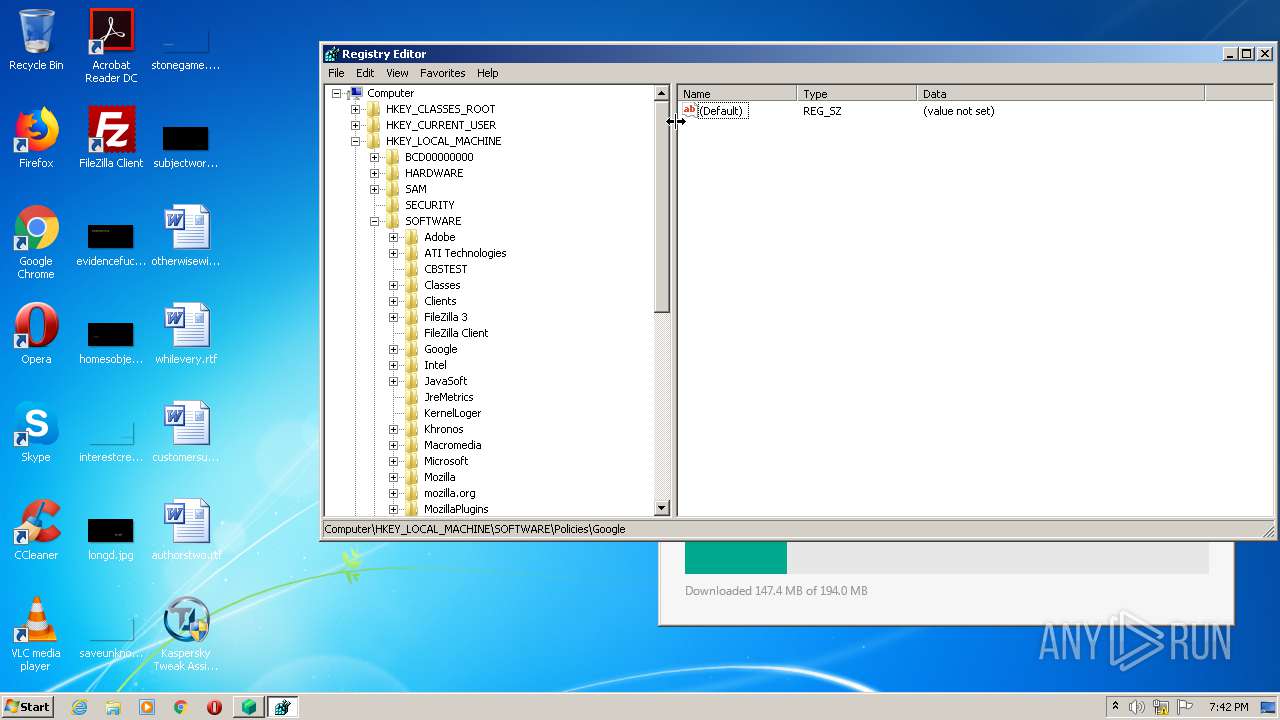
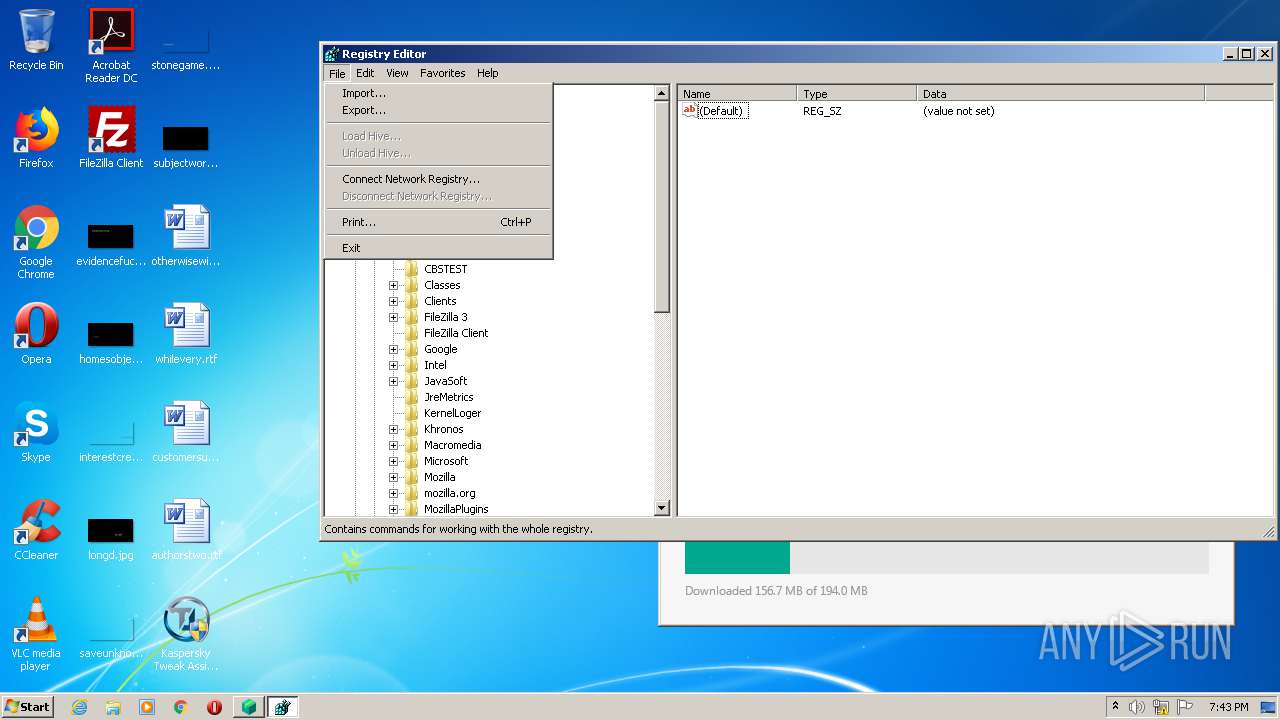
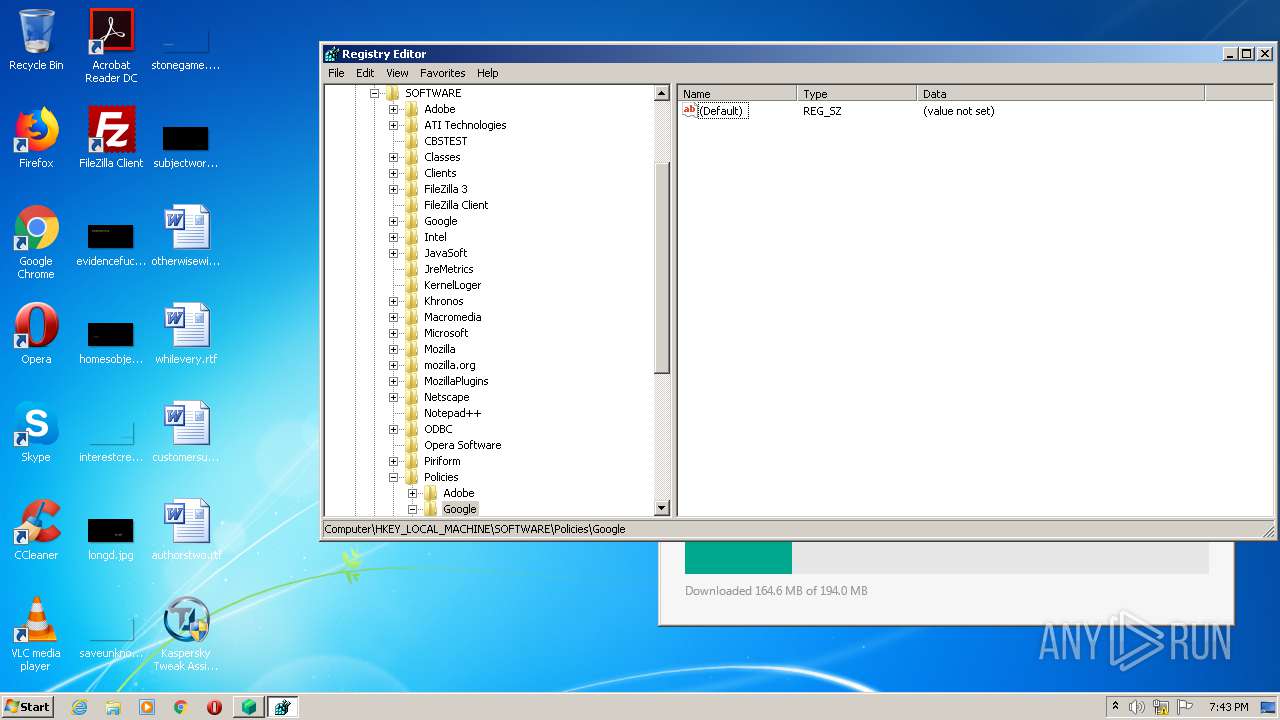
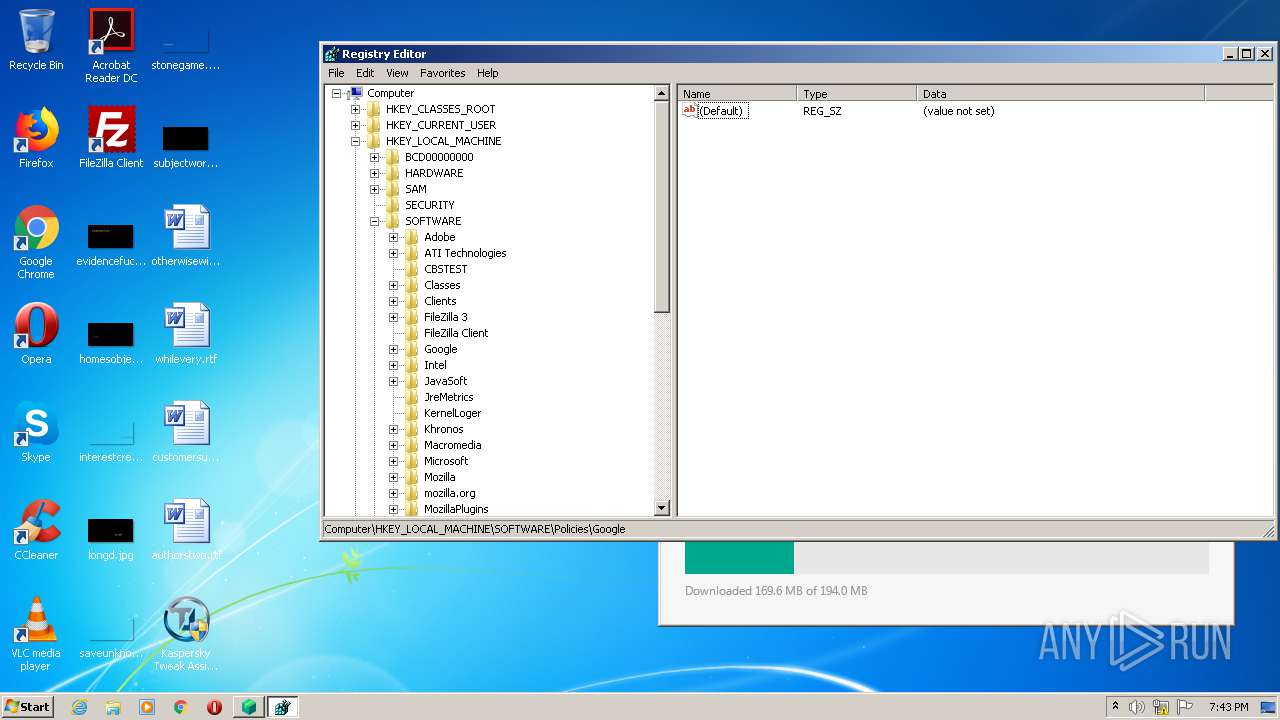
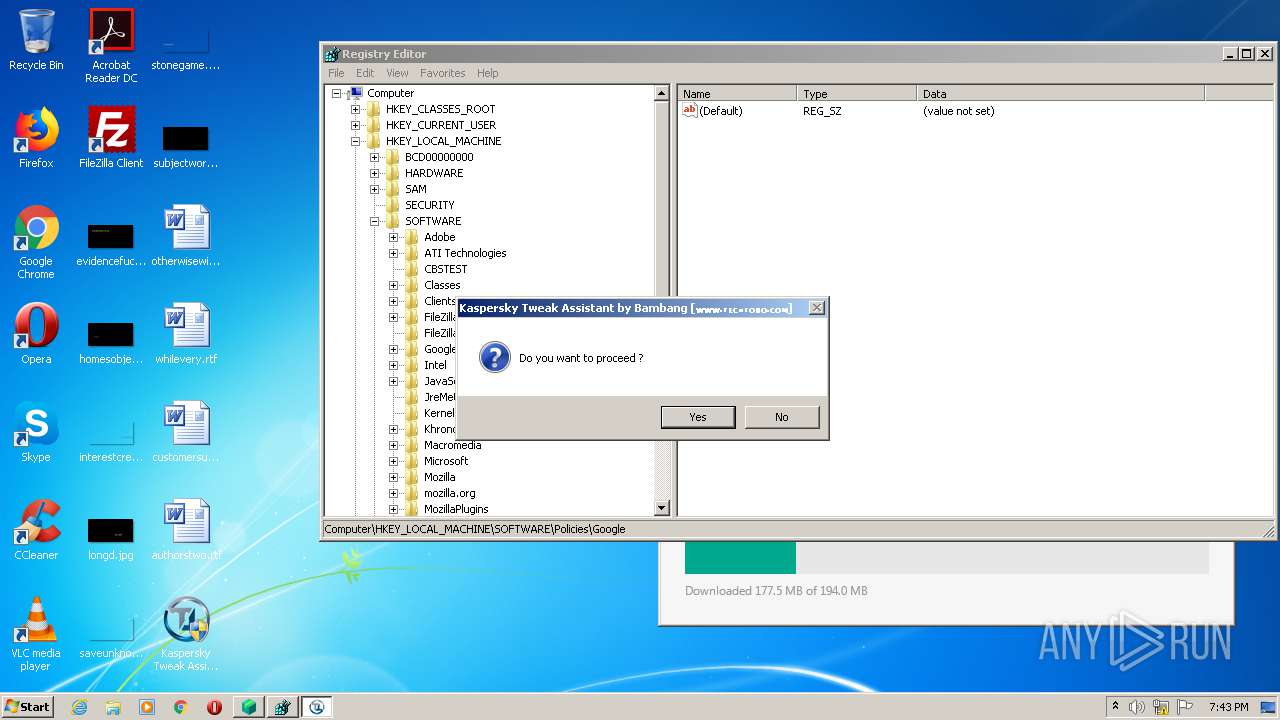
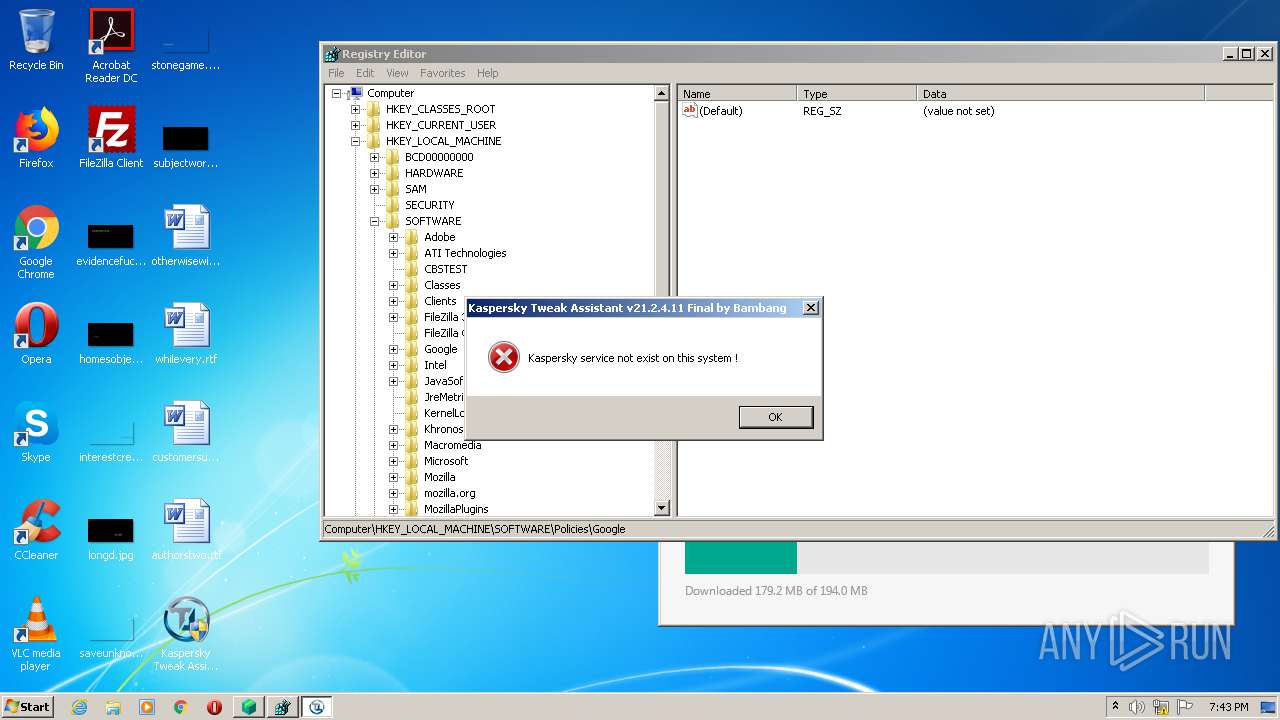
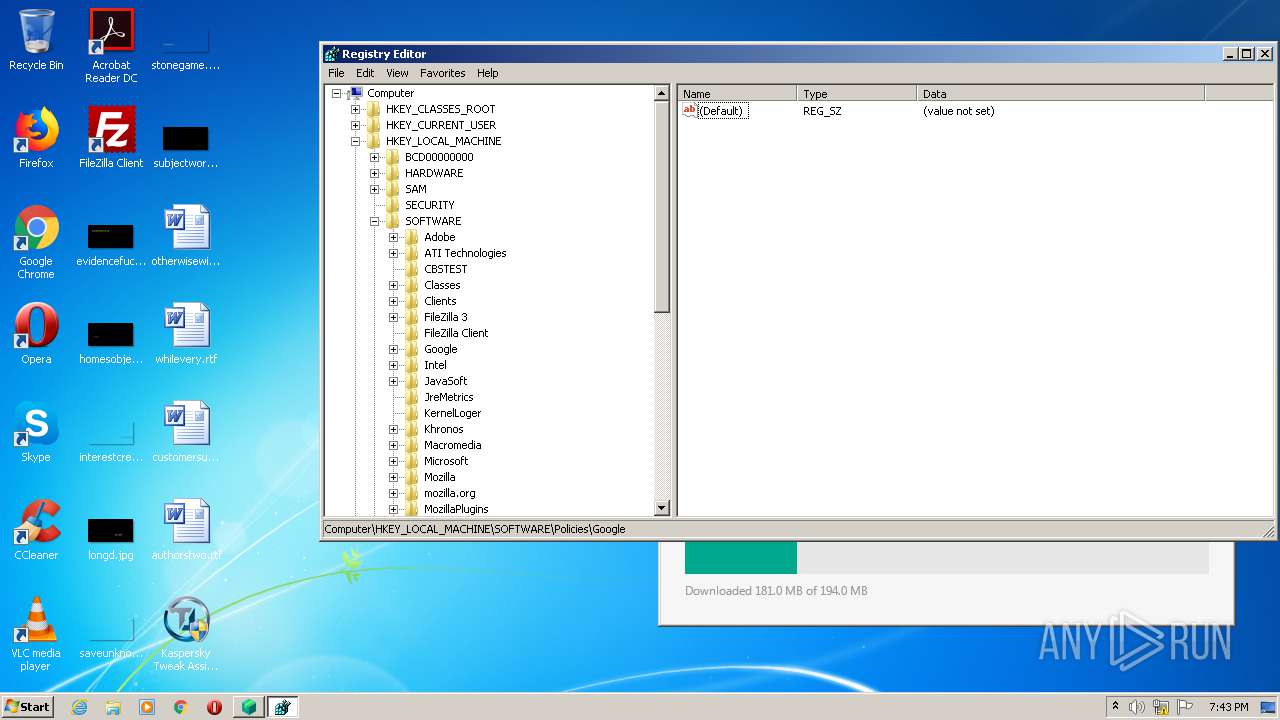
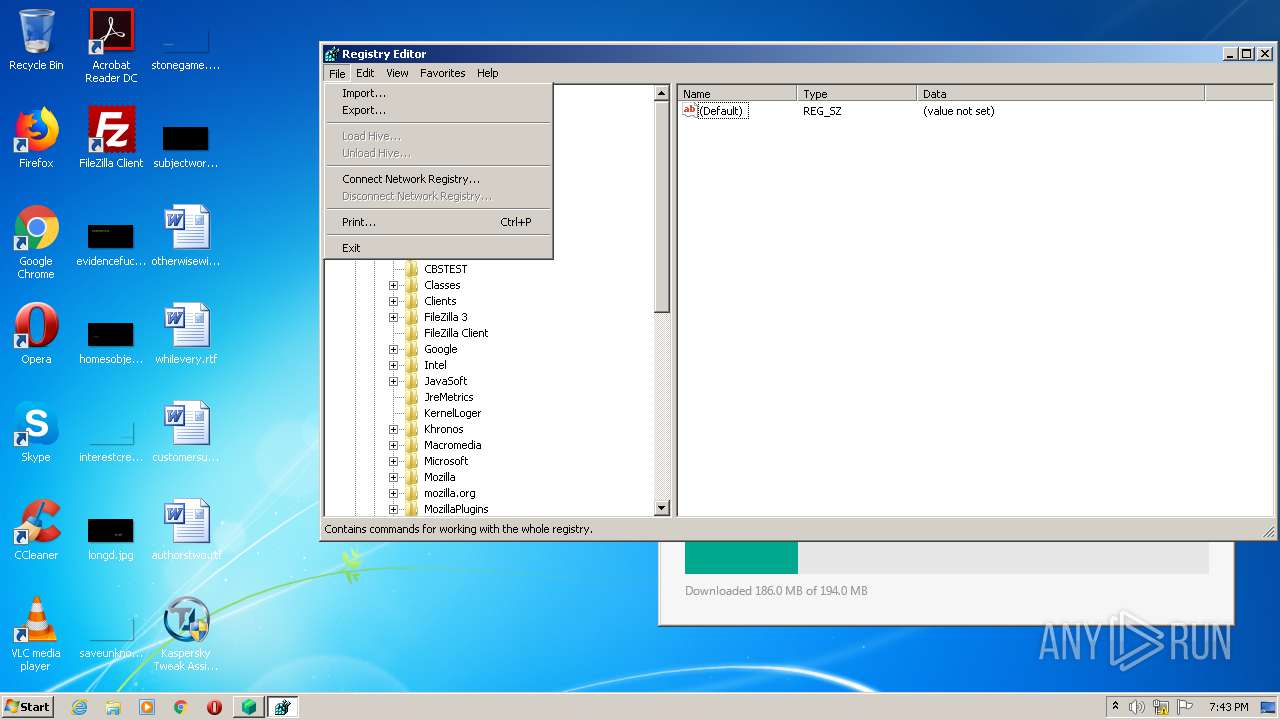
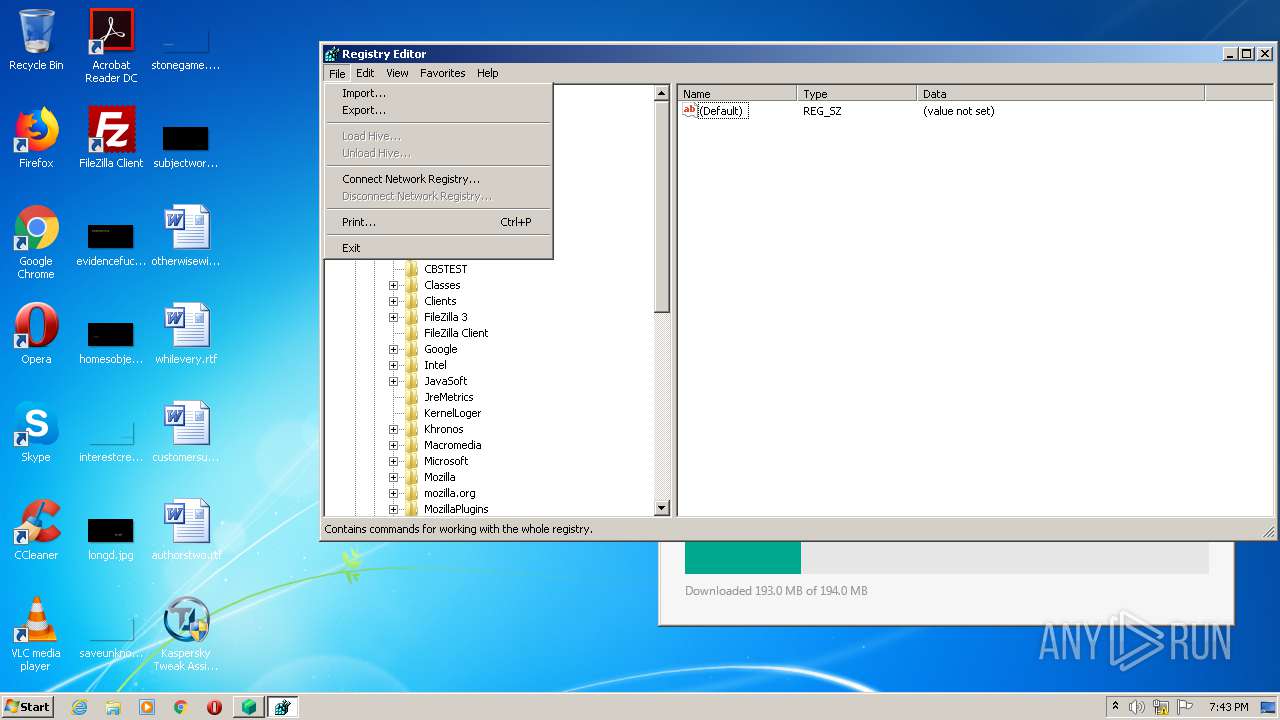
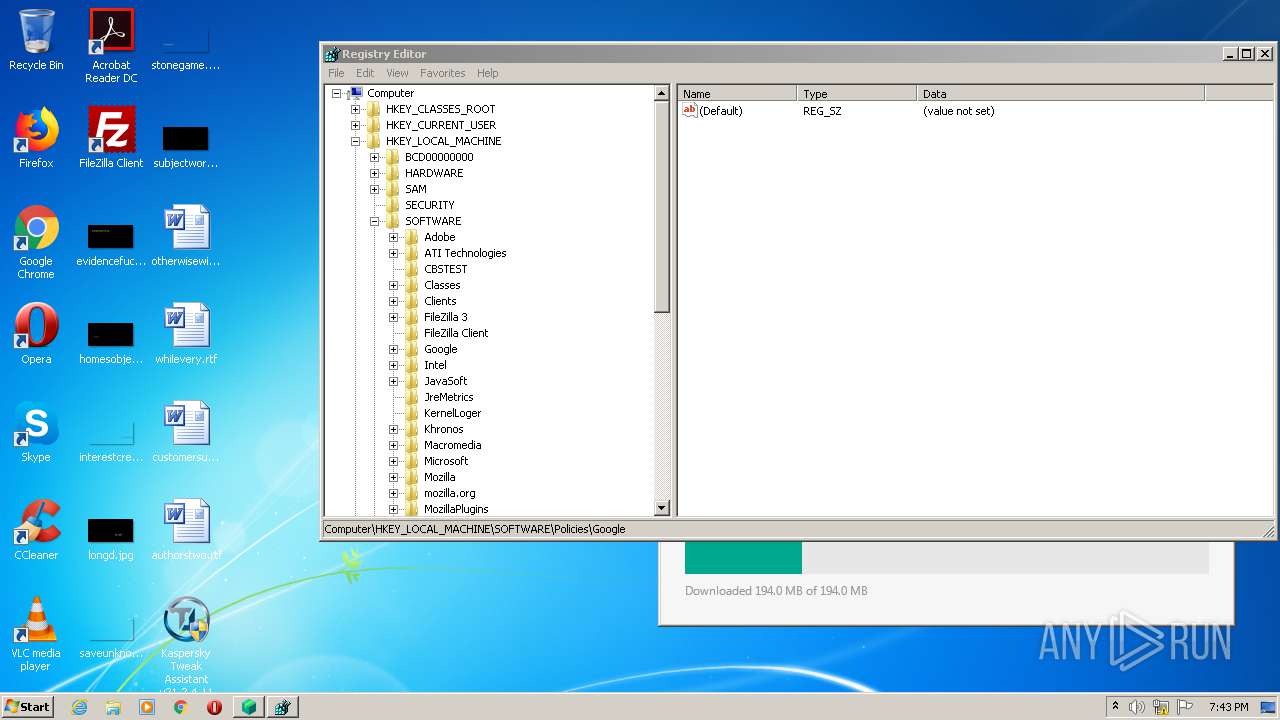
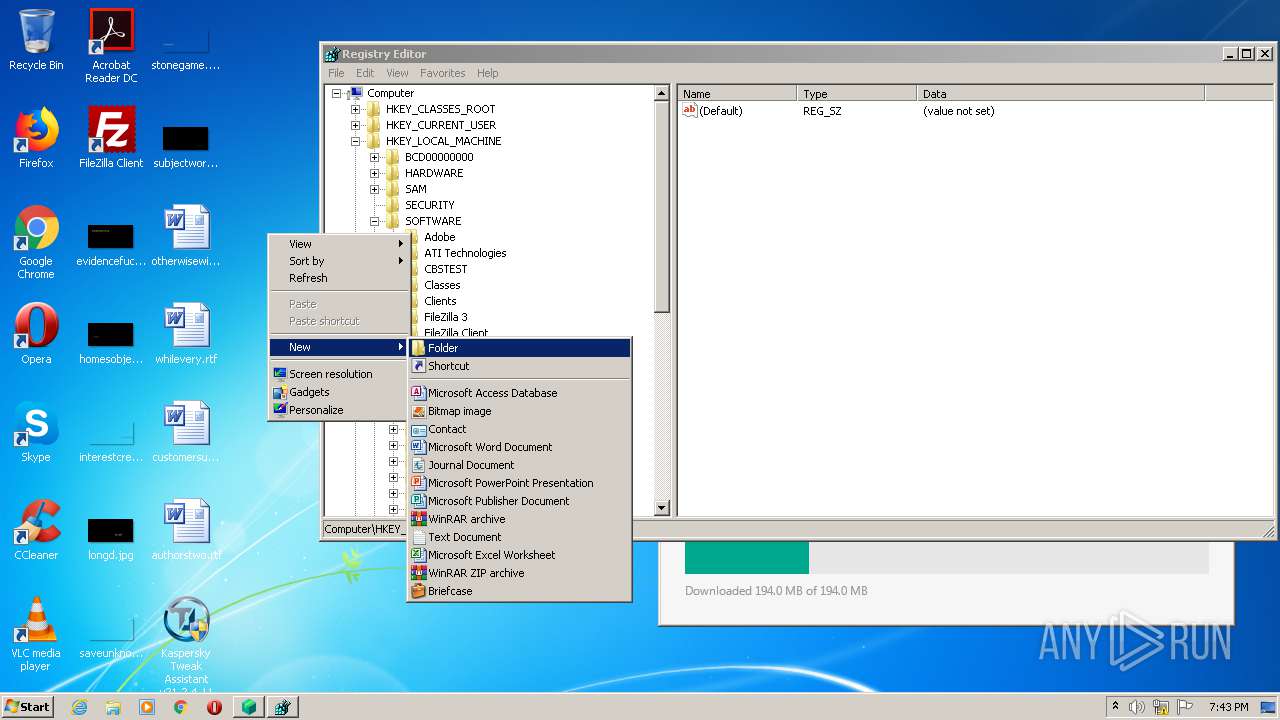
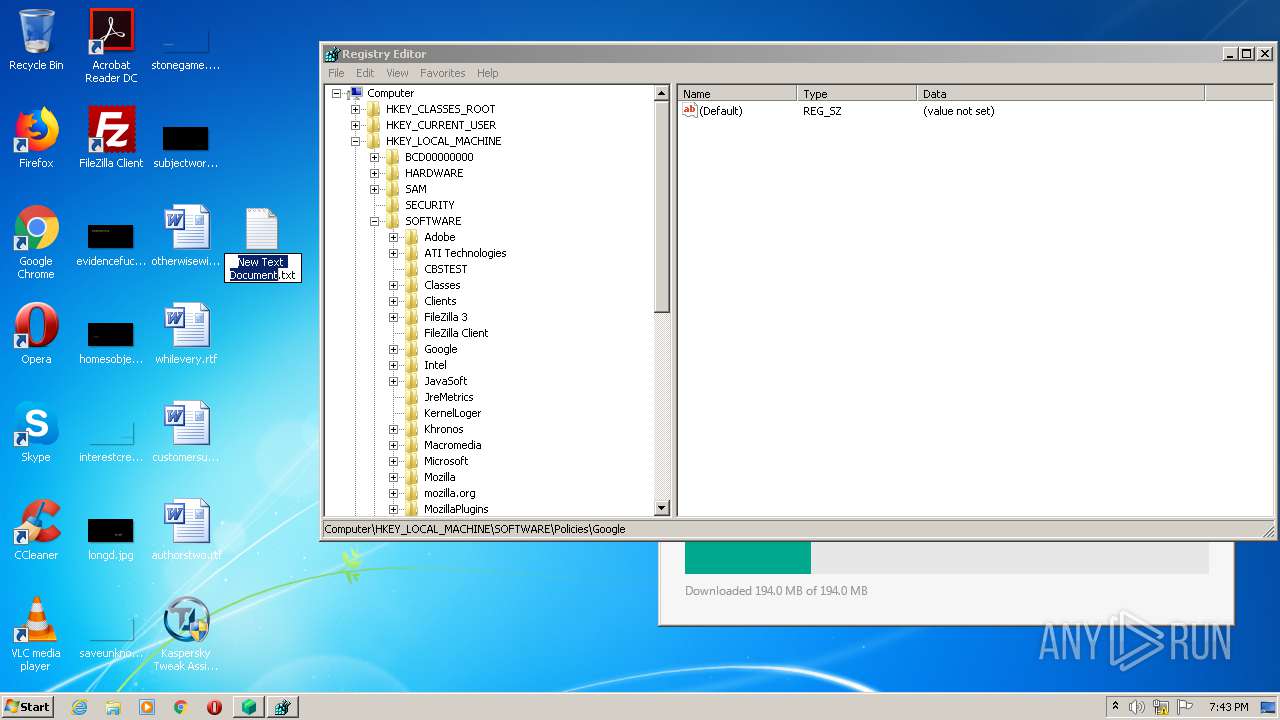
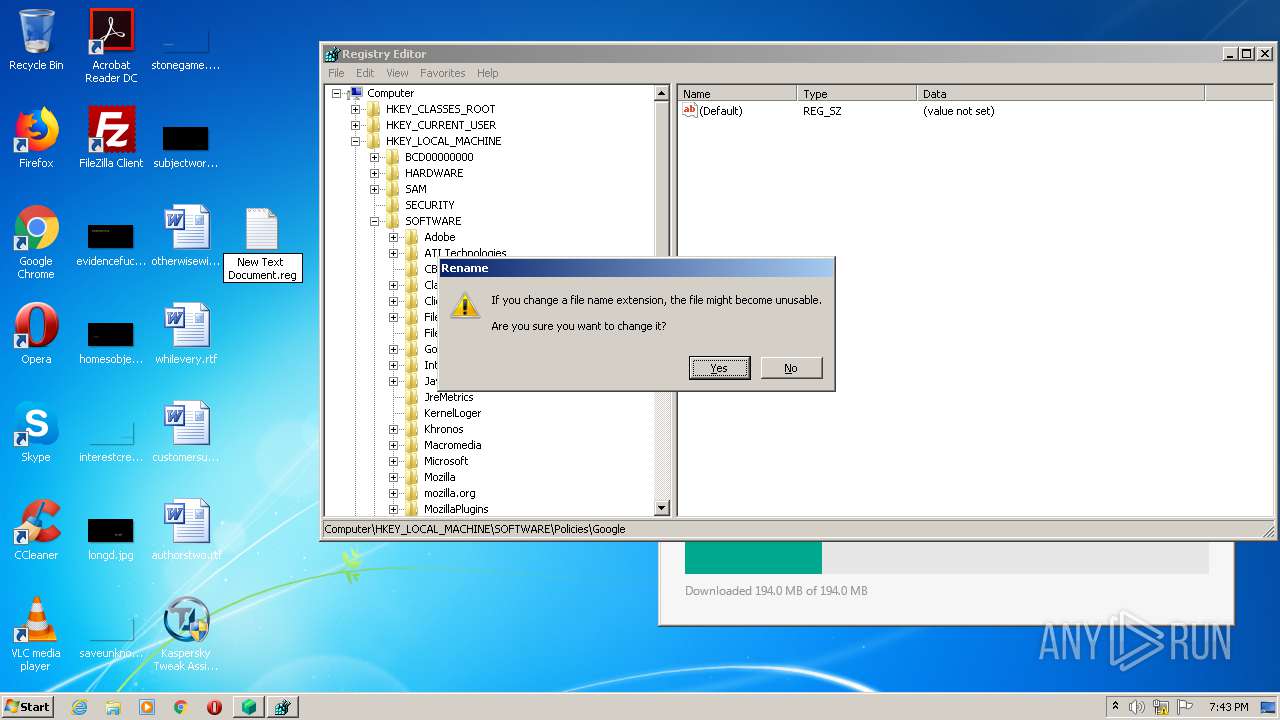
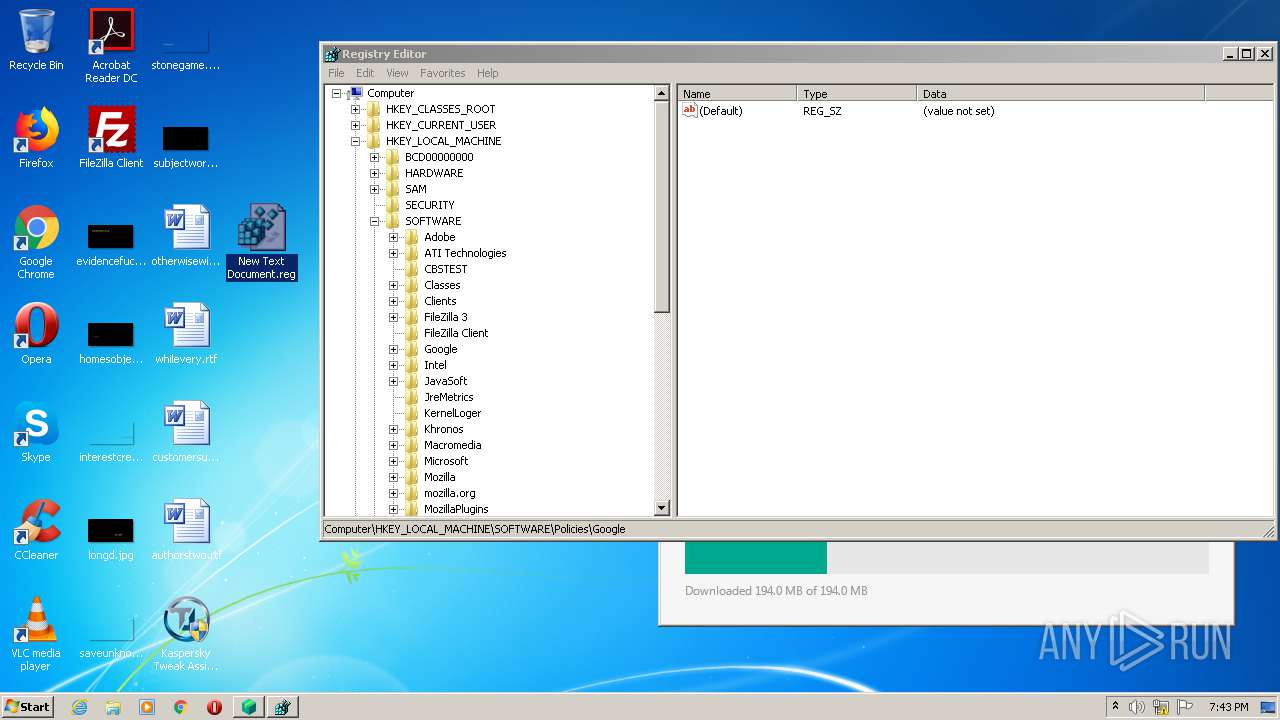
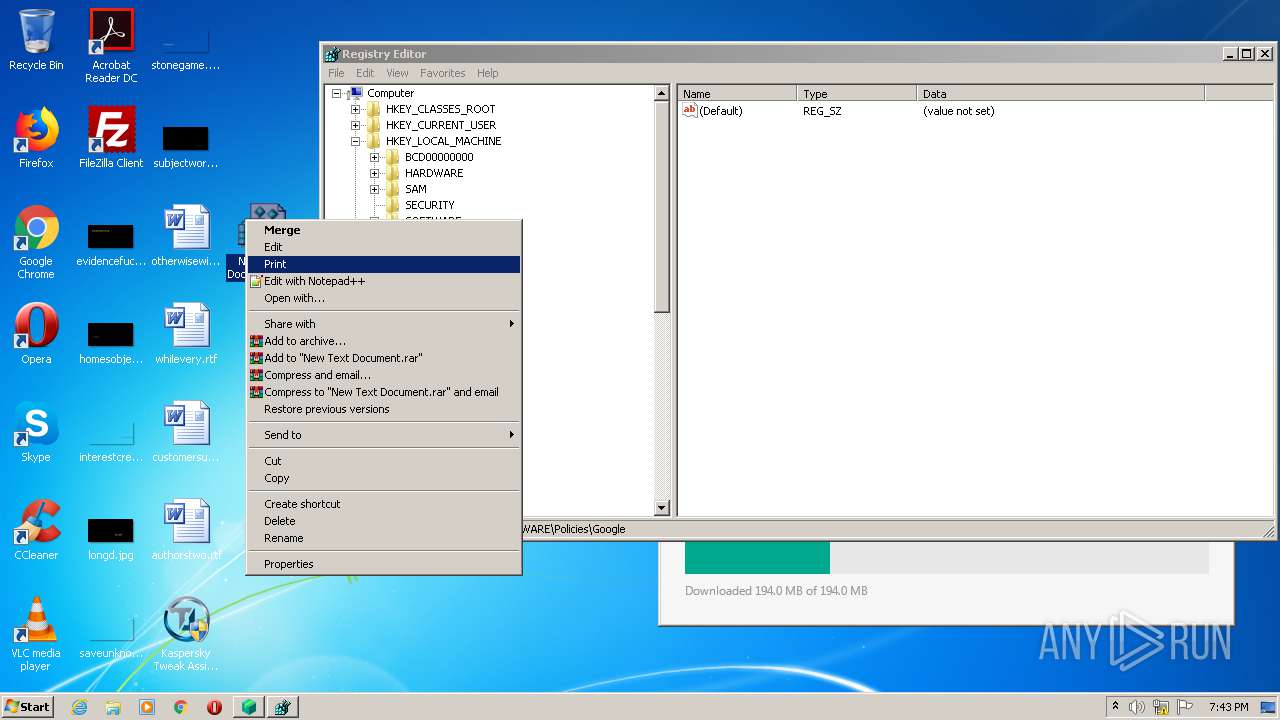
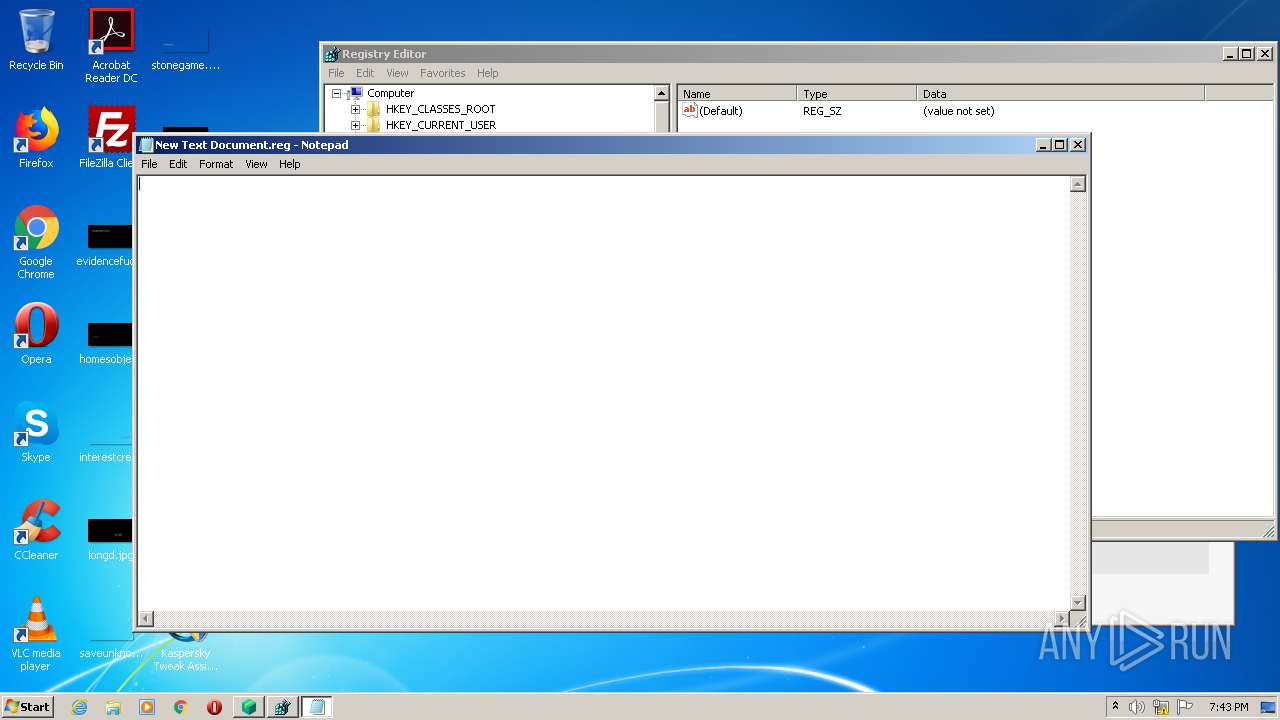
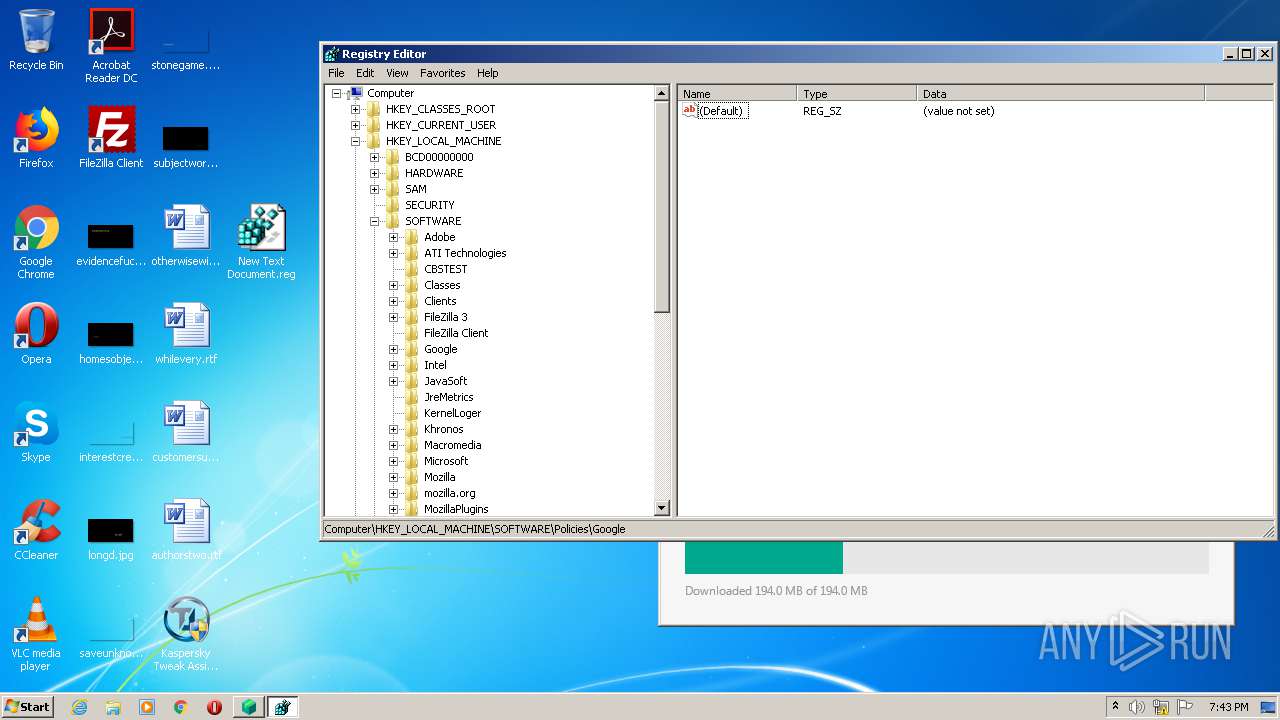
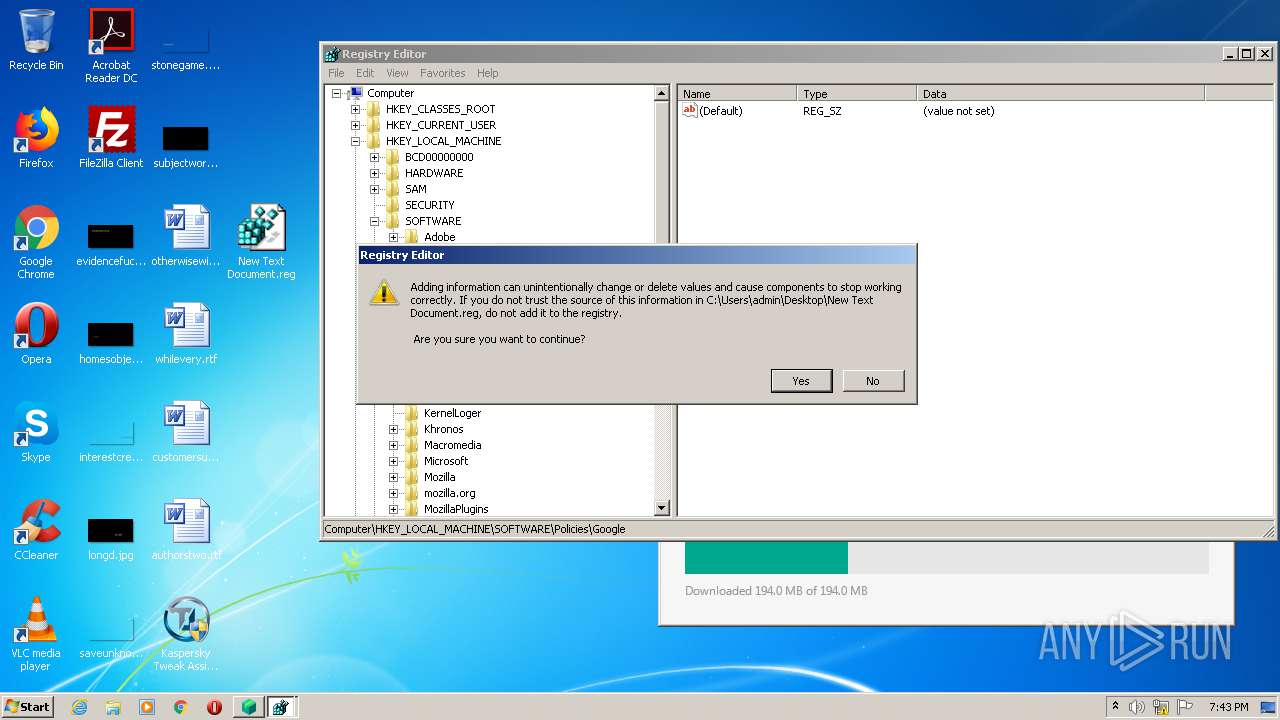
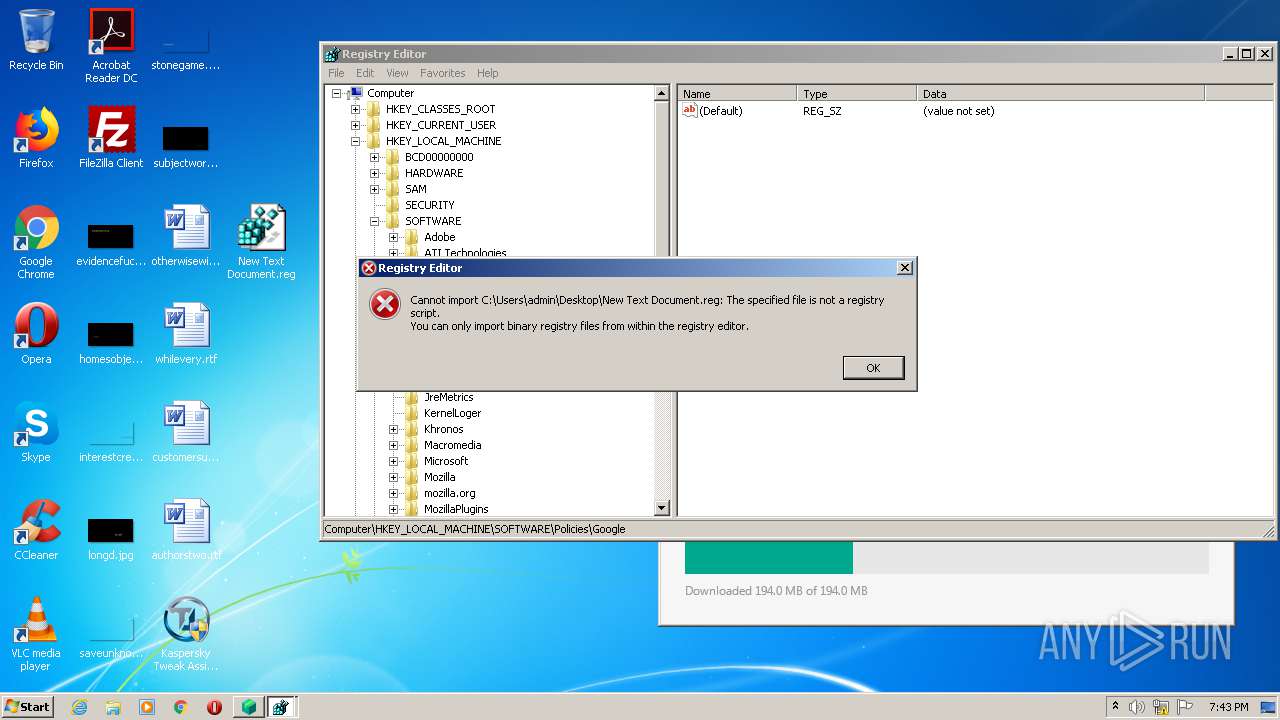
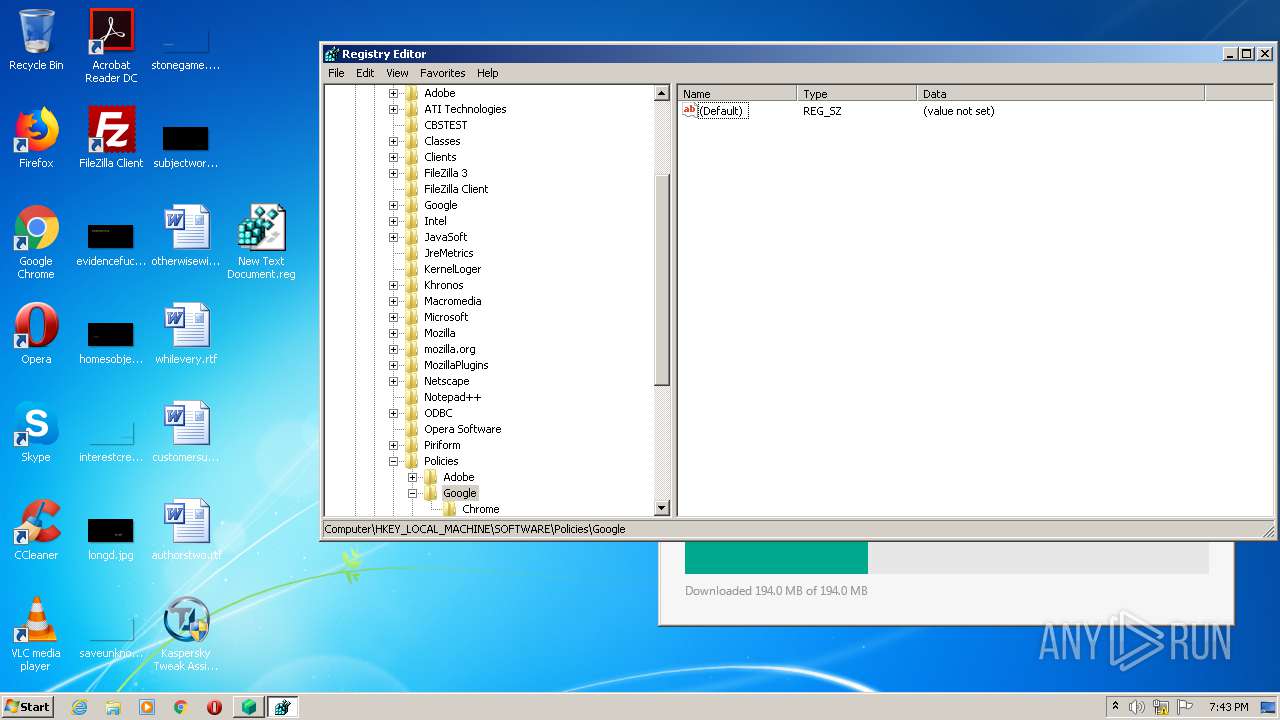
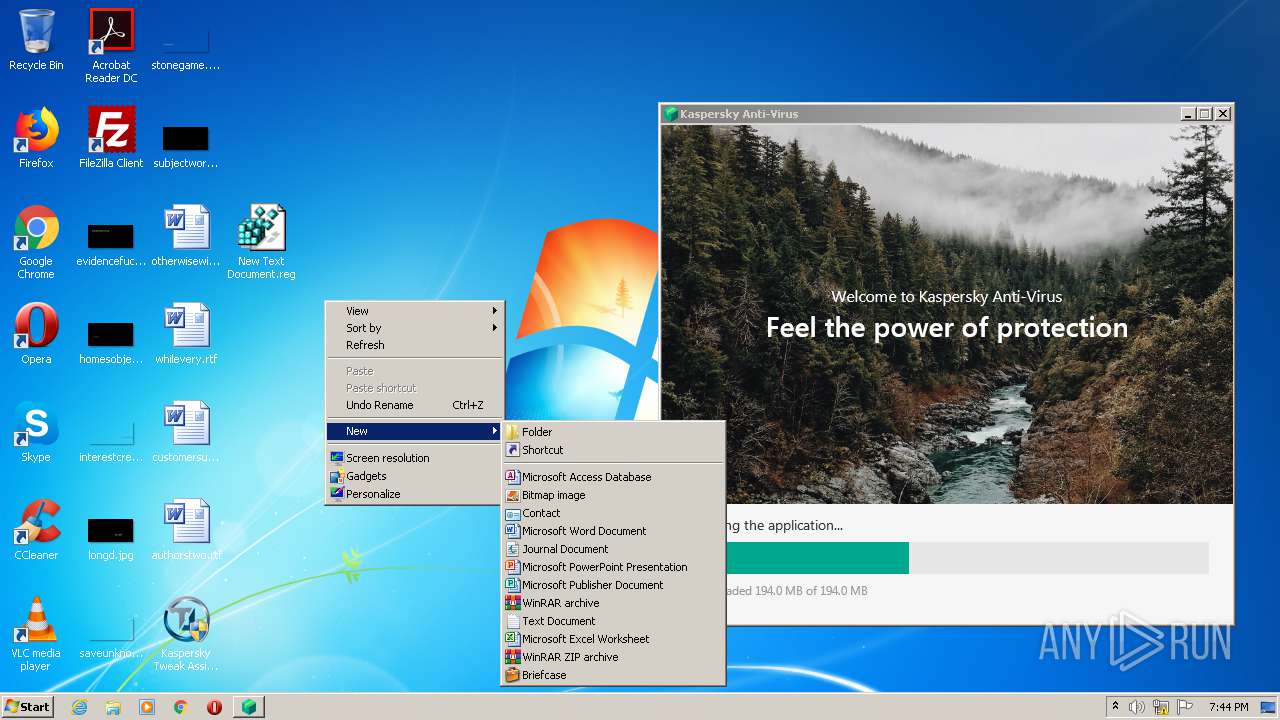
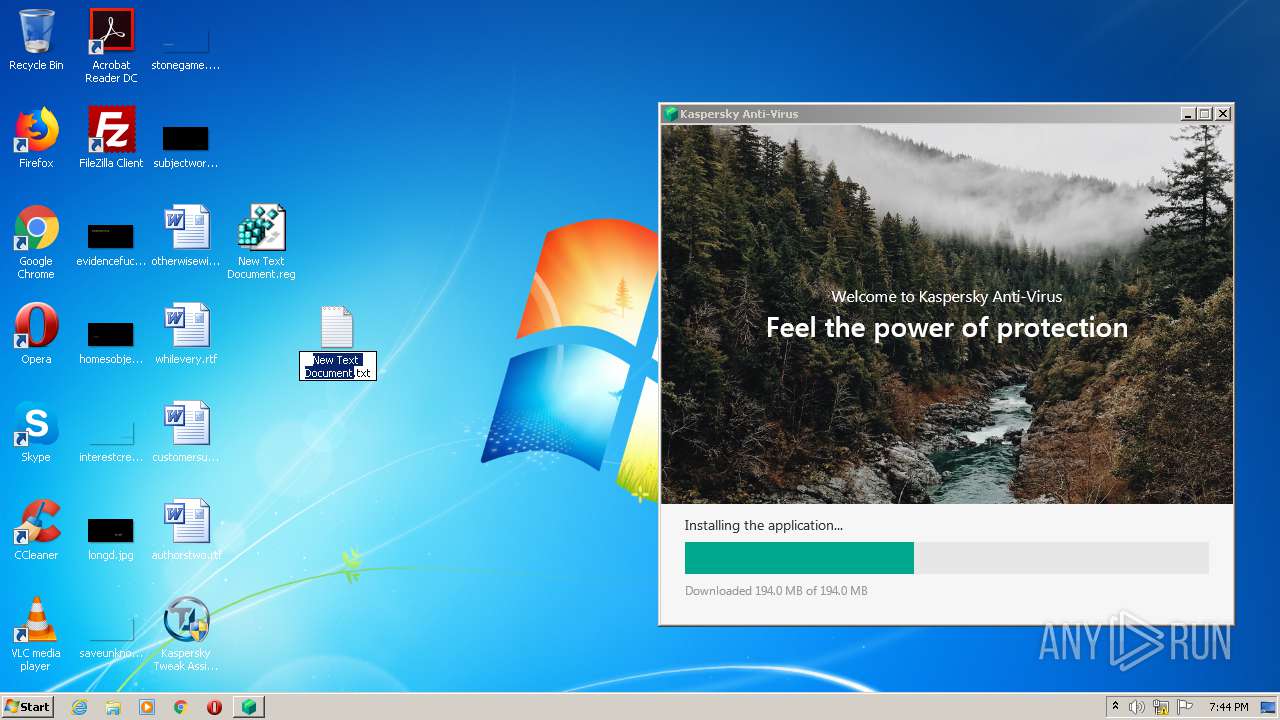
Manual execution by user
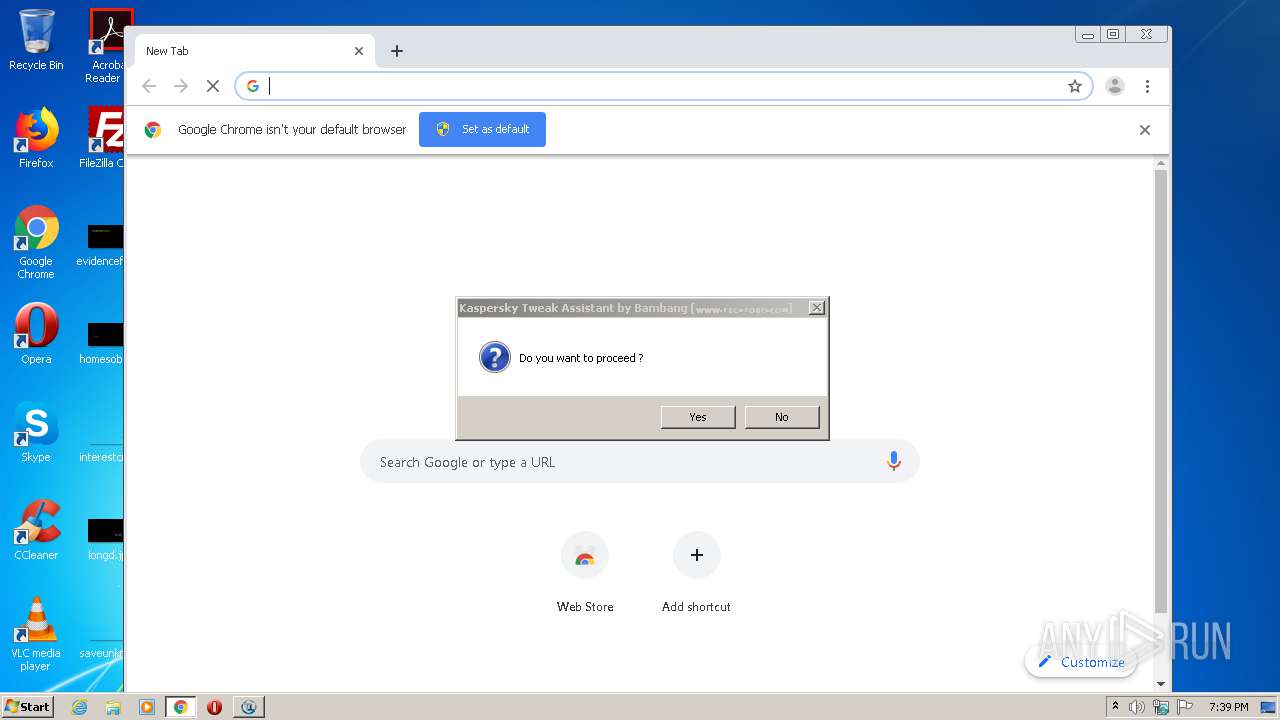
- chrome.exe (PID: 1704)
- Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe (PID: 272)
- Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe (PID: 2772)
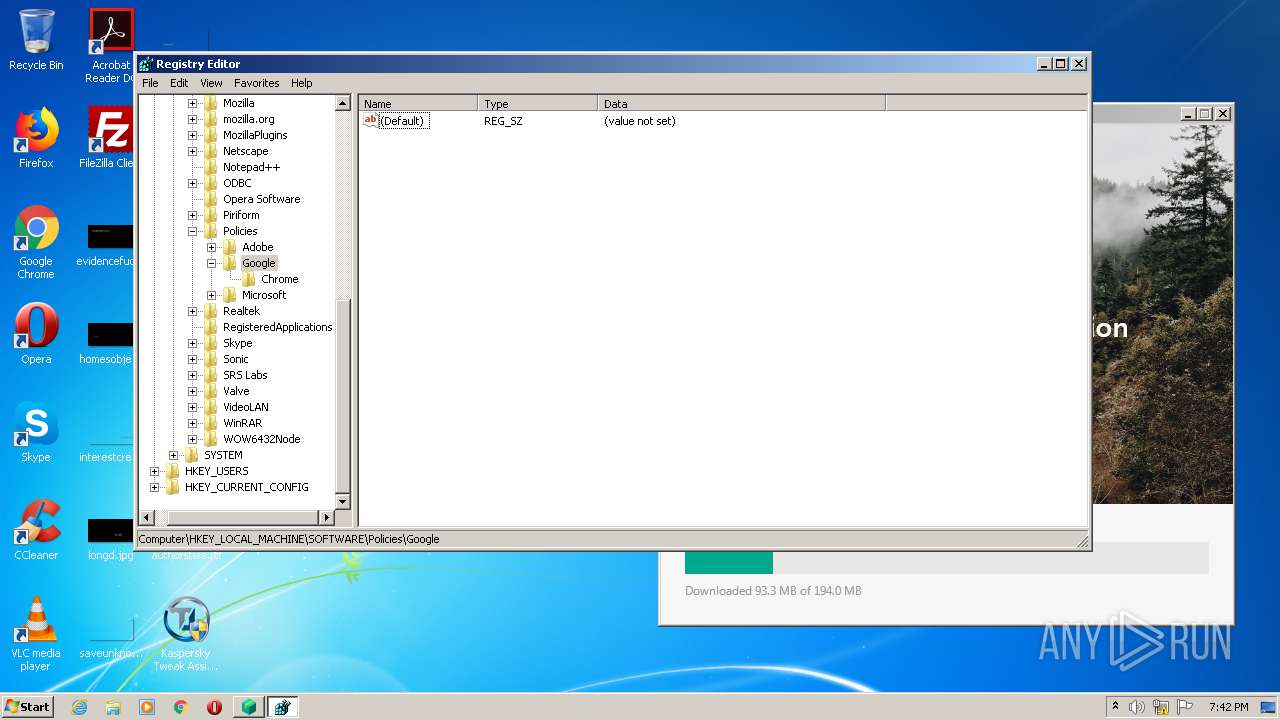
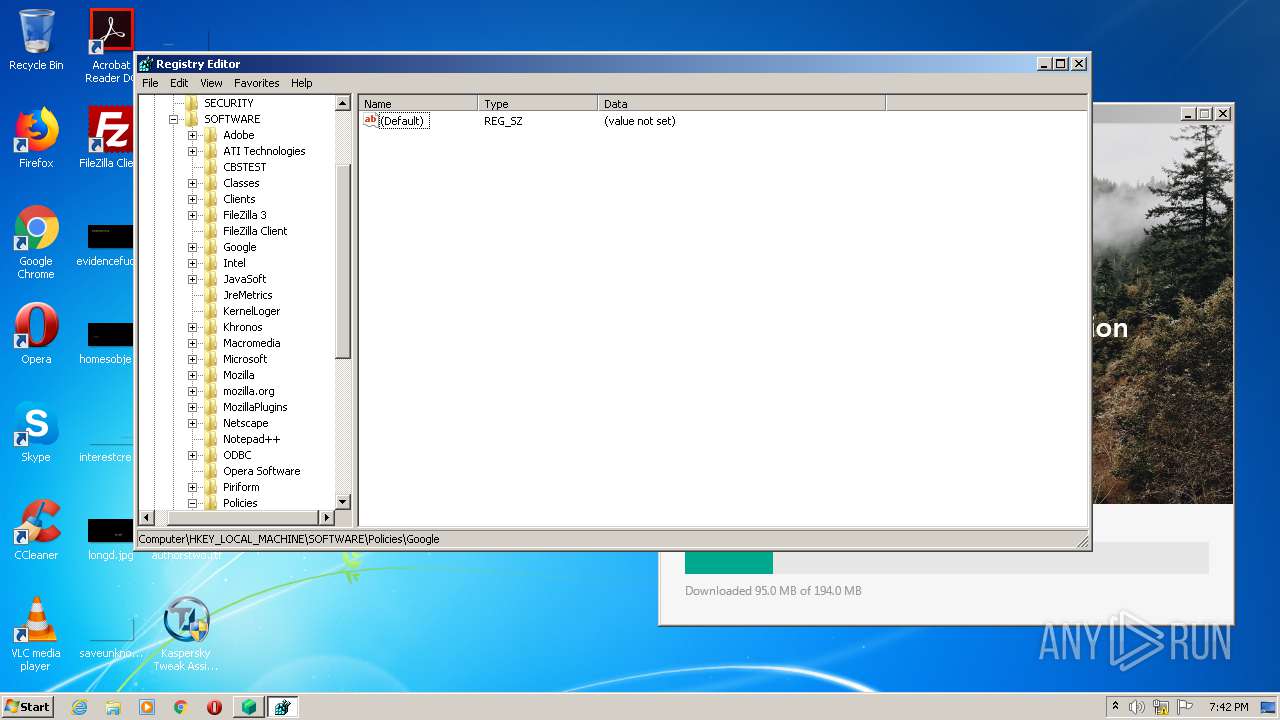
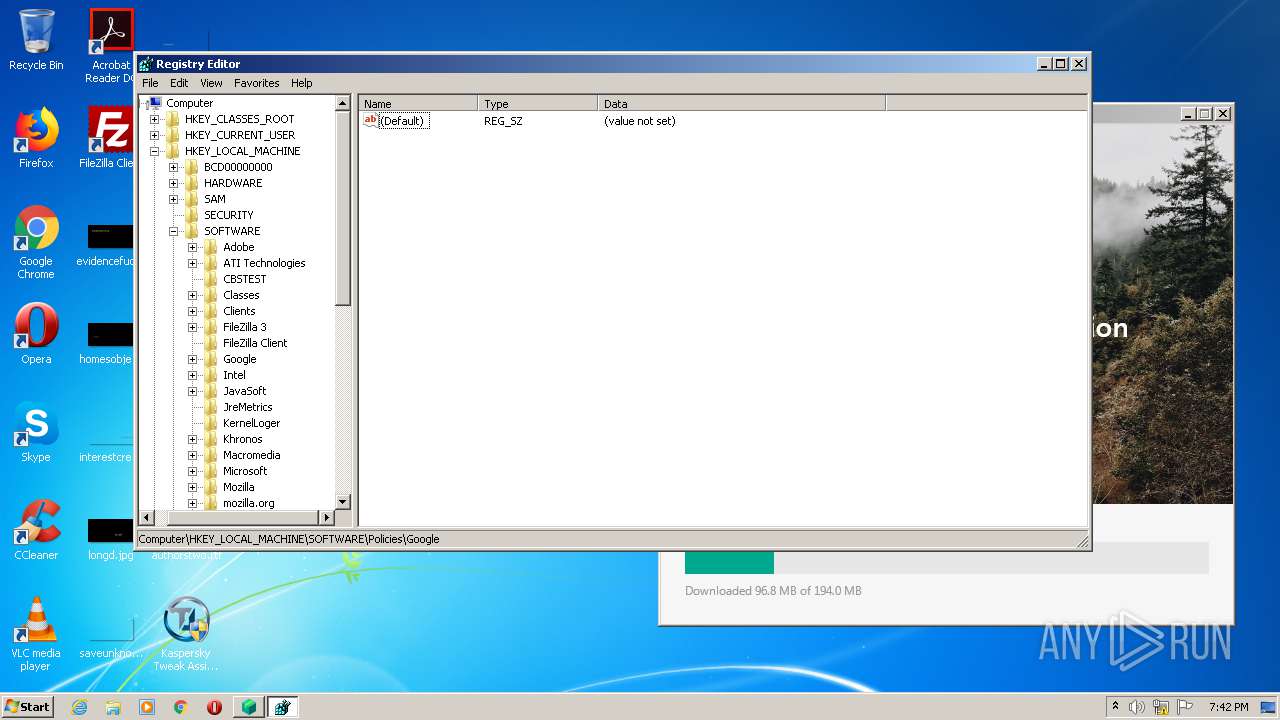
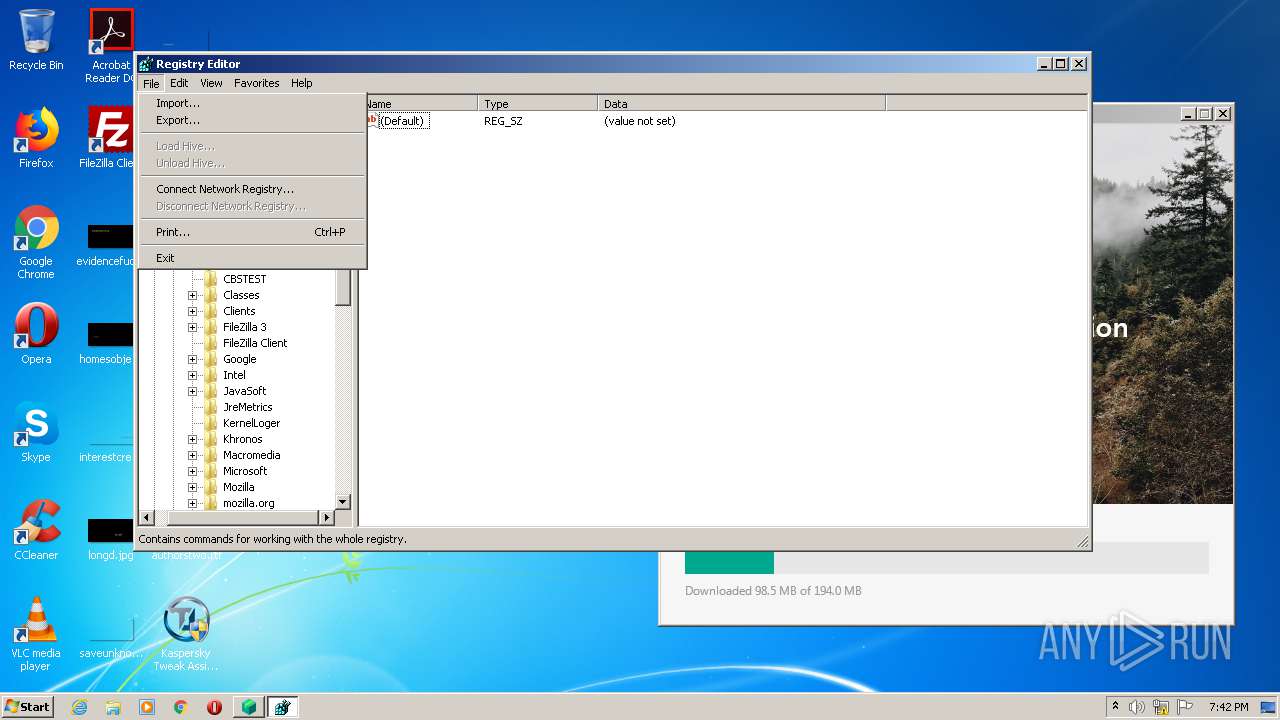
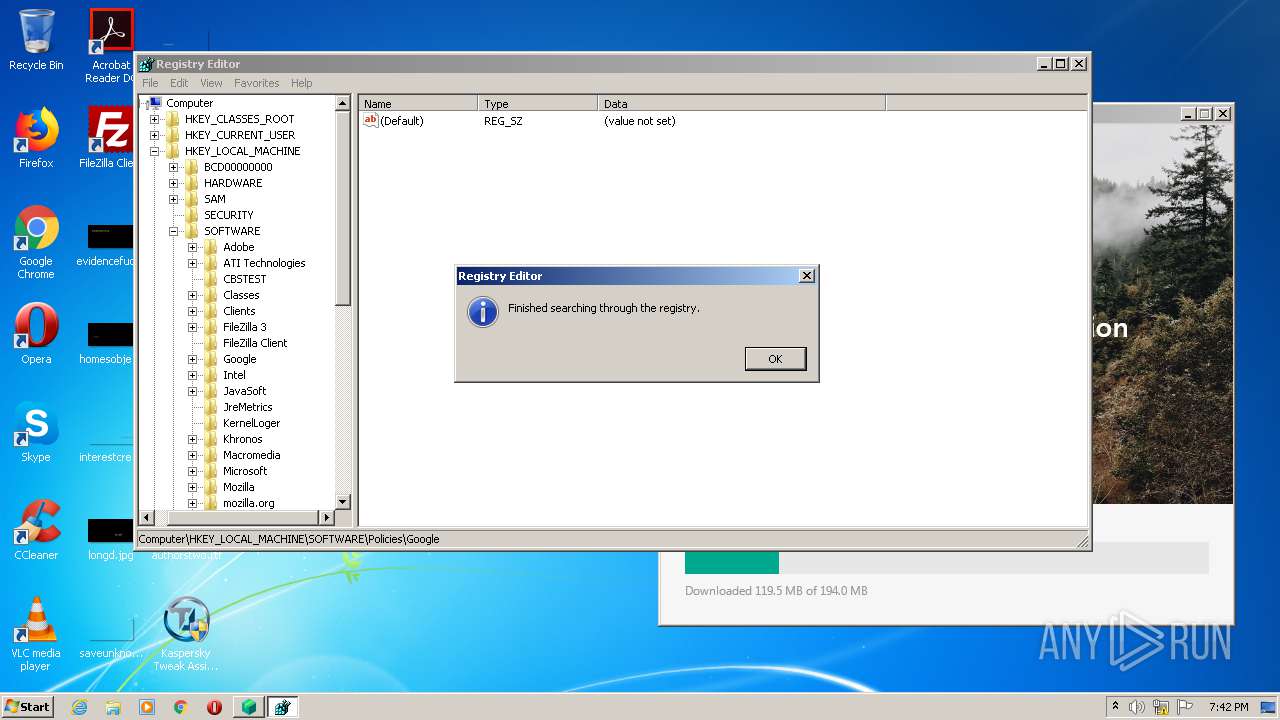
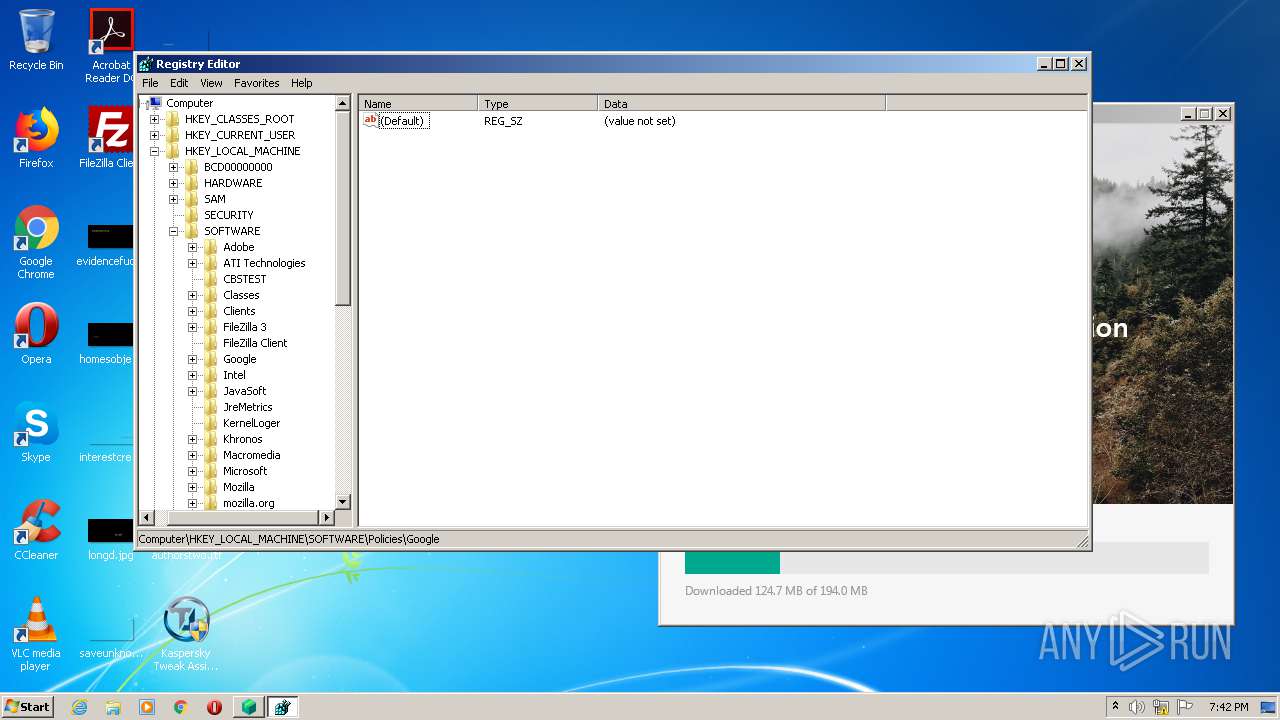
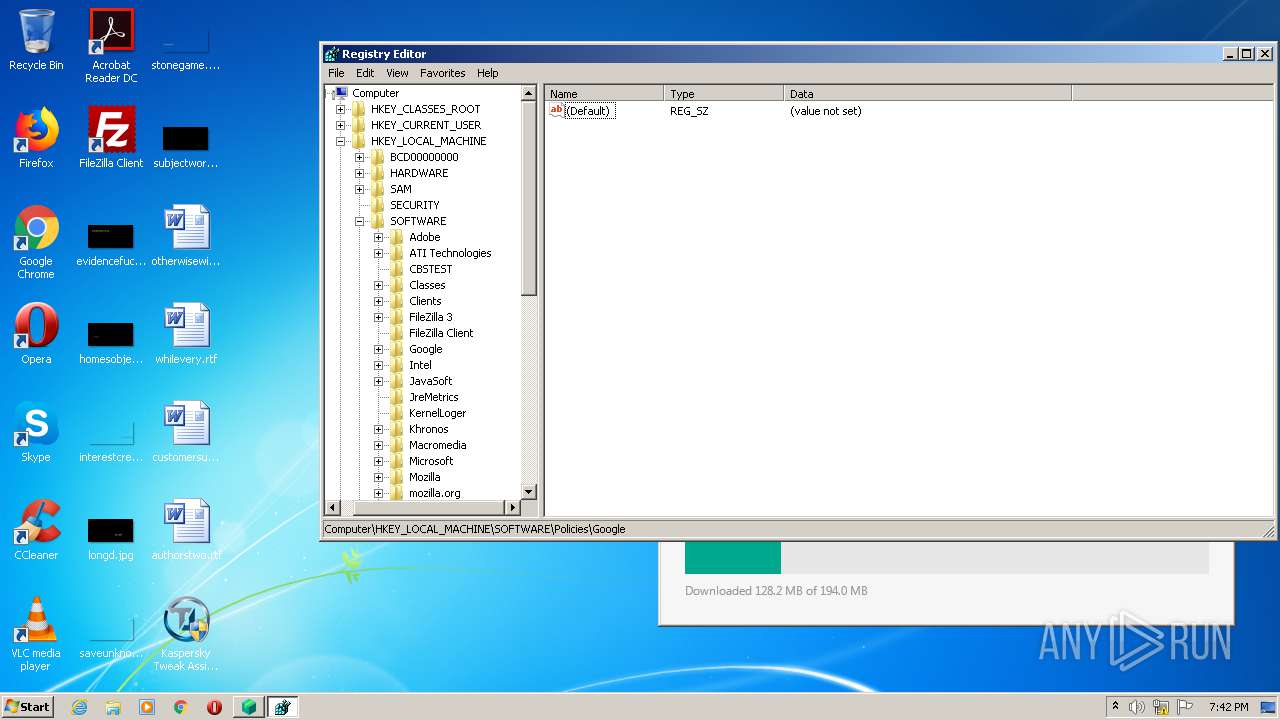
- regedit.exe (PID: 3024)
- regedit.exe (PID: 912)
- Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe (PID: 2372)
- Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe (PID: 2932)
- regedit.exe (PID: 3420)
- notepad.exe (PID: 3140)
- regedit.exe (PID: 2144)
Application launched itself
- chrome.exe (PID: 1704)
- msiexec.exe (PID: 2760)
Reads the hosts file
- chrome.exe (PID: 1704)
- chrome.exe (PID: 1648)
Reads Microsoft Office registry keys
- regedit.exe (PID: 912)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 396)
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 3416)
Creates files in the program directory
- msiexec.exe (PID: 2760)
- MsiExec.exe (PID: 3416)
- MsiExec.exe (PID: 396)
Dropped object may contain Bitcoin addresses
- MsiExec.exe (PID: 396)
Creates or modifies windows services
- MsiExec.exe (PID: 3416)
Searches for installed software
- DrvInst.exe (PID: 3392)
Low-level read access rights to disk partition
- vssvc.exe (PID: 1736)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (61.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.6) |
| .exe | | | Win32 Executable (generic) (10) |
| .exe | | | Win16/32 Executable Delphi generic (4.6) |
| .exe | | | Generic Win/DOS Executable (4.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2020:11:04 05:15:15+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 12 |
| CodeSize: | 581632 |
| InitializedDataSize: | 435712 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x52d9c1 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 21.2.4.11 |
| ProductVersionNumber: | 21.2.4.11 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Unknown |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileVersion: | 21.2.4.11 |
| Comments: | Kaspersky Tweak Assistant |
| FileDescription: | Kaspersky Tweak Assistant |
| ProductName: | Kaspersky Tweak Assistant |
| ProductVersion: | 21.2.4.11 |
| CompanyName: | TechTobo Forums |
| LegalCopyright: | Copyright © 2020 Bambang |
| LegalTradeMarks: | TechTobo |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 04-Nov-2020 04:15:15 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 04-Nov-2020 04:15:15 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0008DFDD | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.rdata | 0x0008F000 | 0x0002FD8E | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0 |
.data | 0x000BF000 | 0x00008F74 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.sgt0 | 0x000C8000 | 0x00367797 | 0x00000000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0 |
.sgt1 | 0x00430000 | 0x005AC4E0 | 0x005AC600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.96353 |
.rsrc | 0x009DD000 | 0x000159B5 | 0x00015A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.4242 |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
IPHLPAPI.DLL |
KERNEL32.dll |
MPR.dll |
OLEAUT32.dll |
PSAPI.DLL |
SHELL32.dll |
Total processes
114
Monitored processes
53
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "C:\Users\admin\Desktop\Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe" | C:\Users\admin\Desktop\Kaspersky Tweak Assistant v21.2.4.11 Final by Bambang.exe | — | explorer.exe | |||||||||||
User: admin Company: TechTobo Forums Integrity Level: MEDIUM Description: Kaspersky Tweak Assistant Exit code: 3221226540 Version: 21.2.4.11 Modules
| |||||||||||||||
| 396 | C:\Windows\system32\MsiExec.exe -Embedding 9F47D7B2A00F8E632756D0E9C42EA589 | C:\Windows\system32\MsiExec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 692 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9856481498670780529,12201888629015656781,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15589929823694846030 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3576 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9856481498670780529,12201888629015656781,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11243797798034364270 --renderer-client-id=23 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3980 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 784 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,9856481498670780529,12201888629015656781,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4329621016780048204 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2268 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9856481498670780529,12201888629015656781,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5898736593682942461 --mojo-platform-channel-handle=4700 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 912 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9856481498670780529,12201888629015656781,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6370609899829124608 --mojo-platform-channel-handle=3332 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 992 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,9856481498670780529,12201888629015656781,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14410730693031335878 --mojo-platform-channel-handle=3324 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1028 | rundll32.exe C:\Windows\system32\pnpui.dll,InstallSecurityPromptRunDllW 20 Global\{1e9ec875-61f3-43a2-2375-ef63536d0200} Global\{6046cd08-c059-340f-911d-bb7ace9ee065} C:\Windows\System32\DriverStore\Temp\{47b25f2e-5a54-36fd-d756-a61826e7e022}\klim6.inf C:\Windows\System32\DriverStore\Temp\{47b25f2e-5a54-36fd-d756-a61826e7e022}\klim6.cat | C:\Windows\system32\rundll32.exe | — | DrvInst.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 086
Read events
2 456
Write events
621
Delete events
9
Modification events
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (1720) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1704-13257891560713750 |
Value: 259 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
| (PID) Process: | (1704) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1704-13257891560713750 |
Value: 259 | |||
Executable files
248
Suspicious files
139
Text files
871
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-602ACDE9-6A8.pma | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\67c5eea9-83f6-4f98-9c79-ebd7c3362e7b.tmp | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old~RF14783c.TMP | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF1476c5.TMP | text | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1704 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF147964.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
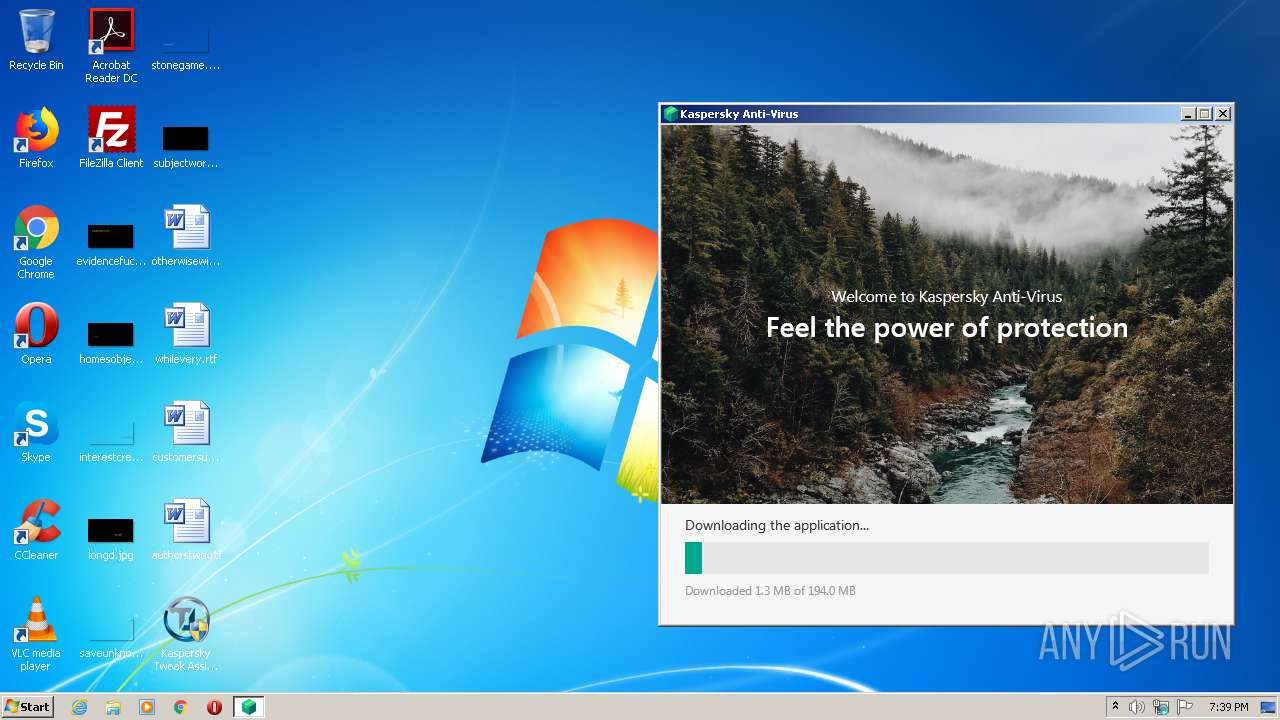
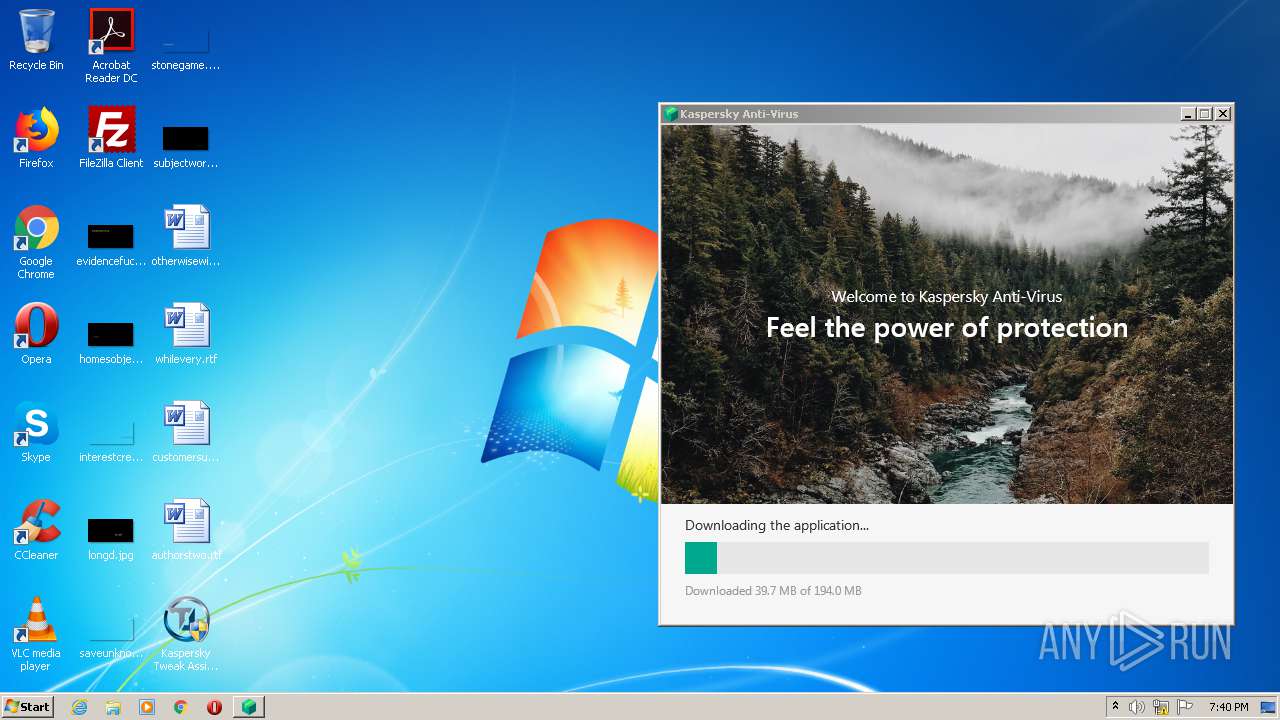
HTTP(S) requests
7
TCP/UDP connections
44
DNS requests
21
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2444 | kav21.2.16.590aben_26210.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
1648 | chrome.exe | GET | 302 | 108.177.126.198:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 521 b | whitelisted |
2168 | kav21.2.16.590aben_26210.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
1648 | chrome.exe | GET | 200 | 173.194.5.230:80 | http://r1---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx?cms_redirect=yes&mh=e_&mip=185.217.117.123&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1613417778&mv=m&mvi=1&pl=26&shardbypass=yes | US | crx | 242 Kb | whitelisted |
2168 | kav21.2.16.590aben_26210.exe | GET | 301 | 77.74.177.233:80 | http://redirect.kaspersky.com/slideshow_default | RU | html | 246 b | suspicious |
2168 | kav21.2.16.590aben_26210.exe | GET | 301 | 77.74.177.233:80 | http://redirect.kaspersky.com/slideshow_default | RU | html | 246 b | suspicious |
2168 | kav21.2.16.590aben_26210.exe | GET | 301 | 77.74.177.233:80 | http://redirect.kaspersky.com/slideshow_default | RU | html | 246 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2444 | kav21.2.16.590aben_26210.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1648 | chrome.exe | 142.250.185.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1648 | chrome.exe | 172.217.18.99:443 | www.google.com.ua | Google Inc. | US | whitelisted |
1648 | chrome.exe | 142.250.185.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
1648 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
1648 | chrome.exe | 142.250.74.195:443 | www.gstatic.com | Google Inc. | US | whitelisted |
1648 | chrome.exe | 172.217.218.196:443 | apis.google.com | Google Inc. | US | whitelisted |
1648 | chrome.exe | 142.250.186.110:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
1648 | chrome.exe | 62.115.255.86:443 | pdc5.pa2.pdc.kaspersky.com | Telia Company AB | — | unknown |
1648 | chrome.exe | 142.250.186.36:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com.ua |
| whitelisted |
pdc5.pa2.pdc.kaspersky.com |
| unknown |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2168 | kav21.2.16.590aben_26210.exe | Misc activity | APP [PTsecurity] Kaspersky Downloader |
2168 | kav21.2.16.590aben_26210.exe | Misc activity | APP [PTsecurity] Kaspersky Downloader |
2168 | kav21.2.16.590aben_26210.exe | Misc activity | APP [PTsecurity] Kaspersky Downloader |
3 ETPRO signatures available at the full report